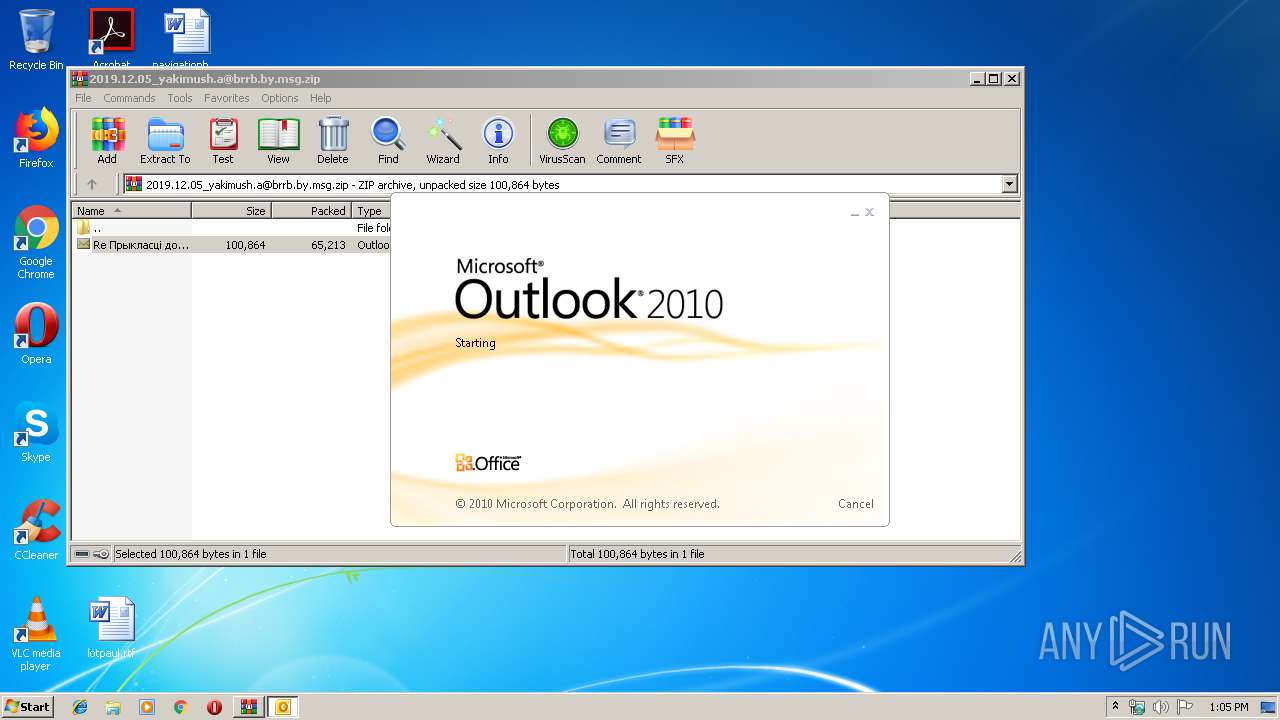
| File name: | 2019.12.05_yakimush.a@brrb.by.msg.zip |
| Full analysis: | https://app.any.run/tasks/6c2f305f-15d4-45cf-a0ab-bb5cfd086669 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 13:04:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | AD46B142361DE3EA610411962A8F04BB |
| SHA1: | 22361C4251F8A8AD6A9D1B07E666D9BD81B9352C |
| SHA256: | 0770D84CBC6CF82D9C04C6722C15688CD96A61C511DB35FC3401877A173DD776 |
| SSDEEP: | 1536:ks5+iAcWQBfaBdblNyPLOTWuNEzZ5lOuPYbf9Ue88x30Y:QiqESBtlN8LI9215lOoYT9ozY |
MALICIOUS
Changes the autorun value in the registry
- TT SWIFT COPY_pdf_____________________________________________________________.exe (PID: 1756)
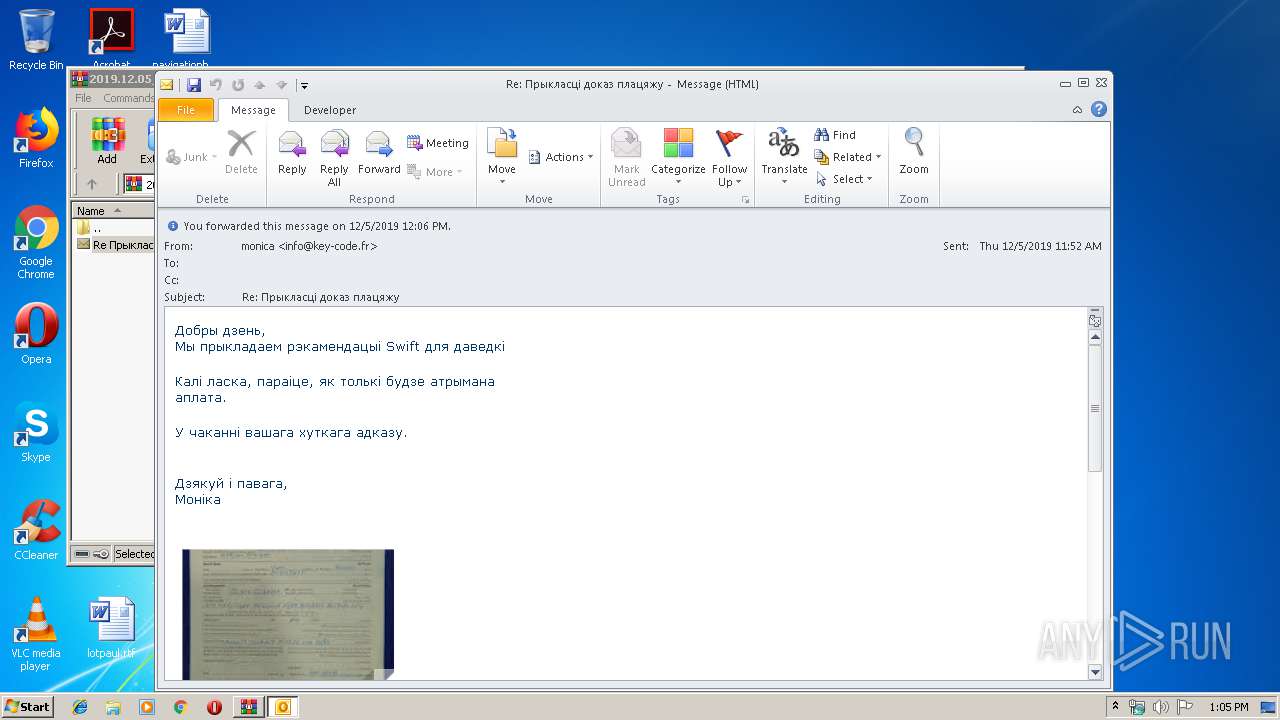
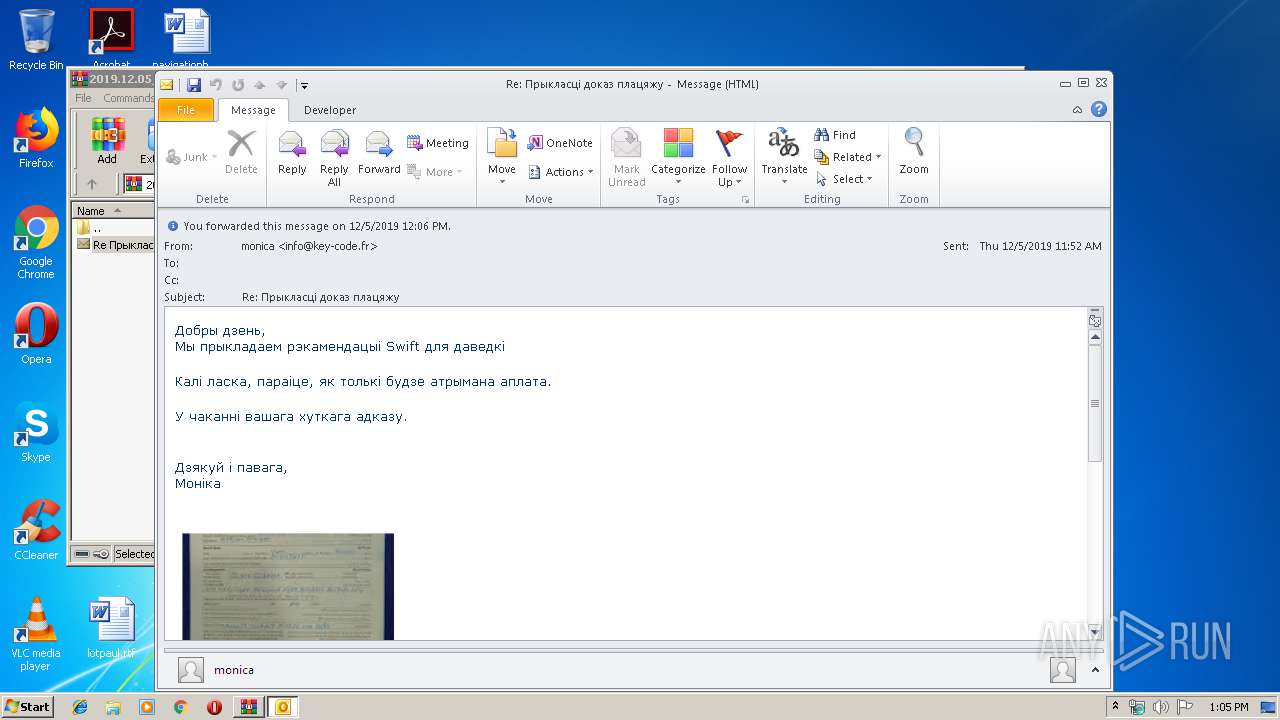
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2156)
Application was dropped or rewritten from another process
- TT SWIFT COPY_pdf_____________________________________________________________.exe (PID: 1756)
- TT SWIFT COPY_pdf_____________________________________________________________.exe (PID: 4024)
Actions looks like stealing of personal data
- InstallUtil.exe (PID: 2488)
- InstallUtil.exe (PID: 2344)
SUSPICIOUS
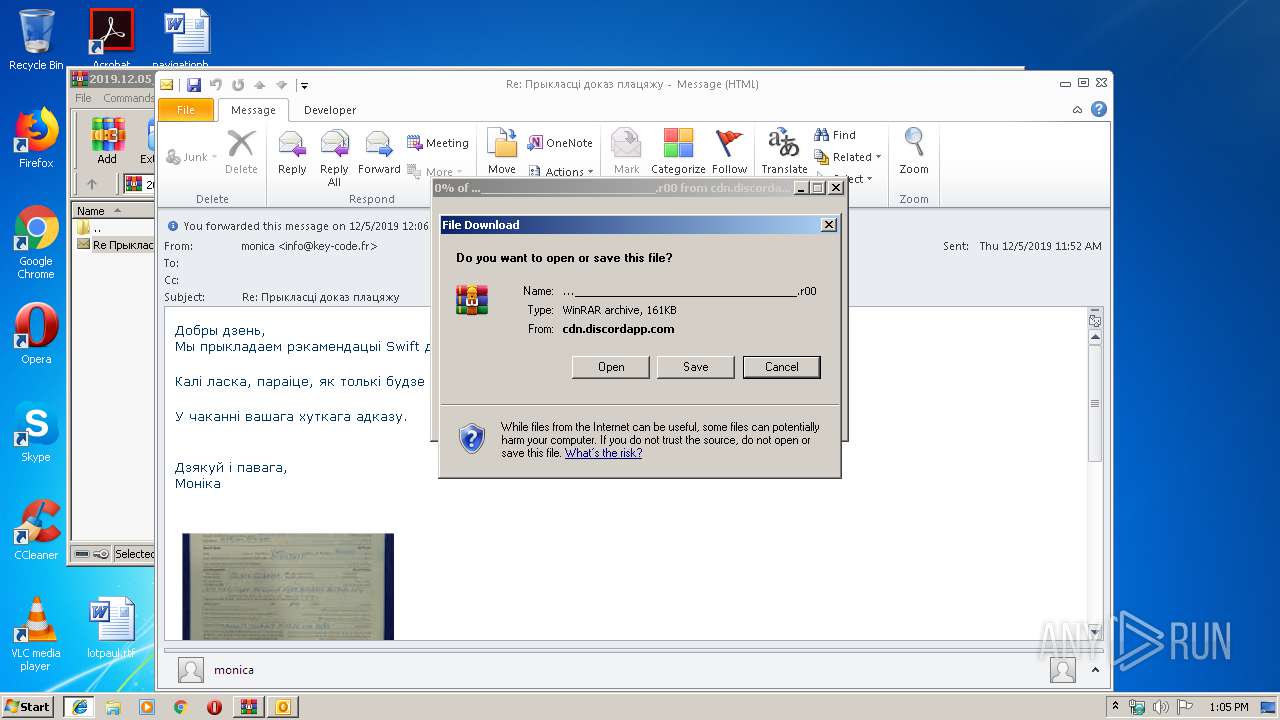
Starts Microsoft Office Application
- WinRAR.exe (PID: 1296)
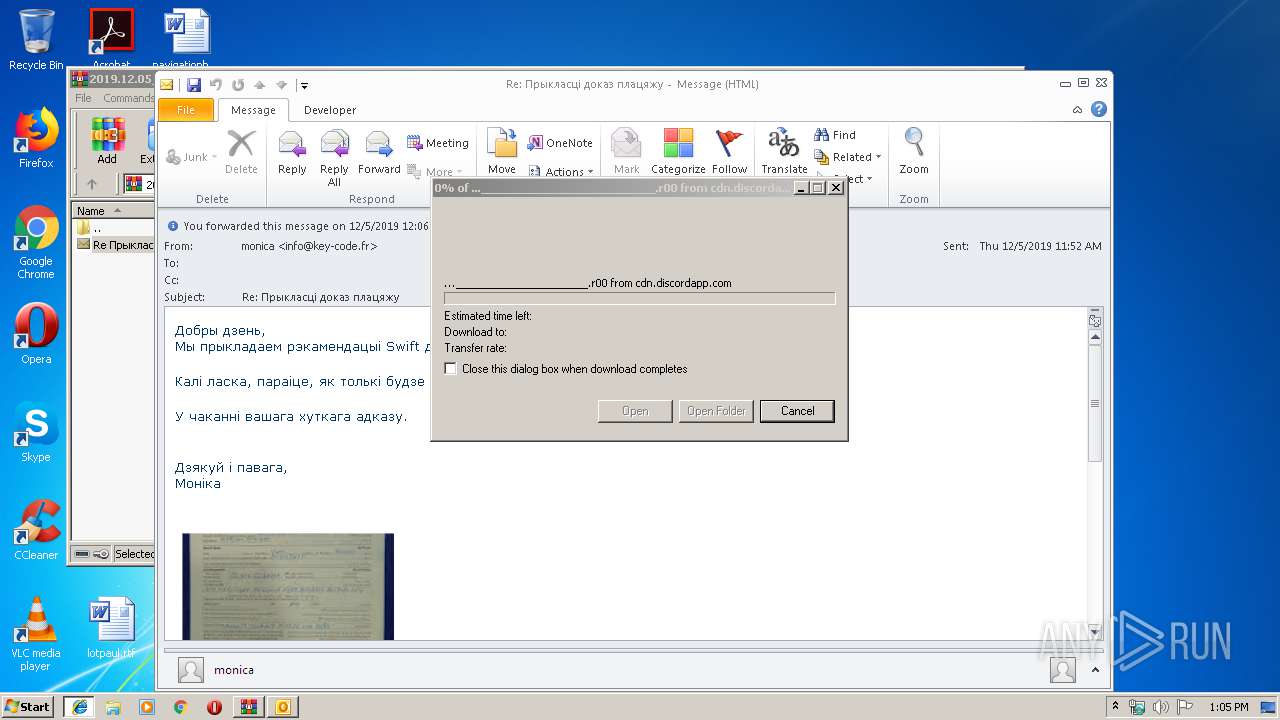
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2156)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2156)
- TT SWIFT COPY_pdf_____________________________________________________________.exe (PID: 1756)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2156)
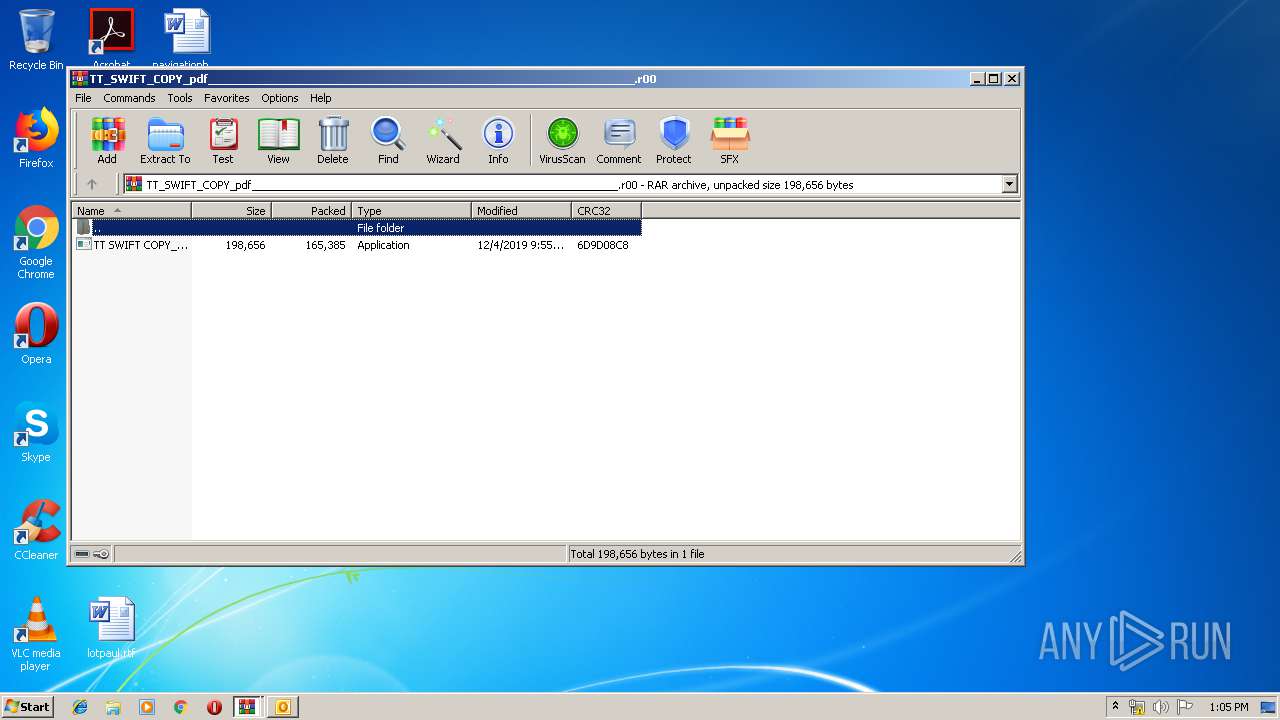
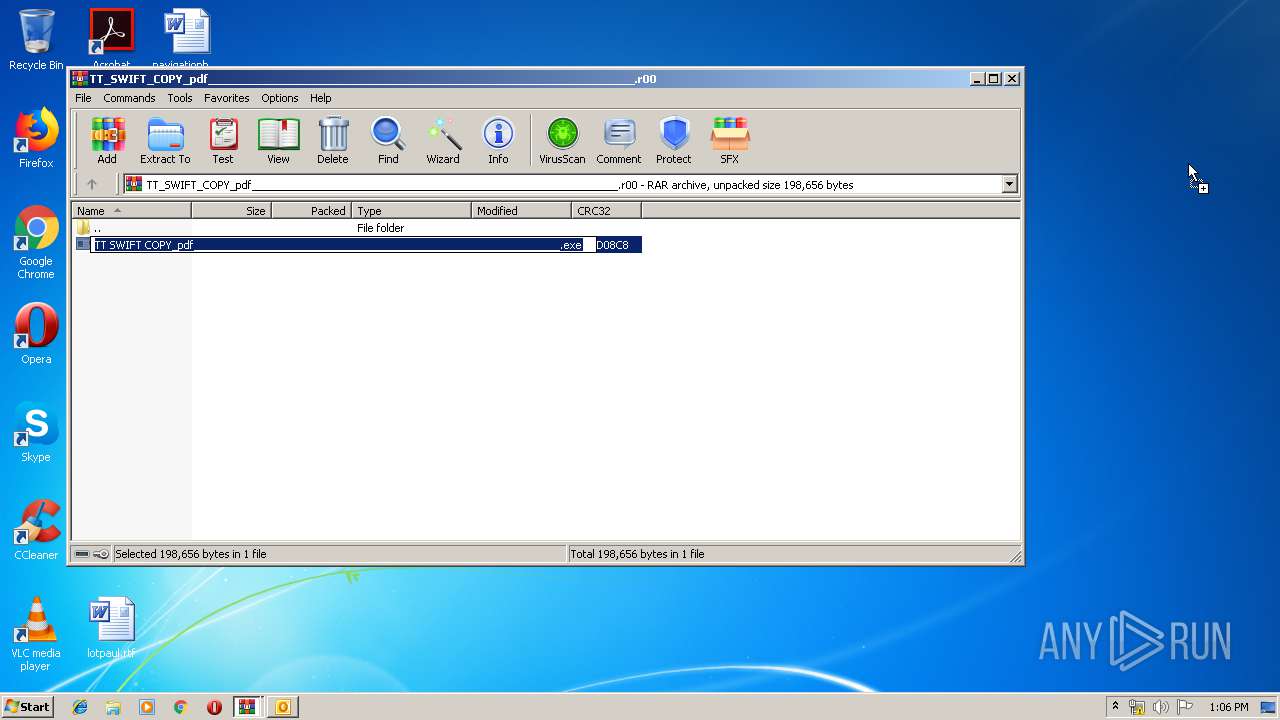
Executable content was dropped or overwritten
- WinRAR.exe (PID: 332)
- TT SWIFT COPY_pdf_____________________________________________________________.exe (PID: 1756)
Loads DLL from Mozilla Firefox
- InstallUtil.exe (PID: 2488)
- InstallUtil.exe (PID: 2344)
Checks for external IP
- InstallUtil.exe (PID: 2344)
- InstallUtil.exe (PID: 2488)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3764)
- iexplore.exe (PID: 2196)
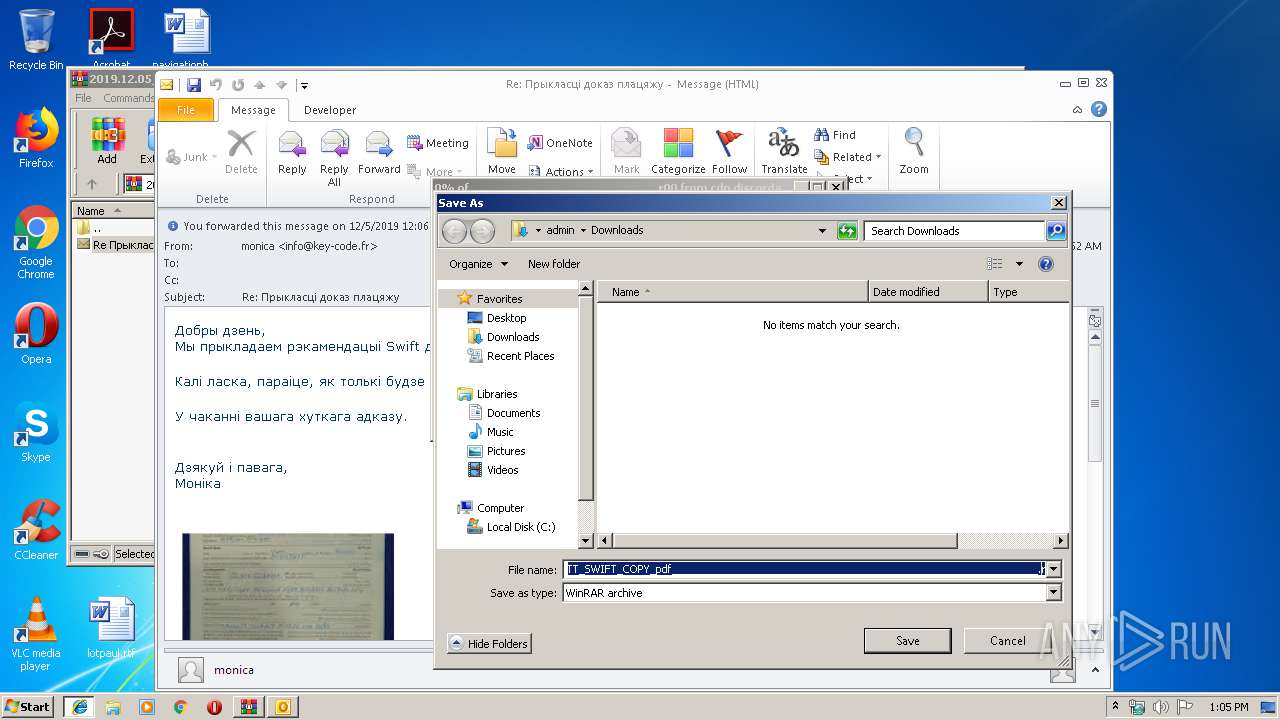
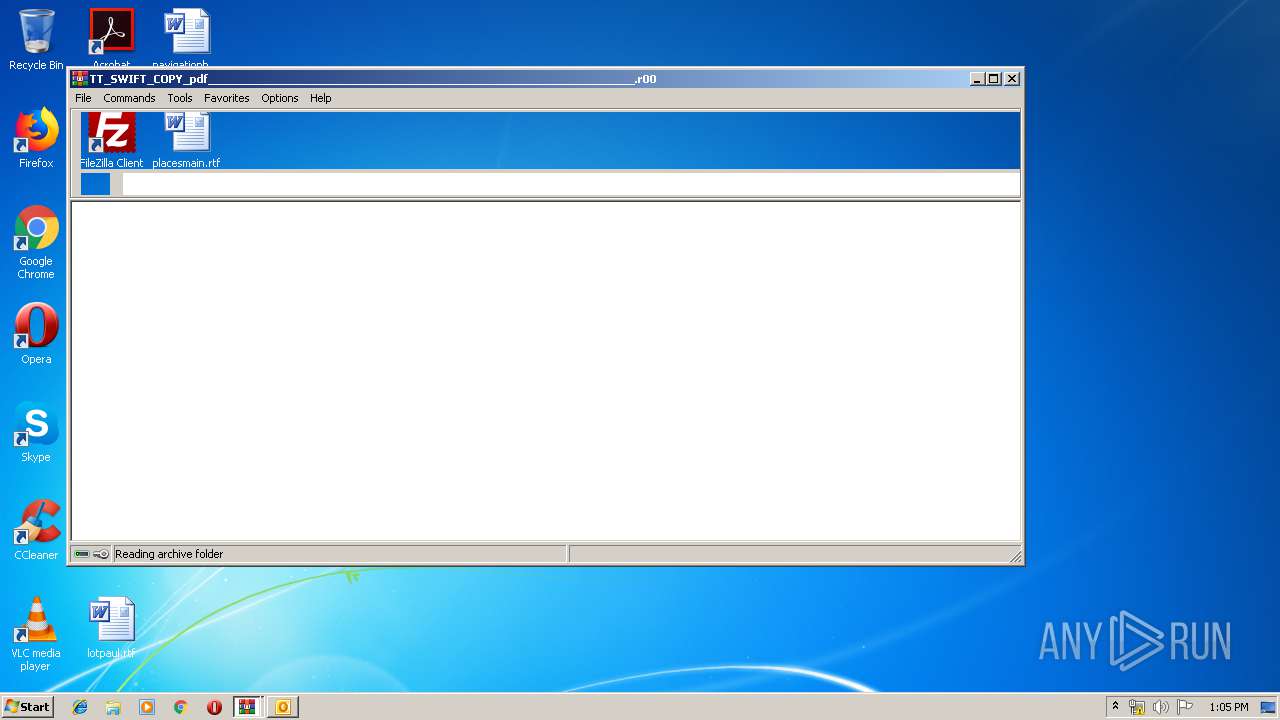
Manual execution by user
- WinRAR.exe (PID: 332)
- TT SWIFT COPY_pdf_____________________________________________________________.exe (PID: 4024)
Changes internet zones settings
- iexplore.exe (PID: 3764)
Creates files in the user directory
- iexplore.exe (PID: 2196)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2156)
Reads settings of System Certificates
- InstallUtil.exe (PID: 2488)
- InstallUtil.exe (PID: 2344)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
Total processes
47
Monitored processes
9
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
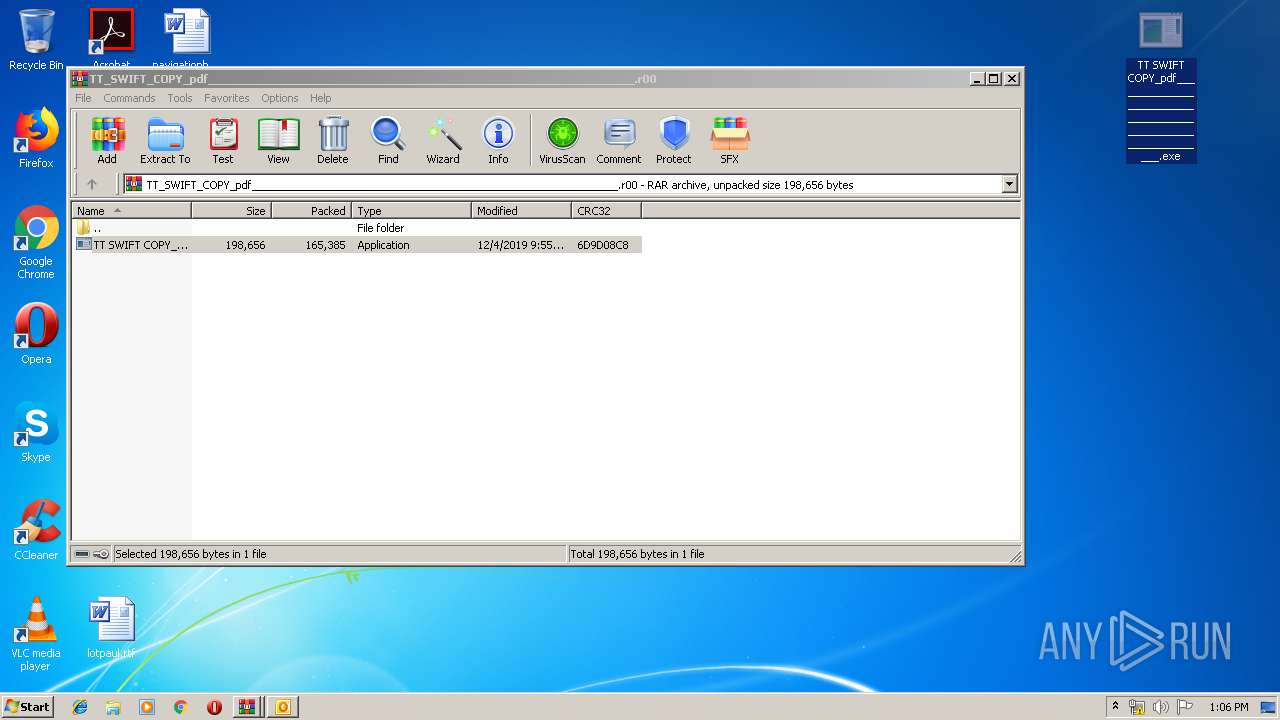
| 332 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\TT_SWIFT_COPY_pdf_____________________________________________________________.r00" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
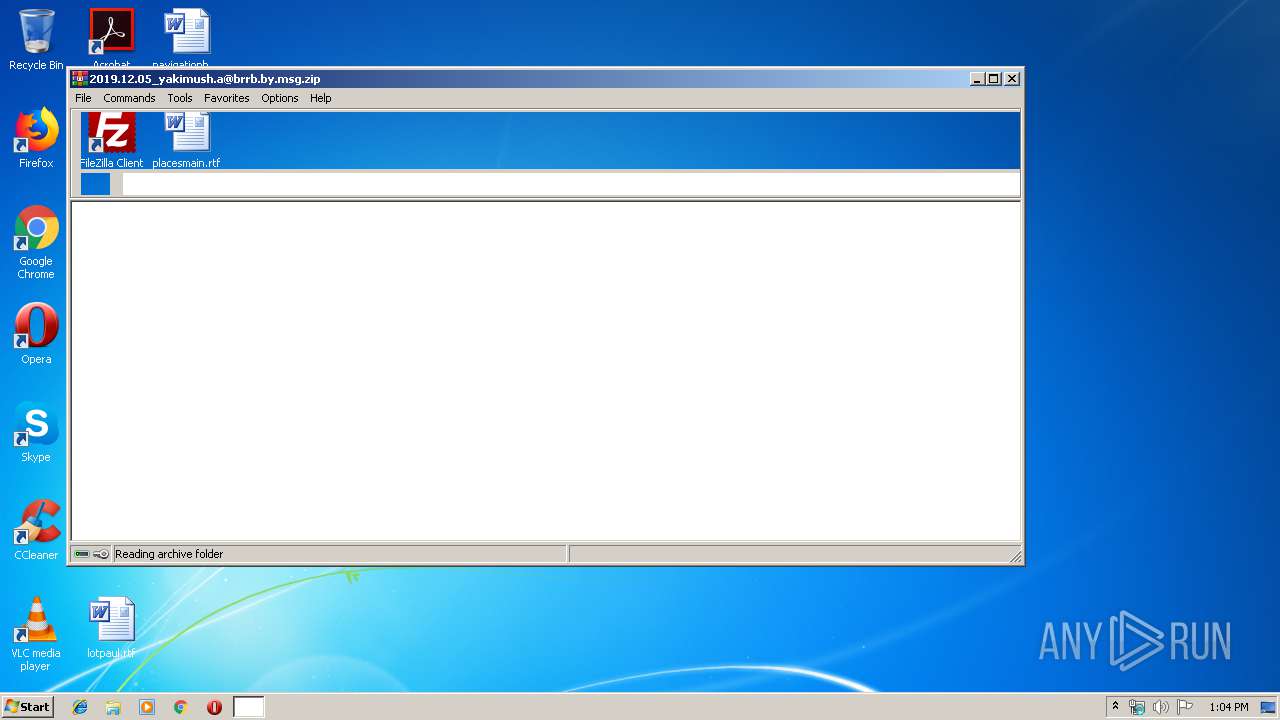
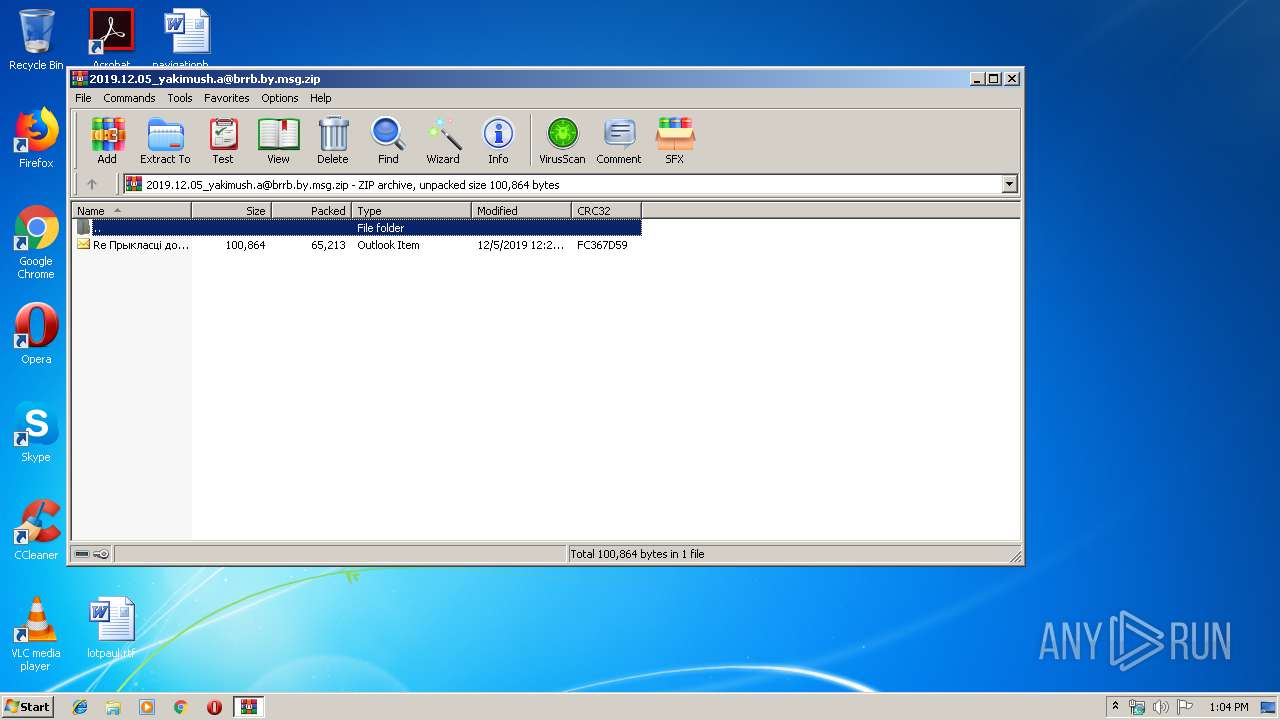
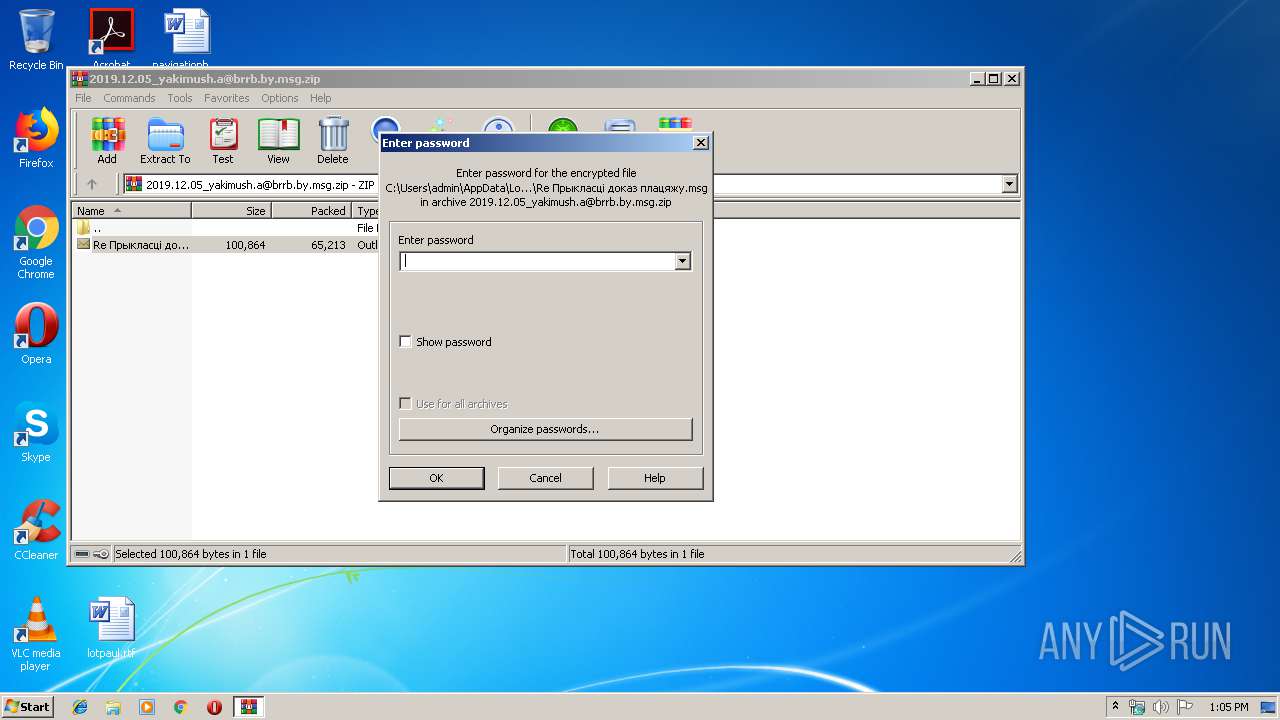
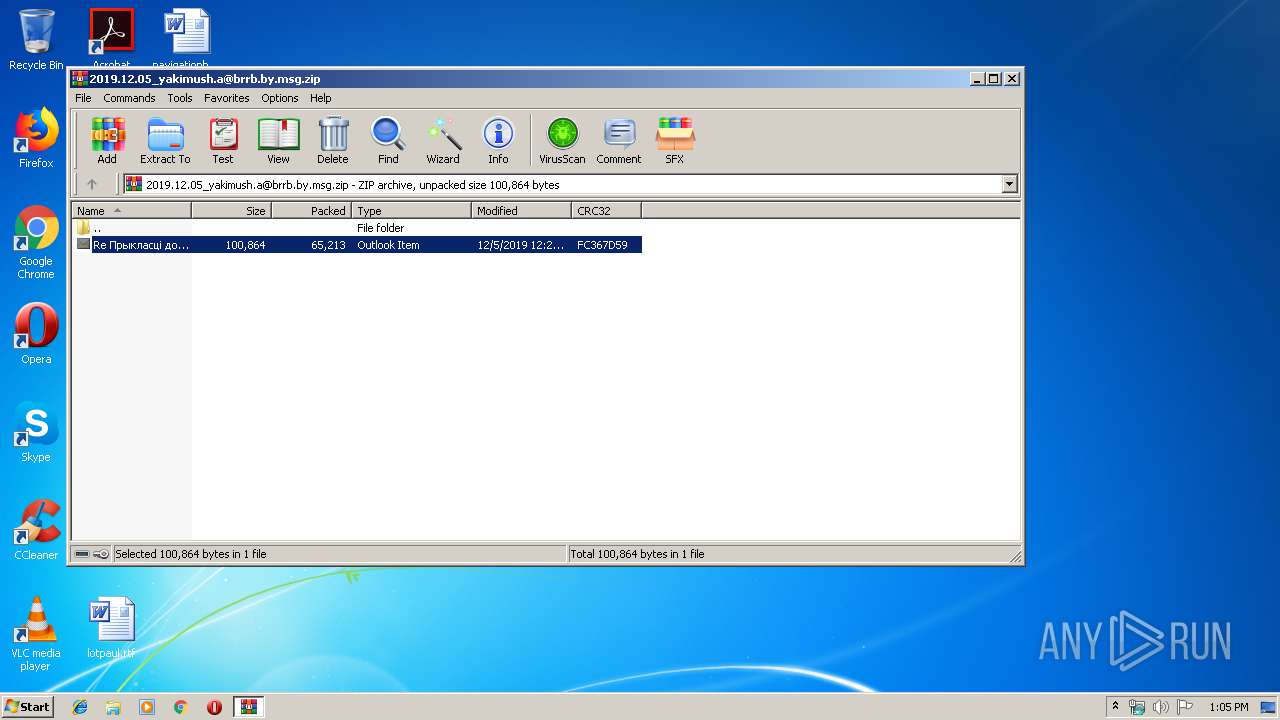
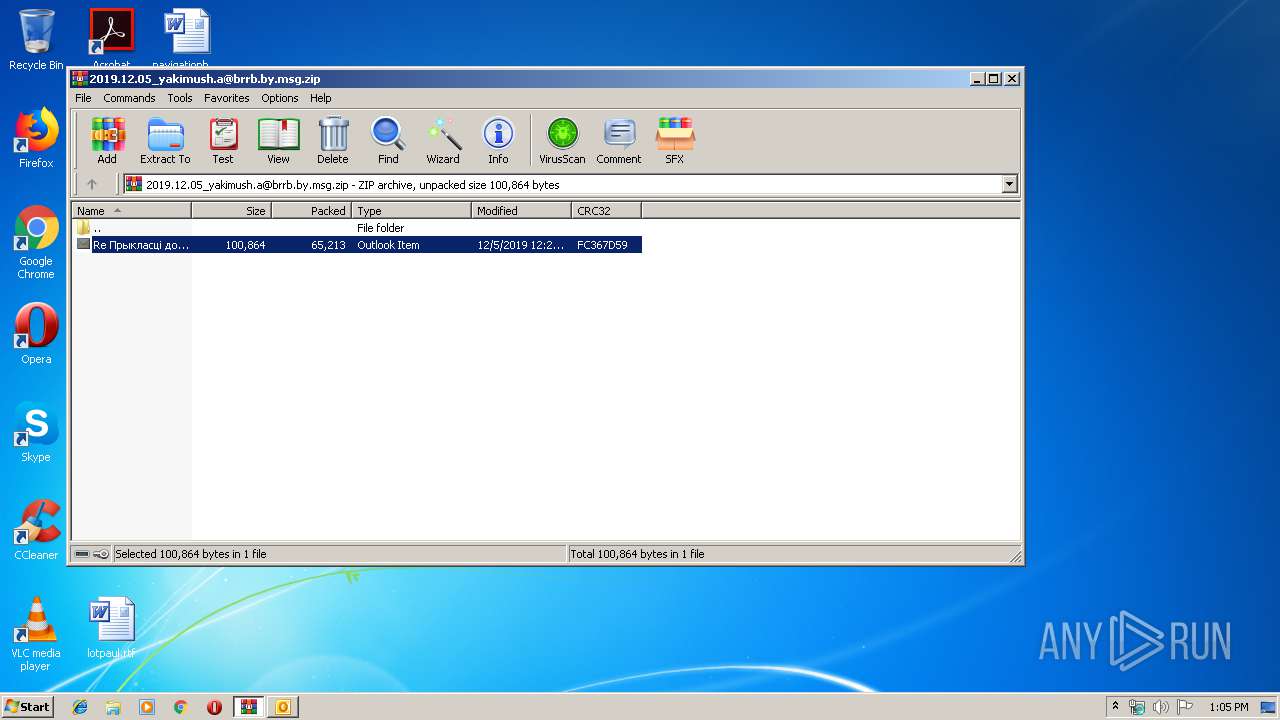
| 1296 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\2019.12.05_yakimush.a@brrb.by.msg.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1756 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa332.6025\TT SWIFT COPY_pdf_____________________________________________________________.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa332.6025\TT SWIFT COPY_pdf_____________________________________________________________.exe | WinRAR.exe | ||||||||||||
User: admin Company: Atilla Best! Integrity Level: MEDIUM Description: Exit code: 1 Version: 1.1.1.1 Modules
| |||||||||||||||
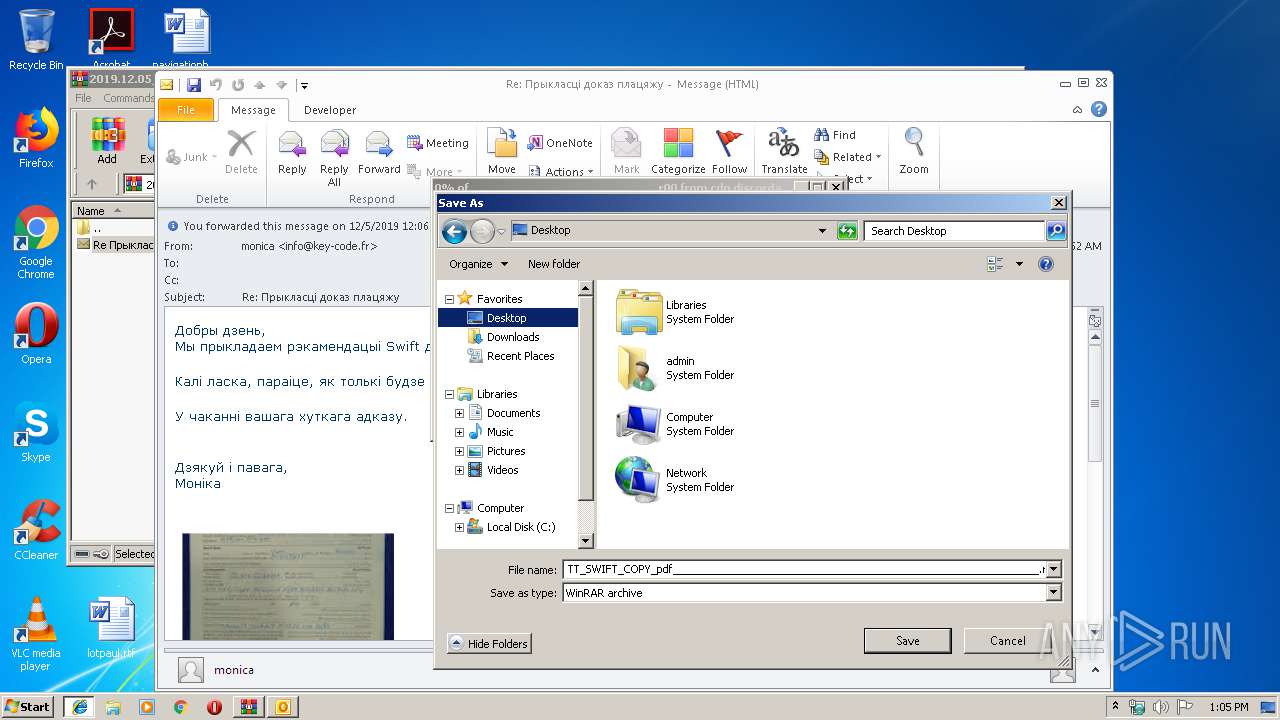
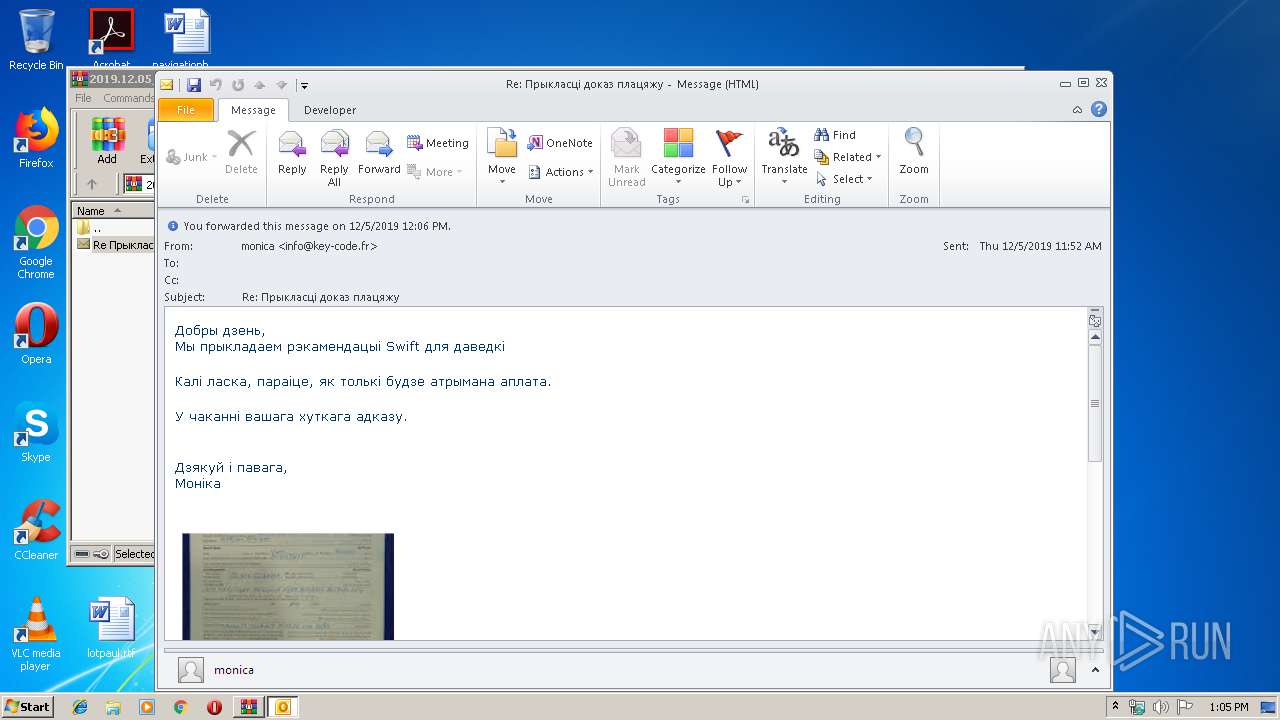
| 2156 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Rar$DIb1296.1614\Re Прыкласці доказ плацяжу.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2196 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3764 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2344 | "C:\Windows\\Microsoft.NET\\Framework\\v4.0.30319\\InstallUtil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | TT SWIFT COPY_pdf_____________________________________________________________.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 2488 | "C:\Windows\\Microsoft.NET\\Framework\\v4.0.30319\\InstallUtil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | TT SWIFT COPY_pdf_____________________________________________________________.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
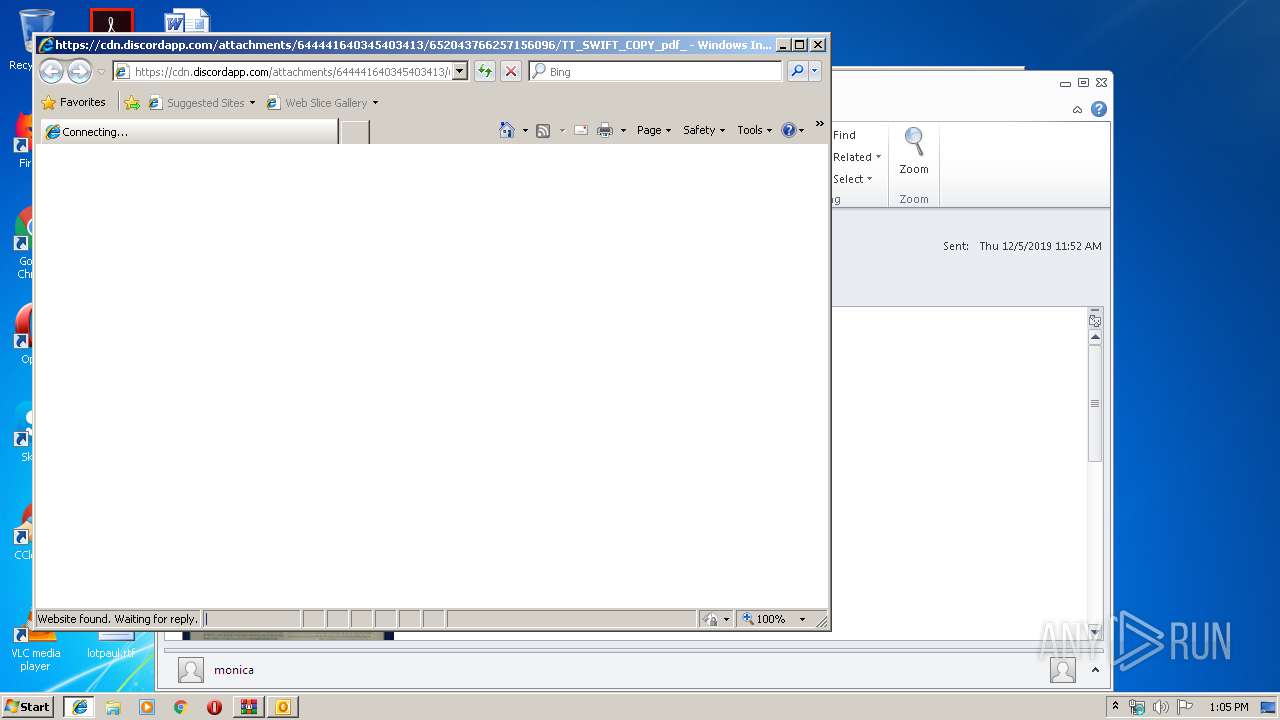
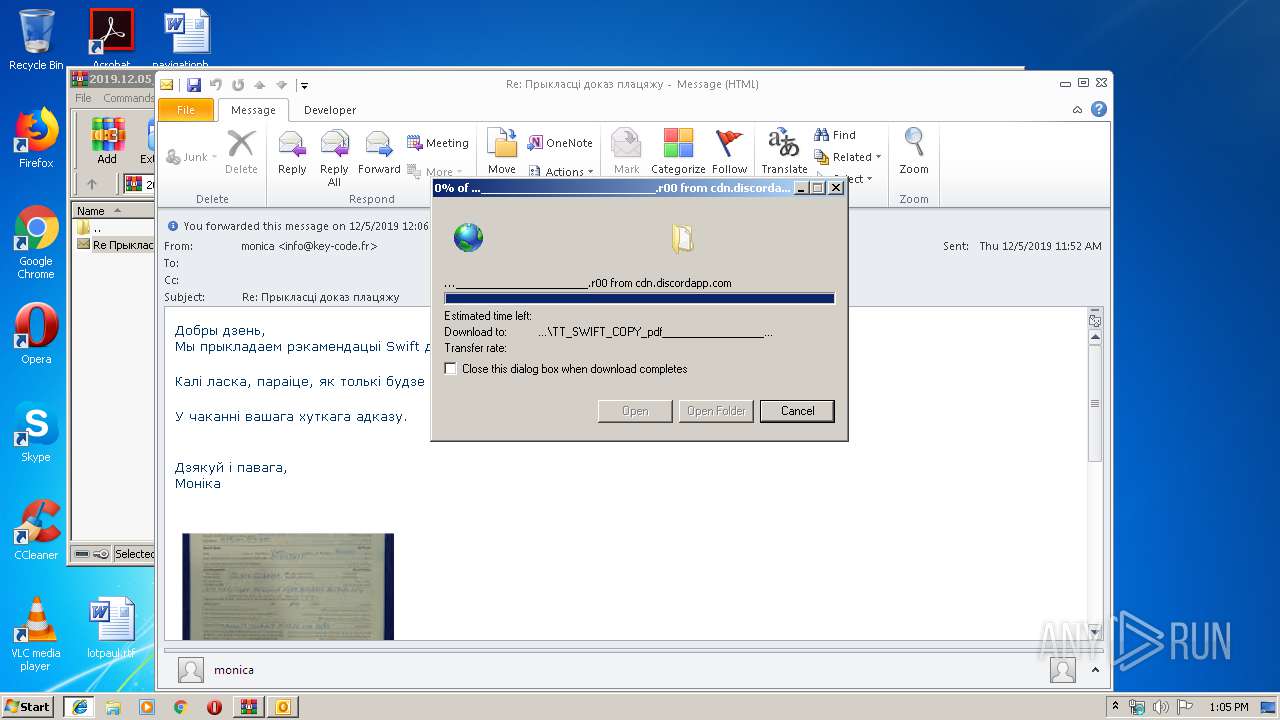
| 3764 | "C:\Program Files\Internet Explorer\iexplore.exe" https://cdn.discordapp.com/attachments/644441640345403413/652043766257156096/TT_SWIFT_COPY_pdf_____________________________________________________________.r00 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4024 | "C:\Users\admin\Desktop\TT SWIFT COPY_pdf_____________________________________________________________.exe" | C:\Users\admin\Desktop\TT SWIFT COPY_pdf_____________________________________________________________.exe | — | explorer.exe | |||||||||||
User: admin Company: Atilla Best! Integrity Level: MEDIUM Description: Exit code: 1 Version: 1.1.1.1 Modules
| |||||||||||||||
Total events
3 446
Read events
2 700
Write events
723
Delete events
23
Modification events
| (PID) Process: | (1296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1296) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\2019.12.05_yakimush.a@brrb.by.msg.zip | |||
| (PID) Process: | (1296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {0006F045-0000-0000-C000-000000000046} {000214FA-0000-0000-C000-000000000046} 0xFFFF |
Value: 01000000000000001E8712C135ACD501 | |||
| (PID) Process: | (1296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {0006F045-0000-0000-C000-000000000046} {000214EB-0000-0000-C000-000000000046} 0xFFFF |
Value: 0100000000000000D24B17C135ACD501 | |||
Executable files
3
Suspicious files
3
Text files
36
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2156 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR25EC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3764 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3764 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2156 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 1296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb1296.1614\Re Прыкласці доказ плацяжу.msg | msg | |
MD5:— | SHA256:— | |||
| 3764 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFDD6B159CA12FDF36.TMP | — | |
MD5:— | SHA256:— | |||
| 2156 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2156 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\FAD8CB37.dat | image | |
MD5:— | SHA256:— | |||
| 2196 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2156 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_BA87B004D953564BBB59636A4CFD2D4C.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
7
DNS requests
5
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2156 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2488 | InstallUtil.exe | GET | 200 | 216.146.43.70:80 | http://checkip.dyndns.org/ | US | html | 107 b | shared |
2344 | InstallUtil.exe | GET | 200 | 216.146.43.70:80 | http://checkip.dyndns.org/ | US | html | 107 b | shared |
3764 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2196 | iexplore.exe | 162.159.130.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
2488 | InstallUtil.exe | 216.146.43.70:80 | checkip.dyndns.org | Dynamic Network Services, Inc. | US | shared |
3764 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2488 | InstallUtil.exe | 199.193.7.228:587 | smtp.privateemail.com | Namecheap, Inc. | US | unknown |
2156 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2344 | InstallUtil.exe | 199.193.7.228:587 | smtp.privateemail.com | Namecheap, Inc. | US | unknown |
2344 | InstallUtil.exe | 216.146.43.70:80 | checkip.dyndns.org | Dynamic Network Services, Inc. | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
cdn.discordapp.com |
| shared |
www.bing.com |
| whitelisted |
checkip.dyndns.org |
| shared |
smtp.privateemail.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.dyndns. Domain |
1080 | svchost.exe | Misc activity | AV INFO Query to checkip.dyndns. Domain |
2488 | InstallUtil.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup - checkip.dyndns.org |
2488 | InstallUtil.exe | Potentially Bad Traffic | ET POLICY DynDNS CheckIp External IP Address Server Response |
2488 | InstallUtil.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2344 | InstallUtil.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup - checkip.dyndns.org |
2344 | InstallUtil.exe | Potentially Bad Traffic | ET POLICY DynDNS CheckIp External IP Address Server Response |
2344 | InstallUtil.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |