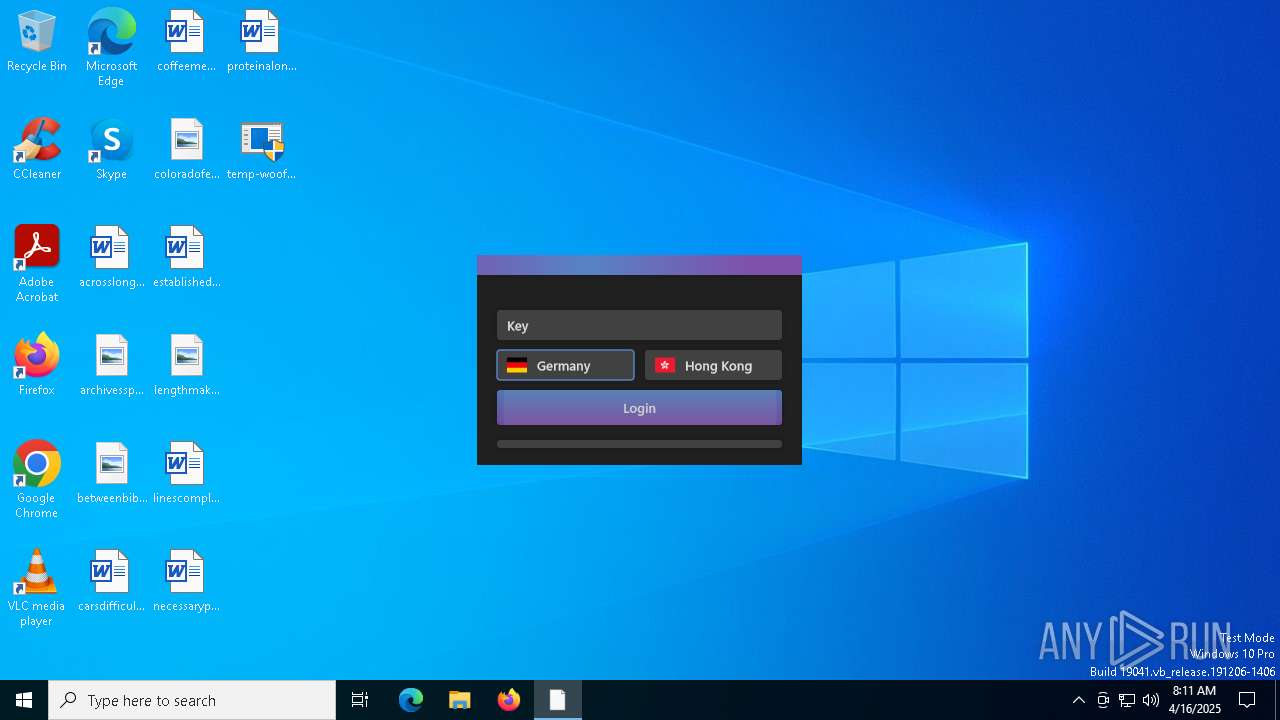
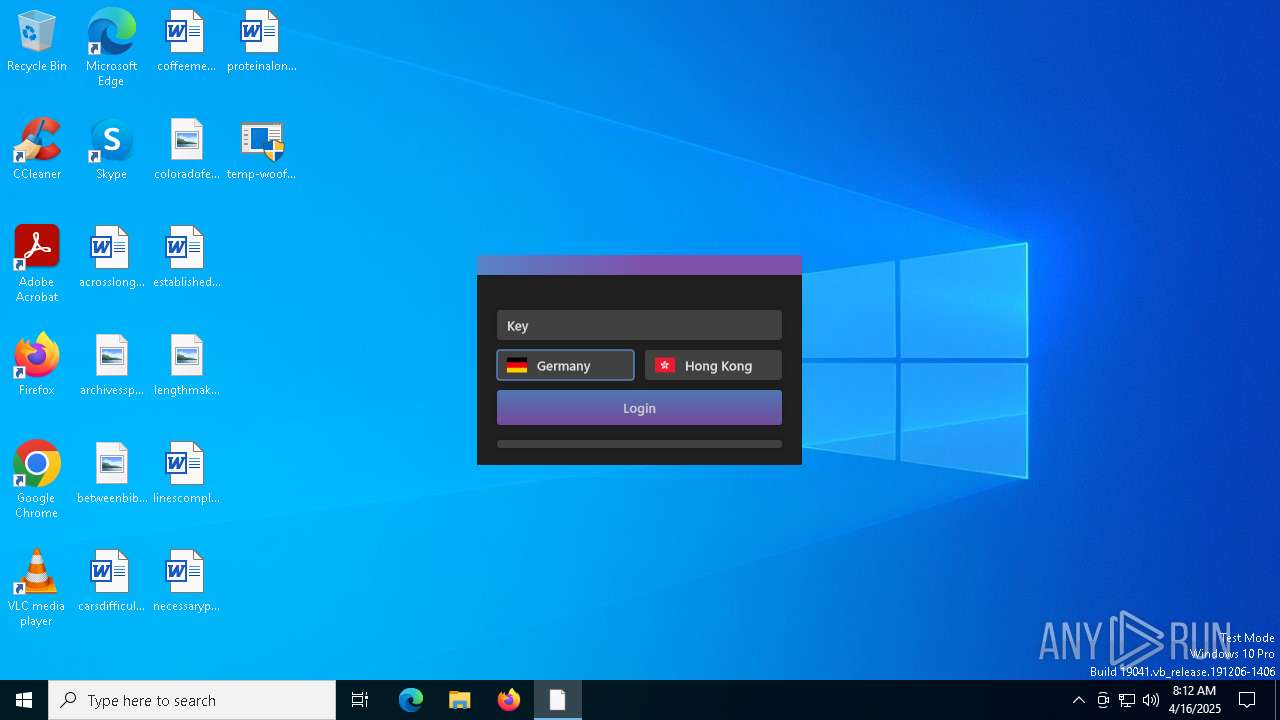
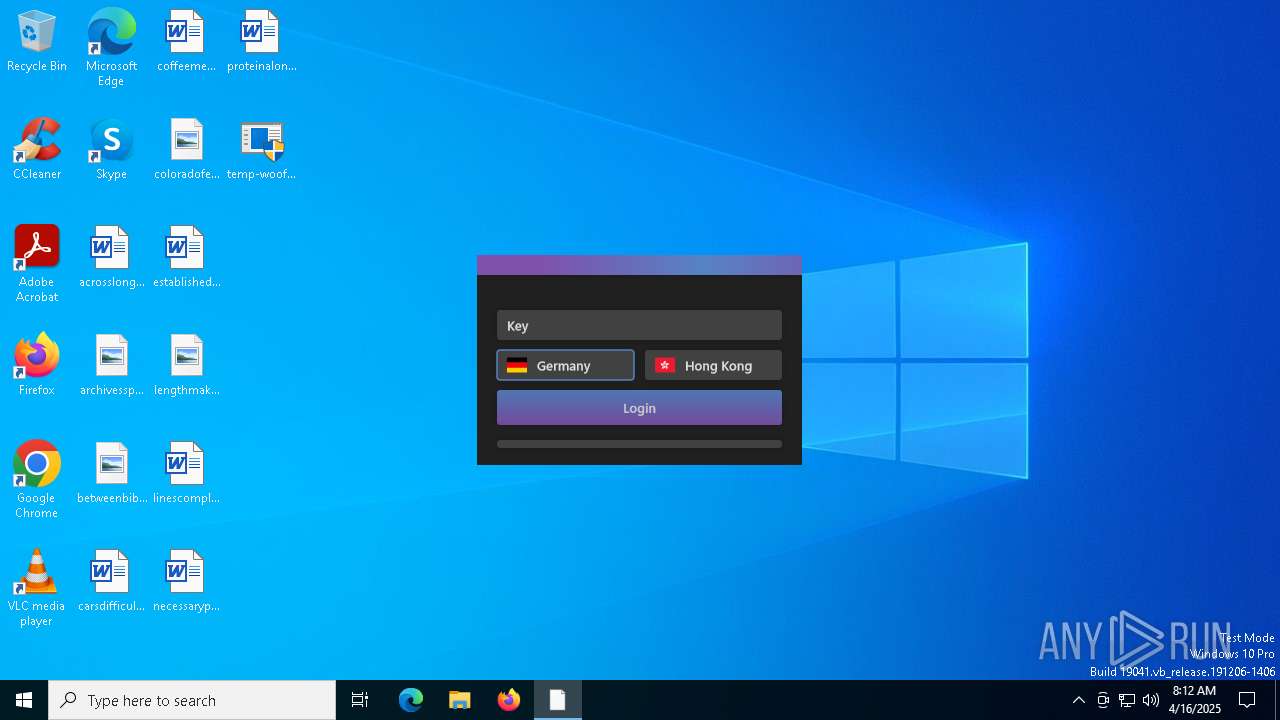
| File name: | temp-woofer.exe |
| Full analysis: | https://app.any.run/tasks/c428897f-14fa-4168-9815-4ce86f424ec2 |
| Verdict: | Malicious activity |
| Analysis date: | April 16, 2025, 08:10:13 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | E8530662F3DA98C34AA3B3D9E0434A4A |
| SHA1: | 02EF335FCEA84E72DB8F01E0DB963227C7F4E043 |
| SHA256: | 0740255F7B53654E2486E1275AE2E7D6C11D072849045C143F530C7B4C4FD1CF |
| SSDEEP: | 98304:5ciy/W+JUeTwXPFogbDJ8TpRQedKD35MLHbIryT2mw94Ze91/k/aQ4v3zG2EEI3e:Z9GgLXwqKfmvv51Yf/oZ0i |
MALICIOUS
JEEFO has been detected
- temp-woofer.exe (PID: 5728)
- icsys.icn.exe (PID: 3020)
- explorer.exe (PID: 1812)
- svchost.exe (PID: 5608)
Changes the autorun value in the registry
- explorer.exe (PID: 1812)
- svchost.exe (PID: 5608)
SUSPICIOUS
Executable content was dropped or overwritten
- temp-woofer.exe (PID: 5728)
- icsys.icn.exe (PID: 3020)
- explorer.exe (PID: 1812)
- spoolsv.exe (PID: 1272)
Starts itself from another location
- temp-woofer.exe (PID: 5728)
- icsys.icn.exe (PID: 3020)
- explorer.exe (PID: 1812)
- spoolsv.exe (PID: 1272)
- svchost.exe (PID: 5608)
Starts application with an unusual extension
- temp-woofer.exe (PID: 5728)
The process creates files with name similar to system file names
- icsys.icn.exe (PID: 3020)
- spoolsv.exe (PID: 1272)
Creates or modifies Windows services
- svchost.exe (PID: 5608)
INFO
Reads the computer name
- temp-woofer.exe (PID: 1764)
- svchost.exe (PID: 5608)
The sample compiled with english language support
- temp-woofer.exe (PID: 5728)
- icsys.icn.exe (PID: 3020)
- explorer.exe (PID: 1812)
- spoolsv.exe (PID: 1272)
Checks supported languages
- temp-woofer.exe (PID: 1764)
- icsys.icn.exe (PID: 3020)
- temp-woofer.exe (PID: 5728)
- explorer.exe (PID: 1812)
- spoolsv.exe (PID: 6240)
- svchost.exe (PID: 5608)
- spoolsv.exe (PID: 1272)
Create files in a temporary directory
- temp-woofer.exe (PID: 5728)
- icsys.icn.exe (PID: 3020)
- explorer.exe (PID: 1812)
- spoolsv.exe (PID: 1272)
- svchost.exe (PID: 5608)
- spoolsv.exe (PID: 6240)
- temp-woofer.exe (PID: 1764)
Checks proxy server information
- slui.exe (PID: 6372)
Reads the software policy settings
- slui.exe (PID: 6372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:04:01 07:08:22+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 106496 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x290c |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| ProductName: | Project1 |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | TJprojMain |
| OriginalFileName: | TJprojMain.exe |
Total processes
133
Monitored processes
9
Malicious processes
5
Suspicious processes
0
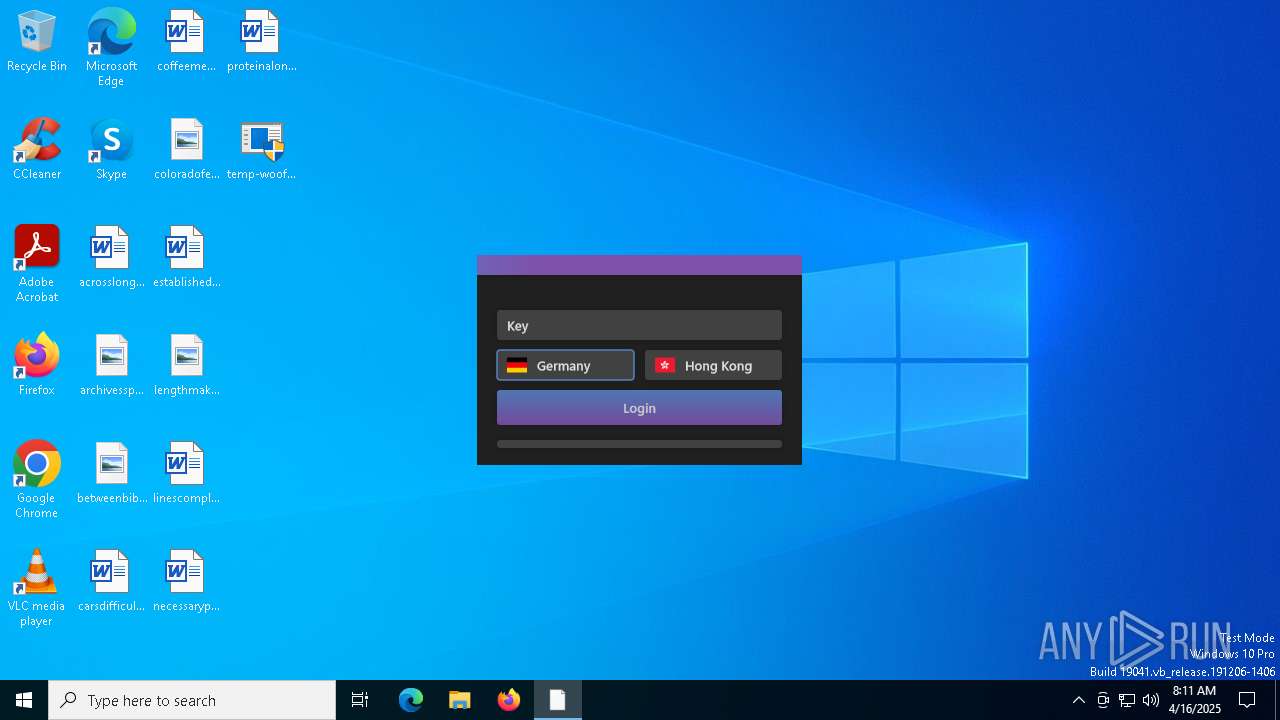
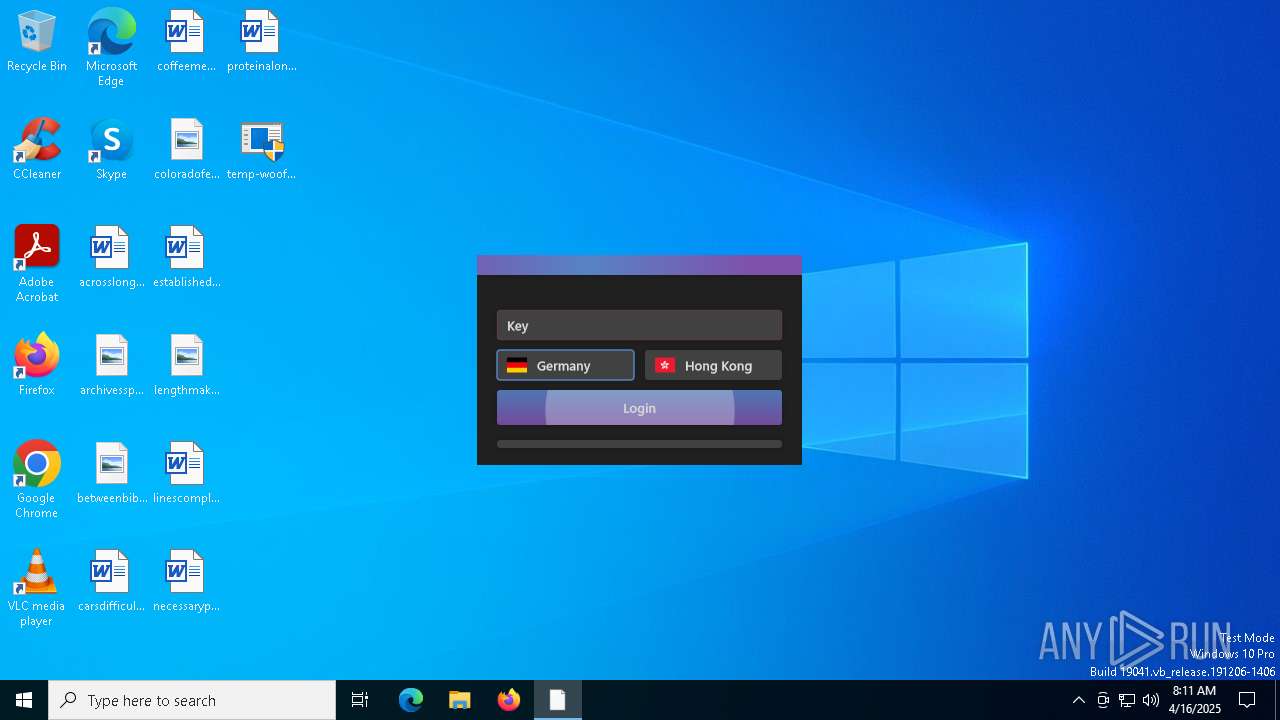
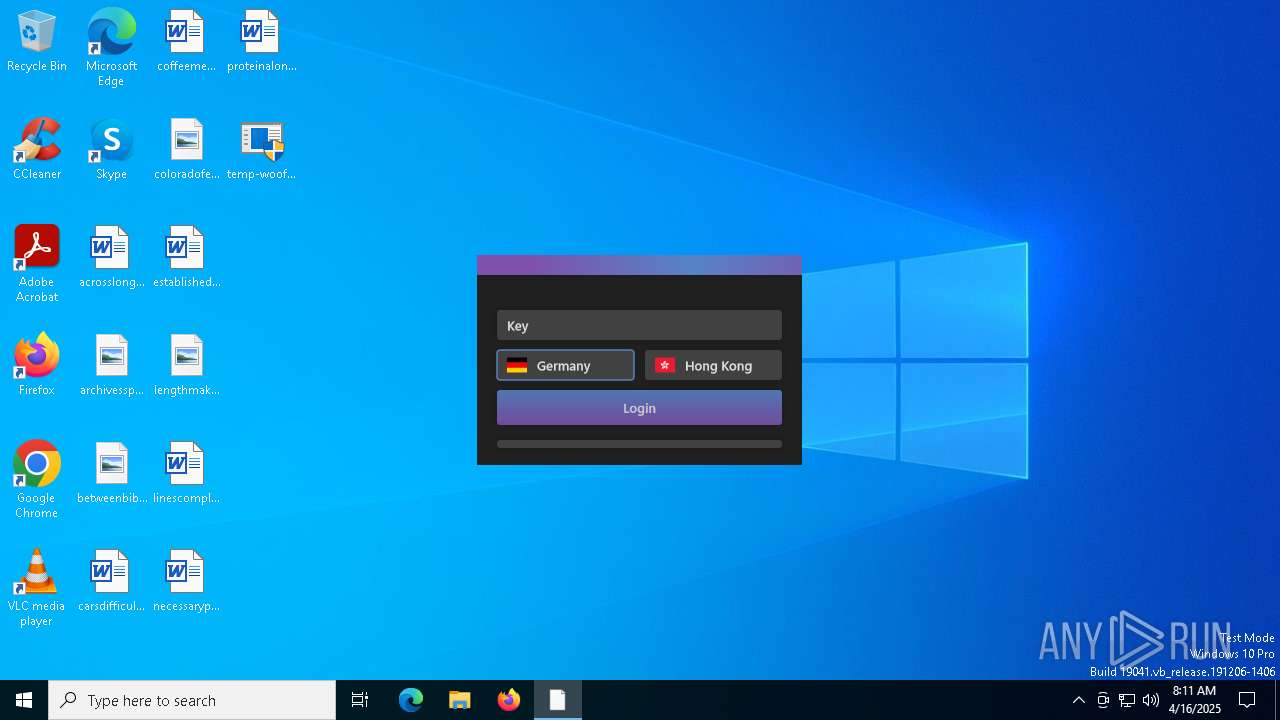
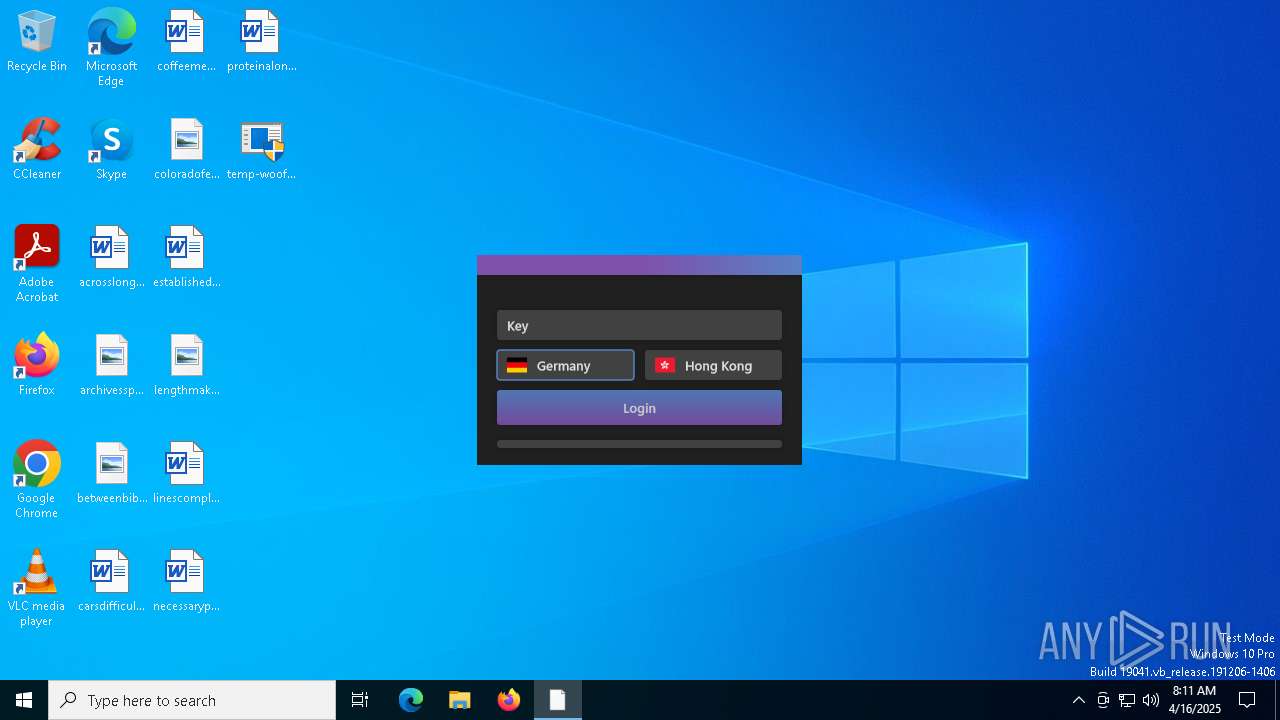
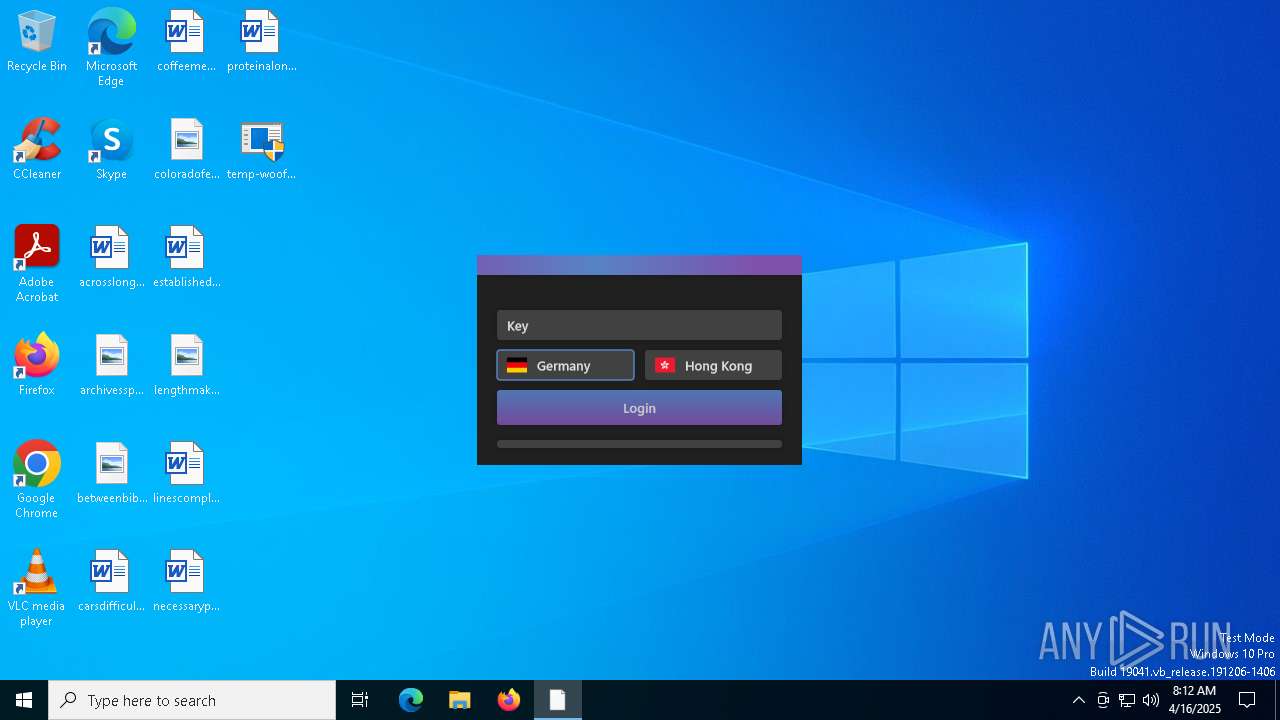
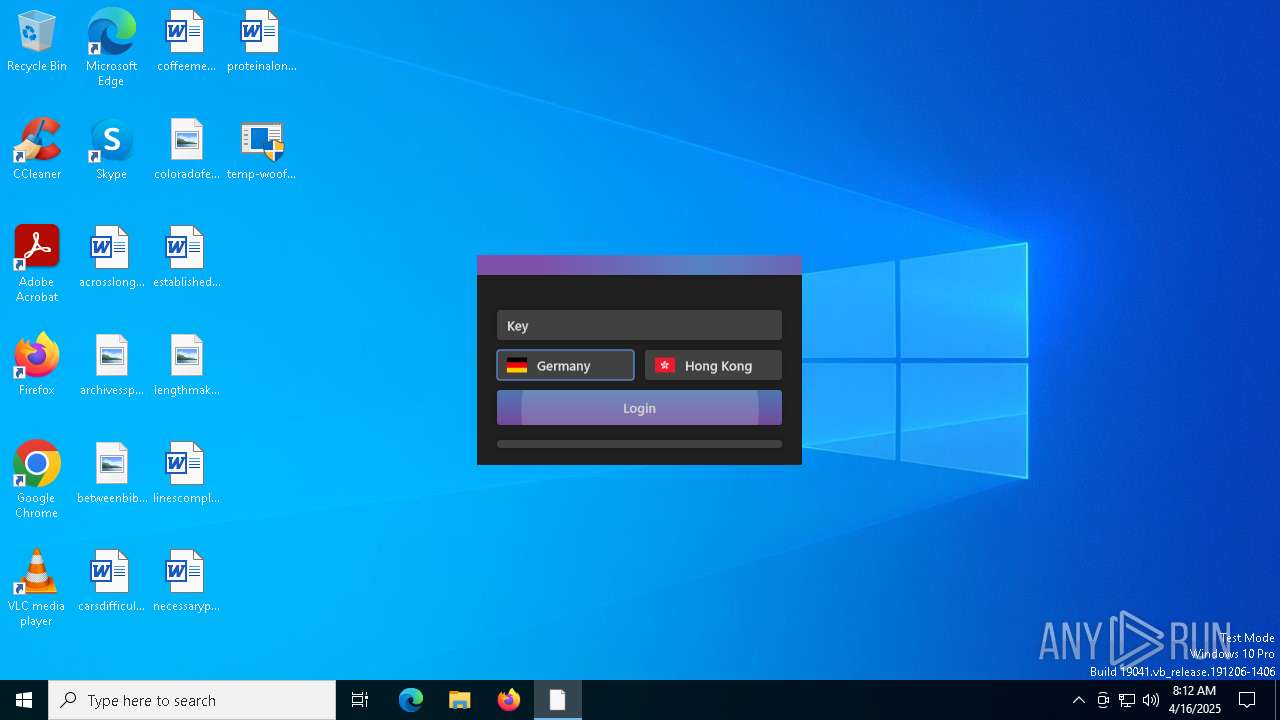
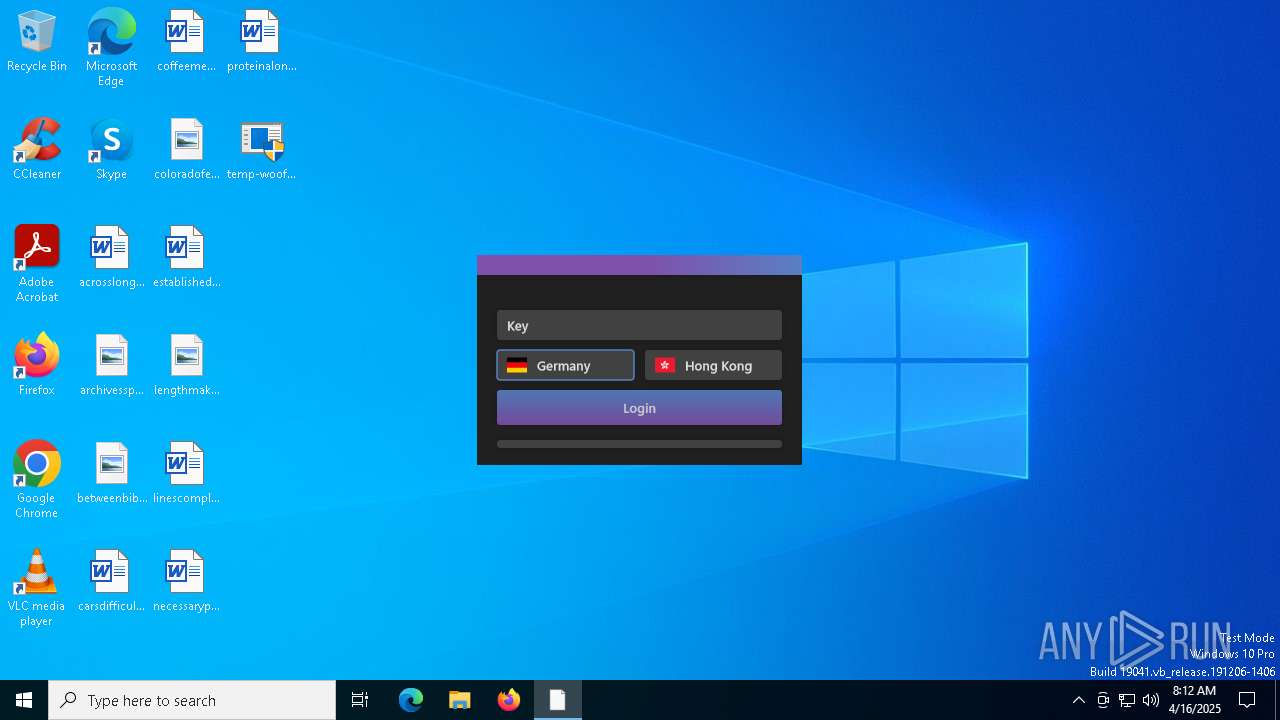
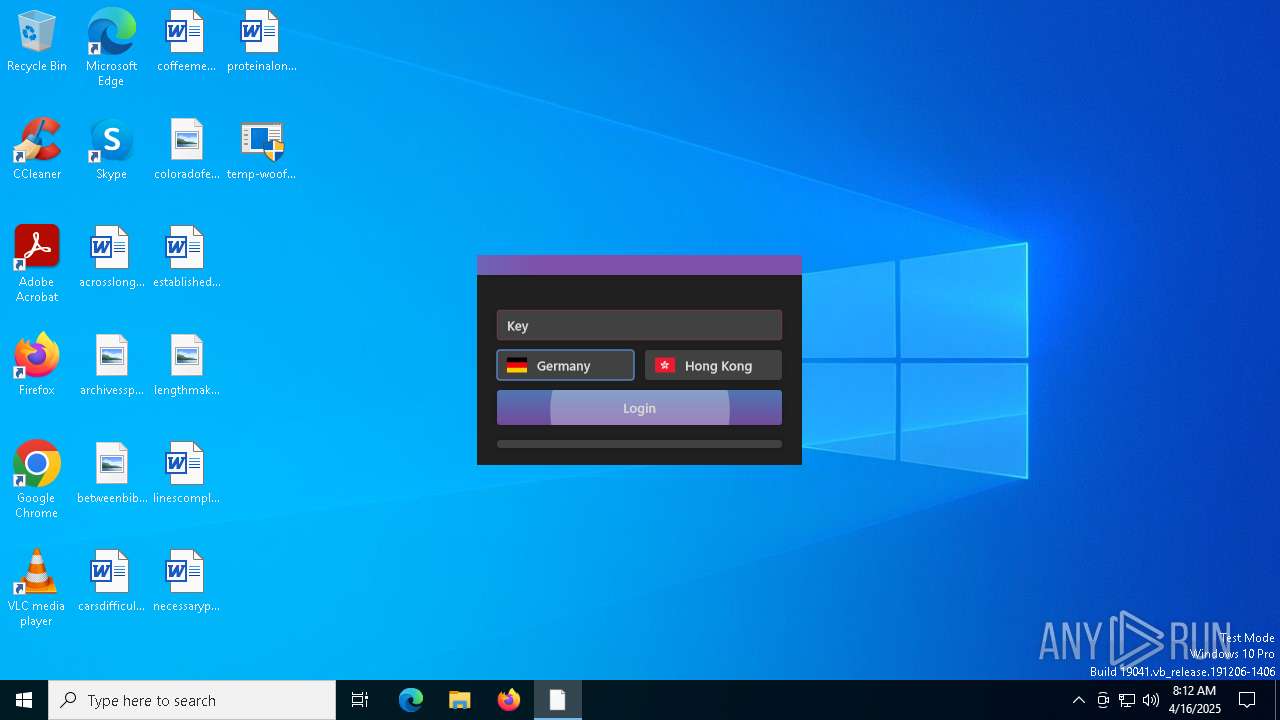
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1272 | c:\windows\resources\spoolsv.exe SE | C:\Windows\Resources\spoolsv.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 1764 | c:\users\admin\desktop\temp-woofer.exe | C:\Users\admin\Desktop\temp-woofer.exe | — | temp-woofer.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1812 | c:\windows\resources\themes\explorer.exe | C:\Windows\Resources\Themes\explorer.exe | icsys.icn.exe | ||||||||||||
User: admin Integrity Level: HIGH Version: 1.00 Modules
| |||||||||||||||
| 3020 | C:\Windows\Resources\Themes\icsys.icn.exe | C:\Windows\Resources\Themes\icsys.icn.exe | temp-woofer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 4892 | "C:\Users\admin\Desktop\temp-woofer.exe" | C:\Users\admin\Desktop\temp-woofer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.00 Modules
| |||||||||||||||
| 5608 | c:\windows\resources\svchost.exe | C:\Windows\Resources\svchost.exe | spoolsv.exe | ||||||||||||
User: admin Integrity Level: HIGH Version: 1.00 Modules
| |||||||||||||||
| 5728 | "C:\Users\admin\Desktop\temp-woofer.exe" | C:\Users\admin\Desktop\temp-woofer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 6240 | c:\windows\resources\spoolsv.exe PR | C:\Windows\Resources\spoolsv.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 6372 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 748
Read events
3 729
Write events
15
Delete events
4
Modification events
| (PID) Process: | (3020) icsys.icn.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (5728) temp-woofer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (1812) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Explorer |
Value: c:\windows\resources\themes\explorer.exe RO | |||
| (PID) Process: | (1812) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Svchost |
Value: c:\windows\resources\svchost.exe RO | |||
| (PID) Process: | (1812) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Explorer |
Value: | |||
| (PID) Process: | (1812) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Svchost |
Value: | |||
| (PID) Process: | (5608) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Explorer |
Value: c:\windows\resources\themes\explorer.exe RO | |||
| (PID) Process: | (5608) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Svchost |
Value: c:\windows\resources\svchost.exe RO | |||
| (PID) Process: | (5608) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Explorer |
Value: | |||
| (PID) Process: | (5608) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Svchost |
Value: | |||
Executable files
5
Suspicious files
5
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1272 | spoolsv.exe | C:\Windows\Resources\svchost.exe | executable | |
MD5:7B68EC5E79397B66DB1FD2A639CA172E | SHA256:D2AC3492122D0D0571E869D4ED0C5B127780C346EB10DE11C72C0BD9FE46DC8B | |||
| 3020 | icsys.icn.exe | C:\Users\admin\AppData\Local\Temp\~DF255B9E3CF30D4FA2.TMP | binary | |
MD5:2FC6372DD6C1C9D15ECC9F107FD4A19E | SHA256:F2ED47B4A56A8FFD8F28DC2C41A3AB9A1065BE4F18E401FAC518460D96041AD0 | |||
| 6240 | spoolsv.exe | C:\Users\admin\AppData\Local\Temp\~DFDD99C50A4BF8F13A.TMP | binary | |
MD5:740B1790C0AF6E2BD5C709CDE8CAFE0F | SHA256:E8C8884CCD29D7D71D82F03D373F76F80D1D726BEF91673D3EEA9ADB93586F07 | |||
| 1764 | temp-woofer.exe | C:\Users\admin\AppData\Local\Temp\71C762C8E0D8F496 | binary | |
MD5:EE3B21C99F4E4985CBA5A916DC48F1EF | SHA256:86ED35F2E6EEFD6796E1B6FABBCC0F75EF4F7DA36AB5ED179E60864147442FDD | |||
| 3020 | icsys.icn.exe | C:\Windows\Resources\Themes\explorer.exe | executable | |
MD5:98BFF804FB8CE29F0992CAD47D7915DF | SHA256:6D39B5F54A6A4272BE0473628303EBE935A473BF2EA3B63C76F129042ABD789F | |||
| 5728 | temp-woofer.exe | C:\Windows\Resources\Themes\icsys.icn.exe | executable | |
MD5:44E7273C35367DFB301D5B09DB5189AD | SHA256:F93002C2FA55085E1FC37519A76E4E011C33AEC1B04D00F79CF195D766BD832C | |||
| 5728 | temp-woofer.exe | C:\Users\admin\Desktop\temp-woofer.exe | executable | |
MD5:DE247ADC0271250CF88EAECC025870E9 | SHA256:31D35A385663B70A2579FC86116C29A30F2606A46F72E16A03B4AE249974E266 | |||
| 1812 | explorer.exe | C:\Windows\Resources\spoolsv.exe | executable | |
MD5:648600D4CFEFD0B9CEBBCD80429E6A1F | SHA256:7E06F96BB30340DF1DFD64CC552101F469560589FA176FEB73D67827ECFB613C | |||
| 1272 | spoolsv.exe | C:\Users\admin\AppData\Local\Temp\~DFD9A0779D8B099025.TMP | binary | |
MD5:24A61EBC654030FF7BEB1C3139E305B2 | SHA256:9FD857BCFAF7D084A133986E79B3883A38BAFDF6F3AEFF521C0A1FDE7B2E7894 | |||
| 5728 | temp-woofer.exe | C:\Users\admin\AppData\Local\Temp\~DF02CCDA5962CED69A.TMP | binary | |
MD5:3E4AF5233CA9C69B69AE6E0050F1875E | SHA256:73E90A7FD632425534FE9DB86AD4E05C8F02B2213A812C7E95842BAB7551C4D6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
43
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.158:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 304 | 4.245.163.56:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
4892 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
4892 | SIHClient.exe | GET | 200 | 23.48.23.188:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
4892 | SIHClient.exe | GET | 200 | 23.48.23.188:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
4892 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
4892 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 20.3.187.198:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
4892 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 4.245.163.56:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.158:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6544 | svchost.exe | 20.190.159.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4892 | SIHClient.exe | 4.245.163.56:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |