| File name: | BWCStartMSI.exe |
| Full analysis: | https://app.any.run/tasks/770ddded-56d5-4c1a-861d-efa1bb0e400e |
| Verdict: | Malicious activity |
| Analysis date: | September 10, 2020, 09:40:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D923E1E19402BE79BE05341FBAE69E33 |
| SHA1: | 7FC190608949C123C282EC22A20941E93E8092DA |
| SHA256: | 073C958D172988108FCB7B13D394C377591A0378BE4E5EE9F6ED91628334C35A |
| SSDEEP: | 196608:rknpY6p4E0qY76jUClvuxRKnMNjJ7EEkfTmEv/SKE8:rkHUPCl2xRKnMb6fiEyKE8 |
MALICIOUS
Application was dropped or rewritten from another process
- BingWallpaperApp.exe (PID: 3944)
- BWCStartMSI.exe (PID: 1676)
- MEDefaultPCReset.exe (PID: 1772)
- MEDefaultPCReset.exe (PID: 560)
Loads dropped or rewritten executable
- rundll32.exe (PID: 1064)
- rundll32.exe (PID: 2872)
- MEDefaultPCReset.exe (PID: 560)
SUSPICIOUS
Executable content was dropped or overwritten
- BWCStartMSI.exe (PID: 2640)
- rundll32.exe (PID: 1064)
- BingWallpaperApp.exe (PID: 3944)
- BWCStartMSI.exe (PID: 1676)
- MEDefaultPCReset.exe (PID: 1772)
Reads Environment values
- BingWallpaperApp.exe (PID: 3944)
- MEDefaultPCReset.exe (PID: 560)
Uses RUNDLL32.EXE to load library
- MsiExec.exe (PID: 4084)
Reads Internet Cache Settings
- rundll32.exe (PID: 1064)
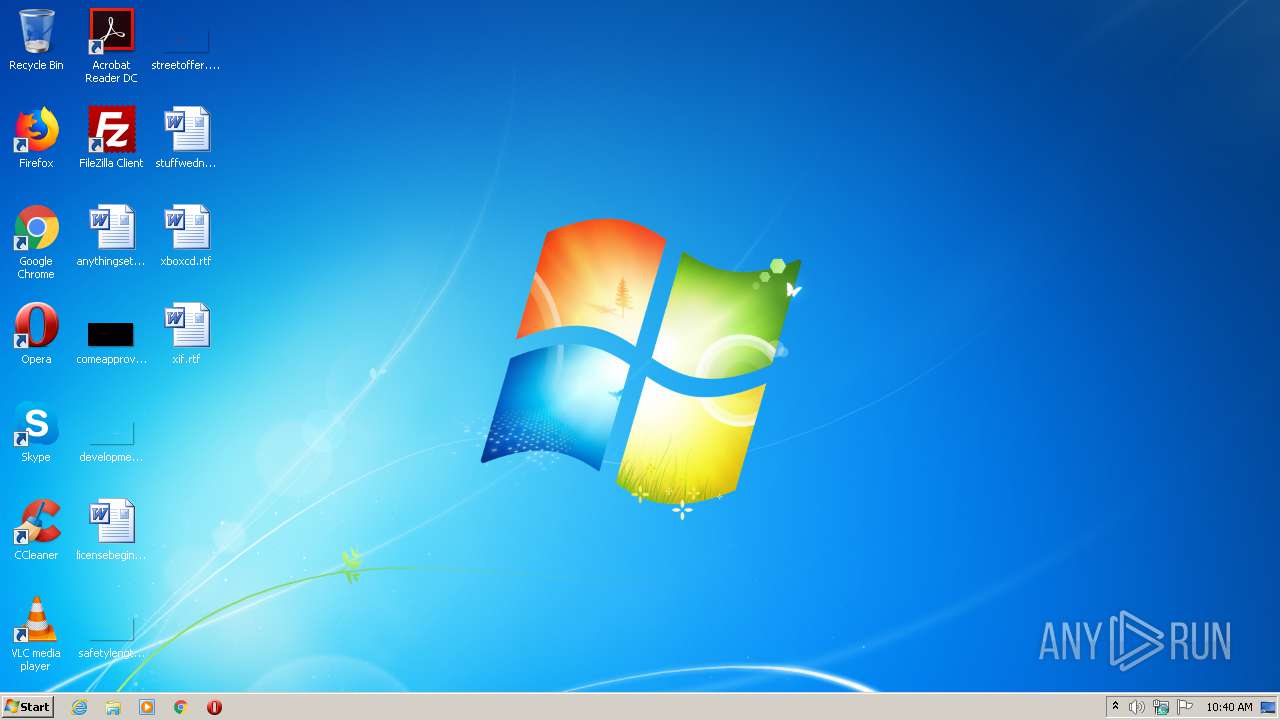
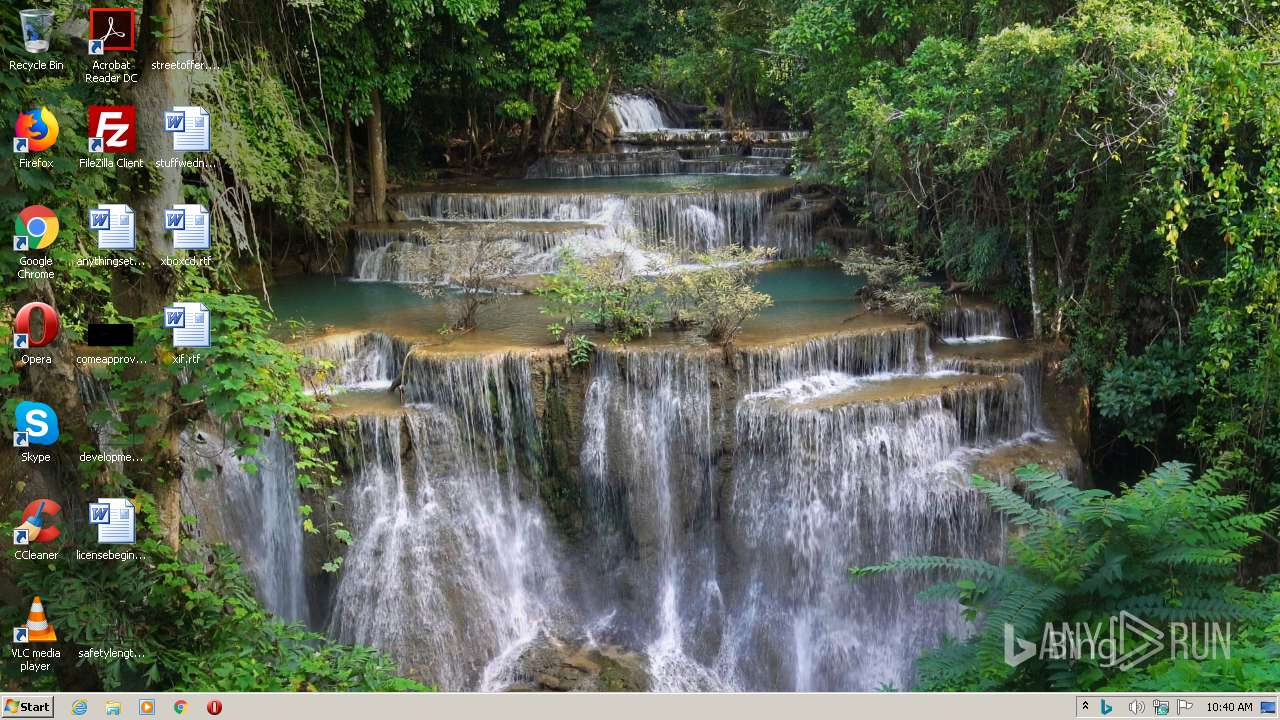
Changes the desktop background image
- BingWallpaperApp.exe (PID: 3944)
INFO
Loads dropped or rewritten executable
- MsiExec.exe (PID: 4084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2068:06:21 08:07:02+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.15 |
| CodeSize: | 25600 |
| InitializedDataSize: | 7340544 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6a00 |
| OSVersion: | 10 |
| ImageVersion: | 10 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.7.6 |
| ProductVersionNumber: | 1.0.7.6 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | BWCStartMSI |
| FileVersion: | 1.0.7.6 |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WEXTRACT.EXE .MUI |
| ProductName: | BWCStartMSI |
| ProductVersion: | 1.0.7.6 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-May-1932 23:38:46 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 11.00.18362.1 (WinBuild.160101.0800) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | WEXTRACT.EXE .MUI |
| ProductName: | Internet Explorer |
| ProductVersion: | 11.00.18362.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-May-1932 23:38:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000062C4 | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.30395 |
.data | 0x00008000 | 0x00001A48 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.97064 |
.idata | 0x0000A000 | 0x00001052 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.0209 |
.rsrc | 0x0000C000 | 0x006FE2A8 | 0x006FE400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99778 |
.reloc | 0x0070B000 | 0x00000888 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.27286 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00338 | 2018 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.15864 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.07737 | 488 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.50949 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.56662 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.94251 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.99361 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 3.37828 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 7.98515 | 55762 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 5.33023 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
Cabinet.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
VERSION.dll |
msvcrt.dll |
Total processes
46
Monitored processes
9
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | C:\Users\admin\AppData\Local\Temp\IXP001.TMP\MEDefaultPCReset.exe | C:\Users\admin\AppData\Local\Temp\IXP001.TMP\MEDefaultPCReset.exe | MEDefaultPCReset.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: MEDefaultPCReset Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1064 | rundll32.exe "C:\Windows\Installer\MSIE430.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_981312 1 CustomActions!CustomActions.CustomActions.InstallPing | C:\Windows\system32\rundll32.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1660 | "C:\Windows\System32\msiexec.exe" /q /i BWCInstaller.msi /norestart | C:\Windows\System32\msiexec.exe | — | BWCStartMSI.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1676 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\BWCStartMSI.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\BWCStartMSI.exe | BWCStartMSI.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: BWCStartMSI Exit code: 0 Version: 1.0.7.6 Modules
| |||||||||||||||
| 1772 | "C:\Users\admin\AppData\Local\Temp\MEDefaultPCReset.exe" | C:\Users\admin\AppData\Local\Temp\MEDefaultPCReset.exe | BWCStartMSI.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MEDefaultPCReset Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2640 | "C:\Users\admin\AppData\Local\Temp\BWCStartMSI.exe" | C:\Users\admin\AppData\Local\Temp\BWCStartMSI.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: BWCStartMSI Exit code: 0 Version: 1.0.7.6 Modules
| |||||||||||||||
| 2872 | rundll32.exe "C:\Windows\Installer\MSI5A5B.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1006156 7 CustomActions!CustomActions.CustomActions.VSRegisterCheck | C:\Windows\system32\rundll32.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3944 | "C:\Users\admin\AppData\Local\Microsoft\BingWallpaperApp\BingWallpaperApp.exe" | C:\Users\admin\AppData\Local\Microsoft\BingWallpaperApp\BingWallpaperApp.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Bing Wallpaper Exit code: 0 Version: 1.0.7.6 Modules
| |||||||||||||||
| 4084 | C:\Windows\system32\MsiExec.exe -Embedding E11CF5BAA003575196A4FC55D020D9E9 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
592
Read events
521
Write events
71
Delete events
0
Modification events
| (PID) Process: | (1676) BWCStartMSI.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1676) BWCStartMSI.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1064) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\BingWallpaperApp |
| Operation: | write | Name: | InstallDate |
Value: 2020-09-10 | |||
| (PID) Process: | (1064) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\BingWallpaperApp |
| Operation: | write | Name: | InstallTime |
Value: 09:40:34:691 | |||
| (PID) Process: | (3944) BingWallpaperApp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BingWallpaperApp_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3944) BingWallpaperApp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BingWallpaperApp_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3944) BingWallpaperApp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BingWallpaperApp_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3944) BingWallpaperApp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BingWallpaperApp_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3944) BingWallpaperApp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BingWallpaperApp_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3944) BingWallpaperApp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BingWallpaperApp_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
10
Suspicious files
3
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2640 | BWCStartMSI.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\BWCInstaller.msi | — | |
MD5:— | SHA256:— | |||
| 2872 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI5A5B.tmp-\CustomActions.dll | — | |
MD5:— | SHA256:— | |||
| 2872 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI5A5B.tmp-\Microsoft.Deployment.WindowsInstaller.dll | — | |
MD5:— | SHA256:— | |||
| 2872 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI5A5B.tmp-\CustomAction.config | — | |
MD5:— | SHA256:— | |||
| 2872 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI5A5B.tmp-\DispatchQueue.dll | — | |
MD5:— | SHA256:— | |||
| 2640 | BWCStartMSI.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\BWCStartMSI.exe | executable | |
MD5:— | SHA256:— | |||
| 1064 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSIE430.tmp-\CustomActions.dll | executable | |
MD5:— | SHA256:— | |||
| 3944 | BingWallpaperApp.exe | C:\Users\admin\AppData\Local\Microsoft\BingWallpaperApp\WPImages\20200909.jpg | image | |
MD5:— | SHA256:— | |||
| 3944 | BingWallpaperApp.exe | C:\Users\admin\AppData\Local\Microsoft\BingWallpaperApp\WPImages\20200908.jpg | image | |
MD5:— | SHA256:— | |||
| 3944 | BingWallpaperApp.exe | C:\Users\admin\AppData\Local\Microsoft\BingWallpaperApp\WPImages\20200907.jpg | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
6
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3944 | BingWallpaperApp.exe | 13.107.21.200:443 | bing.com | Microsoft Corporation | US | whitelisted |
560 | MEDefaultPCReset.exe | 104.108.39.131:443 | go.microsoft.com | Akamai Technologies, Inc. | NL | unknown |
560 | MEDefaultPCReset.exe | 52.173.134.115:443 | bingwallpaper.microsoft.com | Microsoft Corporation | US | unknown |
1064 | rundll32.exe | 20.41.62.11:80 | g.ceipmsn.com | — | US | suspicious |
3944 | BingWallpaperApp.exe | 52.173.134.115:443 | bingwallpaper.microsoft.com | Microsoft Corporation | US | unknown |
3944 | BingWallpaperApp.exe | 204.79.197.200:443 | bing.com | Microsoft Corporation | US | whitelisted |
— | — | 92.123.16.55:443 | go.microsoft.com | Telia Company AB | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bing.com |
| whitelisted |
g.ceipmsn.com |
| suspicious |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
bingwallpaper.microsoft.com |
| whitelisted |