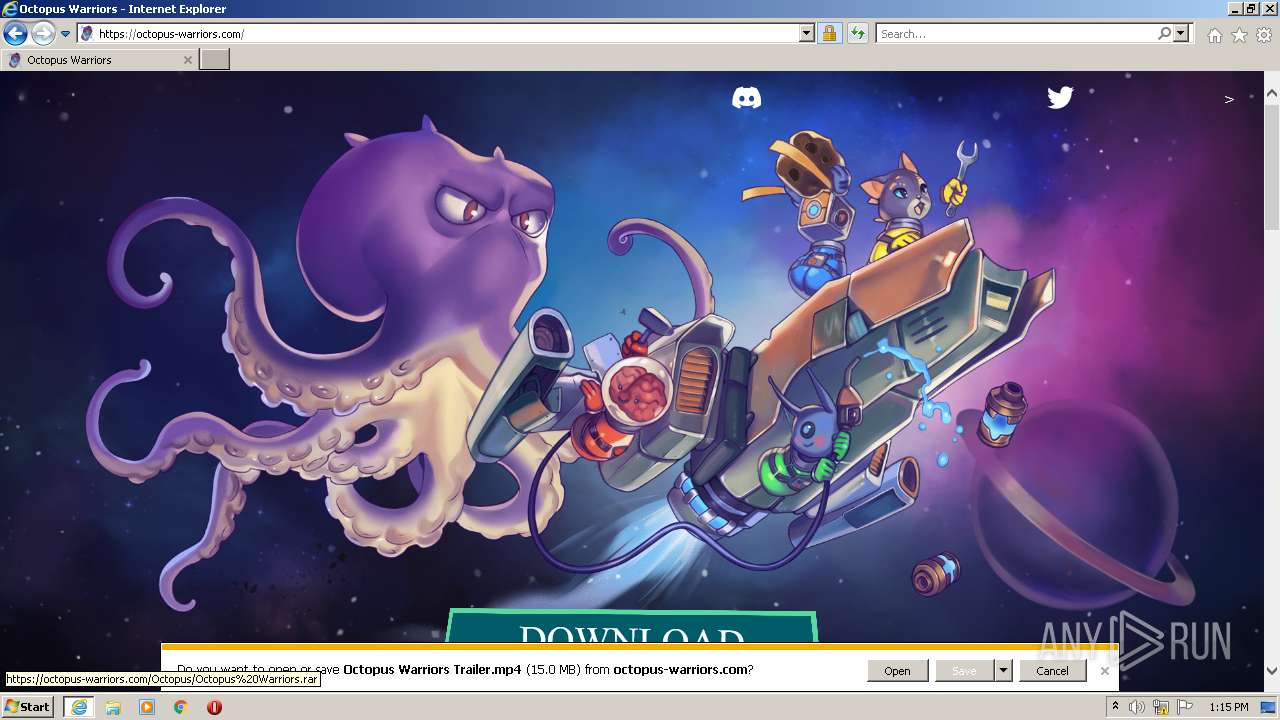
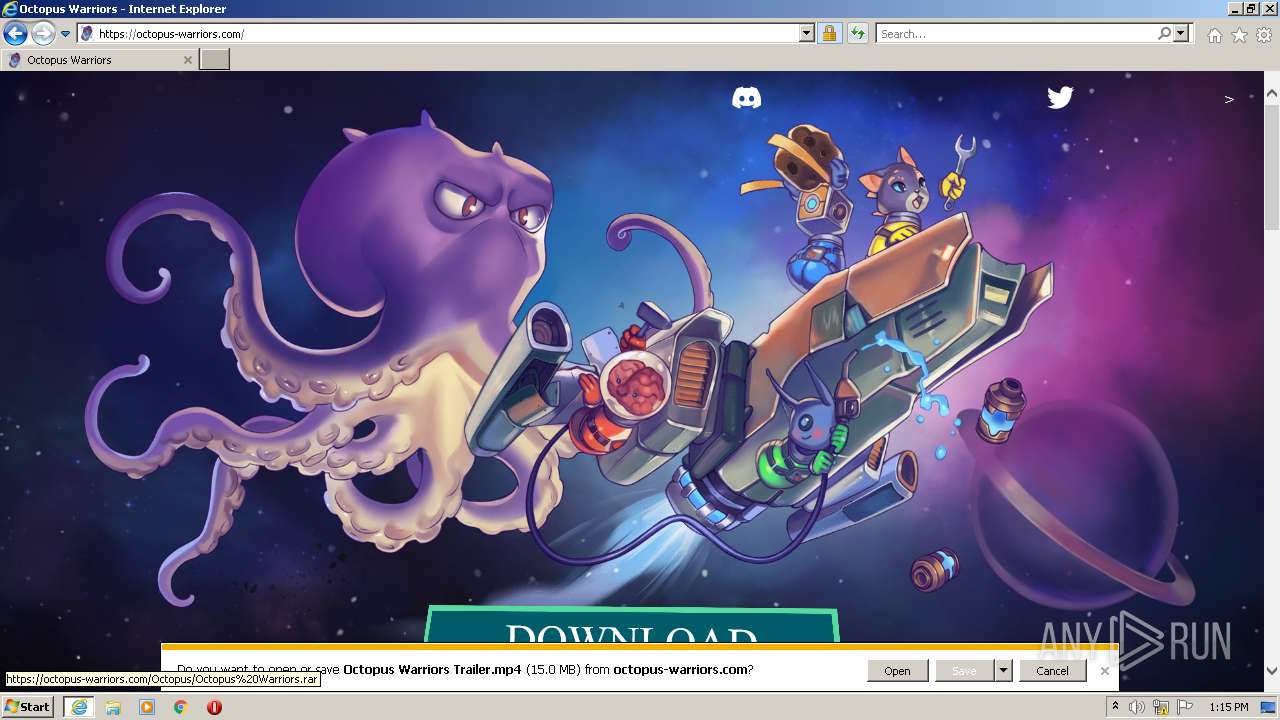
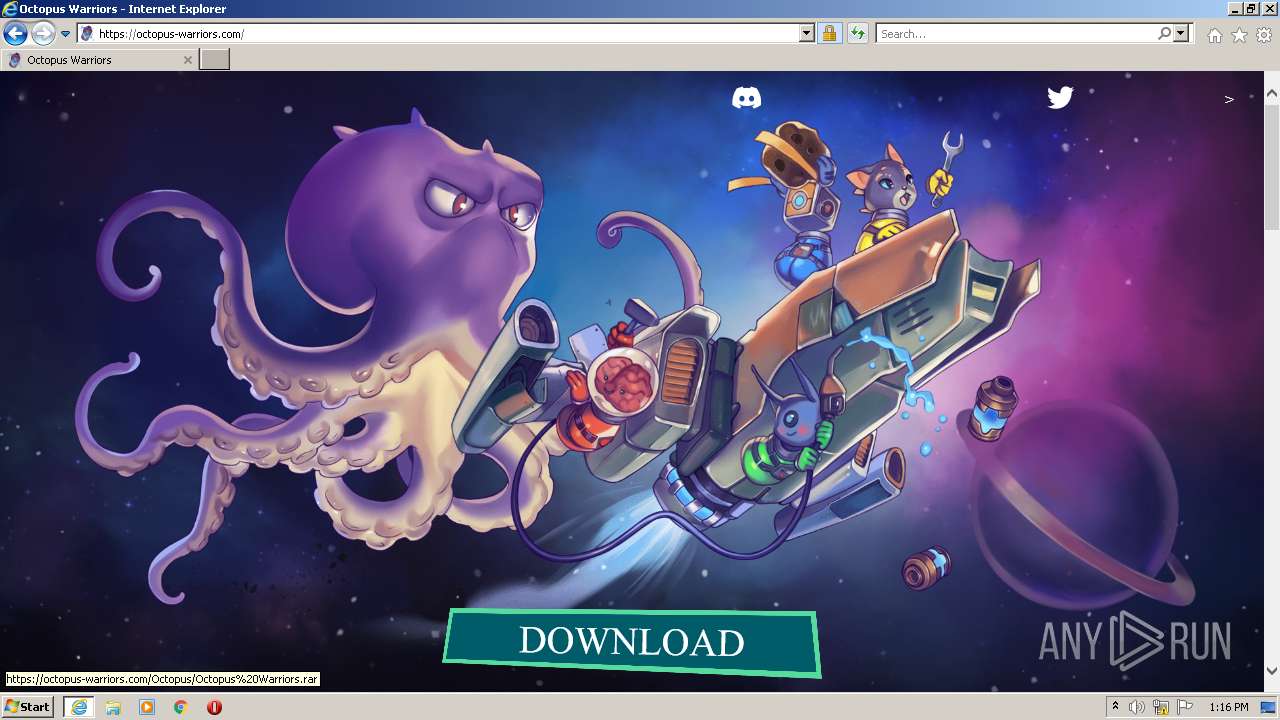
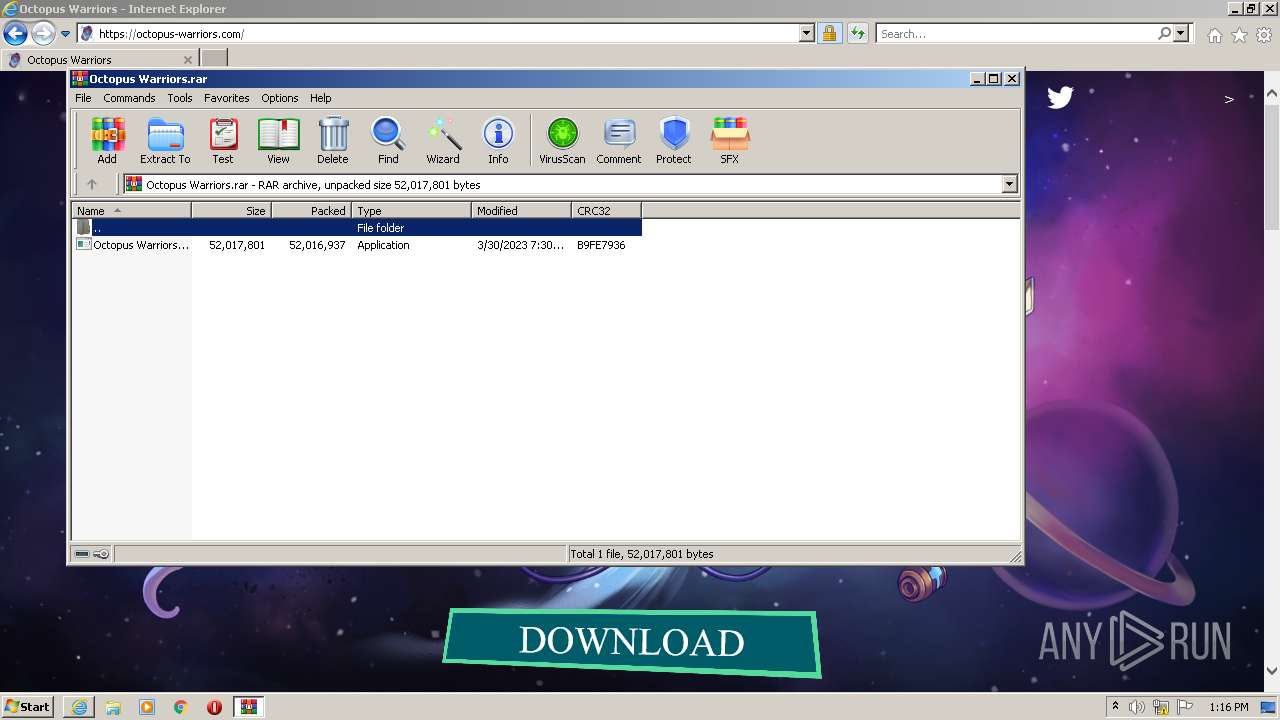
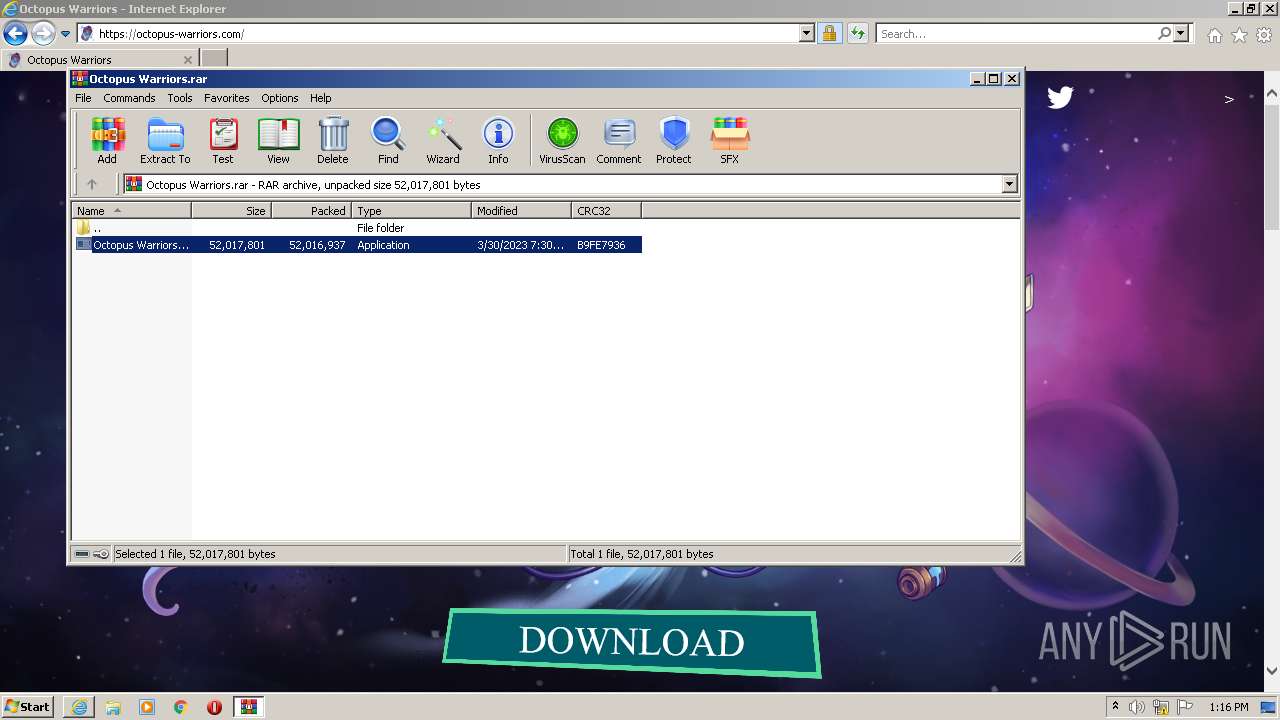
| URL: | https://octopus-warriors.com/Octopus/Octopu%20Warriors.rar |
| Full analysis: | https://app.any.run/tasks/02da5efa-d23f-421d-ac8e-c3434db5769c |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 12:15:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B6607B8CA5741B1A8CBE2B785F7E4BF5 |
| SHA1: | 09D570F2CE87C79F6A0EE0ACFA90DB866B08631B |
| SHA256: | 0735D6C9C537B87BACC7C659B4D26C1F6FCB5F00C23402991299094C8B8AF0CC |
| SSDEEP: | 3:N8PsVU72moqGqYoLXDX:2kVA32qJLzX |
MALICIOUS
Create files in the Startup directory
- asd.exe (PID: 3460)
Actions looks like stealing of personal data
- asd.exe (PID: 3460)
SUSPICIOUS
The process creates files with name similar to system file names
- Octopus Warriors.exe (PID: 2452)
Executable content was dropped or overwritten
- Octopus Warriors.exe (PID: 2452)
- asd.exe (PID: 3460)
Starts CMD.EXE for commands execution
- asd.exe (PID: 3460)
Get information on the list of running processes
- asd.exe (PID: 3460)
- cmd.exe (PID: 3720)
- cmd.exe (PID: 3008)
Reads browser cookies
- asd.exe (PID: 3460)
Application launched itself
- asd.exe (PID: 3460)
Reads the Internet Settings
- asd.exe (PID: 3460)
INFO
Application launched itself
- iexplore.exe (PID: 2680)
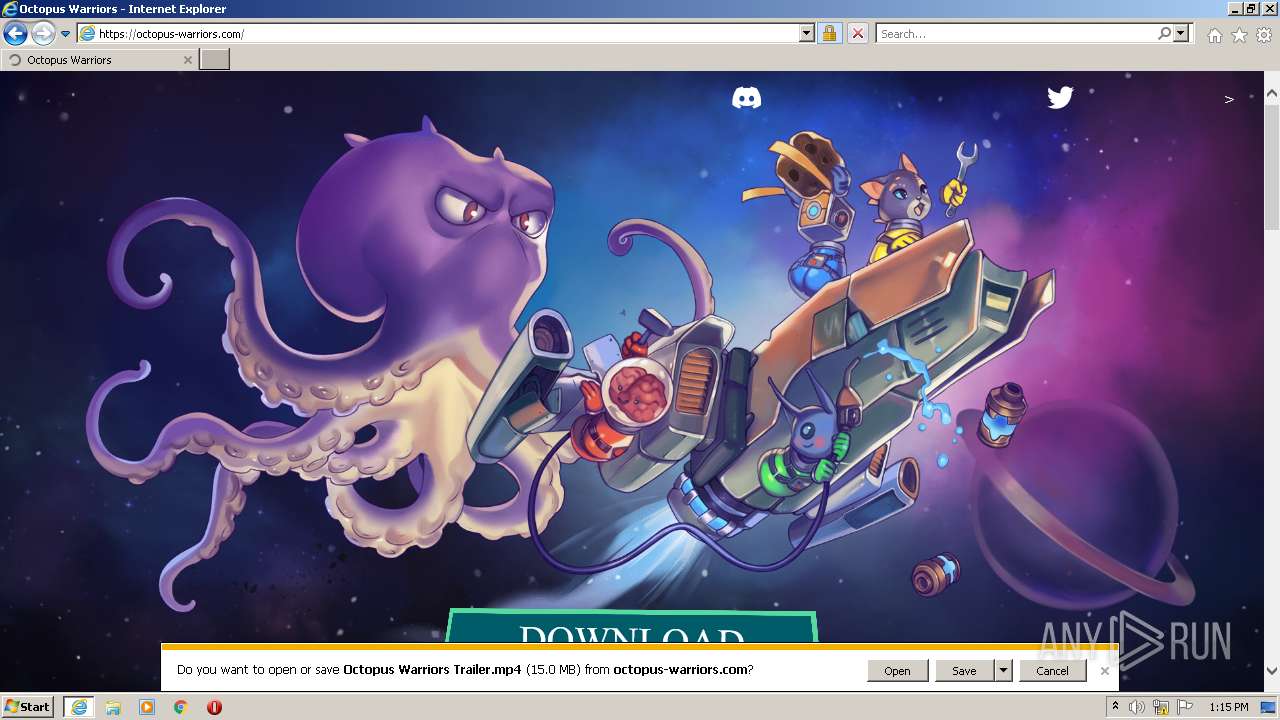
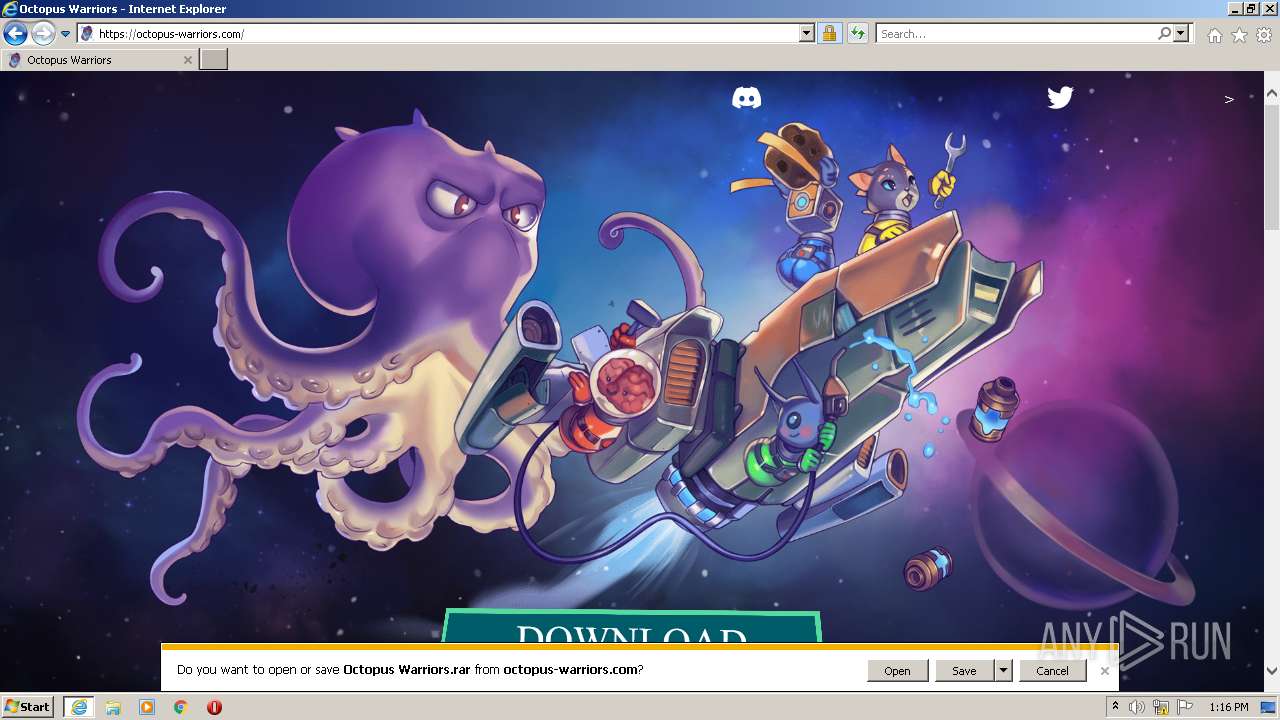
The process uses the downloaded file
- iexplore.exe (PID: 2680)
- WinRAR.exe (PID: 2184)
Checks supported languages
- Octopus Warriors.exe (PID: 2452)
- asd.exe (PID: 3460)
- asd.exe (PID: 584)
- asd.exe (PID: 3476)
- asd.exe (PID: 3756)
- asd.exe (PID: 3964)
The process checks LSA protection
- Octopus Warriors.exe (PID: 2452)
- asd.exe (PID: 3460)
- tasklist.exe (PID: 3916)
- tasklist.exe (PID: 3988)
- asd.exe (PID: 3476)
Reads the computer name
- Octopus Warriors.exe (PID: 2452)
- asd.exe (PID: 3460)
- asd.exe (PID: 584)
- asd.exe (PID: 3476)
- asd.exe (PID: 3964)
- asd.exe (PID: 3756)
Reads the machine GUID from the registry
- Octopus Warriors.exe (PID: 2452)
Loads dropped or rewritten executable
- Octopus Warriors.exe (PID: 2452)
Create files in a temporary directory
- Octopus Warriors.exe (PID: 2452)
- iexplore.exe (PID: 2680)
- iexplore.exe (PID: 3108)
- asd.exe (PID: 3460)
Reads Environment values
- asd.exe (PID: 3460)
Reads product name
- asd.exe (PID: 3460)
Creates files or folders in the user directory
- asd.exe (PID: 3460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
14
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Users\admin\AppData\Local\Temp\2NkFgue9KSxOGMyI9C5R673qS4C\asd.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\xxxxxxxxxxxxxxxx" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1264 --field-trial-handle=1304,i,1439662707607632482,12464468141262450227,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Users\admin\AppData\Local\Temp\2NkFgue9KSxOGMyI9C5R673qS4C\asd.exe | — | asd.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: LOW Description: asd Exit code: 0 Version: 6.7.8 Modules
| |||||||||||||||
| 1240 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2680 CREDAT:3740956 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2184 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Octopus Warriors.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2452 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2184.38592\Octopus Warriors.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2184.38592\Octopus Warriors.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: xxxxxxxxxxxxxxxx Exit code: 0 Version: 6.7.8 Modules
| |||||||||||||||
| 2680 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://octopus-warriors.com/Octopus/Octopu%20Warriors.rar" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3008 | C:\Windows\system32\cmd.exe /d /s /c "tasklist" | C:\Windows\System32\cmd.exe | — | asd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3108 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2680 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3460 | C:\Users\admin\AppData\Local\Temp\2NkFgue9KSxOGMyI9C5R673qS4C\asd.exe | C:\Users\admin\AppData\Local\Temp\2NkFgue9KSxOGMyI9C5R673qS4C\asd.exe | Octopus Warriors.exe | ||||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: asd Exit code: 0 Version: 6.7.8 Modules
| |||||||||||||||
| 3476 | "C:\Users\admin\AppData\Local\Temp\2NkFgue9KSxOGMyI9C5R673qS4C\asd.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\xxxxxxxxxxxxxxxx" --mojo-platform-channel-handle=1660 --field-trial-handle=1304,i,1439662707607632482,12464468141262450227,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:8 | C:\Users\admin\AppData\Local\Temp\2NkFgue9KSxOGMyI9C5R673qS4C\asd.exe | — | asd.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: asd Exit code: 0 Version: 6.7.8 Modules
| |||||||||||||||
| 3720 | C:\Windows\system32\cmd.exe /d /s /c "tasklist" | C:\Windows\System32\cmd.exe | — | asd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
55 894
Read events
55 562
Write events
324
Delete events
8
Modification events
| (PID) Process: | (2680) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2680) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2680) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2680) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2680) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2680) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2680) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2680) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2680) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2680) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
38
Suspicious files
64
Text files
94
Unknown types
58
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\139F586CA85A10A919364D5E2BD05E8C | binary | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:E71C8443AE0BC2E282C73FAEAD0A6DD3 | SHA256:95B0A5ACC5BF70D3ABDFD091D0C9F9063AA4FDE65BD34DBF16786082E1992E72 | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\139F586CA85A10A919364D5E2BD05E8C | der | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E87CE99F124623F95572A696C80EFCAF_AA1ADD4071D073F3048022453A5FE061 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
59
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3108 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGuOw5S%2FgZeuCs2W38ctSDs%3D | US | der | 471 b | whitelisted |
3108 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCXh%2B17FzWzVgrisikgAGpW | US | der | 472 b | whitelisted |
3108 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | US | der | 471 b | whitelisted |
3108 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrHR6YzPN2BNbByL0VoiTIBBMAOAQUCrwIKReMpTlteg7OM8cus%2B37w3oCEAJaYQ9Y64TxrVOuA9yphHo%3D | US | der | 313 b | whitelisted |
3108 | iexplore.exe | GET | 200 | 2.16.186.10:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgTLSuUUQ8fd3yCUGgDtkbLFSg%3D%3D | unknown | der | 503 b | shared |
3108 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2680 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2680 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2680 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
3108 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCXh%2B17FzWzVgrisikgAGpW | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3108 | iexplore.exe | 8.238.191.126:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
3108 | iexplore.exe | 35.246.229.114:443 | — | GOOGLE-CLOUD-PLATFORM | DE | malicious |
3108 | iexplore.exe | 2.16.186.10:80 | r3.o.lencr.org | Akamai International B.V. | DE | whitelisted |
3108 | iexplore.exe | 23.37.41.57:80 | x1.c.lencr.org | AKAMAI-AS | DE | suspicious |
3108 | iexplore.exe | 142.250.185.138:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
3108 | iexplore.exe | 142.250.185.195:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
2680 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3108 | iexplore.exe | 142.250.186.67:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
— | — | 35.246.229.114:443 | — | GOOGLE-CLOUD-PLATFORM | DE | malicious |
— | — | 142.250.185.100:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
fonts.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.google.com |
| malicious |