| File name: | autoD.exe |
| Full analysis: | https://app.any.run/tasks/beaf664c-d403-40c5-9690-04d966f46a0b |
| Verdict: | Malicious activity |
| Analysis date: | April 17, 2025, 10:46:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, 9 sections |
| MD5: | 1F074C6FEDA36DBAC2F46120144DE943 |
| SHA1: | 4173EAA197CAA3A246B99A0467018D9AEC3A501E |
| SHA256: | 073468D13772C8D66161108EB00069BDF0606610608C904798FBFEE478BCAAD1 |
| SSDEEP: | 12288:Lb5ZUGDCfwbxtWmW3HCGWENGoZux9xTIJej9a3M28+OOwuKX+0lICYqyoxWwRq:/5Z/DCfwbxtjK+1j9r+OOwE0lIkXI |
MALICIOUS
Changes settings for real-time protection
- powershell.exe (PID: 7684)
Disables Windows Defender
- reg.exe (PID: 7512)
Changes Windows Defender settings
- cmd.exe (PID: 7668)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7668)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 7668)
Starts CMD.EXE for commands execution
- autoD.exe (PID: 7604)
- cmd.exe (PID: 7788)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2284)
- cmd.exe (PID: 7568)
- cmd.exe (PID: 6436)
- cmd.exe (PID: 6808)
- cmd.exe (PID: 2568)
- cmd.exe (PID: 3272)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 5380)
- cmd.exe (PID: 1532)
- cmd.exe (PID: 7448)
Found strings related to reading or modifying Windows Defender settings
- autoD.exe (PID: 7604)
Application launched itself
- cmd.exe (PID: 7788)
Windows service management via SC.EXE
- sc.exe (PID: 7148)
Stops a currently running service
- sc.exe (PID: 1912)
INFO
Checks supported languages
- autoD.exe (PID: 7604)
- tar.exe (PID: 7084)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7684)
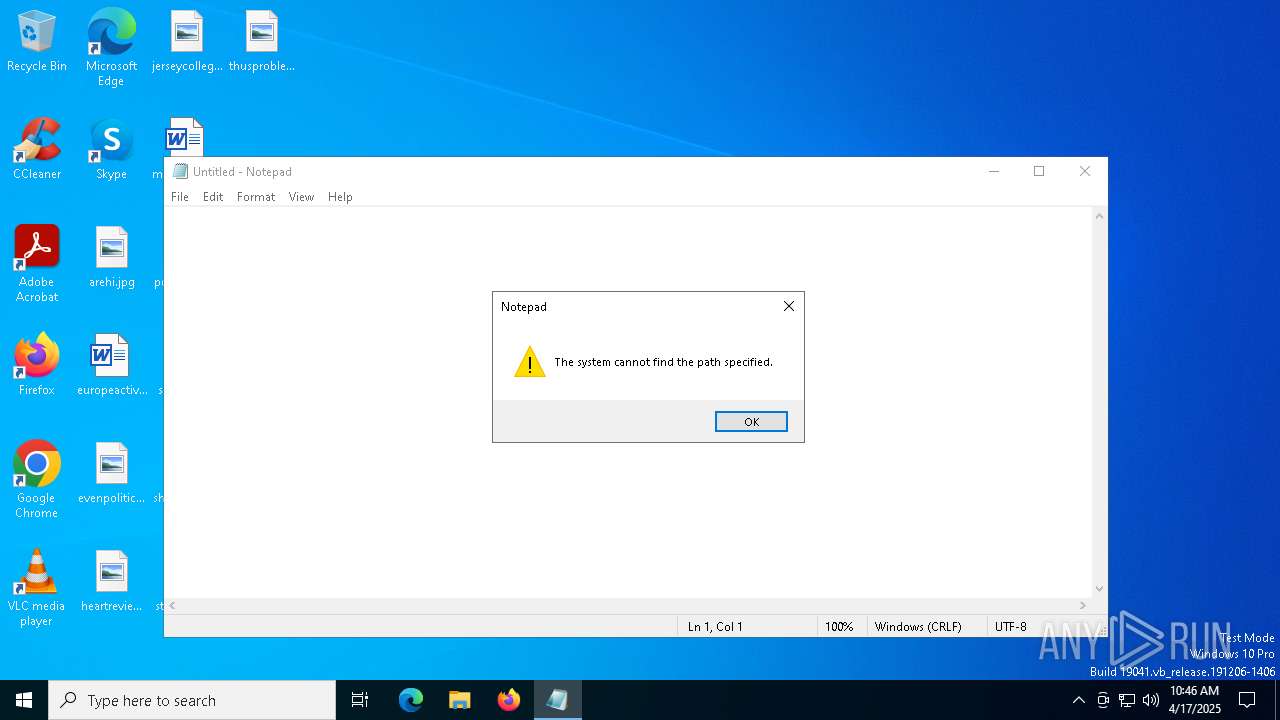
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:03:12 15:53:08+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 733184 |
| InitializedDataSize: | 173056 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5715e |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
176
Monitored processes
47
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1184 | REG ADD "HKLM\SOFTWARE\Policies\Microsoft\Windows Defender\Spynet" /v LocalSettingOverrideSpynetReporting /t REG_DWORD /d 0 /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1452 | REG ADD "HKLM\SOFTWARE\Policies\Microsoft\Windows Defender\Spynet" /v SubmitSamplesConsent /t REG_DWORD /d 2 /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | C:\WINDOWS\system32\cmd.exe /c REG ADD HKLM\SYSTEM\CurrentControlSet\Services\WinDefend /v Start /t REG_DWORD /d 4 /f | C:\Windows\SysWOW64\cmd.exe | — | autoD.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1912 | sc stop WinDefend | C:\Windows\SysWOW64\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 5 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2108 | REG ADD "HKLM\SOFTWARE\Policies\Microsoft\Windows Defender\Spynet" /v DisableBlockAtFirstSeen /t REG_DWORD /d 1 /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2284 | C:\WINDOWS\system32\cmd.exe /c REG ADD "HKLM\SOFTWARE\Policies\Microsoft\Windows Defender" /v DisableAntiSpyware /t REG_DWORD /d 1 /f | C:\Windows\SysWOW64\cmd.exe | — | autoD.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2568 | C:\WINDOWS\system32\cmd.exe /c REG ADD "HKLM\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time" /v DisableRealtimeMonitoring /t REG_DWORD /d 1 /f | C:\Windows\SysWOW64\cmd.exe | — | autoD.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2904 | C:\WINDOWS\system32\cmd.exe /c tar -xvzf game2.zip -C %cd% | C:\Windows\SysWOW64\cmd.exe | — | autoD.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3272 | C:\WINDOWS\system32\cmd.exe /c REG ADD "HKLM\SOFTWARE\Policies\Microsoft\Windows Defender\Spynet" /v LocalSettingOverrideSpynetReporting /t REG_DWORD /d 0 /f | C:\Windows\SysWOW64\cmd.exe | — | autoD.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4424 | C:\WINDOWS\system32\cmd.exe /c sc config WinDefend start= disabled | C:\Windows\SysWOW64\cmd.exe | — | autoD.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 5 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 914
Read events
5 905
Write events
9
Delete events
0
Modification events
| (PID) Process: | (7512) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (7600) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | AllowFastServiceStartup |
Value: 0 | |||
| (PID) Process: | (4784) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time |
| Operation: | write | Name: | DisableIOAVProtection |
Value: 1 | |||
| (PID) Process: | (1184) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Spynet |
| Operation: | write | Name: | LocalSettingOverrideSpynetReporting |
Value: 0 | |||
| (PID) Process: | (1452) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Spynet |
| Operation: | write | Name: | SubmitSamplesConsent |
Value: 2 | |||
| (PID) Process: | (5072) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\System |
| Operation: | write | Name: | EnableSmartScreen |
Value: 0 | |||
| (PID) Process: | (7216) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | ServiceKeepAlive |
Value: 0 | |||
| (PID) Process: | (4488) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time |
| Operation: | write | Name: | DisableRealtimeMonitoring |
Value: 1 | |||
| (PID) Process: | (2108) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Spynet |
| Operation: | write | Name: | DisableBlockAtFirstSeen |
Value: 1 | |||
Executable files
0
Suspicious files
1
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7684 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_claaatcu.1im.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7684 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jd1hul05.zjj.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7684 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:284F833FF3198733B308852F6FB6E13E | SHA256:9E032A0832495637CE9D3434F71309955CDB3E4D08D81E290A1BDA312B91E2B0 | |||
| 7684 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_eg10pgy3.oqq.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7684 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_eyx5wx3s.i5m.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
17
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6476 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6476 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6476 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6476 | SIHClient.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |