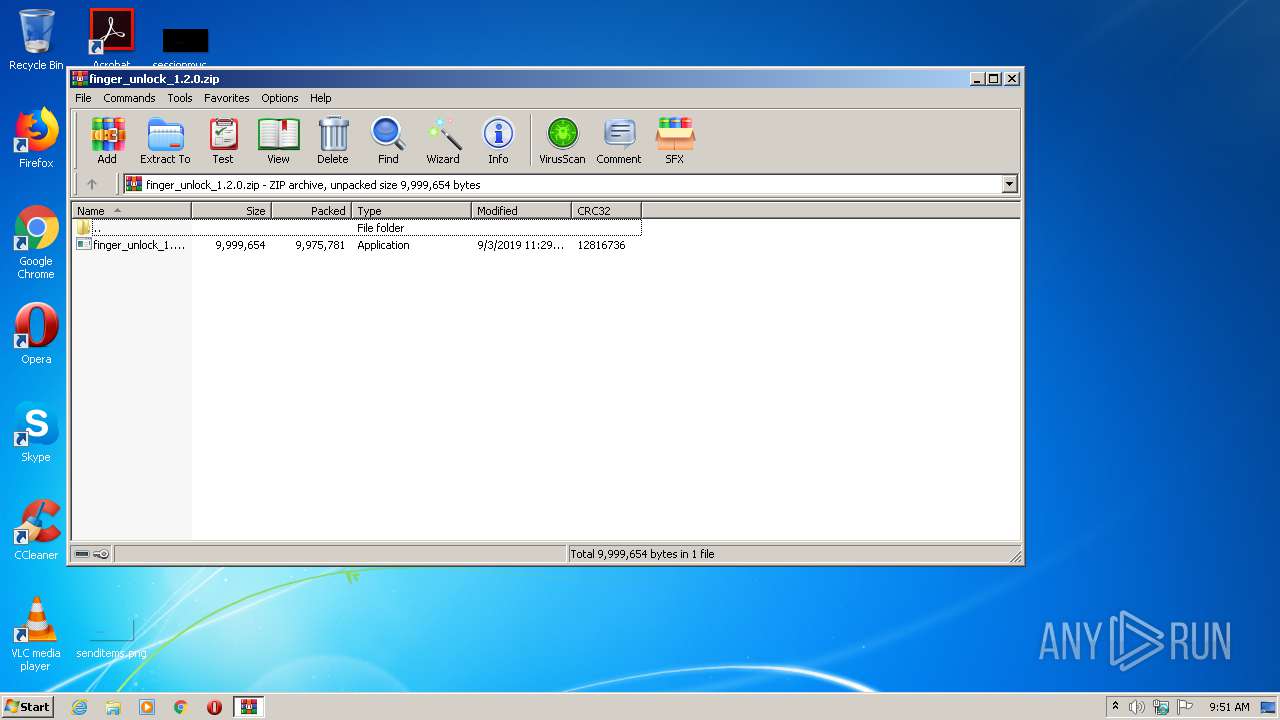
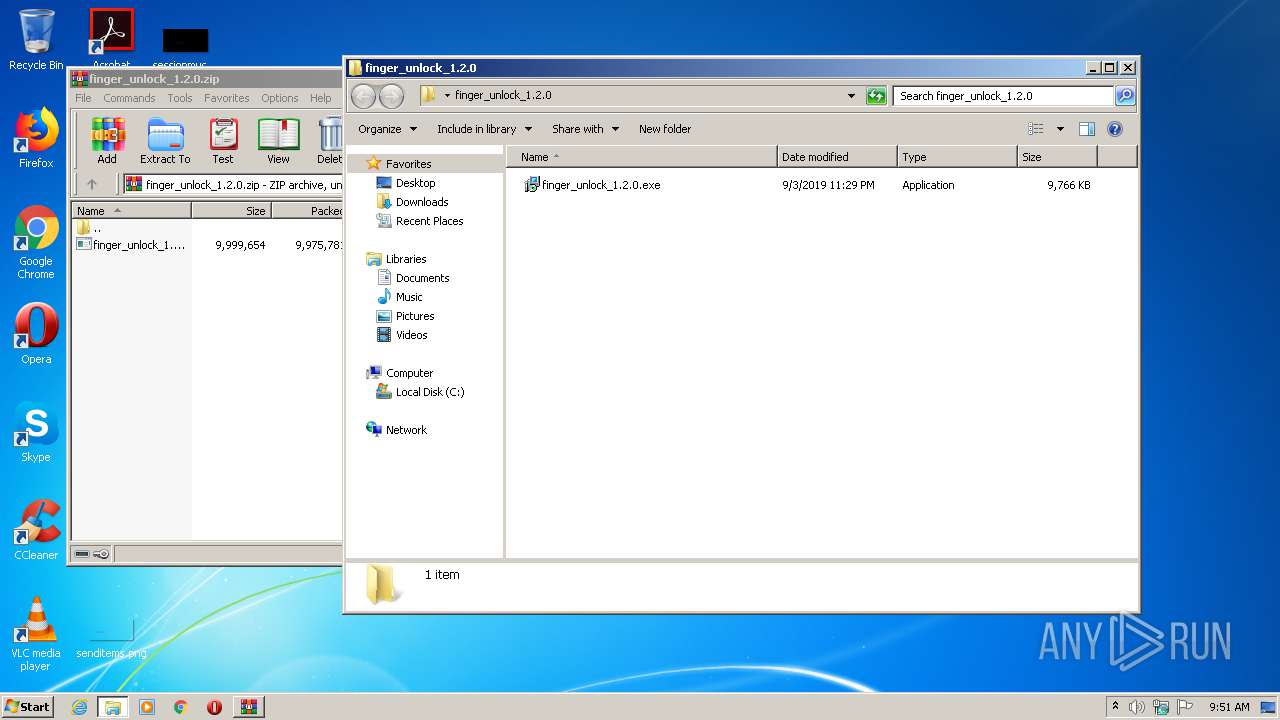
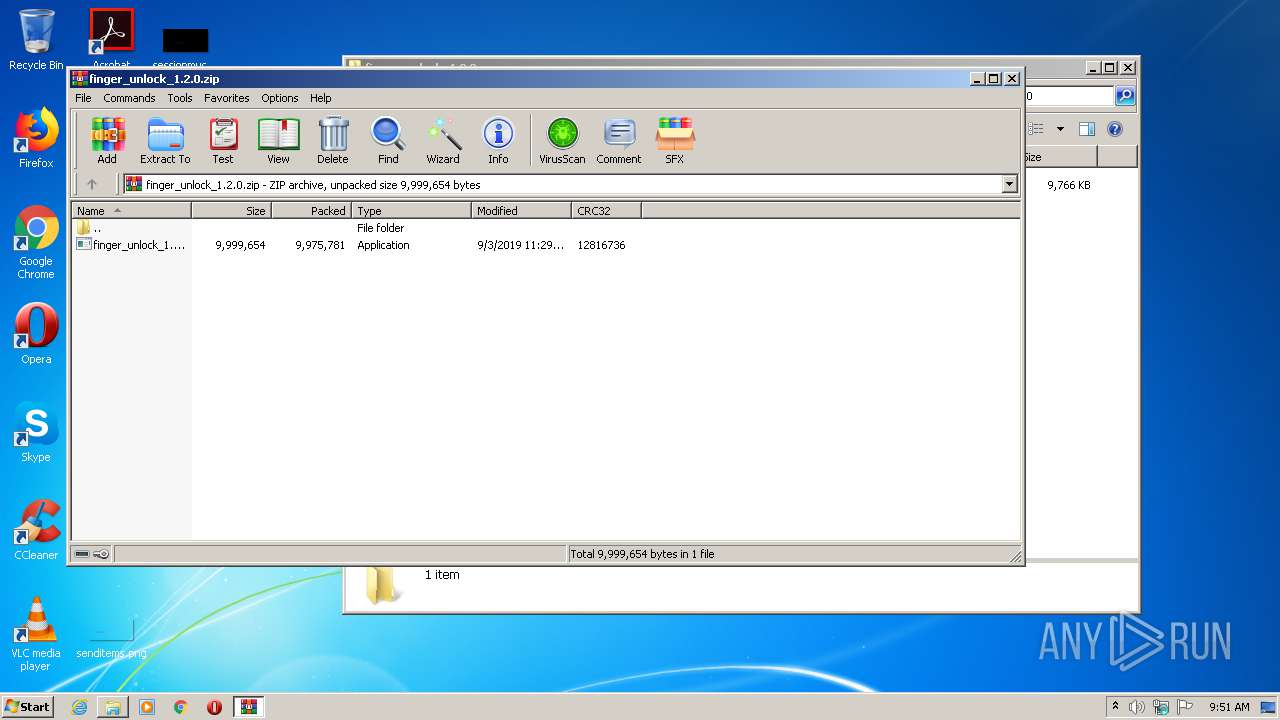
| File name: | finger_unlock_1.2.0.zip |
| Full analysis: | https://app.any.run/tasks/27228284-8dfb-43f4-9742-0ac9abb6c6c7 |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 08:51:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 660BBE3ADE9959B0C5BC342D3008BC50 |
| SHA1: | 5BC29EE616CD43564C2ED229E0B9B124F989A689 |
| SHA256: | 072F554BCE6E6E3C7DBEA7B43FE6712A3C83F5A059B10ECD01AFD0E4A3292500 |
| SSDEEP: | 196608:k97ISbz00q8CEPqjzMLPkssog8XHqFnhrPNwMOqK1rzzTkOeY5WrlDqUkUwJ:k9U8z0j8CWlLPksnHqFnhrPNfRor/VDT |
MALICIOUS
Application was dropped or rewritten from another process
- finger_unlock_1.2.0.exe (PID: 1500)
- finger_unlock_1.2.0.exe (PID: 2352)
SUSPICIOUS
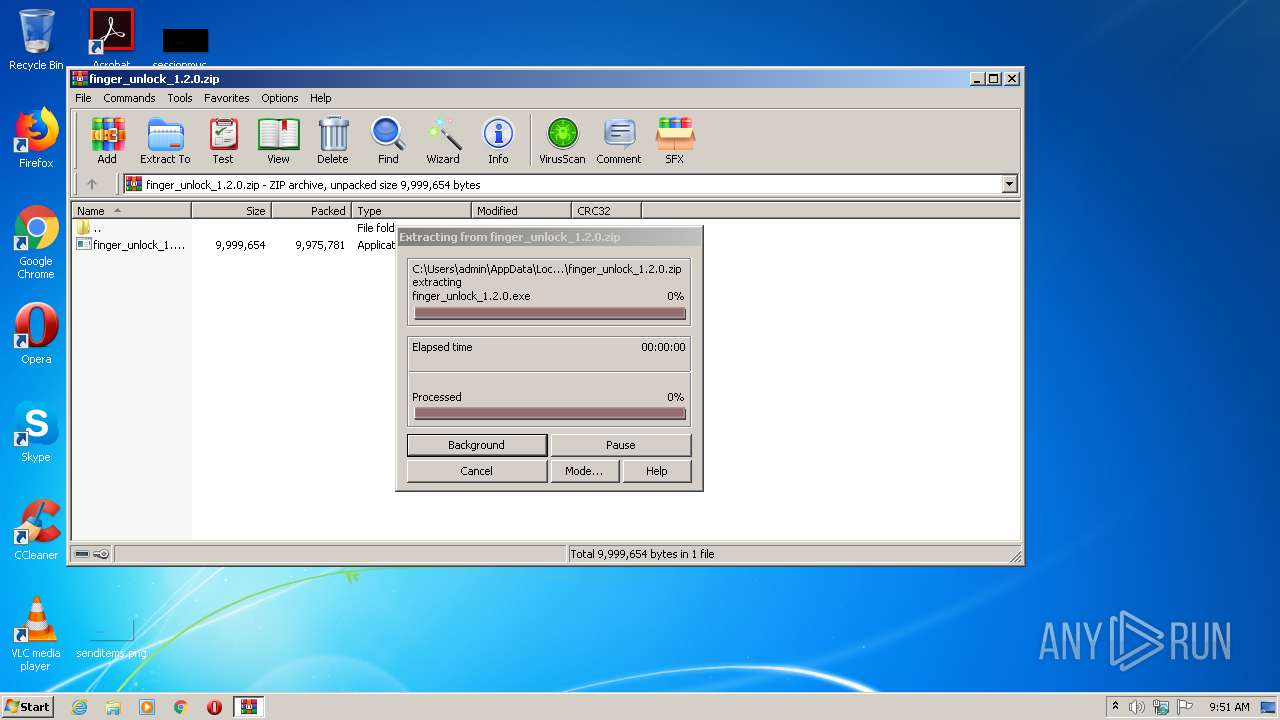
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3244)
- finger_unlock_1.2.0.exe (PID: 1500)
- finger_unlock_1.2.0.exe (PID: 2352)
- finger_unlock_1.2.0.tmp (PID: 2148)
Creates files in the Windows directory
- finger_unlock_1.2.0.tmp (PID: 2148)
- wusa.exe (PID: 3152)
Executes scripts
- finger_unlock_1.2.0.tmp (PID: 2148)
Creates COM task schedule object
- finger_unlock_1.2.0.tmp (PID: 2148)
INFO
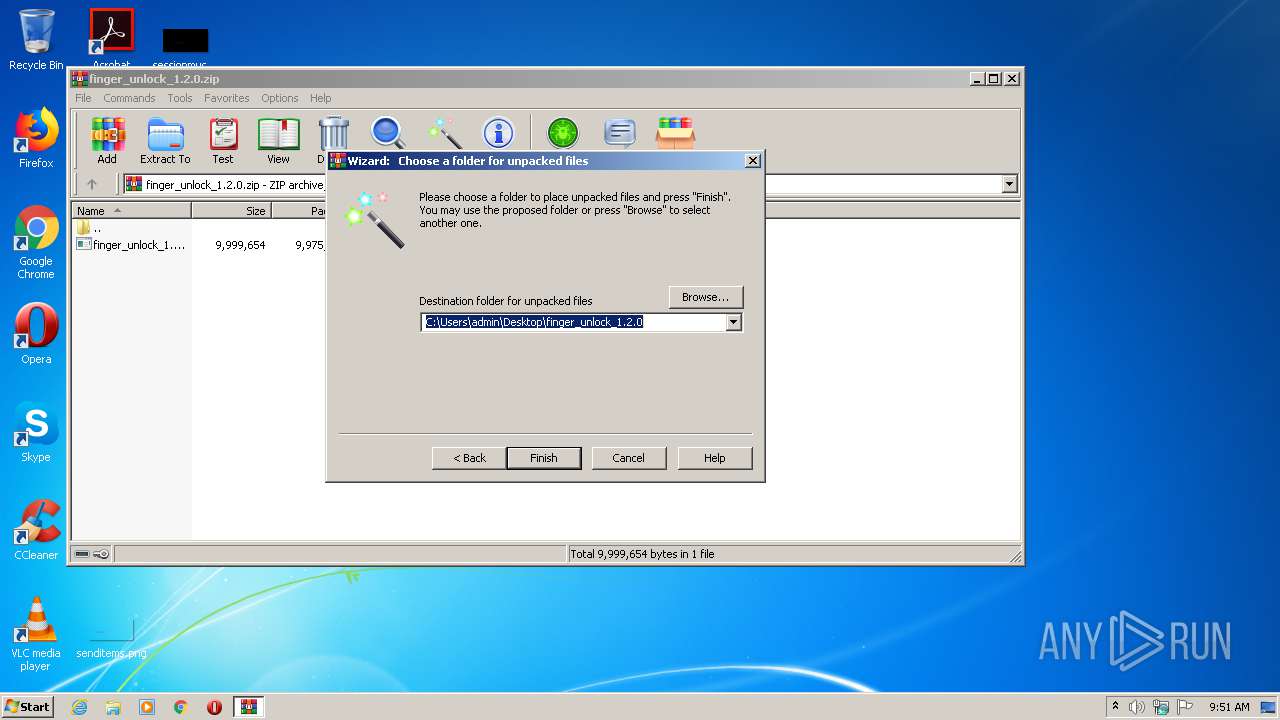
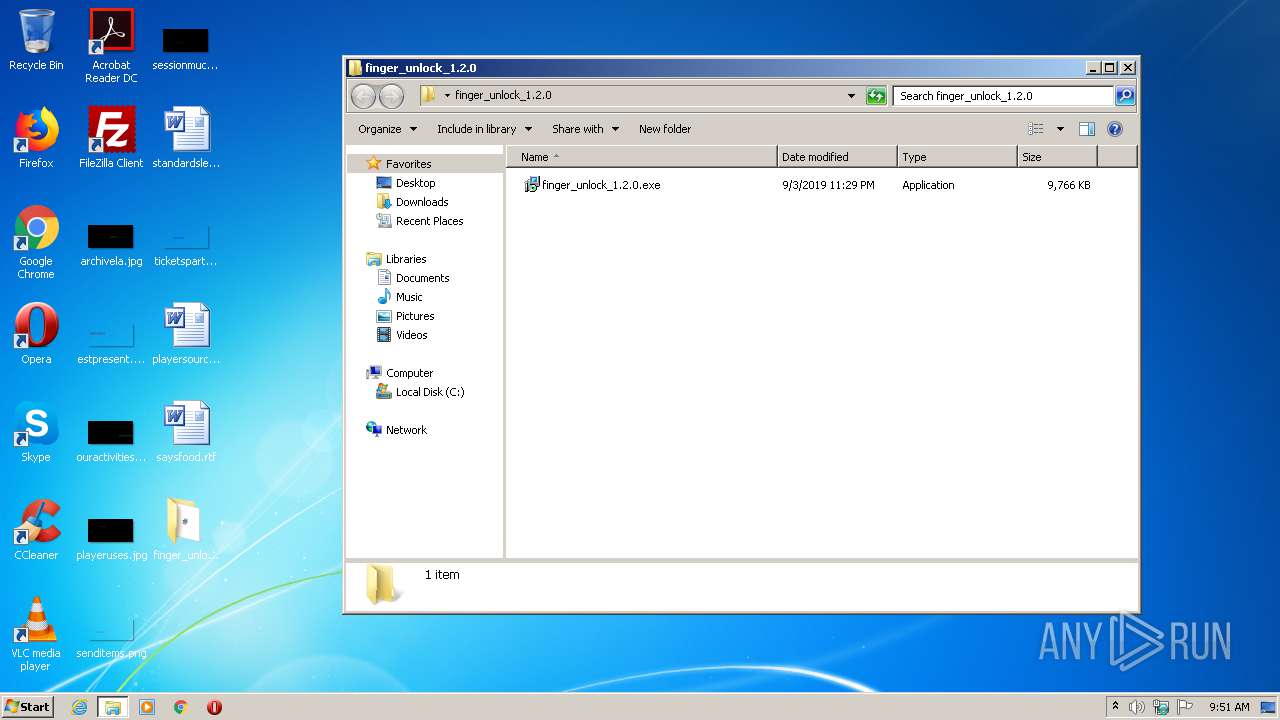
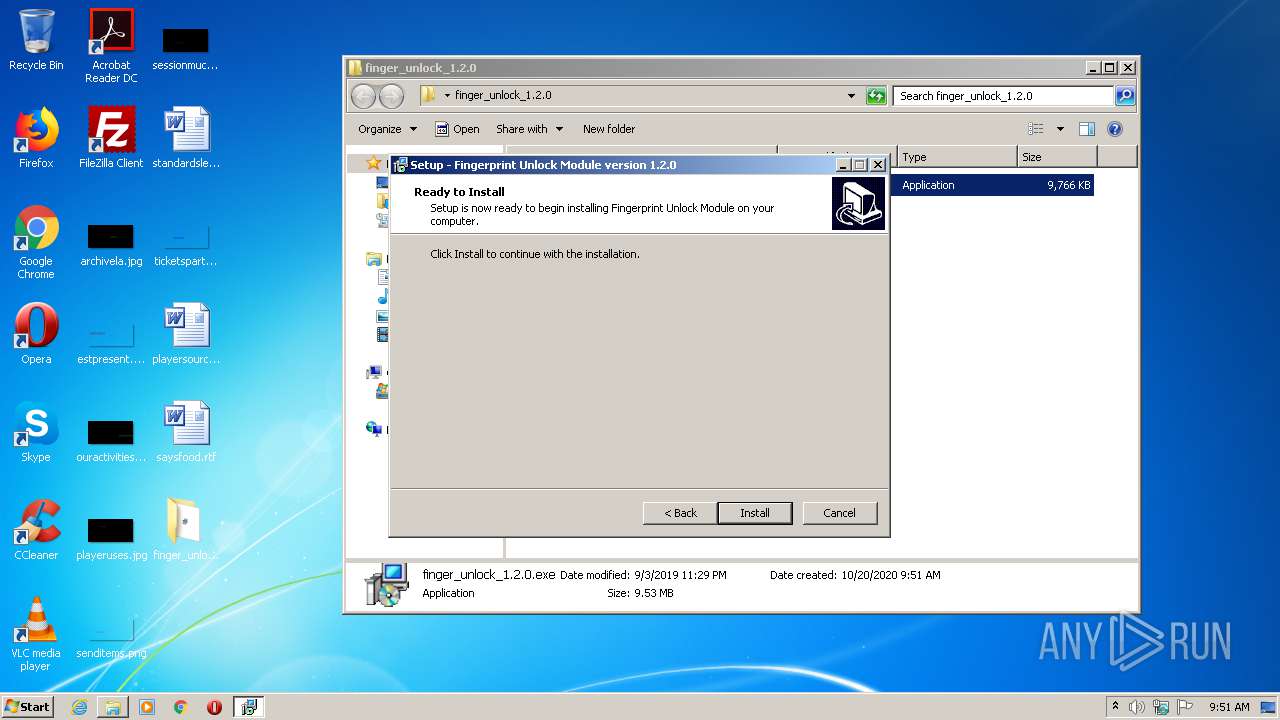
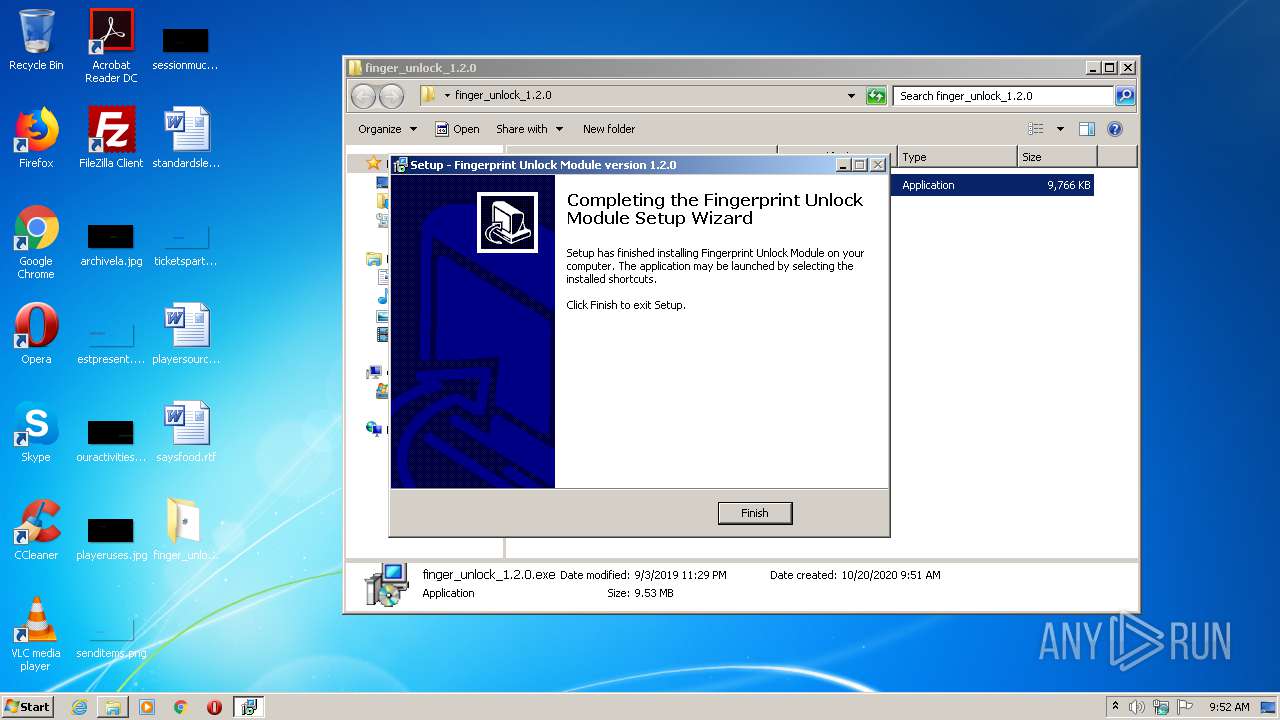
Manual execution by user
- finger_unlock_1.2.0.exe (PID: 1500)
Application was dropped or rewritten from another process
- finger_unlock_1.2.0.tmp (PID: 3276)
- finger_unlock_1.2.0.tmp (PID: 2148)
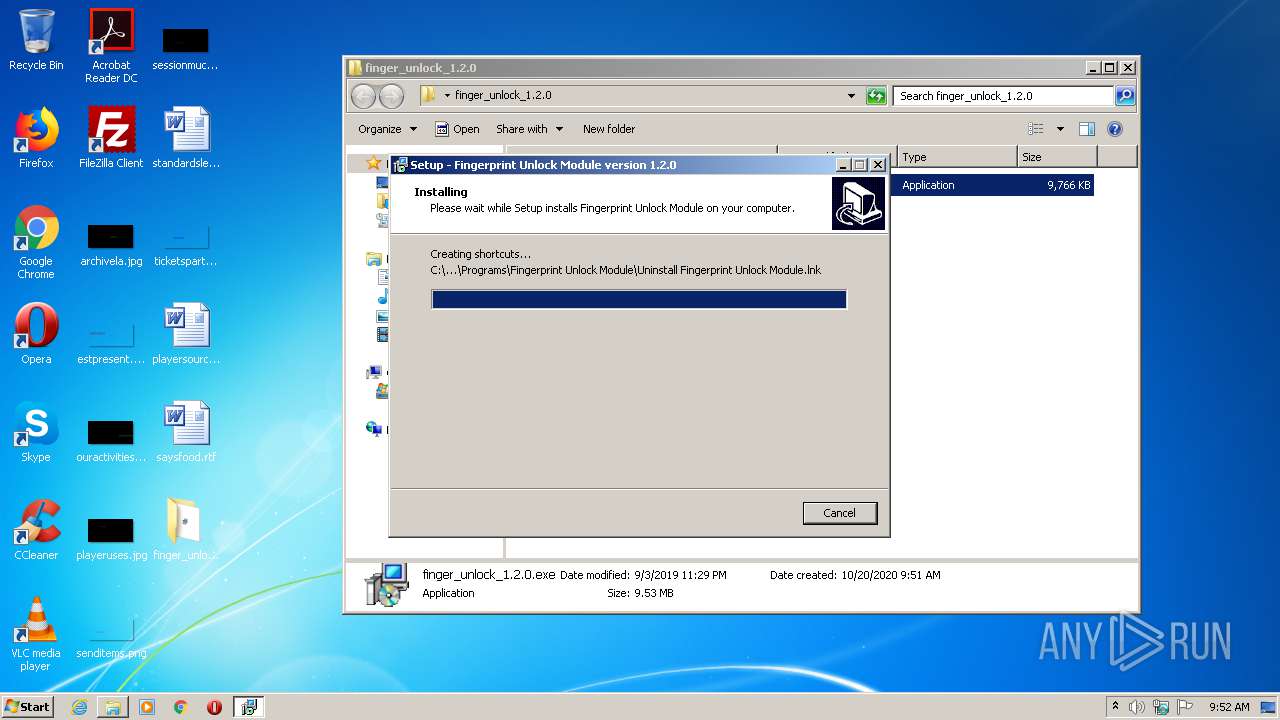
Creates files in the program directory
- finger_unlock_1.2.0.tmp (PID: 2148)
Creates a software uninstall entry
- finger_unlock_1.2.0.tmp (PID: 2148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:09:04 01:29:24 |
| ZipCRC: | 0x12816736 |
| ZipCompressedSize: | 9975781 |
| ZipUncompressedSize: | 9999654 |
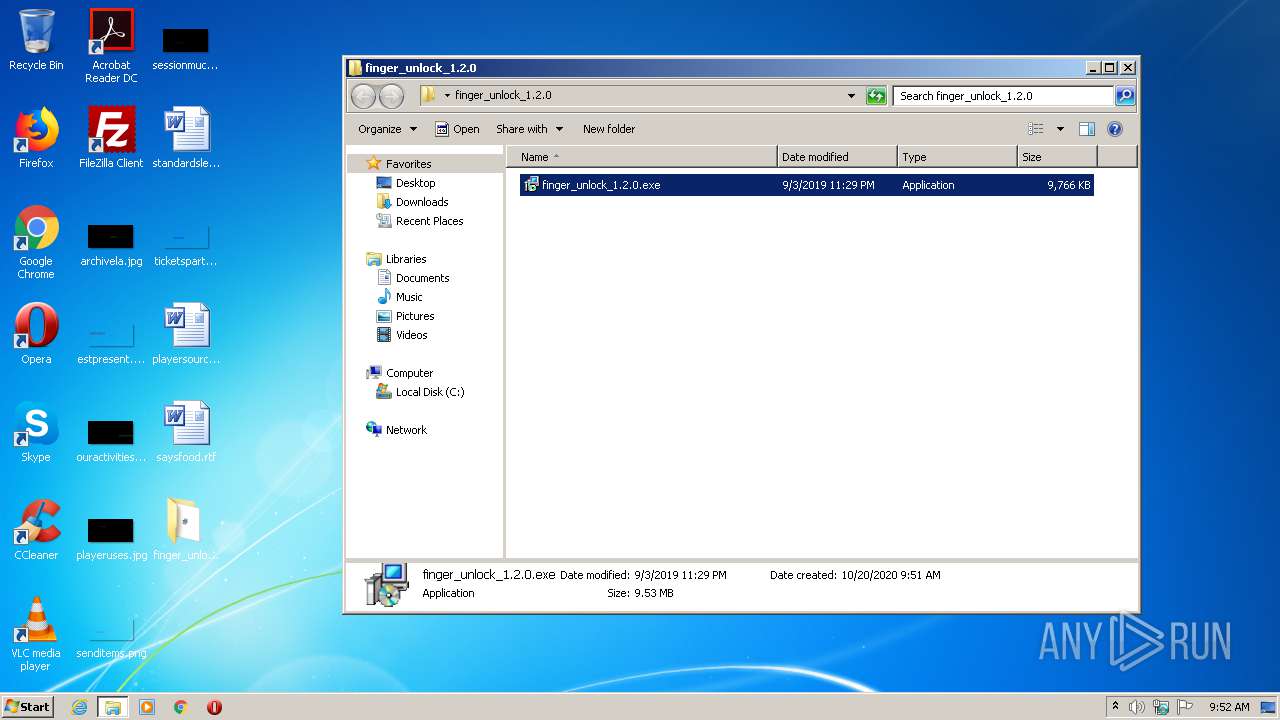
| ZipFileName: | finger_unlock_1.2.0.exe |
Total processes
47
Monitored processes
7
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1500 | "C:\Users\admin\Desktop\finger_unlock_1.2.0\finger_unlock_1.2.0.exe" | C:\Users\admin\Desktop\finger_unlock_1.2.0\finger_unlock_1.2.0.exe | explorer.exe | ||||||||||||
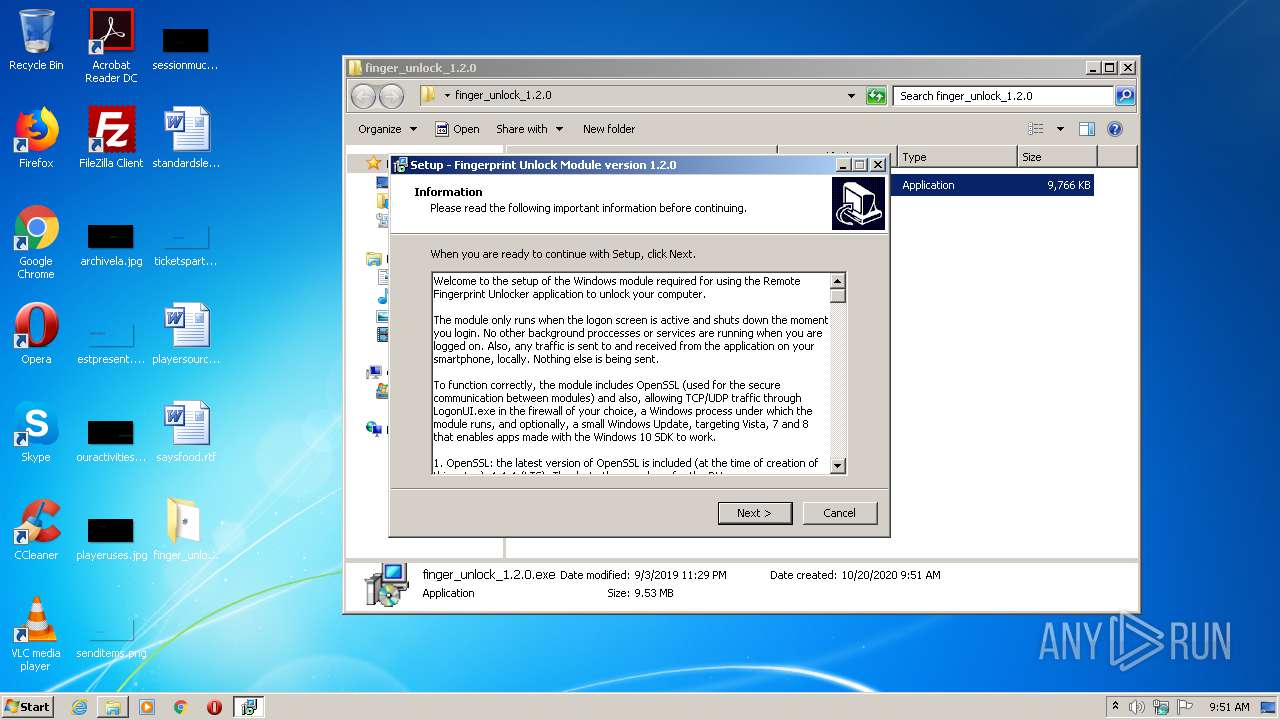
User: admin Company: Andrei Rusu Integrity Level: MEDIUM Description: Fingerprint Unlock Module Setup Exit code: 0 Version: Modules
| |||||||||||||||
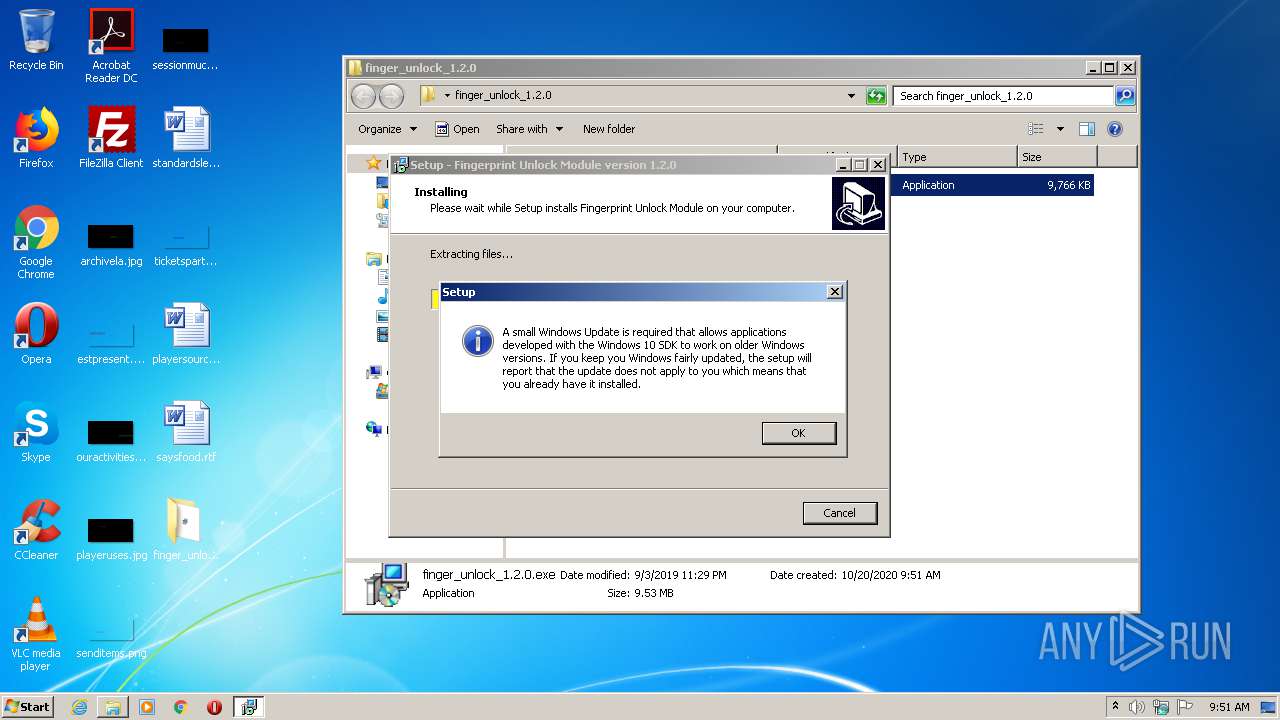
| 2148 | "C:\Users\admin\AppData\Local\Temp\is-R2LTC.tmp\finger_unlock_1.2.0.tmp" /SL5="$301CC,9746687,58368,C:\Users\admin\Desktop\finger_unlock_1.2.0\finger_unlock_1.2.0.exe" /SPAWNWND=$30128 /NOTIFYWND=$3012C | C:\Users\admin\AppData\Local\Temp\is-R2LTC.tmp\finger_unlock_1.2.0.tmp | finger_unlock_1.2.0.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2352 | "C:\Users\admin\Desktop\finger_unlock_1.2.0\finger_unlock_1.2.0.exe" /SPAWNWND=$30128 /NOTIFYWND=$3012C | C:\Users\admin\Desktop\finger_unlock_1.2.0\finger_unlock_1.2.0.exe | finger_unlock_1.2.0.tmp | ||||||||||||
User: admin Company: Andrei Rusu Integrity Level: HIGH Description: Fingerprint Unlock Module Setup Exit code: 0 Version: Modules
| |||||||||||||||
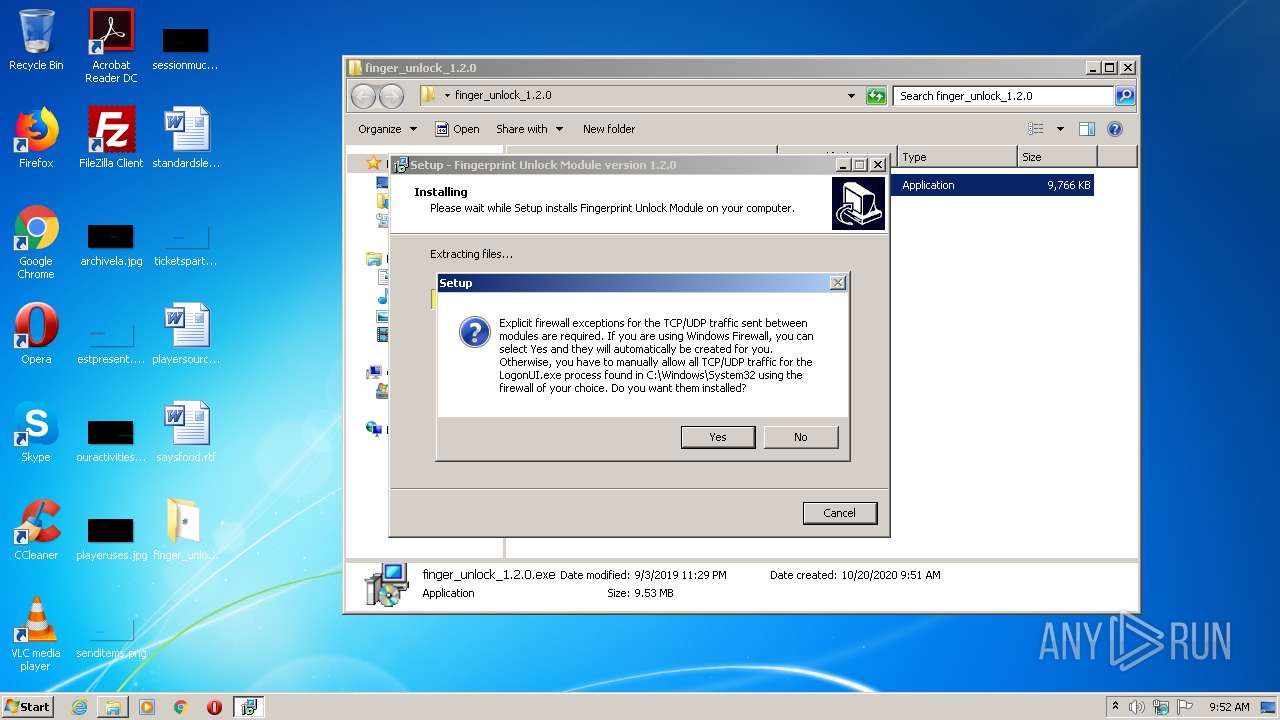
| 2928 | "C:\Windows\system32\cscript.exe" //nologo "C:\Windows\system32\Fingerprint Credentials\firewallexceptions.vbs" /GroupName:"Fingerprint Unlock Module" /RuleName:"Logon UI" /ExePath:"C:\Windows\system32\LogonUI.exe" /Command:"install" | C:\Windows\system32\cscript.exe | — | finger_unlock_1.2.0.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
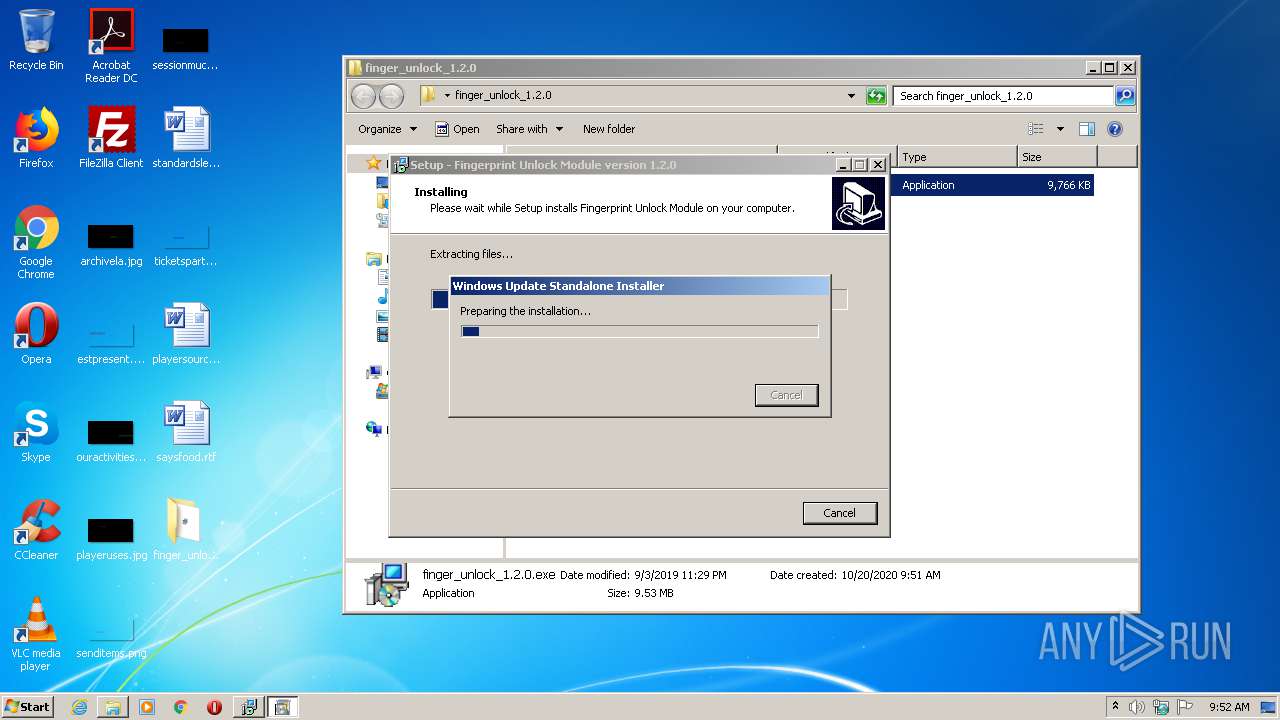
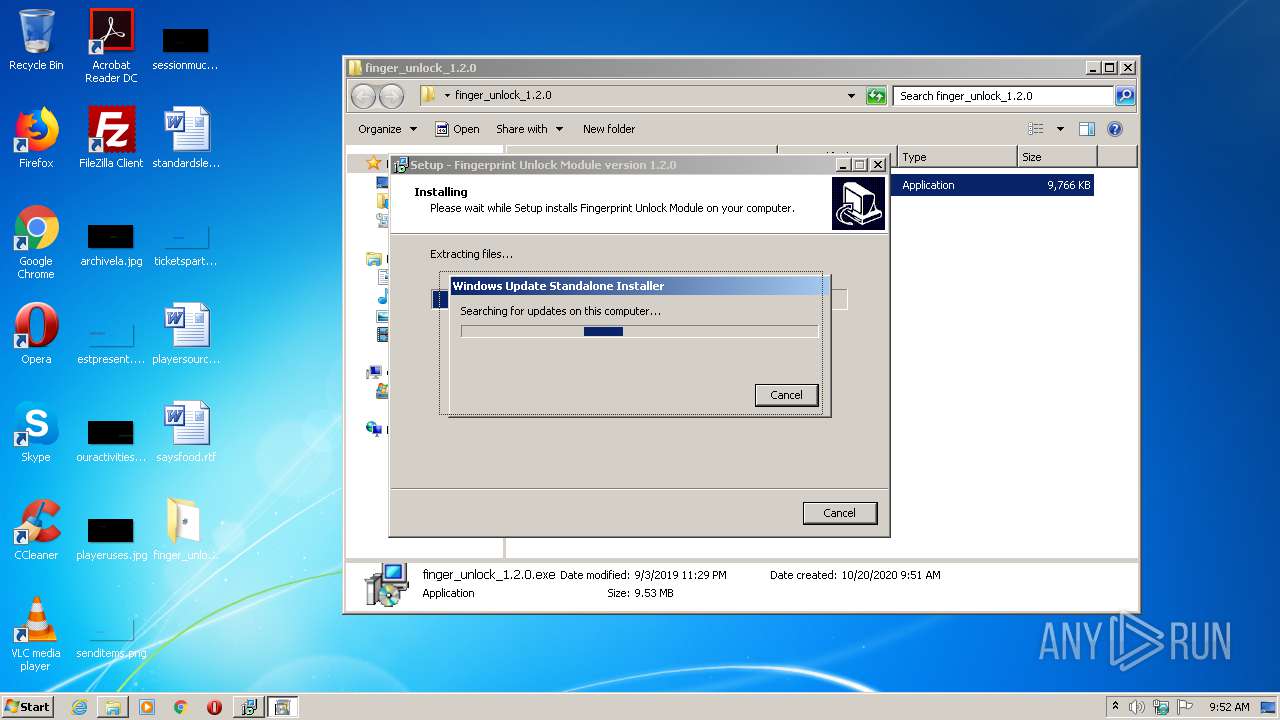
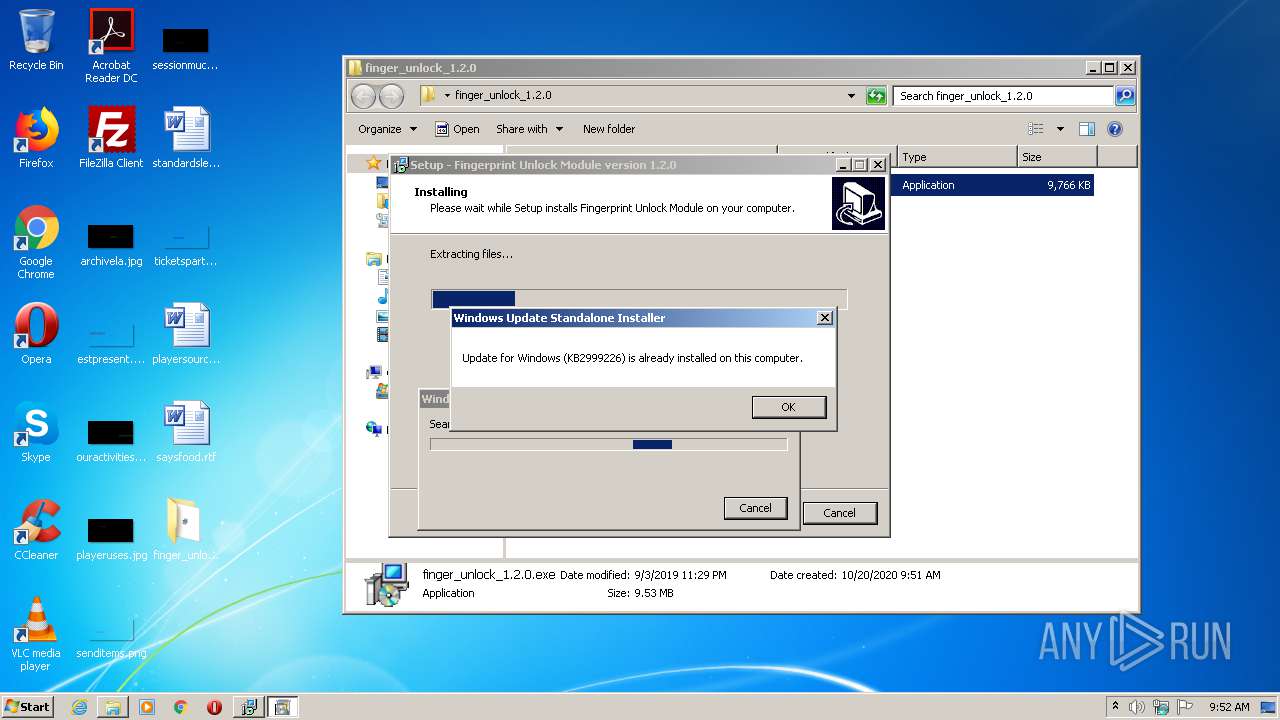
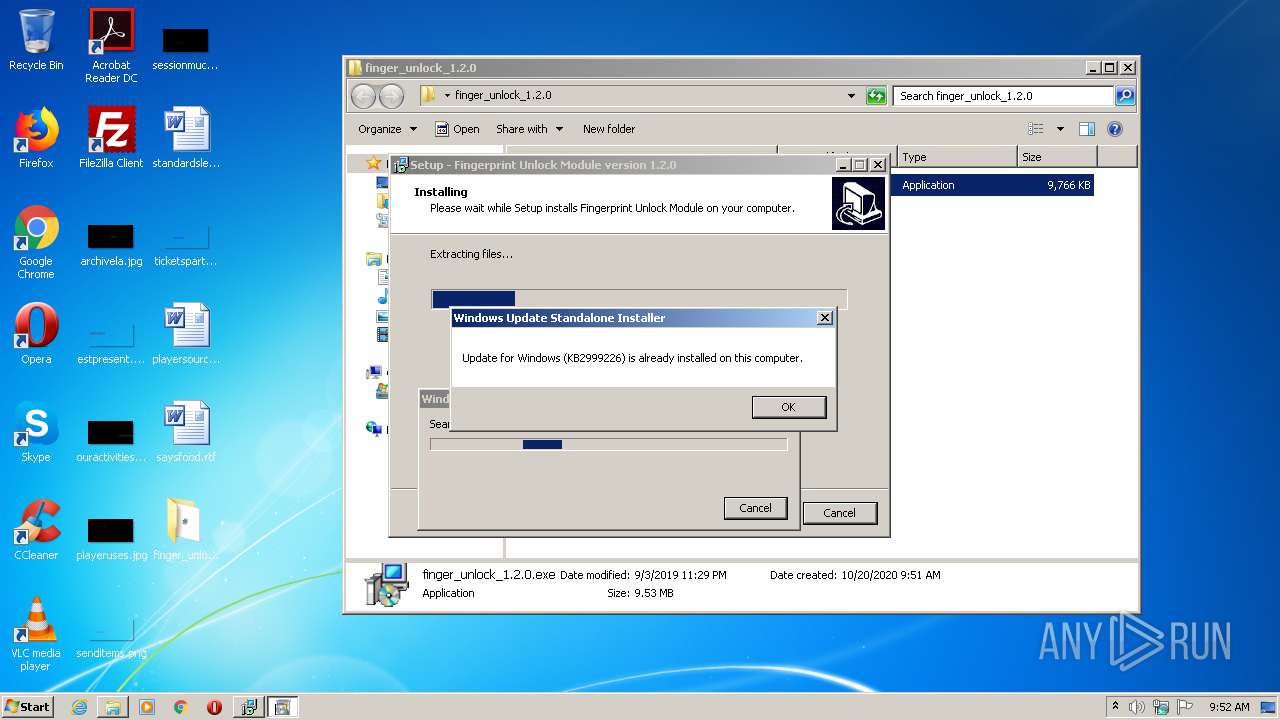
| 3152 | "C:\Windows\system32\wusa.exe" C:\Users\admin\AppData\Local\Temp\is-8LE8P.tmp\Windows6.1-KB2999226-x86.msu | C:\Windows\system32\wusa.exe | — | finger_unlock_1.2.0.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Standalone Installer Exit code: 2359302 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3244 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\finger_unlock_1.2.0.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3276 | "C:\Users\admin\AppData\Local\Temp\is-2AVUV.tmp\finger_unlock_1.2.0.tmp" /SL5="$3012C,9746687,58368,C:\Users\admin\Desktop\finger_unlock_1.2.0\finger_unlock_1.2.0.exe" | C:\Users\admin\AppData\Local\Temp\is-2AVUV.tmp\finger_unlock_1.2.0.tmp | — | finger_unlock_1.2.0.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
Total events
782
Read events
726
Write events
50
Delete events
6
Modification events
| (PID) Process: | (3244) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3244) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3244) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3244) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\finger_unlock_1.2.0.zip | |||
| (PID) Process: | (3244) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3244) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3244) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3244) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3244) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\finger_unlock_1.2.0 | |||
| (PID) Process: | (3244) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
8
Suspicious files
3
Text files
6
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2148 | finger_unlock_1.2.0.tmp | C:\Windows\system32\is-SQJND.tmp | — | |
MD5:— | SHA256:— | |||
| 2148 | finger_unlock_1.2.0.tmp | C:\Users\admin\AppData\Local\Temp\is-8LE8P.tmp\is-ODKMM.tmp | — | |
MD5:— | SHA256:— | |||
| 3152 | wusa.exe | C:\6592c7768a180106aea579ab5e18\$dpx$.tmp\d44da8475ae67b419c83f2456d3eefdf.tmp | — | |
MD5:— | SHA256:— | |||
| 3152 | wusa.exe | C:\6592c7768a180106aea579ab5e18\$dpx$.tmp\6b39cd27594edd47a0c1b946a1d6c293.tmp | — | |
MD5:— | SHA256:— | |||
| 3152 | wusa.exe | C:\6592c7768a180106aea579ab5e18\$dpx$.tmp\7babaeb4b335f74ca6b20a7799a272e4.tmp | — | |
MD5:— | SHA256:— | |||
| 3152 | wusa.exe | C:\6592c7768a180106aea579ab5e18\$dpx$.tmp\51bf2e5c53dd7742a8750353e39a16b4.tmp | — | |
MD5:— | SHA256:— | |||
| 3152 | wusa.exe | C:\Windows\Logs\DPX\setuperr.log | — | |
MD5:— | SHA256:— | |||
| 2148 | finger_unlock_1.2.0.tmp | C:\Windows\system32\is-K8U2C.tmp | — | |
MD5:— | SHA256:— | |||
| 2148 | finger_unlock_1.2.0.tmp | C:\Windows\system32\is-0LB93.tmp | — | |
MD5:— | SHA256:— | |||
| 2148 | finger_unlock_1.2.0.tmp | C:\Windows\system32\is-IRD7S.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report