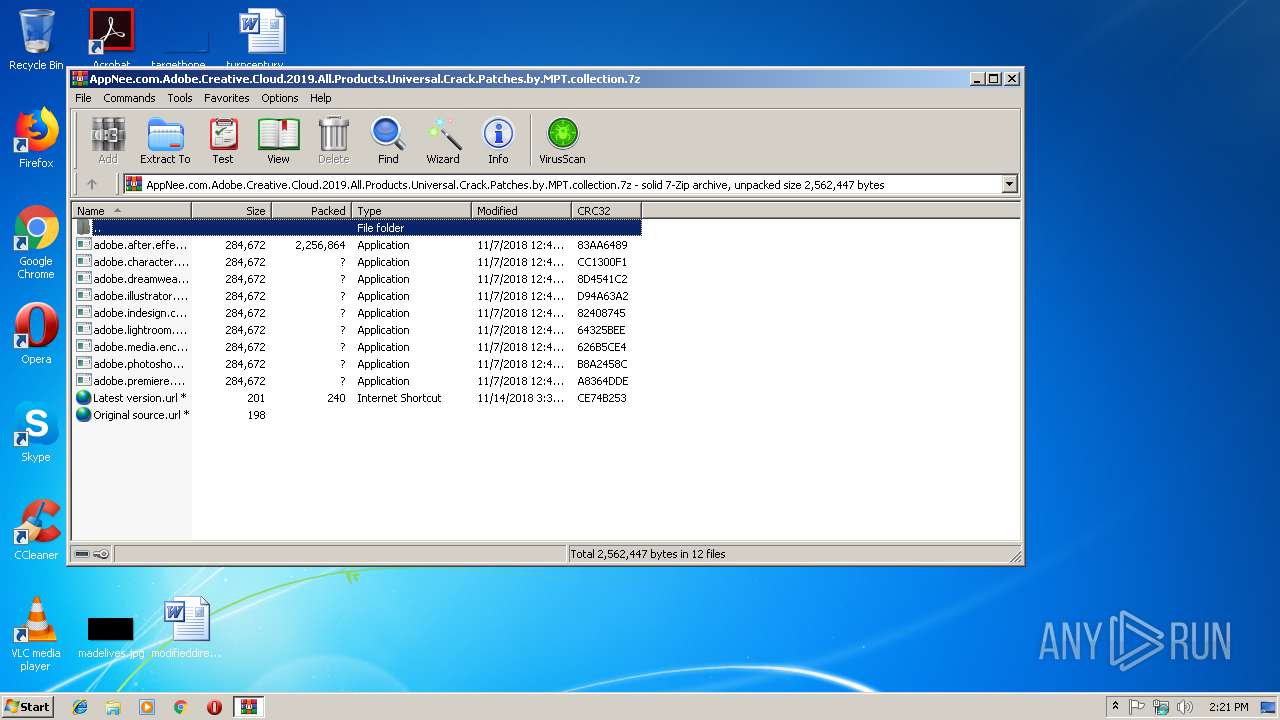
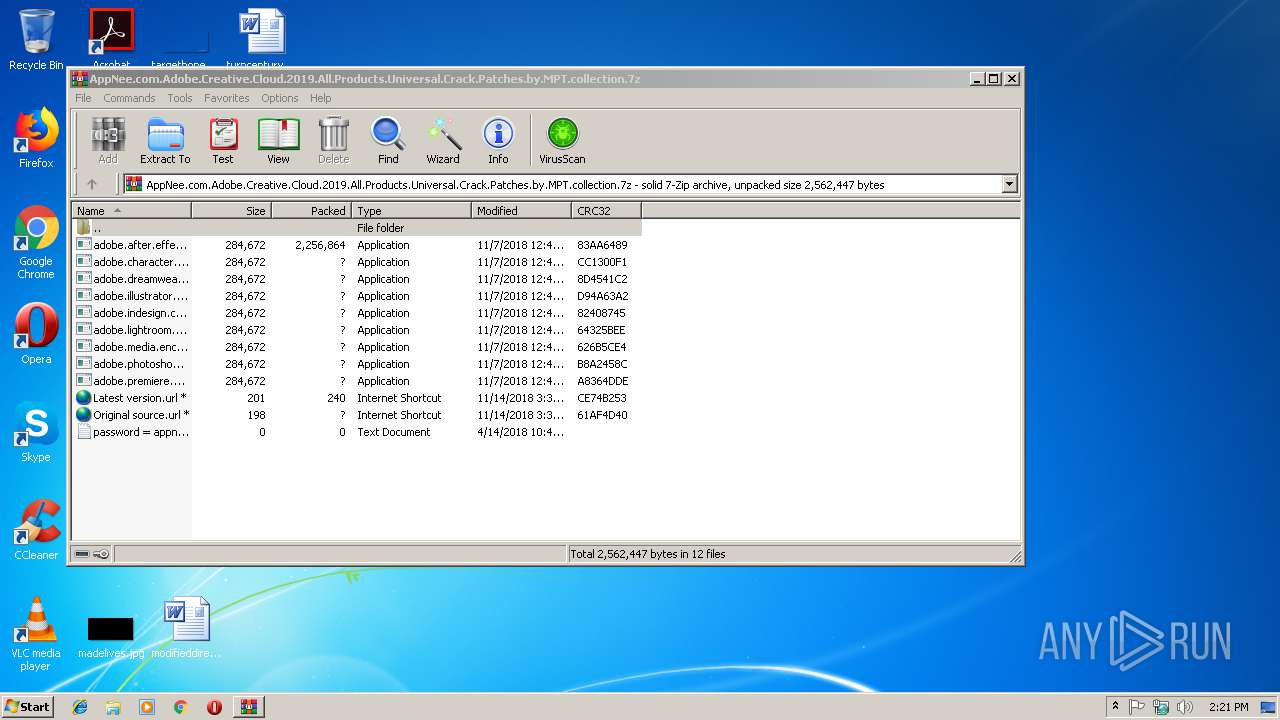
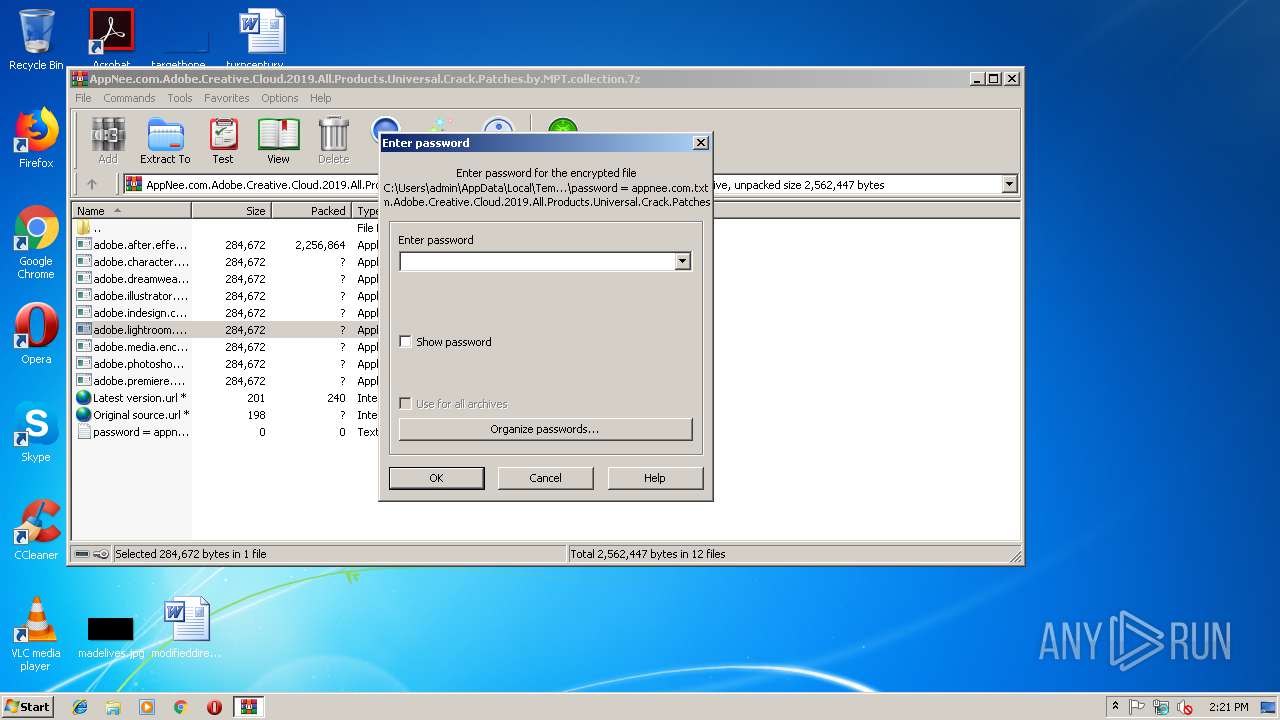
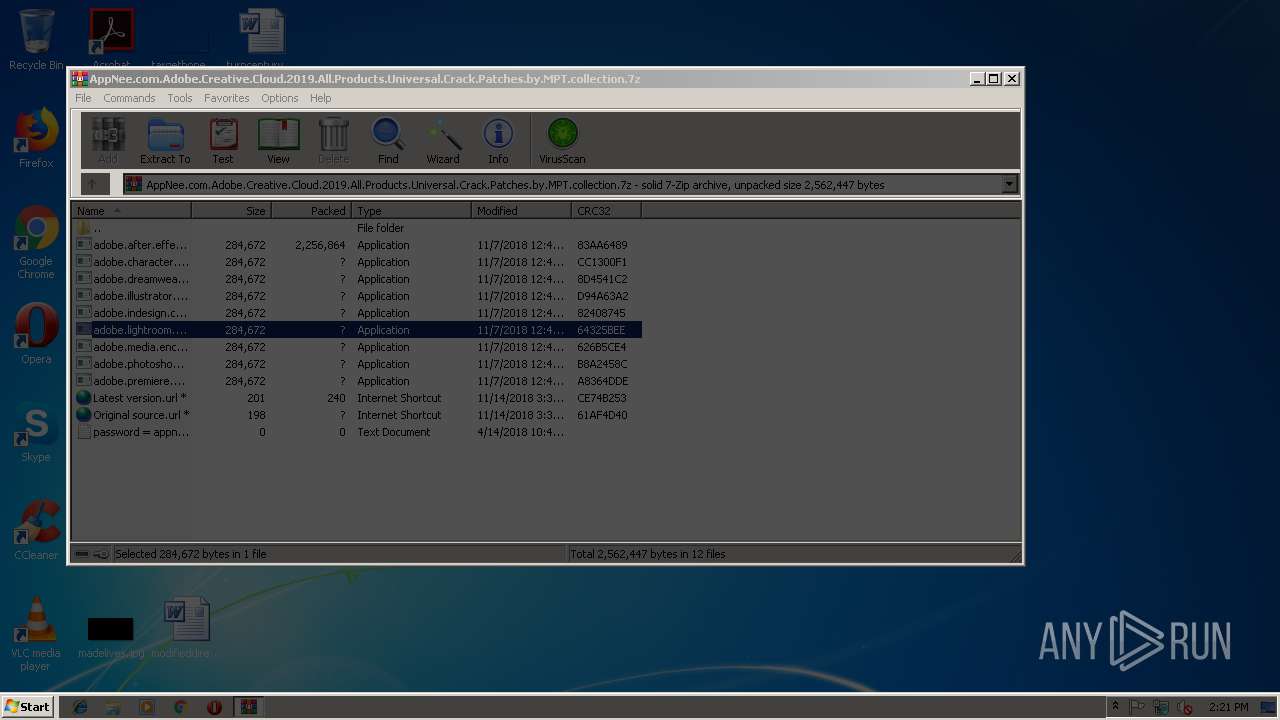
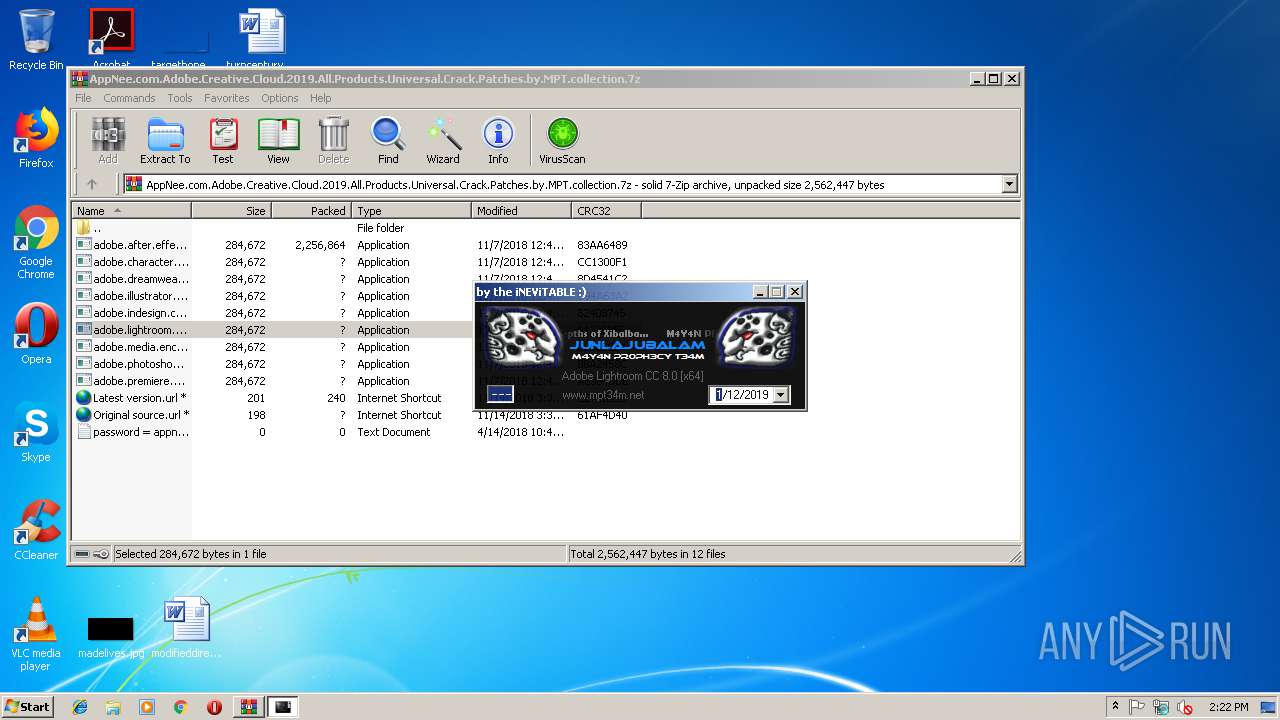
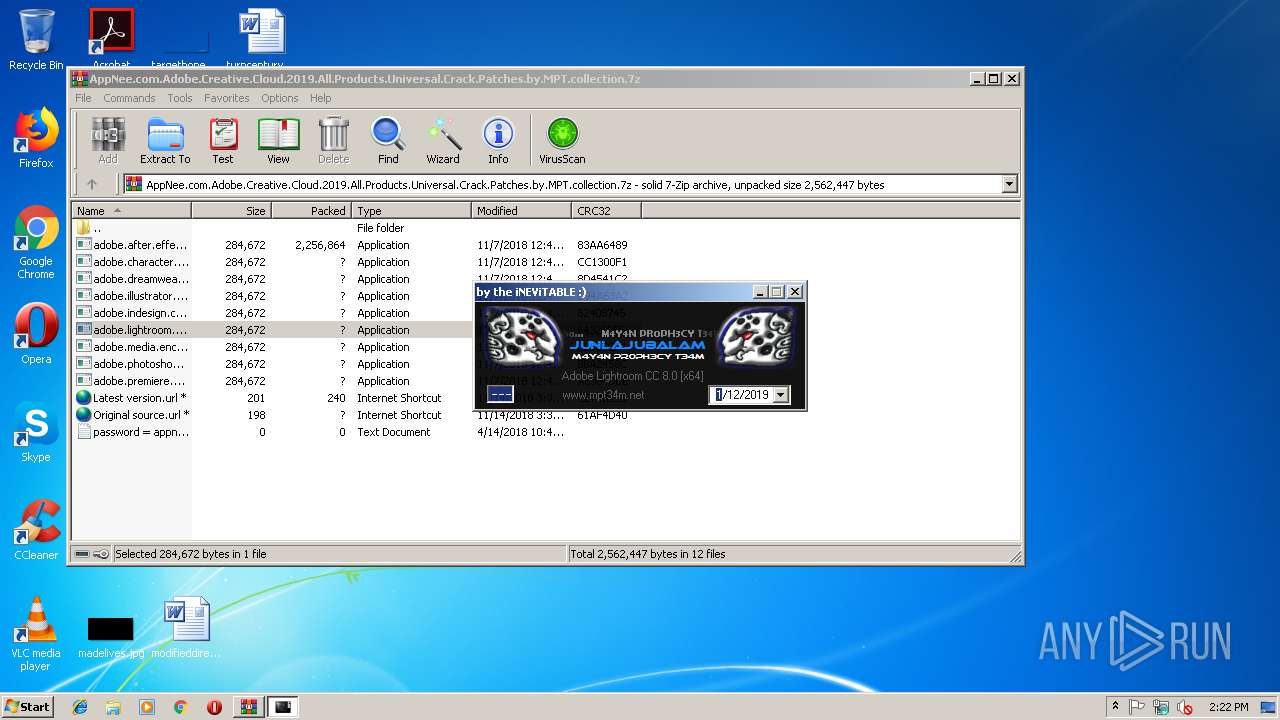
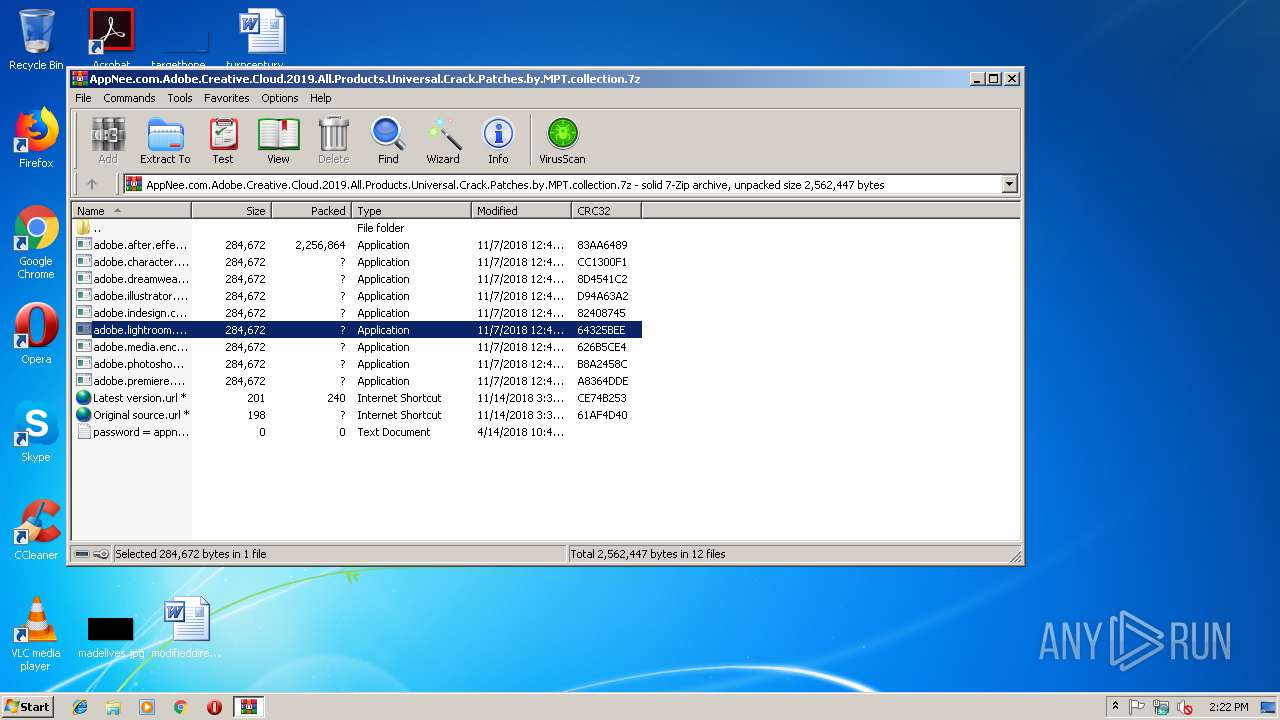
| File name: | AppNee.com.Adobe.Creative.Cloud.2019.All.Products.Universal.Crack.Patches.by.MPT.collection.7z |
| Full analysis: | https://app.any.run/tasks/0f2f8592-534e-4361-8061-0f5718ad2a6c |
| Verdict: | Suspicious activity |
| Analysis date: | January 12, 2019, 14:20:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | C53D393A6BCB2527082CF4123C1C33ED |
| SHA1: | 8D178435EC699AE5403D5F71A84759345CC0AE12 |
| SHA256: | 071ED2F9D05590468D04D0DE3B70B4A4668138D3DD1DEDFBE313DD3D012646CF |
| SSDEEP: | 49152:615y0mgC+6r6urBJaHesjEpRnCEq8HXG6drotJgLUOnl:Yir6coYnnCk3GAotWLR |
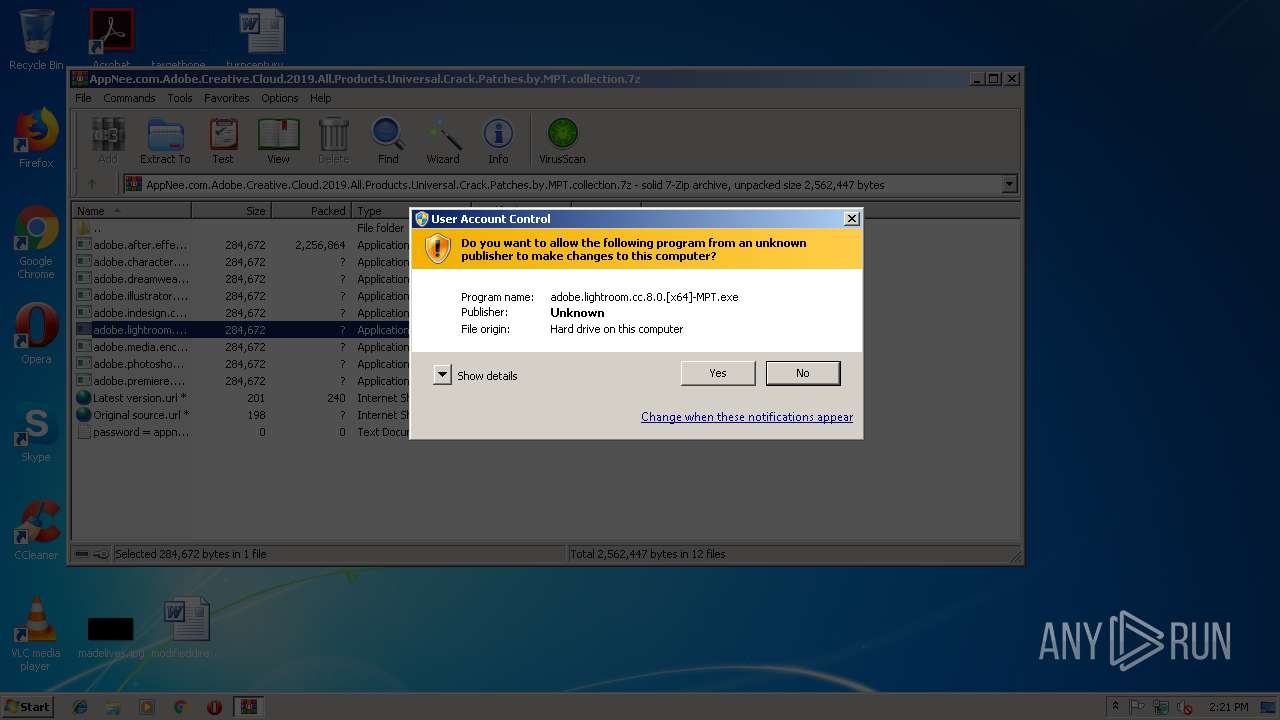
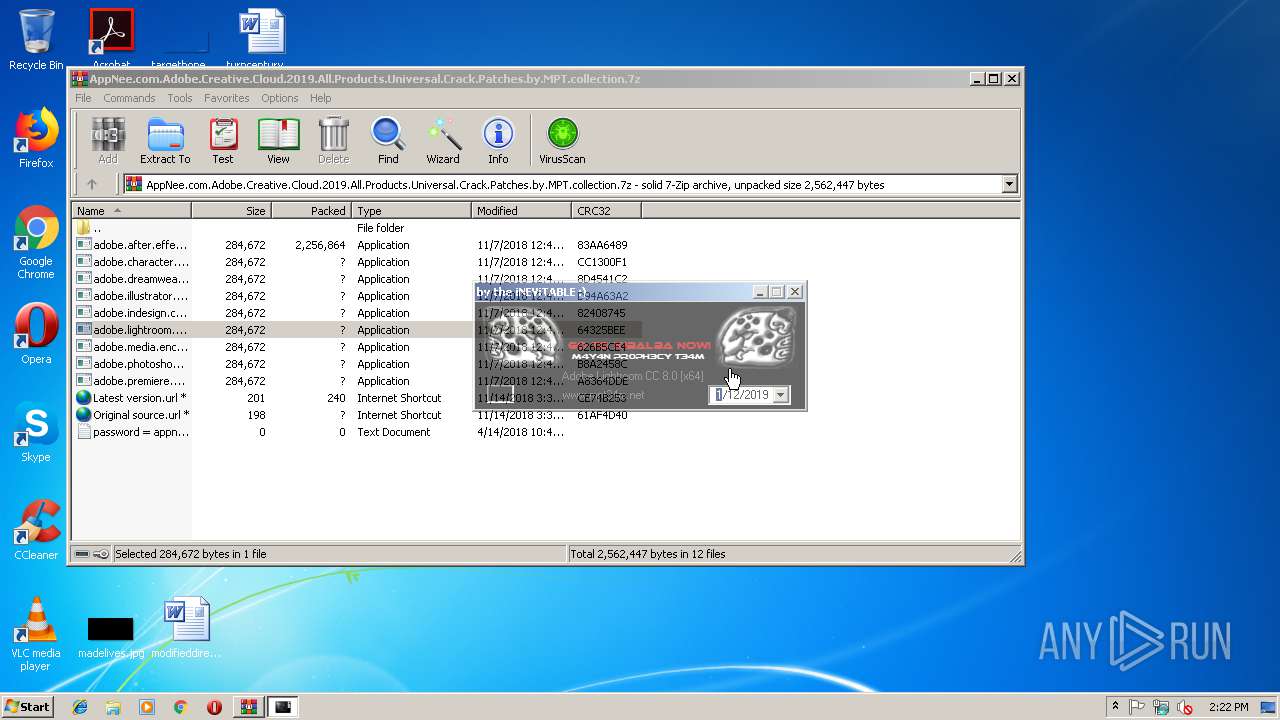
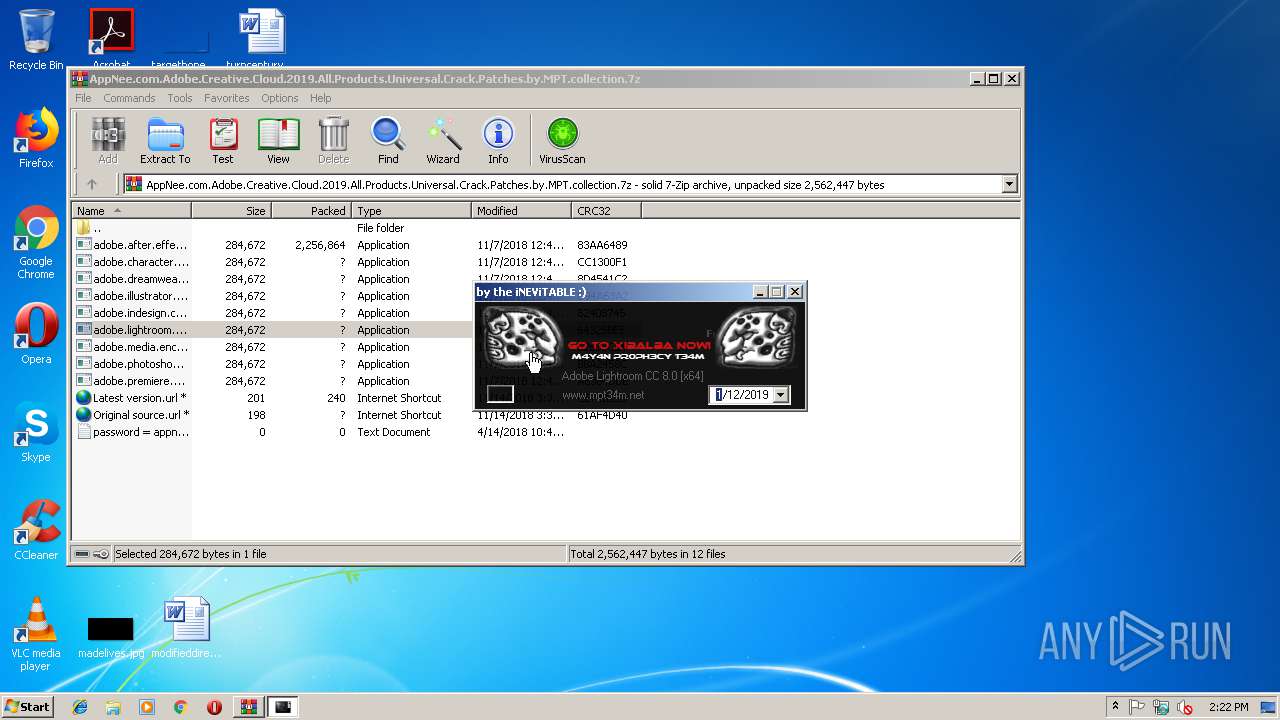
MALICIOUS
Application was dropped or rewritten from another process
- adobe.lightroom.cc.8.0.[x64]-MPT.exe (PID: 4080)
- adobe.lightroom.cc.8.0.[x64]-MPT.exe (PID: 3820)
Loads dropped or rewritten executable
- adobe.lightroom.cc.8.0.[x64]-MPT.exe (PID: 4080)
SUSPICIOUS
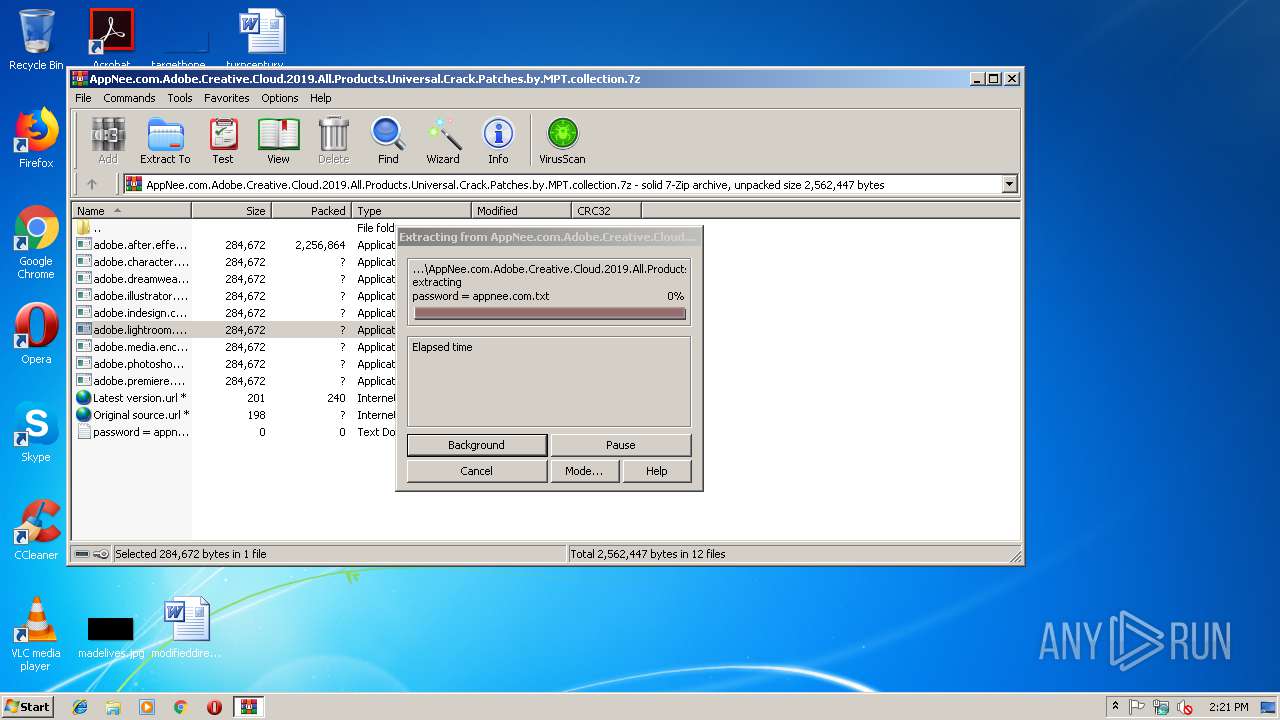
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3000)
- adobe.lightroom.cc.8.0.[x64]-MPT.exe (PID: 4080)
INFO
Application launched itself
- chrome.exe (PID: 2180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
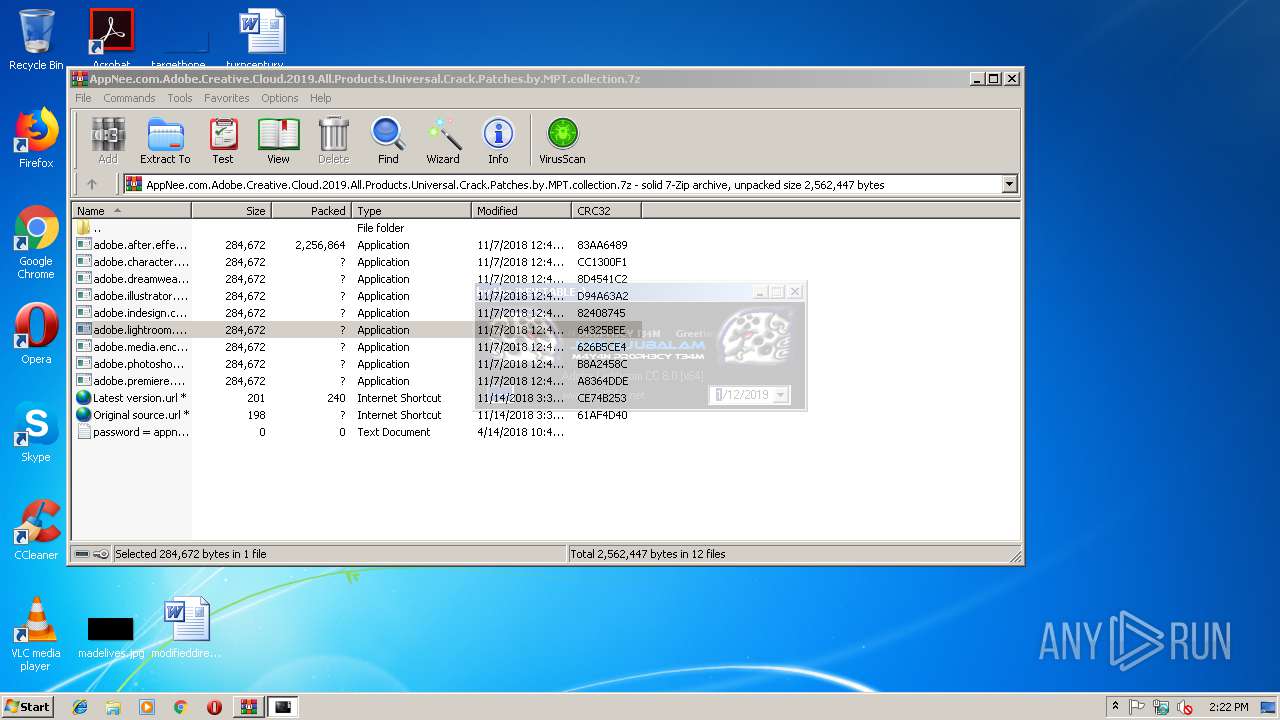
Total processes
43
Monitored processes
10
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,4361484908201063521,3689172358953829998,131072 --enable-features=PasswordImport --service-pipe-token=9774B590B07EC2C445DFCA1108458EA1 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9774B590B07EC2C445DFCA1108458EA1 --renderer-client-id=3 --mojo-platform-channel-handle=2072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 | |||||||||||||||
| 2832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f7a00b0,0x6f7a00c0,0x6f7a00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3000 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\AppNee.com.Adobe.Creative.Cloud.2019.All.Products.Universal.Crack.Patches.by.MPT.collection.7z" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3108 | SndVol.exe -f 45941919 13944 | C:\Windows\system32\SndVol.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Volume Mixer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,4361484908201063521,3689172358953829998,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=E557C44F89E38760C1C45DA320E99D8D --mojo-platform-channel-handle=1000 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,4361484908201063521,3689172358953829998,131072 --enable-features=PasswordImport --service-pipe-token=F3FFCE2E9D44FA4384C2B6B191320CDF --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=F3FFCE2E9D44FA4384C2B6B191320CDF --renderer-client-id=5 --mojo-platform-channel-handle=1812 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
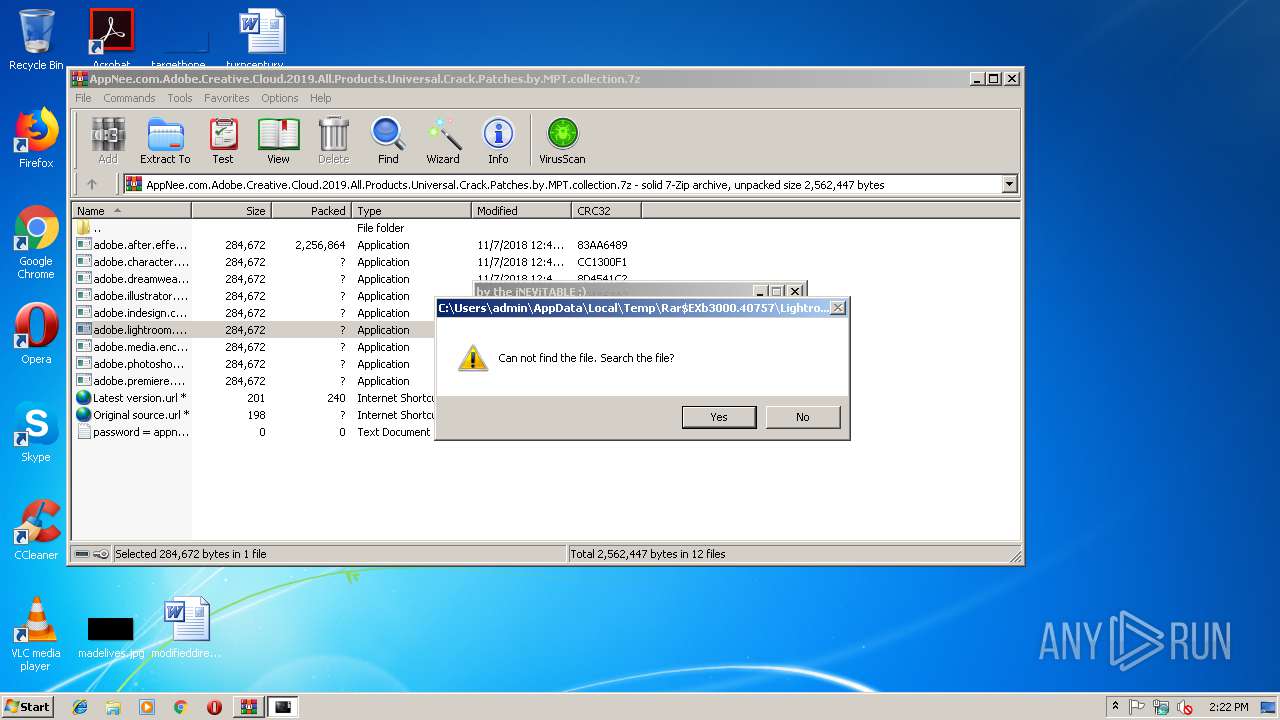
| 3820 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3000.40757\adobe.lightroom.cc.8.0.[x64]-MPT.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb3000.40757\adobe.lightroom.cc.8.0.[x64]-MPT.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2200 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 4080 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3000.40757\adobe.lightroom.cc.8.0.[x64]-MPT.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb3000.40757\adobe.lightroom.cc.8.0.[x64]-MPT.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
589
Read events
537
Write events
49
Delete events
3
Modification events
| (PID) Process: | (3000) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3000) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3000) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3000) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\AppNee.com.Adobe.Creative.Cloud.2019.All.Products.Universal.Crack.Patches.by.MPT.collection.7z | |||
| (PID) Process: | (3000) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3000) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3000) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3000) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3000) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\ieframe.dll,-10046 |
Value: Internet Shortcut | |||
| (PID) Process: | (3000) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
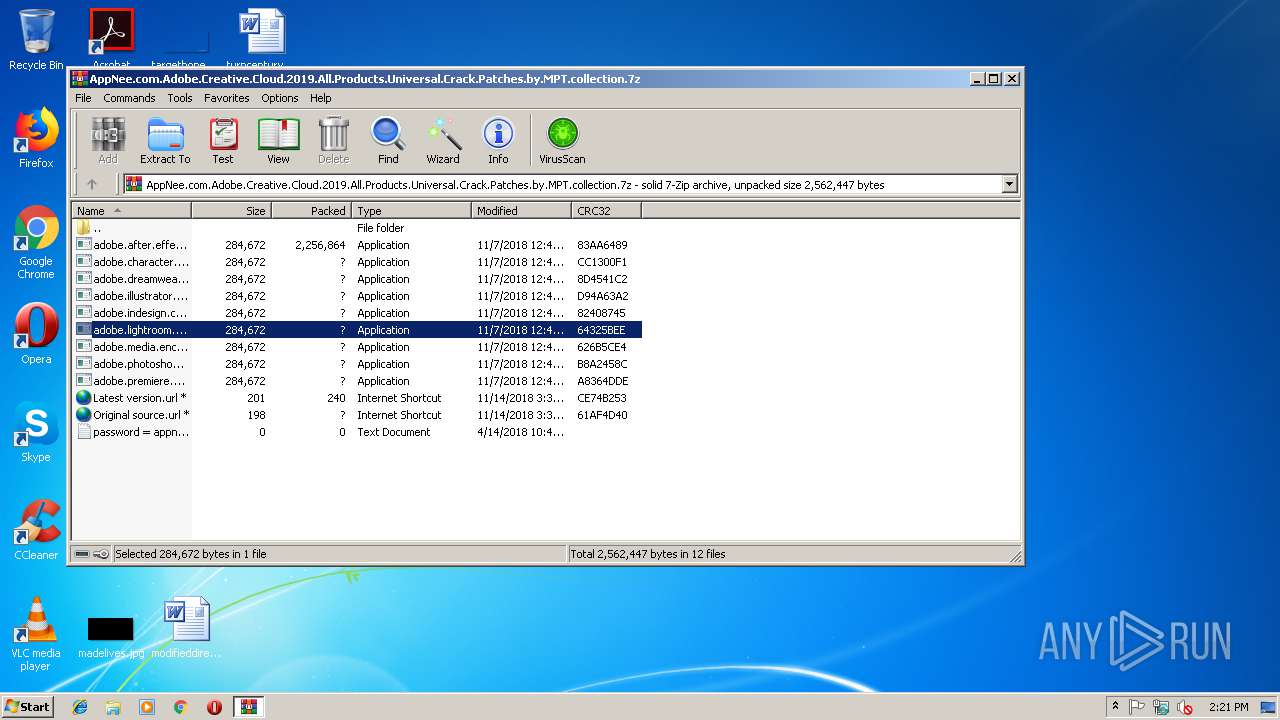
Executable files
12
Suspicious files
2
Text files
18
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3000 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3000.40757\Original source.url | text | |
MD5:— | SHA256:— | |||
| 3000 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3000.40757\Latest version.url | text | |
MD5:— | SHA256:— | |||
| 3000 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3000.40757\adobe.dreamweaver.cc.2019.[x64]-MPT.exe | executable | |
MD5:— | SHA256:— | |||
| 3000 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3000.40757\adobe.after.effects.cc.2019.[x64]-MPT.exe | executable | |
MD5:— | SHA256:— | |||
| 3000 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3000.40757\adobe.lightroom.cc.8.0.[x64]-MPT.exe | executable | |
MD5:— | SHA256:— | |||
| 3000 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3000.40757\adobe.illustrator.cc.2019.[x64]-MPT.exe | executable | |
MD5:— | SHA256:— | |||
| 2180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5cc9f9ed-8d5f-4254-9310-397c1956fcd1.tmp | — | |
MD5:— | SHA256:— | |||
| 3000 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3000.40757\adobe.indesign.cc.2019.[x64]-MPT.exe | executable | |
MD5:— | SHA256:— | |||
| 2180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3000 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3000.40757\adobe.photoshop.cc.2019.[x64]-MPT.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report