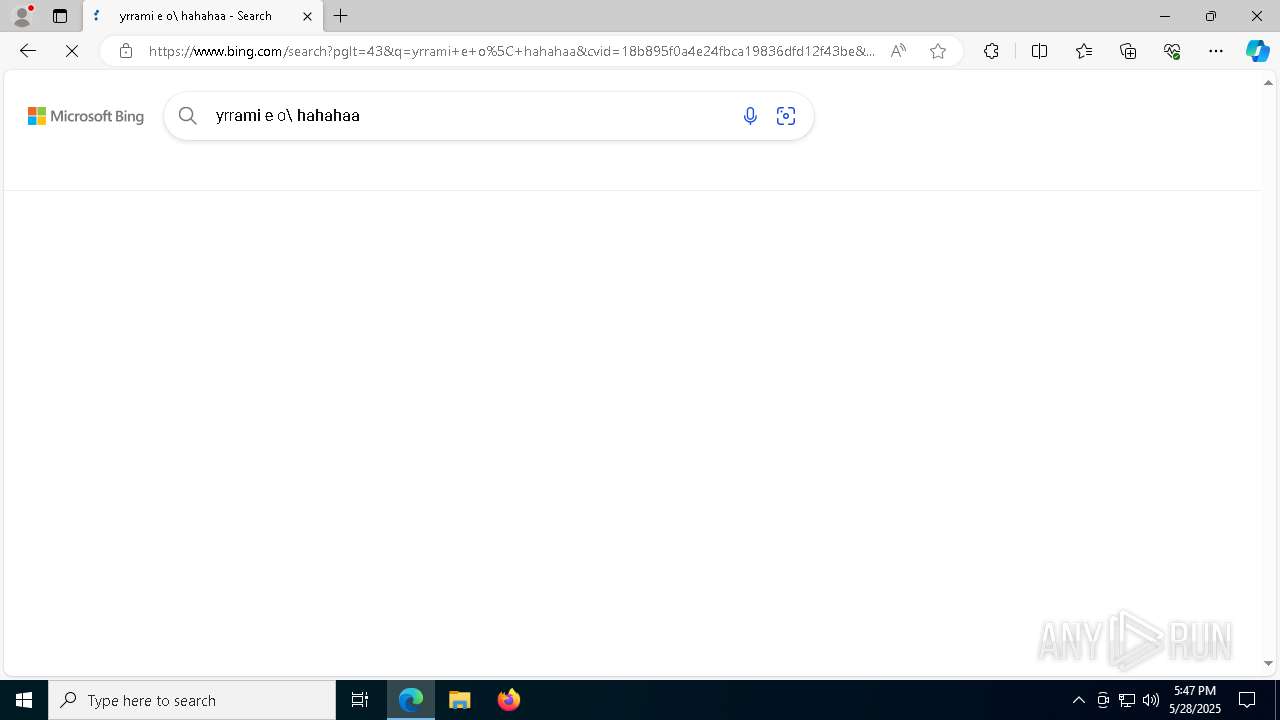
| File name: | yWgZxtfPWjpOPZk_temp.exe |
| Full analysis: | https://app.any.run/tasks/660cda8c-2511-428b-972b-4a979dedd4e3 |
| Verdict: | Malicious activity |
| Analysis date: | May 28, 2025, 17:45:55 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 3F4D1992C27EACD65AF34DBE67AE68CC |
| SHA1: | 05D188F601E38EC4444512EC4CCF9756A92221C5 |
| SHA256: | 071760B5F672E58D2846C0E41BD08CA602A71B08BA8190FB289F49EF82C3C508 |
| SSDEEP: | 49152:HBl0tNqSKjRJjSP+ZmJT3x09JGlxSp4WlOPA7COxiZ:HD |
MALICIOUS
No malicious indicators.SUSPICIOUS
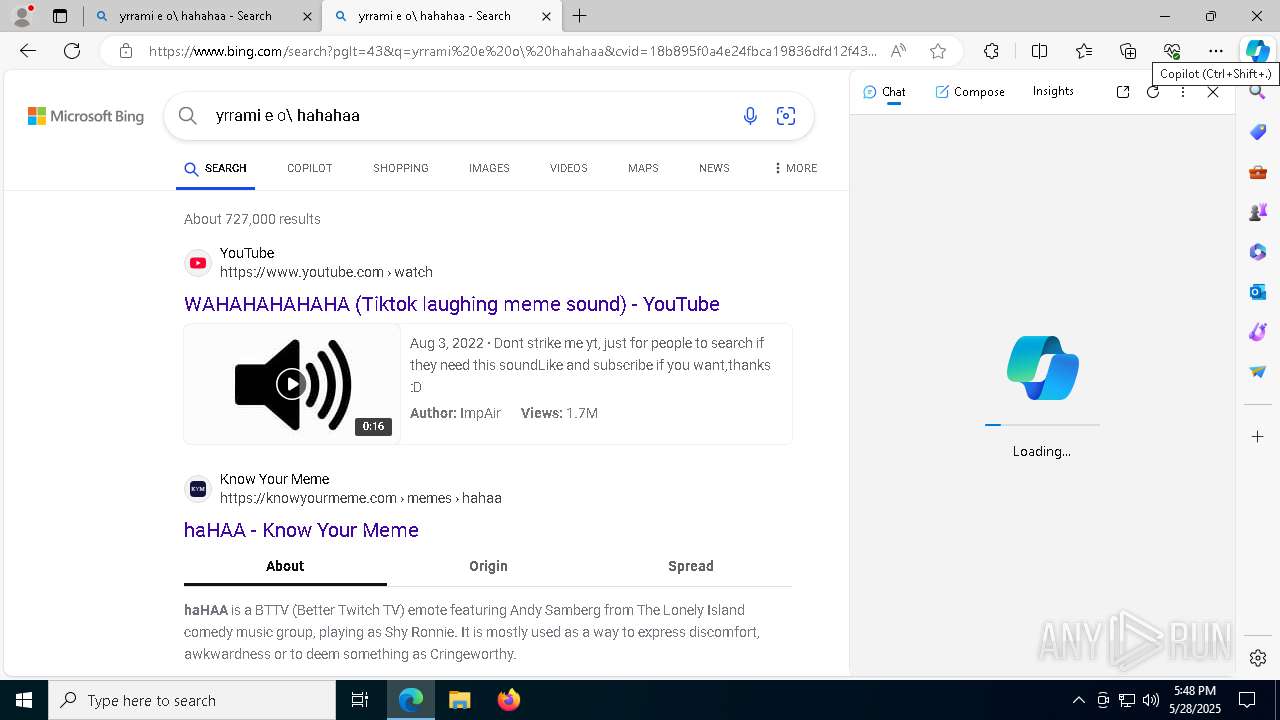
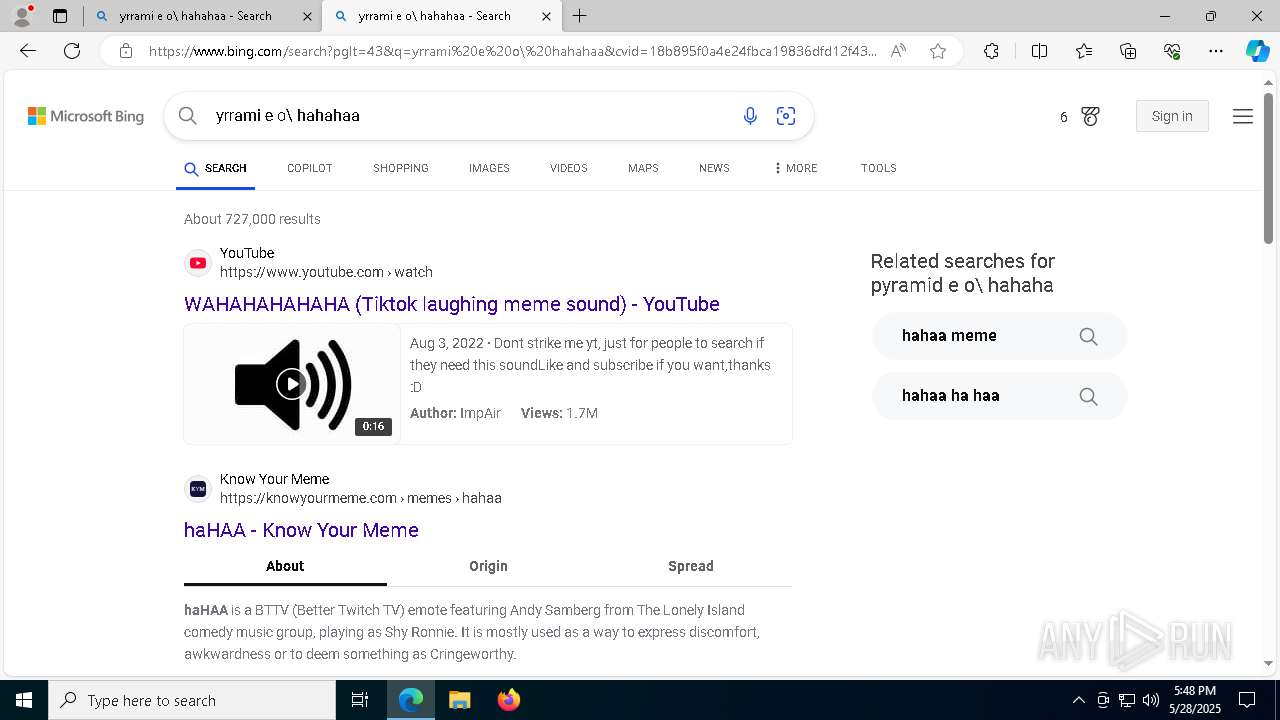
There is functionality for taking screenshot (YARA)
- yWgZxtfPWjpOPZk_temp.exe (PID: 744)
Checks for external IP
- svchost.exe (PID: 2196)
Found regular expressions for crypto-addresses (YARA)
- yWgZxtfPWjpOPZk_temp.exe (PID: 744)
Connects to unusual port
- yWgZxtfPWjpOPZk_temp.exe (PID: 744)
Reads the date of Windows installation
- yWgZxtfPWjpOPZk_temp.exe (PID: 744)
Reads security settings of Internet Explorer
- yWgZxtfPWjpOPZk_temp.exe (PID: 744)
Starts CMD.EXE for commands execution
- yWgZxtfPWjpOPZk_temp.exe (PID: 744)
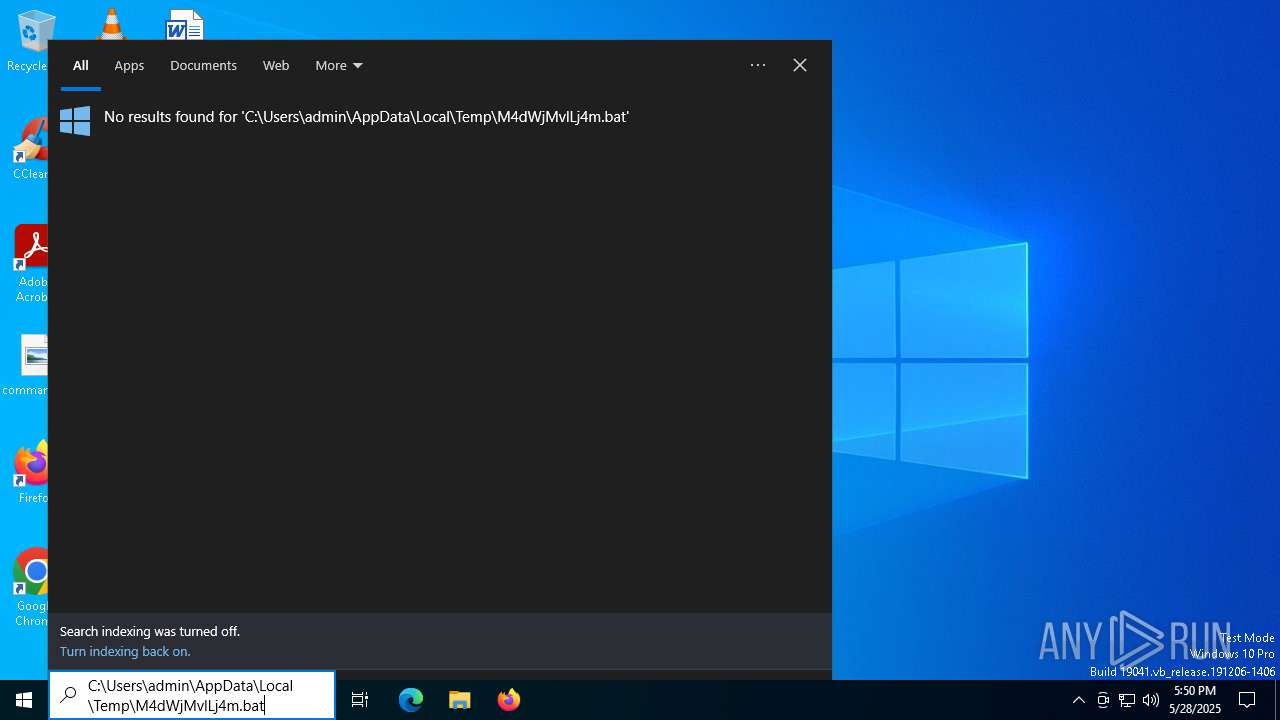
Executing commands from a ".bat" file
- yWgZxtfPWjpOPZk_temp.exe (PID: 744)
Starts application with an unusual extension
- cmd.exe (PID: 7520)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7520)
INFO
Reads the computer name
- identity_helper.exe (PID: 7656)
- yWgZxtfPWjpOPZk_temp.exe (PID: 744)
- identity_helper.exe (PID: 5728)
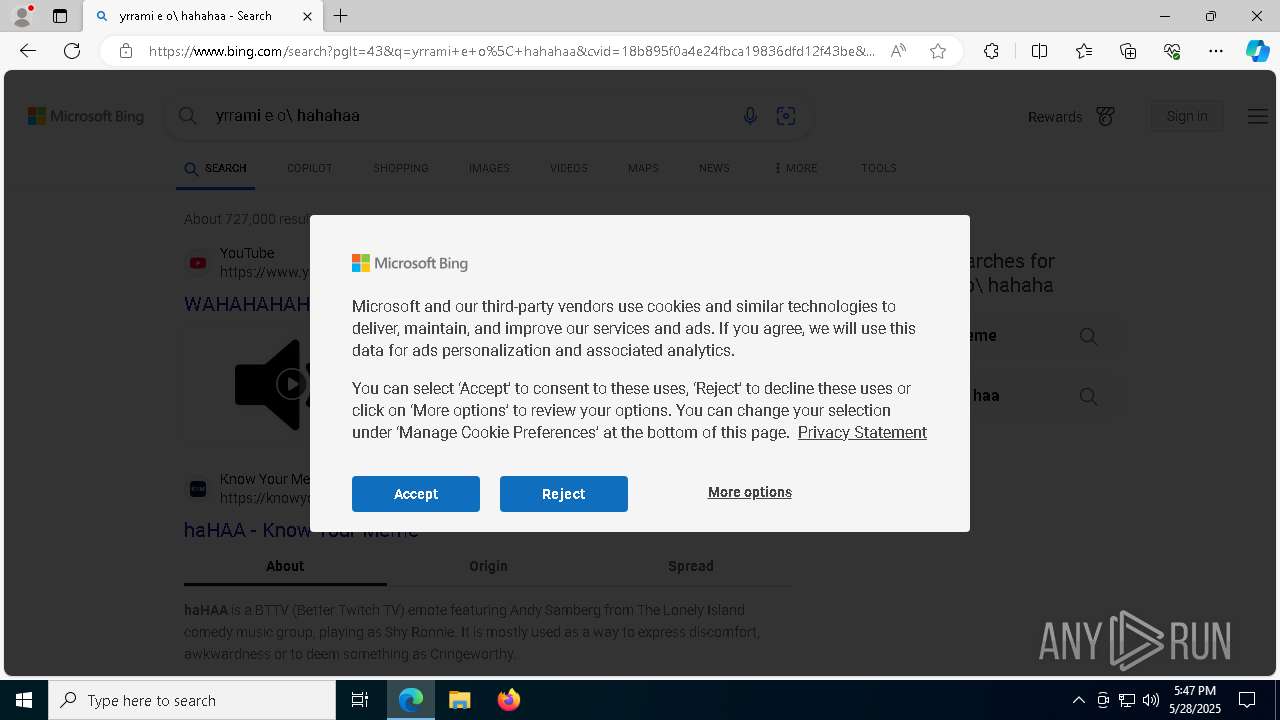
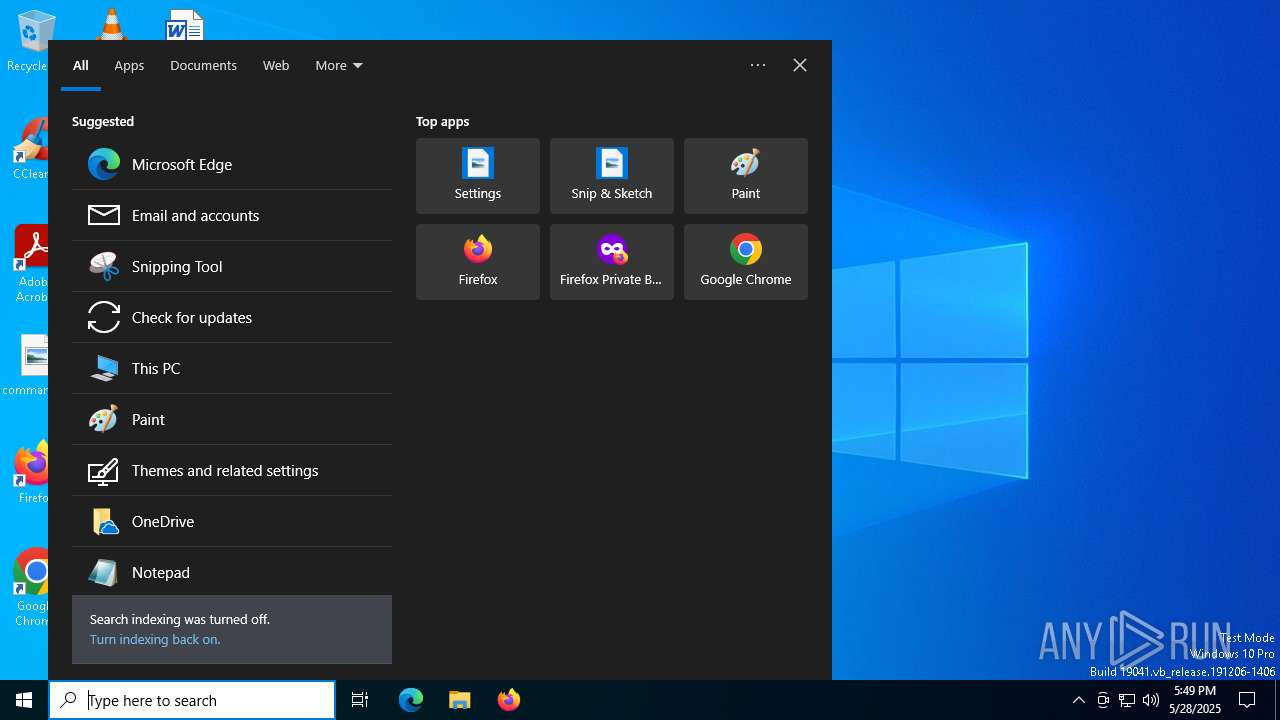
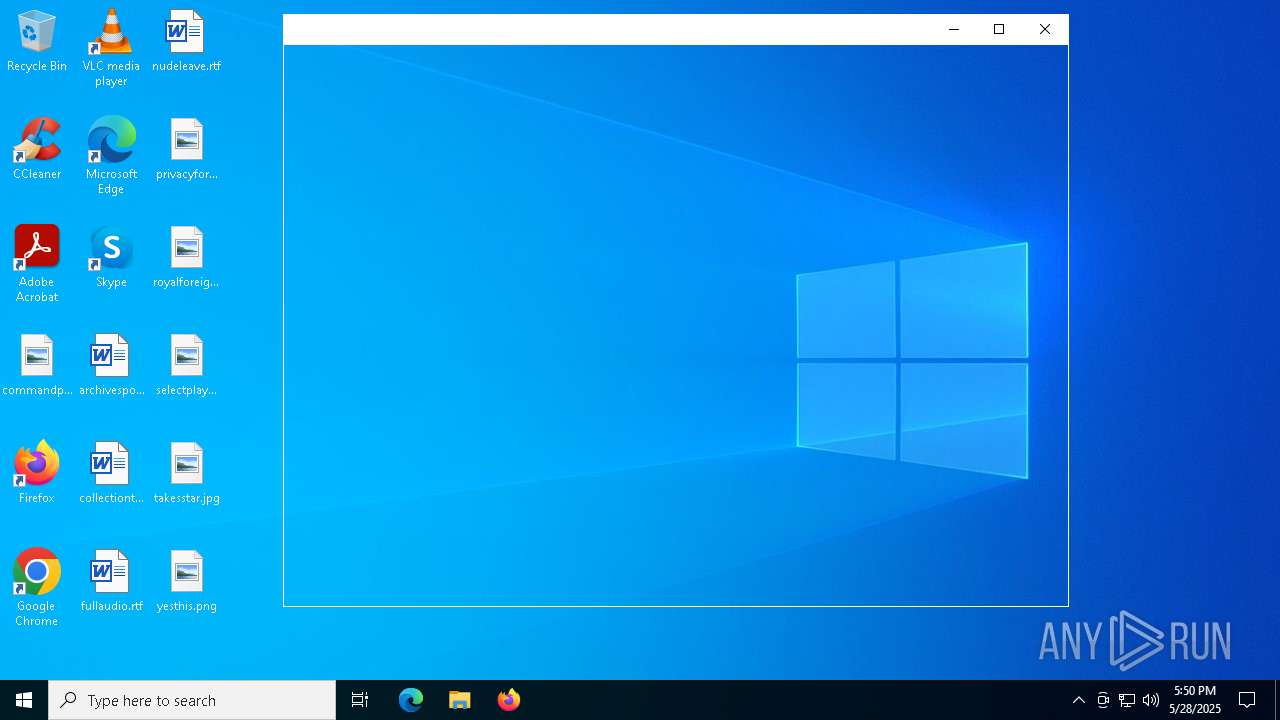
Manual execution by a user
- mspaint.exe (PID: 2320)
- msedge.exe (PID: 6988)
Checks supported languages
- identity_helper.exe (PID: 7656)
- yWgZxtfPWjpOPZk_temp.exe (PID: 744)
- identity_helper.exe (PID: 5728)
- chcp.com (PID: 728)
Checks proxy server information
- yWgZxtfPWjpOPZk_temp.exe (PID: 744)
- slui.exe (PID: 5452)
Reads the software policy settings
- yWgZxtfPWjpOPZk_temp.exe (PID: 744)
- slui.exe (PID: 896)
- slui.exe (PID: 5452)
Disables trace logs
- yWgZxtfPWjpOPZk_temp.exe (PID: 744)
Reads the machine GUID from the registry
- yWgZxtfPWjpOPZk_temp.exe (PID: 744)
Reads Environment values
- yWgZxtfPWjpOPZk_temp.exe (PID: 744)
- identity_helper.exe (PID: 7656)
- identity_helper.exe (PID: 5728)
Application launched itself
- msedge.exe (PID: 6988)
- msedge.exe (PID: 5228)
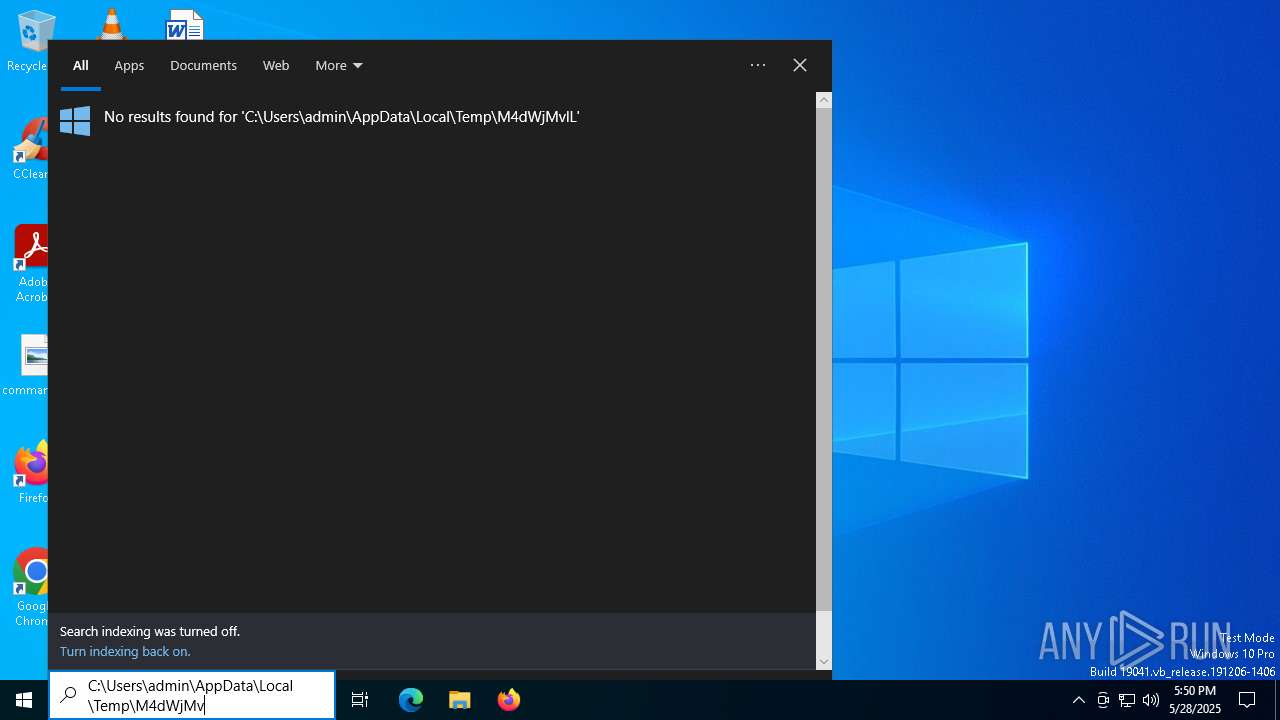
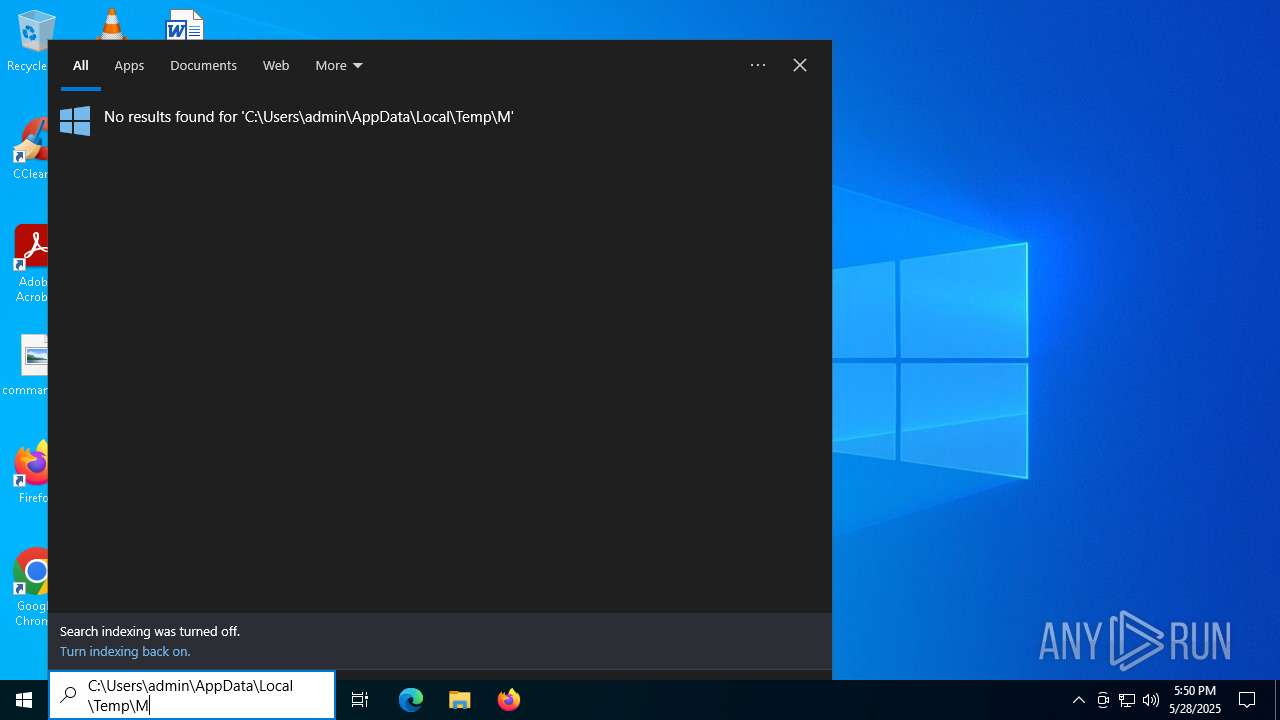
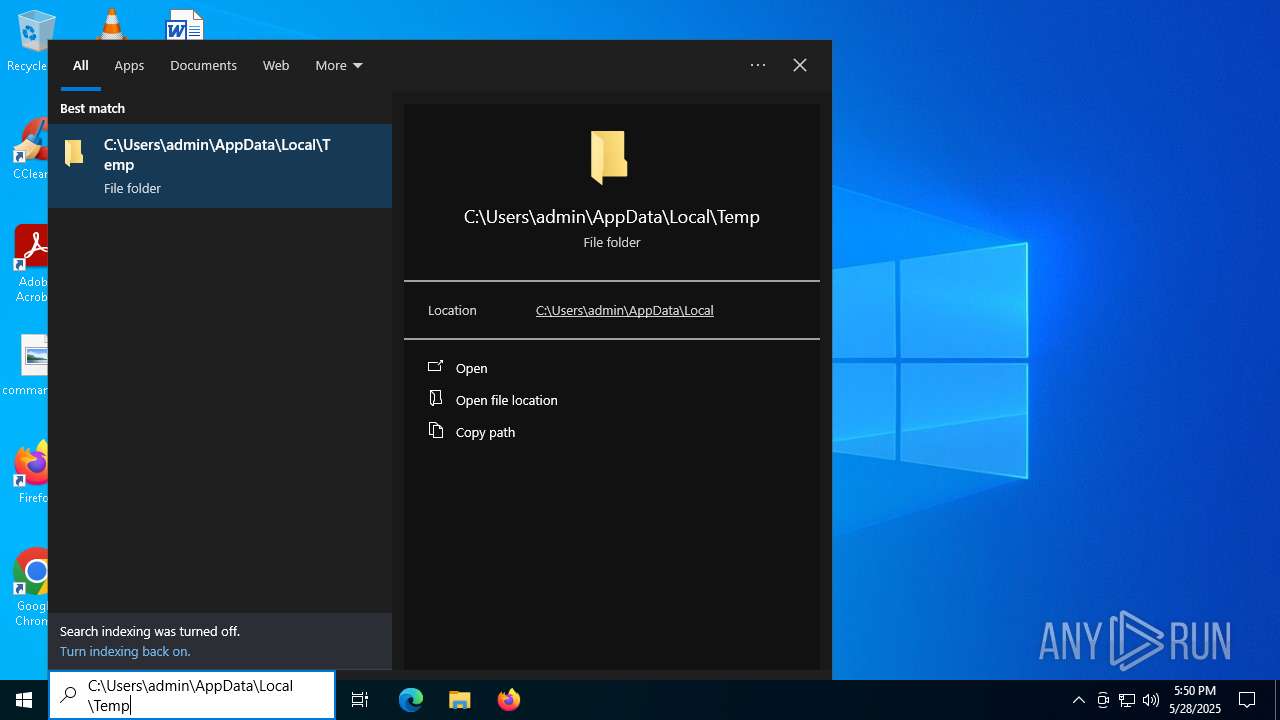
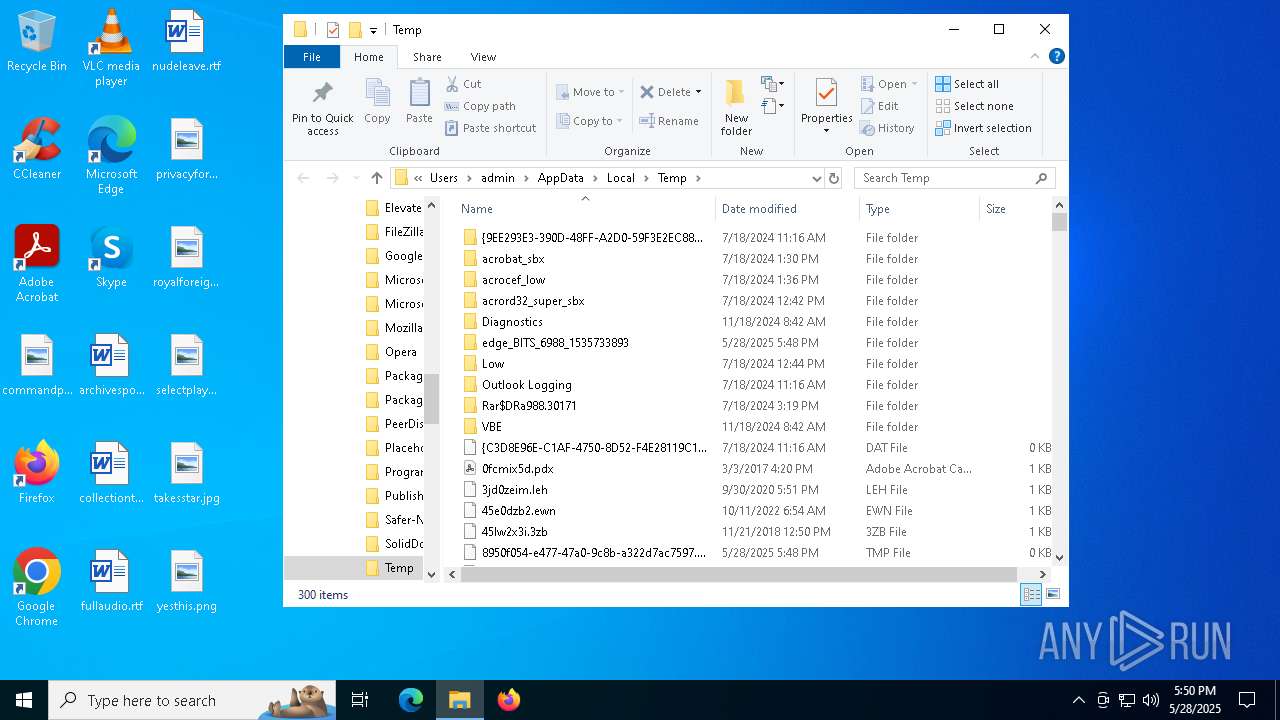
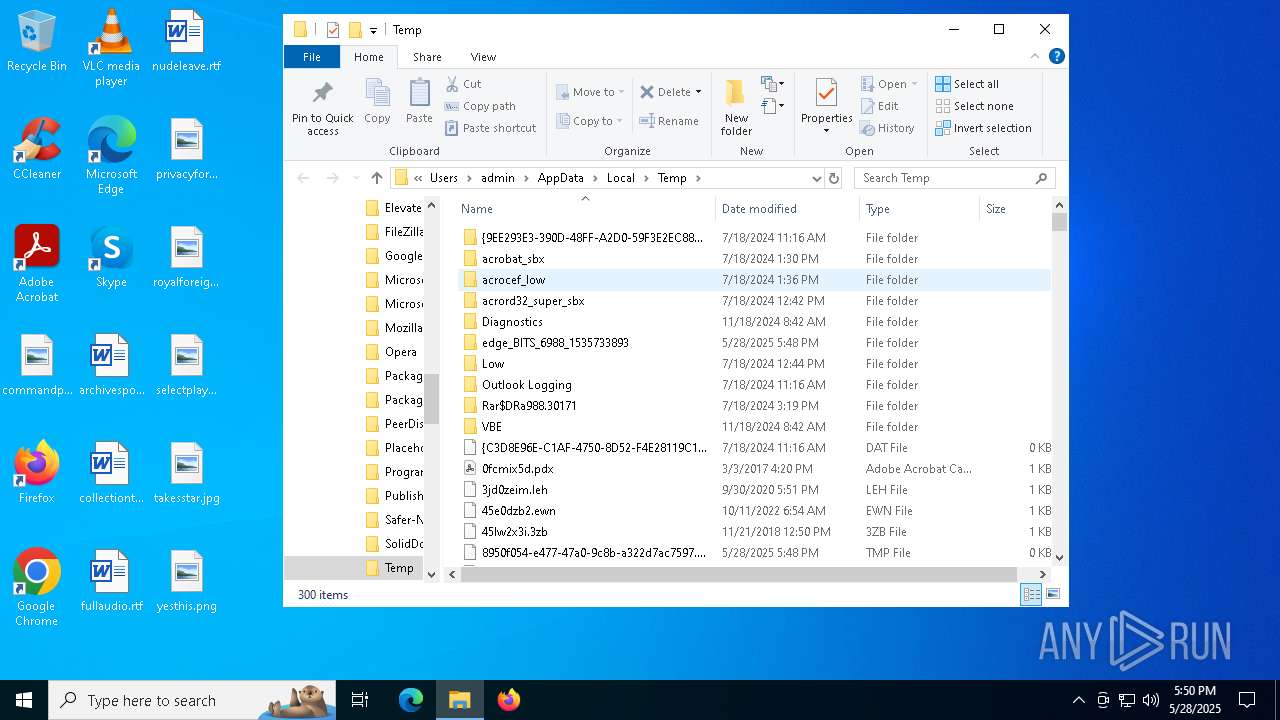
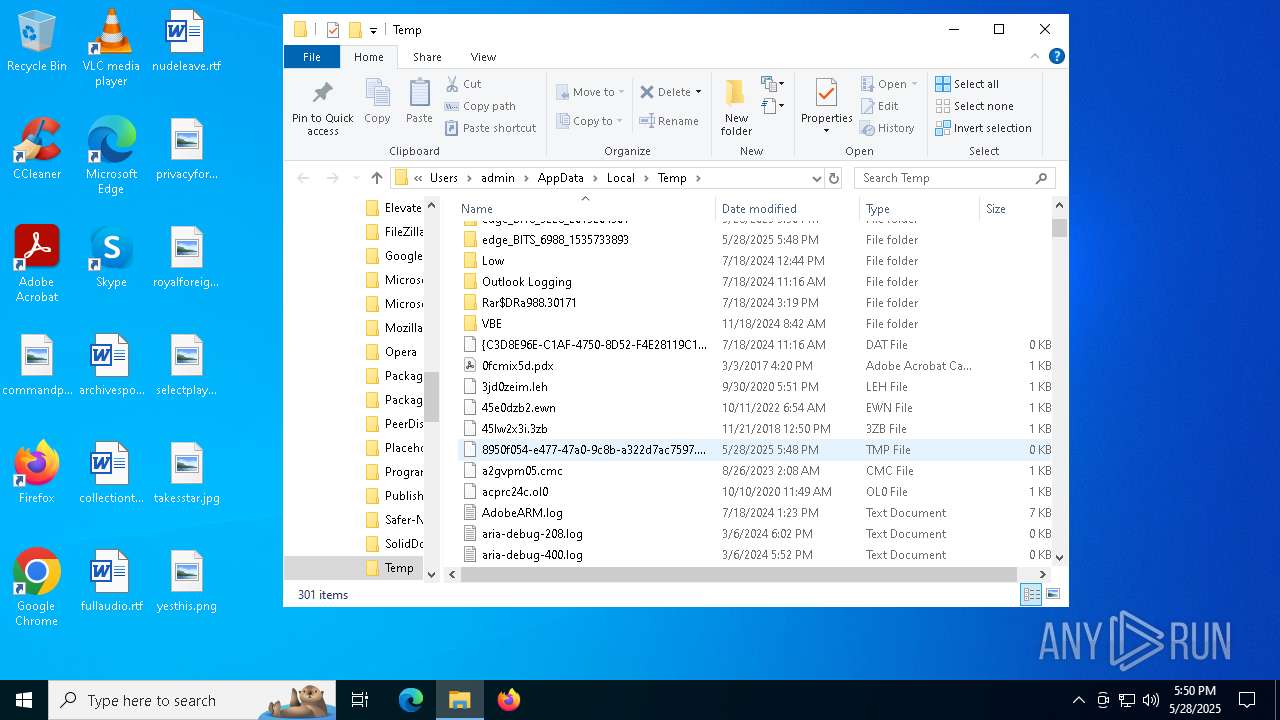
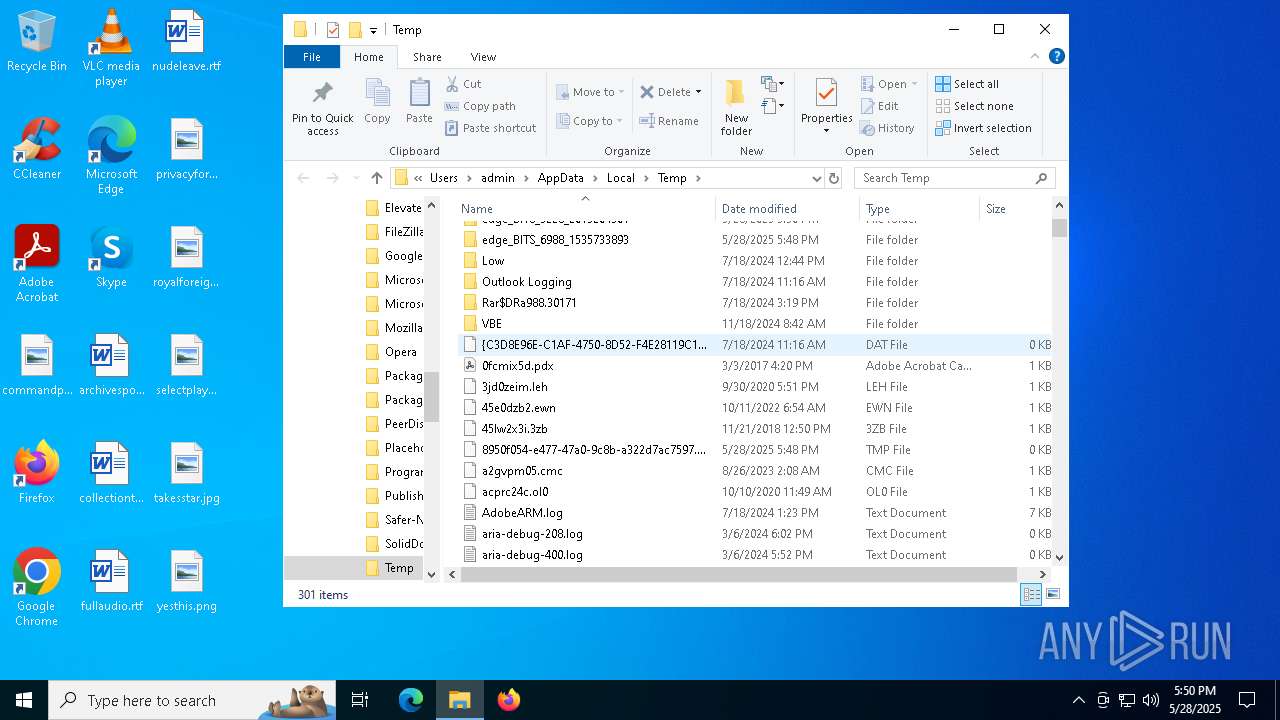
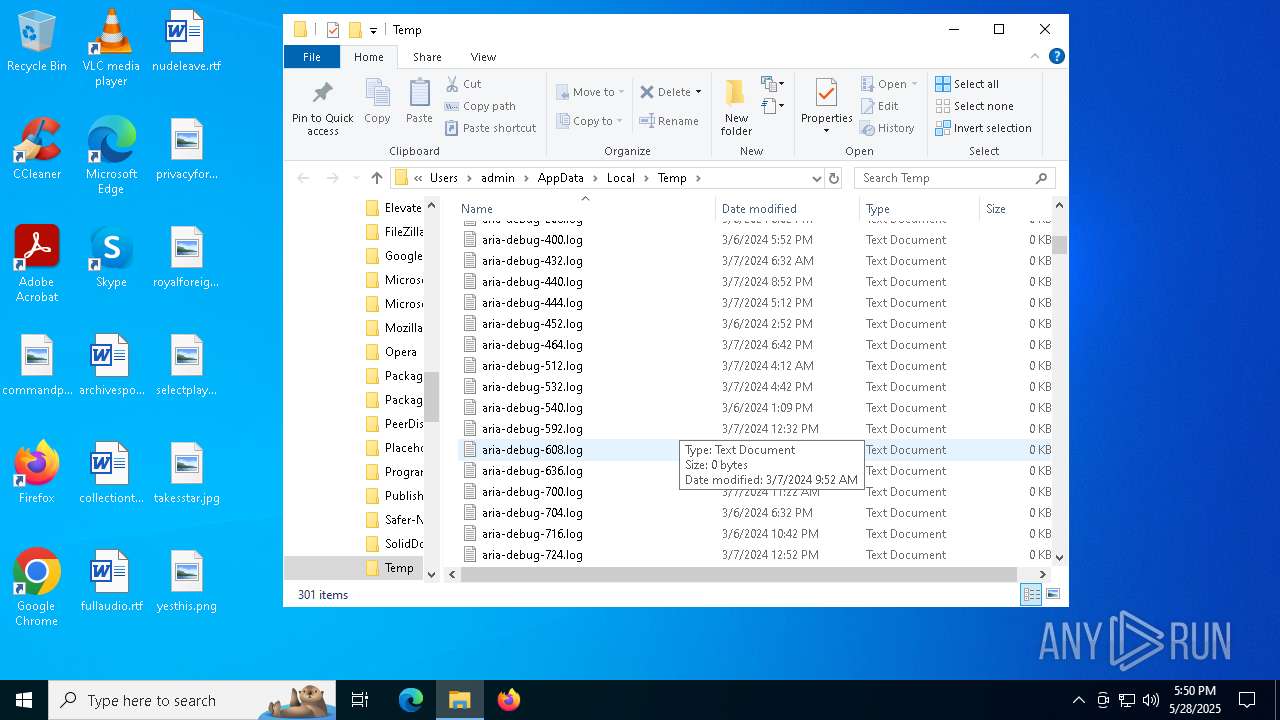
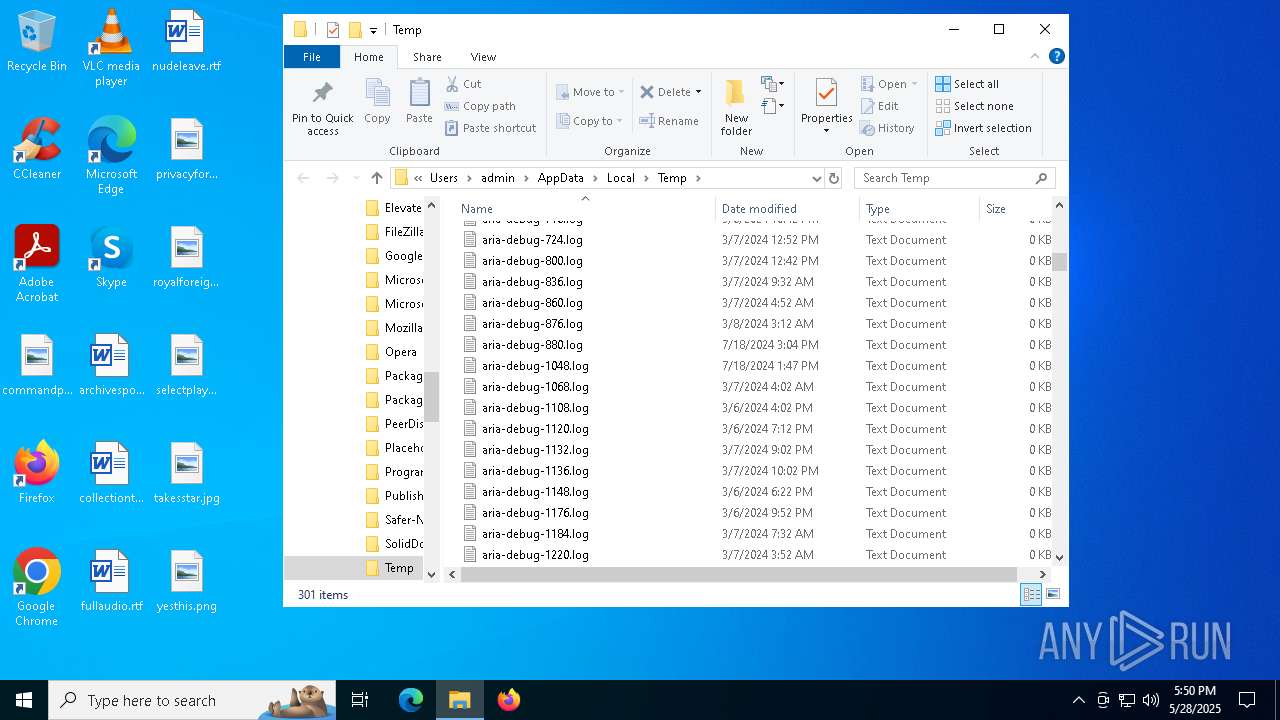
Create files in a temporary directory
- yWgZxtfPWjpOPZk_temp.exe (PID: 744)
Process checks computer location settings
- yWgZxtfPWjpOPZk_temp.exe (PID: 744)
Changes the display of characters in the console
- cmd.exe (PID: 7520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:05:28 14:06:33+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 5184000 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4f38ae |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | yWgZxtfPWjpOPZk_temp.exe |
| LegalCopyright: | |
| OriginalFileName: | yWgZxtfPWjpOPZk_temp.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
211
Monitored processes
79
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --disable-quic --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=8028 --field-trial-handle=2416,i,3288281946879670032,9914987804367339873,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 728 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 744 | "C:\Users\admin\AppData\Local\Temp\yWgZxtfPWjpOPZk_temp.exe" | C:\Users\admin\AppData\Local\Temp\yWgZxtfPWjpOPZk_temp.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5028 --field-trial-handle=2428,i,10757034443913936727,14864732045907845237,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 896 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1012 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4064 --field-trial-handle=2428,i,10757034443913936727,14864732045907845237,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5664 --field-trial-handle=2416,i,3288281946879670032,9914987804367339873,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1128 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6980 --field-trial-handle=2416,i,3288281946879670032,9914987804367339873,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1240 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4176 --field-trial-handle=2428,i,10757034443913936727,14864732045907845237,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1272 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6808 --field-trial-handle=2416,i,3288281946879670032,9914987804367339873,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
15 496
Read events
15 407
Write events
88
Delete events
1
Modification events
| (PID) Process: | (744) yWgZxtfPWjpOPZk_temp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\yWgZxtfPWjpOPZk_temp_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (744) yWgZxtfPWjpOPZk_temp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\yWgZxtfPWjpOPZk_temp_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (744) yWgZxtfPWjpOPZk_temp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\yWgZxtfPWjpOPZk_temp_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (744) yWgZxtfPWjpOPZk_temp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\yWgZxtfPWjpOPZk_temp_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (744) yWgZxtfPWjpOPZk_temp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\yWgZxtfPWjpOPZk_temp_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (744) yWgZxtfPWjpOPZk_temp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\yWgZxtfPWjpOPZk_temp_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (744) yWgZxtfPWjpOPZk_temp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\yWgZxtfPWjpOPZk_temp_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (744) yWgZxtfPWjpOPZk_temp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\yWgZxtfPWjpOPZk_temp_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (744) yWgZxtfPWjpOPZk_temp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\yWgZxtfPWjpOPZk_temp_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (744) yWgZxtfPWjpOPZk_temp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\yWgZxtfPWjpOPZk_temp_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
759
Text files
194
Unknown types
48
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1350f2.TMP | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135101.TMP | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135140.TMP | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF13515f.TMP | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135140.TMP | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
174
DNS requests
197
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4896 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4896 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7800 | svchost.exe | HEAD | 200 | 208.89.74.29:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1748968374&P2=404&P3=2&P4=akX65IPzFH3EnAso%2fa17zG8A9Jg236vnRKUY1B5S8Wnw5nyV855ok8NK2qsNH1eBPjACwnc%2fqoNLLZoJwuCW3w%3d%3d | unknown | — | — | whitelisted |
7800 | svchost.exe | GET | 206 | 208.89.74.29:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1748968374&P2=404&P3=2&P4=akX65IPzFH3EnAso%2fa17zG8A9Jg236vnRKUY1B5S8Wnw5nyV855ok8NK2qsNH1eBPjACwnc%2fqoNLLZoJwuCW3w%3d%3d | unknown | — | — | whitelisted |
7800 | svchost.exe | GET | 206 | 208.89.74.29:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1748968374&P2=404&P3=2&P4=akX65IPzFH3EnAso%2fa17zG8A9Jg236vnRKUY1B5S8Wnw5nyV855ok8NK2qsNH1eBPjACwnc%2fqoNLLZoJwuCW3w%3d%3d | unknown | — | — | whitelisted |
7800 | svchost.exe | GET | 206 | 208.89.74.29:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1748968374&P2=404&P3=2&P4=akX65IPzFH3EnAso%2fa17zG8A9Jg236vnRKUY1B5S8Wnw5nyV855ok8NK2qsNH1eBPjACwnc%2fqoNLLZoJwuCW3w%3d%3d | unknown | — | — | whitelisted |
7800 | svchost.exe | GET | 206 | 208.89.74.29:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1748968374&P2=404&P3=2&P4=akX65IPzFH3EnAso%2fa17zG8A9Jg236vnRKUY1B5S8Wnw5nyV855ok8NK2qsNH1eBPjACwnc%2fqoNLLZoJwuCW3w%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2560 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7360 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
744 | yWgZxtfPWjpOPZk_temp.exe | 147.185.221.28:49723 | modified-sentences.gl.at.ply.gg | PLAYIT-GG | US | suspicious |
744 | yWgZxtfPWjpOPZk_temp.exe | 195.201.57.90:443 | ipwho.is | Hetzner Online GmbH | DE | malicious |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
modified-sentences.gl.at.ply.gg |
| unknown |
ipwho.is |
| malicious |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |
2196 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES Tunneling Service in DNS Lookup (* .ply .gg) |
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected domain Associated with Malware Distribution (.ply .gg) |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO External IP Lookup Domain in DNS Lookup (ipwho .is) |