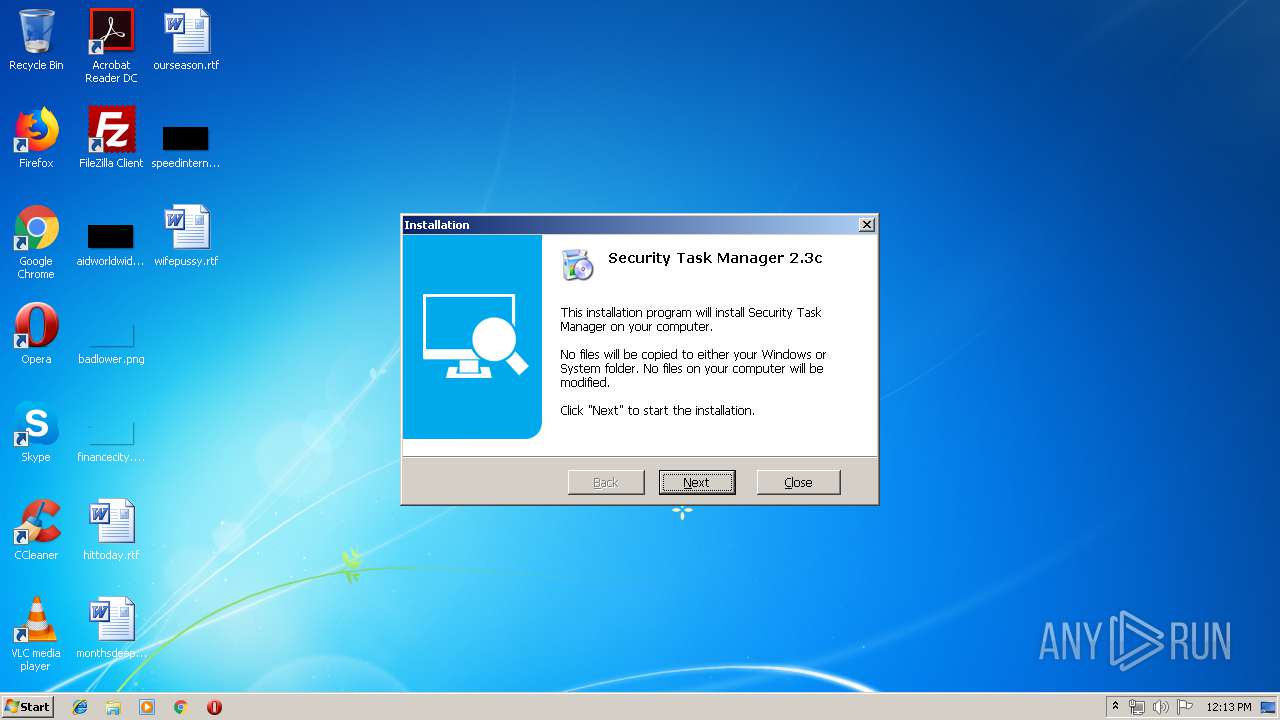
| File name: | SecurityTaskManager_Setup.exe |
| Full analysis: | https://app.any.run/tasks/657a23b3-05f3-4229-891b-8ce7fde937ad |
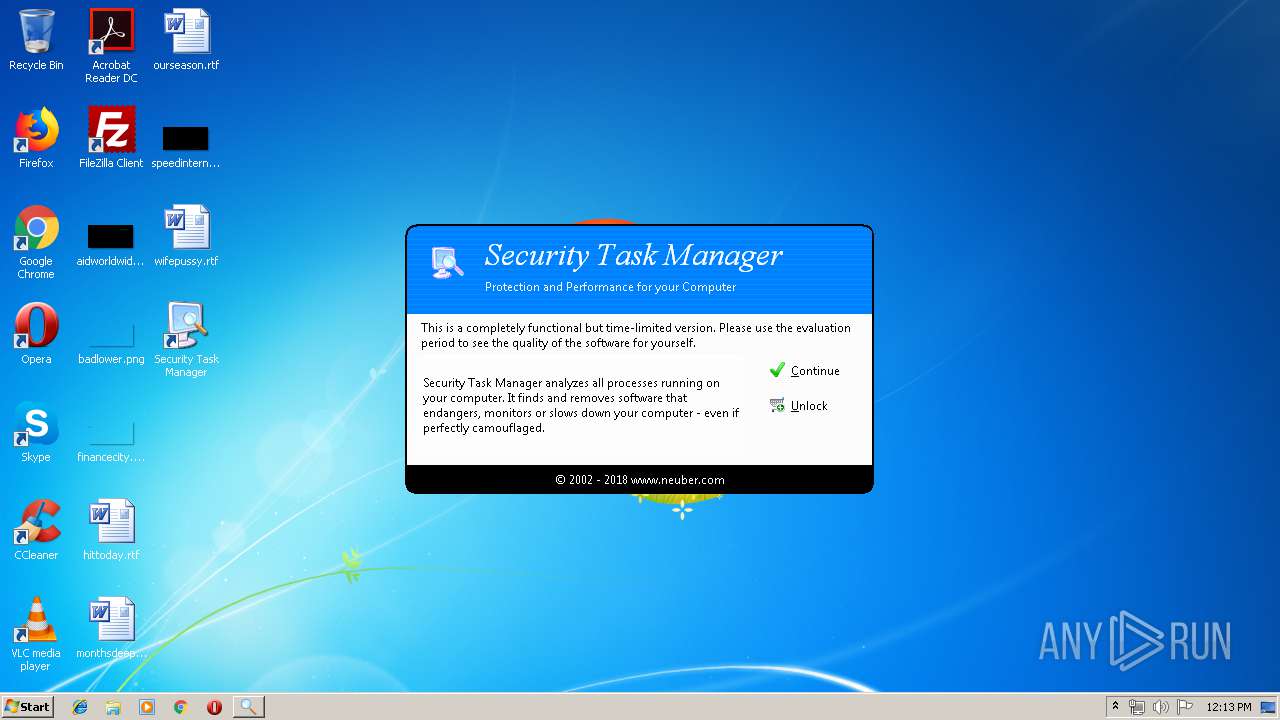
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2019, 11:12:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FA13E018D324BB73E1FE41423CF33257 |
| SHA1: | 454C9B9A380A216D1186F1B7B9CFB87B6D7DDBEB |
| SHA256: | 07115D2C2819C1963B646B58D97BCDE9FA16D4E86073C5EB087FF36661A52E15 |
| SSDEEP: | 49152:1B+H1XcROVf1pe2h9ubGOK/5+kQdKmltavtaKhGiD79l+90X:1B+mROVdpe2zAYxvQcscg6939l+k |
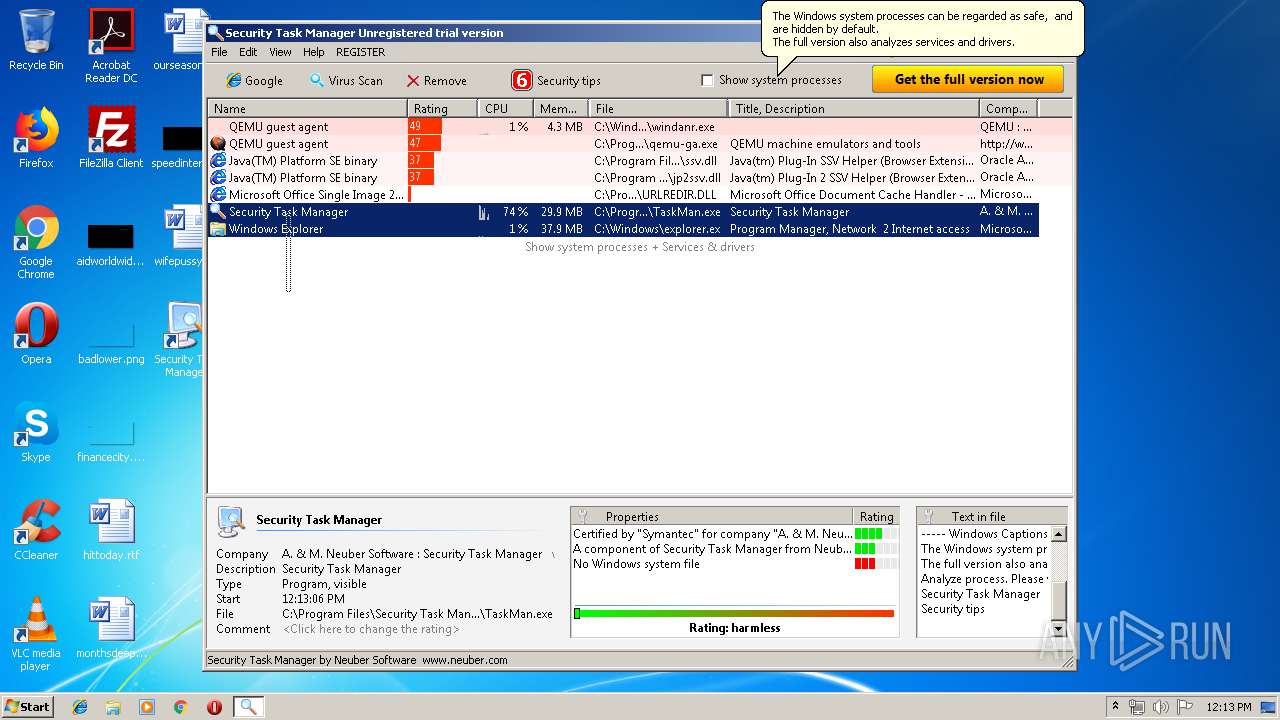
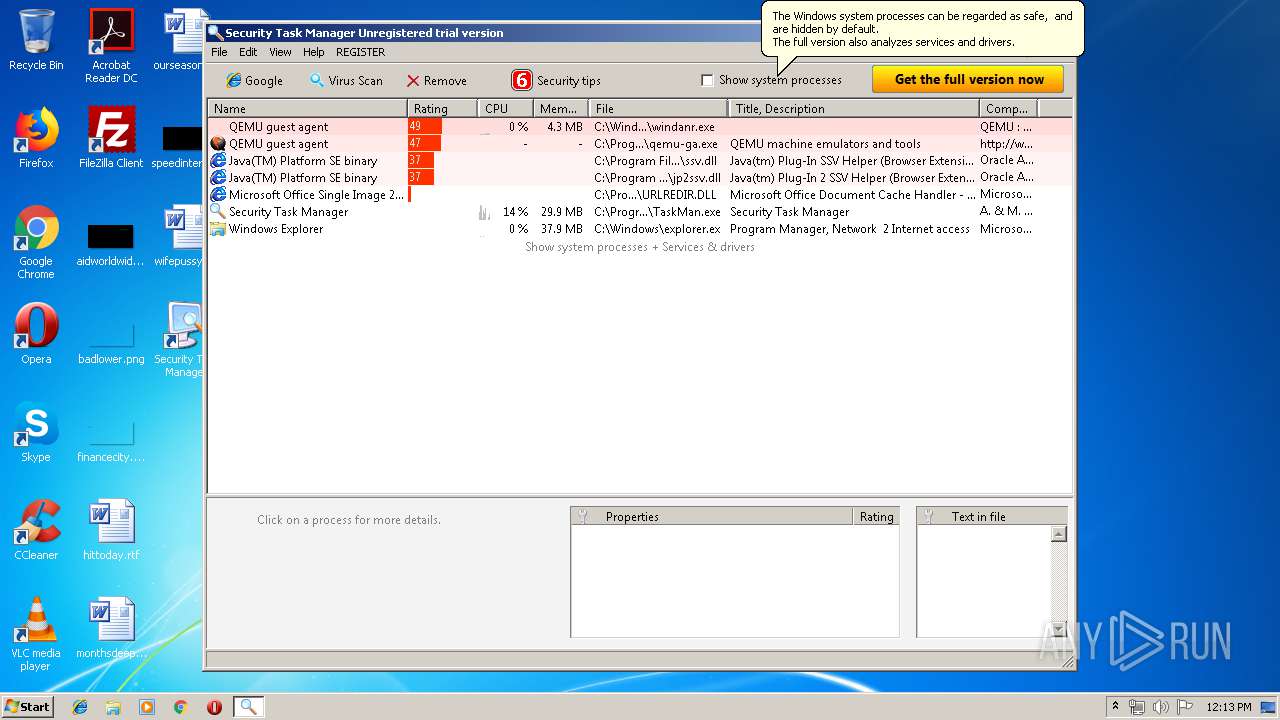
MALICIOUS
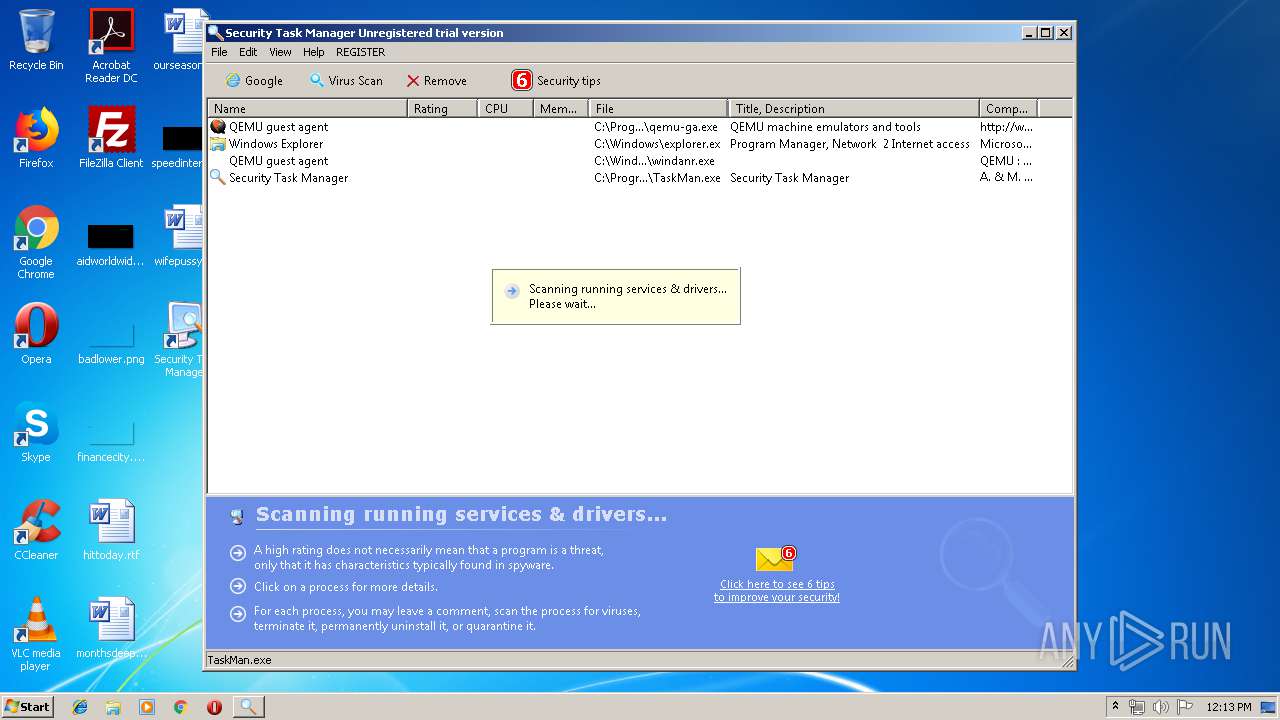
Application was dropped or rewritten from another process
- setup.exe (PID: 2300)
- TaskMan.exe (PID: 3092)
Loads dropped or rewritten executable
- explorer.exe (PID: 2044)
- ctfmon.exe (PID: 3780)
- TaskMan.exe (PID: 3092)
Loads the Task Scheduler COM API
- TaskMan.exe (PID: 3092)
SUSPICIOUS
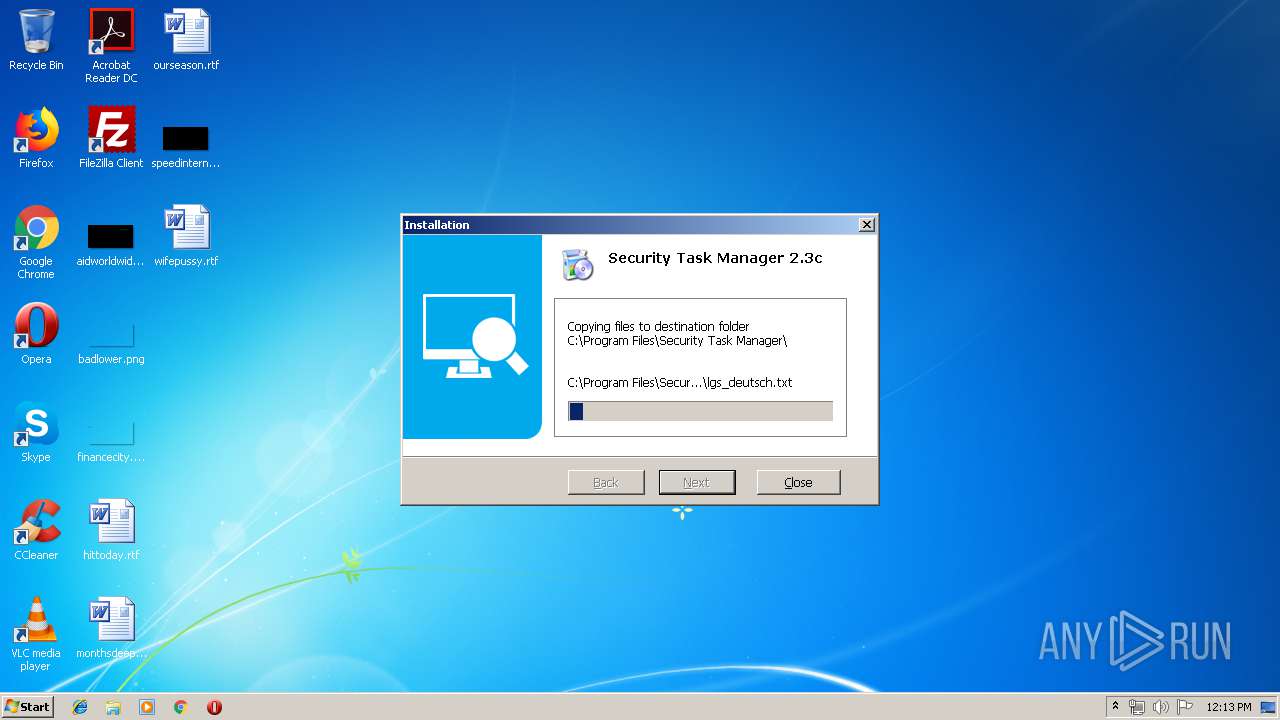
Executable content was dropped or overwritten
- SecurityTaskManager_Setup.exe (PID: 2084)
- setup.exe (PID: 2300)
Creates files in the program directory
- setup.exe (PID: 2300)
- TaskMan.exe (PID: 3092)
Creates a software uninstall entry
- setup.exe (PID: 2300)
Creates files in the user directory
- TaskMan.exe (PID: 3092)
Searches for installed software
- TaskMan.exe (PID: 3092)
INFO
Reads settings of System Certificates
- TaskMan.exe (PID: 3092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (32.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (28.5) |
| .exe | | | Winzip Win32 self-extracting archive (generic) (23.7) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.7) |
| .exe | | | Win32 Executable (generic) (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:02:24 16:50:34+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 77824 |
| InitializedDataSize: | 65536 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaf1e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Feb-2009 15:50:34 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 24-Feb-2009 15:50:34 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00012775 | 0x00013000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50181 |
.rdata | 0x00014000 | 0x00003822 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.98659 |
.data | 0x00018000 | 0x0000E6E4 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.97272 |
.rsrc | 0x00027000 | 0x0000976C | 0x0000A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.54785 |
_winzip_ | 0x00031000 | 0x002BA000 | 0x002BA000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 7.99955 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.82954 | 989 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.03621 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.14459 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.56342 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.99214 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 3.69605 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.83382 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 6.01045 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 4.68735 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
63 | 3.18826 | 764 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
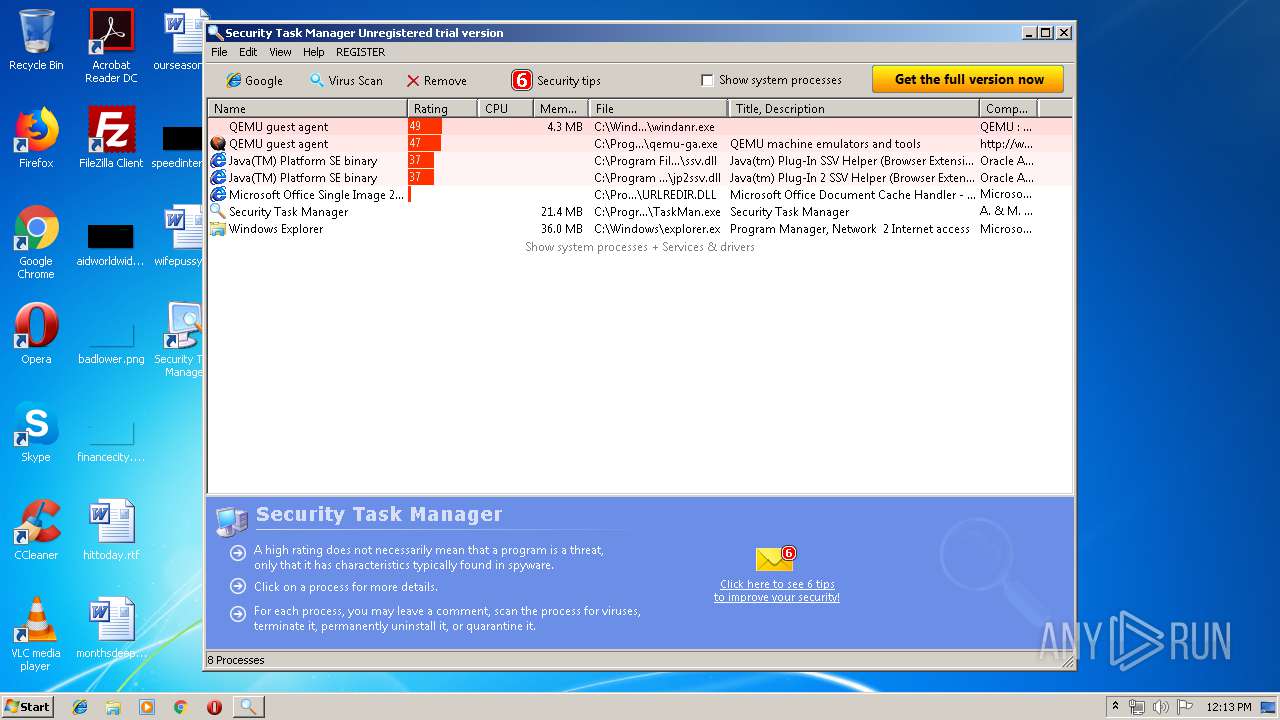
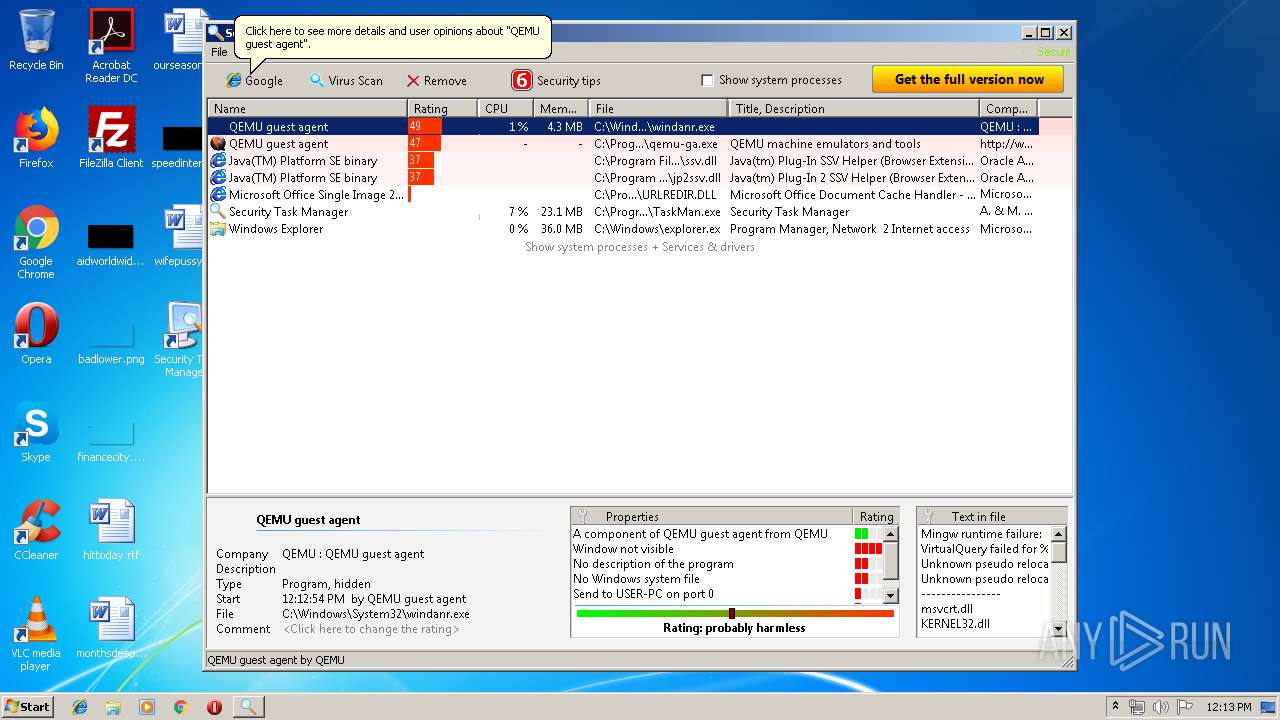
Total processes
42
Monitored processes
8
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
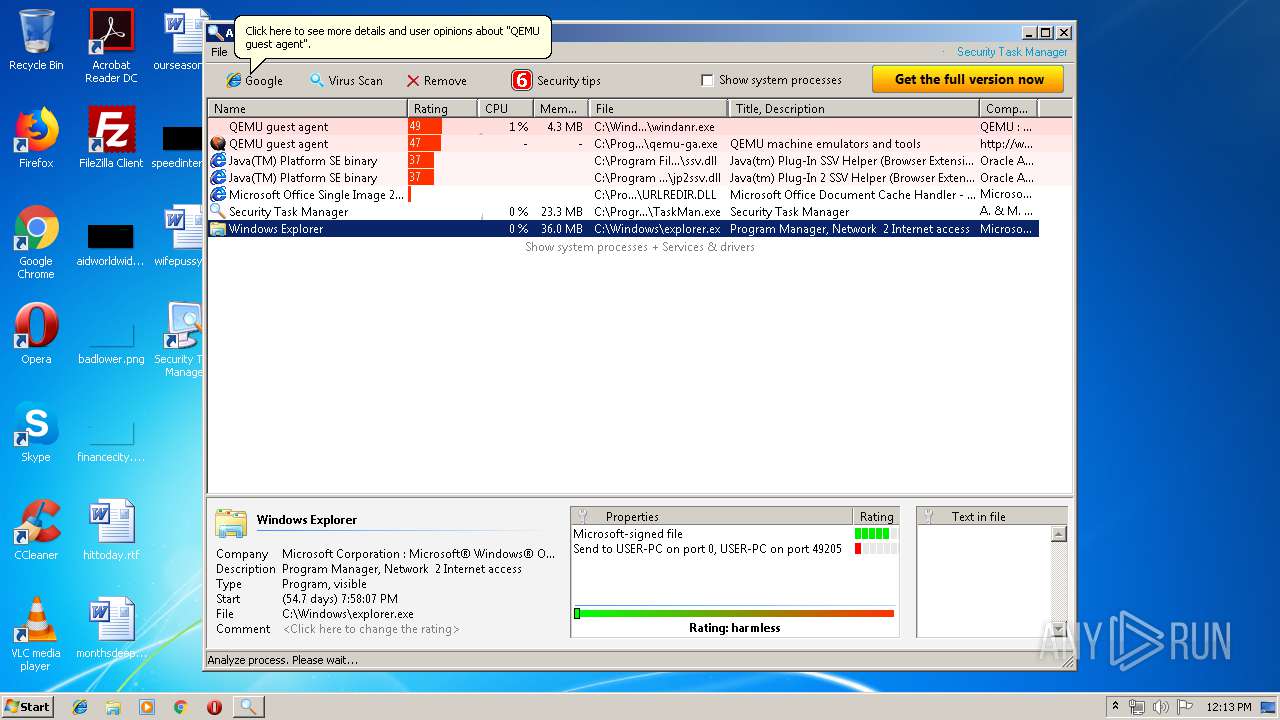
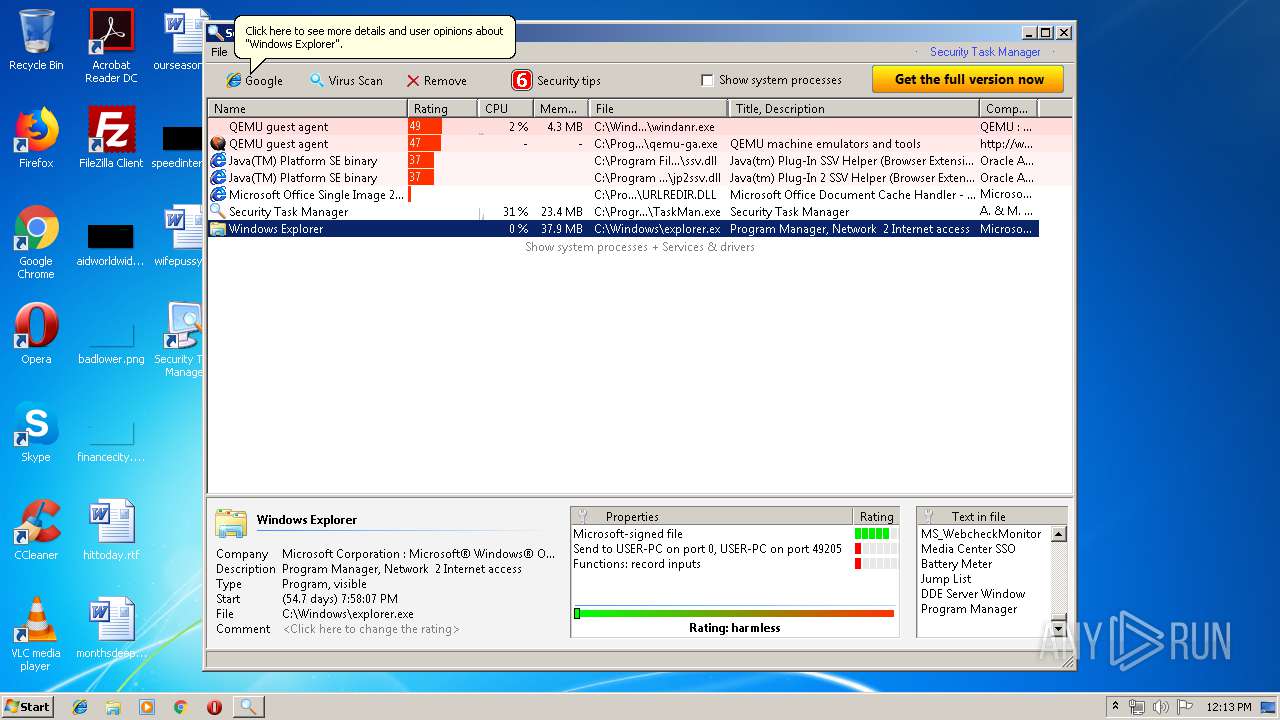
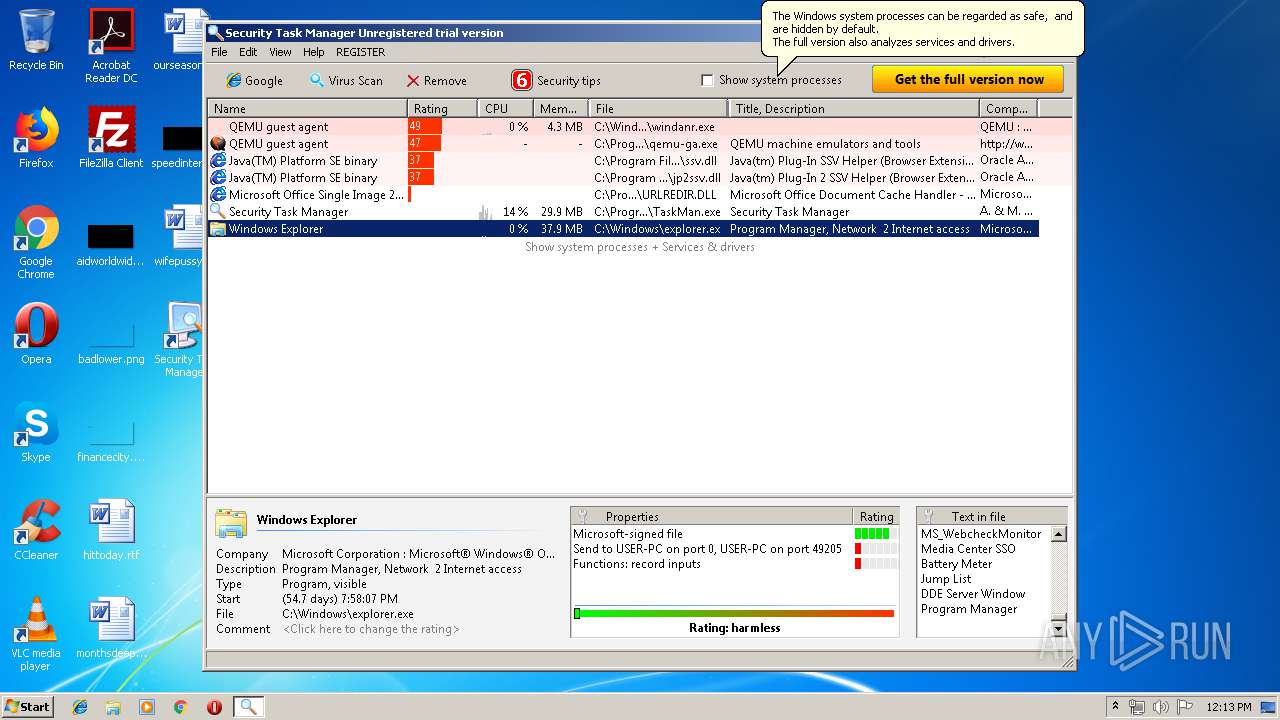
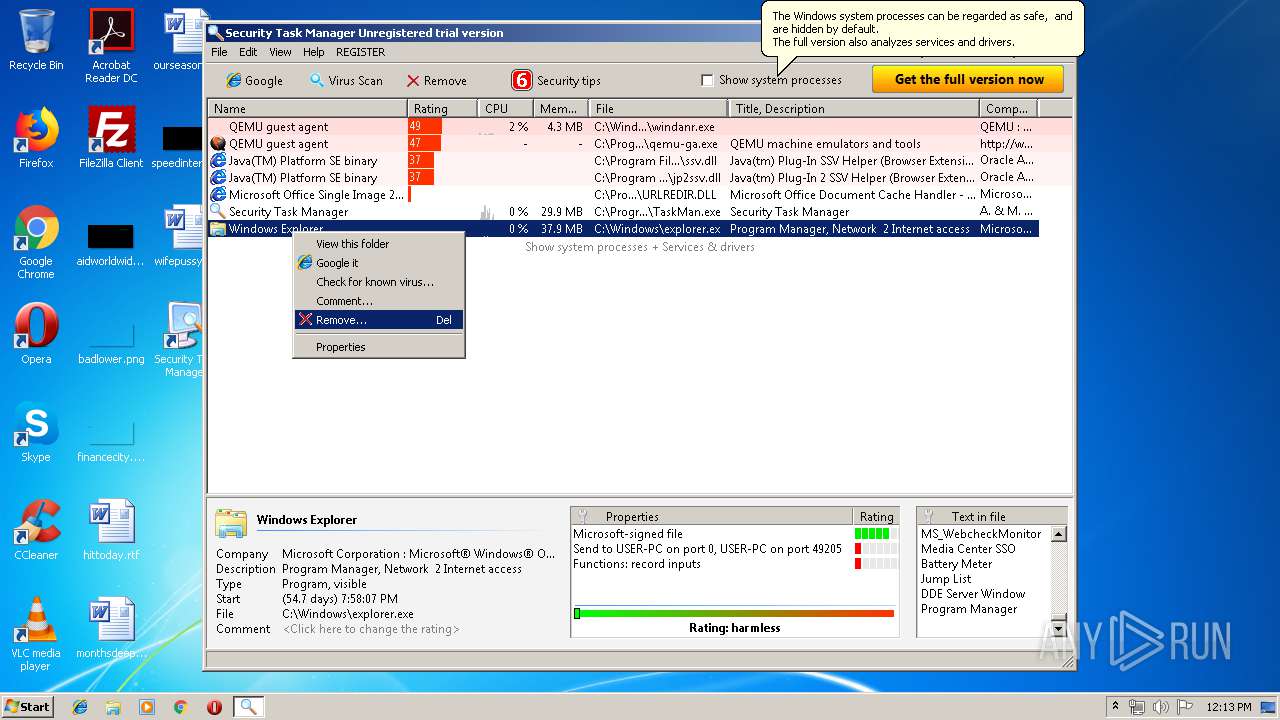
| 324 | C:\Windows\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2044 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
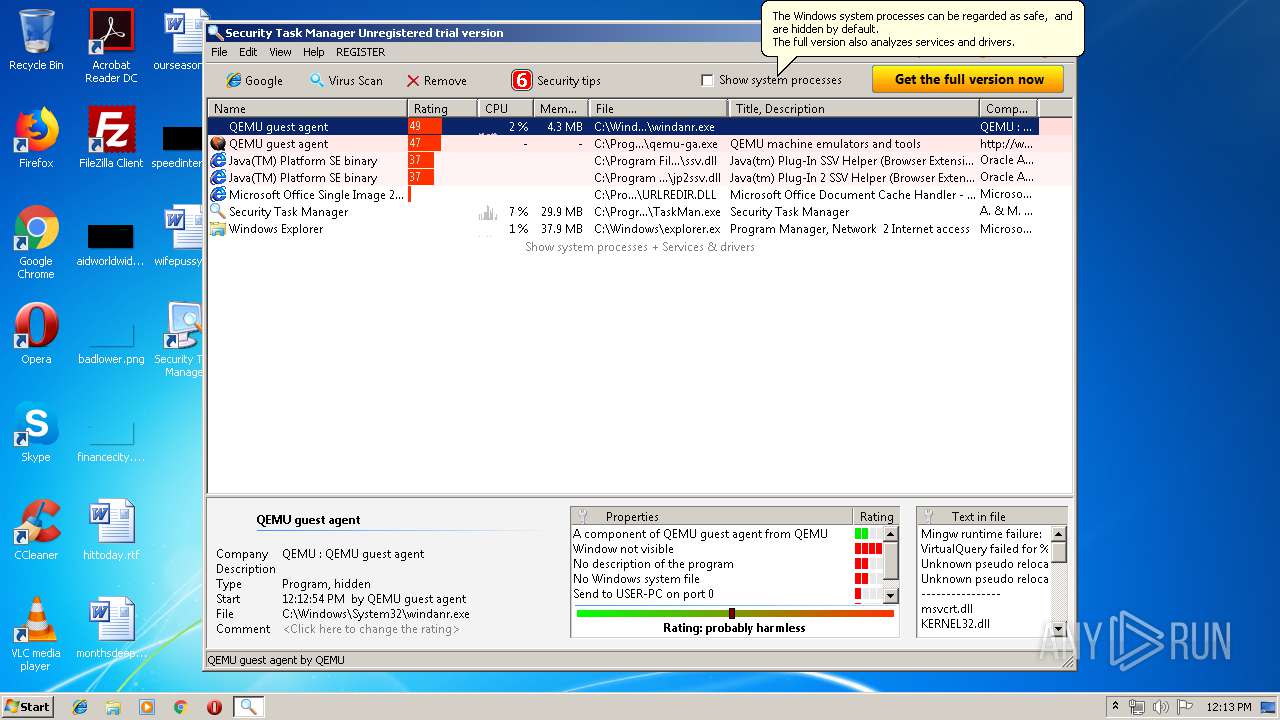
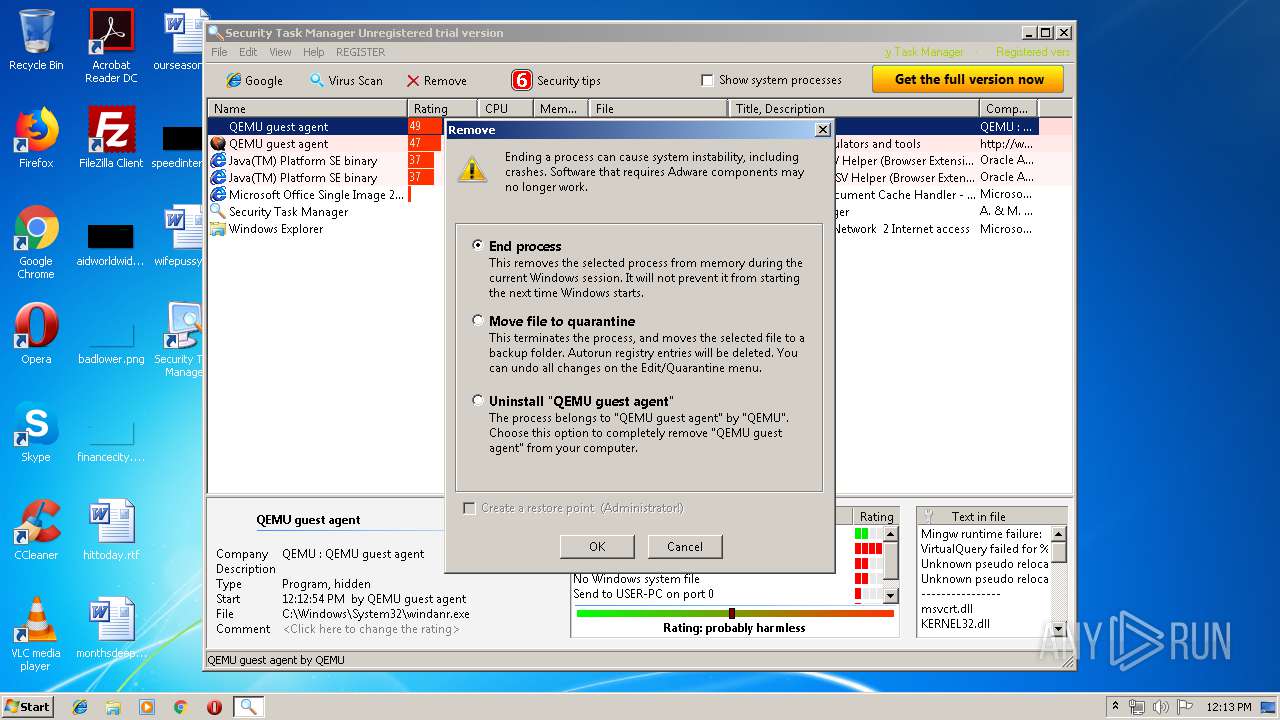
| 2084 | "C:\Users\admin\AppData\Local\Temp\SecurityTaskManager_Setup.exe" | C:\Users\admin\AppData\Local\Temp\SecurityTaskManager_Setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2300 | ".\setup.exe" | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\setup.exe | SecurityTaskManager_Setup.exe | ||||||||||||
User: admin Company: Neuber Software Integrity Level: HIGH Description: Setup program Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
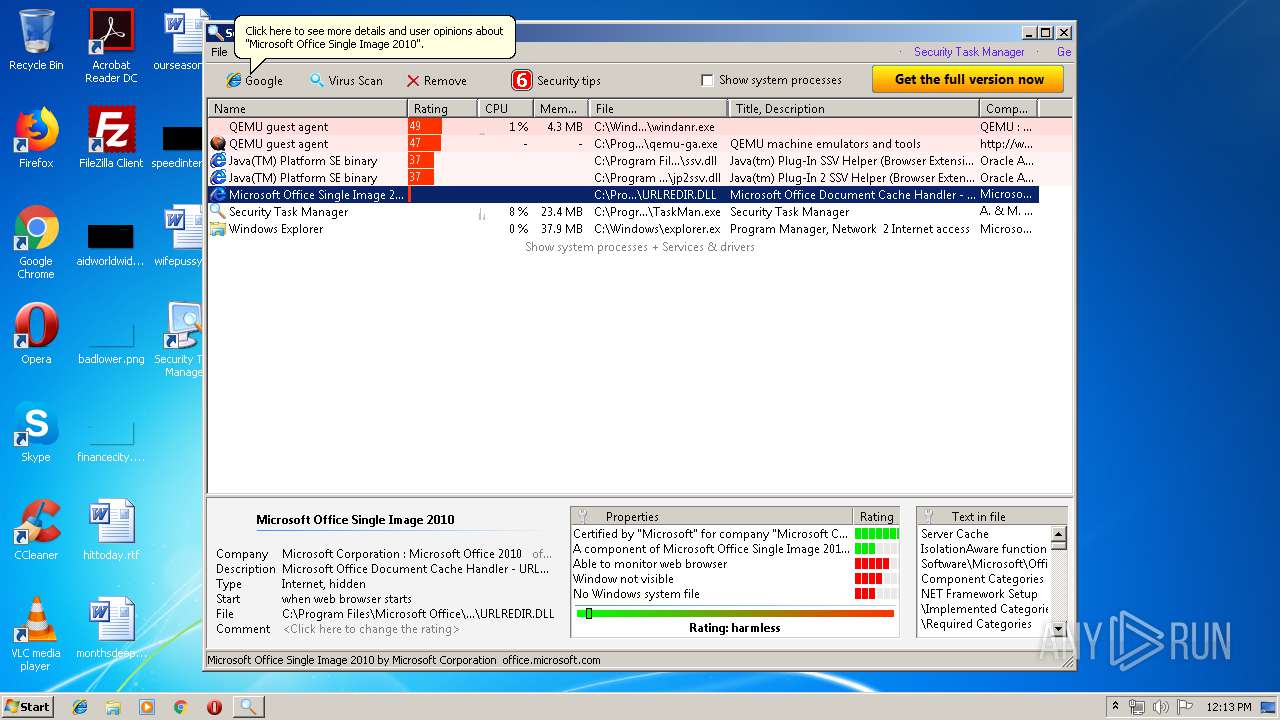
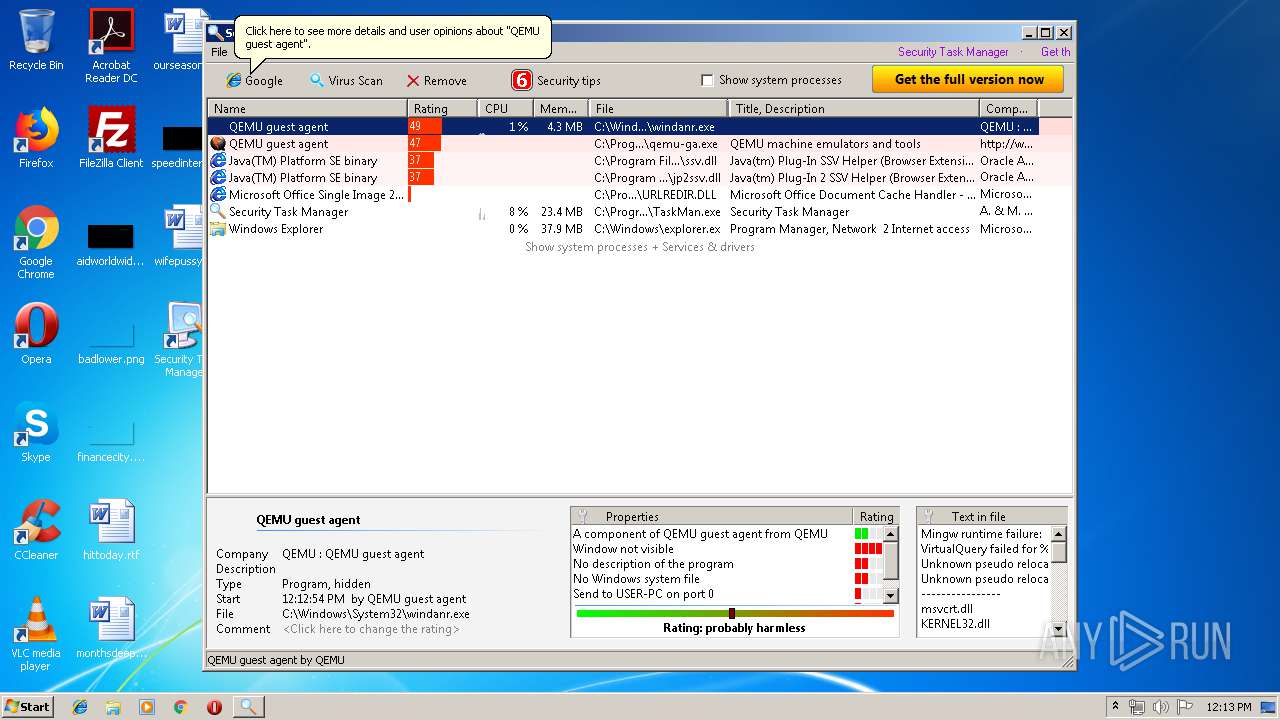
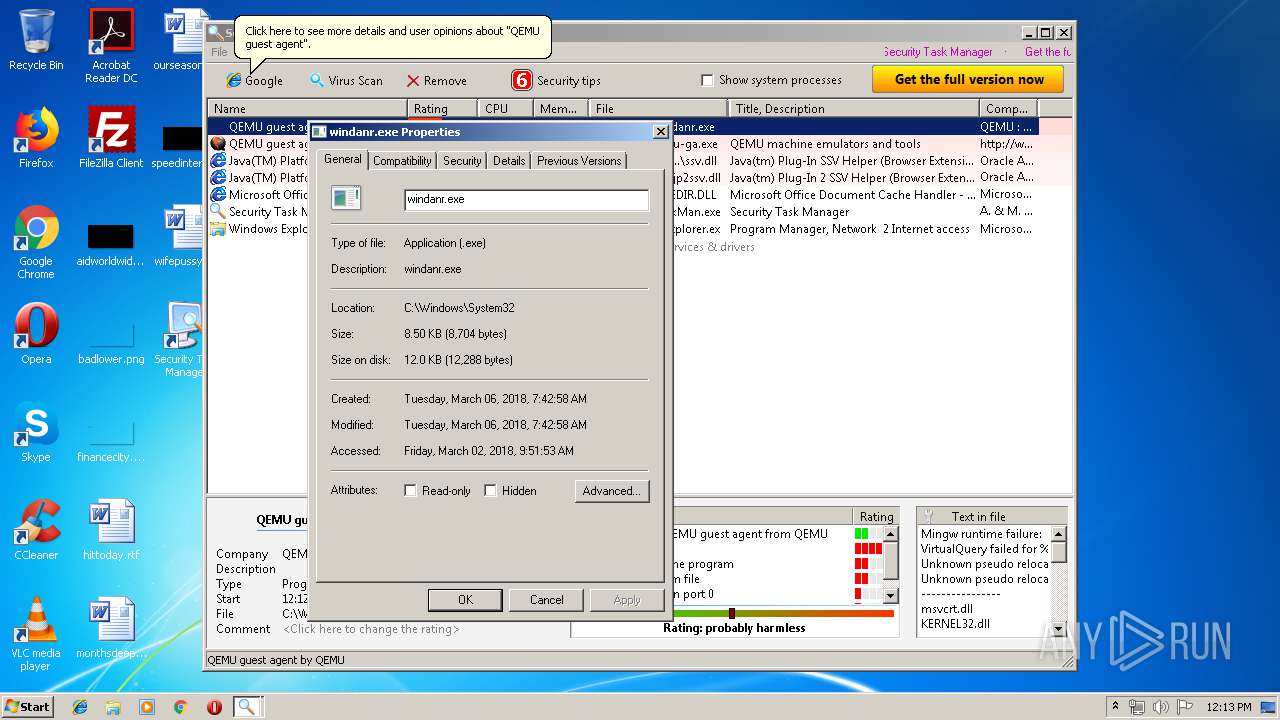
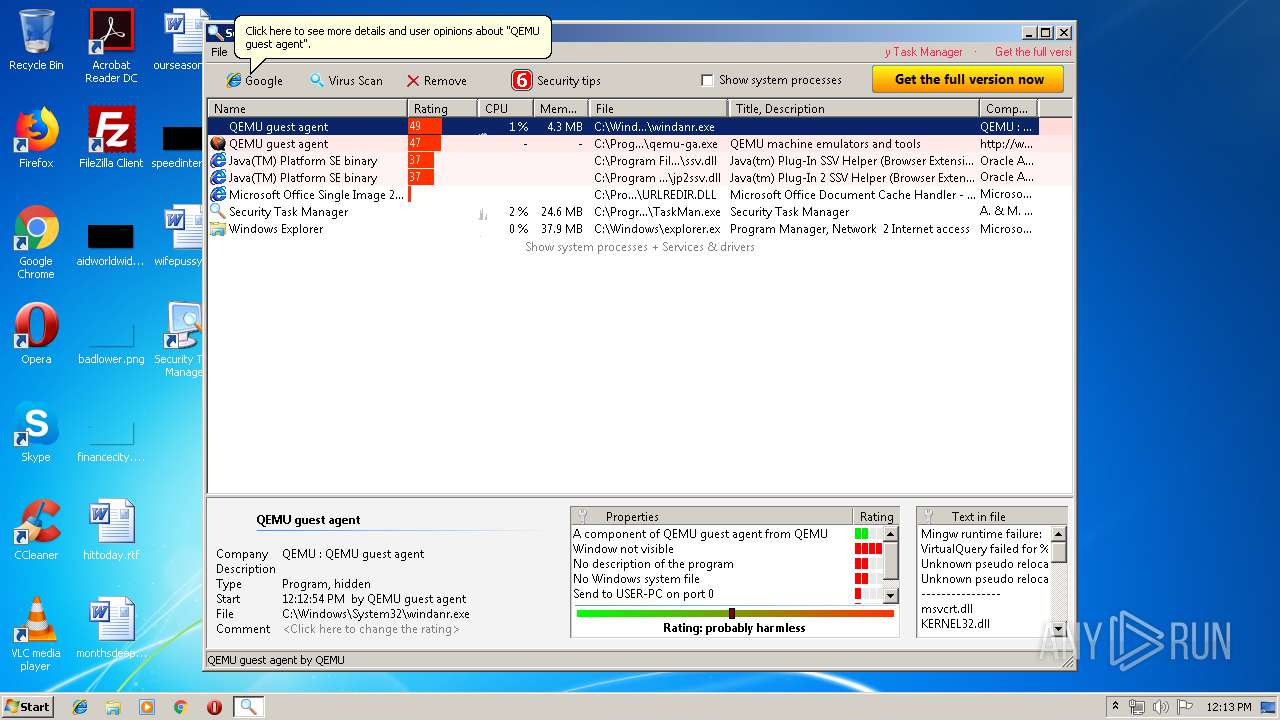
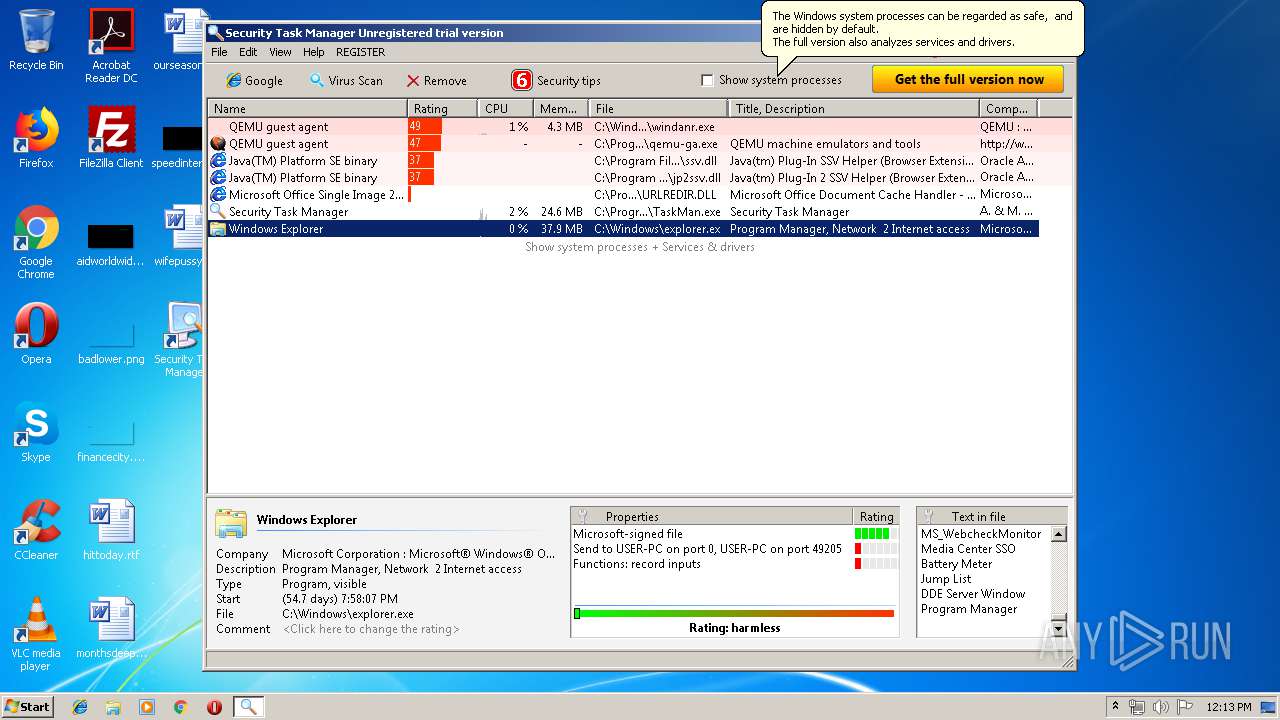
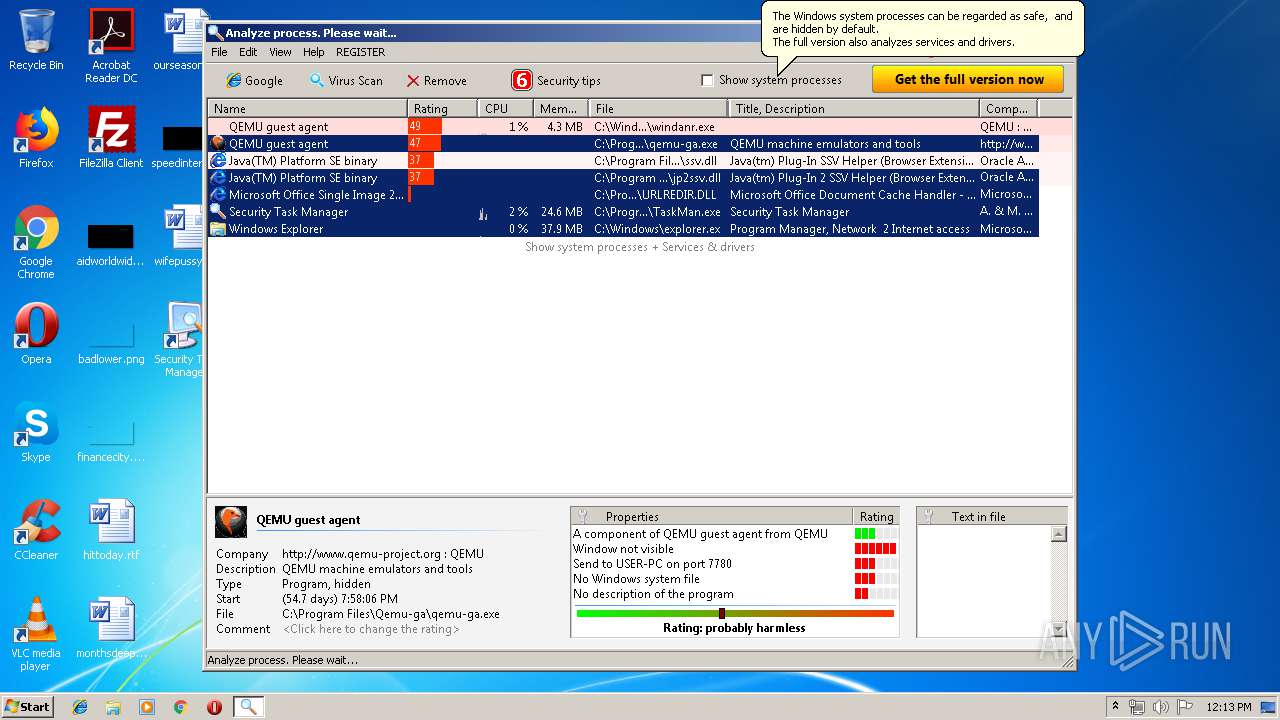
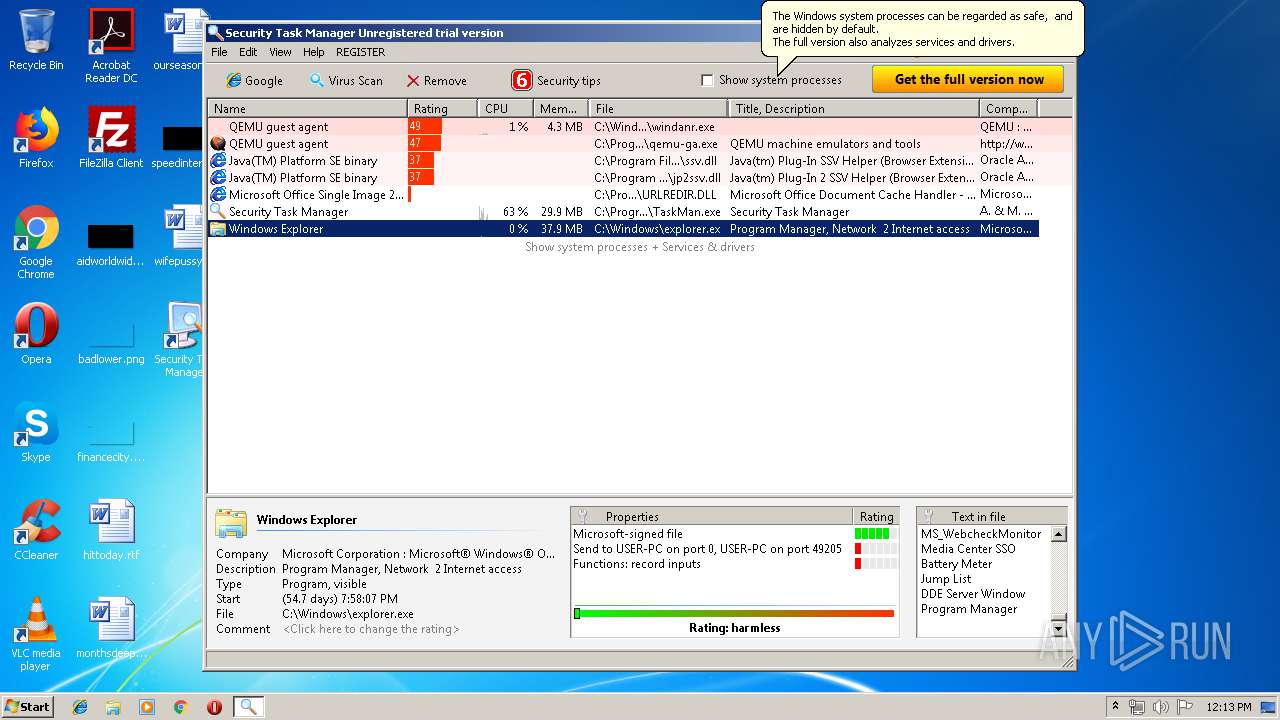
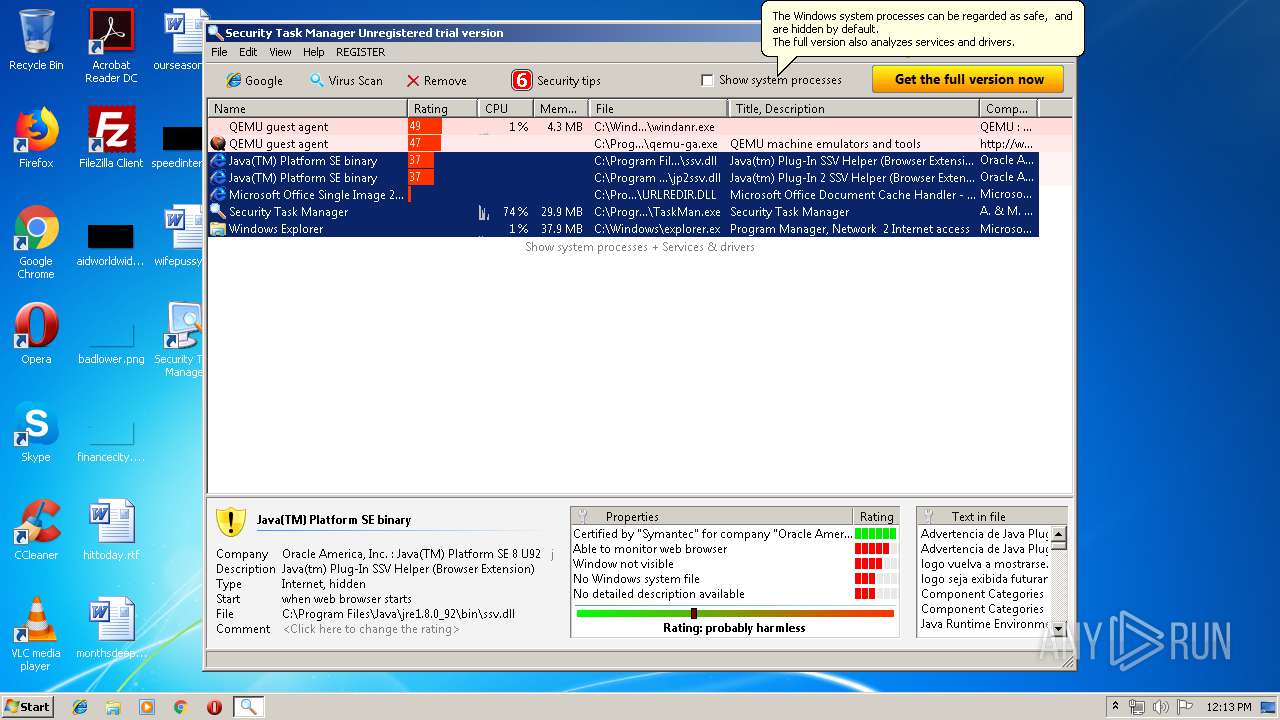
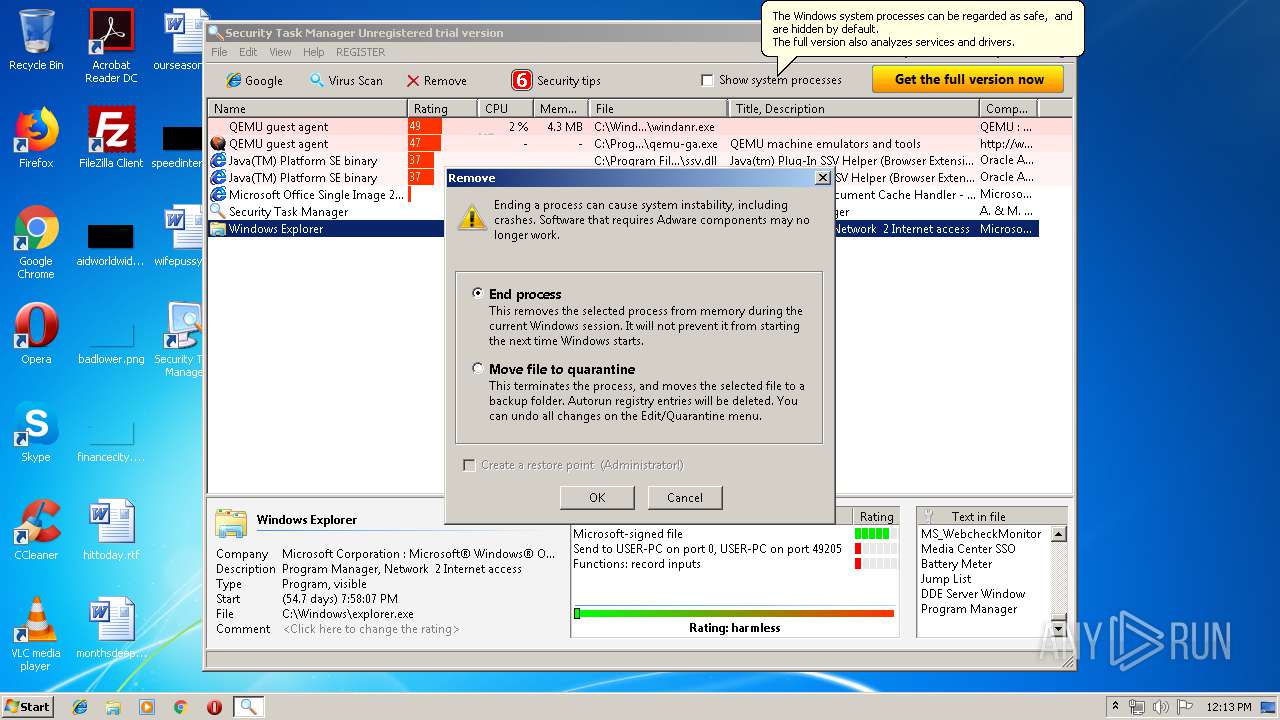
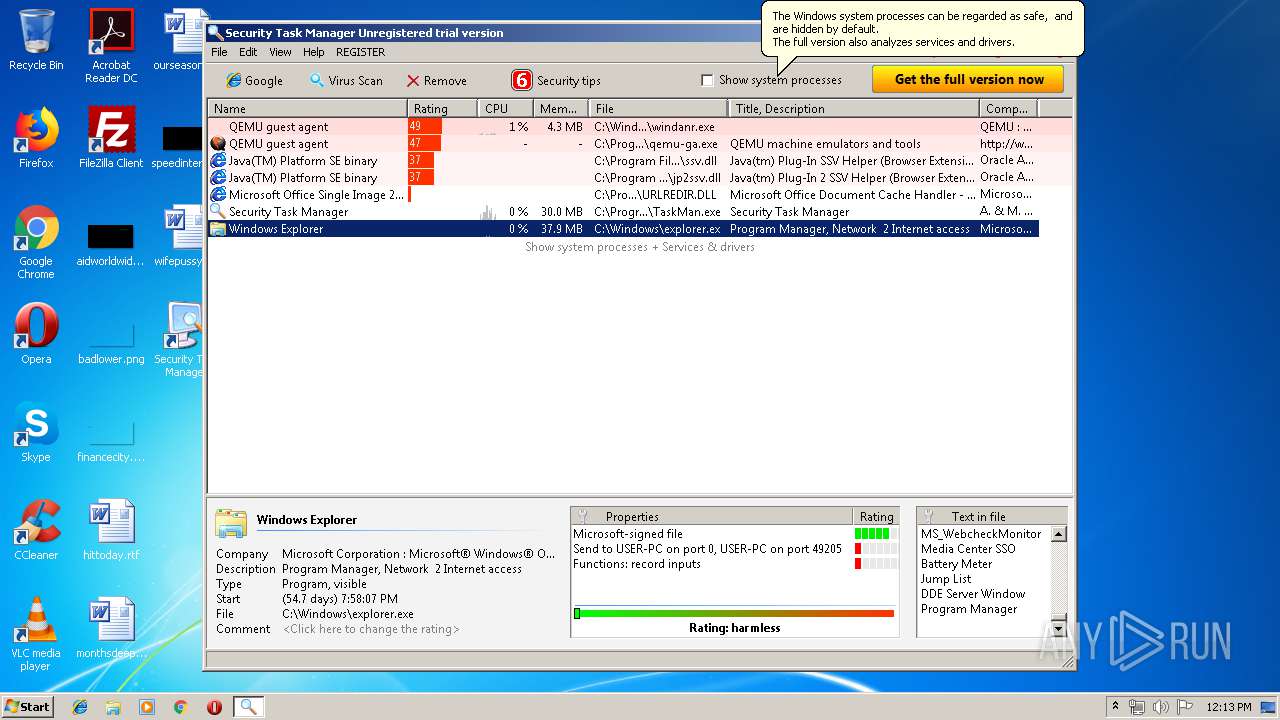
| 3092 | "C:\Program Files\Security Task Manager\TaskMan.exe" | C:\Program Files\Security Task Manager\TaskMan.exe | — | explorer.exe | |||||||||||
User: admin Company: Neuber Software Integrity Level: MEDIUM Description: Security Task Manager Exit code: 0 Version: 2.3.2.0 Modules
| |||||||||||||||
| 3556 | "C:\Windows\explorer.exe" "C:\Program Files\Security Task Manager\taskman.exe" | C:\Windows\explorer.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3696 | "C:\Users\admin\AppData\Local\Temp\SecurityTaskManager_Setup.exe" | C:\Users\admin\AppData\Local\Temp\SecurityTaskManager_Setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3780 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 118
Read events
2 911
Write events
201
Delete events
6
Modification events
| (PID) Process: | (2044) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\FrphevglGnfxZnantre_Frghc.rkr |
Value: 000000000000000000000000B5010000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (2044) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000050000000500000076E100000300000003000000BD6800004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000360200000000BCE8360201000000000000000000577690E836027CE636025E7CFB76BCE83602787CFB76030000008A018C01AC413400ACE63602F77CFB760100000090E83602847CFB76FCE63602F0E6360208E73602000000000000000000000000F8E6360290E8360200000000000000000000000030E8360230E836020000000001000000BCE8360230E83602B2FEFB76F270FB7685FCFB7695B635759A7CFA76AC413400A27EFA7674E83602180000004CFA3602006FFA7600000000000000005CE836023C003E00BCE83602C34E5200FCE6360200000000D8462B000000360258E7360244EA360200000088C8000000C8000000C8000000C8000000E20201000000000000008168B8F35703010600400000000030EA3602105381687FEB51762000000011000000B8452C00B0452C000000000044EA360200000000E4E70000630E855B94E7360282918075E4E7360298E736022795807500000000B45DE702C0E73602CD948075B45DE7026CE836022859E702E1948075000000002859E7026CE83602C8E736020300000003000000BD6800004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000360200000000BCE8360201000000000000000000577690E836027CE636025E7CFB76BCE83602787CFB76030000008A018C01AC413400ACE63602F77CFB760100000090E83602847CFB76FCE63602F0E6360208E73602000000000000000000000000F8E6360290E8360200000000000000000000000030E8360230E836020000000001000000BCE8360230E83602B2FEFB76F270FB7685FCFB7695B635759A7CFA76AC413400A27EFA7674E83602180000004CFA3602006FFA7600000000000000005CE836023C003E00BCE83602C34E5200FCE6360200000000D8462B000000360258E7360244EA360200000088C8000000C8000000C8000000C8000000E20201000000000000008168B8F35703010600400000000030EA3602105381687FEB51762000000011000000B8452C00B0452C000000000044EA360200000000E4E70000630E855B94E7360282918075E4E7360298E736022795807500000000B45DE702C0E73602CD948075B45DE7026CE836022859E702E1948075000000002859E7026CE83602C8E736020300000003000000BD6800004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000360200000000BCE8360201000000000000000000577690E836027CE636025E7CFB76BCE83602787CFB76030000008A018C01AC413400ACE63602F77CFB760100000090E83602847CFB76FCE63602F0E6360208E73602000000000000000000000000F8E6360290E8360200000000000000000000000030E8360230E836020000000001000000BCE8360230E83602B2FEFB76F270FB7685FCFB7695B635759A7CFA76AC413400A27EFA7674E83602180000004CFA3602006FFA7600000000000000005CE836023C003E00BCE83602C34E5200FCE6360200000000D8462B000000360258E7360244EA360200000088C8000000C8000000C8000000C8000000E20201000000000000008168B8F35703010600400000000030EA3602105381687FEB51762000000011000000B8452C00B0452C000000000044EA360200000000E4E70000630E855B94E7360282918075E4E7360298E736022795807500000000B45DE702C0E73602CD948075B45DE7026CE836022859E702E1948075000000002859E7026CE83602C8E73602 | |||
| (PID) Process: | (2300) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Security Task Manager |
| Operation: | write | Name: | DisplayName |
Value: Security Task Manager 2.3c | |||
| (PID) Process: | (2300) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Security Task Manager |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\Security Task Manager\Uninstal.exe | |||
| (PID) Process: | (2300) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Security Task Manager |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Security Task Manager\ | |||
| (PID) Process: | (2300) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Security Task Manager |
| Operation: | write | Name: | UninstallPath |
Value: C:\Program Files\Security Task Manager\ | |||
| (PID) Process: | (2300) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Security Task Manager |
| Operation: | write | Name: | Publisher |
Value: Neuber Software | |||
| (PID) Process: | (2300) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Security Task Manager |
| Operation: | write | Name: | VersionMajor |
Value: 2 | |||
| (PID) Process: | (2300) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Security Task Manager |
| Operation: | write | Name: | VersionMinor |
Value: 3 | |||
| (PID) Process: | (2300) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Security Task Manager |
| Operation: | write | Name: | Contact |
Value: info@neuber.com | |||
Executable files
16
Suspicious files
64
Text files
94
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2084 | SecurityTaskManager_Setup.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\file_id.diz | text | |
MD5:— | SHA256:— | |||
| 2084 | SecurityTaskManager_Setup.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\liesmich.txt | text | |
MD5:— | SHA256:— | |||
| 2084 | SecurityTaskManager_Setup.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\readme.txt | text | |
MD5:— | SHA256:— | |||
| 2084 | SecurityTaskManager_Setup.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\manual_en.pdf | ||
MD5:F8DC026AC75362E1E5E41469CDDAE40C | SHA256:D97AAD84FC29C2B71FF9D07C645BB1B3DB779412F5673F5BD37B55520710CBCE | |||
| 2084 | SecurityTaskManager_Setup.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\SpyProtector.exe | executable | |
MD5:FE1390FF004AA8FB73F403D603A93A54 | SHA256:C9D4CAE5805C82490FACF0BC7F6766B8DE645177566532376041AF3C4D1000B5 | |||
| 2084 | SecurityTaskManager_Setup.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\manual_de.pdf | ||
MD5:17BBDF9FC220E9EFFACAA5A76CF4B688 | SHA256:AF89A8B1030FAF760C16B66524F8A04188E49669FAA6F8123E2A4BF0ABAA75BC | |||
| 2084 | SecurityTaskManager_Setup.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\SpyProDll.dll | executable | |
MD5:642021C03975D907D65803AAE9EC3DEE | SHA256:0289FF37A7D4B6BD44AC96C714FE58329D4B1FDEA53F744AC3A5AE731236F87C | |||
| 2084 | SecurityTaskManager_Setup.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\Setup.exe | executable | |
MD5:694BA0B43CC2EC5055A7FFA3C4FC3AAE | SHA256:A771E2F459F171469C5EF3407034A7DDA4ECE86F5B4DB943CC728696DAAD6295 | |||
| 2084 | SecurityTaskManager_Setup.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\LisezMoi.txt | text | |
MD5:0637BCD4FCCF8D53C05C4935292D5289 | SHA256:00201A7697011646E1B8AECBD7AB8EE113EEF5D01F7DB4D9A3A594FBFE11CEC3 | |||
| 2084 | SecurityTaskManager_Setup.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\bestell.txt | text | |
MD5:481325E02BD95664323A5299DA4F8BFE | SHA256:D9B135D7C0B39E38FEF169306599F3F8B1A82D701424892969EA8C5D6E790777 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report