| File name: | 070f2306c458df667effc63ee3ab65f76a2f5c5b3208be9ff4539941a67a9b0d.doc |
| Full analysis: | https://app.any.run/tasks/428800fe-baab-4945-8ae1-b125815e6207 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 16:26:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 1EF9AD43E1117C6513EBBB6E936C66F2 |
| SHA1: | 98DFE78D777DBB92ADED57557FC8354F77446CE0 |
| SHA256: | 070F2306C458DF667EFFC63EE3AB65F76A2F5C5B3208BE9FF4539941A67A9B0D |
| SSDEEP: | 1536:/VS1D/ZZ8fV4LGSReoqQd5YFWAfV9AN7svtzTk7BD+DeHVI:/VY/ZZc4LR59YAAbs7svJQ7BD8eW |
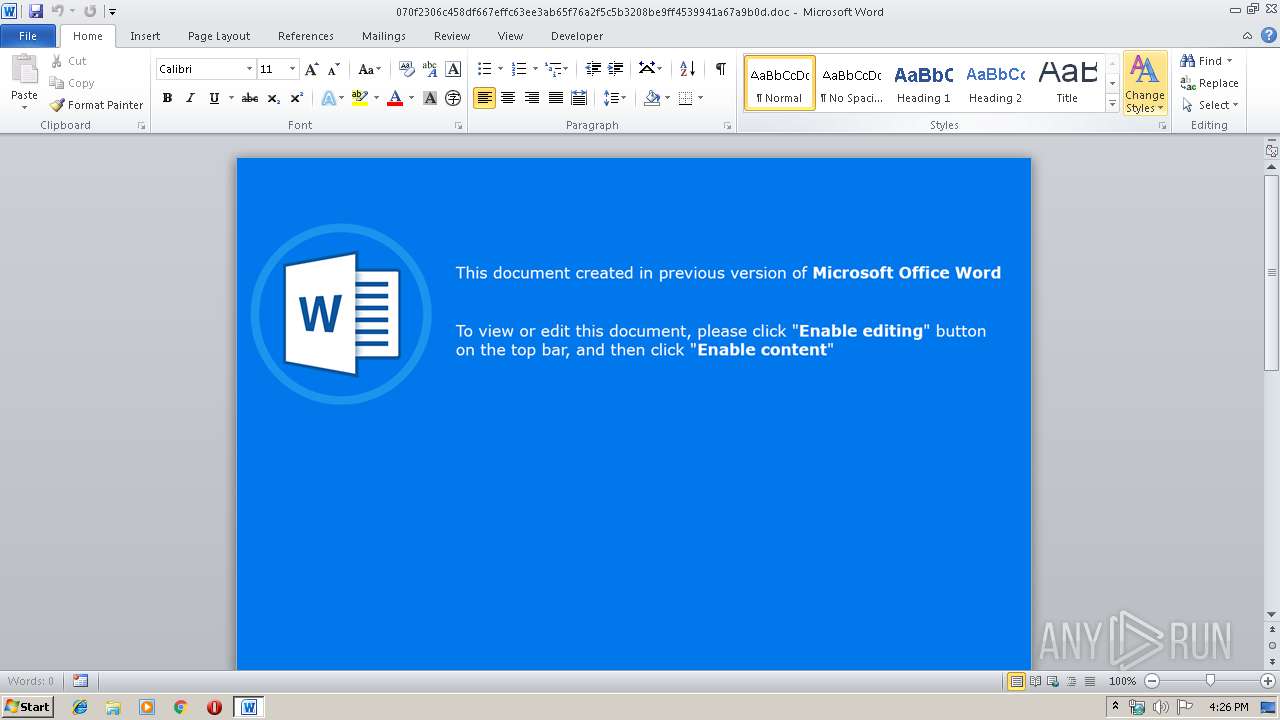
MALICIOUS
Uses WMIC.EXE to invoke XSL script
- WINWORD.EXE (PID: 640)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 640)
SUSPICIOUS
Creates files in the Windows directory
- WINWORD.EXE (PID: 640)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 640)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0xc8e48bf2 |
| ZipCompressedSize: | 426 |
| ZipUncompressedSize: | 1635 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal.dotm |
|---|---|
| TotalEditTime: | - |
| Pages: | 1 |
| Words: | - |
| Characters: | - |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 2 |
| Paragraphs: | - |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | |
| Manager: | - |
| Company: | home |
| LinksUpToDate: | No |
| CharactersWithSpaces: | - |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
| Keywords: | - |
| LastModifiedBy: | admin |
| RevisionNumber: | 2 |
| CreateDate: | 2019:12:04 09:32:00Z |
| ModifyDate: | 2019:12:04 09:32:00Z |
| Category: | - |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | ryhjy |
| Description: | - |
Total processes
38
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 640 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\070f2306c458df667effc63ee3ab65f76a2f5c5b3208be9ff4539941a67a9b0d.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3856 | wmic process list /format:"c:\windows\temp\aRcmEw.xsl" | C:\Windows\System32\Wbem\wmic.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147500037 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 161
Read events
1 024
Write events
1 007
Delete events
130
Modification events
| (PID) Process: | (640) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | .0; |
Value: 2E303B0080020000010000000000000000000000 | |||
| (PID) Process: | (640) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (640) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (640) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (640) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (640) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (640) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (640) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (640) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (640) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1334181950 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 640 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA89E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 640 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 640 | WINWORD.EXE | C:\windows\temp\aRcmEw.xsl | xml | |
MD5:— | SHA256:— | |||
| 640 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$0f2306c458df667effc63ee3ab65f76a2f5c5b3208be9ff4539941a67a9b0d.doc | pgc | |
MD5:— | SHA256:— | |||
| 640 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3856 | wmic.exe | GET | 404 | 91.211.247.93:80 | http://aermewerog.com/edgron/siloft.php?l=yorght10.cab | LT | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3856 | wmic.exe | 91.211.247.93:80 | aermewerog.com | UAB Esnet | LT | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
aermewerog.com |
| suspicious |
Threats
1 ETPRO signatures available at the full report