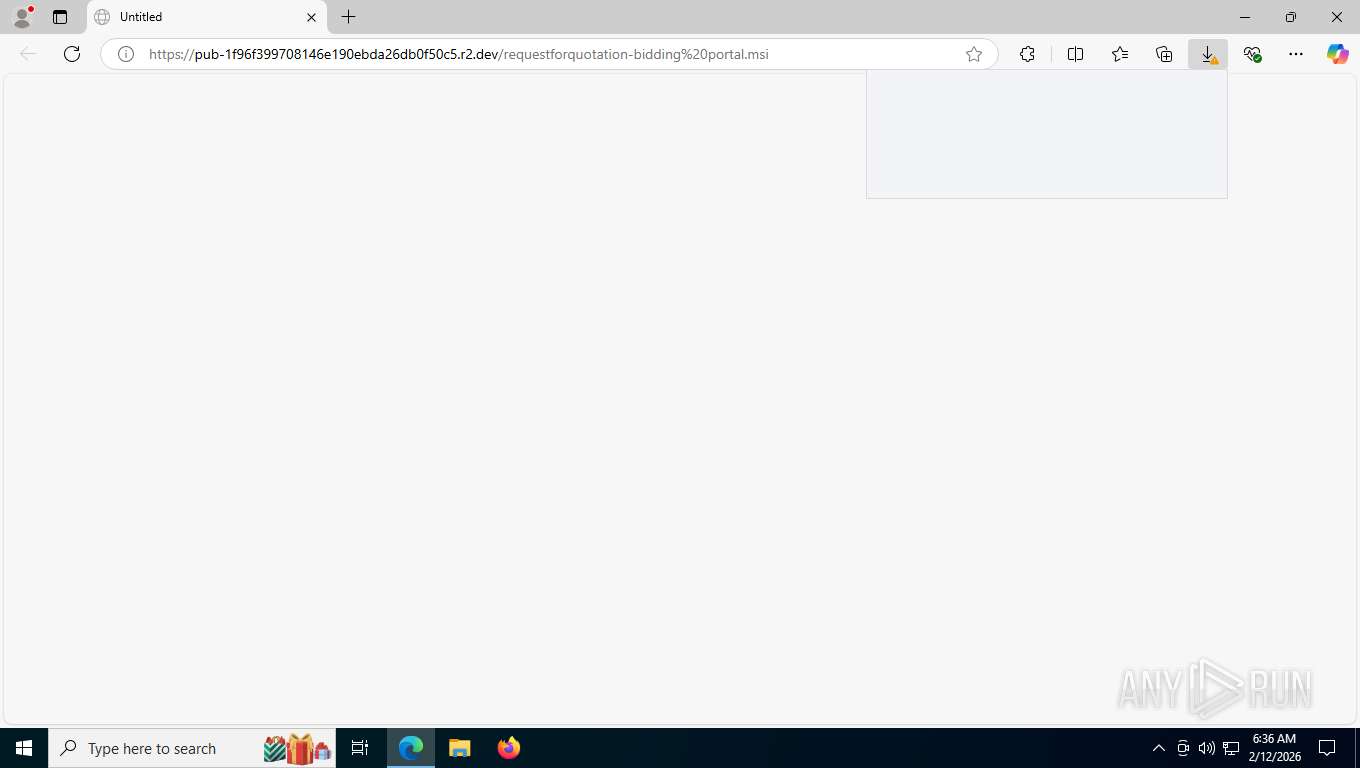
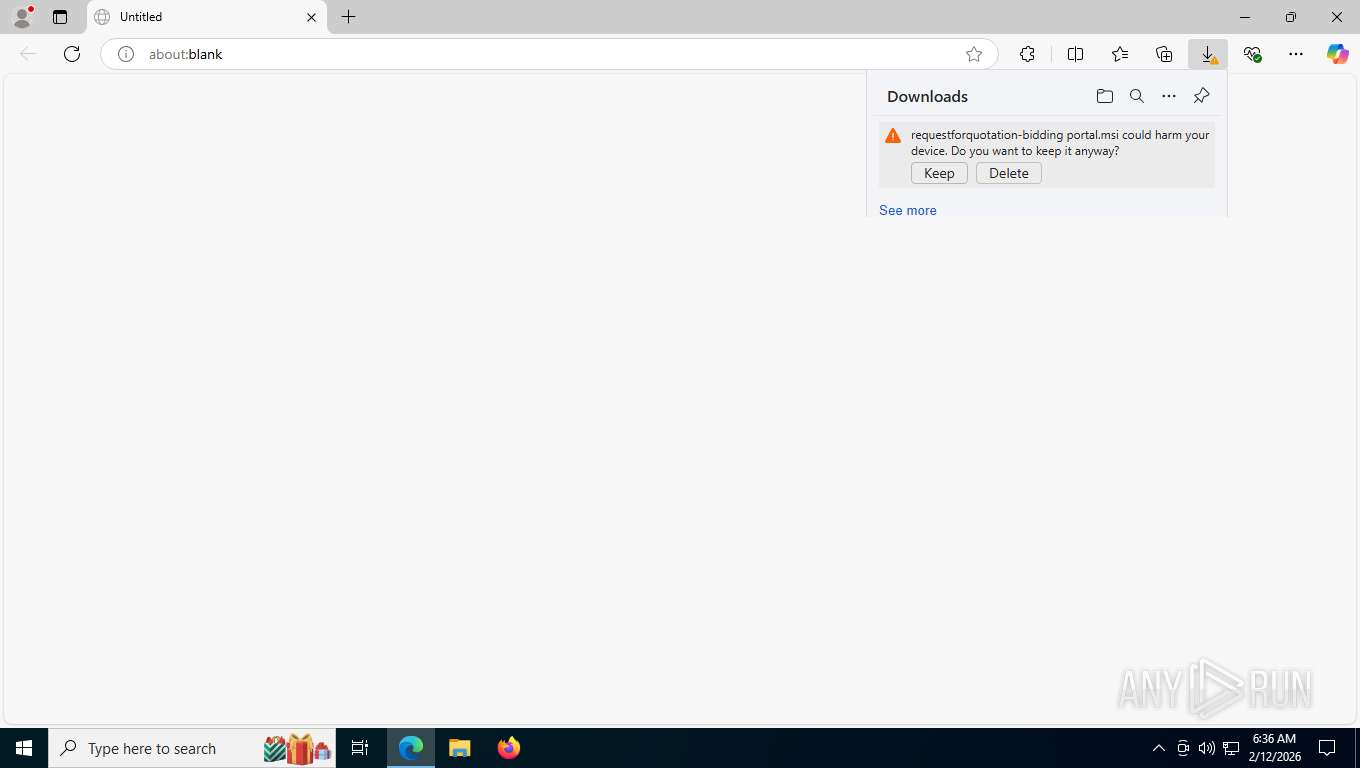
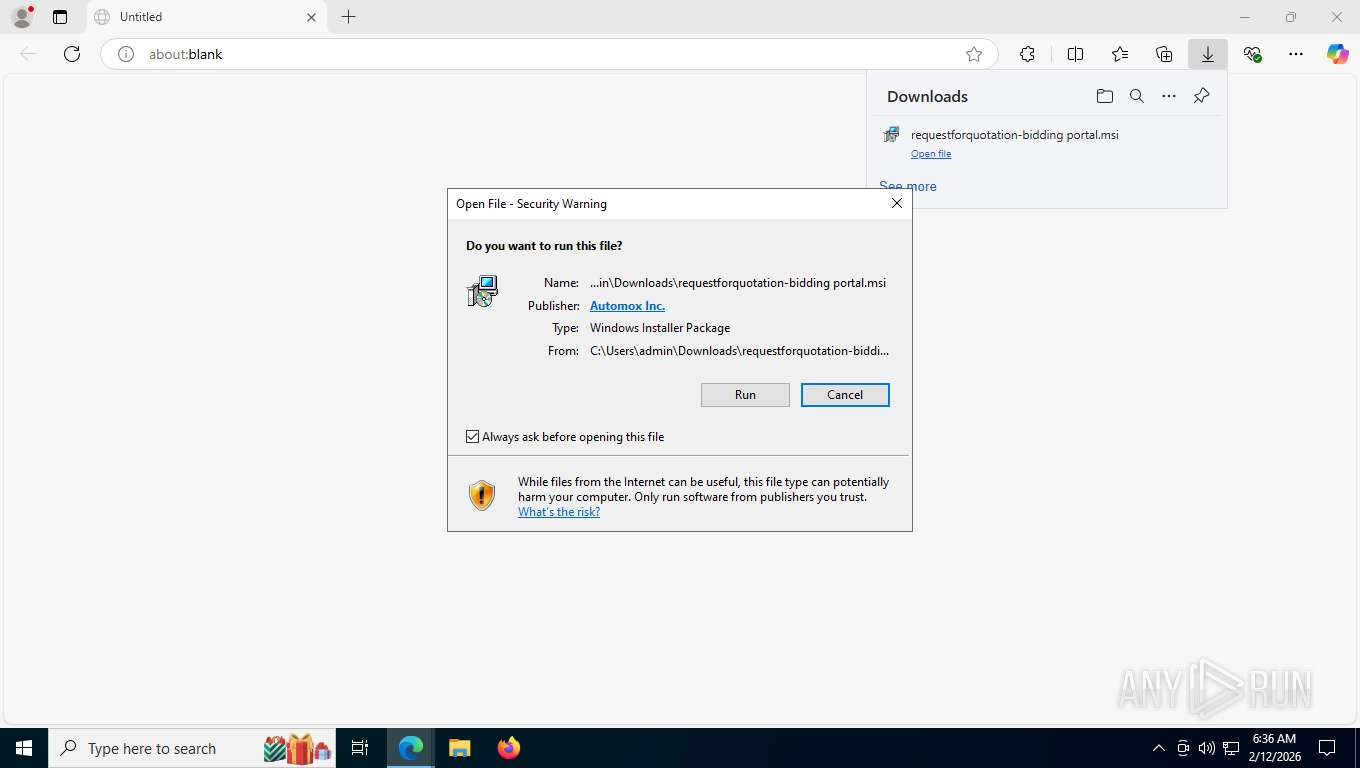
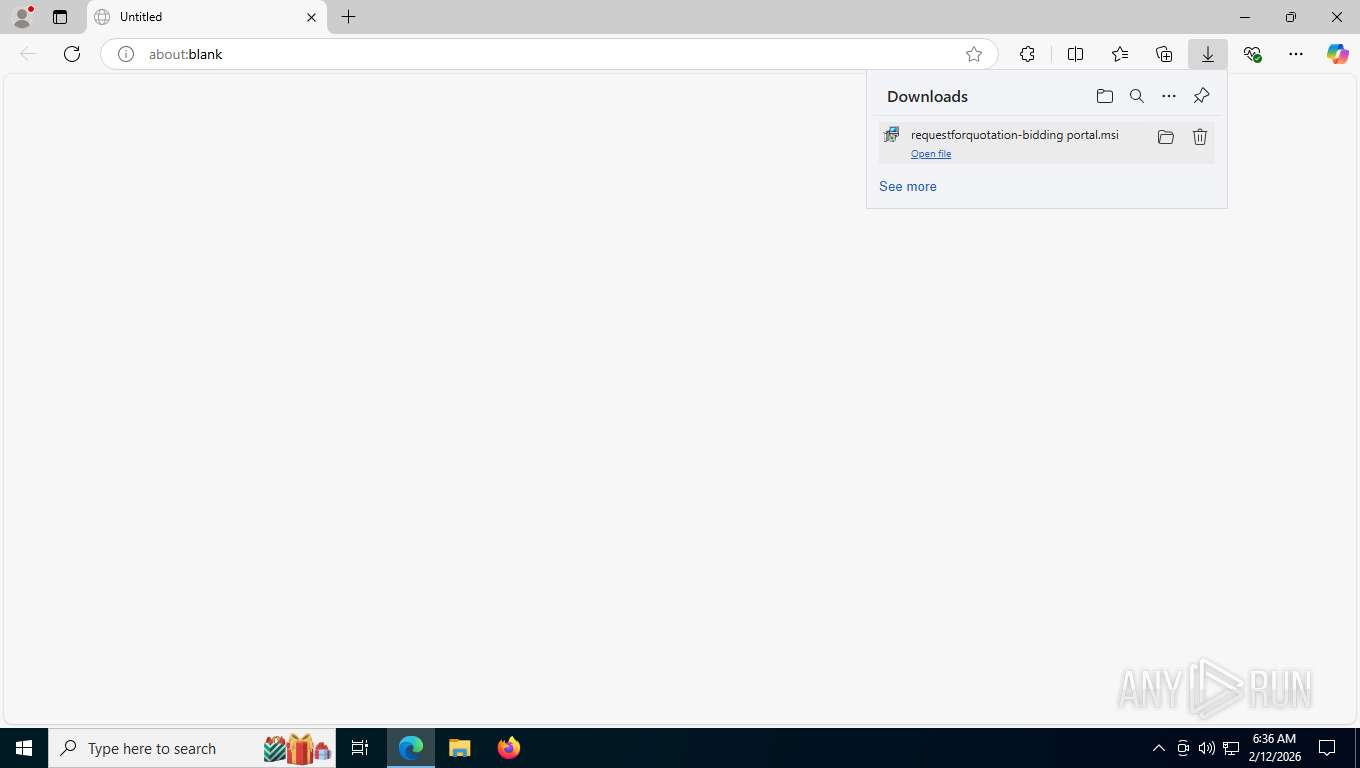
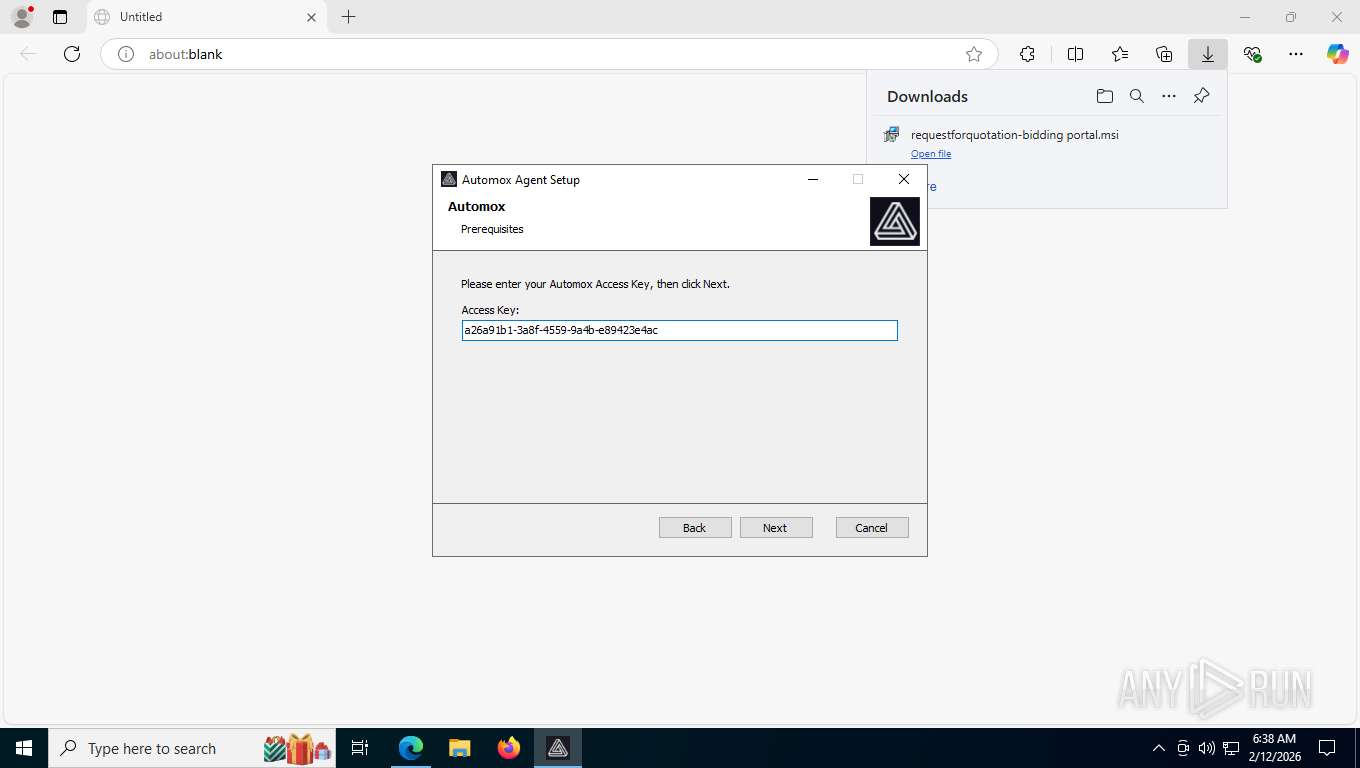
| URL: | https://pub-1f96f399708146e190ebda26db0f50c5.r2.dev/requestforquotation-bidding%20portal.msi |
| Full analysis: | https://app.any.run/tasks/50d1a223-d7a4-4bab-9243-092a70381016 |
| Verdict: | Malicious activity |
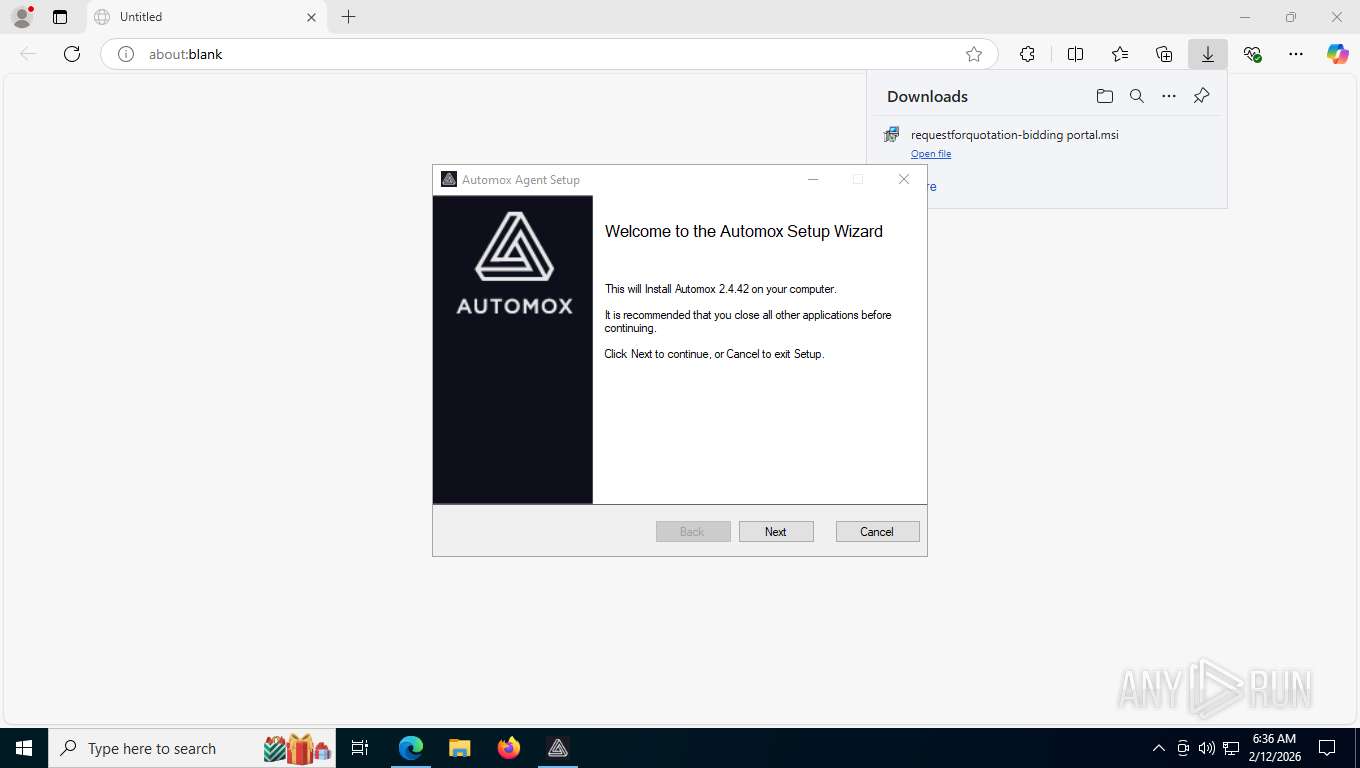
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | February 12, 2026, 11:35:54 |
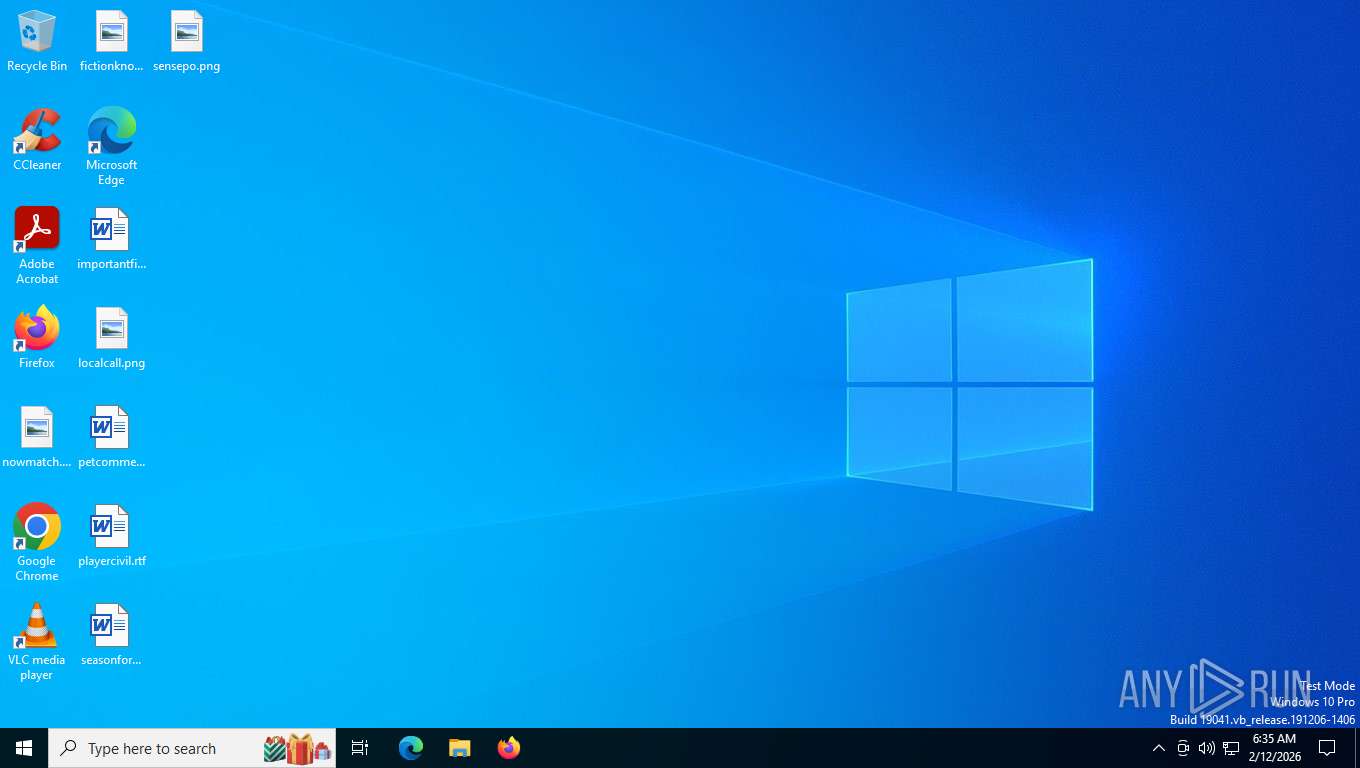
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | EB825D4D6976919B1818CD17C595B4DA |
| SHA1: | 645D791E309F380F194AD04FFE6E71F7FBF87EA9 |
| SHA256: | 070931940BFB863448C9CADD23A40A30D84A07D8A9A48E37845F05C35DCEE5E2 |
| SSDEEP: | 3:N8UJ0jYLyF+NXX1AGQ5RWXUfREag6nSAY:2Umiy0NH1AGQ5RWIDg6nLY |
MALICIOUS
Changes powershell execution policy (Unrestricted)
- amagent.exe (PID: 3056)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 8492)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 2868)
PowerShell executes remote file download (POWERSHELL)
- powershell.exe (PID: 2868)
Changes settings of System certificates
- osqueryi.exe (PID: 8568)
Changes powershell execution policy (Default)
- wdk.exe (PID: 8920)
Queries network adapter information (Win32_NetworkAdapter) (SCRIPT)
- powershell.exe (PID: 6612)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 9004)
- amagent.exe (PID: 3056)
- amagent-watchdog.exe (PID: 2376)
- MicrosoftEdgeUpdate.exe (PID: 1352)
- WmiApSrv.exe (PID: 3332)
Executable content was dropped or overwritten
- rundll32.exe (PID: 5320)
- rundll32.exe (PID: 7920)
- rundll32.exe (PID: 3208)
- rundll32.exe (PID: 8628)
- amagent-watchdog.exe (PID: 2376)
- MicrosoftEdgeWebview2Setup-3001030445.exe (PID: 5448)
- rundll32.exe (PID: 5500)
- rundll32.exe (PID: 2796)
- MicrosoftEdge_X64_144.0.3719.115.exe (PID: 8332)
- powershell.exe (PID: 8492)
- powershell.exe (PID: 5780)
- setup.exe (PID: 8112)
Windows service management via SC.EXE
- sc.exe (PID: 4404)
- sc.exe (PID: 1492)
- sc.exe (PID: 5460)
- sc.exe (PID: 680)
- sc.exe (PID: 7104)
Process drops legitimate windows executable
- amagent-watchdog.exe (PID: 2376)
- MicrosoftEdgeWebview2Setup-3001030445.exe (PID: 5448)
- MicrosoftEdgeUpdate.exe (PID: 2708)
- MicrosoftEdge_X64_144.0.3719.115.exe (PID: 8332)
- powershell.exe (PID: 5780)
- setup.exe (PID: 8112)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup-3001030445.exe (PID: 5448)
- MicrosoftEdgeUpdate.exe (PID: 2708)
- DismHost.exe (PID: 8296)
Probably fake Windows Update file has been dropped
- amagent.exe (PID: 3056)
Searches for installed software
- rundll32.exe (PID: 5500)
- setup.exe (PID: 8112)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 2708)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8600)
- MicrosoftEdgeUpdate.exe (PID: 3536)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 4200)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8836)
Disables SEHOP
- MicrosoftEdgeUpdate.exe (PID: 2708)
Application launched itself
- MicrosoftEdgeUpdate.exe (PID: 1352)
- powershell.exe (PID: 8492)
- setup.exe (PID: 8112)
- msedgewebview2.exe (PID: 680)
The process executes Powershell scripts
- powershell.exe (PID: 5808)
- powershell.exe (PID: 9112)
- powershell.exe (PID: 3024)
- powershell.exe (PID: 680)
- powershell.exe (PID: 2640)
- powershell.exe (PID: 2868)
- powershell.exe (PID: 8600)
- powershell.exe (PID: 8492)
- powershell.exe (PID: 1512)
- powershell.exe (PID: 2312)
- powershell.exe (PID: 7432)
- powershell.exe (PID: 2748)
- powershell.exe (PID: 3536)
- powershell.exe (PID: 8096)
- powershell.exe (PID: 8920)
- powershell.exe (PID: 7920)
- powershell.exe (PID: 4688)
- powershell.exe (PID: 1512)
- powershell.exe (PID: 5780)
- powershell.exe (PID: 3040)
- powershell.exe (PID: 1156)
- powershell.exe (PID: 7004)
- powershell.exe (PID: 6396)
- powershell.exe (PID: 6496)
- powershell.exe (PID: 1044)
- powershell.exe (PID: 4804)
- powershell.exe (PID: 2712)
- powershell.exe (PID: 1576)
- powershell.exe (PID: 1432)
- powershell.exe (PID: 9112)
- powershell.exe (PID: 7980)
- powershell.exe (PID: 4964)
- powershell.exe (PID: 2096)
- powershell.exe (PID: 8824)
- powershell.exe (PID: 2164)
- powershell.exe (PID: 2452)
- powershell.exe (PID: 8356)
- powershell.exe (PID: 7716)
- powershell.exe (PID: 1212)
- powershell.exe (PID: 4804)
- powershell.exe (PID: 4552)
- powershell.exe (PID: 6612)
- powershell.exe (PID: 1924)
- powershell.exe (PID: 2740)
- powershell.exe (PID: 7564)
- powershell.exe (PID: 3700)
- powershell.exe (PID: 6232)
- powershell.exe (PID: 1212)
- powershell.exe (PID: 9240)
- powershell.exe (PID: 9736)
- powershell.exe (PID: 9648)
- powershell.exe (PID: 10008)
- powershell.exe (PID: 10104)
- powershell.exe (PID: 3208)
- powershell.exe (PID: 9576)
- powershell.exe (PID: 4140)
The process hides Powershell's copyright startup banner
- amagent.exe (PID: 3056)
The process bypasses the loading of PowerShell profile settings
- amagent.exe (PID: 3056)
- powershell.exe (PID: 8492)
- wdk.exe (PID: 8920)
Starts POWERSHELL.EXE for commands execution
- amagent.exe (PID: 3056)
- powershell.exe (PID: 8492)
- wdk.exe (PID: 8920)
The process hide an interactive prompt from the user
- amagent.exe (PID: 3056)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 8492)
- powershell.exe (PID: 1432)
Bypass execution policy to execute commands
- powershell.exe (PID: 2868)
- powershell.exe (PID: 5604)
Reads Internet Explorer settings
- msiexec.exe (PID: 6080)
Creates a directory (POWERSHELL)
- powershell.exe (PID: 2868)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 2868)
- powershell.exe (PID: 8492)
Enumerates operating system information (Win32_OperatingSystem) (SCRIPT)
- powershell.exe (PID: 2748)
- powershell.exe (PID: 8096)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 8492)
Adds/modifies Windows certificates
- osqueryi.exe (PID: 8568)
The process creates files with name similar to system file names
- powershell.exe (PID: 5780)
Removes files via Powershell
- powershell.exe (PID: 5604)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 5604)
Gets BIOS serial number (POWERSHELL)
- powershell.exe (PID: 6496)
Obfuscation pattern (POWERSHELL)
- powershell.exe (PID: 5604)
Probably obfuscated PowerShell command line is found
- wdk.exe (PID: 8920)
Returns all items found within a container (POWERSHELL)
- powershell.exe (PID: 5604)
Manipulates environment variables
- powershell.exe (PID: 5604)
Reads the date of Windows installation
- osqueryi.exe (PID: 8436)
Reads the Windows owner or organization settings
- osqueryi.exe (PID: 8436)
INFO
Checks supported languages
- identity_helper.exe (PID: 7028)
- msiexec.exe (PID: 5660)
- msiexec.exe (PID: 6080)
- msiexec.exe (PID: 3188)
- amagent.exe (PID: 4020)
- agent-db-migration_windows_386.exe (PID: 7004)
- agent-db-migration_windows_386.exe (PID: 8436)
- amagent.exe (PID: 1688)
- msiexec.exe (PID: 7024)
- amagent.exe (PID: 3056)
- amagent.exe (PID: 7492)
- amagent.exe (PID: 4684)
- MicrosoftEdgeWebview2Setup-3001030445.exe (PID: 5448)
- MicrosoftEdgeUpdate.exe (PID: 2708)
- amagent-watchdog.exe (PID: 2376)
- MicrosoftEdgeUpdate.exe (PID: 3536)
- MicrosoftEdgeUpdate.exe (PID: 1128)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8600)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 4200)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8836)
- MicrosoftEdgeUpdate.exe (PID: 1856)
- MicrosoftEdgeUpdate.exe (PID: 5524)
- MicrosoftEdgeUpdate.exe (PID: 1352)
- MicrosoftEdgeUpdate.exe (PID: 4688)
- osqueryi.exe (PID: 8568)
- osqueryi.exe (PID: 4688)
- MicrosoftEdge_X64_144.0.3719.115.exe (PID: 8332)
- setup.exe (PID: 8112)
- setup.exe (PID: 9188)
- osqueryi.exe (PID: 2680)
- osqueryi.exe (PID: 8156)
- DismHost.exe (PID: 8296)
- osqueryi.exe (PID: 4120)
- osqueryi.exe (PID: 5320)
- wdk.exe (PID: 8920)
- osqueryi.exe (PID: 8496)
- osqueryi.exe (PID: 8824)
- osqueryi.exe (PID: 4368)
- osqueryi.exe (PID: 2796)
- osqueryi.exe (PID: 7672)
- osqueryi.exe (PID: 2680)
- osqueryi.exe (PID: 8436)
- osqueryi.exe (PID: 8608)
- osqueryi.exe (PID: 8496)
- osqueryi.exe (PID: 8588)
- osqueryi.exe (PID: 8260)
- osqueryi.exe (PID: 3584)
- MicrosoftEdgeUpdate.exe (PID: 6476)
- osqueryi.exe (PID: 3976)
- amagent-ui.exe (PID: 8520)
- msedgewebview2.exe (PID: 4516)
- msedgewebview2.exe (PID: 680)
- osqueryi.exe (PID: 2140)
- msedgewebview2.exe (PID: 5016)
- msedgewebview2.exe (PID: 2052)
- msedgewebview2.exe (PID: 4816)
- msedgewebview2.exe (PID: 4992)
- osqueryi.exe (PID: 9616)
- osqueryi.exe (PID: 9960)
- osqueryi.exe (PID: 4340)
- osqueryi.exe (PID: 9548)
- osqueryi.exe (PID: 9508)
- osqueryi.exe (PID: 9708)
Application launched itself
- msedge.exe (PID: 4644)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 3348)
- MicrosoftEdgeUpdate.exe (PID: 2708)
- msedgewebview2.exe (PID: 680)
Reads the computer name
- identity_helper.exe (PID: 7028)
- msiexec.exe (PID: 5660)
- msiexec.exe (PID: 6080)
- msiexec.exe (PID: 3188)
- msiexec.exe (PID: 7024)
- amagent.exe (PID: 1688)
- amagent.exe (PID: 4020)
- amagent.exe (PID: 3056)
- amagent.exe (PID: 7492)
- amagent.exe (PID: 4684)
- amagent-watchdog.exe (PID: 2376)
- MicrosoftEdgeUpdate.exe (PID: 2708)
- MicrosoftEdgeUpdate.exe (PID: 1128)
- MicrosoftEdgeUpdate.exe (PID: 3536)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8600)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 4200)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8836)
- MicrosoftEdgeUpdate.exe (PID: 5524)
- MicrosoftEdgeUpdate.exe (PID: 1856)
- MicrosoftEdgeUpdate.exe (PID: 1352)
- MicrosoftEdgeUpdate.exe (PID: 4688)
- osqueryi.exe (PID: 4688)
- osqueryi.exe (PID: 8568)
- MicrosoftEdge_X64_144.0.3719.115.exe (PID: 8332)
- setup.exe (PID: 8112)
- osqueryi.exe (PID: 2680)
- osqueryi.exe (PID: 8156)
- DismHost.exe (PID: 8296)
- osqueryi.exe (PID: 4120)
- osqueryi.exe (PID: 5320)
- osqueryi.exe (PID: 8496)
- osqueryi.exe (PID: 8824)
- osqueryi.exe (PID: 4368)
- osqueryi.exe (PID: 2796)
- osqueryi.exe (PID: 7672)
- osqueryi.exe (PID: 2680)
- osqueryi.exe (PID: 8436)
- osqueryi.exe (PID: 8588)
- osqueryi.exe (PID: 8608)
- osqueryi.exe (PID: 8496)
- osqueryi.exe (PID: 3584)
- osqueryi.exe (PID: 8260)
- osqueryi.exe (PID: 3976)
- amagent-ui.exe (PID: 8520)
- msedgewebview2.exe (PID: 680)
- MicrosoftEdgeUpdate.exe (PID: 6476)
- msedgewebview2.exe (PID: 5016)
- msedgewebview2.exe (PID: 2052)
- osqueryi.exe (PID: 2140)
- osqueryi.exe (PID: 9616)
- osqueryi.exe (PID: 9960)
- osqueryi.exe (PID: 4340)
- osqueryi.exe (PID: 9548)
- osqueryi.exe (PID: 9708)
- osqueryi.exe (PID: 9508)
Reads Environment values
- identity_helper.exe (PID: 7028)
- amagent.exe (PID: 1688)
- amagent.exe (PID: 3056)
- amagent.exe (PID: 4684)
- amagent-watchdog.exe (PID: 2376)
- MicrosoftEdgeUpdate.exe (PID: 5524)
- MicrosoftEdgeUpdate.exe (PID: 4688)
- DismHost.exe (PID: 8296)
- osqueryi.exe (PID: 8436)
- MicrosoftEdgeUpdate.exe (PID: 6476)
- msedgewebview2.exe (PID: 680)
Drops script file
- msedge.exe (PID: 8684)
- amagent.exe (PID: 3056)
- powershell.exe (PID: 5808)
- powershell.exe (PID: 8492)
- powershell.exe (PID: 9112)
- powershell.exe (PID: 3024)
- powershell.exe (PID: 680)
- powershell.exe (PID: 2640)
- powershell.exe (PID: 8600)
- powershell.exe (PID: 2868)
- powershell.exe (PID: 1512)
- powershell.exe (PID: 2312)
- powershell.exe (PID: 3536)
- powershell.exe (PID: 2748)
- powershell.exe (PID: 8096)
- powershell.exe (PID: 7432)
- powershell.exe (PID: 8920)
- powershell.exe (PID: 7920)
- powershell.exe (PID: 4688)
- powershell.exe (PID: 1512)
- powershell.exe (PID: 3040)
- powershell.exe (PID: 5780)
- powershell.exe (PID: 1156)
- powershell.exe (PID: 7004)
- powershell.exe (PID: 6396)
- powershell.exe (PID: 1044)
- powershell.exe (PID: 2712)
- powershell.exe (PID: 1576)
- powershell.exe (PID: 4804)
- powershell.exe (PID: 6496)
- setup.exe (PID: 8112)
- powershell.exe (PID: 5604)
- powershell.exe (PID: 7980)
- powershell.exe (PID: 9112)
- powershell.exe (PID: 1432)
- powershell.exe (PID: 4964)
- powershell.exe (PID: 8824)
- powershell.exe (PID: 2096)
- powershell.exe (PID: 2164)
- powershell.exe (PID: 7716)
- powershell.exe (PID: 1212)
- powershell.exe (PID: 4804)
- powershell.exe (PID: 4552)
- powershell.exe (PID: 2452)
- powershell.exe (PID: 8356)
- powershell.exe (PID: 1924)
- powershell.exe (PID: 2740)
- powershell.exe (PID: 3700)
- powershell.exe (PID: 6612)
- powershell.exe (PID: 7564)
- powershell.exe (PID: 1212)
- powershell.exe (PID: 9240)
- powershell.exe (PID: 6232)
- powershell.exe (PID: 9648)
- powershell.exe (PID: 9736)
- powershell.exe (PID: 10008)
- powershell.exe (PID: 10104)
- powershell.exe (PID: 3208)
- powershell.exe (PID: 9576)
- powershell.exe (PID: 4140)
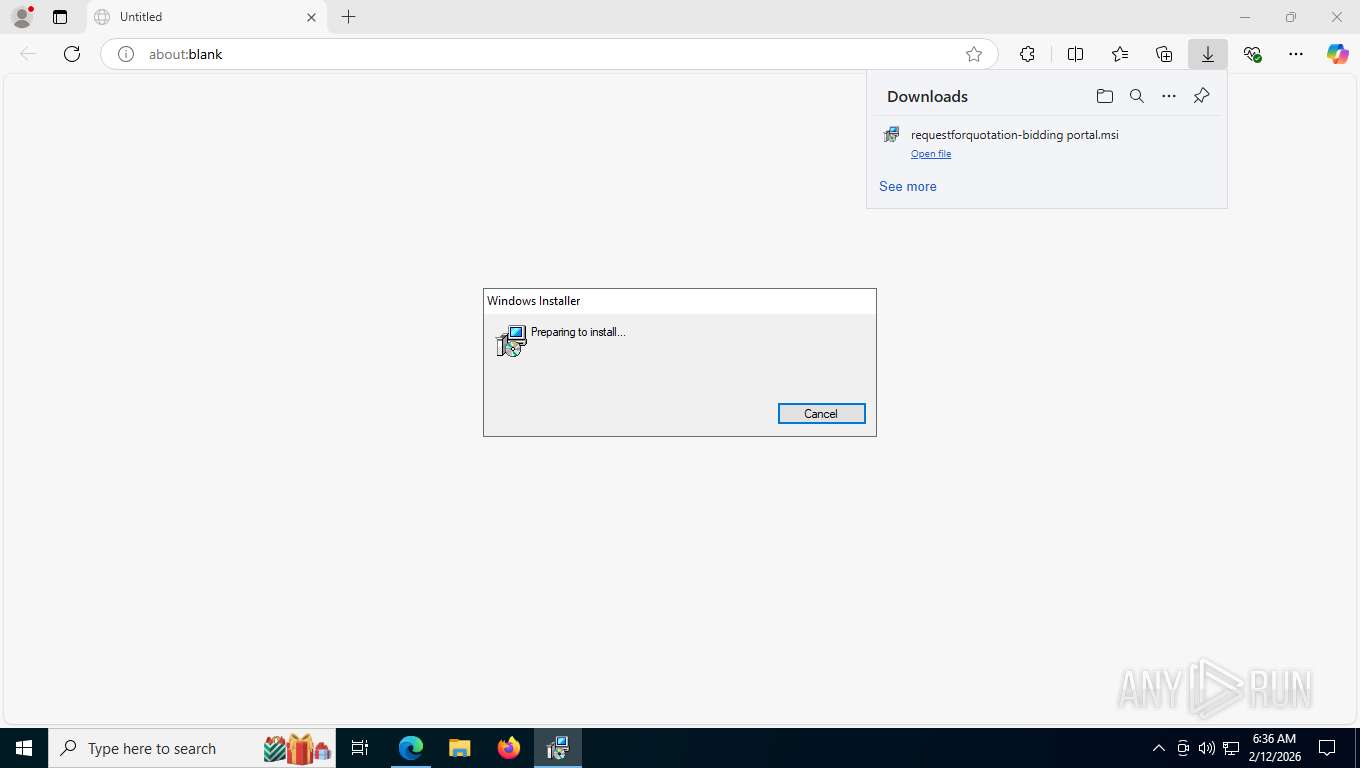
Create files in a temporary directory
- msiexec.exe (PID: 3348)
- msiexec.exe (PID: 6080)
- rundll32.exe (PID: 7920)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3348)
- msiexec.exe (PID: 6080)
- msiexec.exe (PID: 5660)
Reads the machine GUID from the registry
- msiexec.exe (PID: 6080)
- amagent.exe (PID: 1688)
- amagent.exe (PID: 3056)
- amagent.exe (PID: 4684)
- amagent-watchdog.exe (PID: 2376)
- osqueryi.exe (PID: 8568)
- amagent-ui.exe (PID: 8520)
- msedgewebview2.exe (PID: 680)
Checks proxy server information
- slui.exe (PID: 7600)
- msedgewebview2.exe (PID: 680)
Manages system restore points
- SrTasks.exe (PID: 8308)
The sample compiled with english language support
- msiexec.exe (PID: 5660)
- amagent-watchdog.exe (PID: 2376)
- MicrosoftEdgeWebview2Setup-3001030445.exe (PID: 5448)
- MicrosoftEdgeUpdate.exe (PID: 2708)
- MicrosoftEdge_X64_144.0.3719.115.exe (PID: 8332)
- powershell.exe (PID: 8492)
- powershell.exe (PID: 5780)
- setup.exe (PID: 8112)
Creates files in the program directory
- amagent.exe (PID: 1688)
- amagent.exe (PID: 4020)
- amagent.exe (PID: 3056)
- MicrosoftEdgeWebview2Setup-3001030445.exe (PID: 5448)
- powershell.exe (PID: 8492)
- powershell.exe (PID: 2868)
- MicrosoftEdge_X64_144.0.3719.115.exe (PID: 8332)
- setup.exe (PID: 8112)
Reads product name
- amagent.exe (PID: 1688)
- amagent.exe (PID: 3056)
- amagent.exe (PID: 4684)
- osqueryi.exe (PID: 8436)
Drops encrypted JS script (Microsoft Script Encoder)
- amagent.exe (PID: 3056)
Creates a software uninstall entry
- rundll32.exe (PID: 5500)
- setup.exe (PID: 8112)
Disables trace logs
- powershell.exe (PID: 8492)
- powershell.exe (PID: 680)
- powershell.exe (PID: 2868)
- powershell.exe (PID: 2748)
- powershell.exe (PID: 1512)
- powershell.exe (PID: 6496)
- powershell.exe (PID: 9648)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 2868)
- powershell.exe (PID: 8492)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2868)
- powershell.exe (PID: 8492)
- powershell.exe (PID: 8920)
- powershell.exe (PID: 2712)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 8600)
- powershell.exe (PID: 8096)
- powershell.exe (PID: 8492)
- powershell.exe (PID: 7004)
- powershell.exe (PID: 1432)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1512)
- powershell.exe (PID: 8096)
- powershell.exe (PID: 7004)
Gets data length (POWERSHELL)
- powershell.exe (PID: 8600)
- powershell.exe (PID: 1432)
- powershell.exe (PID: 6232)
Using PowerShell for ZIP File Operations
- powershell.exe (PID: 2868)
- powershell.exe (PID: 8492)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 6496)
Returns hidden items found within a container (POWERSHELL)
- conhost.exe (PID: 3176)
- conhost.exe (PID: 1212)
- conhost.exe (PID: 7700)
- conhost.exe (PID: 8436)
- conhost.exe (PID: 3584)
- conhost.exe (PID: 4368)
- conhost.exe (PID: 3348)
- conhost.exe (PID: 7980)
- conhost.exe (PID: 3208)
- conhost.exe (PID: 7208)
- conhost.exe (PID: 1176)
- conhost.exe (PID: 1908)
- conhost.exe (PID: 7856)
- conhost.exe (PID: 1484)
- conhost.exe (PID: 8436)
- conhost.exe (PID: 1176)
- conhost.exe (PID: 2680)
- conhost.exe (PID: 7864)
- conhost.exe (PID: 876)
- conhost.exe (PID: 4876)
- conhost.exe (PID: 9272)
- conhost.exe (PID: 9744)
- conhost.exe (PID: 10112)
- conhost.exe (PID: 10016)
- conhost.exe (PID: 9656)
- conhost.exe (PID: 9584)
- conhost.exe (PID: 9852)
- conhost.exe (PID: 4104)
Process checks computer location settings
- setup.exe (PID: 8112)
- msedgewebview2.exe (PID: 680)
- msedgewebview2.exe (PID: 4992)
Reads Windows Product ID
- osqueryi.exe (PID: 8436)
Reads CPU info
- osqueryi.exe (PID: 3584)
Creates files or folders in the user directory
- msedgewebview2.exe (PID: 4516)
- amagent-ui.exe (PID: 8520)
- msedgewebview2.exe (PID: 680)
- msedgewebview2.exe (PID: 2052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
405
Monitored processes
240
Malicious processes
7
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5664,i,6854095249799313376,17804986588212068074,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=8028 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 412 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2336,i,6854095249799313376,17804986588212068074,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2188 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 680 | "C:\WINDOWS\System32\sc.exe" query amagent | C:\Windows\SysWOW64\sc.exe | — | rundll32.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe -NoProfile -NonInteractive -NoLogo -ExecutionPolicy unrestricted -File "C:\Program Files (x86)\Automox\inventory_workspace\4285935421\content.ps1" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | amagent.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | "C:\Program Files (x86)\Microsoft\EdgeWebView\Application\144.0.3719.115\msedgewebview2.exe" --embedded-browser-webview=1 --webview-exe-name=amagent-ui.exe --webview-exe-version=2.0.13-cpu-fix --user-data-dir="C:\Users\admin\AppData\Local\com.automox.agent-ui\EBWebView" --noerrdialogs --embedded-browser-webview-dpi-awareness=2 --autoplay-policy=no-user-gesture-required --disable-features=msWebOOUI,msPdfOOUI,msSmartScreenProtection --lang=en-US --mojo-named-platform-channel-pipe=8520.2416.8793115520575075461 | C:\Program Files (x86)\Microsoft\EdgeWebView\Application\144.0.3719.115\msedgewebview2.exe | amagent-ui.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge WebView2 Version: 144.0.3719.115 Modules
| |||||||||||||||
| 756 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3616,i,6854095249799313376,17804986588212068074,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3888 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 876 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1044 | C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe -NoProfile -NonInteractive -NoLogo -ExecutionPolicy unrestricted -File "C:\Program Files (x86)\Automox\inventory_workspace\3757091067\content.ps1" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | amagent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | "C:\Program Files (x86)\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /regsvc | C:\Program Files (x86)\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.217.3 Modules
| |||||||||||||||
| 1156 | C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe -NoProfile -NonInteractive -NoLogo -ExecutionPolicy unrestricted -File "C:\Program Files (x86)\Automox\execDir37970028\execcmd2123043370.ps1" "" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | amagent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
331 426
Read events
329 627
Write events
1 658
Delete events
141
Modification events
| (PID) Process: | (5660) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000BBD10B32149CDC011C160000A4070000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5660) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000BBD10B32149CDC011C160000A4070000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5660) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000C7304C32149CDC011C160000A4070000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5660) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000C7304C32149CDC011C160000A4070000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5660) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000C7304C32149CDC011C160000A4070000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5660) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000000F934E32149CDC011C160000A4070000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5660) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 480000000000000036A66132149CDC011C160000A4070000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5660) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000036A66132149CDC011C160000601E0000E8030000010000000000000000000000CDDA02DC8C96144F98FB4C2BBC9968DD00000000000000000000000000000000 | |||
| (PID) Process: | (9004) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000009E916D32149CDC012C23000014210000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (9004) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000009E916D32149CDC012C230000D81F0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
305
Suspicious files
148
Text files
774
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1e536d.TMP | — | |
MD5:— | SHA256:— | |||
| 4644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1e537d.TMP | — | |
MD5:— | SHA256:— | |||
| 4644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1e537d.TMP | — | |
MD5:— | SHA256:— | |||
| 4644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1e537d.TMP | — | |
MD5:— | SHA256:— | |||
| 4644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1e538c.TMP | — | |
MD5:— | SHA256:— | |||
| 4644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
115
TCP/UDP connections
97
DNS requests
97
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
412 | msedge.exe | GET | 304 | 150.171.27.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | US | — | — | whitelisted |
412 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 446 b | whitelisted |
412 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | US | text | 4.47 Kb | whitelisted |
412 | msedge.exe | GET | 200 | 104.18.50.34:443 | https://pub-1f96f399708146e190ebda26db0f50c5.r2.dev/requestforquotation-bidding%20portal.msi | US | executable | 30.9 Mb | unknown |
412 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:prnK7aGwM0BUTgs2Di4E0uEGAmAkof7r_CGWyrSASMc&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 96 b | whitelisted |
412 | msedge.exe | GET | 200 | 13.107.213.44:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | US | — | 82 b | whitelisted |
412 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | — | 25 b | whitelisted |
412 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/extensionwebstorebase/v1/crx?os=win&arch=x64&os_arch=x86_64&nacl_arch=x86-64&prod=edgecrx&prodchannel=&prodversion=133.0.3065.92&lang=en-US&acceptformat=crx3,puff&x=id%3Djmjflgjpcpepeafmmgdpfkogkghcpiha%26v%3D1.2.1%26installedby%3Dother%26uc%26ping%3Dr%253D55%2526e%253D1 | US | xml | 413 b | whitelisted |
412 | msedge.exe | POST | 200 | 142.251.140.163:443 | https://update.googleapis.com/service/update2/json?cup2key=14:skm75VHU7VseEtcMz1RGxZ38JgoY8BcD1hK6O_t2dlQ&cup2hreq=02f5a8640459acc8cbf1484196e8151a2d12798909f1cd49e25a2696ca99ffaa | US | text | 891 b | whitelisted |
412 | msedge.exe | GET | 200 | 2.16.204.137:443 | https://www.bing.com/api/shopping/v1/user/shoppingsettings?EnabledServiceFeaturesv2=edgeServerUX.shopping.cashbackEUMarkets,edgeServerUX.shopping.msEdgeShoppingCashbackDismissTimeout2s | NL | text | 1.11 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6232 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
7212 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
412 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
412 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
412 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
412 | msedge.exe | 142.250.201.65:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
412 | msedge.exe | 104.18.50.34:443 | pub-1f96f399708146e190ebda26db0f50c5.r2.dev | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
pub-1f96f399708146e190ebda26db0f50c5.r2.dev |
| unknown |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
412 | msedge.exe | Misc activity | ET INFO Observed Cloudflare R2 Public Bucket (r2 .dev) Domain in TLS SNI |
412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] CloudFlare Public R2.dev Bucket |
412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] CloudFlare Public R2.dev Bucket |
412 | msedge.exe | Misc activity | ET INFO Observed Cloudflare R2 Public Bucket (r2 .dev) Domain in TLS SNI |
412 | msedge.exe | Possible Social Engineering Attempted | SUSPICIOUS [ANY.RUN] Abuse Public R2.dev Bucket |
412 | msedge.exe | Possible Social Engineering Attempted | SUSPICIOUS [ANY.RUN] Abuse Public R2.dev Bucket |
412 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Cloudflare R2 Public Bucket (r2 .dev) Domain |
412 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Cloudflare R2 Public Bucket (r2 .dev) Domain |
412 | msedge.exe | Misc activity | ET INFO Observed Cloudflare R2 Public Bucket (r2 .dev) Domain in TLS SNI |
412 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Abuse Public R2.dev Bucket (HTTP) |
Process | Message |
|---|---|
powershell.exe | PID=5780 TID=1340 Lookup in table by path failed for: DummyPath-2BA51B78-C7F7-4910-B99D-BB7345357CDC - CTransactionalImageTable::LookupImagePath
|
powershell.exe | PID=5780 TID=1340 DismApi.dll: Host machine information: OS Version=10.0.19045, Running architecture=x86, Number of processors=6 - DismInitializeInternal
|
powershell.exe | PID=5780 TID=3644 Enter CCommandThread::CommandThreadProcedureStub - CCommandThread::CommandThreadProcedureStub
|
powershell.exe | PID=5780 TID=1340 DismApi.dll: <----- Starting DismApi.dll session -----> - DismInitializeInternal
|
powershell.exe | PID=5780 TID=1340 Initialized SessionTable - DismInitializeInternal
|
powershell.exe | PID=5780 TID=1340 DismApi.dll: - DismInitializeInternal
|
powershell.exe | PID=5780 TID=1340 Initialized GlobalConfig - DismInitializeInternal
|
powershell.exe | PID=5780 TID=1340 DismApi.dll: - DismInitializeInternal
|
powershell.exe | PID=5780 TID=1340 DismApi.dll: Parent process command line: C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe -NoProfile -NonInteractive -NoLogo -ExecutionPolicy unrestricted -File "C:\Program Files (x86)\Automox\inventory_workspace\2272758328\content.ps1" - DismInitializeInternal
|
powershell.exe | PID=5780 TID=1340 Input parameters: LogLevel: 2, LogFilePath: C:\WINDOWS\Logs\DISM\dism.log, ScratchDirectory: (null) - DismInitializeInternal
|