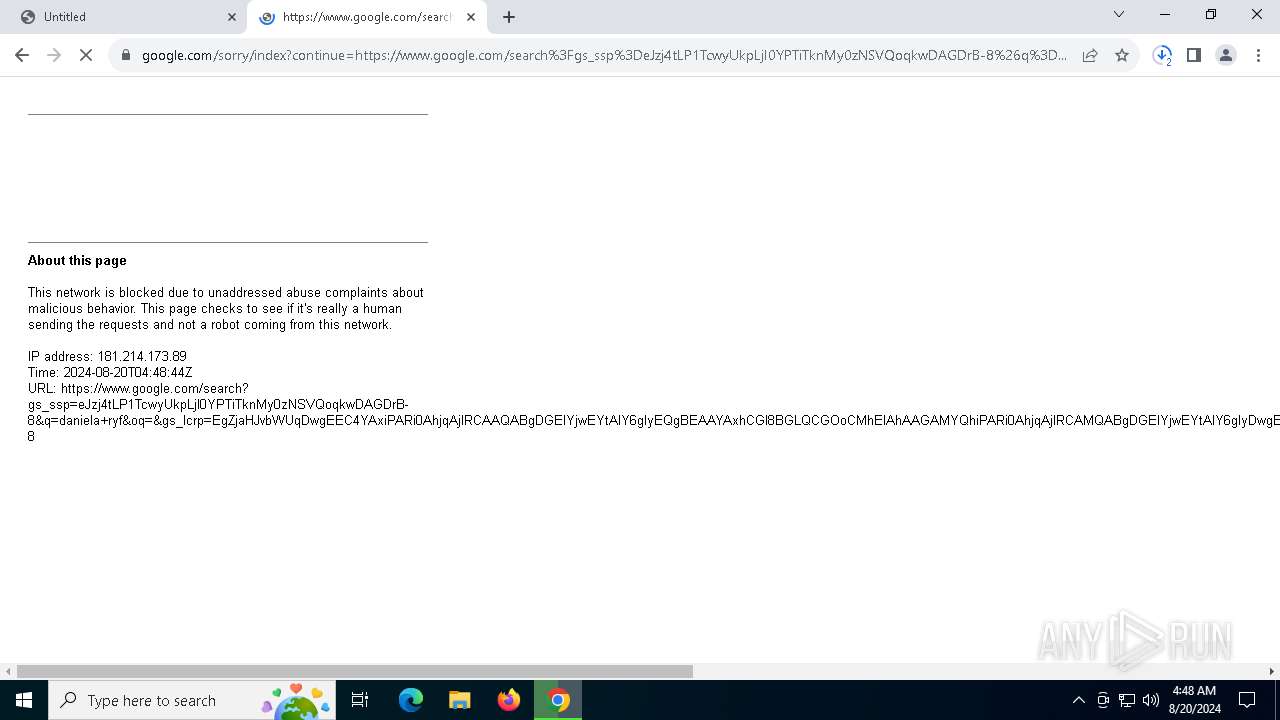
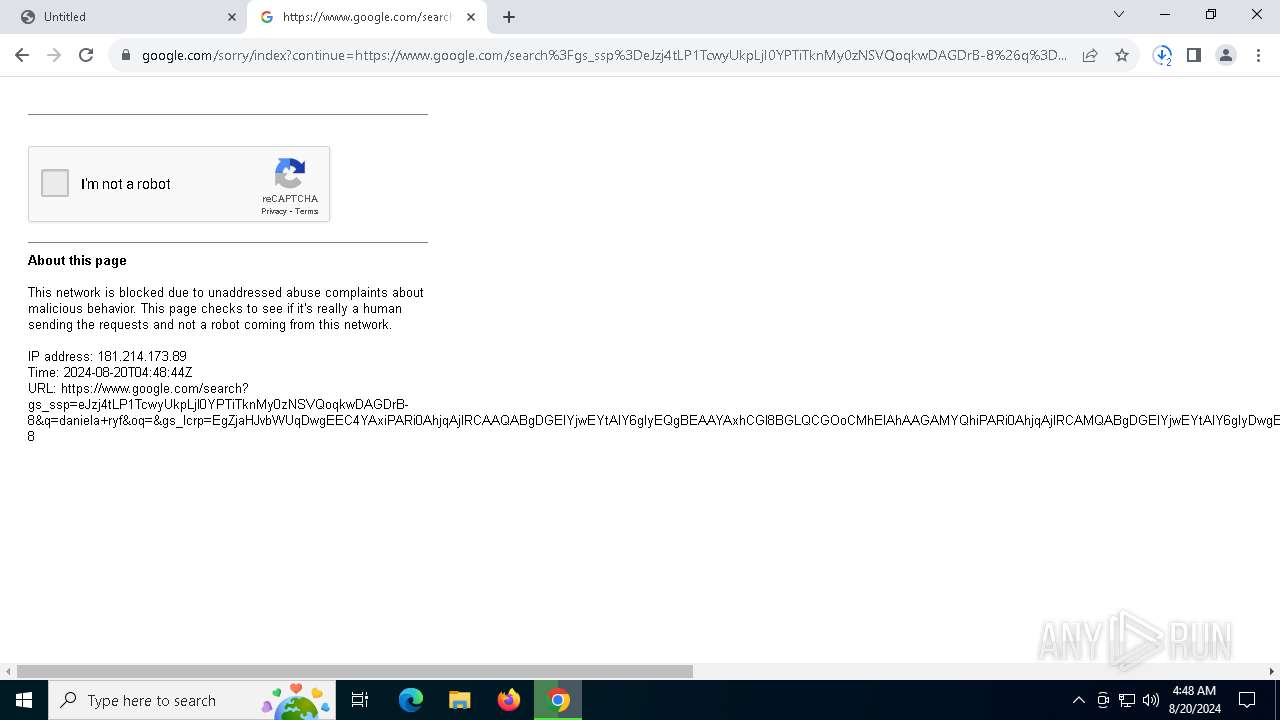
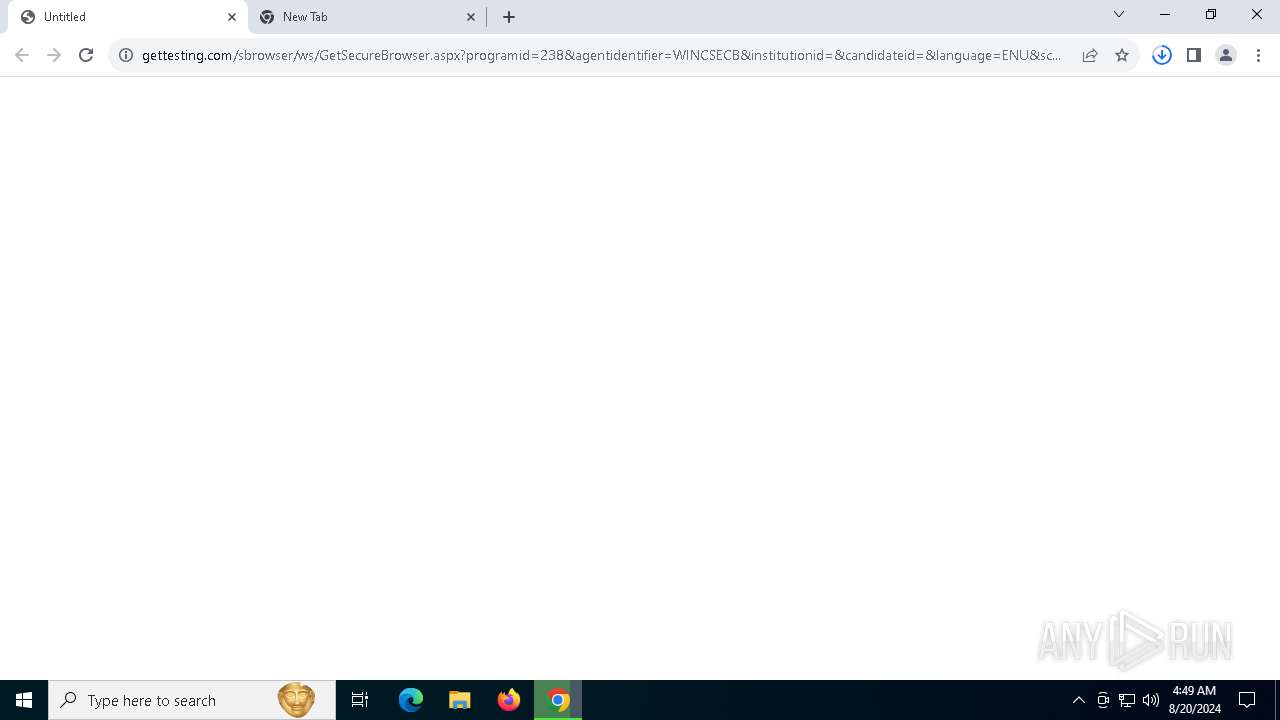
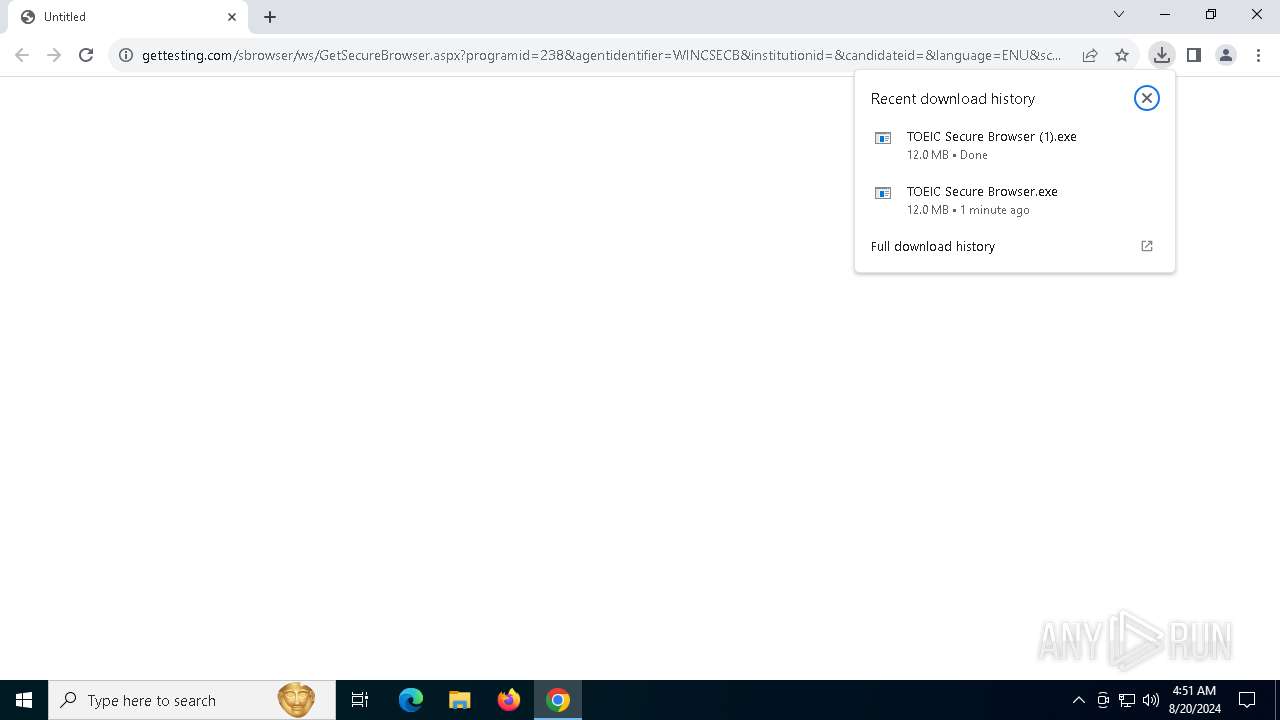
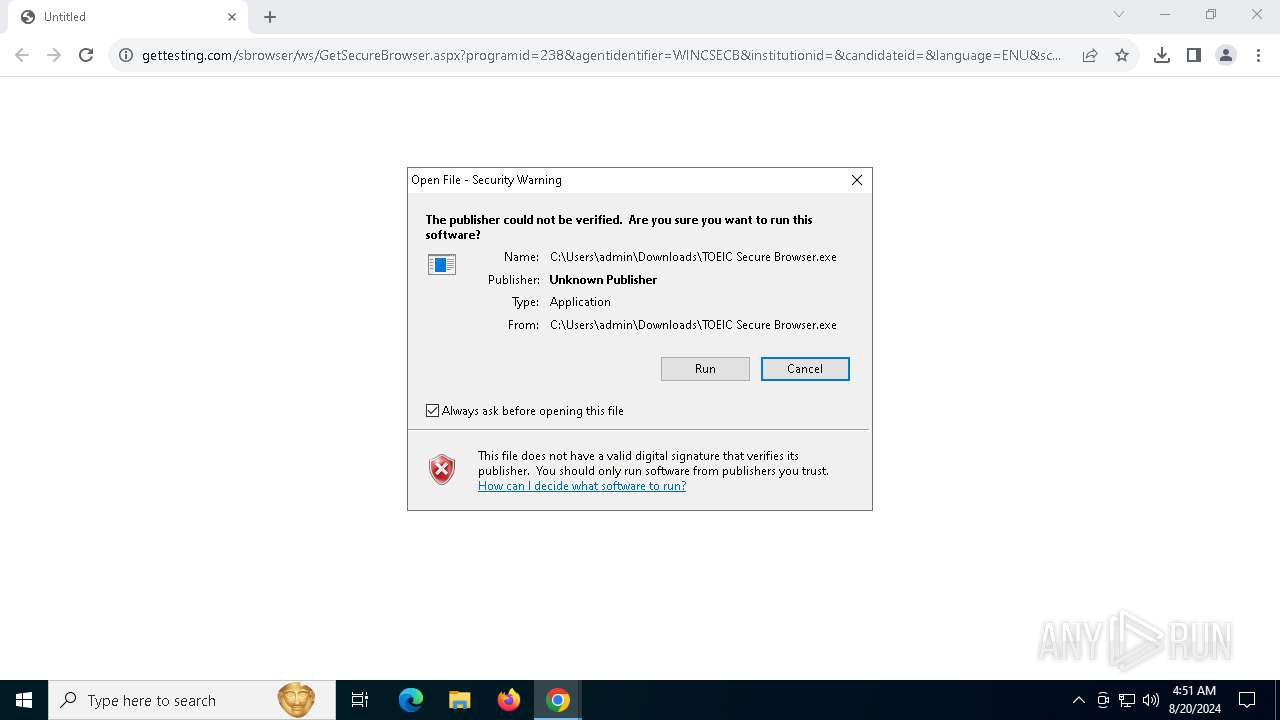
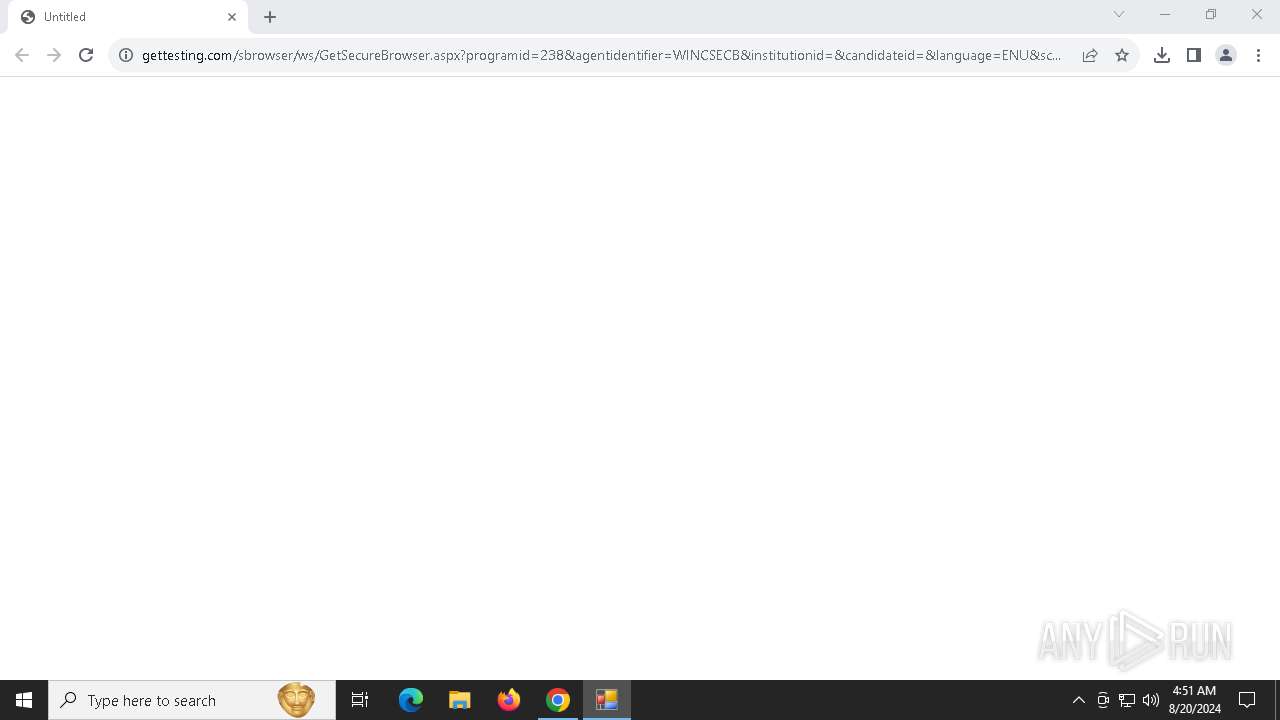
| URL: | https://www.gettesting.com/sbrowser/ws/GetSecureBrowser.aspx?programid=238&agentidentifier=WINCSECB&institutionid=&candidateid=&language=ENU&sc=0ff384d21b2bdcabb446d3bfe8d5d4225fa5b010 |
| Full analysis: | https://app.any.run/tasks/557c95ec-c782-414a-ac58-9e36994da496 |
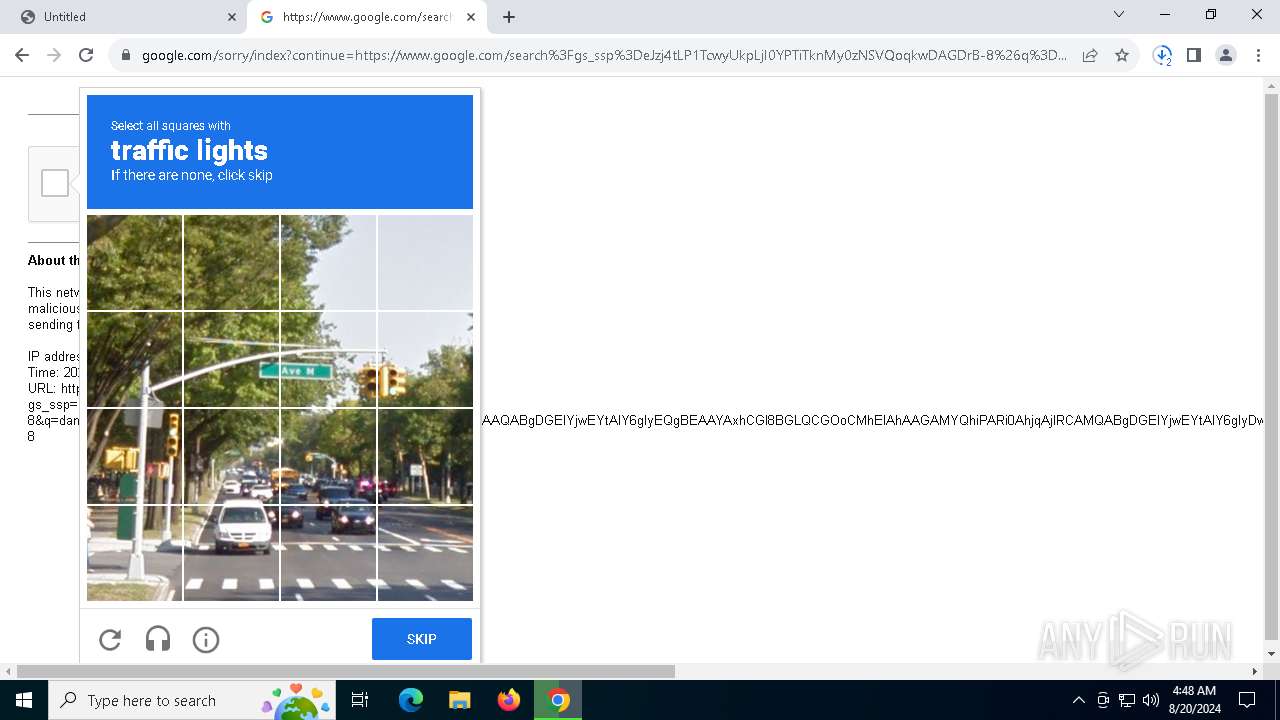
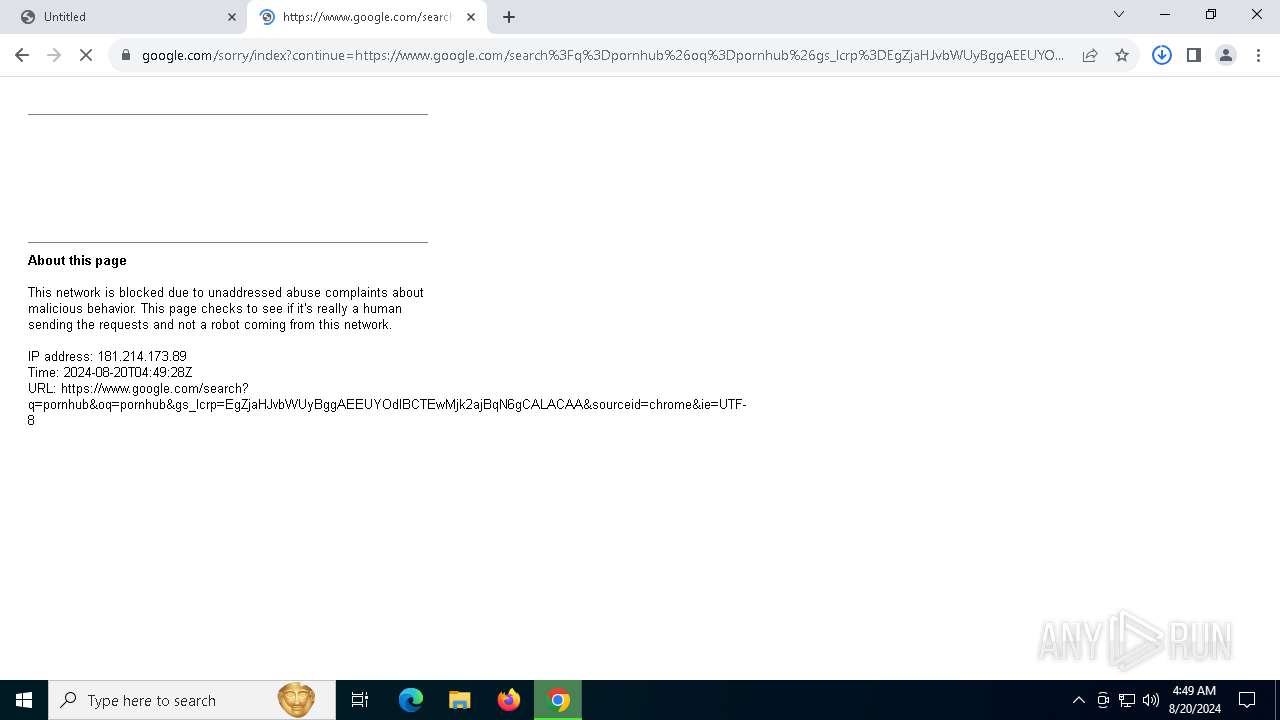
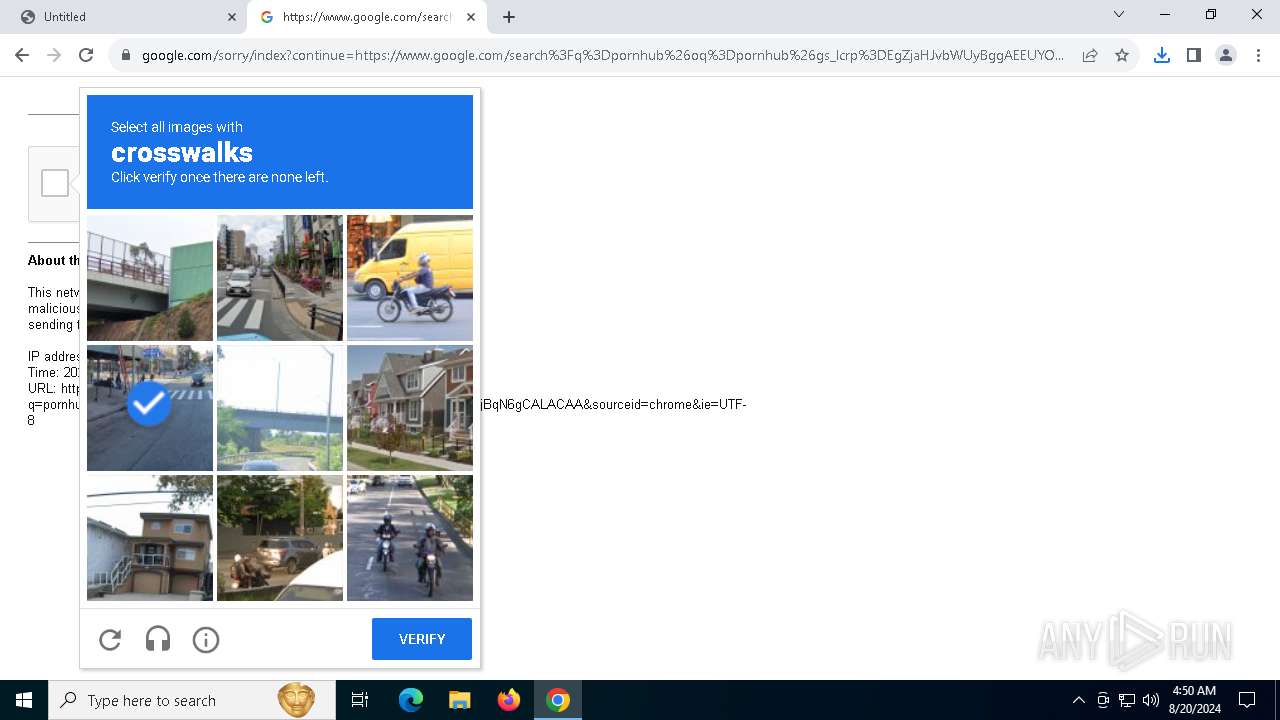
| Verdict: | Malicious activity |
| Analysis date: | August 20, 2024, 04:47:54 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 90F9D850D851677B2F461FA72AB016EB |
| SHA1: | 7C88119390C9A2C07E2DB8B438A95397F133E92F |
| SHA256: | 0702ADA98D62938FAC96F9DABAD91AF1B397869C38161673E2464B4D98E3536D |
| SSDEEP: | 3:N8DSLR1wHaaXnjRCXYpuIZRMB3ALRlLwfKmHycNAT0C9gKuUnX6BxijxzSVMn:2OL7wHaa8XYpuIzMBwlqfKWykAT1jqB0 |
MALICIOUS
Scans artifacts that could help determine the target
- msedgewebview2.exe (PID: 2360)
The DLL Hijacking
- msedgewebview2.exe (PID: 3980)
SUSPICIOUS
Reads the BIOS version
- TOEIC Secure Browser.exe (PID: 7592)
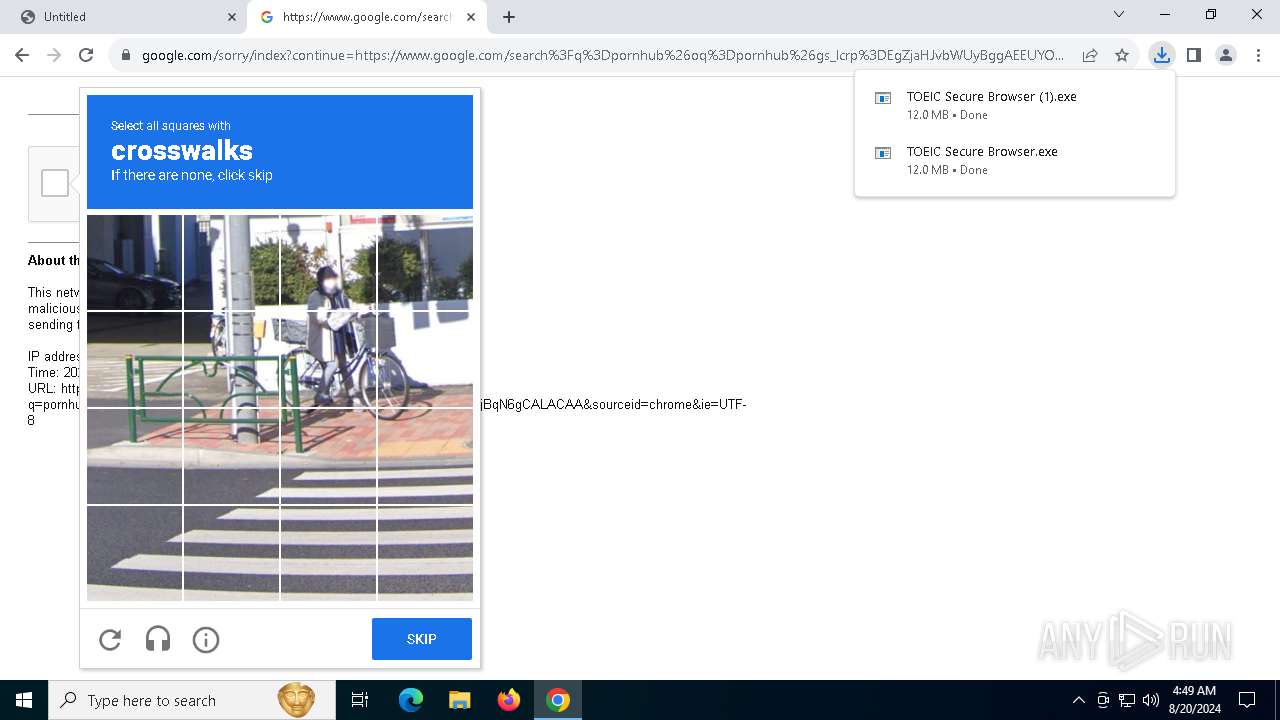
Executable content was dropped or overwritten
- TOEIC Secure Browser.exe (PID: 7592)
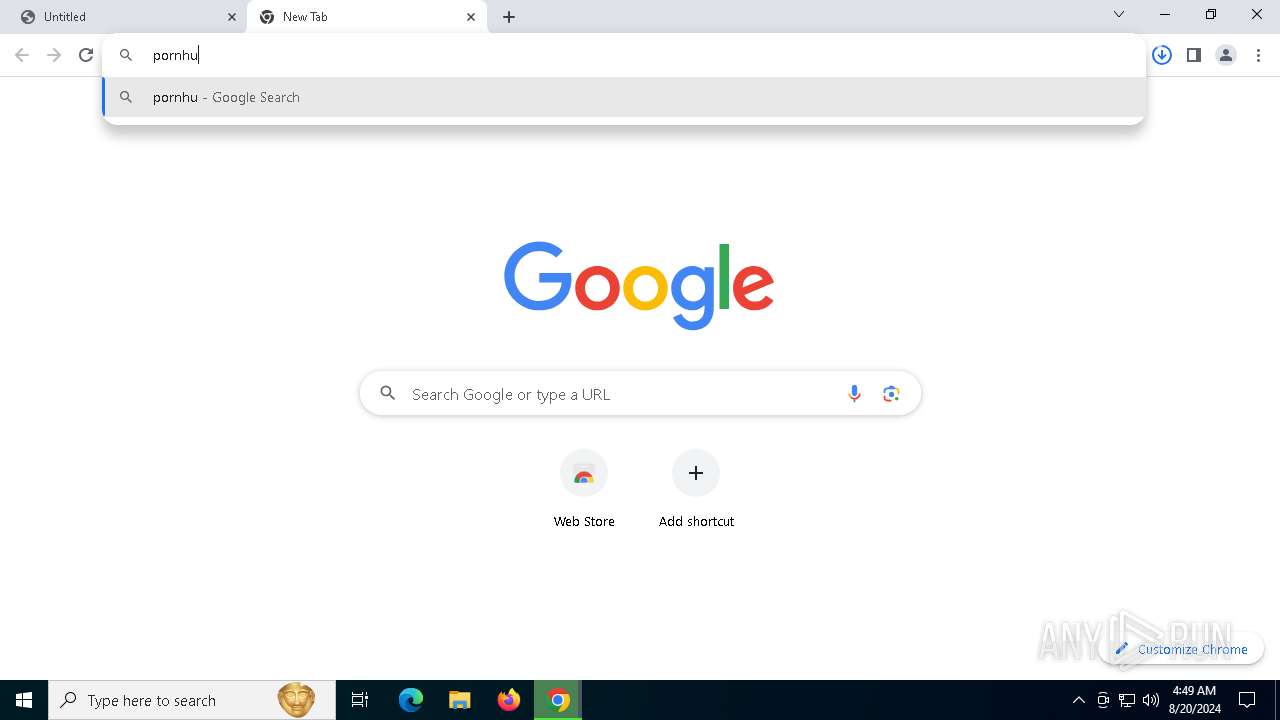
Potential Corporate Privacy Violation
- TOEIC Secure Browser.exe (PID: 7592)
- msedgewebview2.exe (PID: 7964)
Reads security settings of Internet Explorer
- TOEIC Secure Browser.exe (PID: 7592)
- msedgewebview2.exe (PID: 2360)
Checks Windows Trust Settings
- TOEIC Secure Browser.exe (PID: 7592)
Application launched itself
- msedgewebview2.exe (PID: 2360)
Reads the date of Windows installation
- TOEIC Secure Browser.exe (PID: 7592)
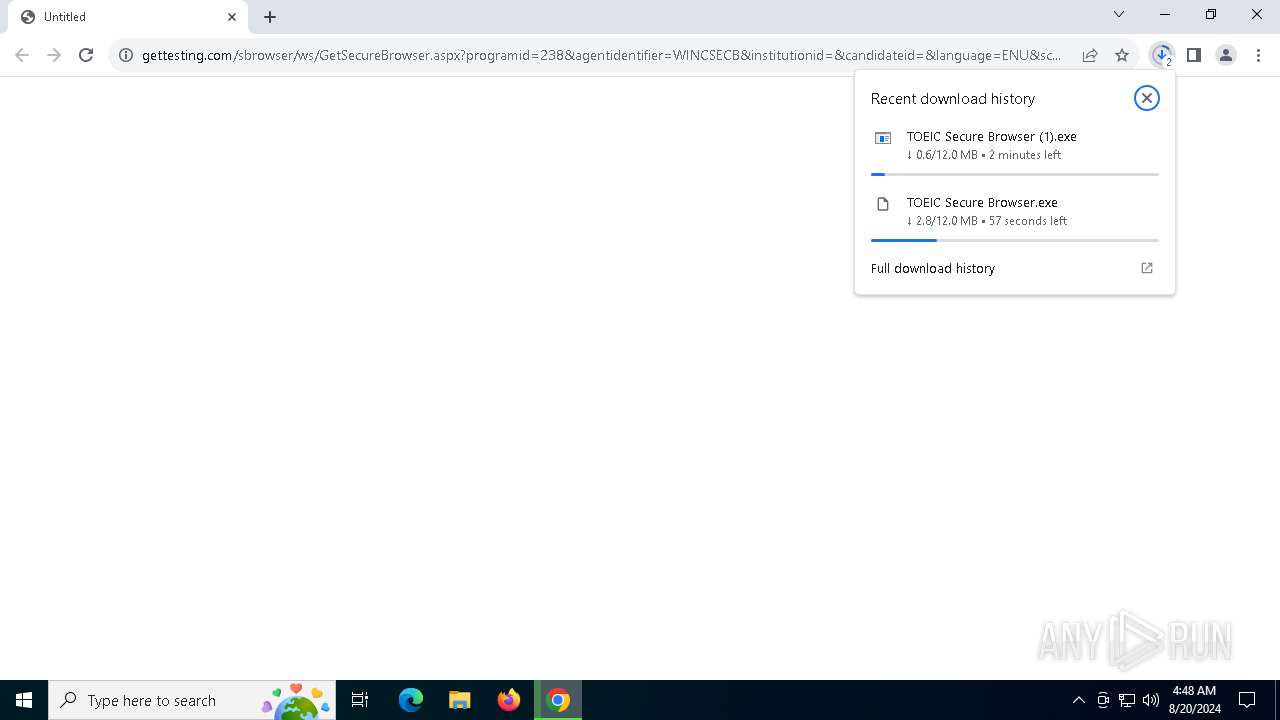
Drops the executable file immediately after the start
- TOEIC Secure Browser.exe (PID: 7592)
INFO
Application launched itself
- chrome.exe (PID: 6732)
Reads the computer name
- SignInfoConsole.exe (PID: 7712)
- SignInfoConsole.exe (PID: 5656)
- SignInfoConsole.exe (PID: 6124)
- msedgewebview2.exe (PID: 2360)
- msedgewebview2.exe (PID: 7964)
- msedgewebview2.exe (PID: 3980)
- msedgewebview2.exe (PID: 3244)
- msedgewebview2.exe (PID: 1480)
- TOEIC Secure Browser.exe (PID: 7592)
Reads Microsoft Office registry keys
- chrome.exe (PID: 6732)
The process uses the downloaded file
- chrome.exe (PID: 6364)
- chrome.exe (PID: 2816)
- TOEIC Secure Browser.exe (PID: 7592)
- chrome.exe (PID: 6732)
Executable content was dropped or overwritten
- chrome.exe (PID: 2232)
- chrome.exe (PID: 6732)
Checks supported languages
- TOEIC Secure Browser.exe (PID: 7592)
- SignInfoConsole.exe (PID: 7712)
- SignInfoConsole.exe (PID: 5656)
- msedgewebview2.exe (PID: 2360)
- SignInfoConsole.exe (PID: 6124)
- msedgewebview2.exe (PID: 6532)
- msedgewebview2.exe (PID: 3980)
- msedgewebview2.exe (PID: 7964)
- msedgewebview2.exe (PID: 6224)
- msedgewebview2.exe (PID: 3244)
- msedgewebview2.exe (PID: 1480)
Disables trace logs
- TOEIC Secure Browser.exe (PID: 7592)
Reads the machine GUID from the registry
- SignInfoConsole.exe (PID: 7712)
- SignInfoConsole.exe (PID: 5656)
- SignInfoConsole.exe (PID: 6124)
- msedgewebview2.exe (PID: 2360)
- TOEIC Secure Browser.exe (PID: 7592)
Reads the software policy settings
- TOEIC Secure Browser.exe (PID: 7592)
Checks proxy server information
- TOEIC Secure Browser.exe (PID: 7592)
- msedgewebview2.exe (PID: 2360)
Create files in a temporary directory
- msedgewebview2.exe (PID: 2360)
- msedgewebview2.exe (PID: 6532)
- msedgewebview2.exe (PID: 7964)
- TOEIC Secure Browser.exe (PID: 7592)
Process checks computer location settings
- msedgewebview2.exe (PID: 2360)
- msedgewebview2.exe (PID: 3244)
- TOEIC Secure Browser.exe (PID: 7592)
- msedgewebview2.exe (PID: 1480)
Creates files or folders in the user directory
- TOEIC Secure Browser.exe (PID: 7592)
Reads Environment values
- msedgewebview2.exe (PID: 2360)
- msedgewebview2.exe (PID: 7964)
- msedgewebview2.exe (PID: 3980)
- msedgewebview2.exe (PID: 6224)
- msedgewebview2.exe (PID: 3244)
- msedgewebview2.exe (PID: 1480)
- TOEIC Secure Browser.exe (PID: 7592)
Reads product name
- TOEIC Secure Browser.exe (PID: 7592)
Reads CPU info
- TOEIC Secure Browser.exe (PID: 7592)
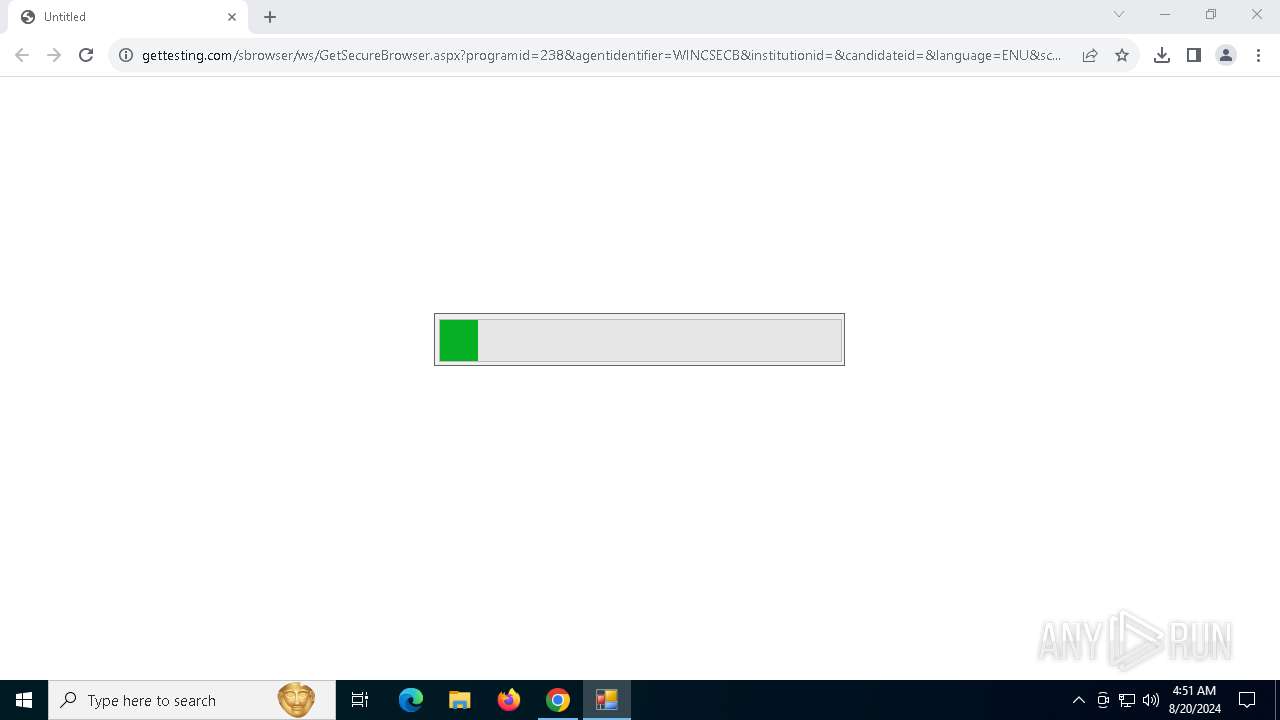
Themida protector has been detected
- TOEIC Secure Browser.exe (PID: 7592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
183
Monitored processes
42
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5552 --field-trial-handle=1892,i,7433163888044889862,16141288801834583376,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5700 --field-trial-handle=1892,i,7433163888044889862,16141288801834583376,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --mojo-platform-channel-handle=4164 --field-trial-handle=1892,i,7433163888044889862,16141288801834583376,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1480 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\msedgewebview2.exe" --type=renderer --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\.WebView2\EBWebView" --webview-exe-name="TOEIC Secure Browser.exe" --webview-exe-version=14.2.2.0 --embedded-browser-webview=1 --embedded-browser-webview-dpi-awareness=0 --edge-webview-custom-scheme --no-appcompat-clear --autoplay-policy=no-user-gesture-required --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --js-flags="--harmony-weak-refs-with-cleanup-some --expose-gc --ms-user-locale=" --mojo-platform-channel-handle=4620 --field-trial-handle=2060,i,2726217841837806526,1185947773298533205,262144 --enable-features=MojoIpcz --disable-features=OverscrollHistoryNavigation,msExperimentalScrolling --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge WebView2 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1568 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SignInfoConsole.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5280 --field-trial-handle=1892,i,7433163888044889862,16141288801834583376,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3312 --field-trial-handle=1892,i,7433163888044889862,16141288801834583376,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2360 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\msedgewebview2.exe" --embedded-browser-webview=1 --webview-exe-name="TOEIC Secure Browser.exe" --webview-exe-version=14.2.2.0 --user-data-dir="C:\Users\admin\AppData\Local\Temp\.WebView2\EBWebView" --noerrdialogs --embedded-browser-webview-dpi-awareness=0 --edge-webview-custom-scheme --autoplay-policy=no-user-gesture-required --disable-features=OverscrollHistoryNavigation,msExperimentalScrolling --enable-features=MojoIpcz --mojo-named-platform-channel-pipe=7592.7300.9685530950017903610 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\msedgewebview2.exe | TOEIC Secure Browser.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge WebView2 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5604 --field-trial-handle=1892,i,7433163888044889862,16141288801834583376,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5676 --field-trial-handle=1892,i,7433163888044889862,16141288801834583376,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
23 320
Read events
23 198
Write events
113
Delete events
9
Modification events
| (PID) Process: | (6732) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6732) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6732) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6732) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6732) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6732) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6732) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6732) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (6732) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6732) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
13
Suspicious files
239
Text files
81
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF11f78c.TMP | — | |
MD5:— | SHA256:— | |||
| 6732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF11f7ca.TMP | — | |
MD5:— | SHA256:— | |||
| 6732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF11f75d.TMP | text | |
MD5:139F545948FC1F10256A27E3C2CEF062 | SHA256:9399CC6F9C335015E086DB37208B1816A7831221A005B04AC83C4F86CC04230D | |||
| 6732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:723783C35EAEEE1492EDB30847AE6750 | SHA256:C29323F784CF873BF34992E7A2B4630B19641BF42980109E31D5AF2D487DF6F8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
84
DNS requests
57
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6524 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
2228 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6336 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6560 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kmmdmy3ouapv6ku7g2gud2axmu_2024.8.18.1/jflhchccmppkfebkiaminageehmchikm_2024.08.18.01_all_nd4t4j4xmonm245kmlj52pp5gq.crx3 | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6560 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kmmdmy3ouapv6ku7g2gud2axmu_2024.8.18.1/jflhchccmppkfebkiaminageehmchikm_2024.08.18.01_all_nd4t4j4xmonm245kmlj52pp5gq.crx3 | unknown | — | — | whitelisted |
6560 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kmmdmy3ouapv6ku7g2gud2axmu_2024.8.18.1/jflhchccmppkfebkiaminageehmchikm_2024.08.18.01_all_nd4t4j4xmonm245kmlj52pp5gq.crx3 | unknown | — | — | whitelisted |
6560 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kmmdmy3ouapv6ku7g2gud2axmu_2024.8.18.1/jflhchccmppkfebkiaminageehmchikm_2024.08.18.01_all_nd4t4j4xmonm245kmlj52pp5gq.crx3 | unknown | — | — | whitelisted |
6560 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kmmdmy3ouapv6ku7g2gud2axmu_2024.8.18.1/jflhchccmppkfebkiaminageehmchikm_2024.08.18.01_all_nd4t4j4xmonm245kmlj52pp5gq.crx3 | unknown | — | — | whitelisted |
6560 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kmmdmy3ouapv6ku7g2gud2axmu_2024.8.18.1/jflhchccmppkfebkiaminageehmchikm_2024.08.18.01_all_nd4t4j4xmonm245kmlj52pp5gq.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2340 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
3308 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6732 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7000 | chrome.exe | 161.47.163.229:443 | www.gettesting.com | RACKSPACE | US | unknown |
7000 | chrome.exe | 74.125.206.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2228 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.gettesting.com |
| unknown |
accounts.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.google.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
4 ETPRO signatures available at the full report
Process | Message |
|---|---|
msedgewebview2.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\.WebView2 directory exists )
|