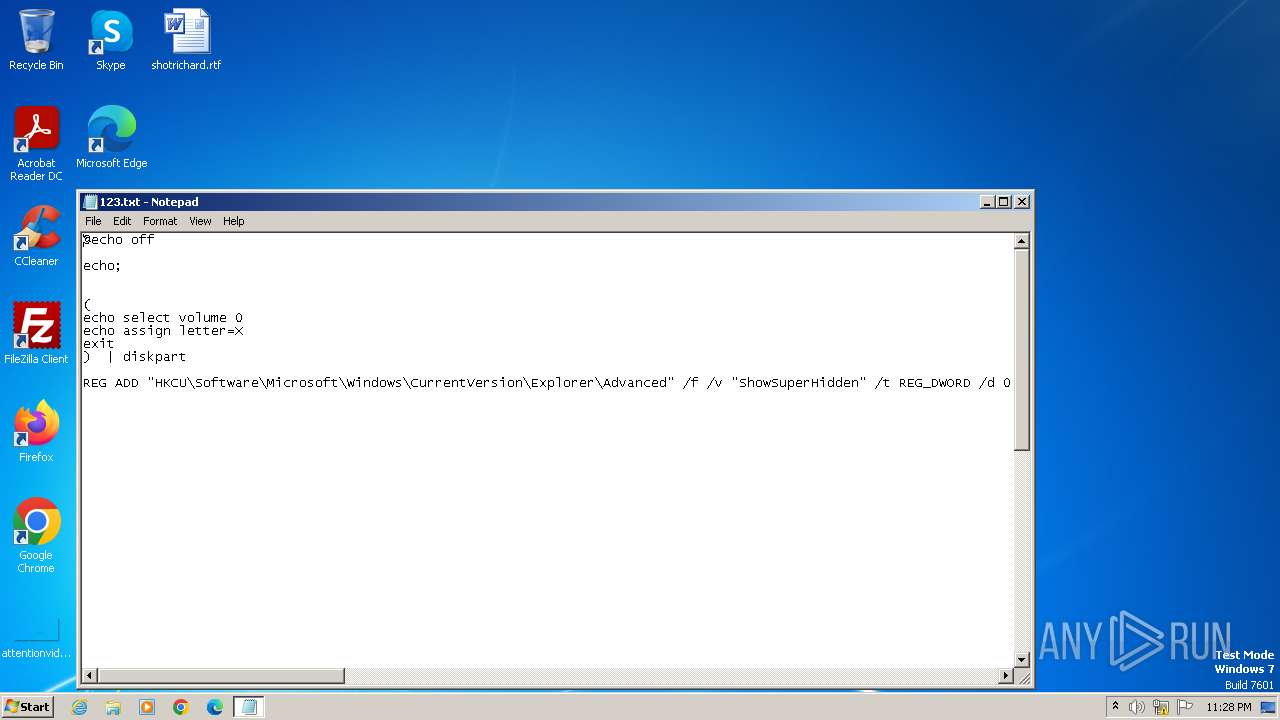
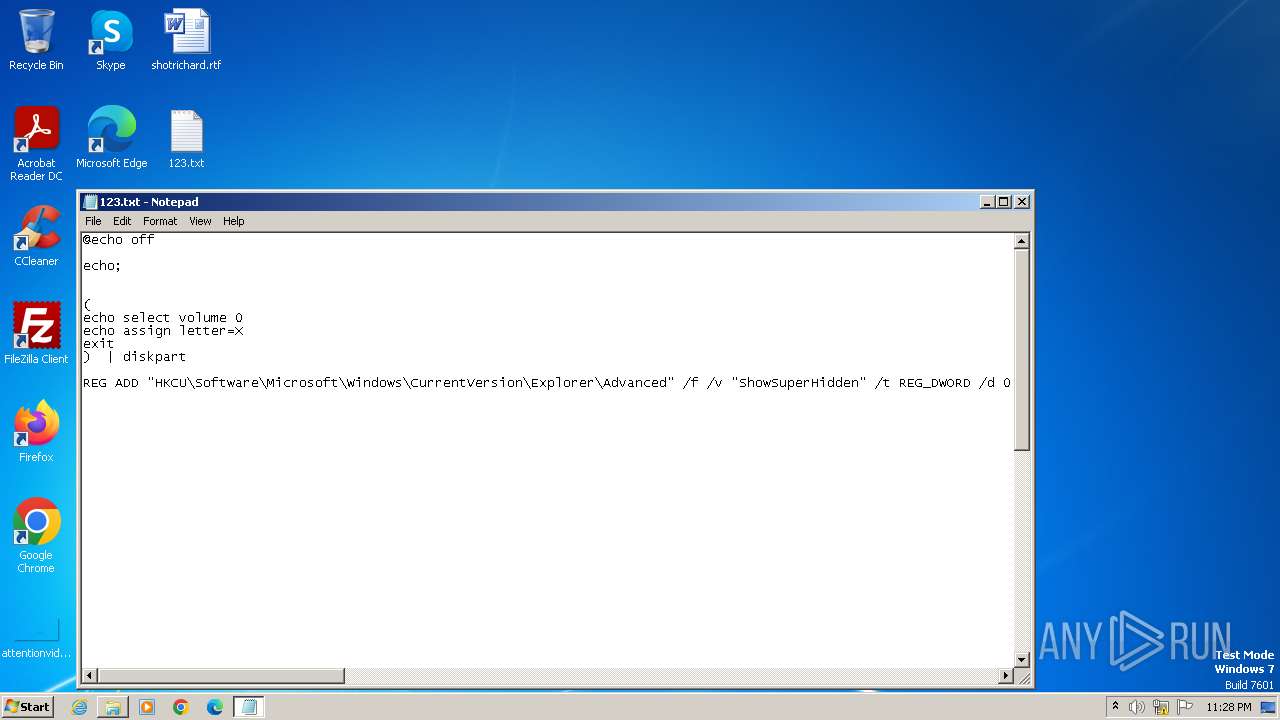
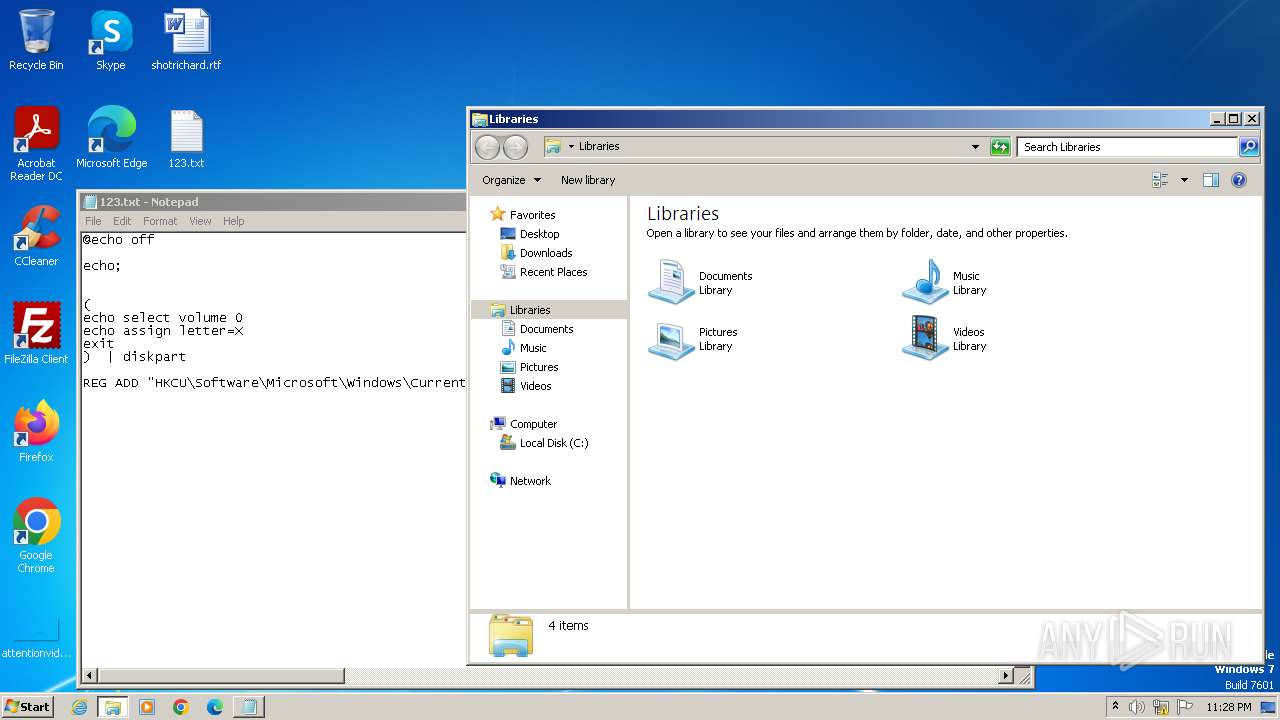
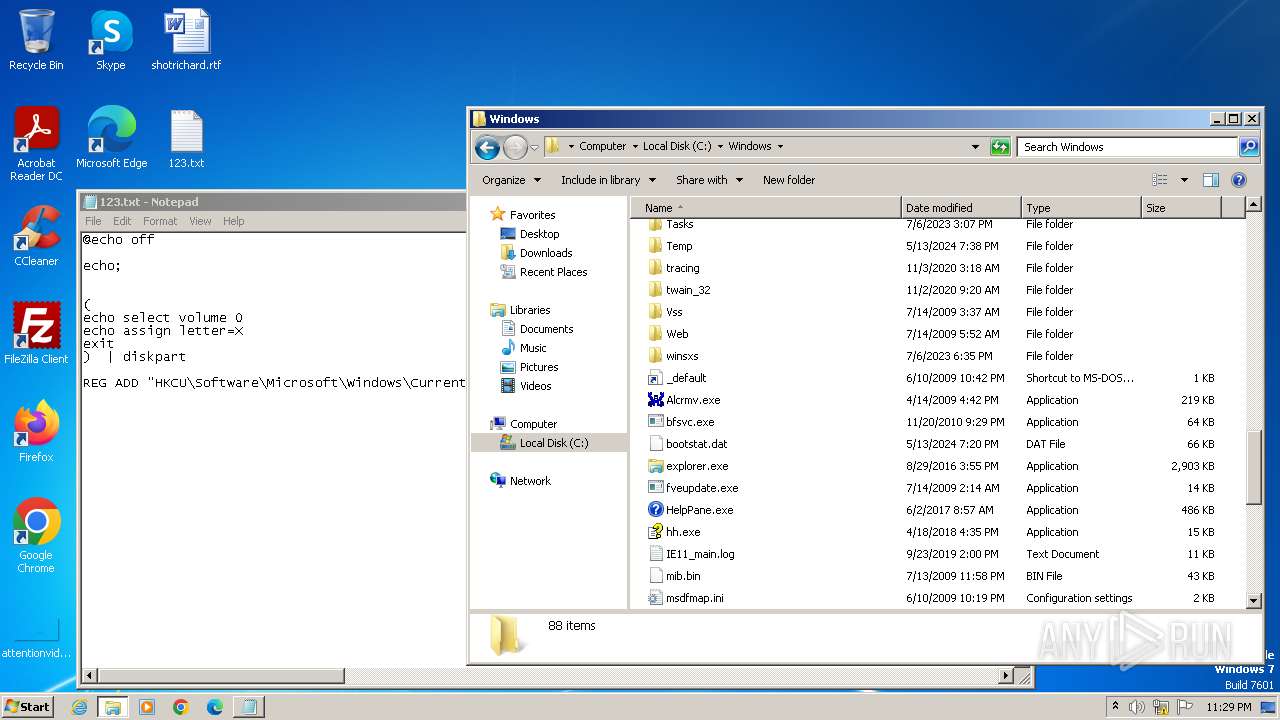
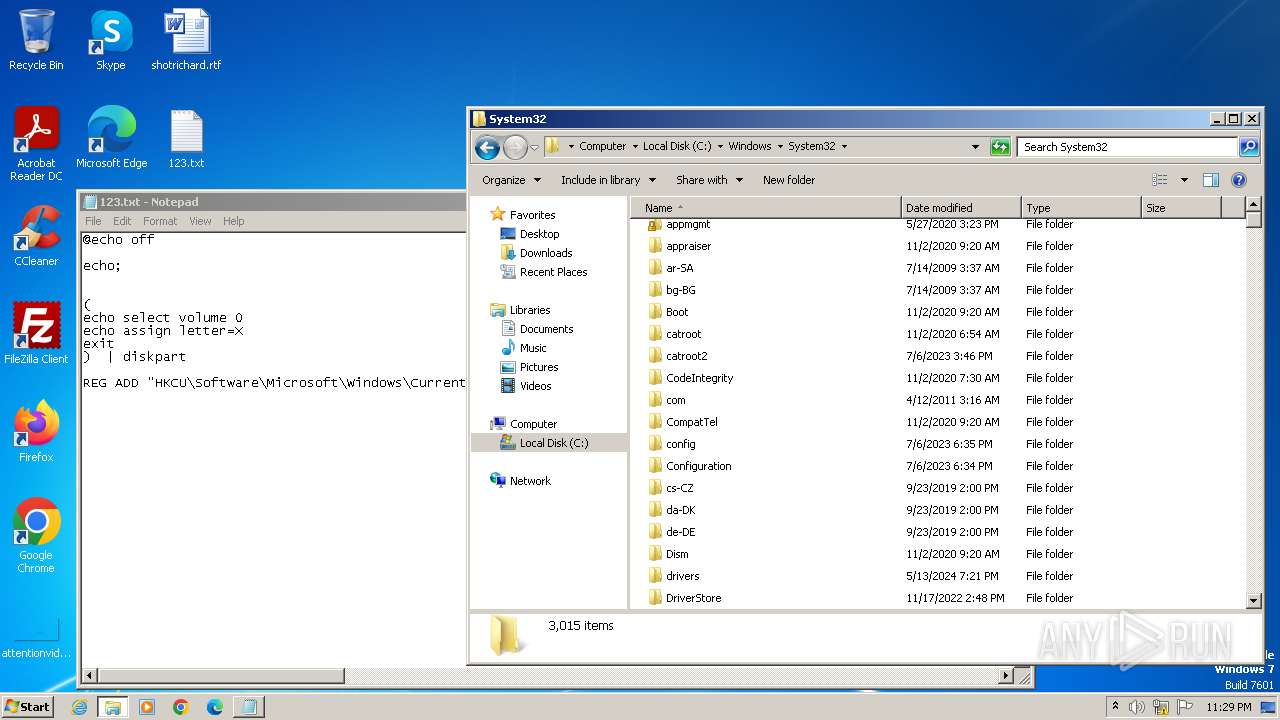
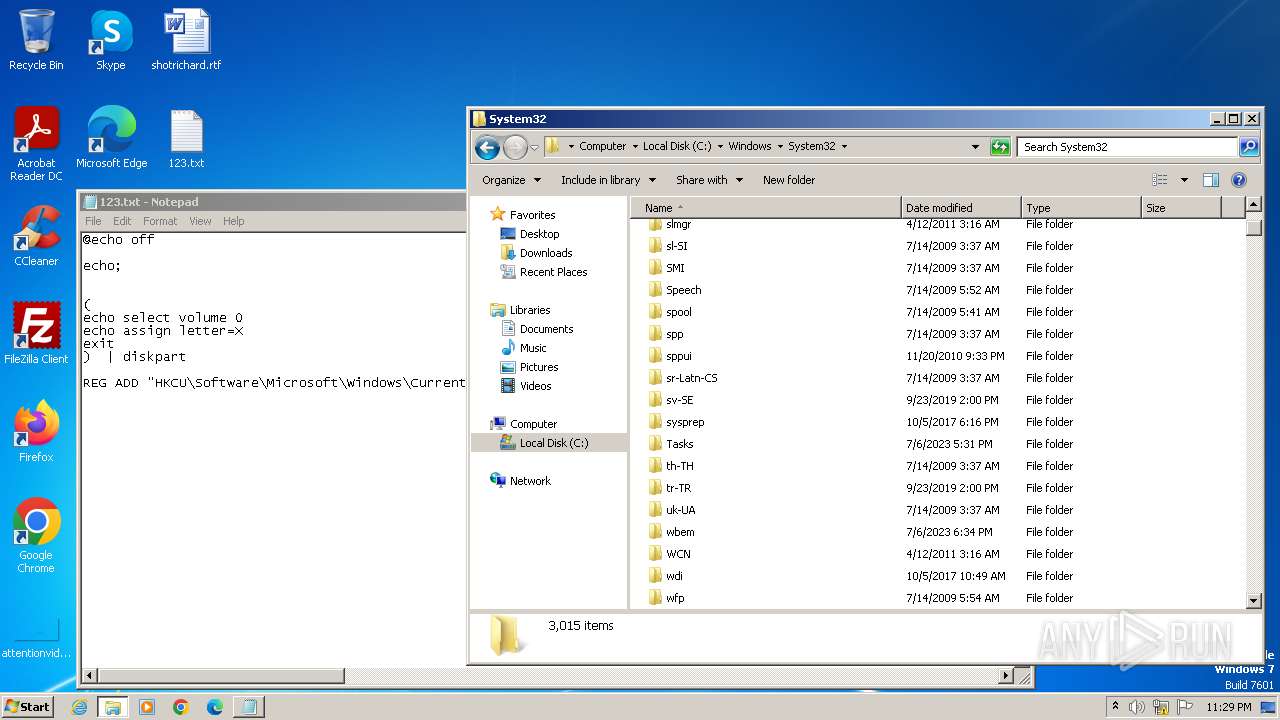
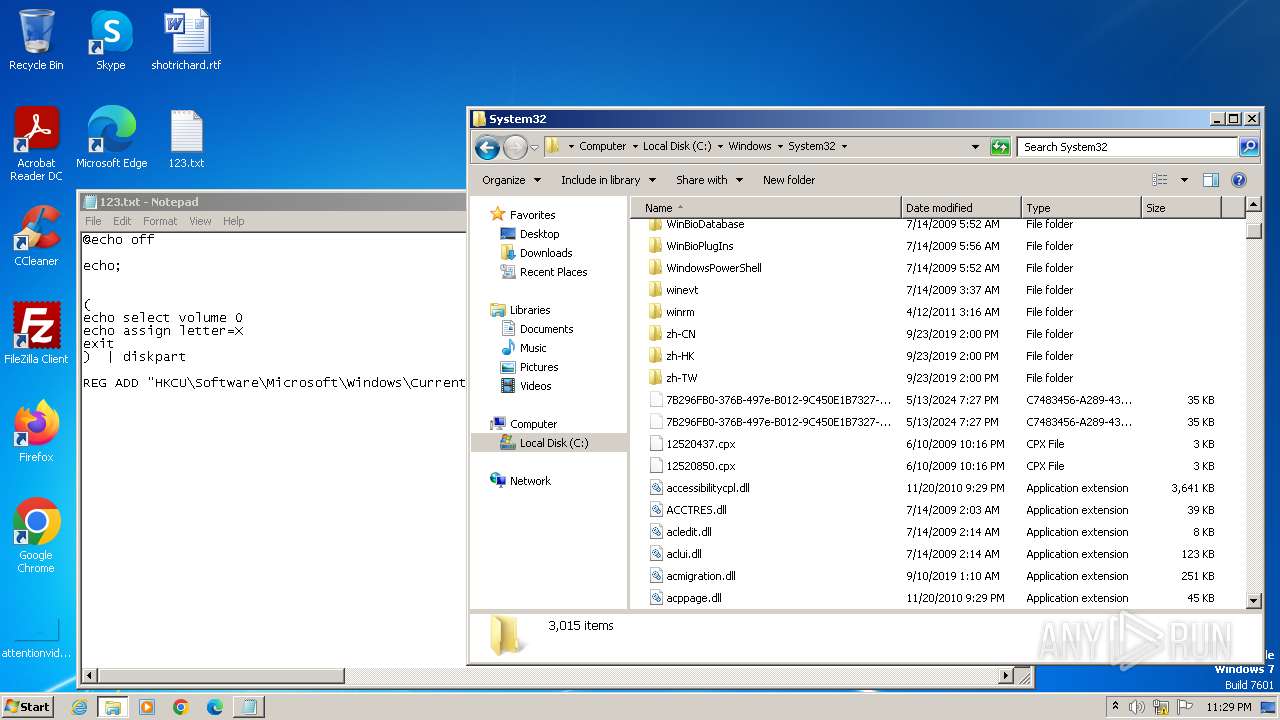
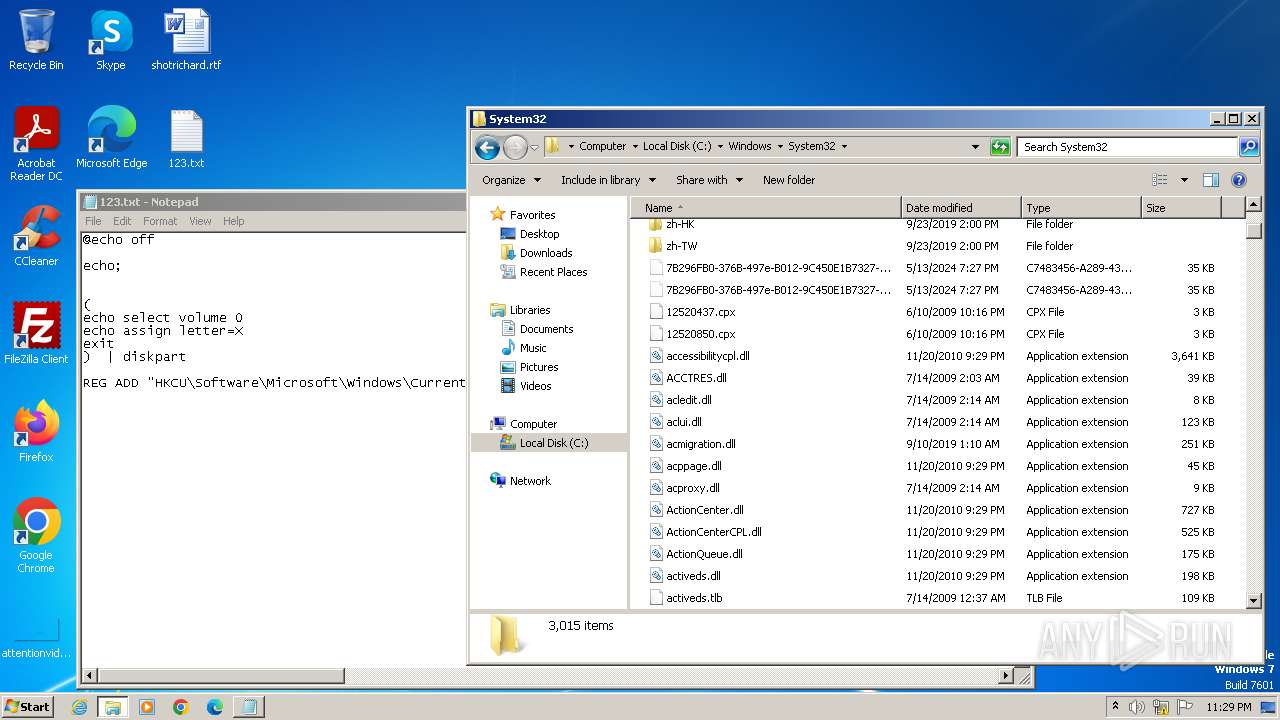
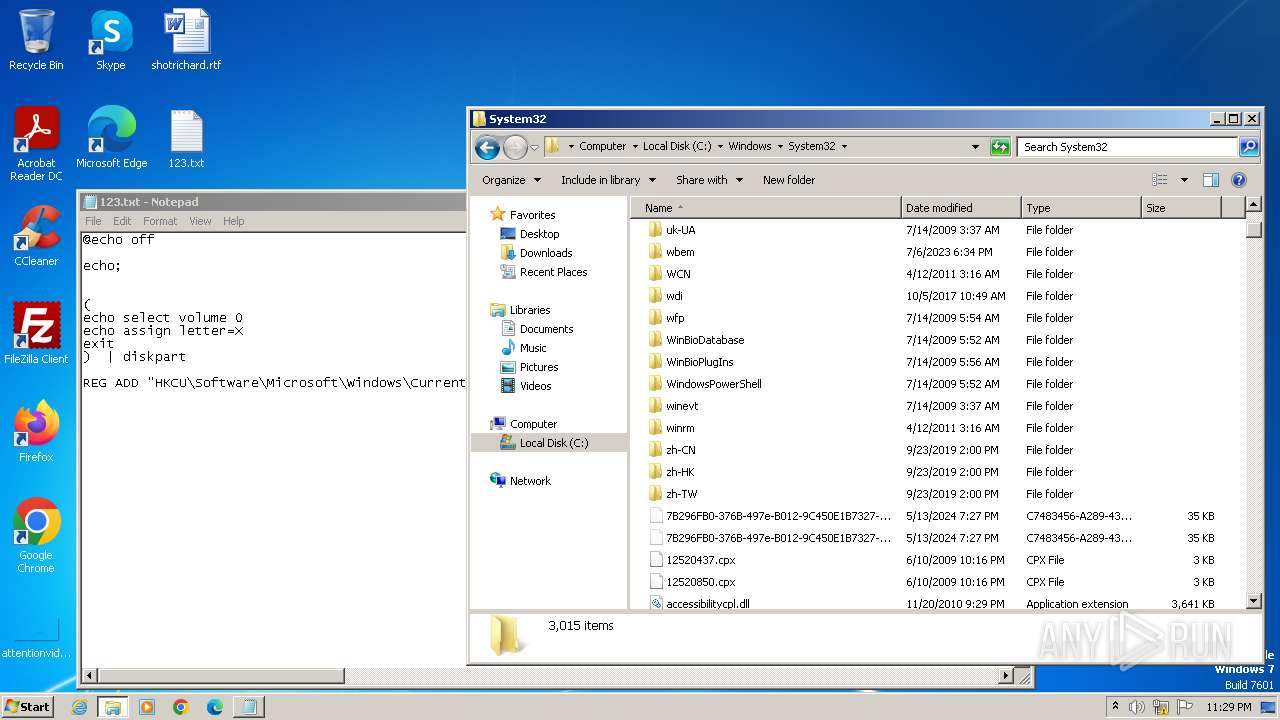
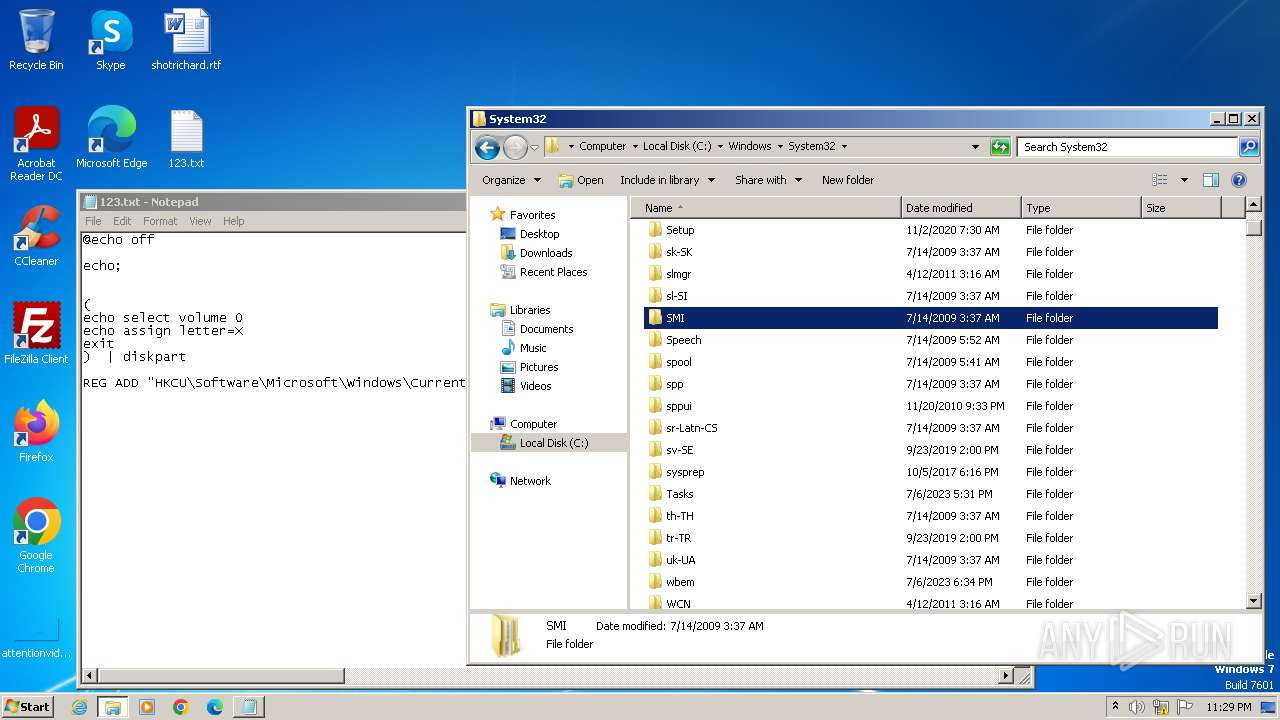
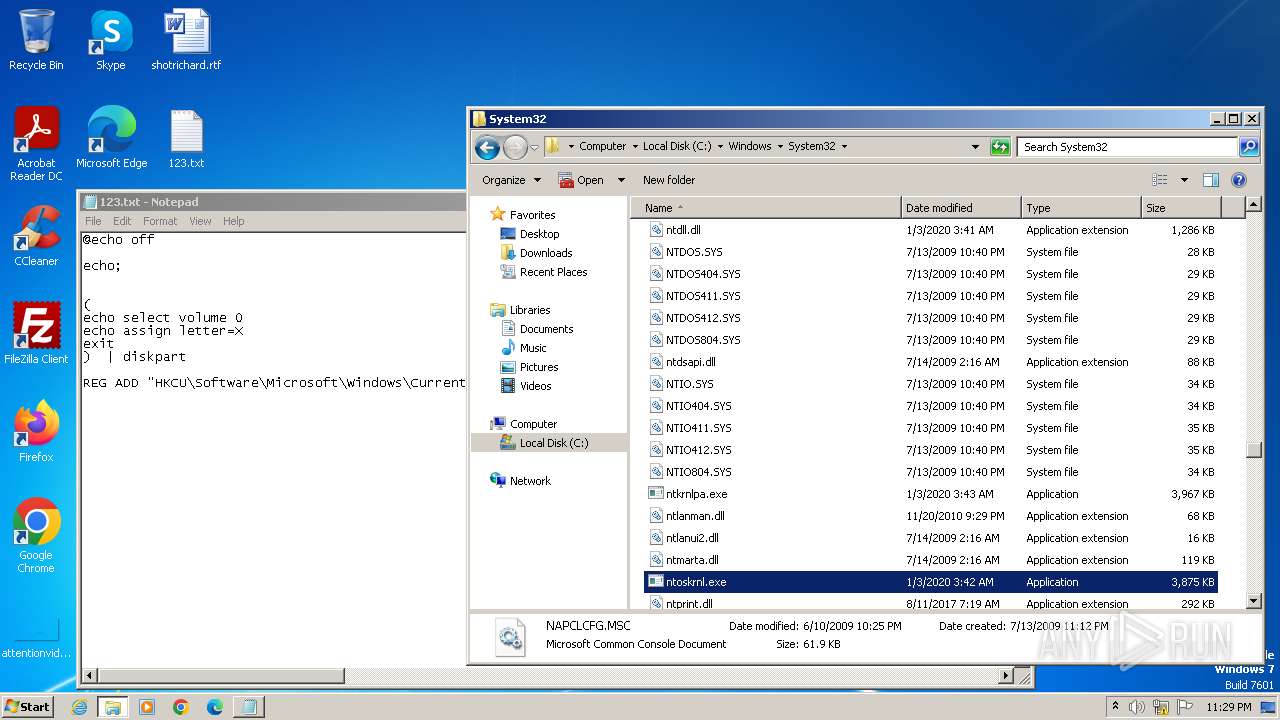
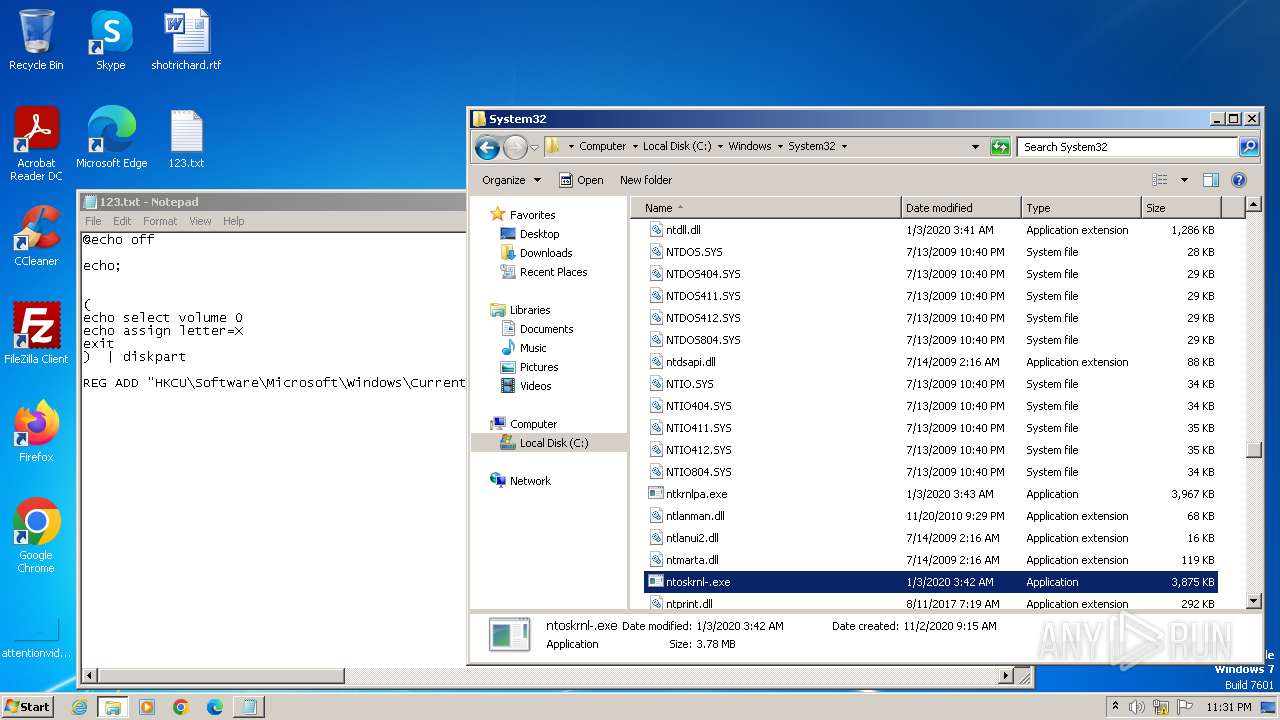
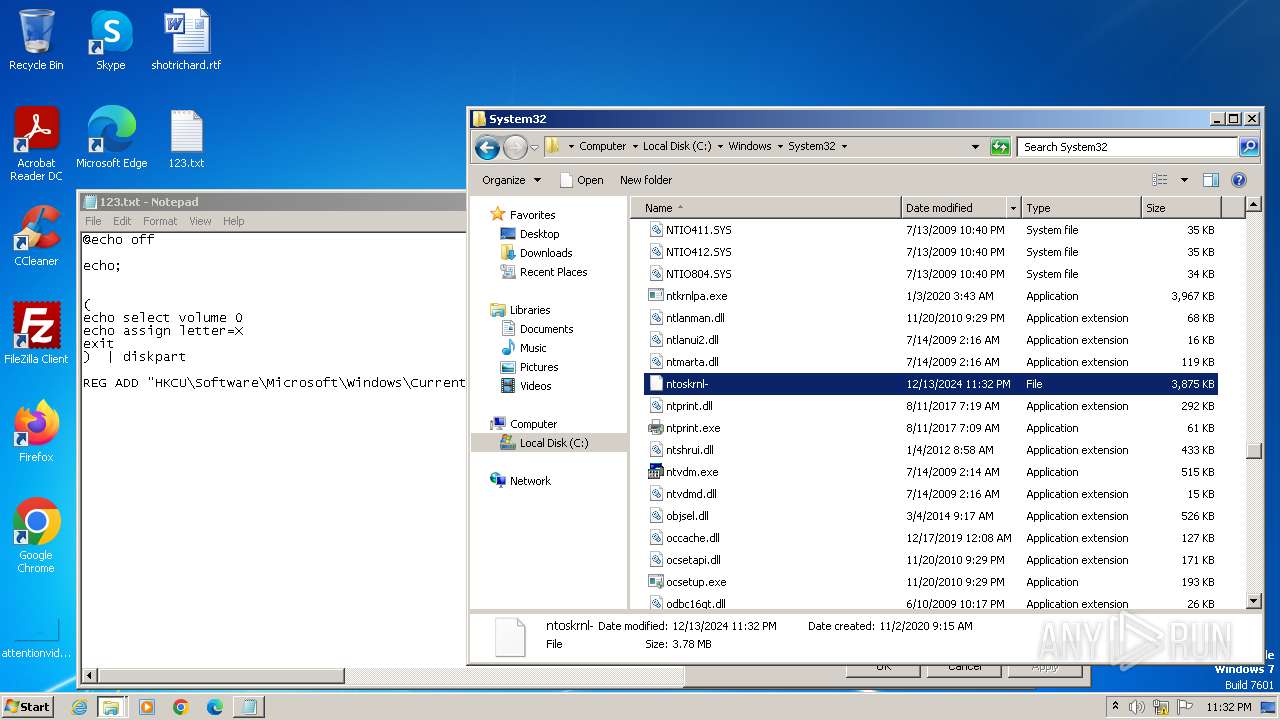
| File name: | 123.txt |
| Full analysis: | https://app.any.run/tasks/b47c8bb2-fa92-4726-90b3-931ddfcb7c2c |
| Verdict: | Malicious activity |
| Analysis date: | December 13, 2024, 23:28:31 |
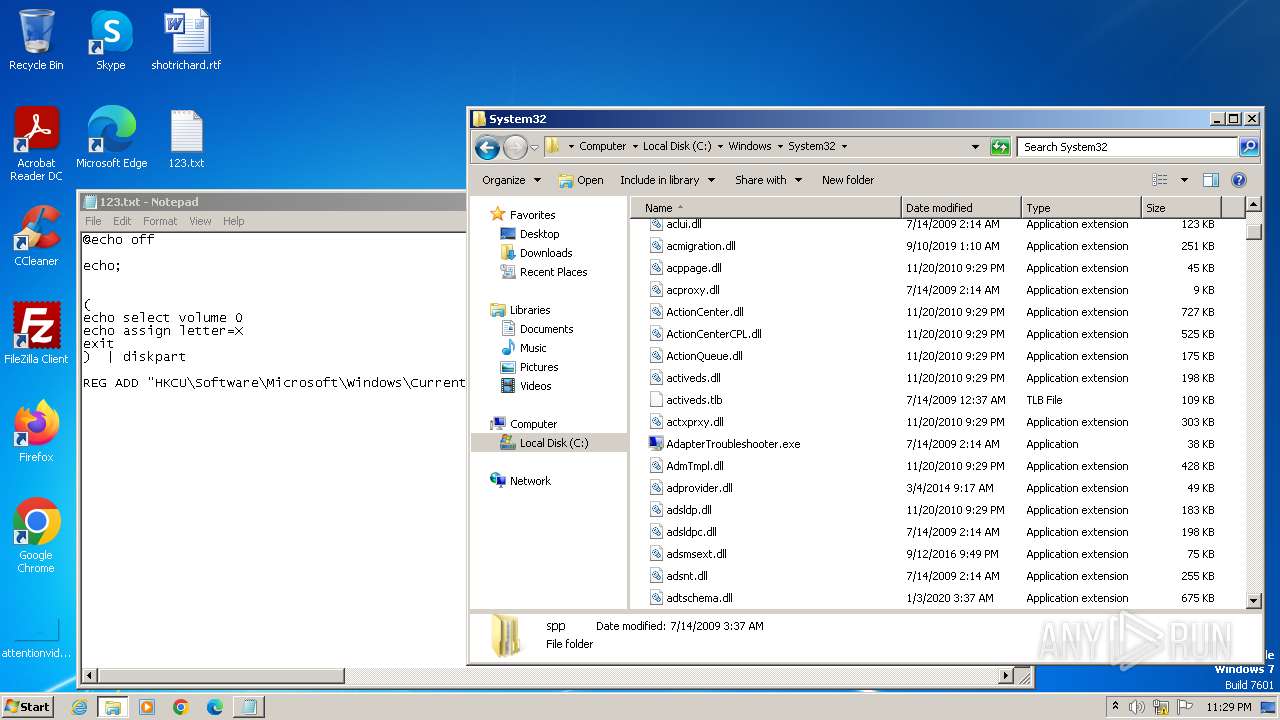
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
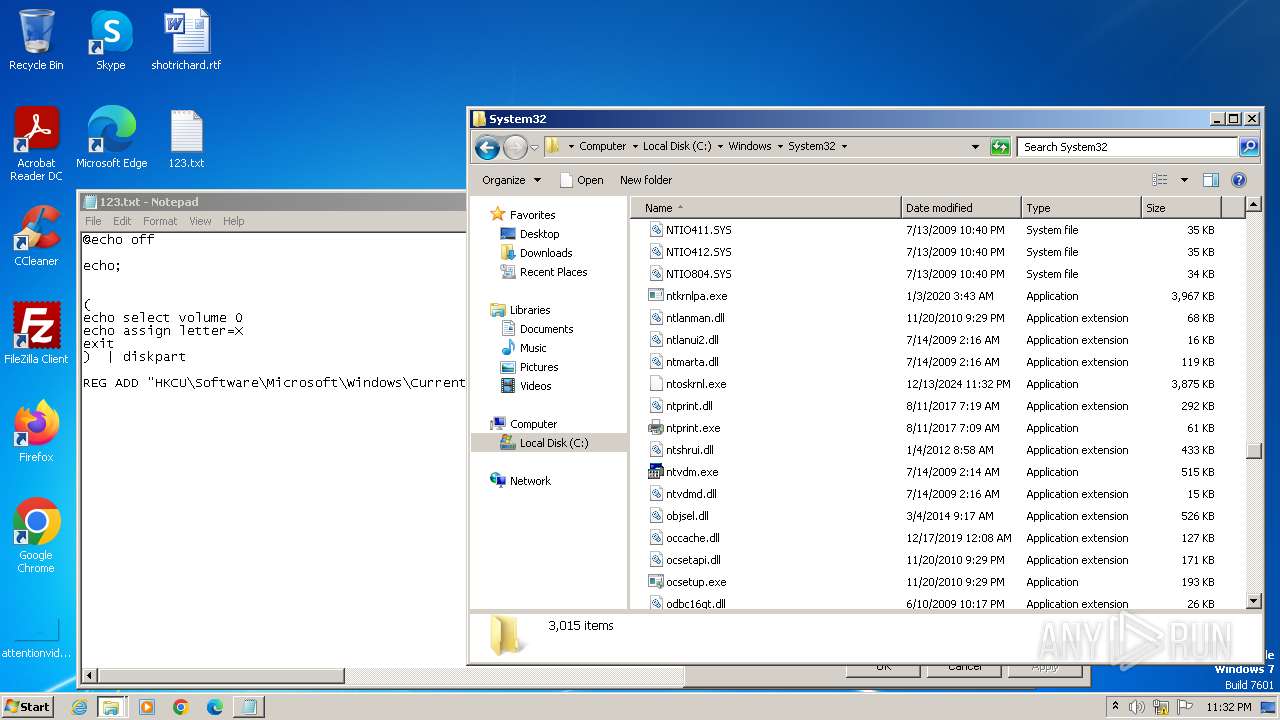
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with very long lines (424), with CRLF line terminators |
| MD5: | 27D782EACCCB2A76774EB1109C03AF6F |
| SHA1: | C8BF807D0726710911D584225CD5354AE1292CC0 |
| SHA256: | 0700FB8950DE3D3C68D60733D69209AB9EA4EE7ACB1E7D87ED68C080B4416AA9 |
| SSDEEP: | 24:foV7Pl0o+Fn0bt8w4yECKzZ1qBdyV7Pl0o+u3NtvDfyEFd:foRlH+FTTZ1qBdyRlH+Ip |
MALICIOUS
No malicious indicators.SUSPICIOUS
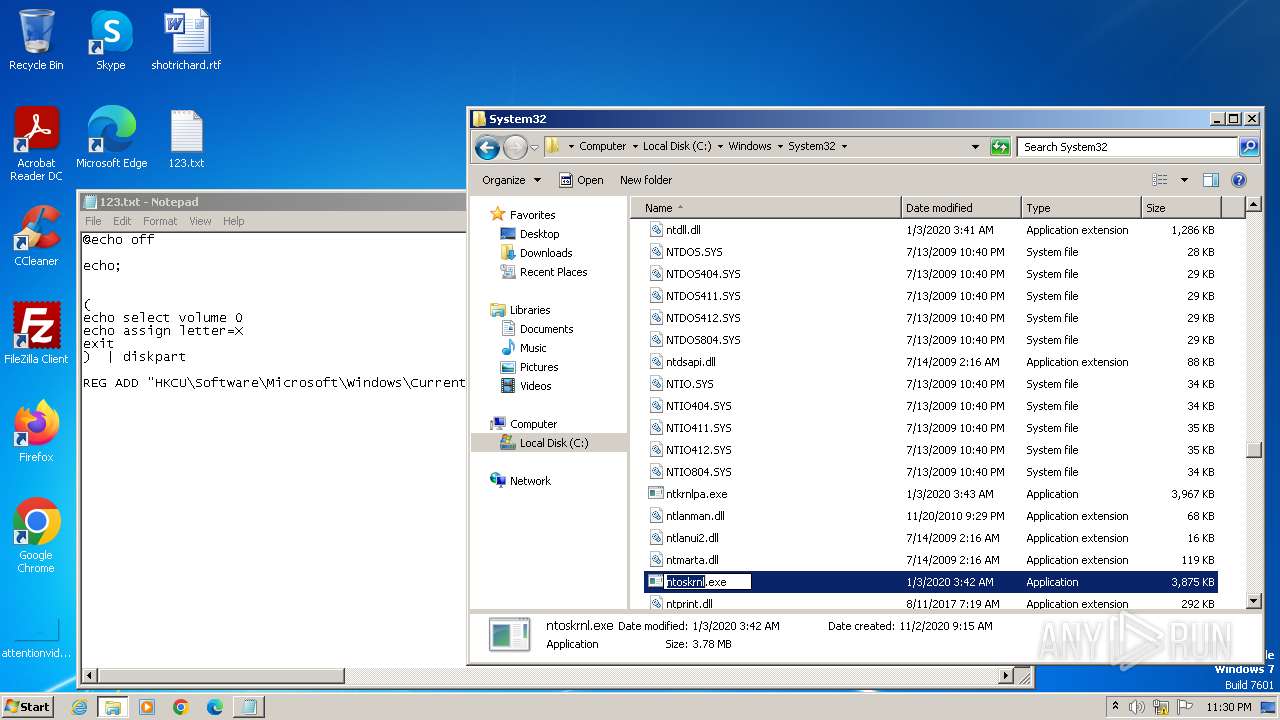
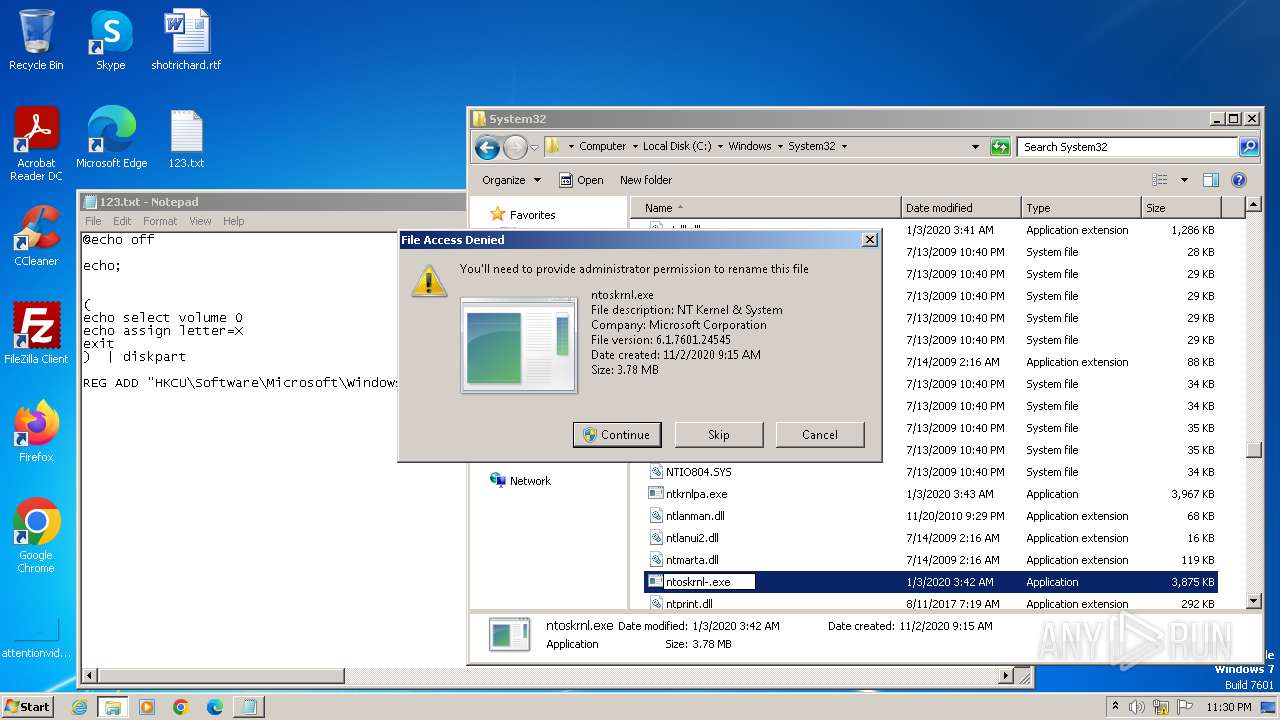
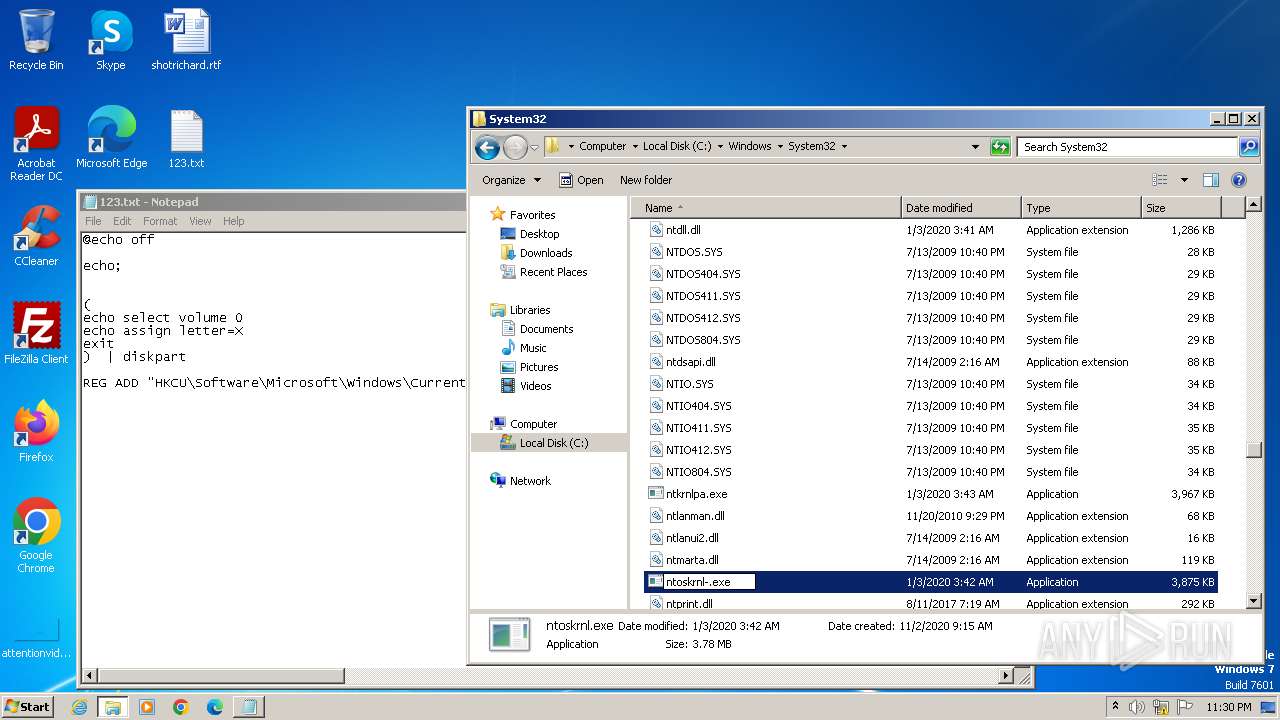
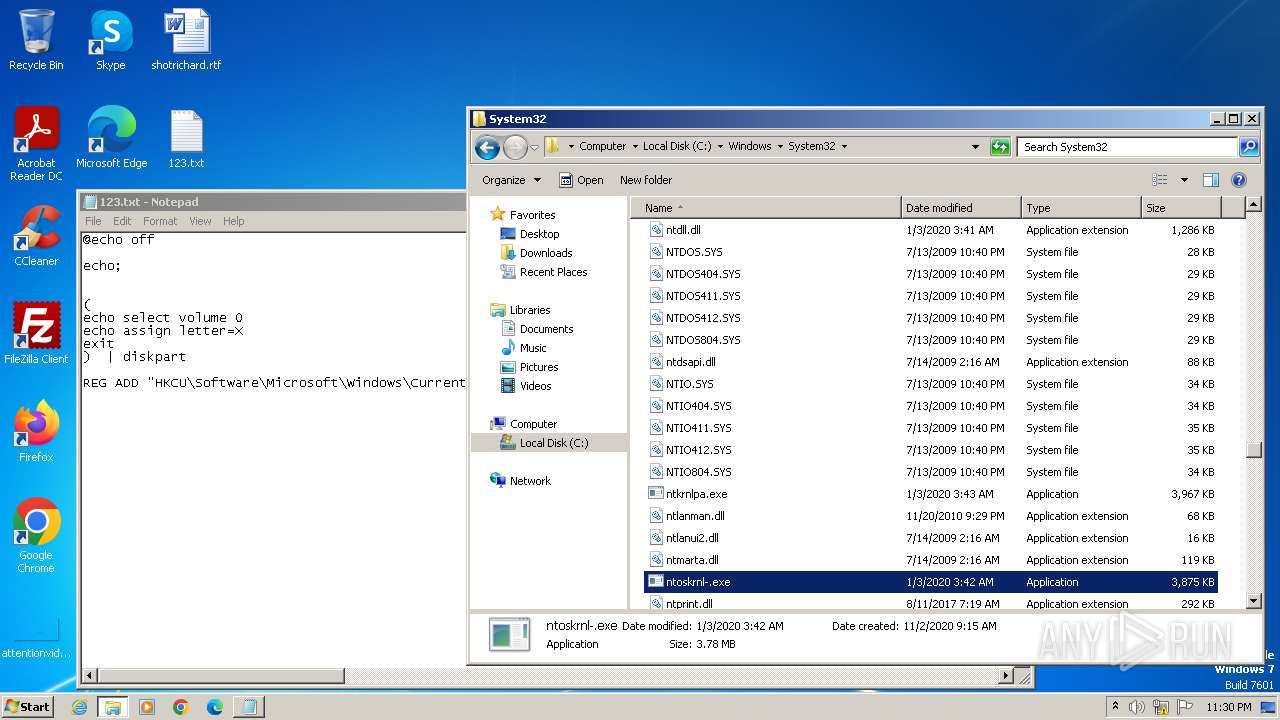
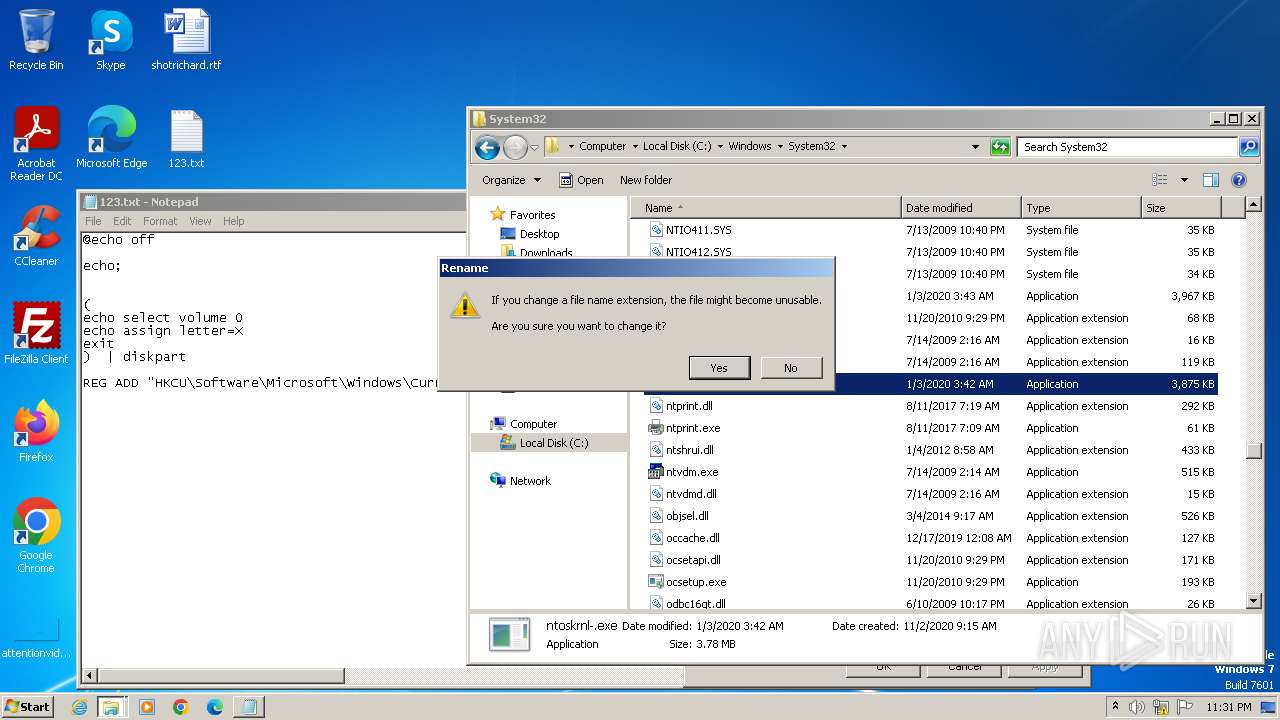
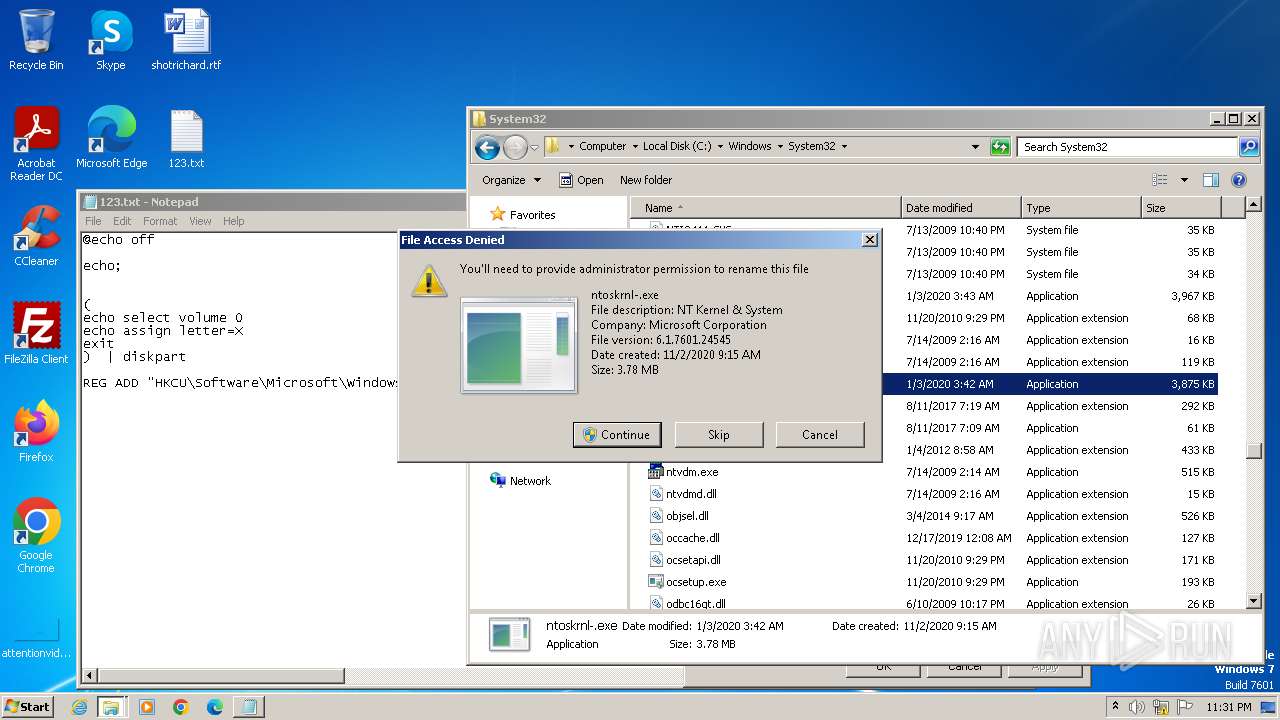
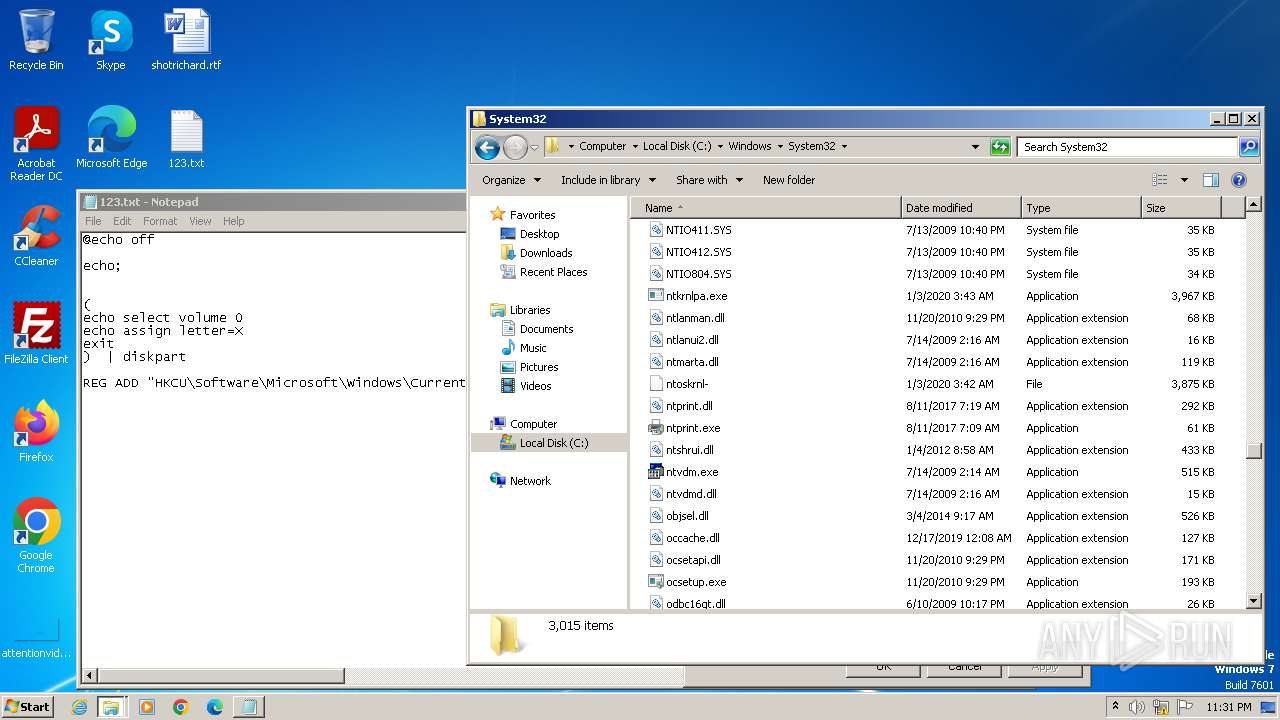
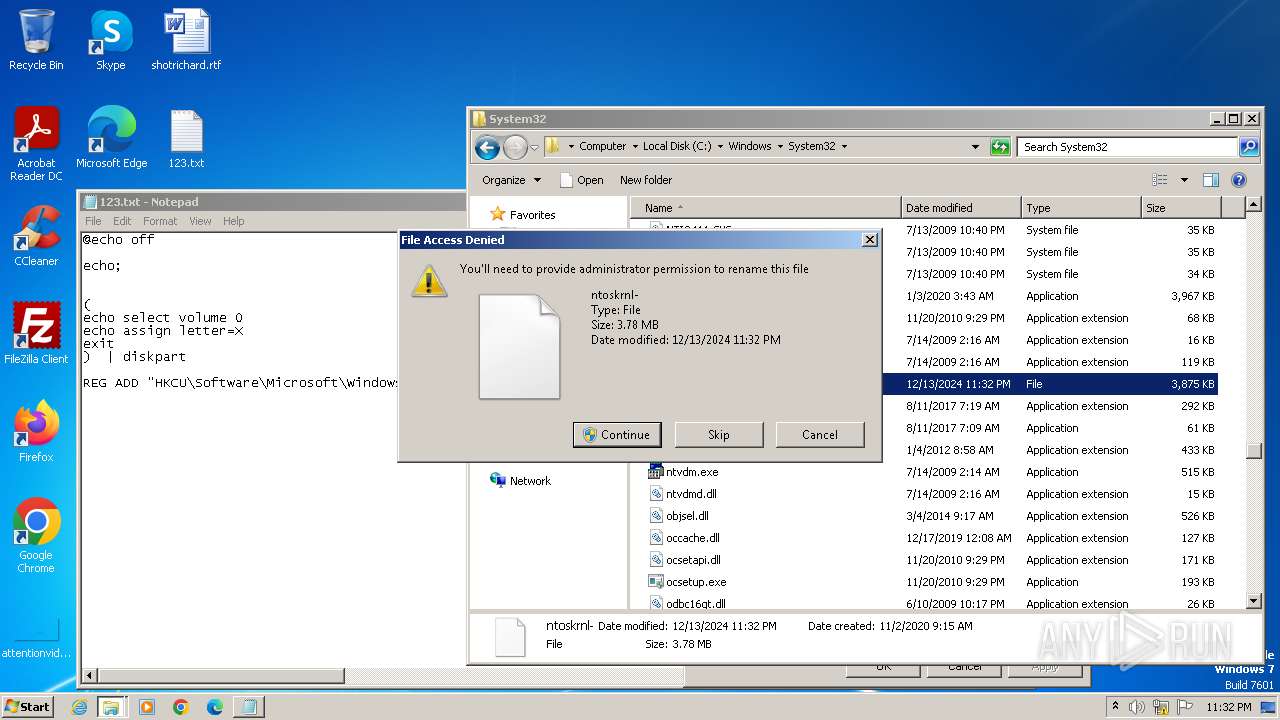
Executable content was dropped or overwritten
- dllhost.exe (PID: 3548)
- dllhost.exe (PID: 3732)
- notepad.exe (PID: 3780)
- dllhost.exe (PID: 1104)
Reads the Internet Settings
- rundll32.exe (PID: 3740)
- sipnotify.exe (PID: 1552)
Reads settings of System Certificates
- sipnotify.exe (PID: 1552)
The process executes via Task Scheduler
- sipnotify.exe (PID: 1552)
- ctfmon.exe (PID: 1592)
INFO
The sample compiled with english language support
- dllhost.exe (PID: 3548)
- dllhost.exe (PID: 3732)
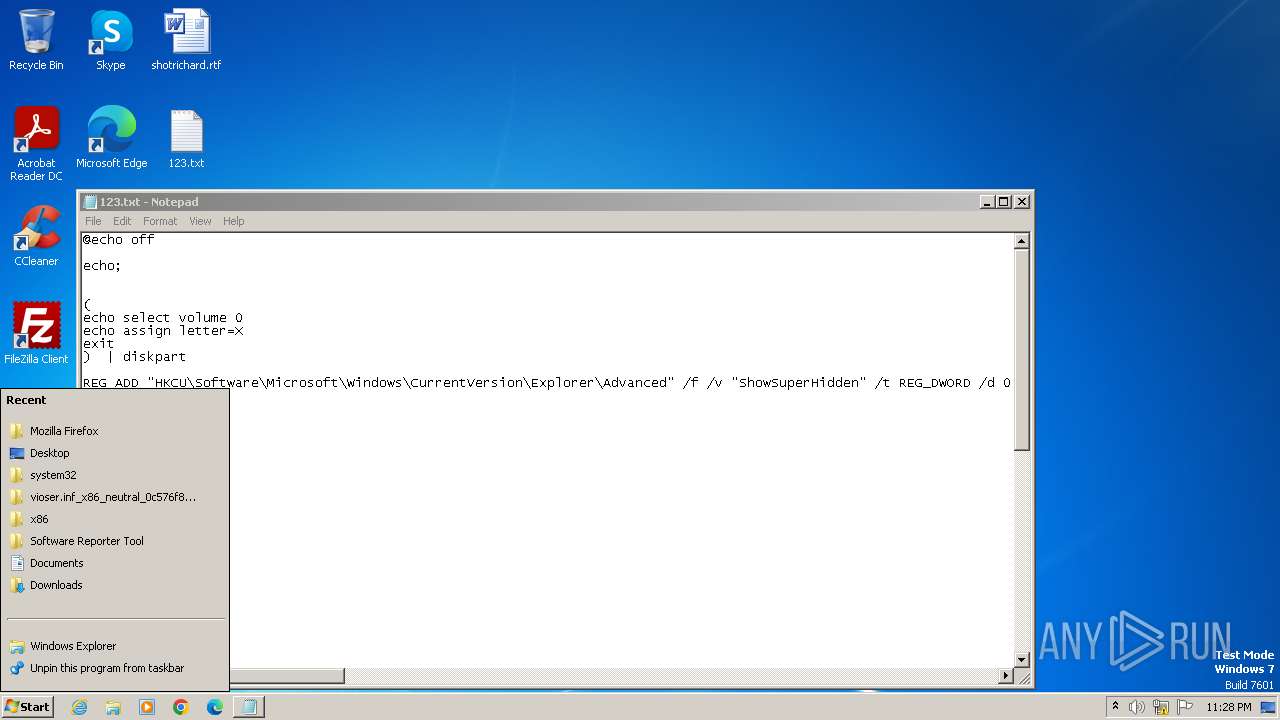
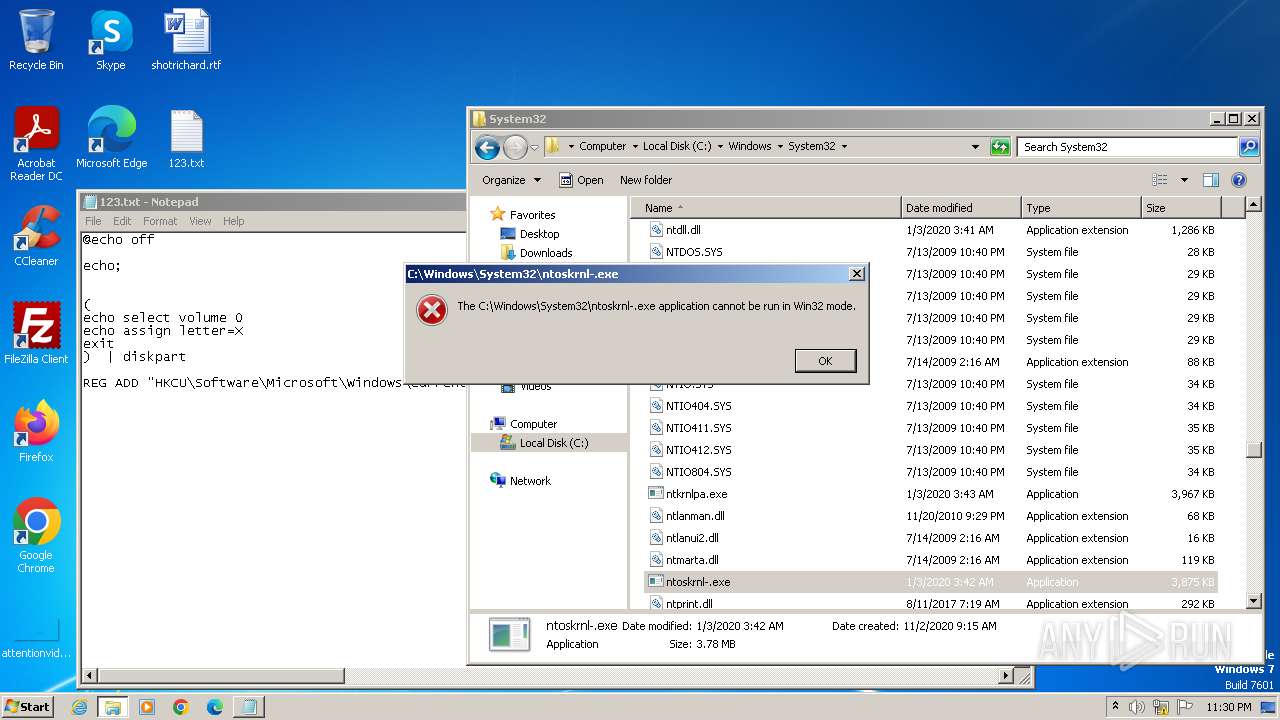
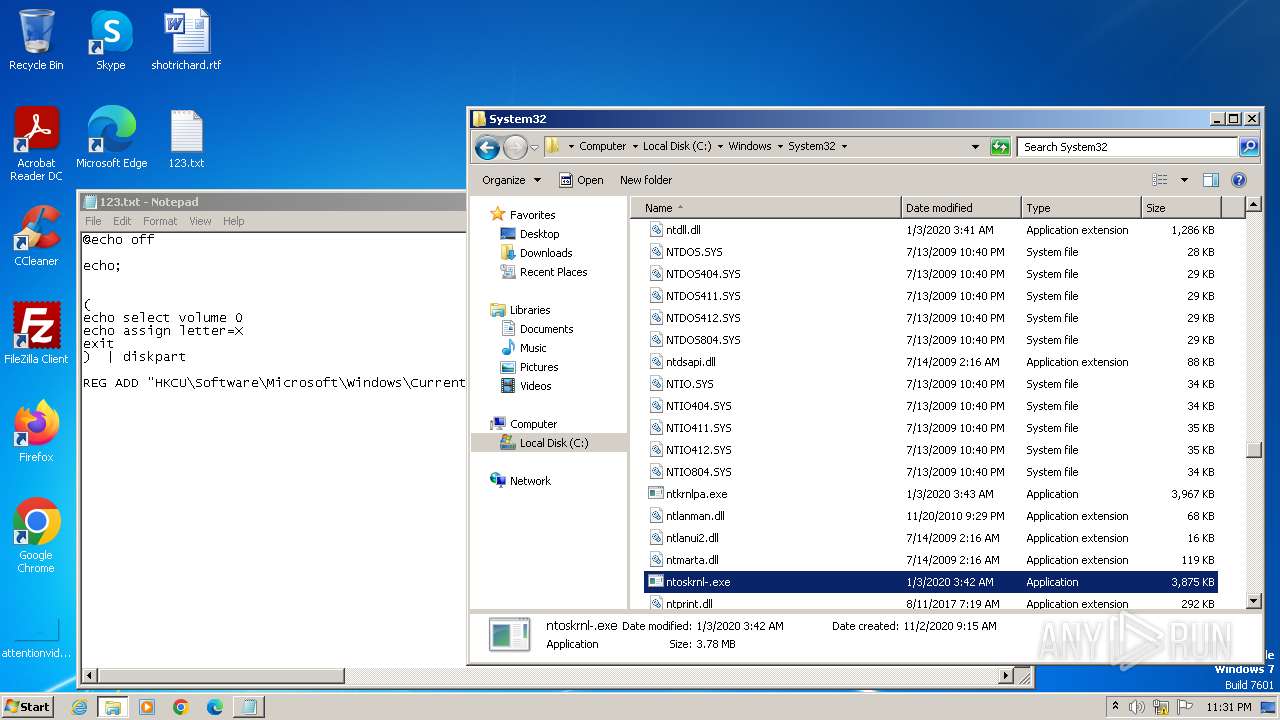
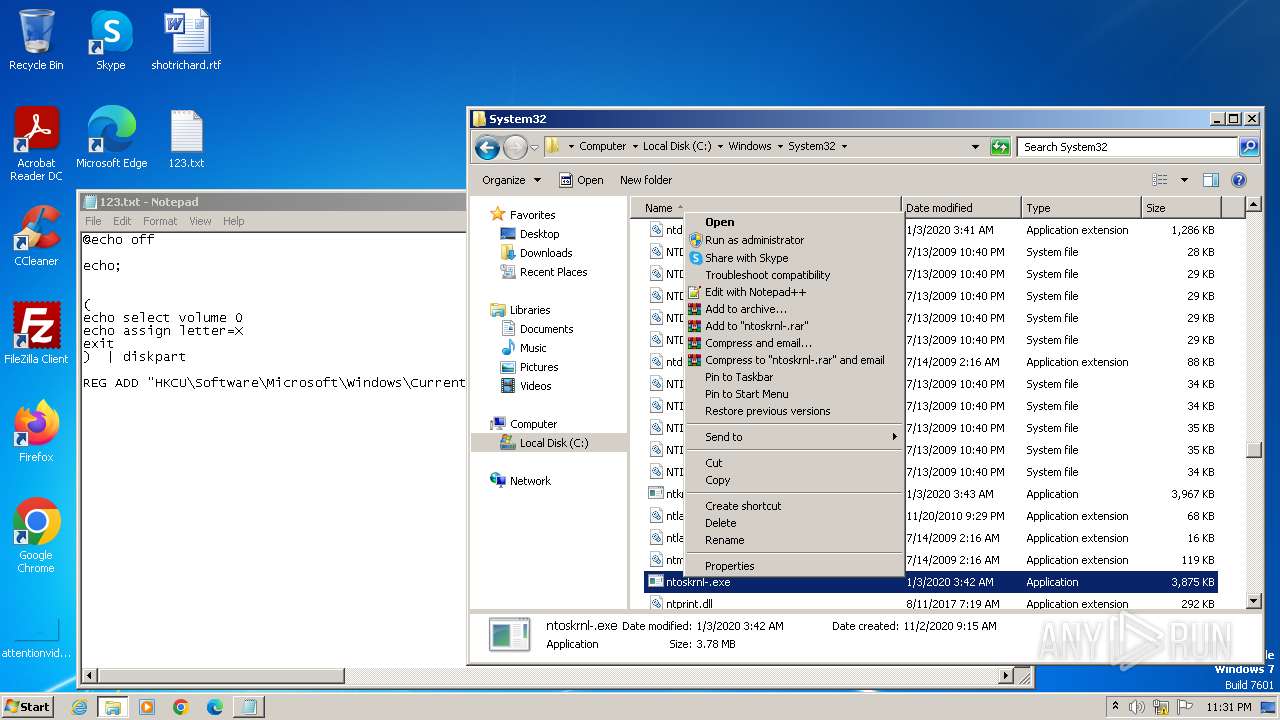
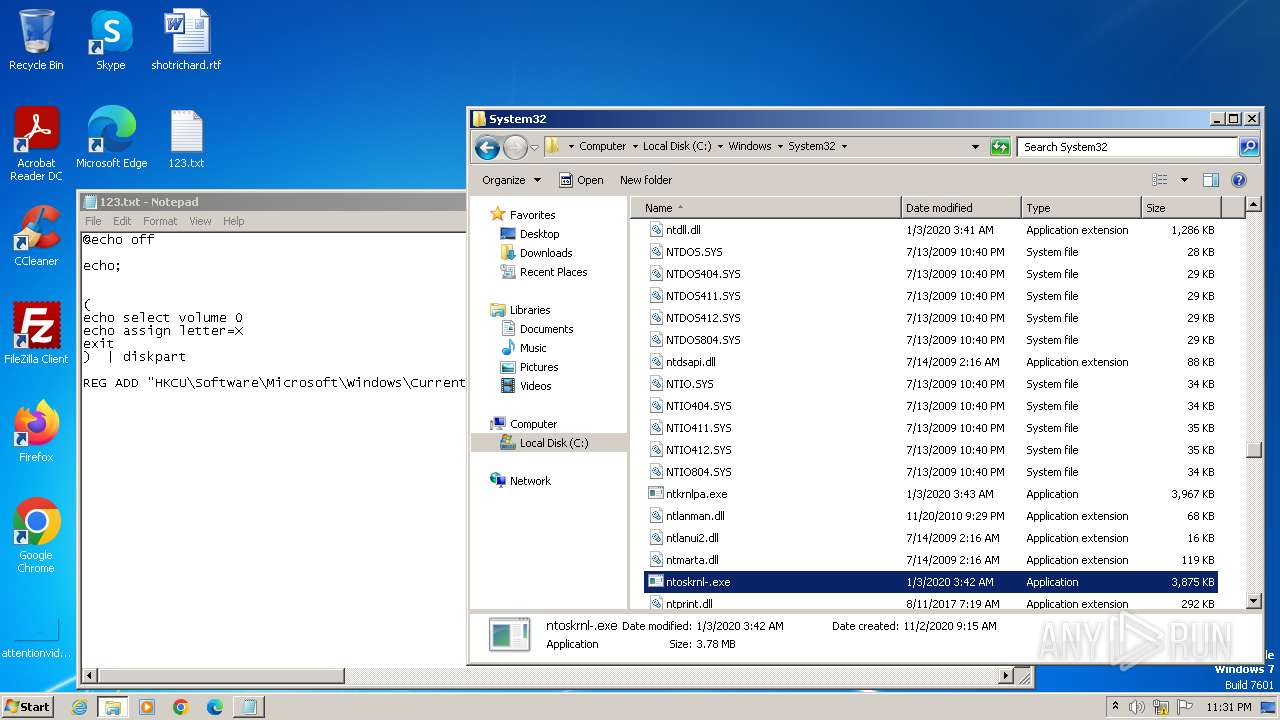
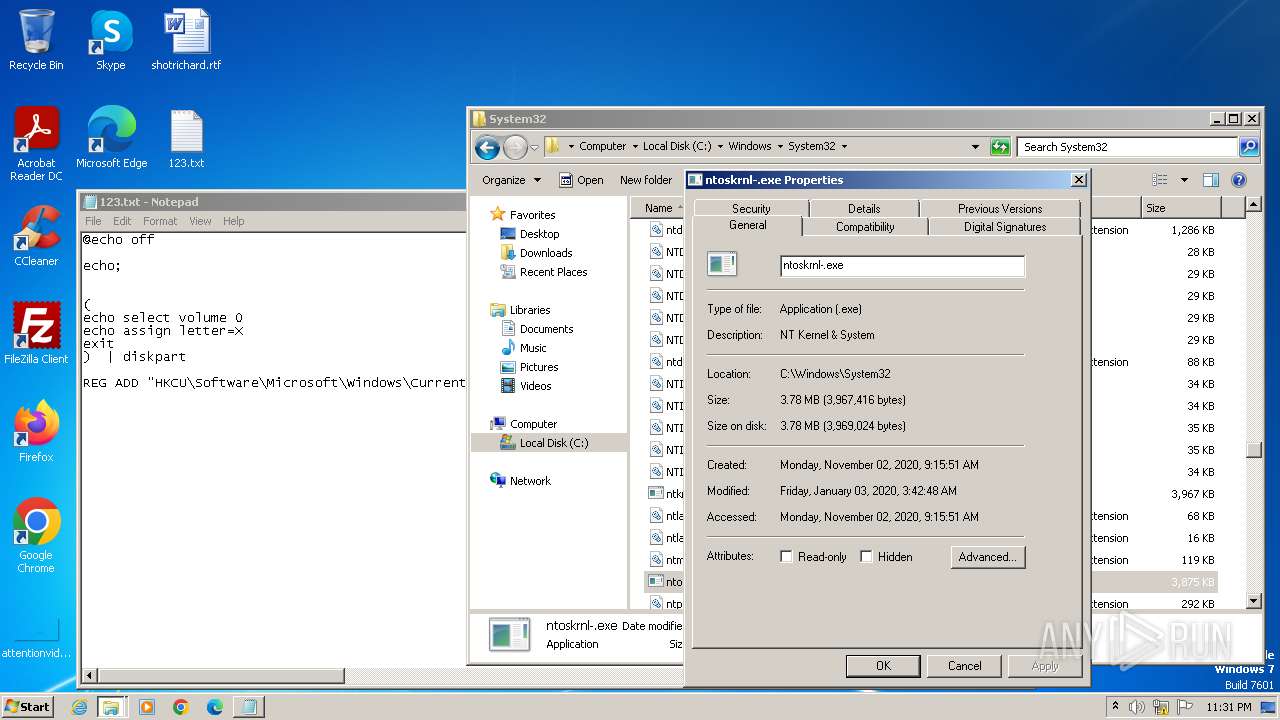
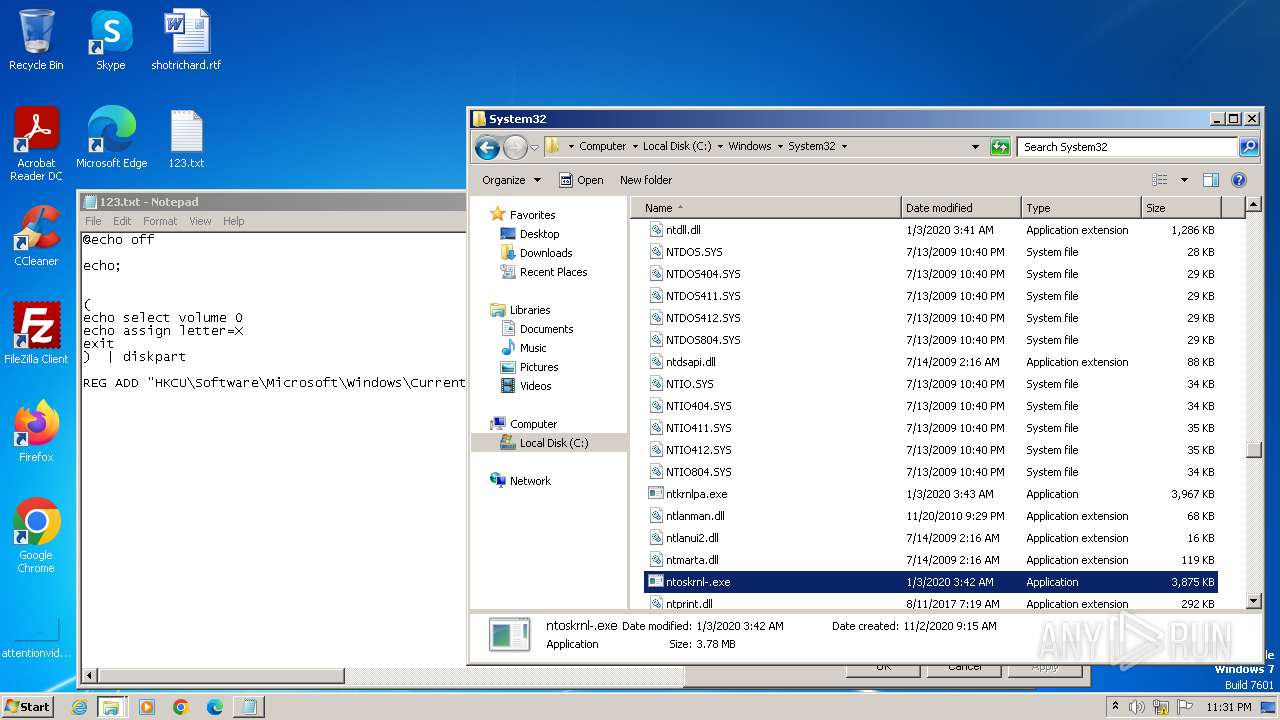
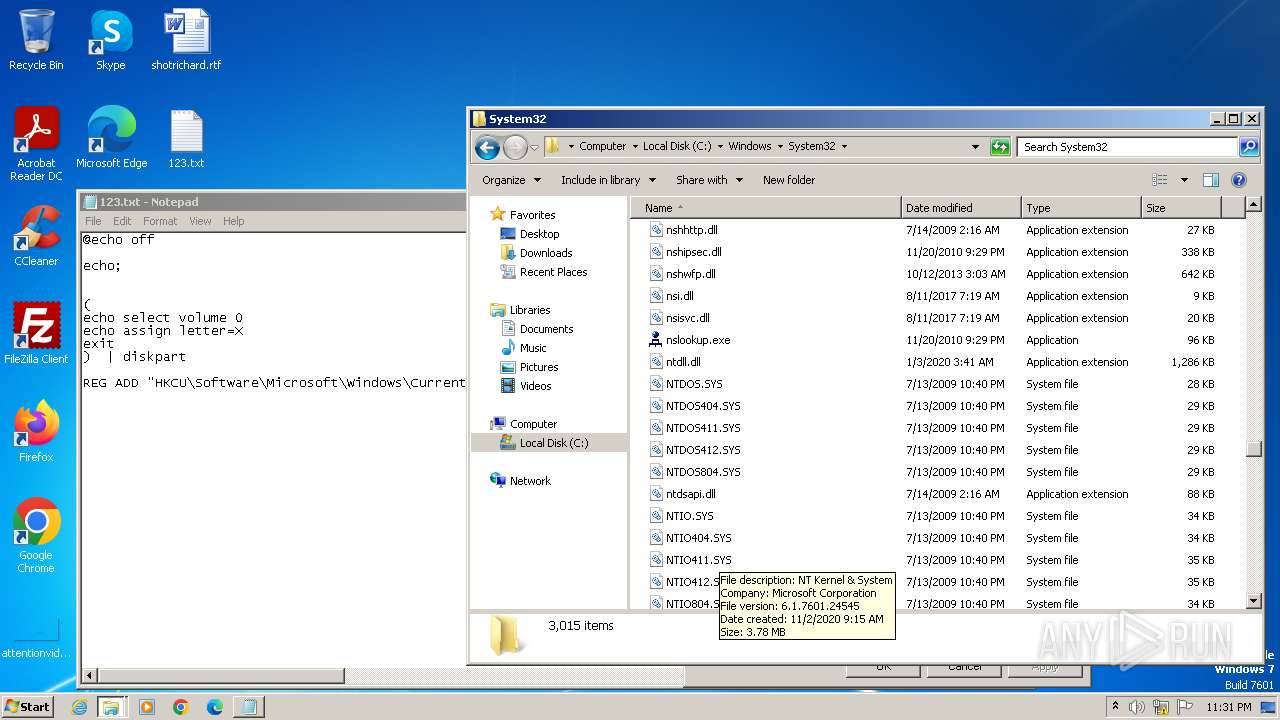
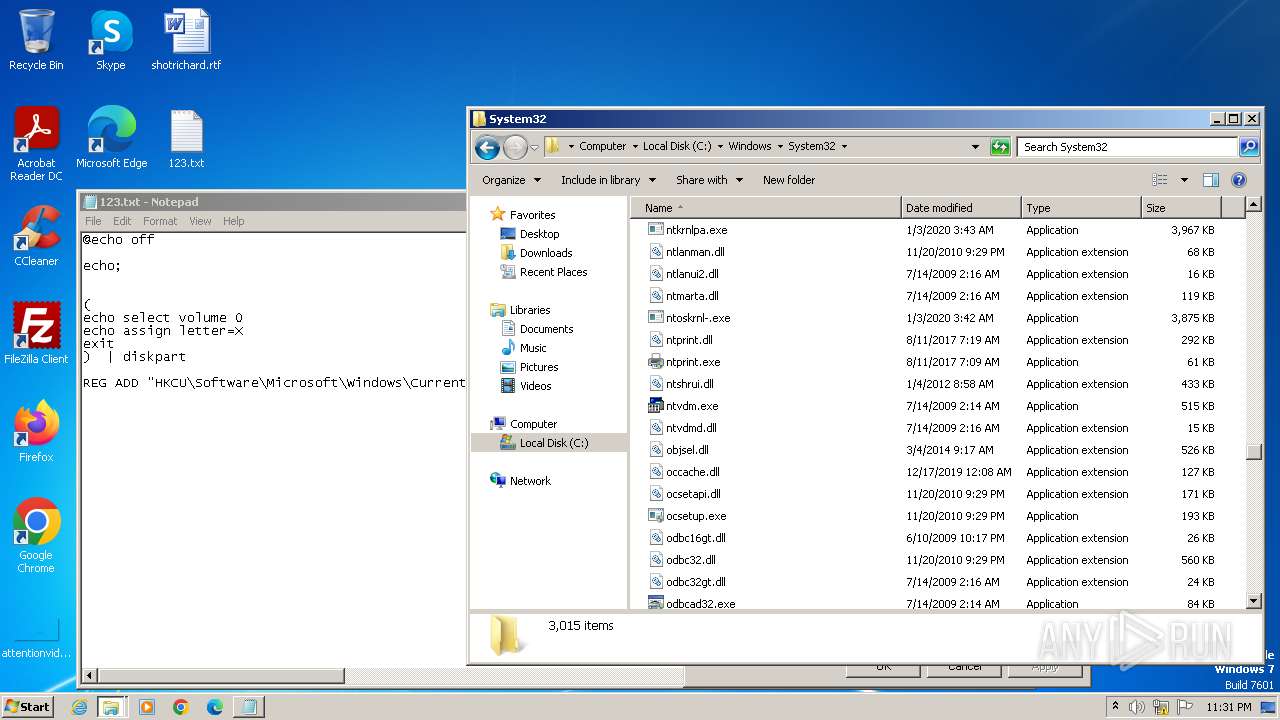
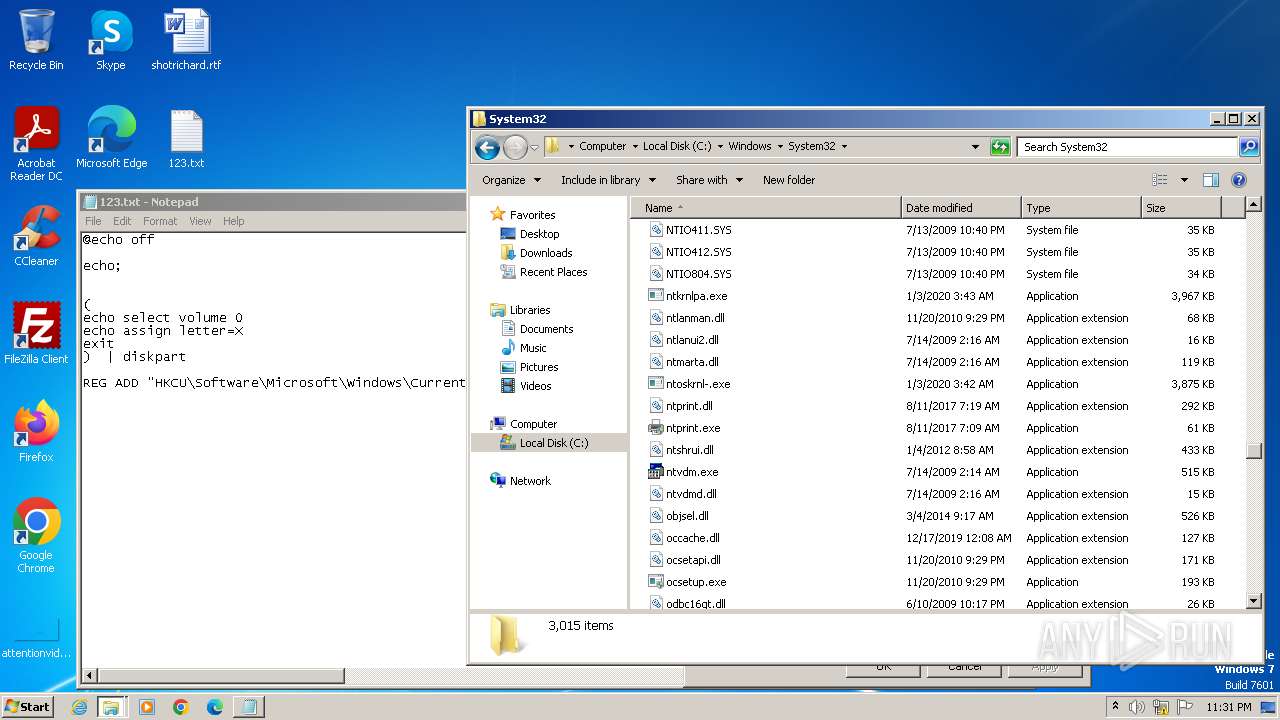
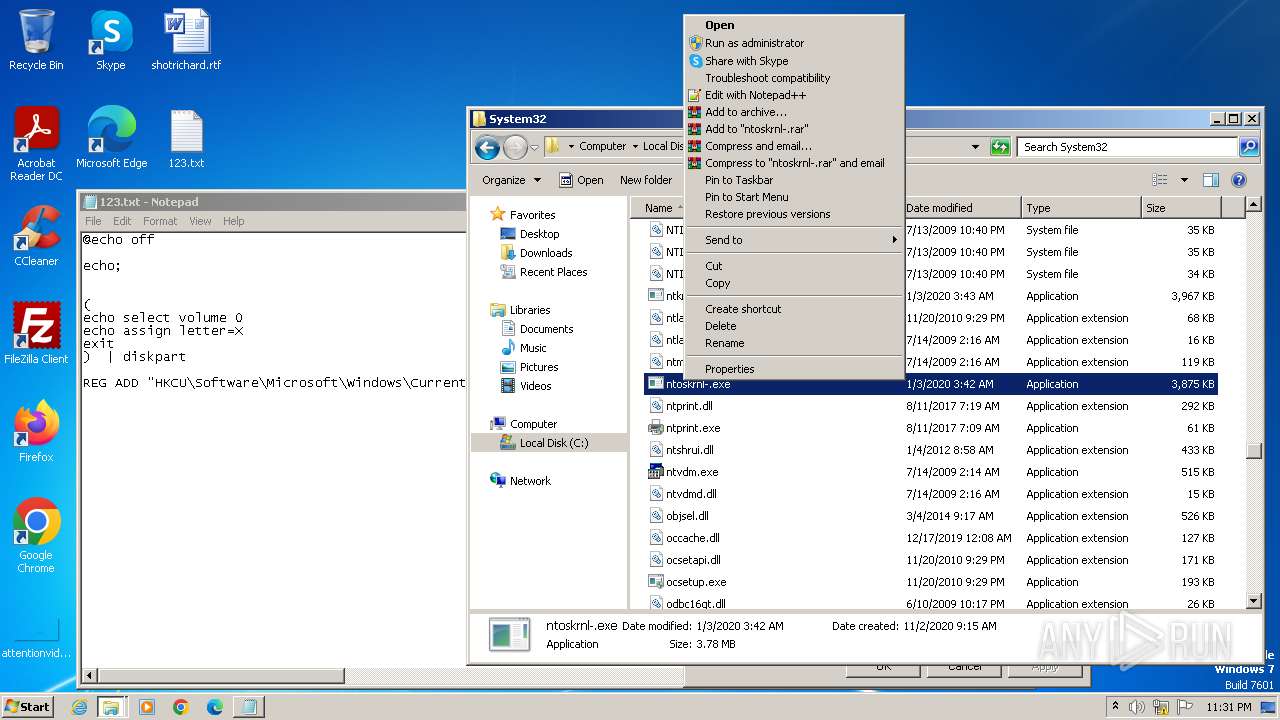
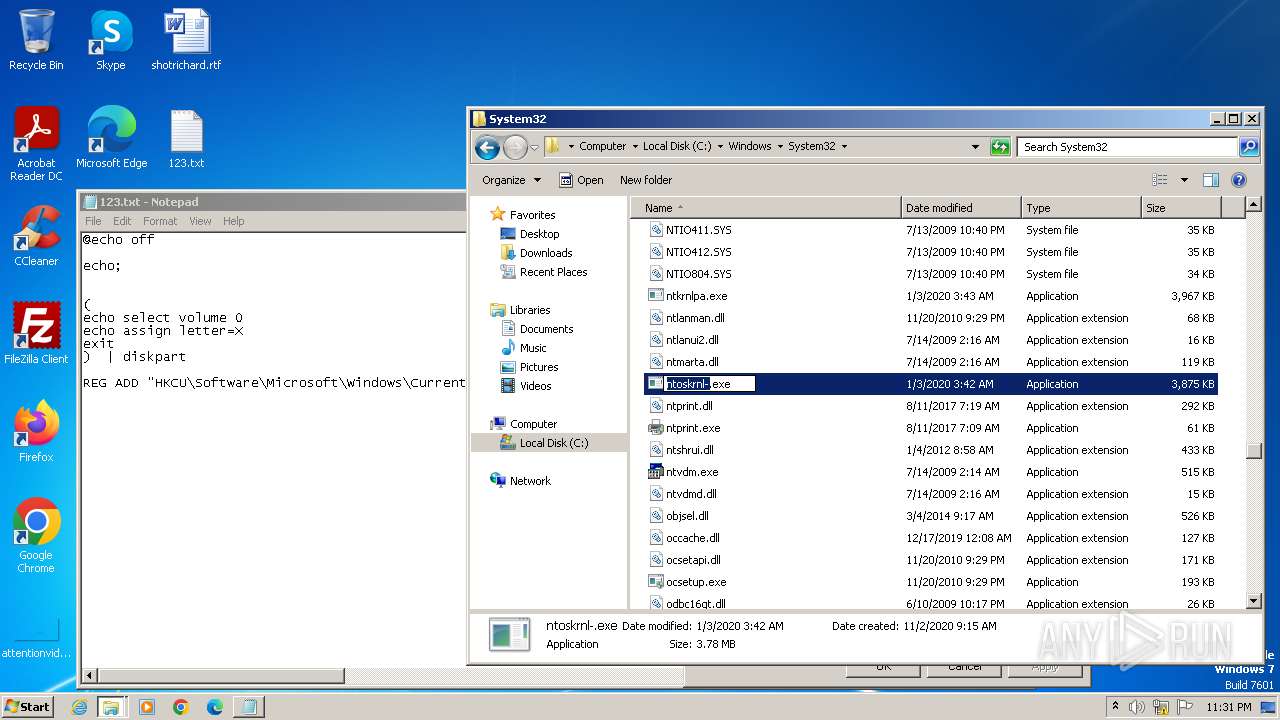
Manual execution by a user
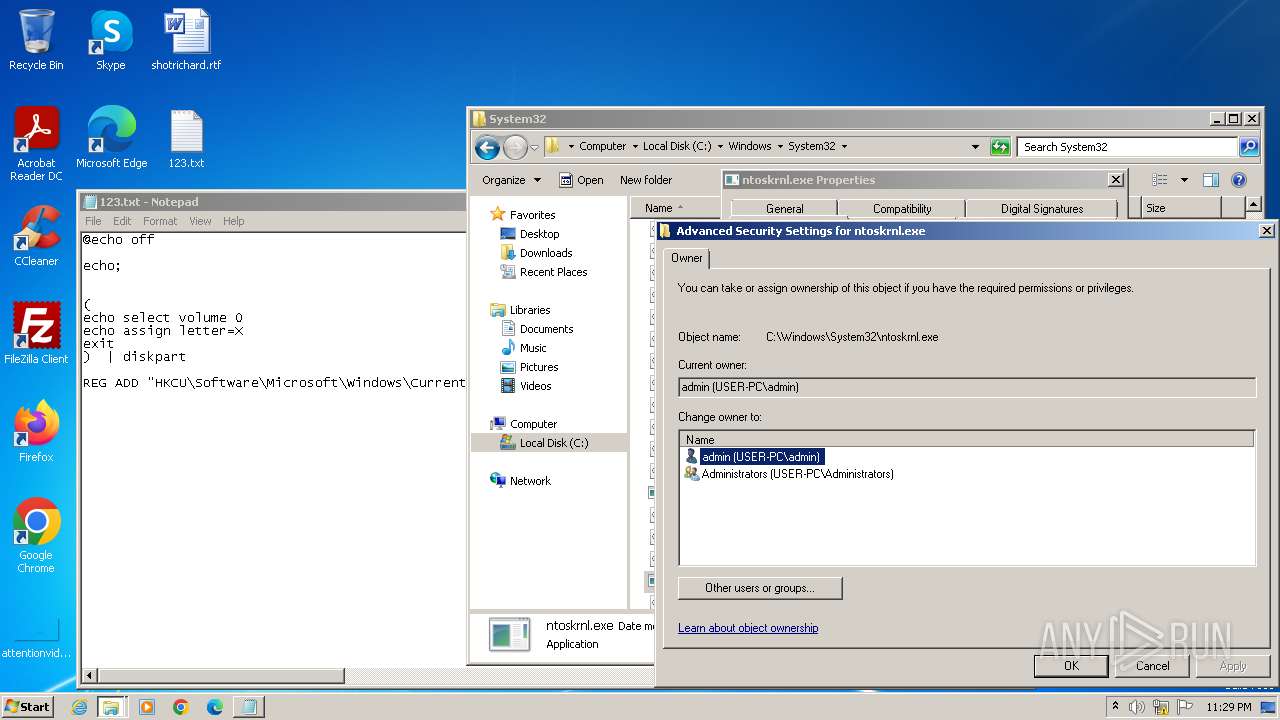
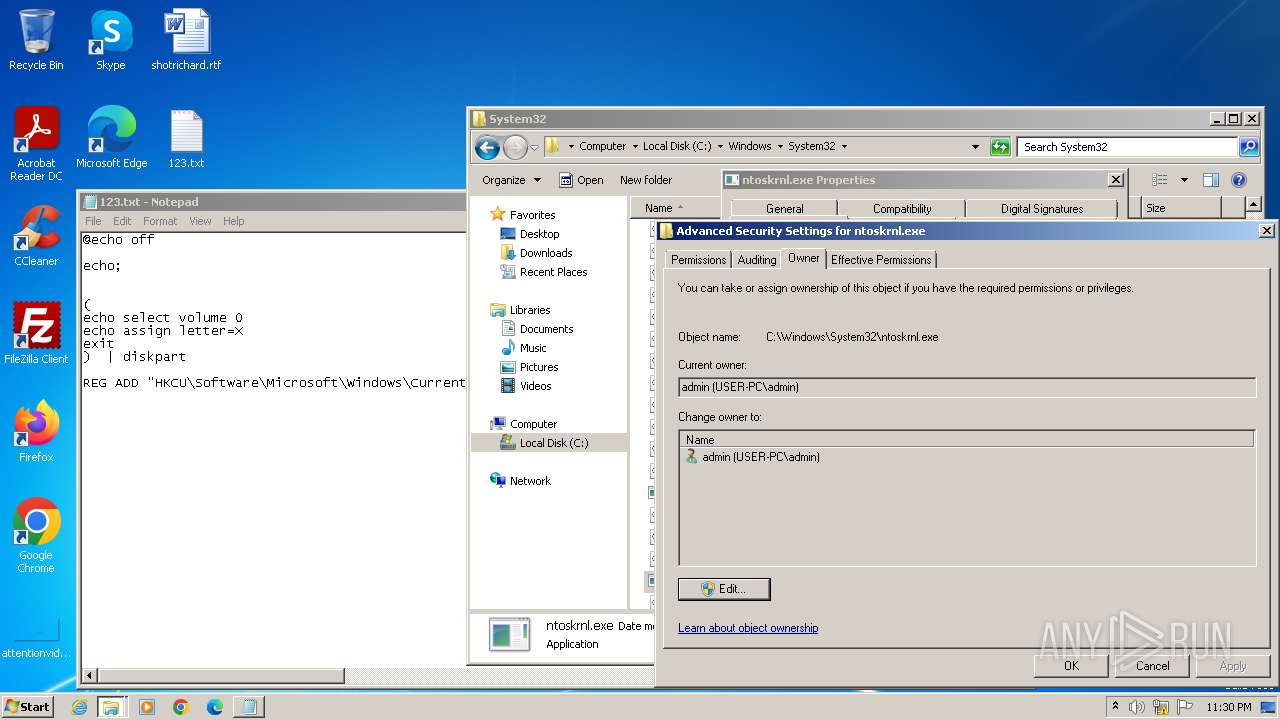
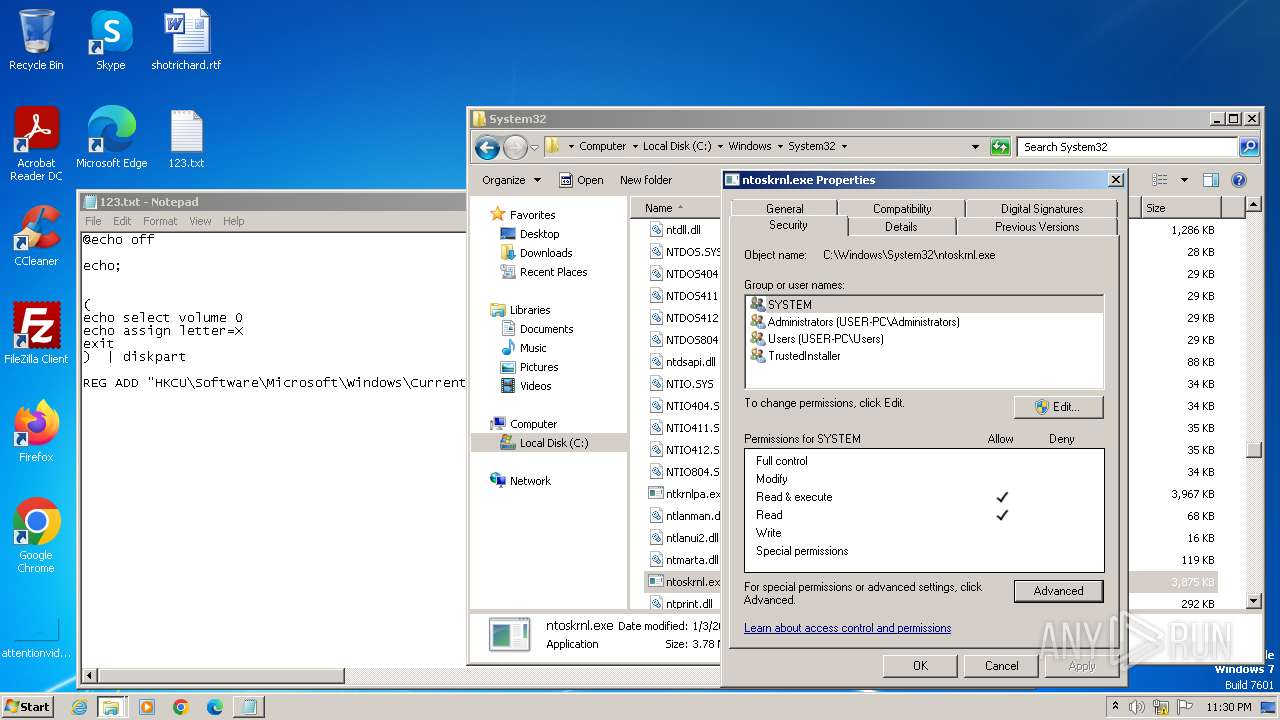
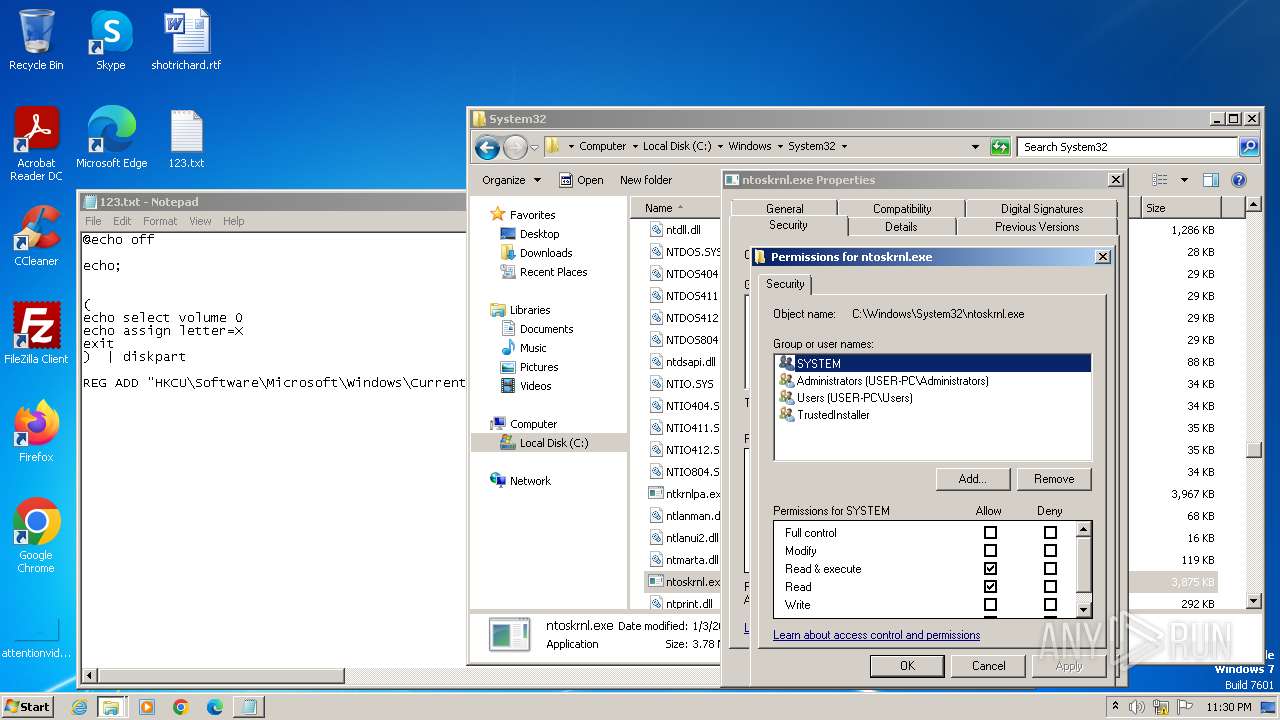
- ntoskrnl-.exe (PID: 3532)
- ntoskrnl-.exe (PID: 3616)
- explorer.exe (PID: 1816)
- rundll32.exe (PID: 3740)
- wmpnscfg.exe (PID: 2360)
- IMEKLMG.EXE (PID: 2080)
- IMEKLMG.EXE (PID: 2092)
- wmpnscfg.exe (PID: 2384)
The process uses the downloaded file
- rundll32.exe (PID: 3740)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 3740)
- sipnotify.exe (PID: 1552)
Checks supported languages
- IMEKLMG.EXE (PID: 2092)
- wmpnscfg.exe (PID: 2360)
- IMEKLMG.EXE (PID: 2080)
- wmpnscfg.exe (PID: 2384)
Reads the computer name
- IMEKLMG.EXE (PID: 2092)
- IMEKLMG.EXE (PID: 2080)
- wmpnscfg.exe (PID: 2360)
- wmpnscfg.exe (PID: 2384)
Process checks whether UAC notifications are on
- IMEKLMG.EXE (PID: 2092)
- IMEKLMG.EXE (PID: 2080)
Reads the software policy settings
- sipnotify.exe (PID: 1552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
112
Monitored processes
17
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1104 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\System32\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1552 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 1592 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1816 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
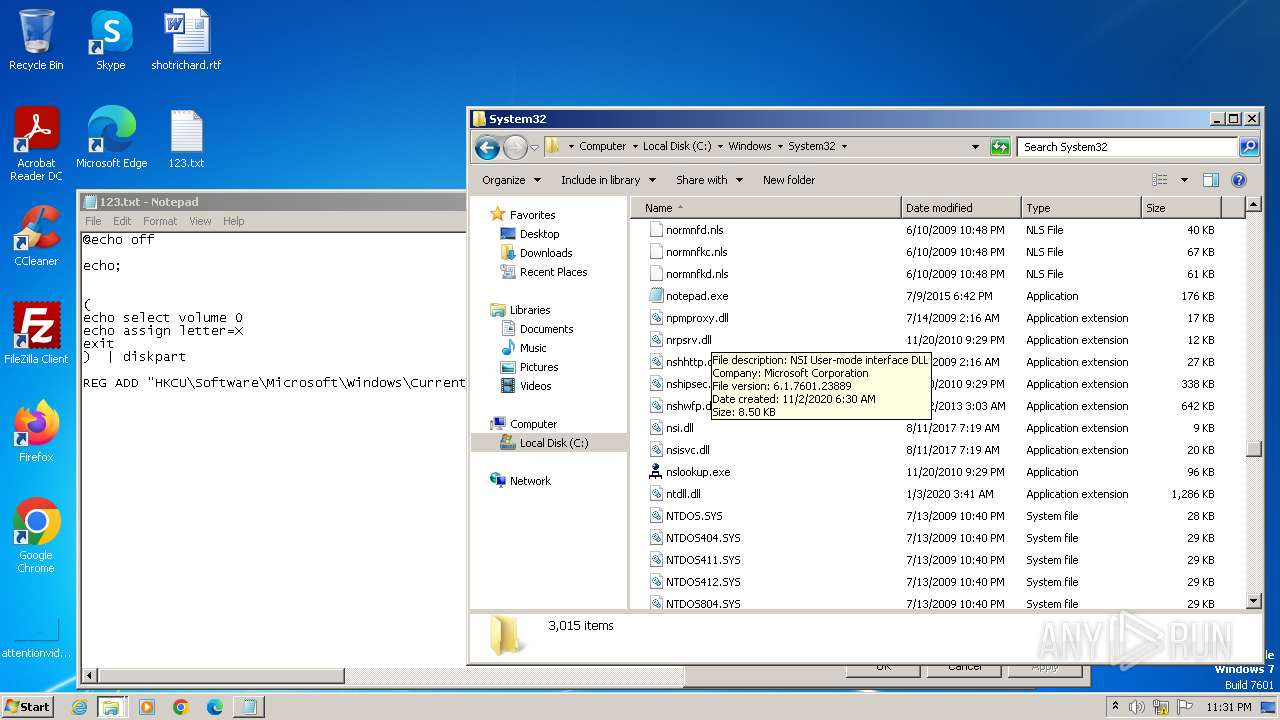
| 1932 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\123.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 1073807364 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /JPN /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 2092 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /KOR /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 2360 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2384 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3260 | C:\Windows\system32\DllHost.exe /Processid:{1F2E5C40-9550-11CE-99D2-00AA006E086C} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 634
Read events
5 543
Write events
90
Delete events
1
Modification events
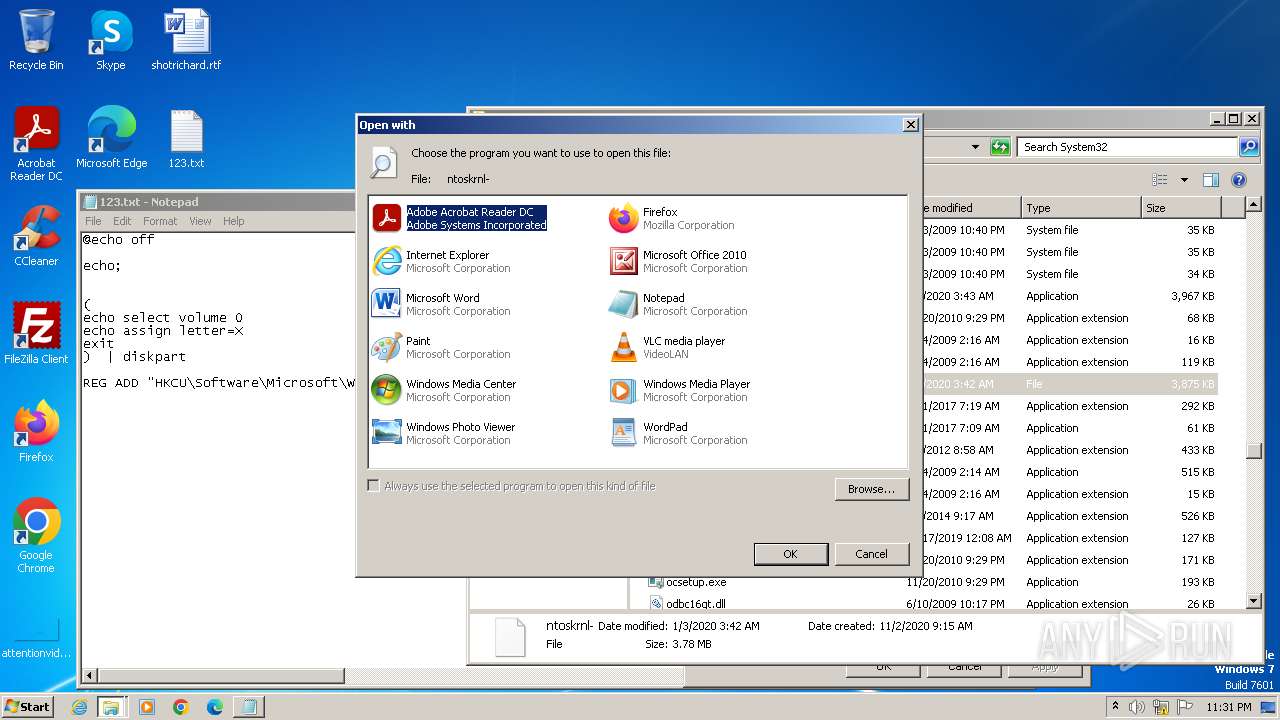
| (PID) Process: | (3740) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (3740) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (3740) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
| (PID) Process: | (3740) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE |
Value: Microsoft Word | |||
| (PID) Process: | (3740) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows NT\Accessories\WORDPAD.EXE |
Value: WordPad | |||
| (PID) Process: | (3740) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (3740) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Internet Explorer\iexplore.exe |
Value: Internet Explorer | |||
| (PID) Process: | (3740) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (3740) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (3740) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
4
Suspicious files
1
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1552 | sipnotify.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\SipNotify\eoscontent\main.jpg | image | |
MD5:B342ACE63F77961249A084C61EABC884 | SHA256:E5067BBA2095B5DA7C3171EC116E9A92337E24E471339B0860A160076EFE49B9 | |||
| 1552 | sipnotify.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\SipNotify\eoscontent\script.js | text | |
MD5:A2682382967C351F7ED21762F9E5DE9E | SHA256:36B1D26F1EC69685648C0528C2FCE95A3C2DBECF828CDFA4A8B4239A15B644A2 | |||
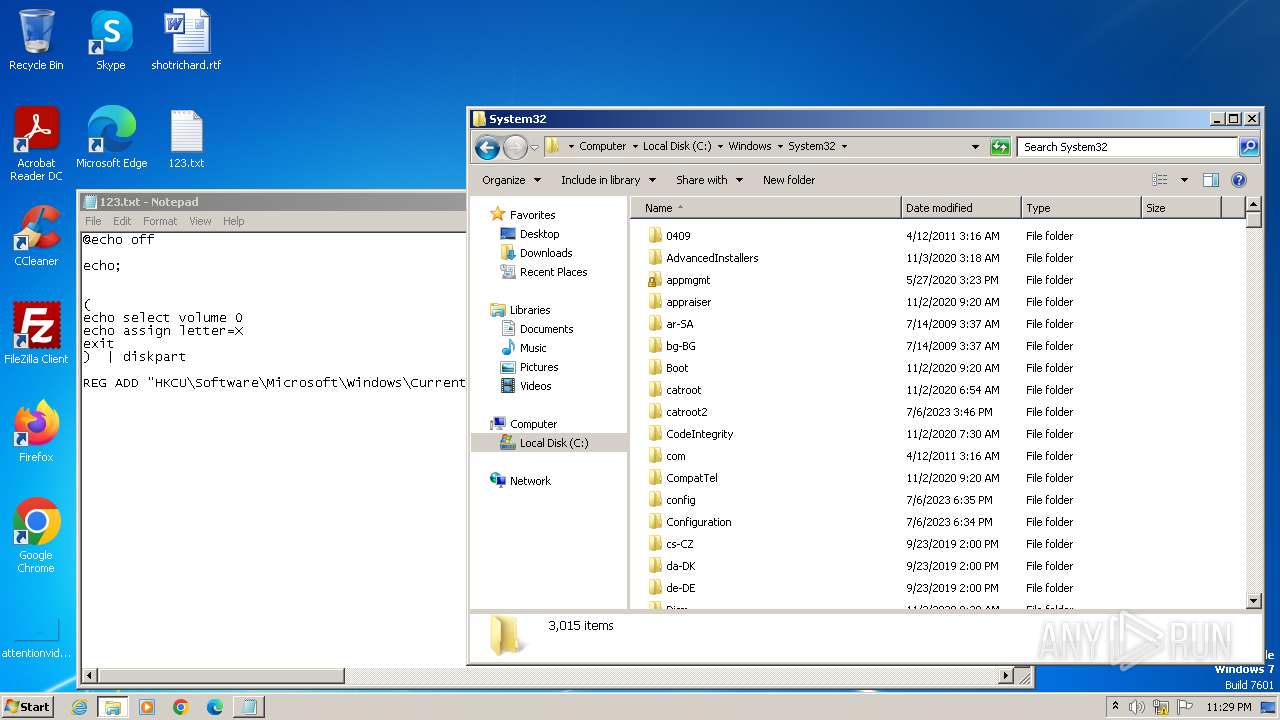
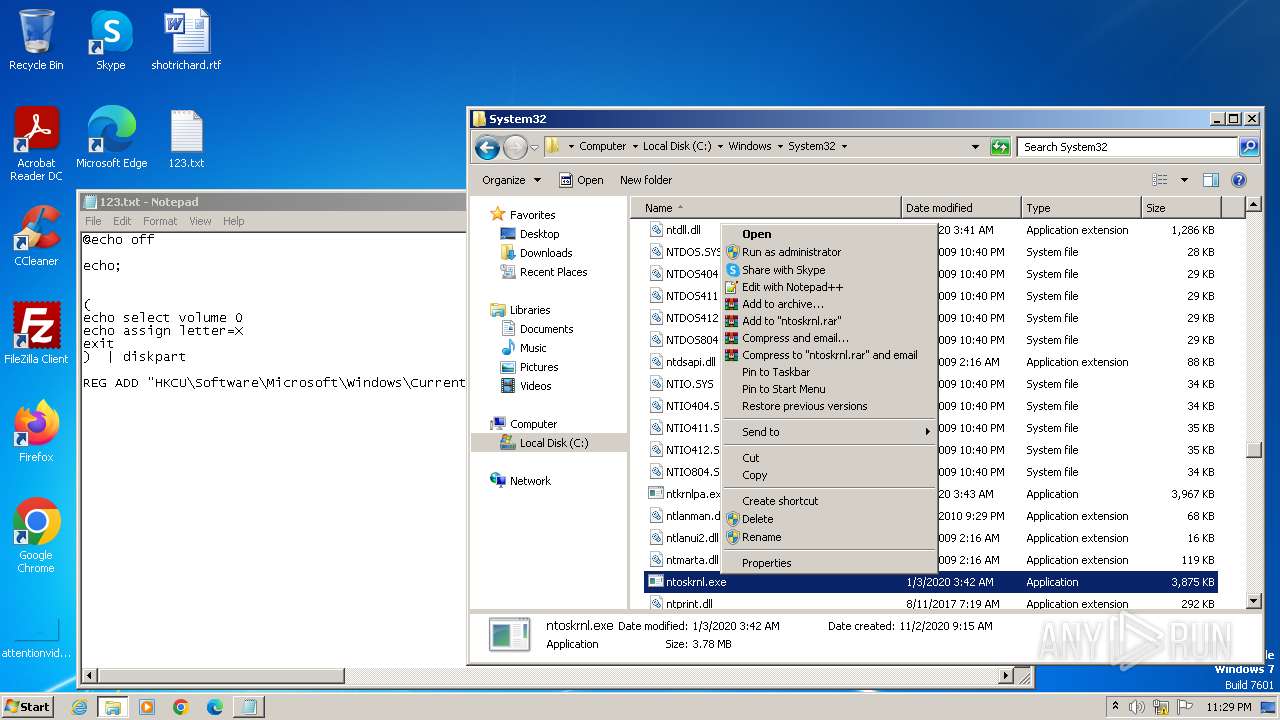
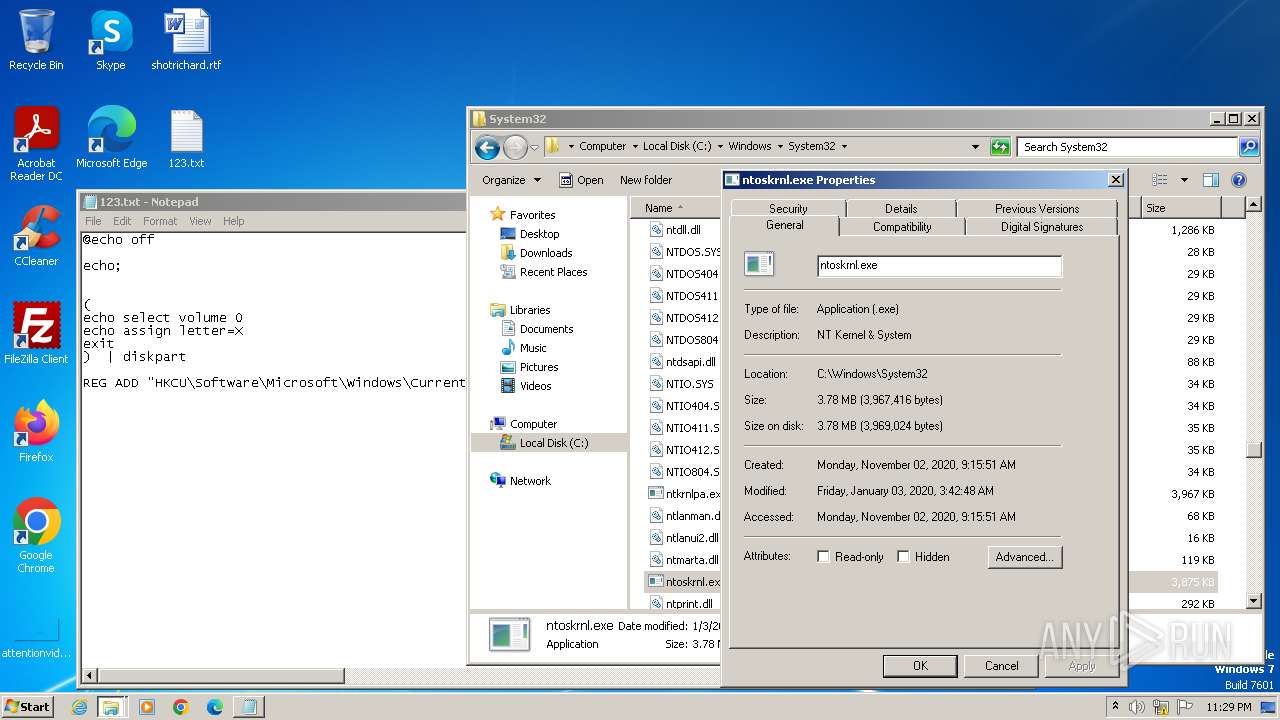
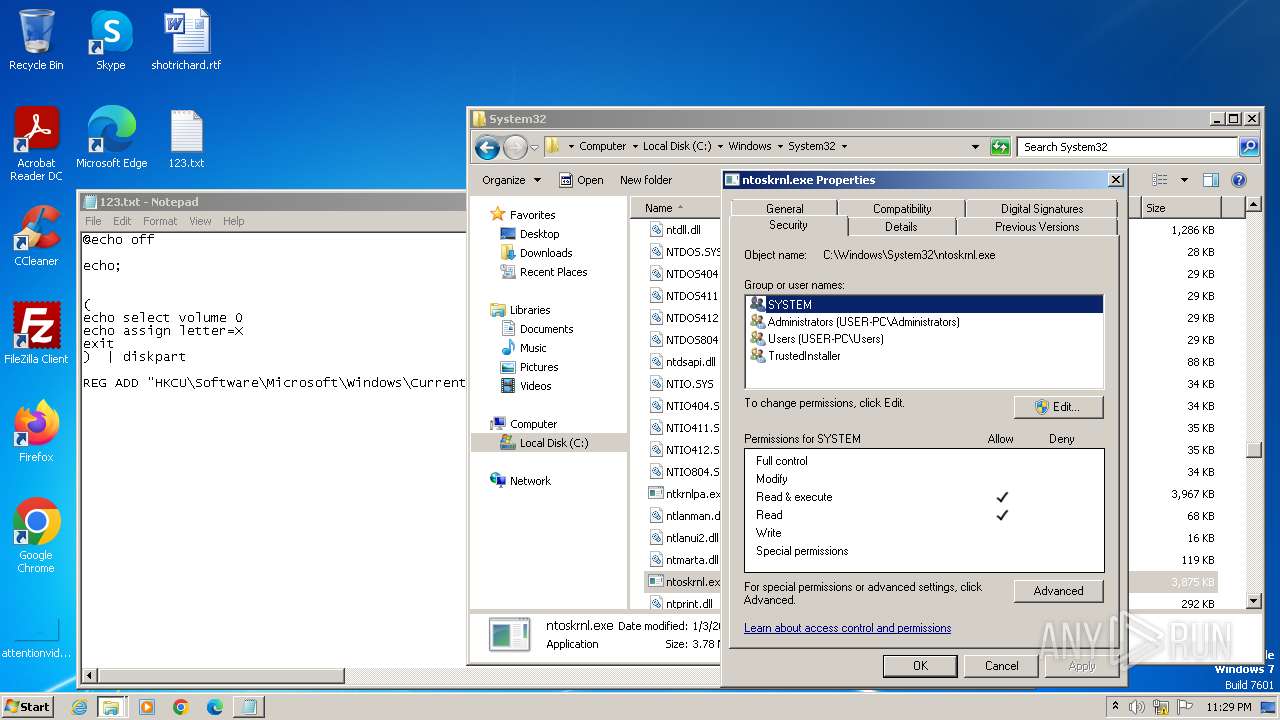
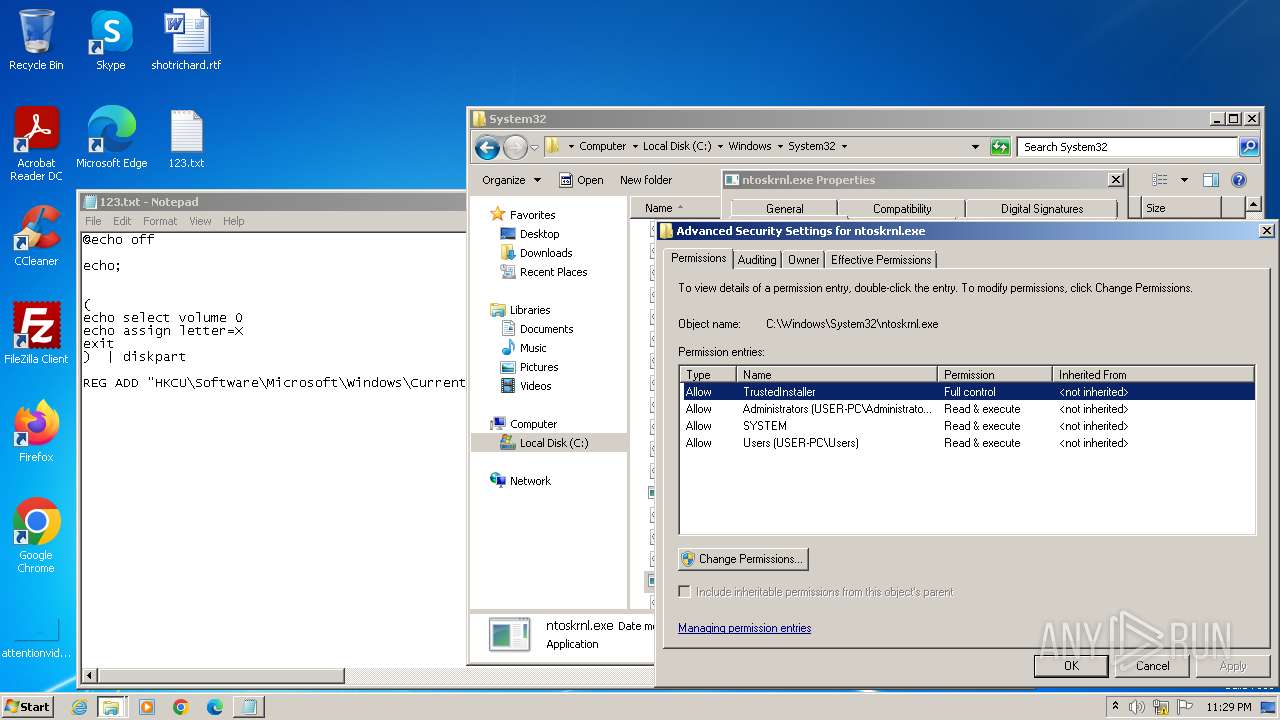
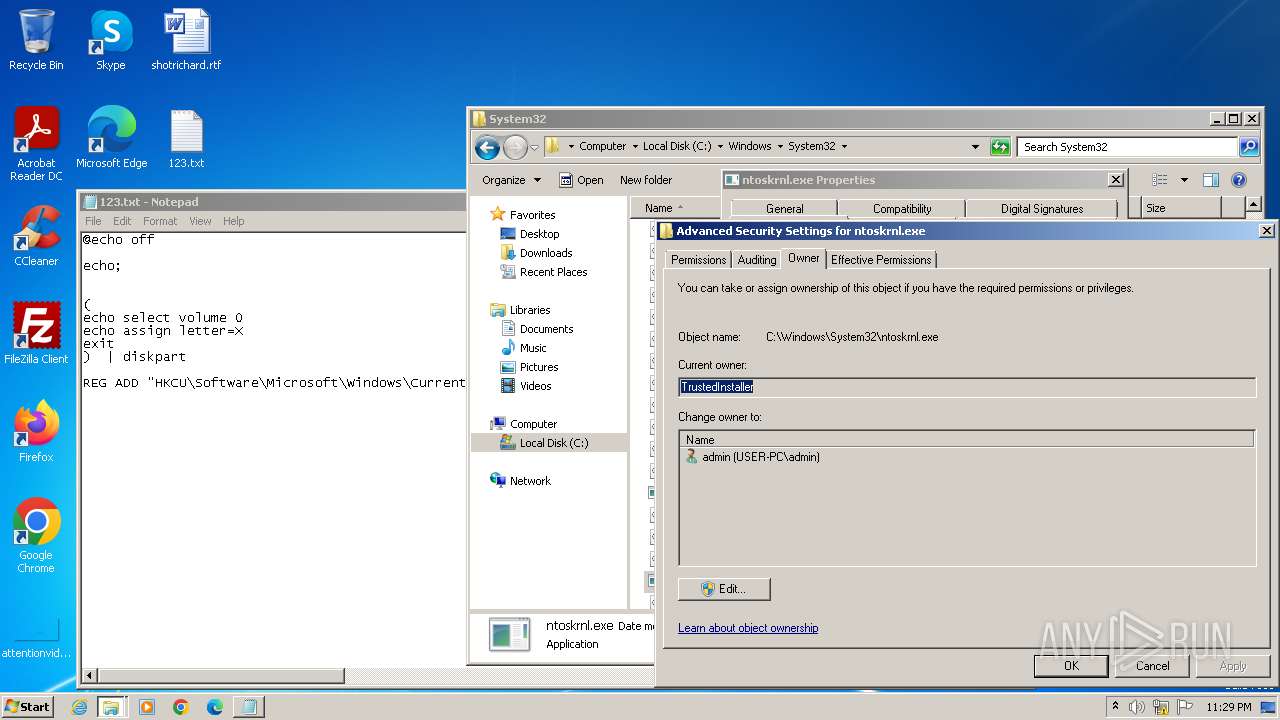
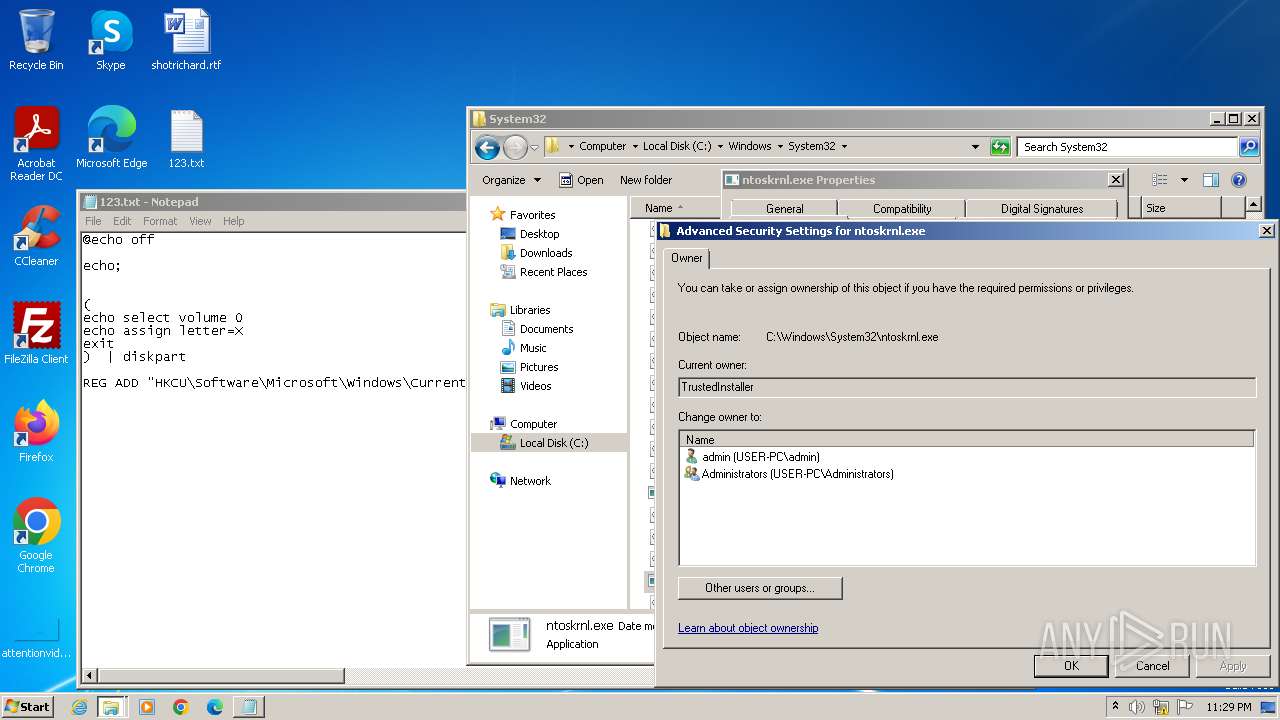
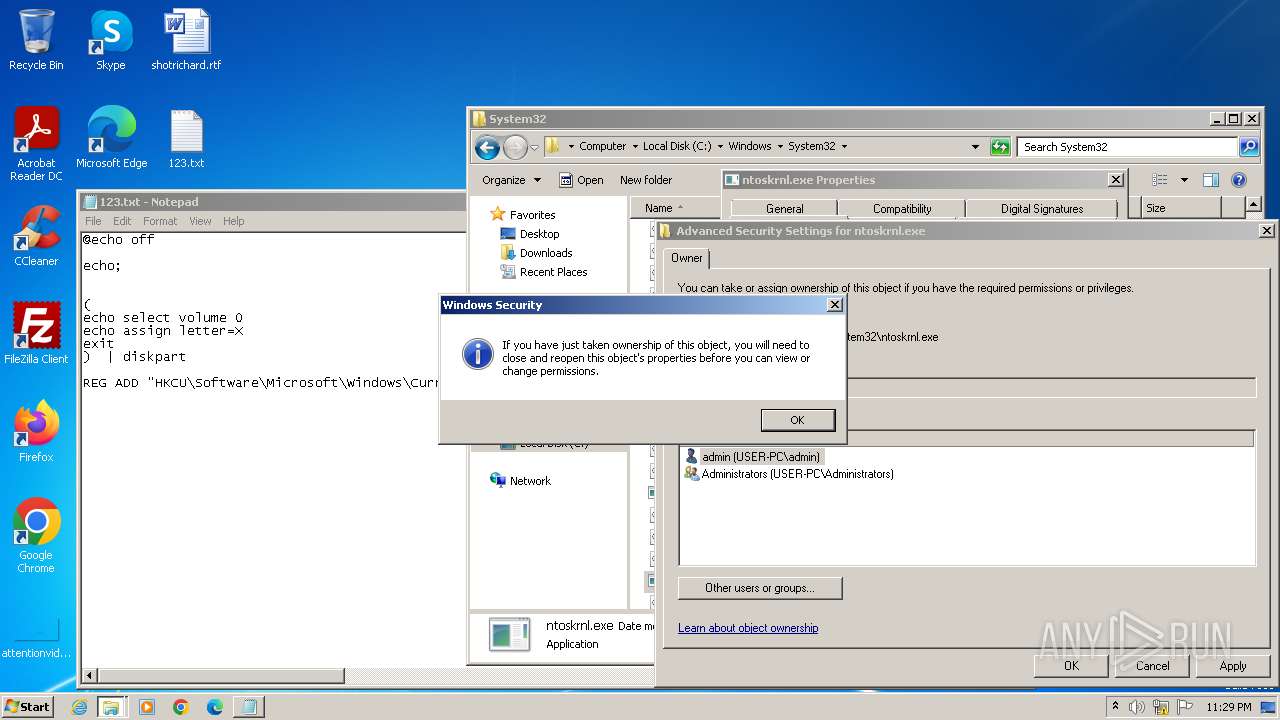
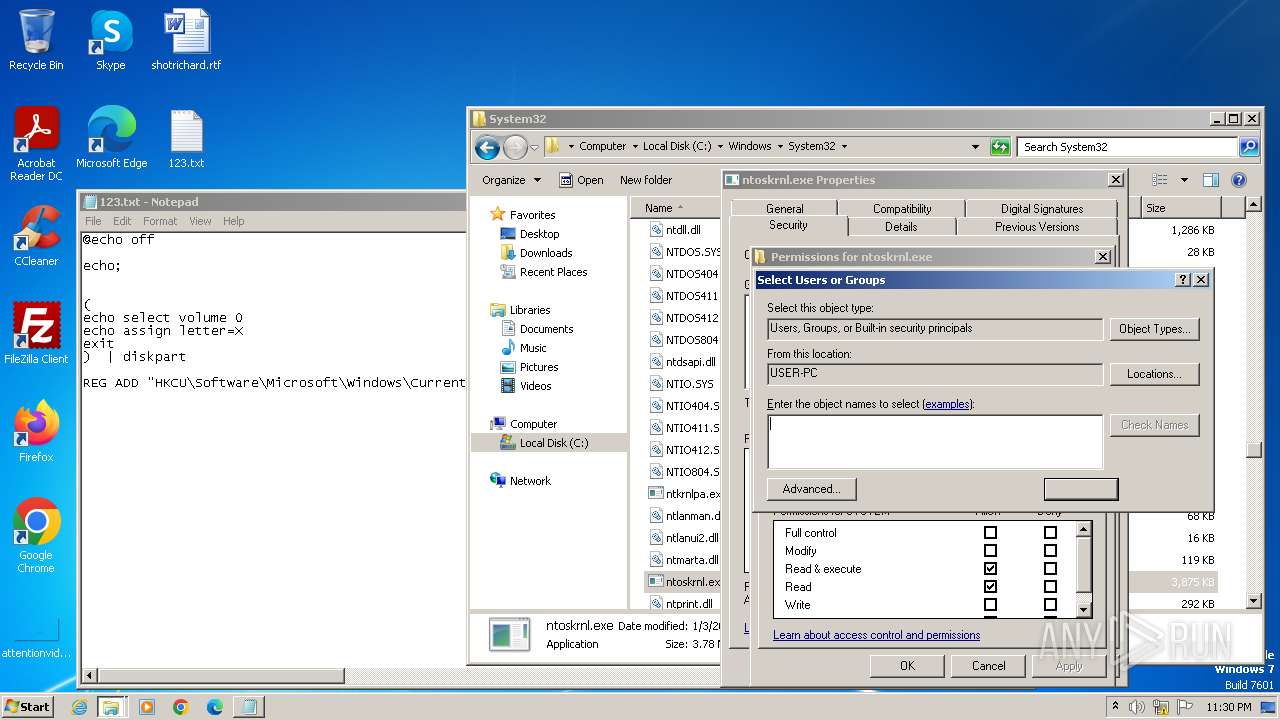
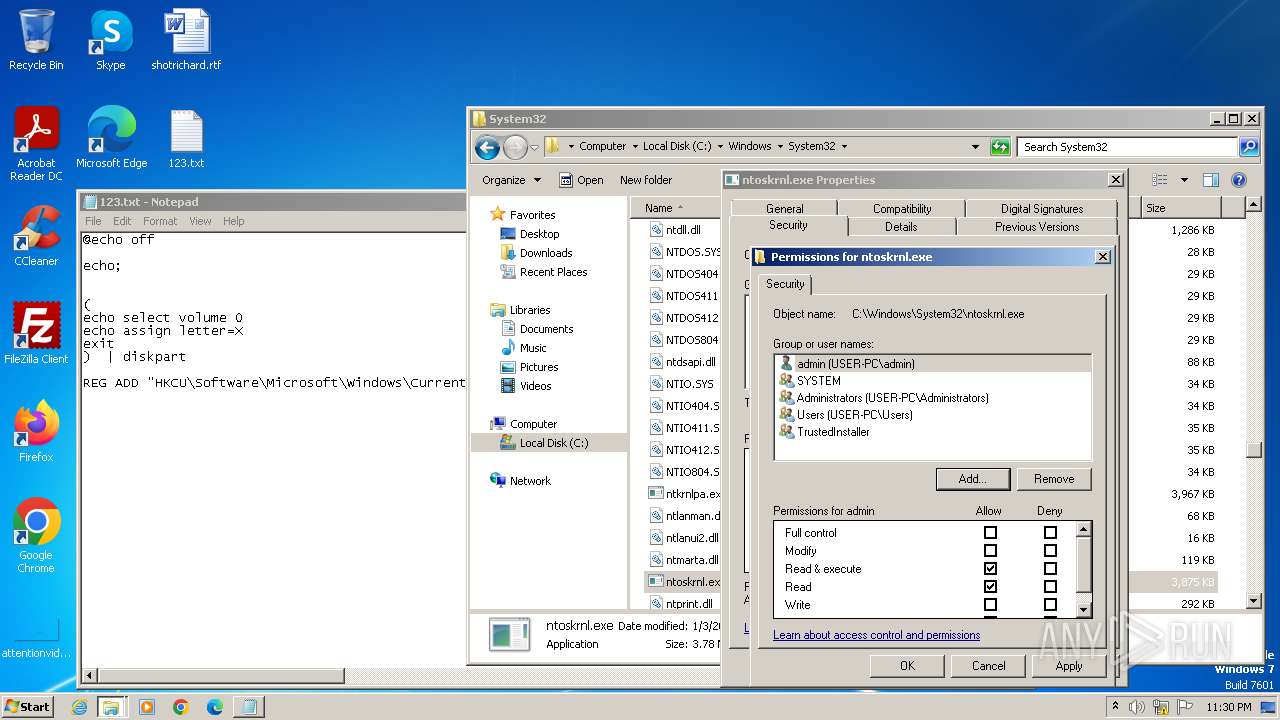
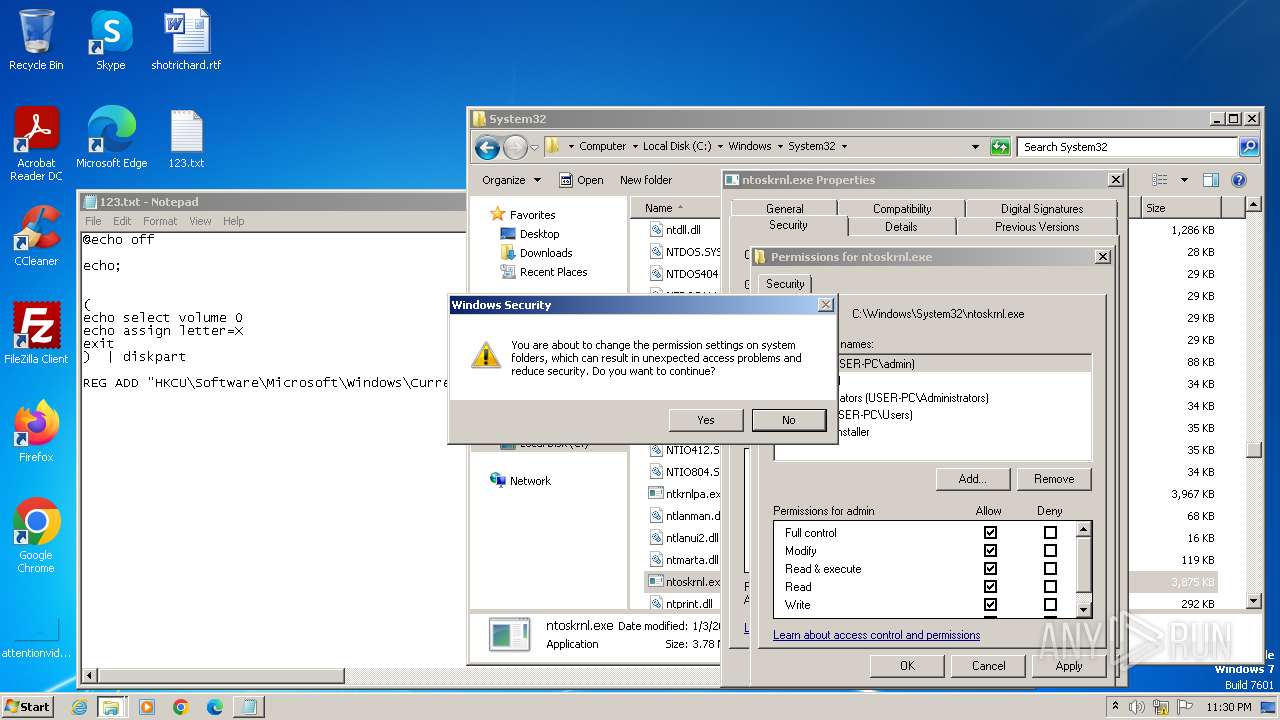
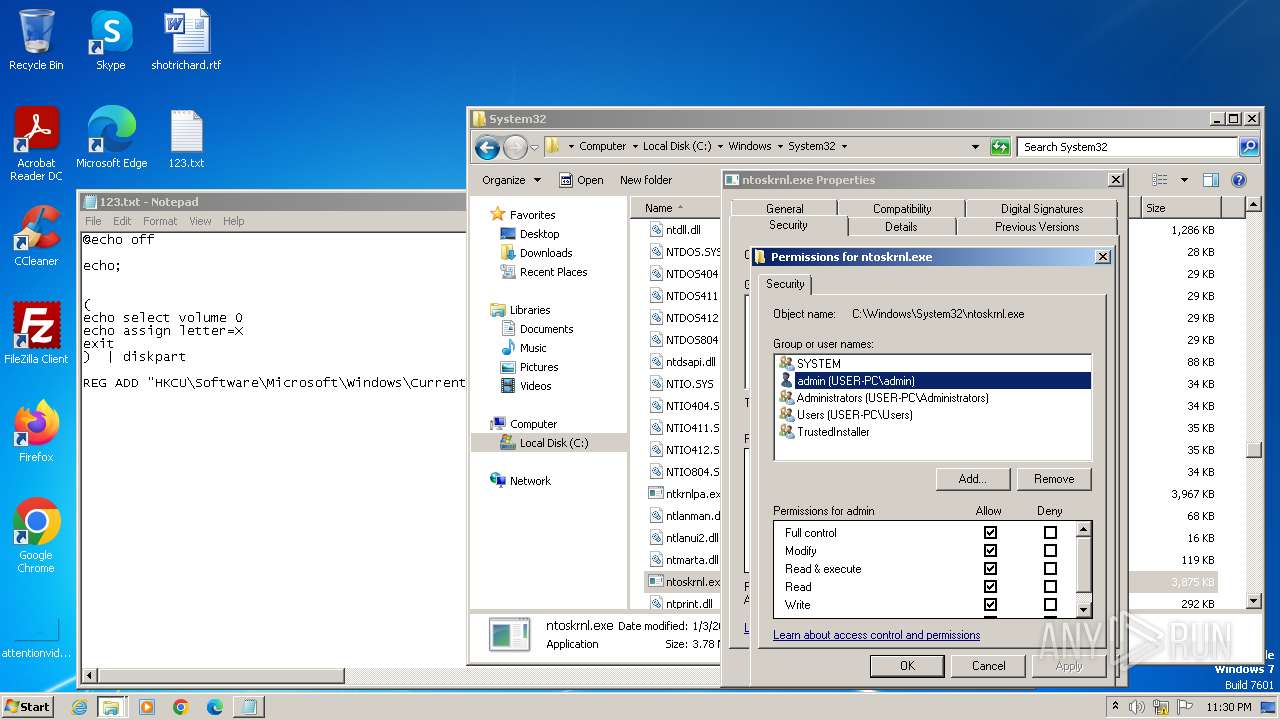
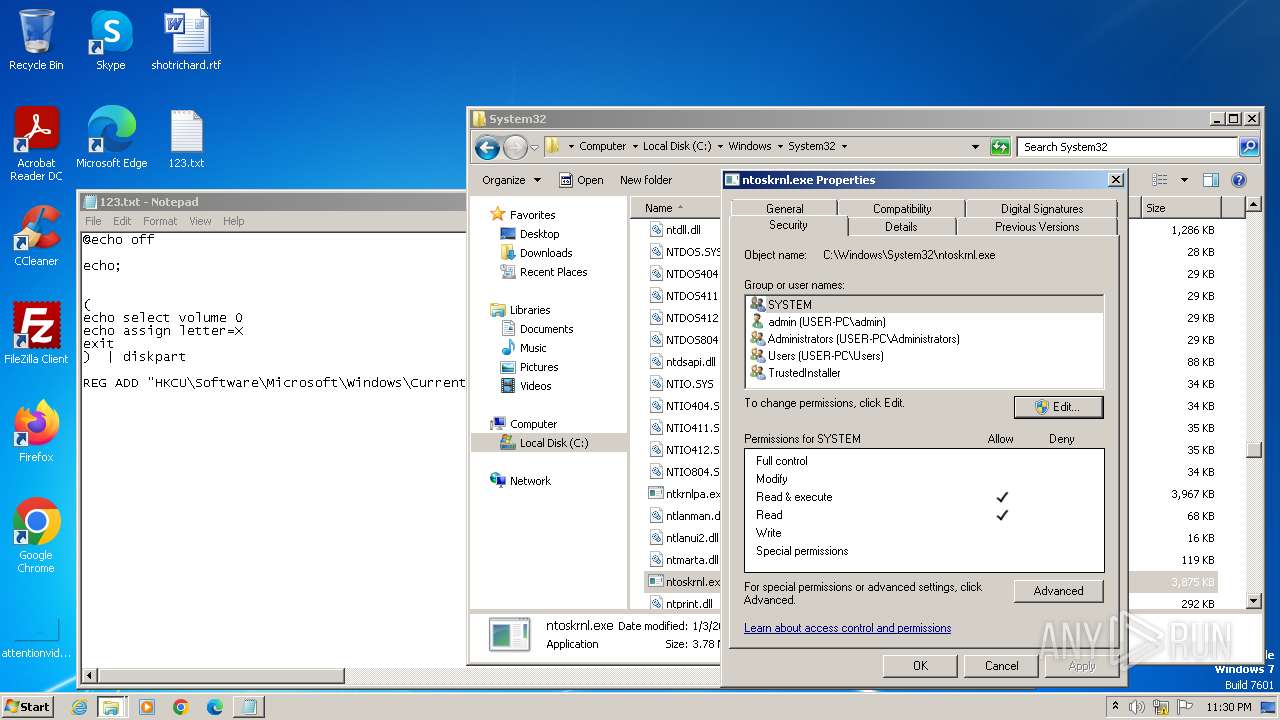
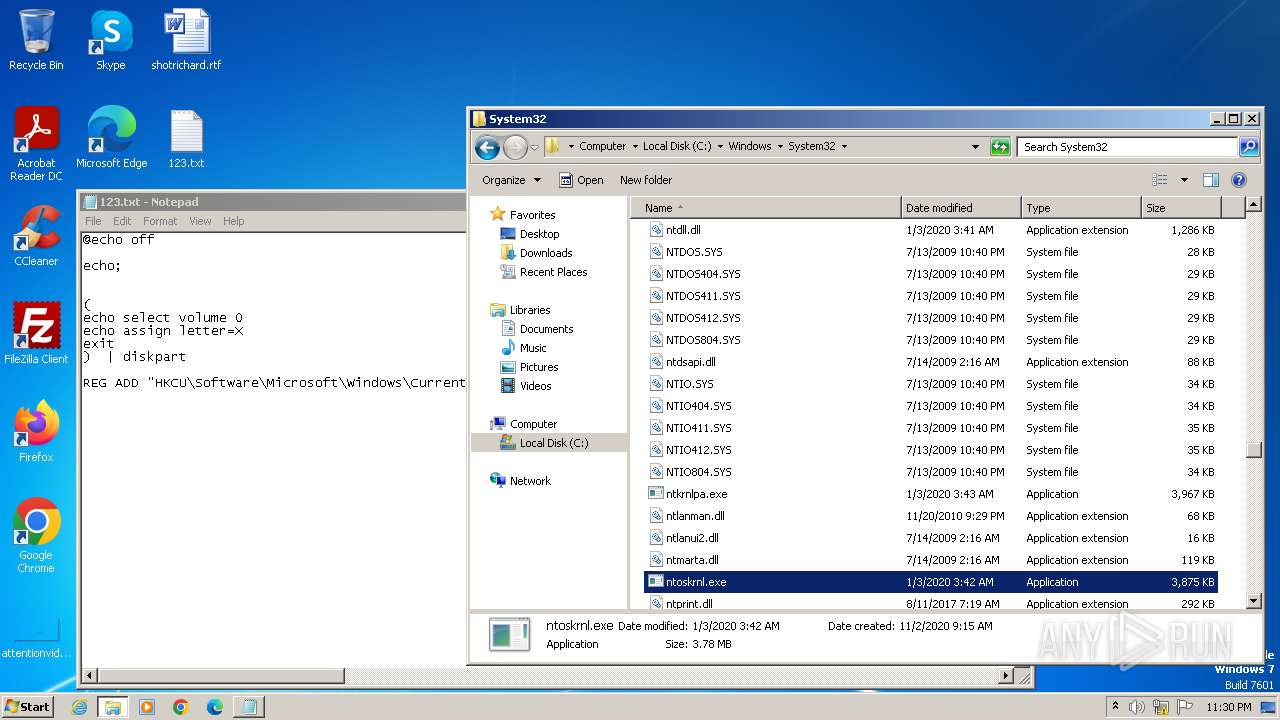
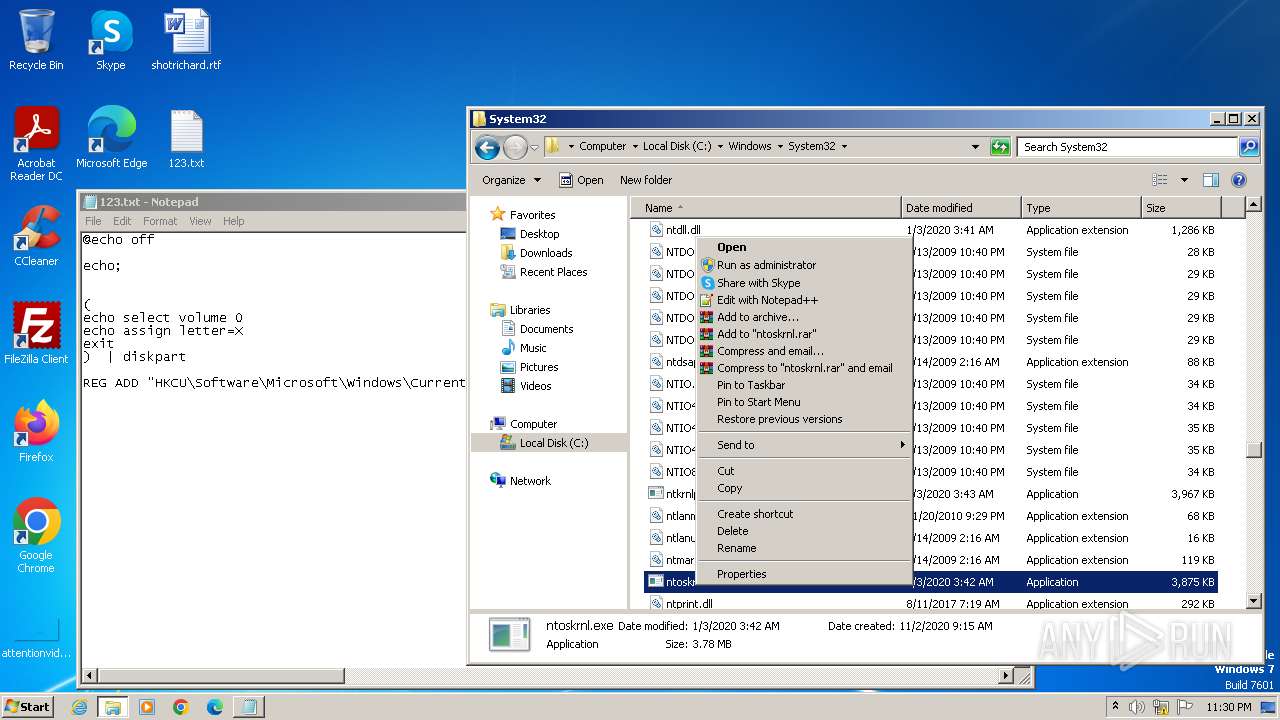
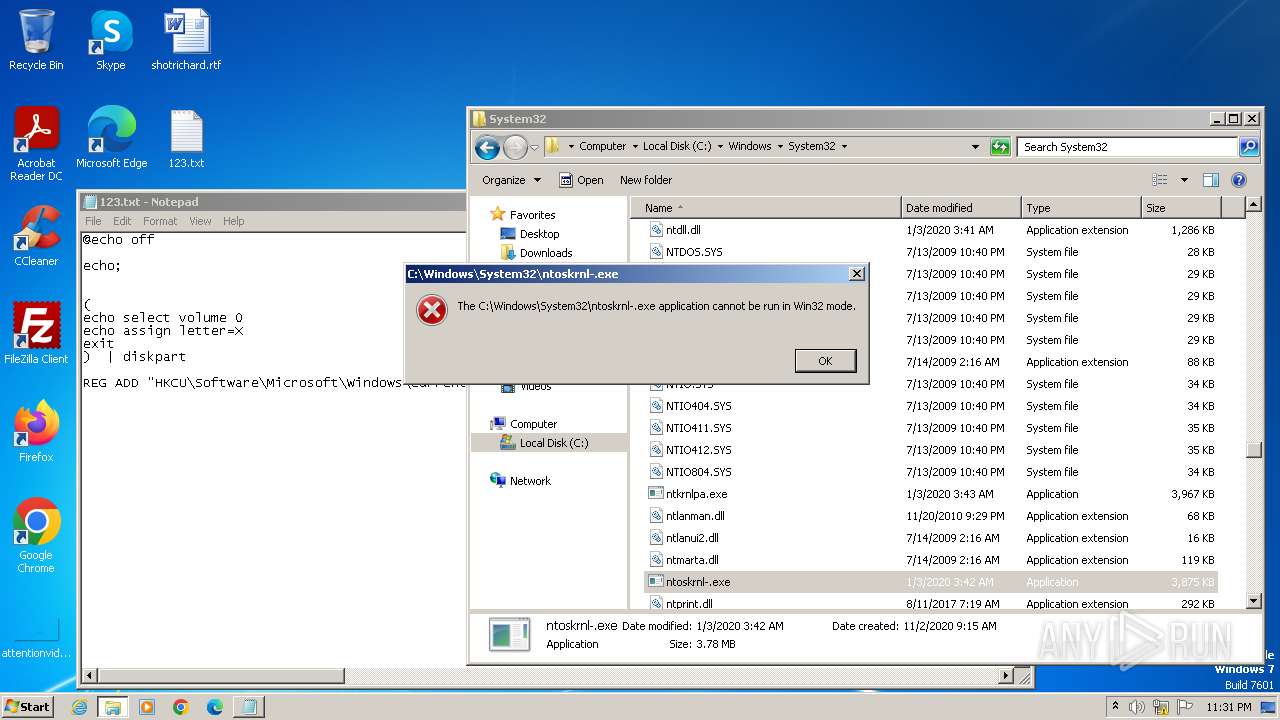
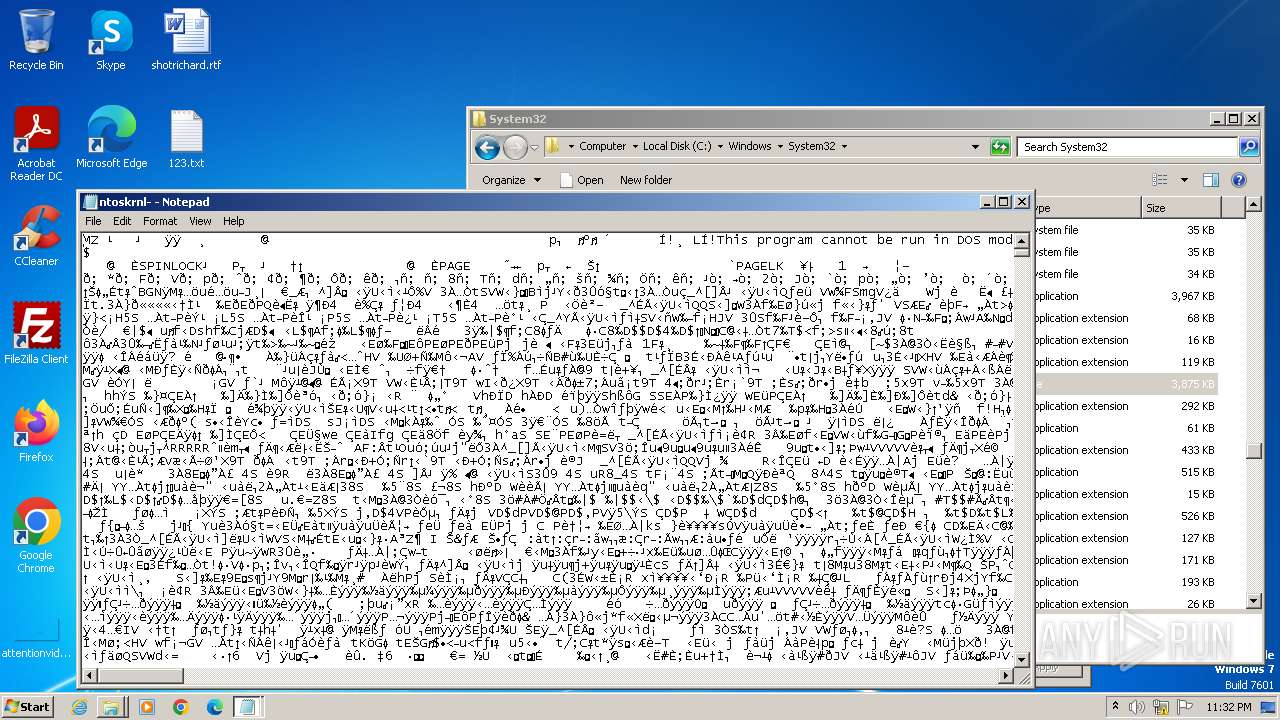
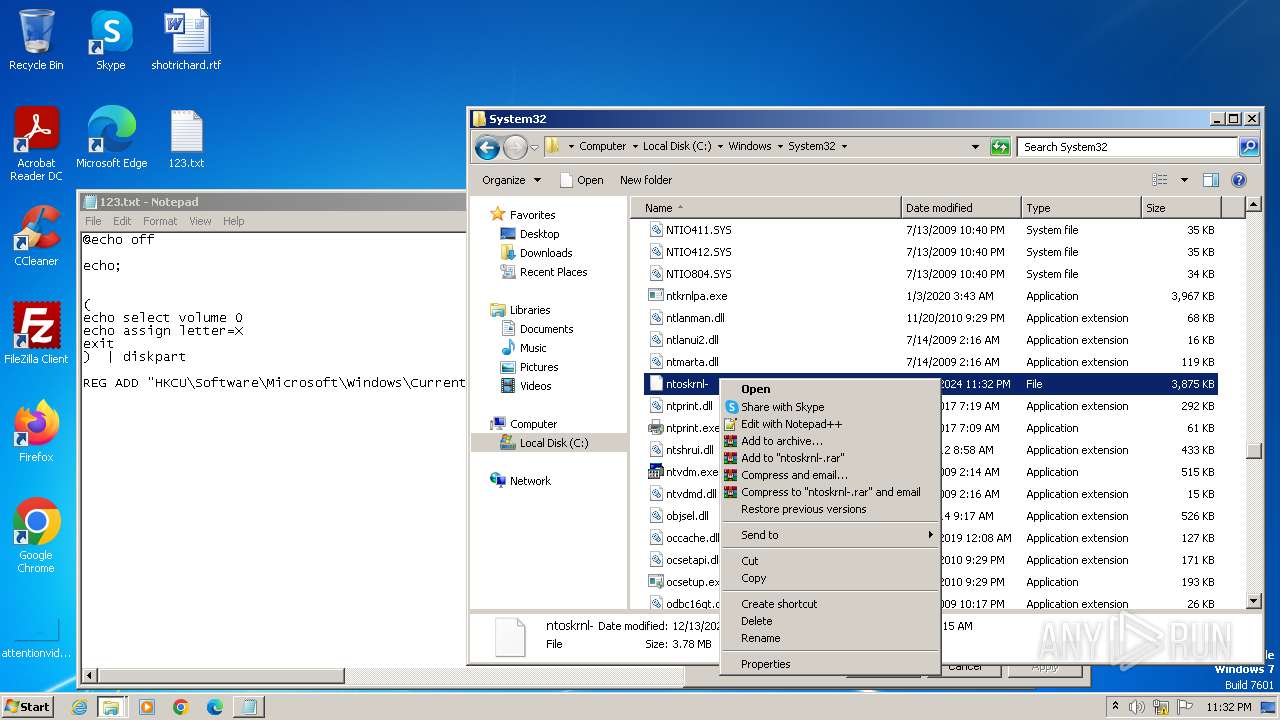
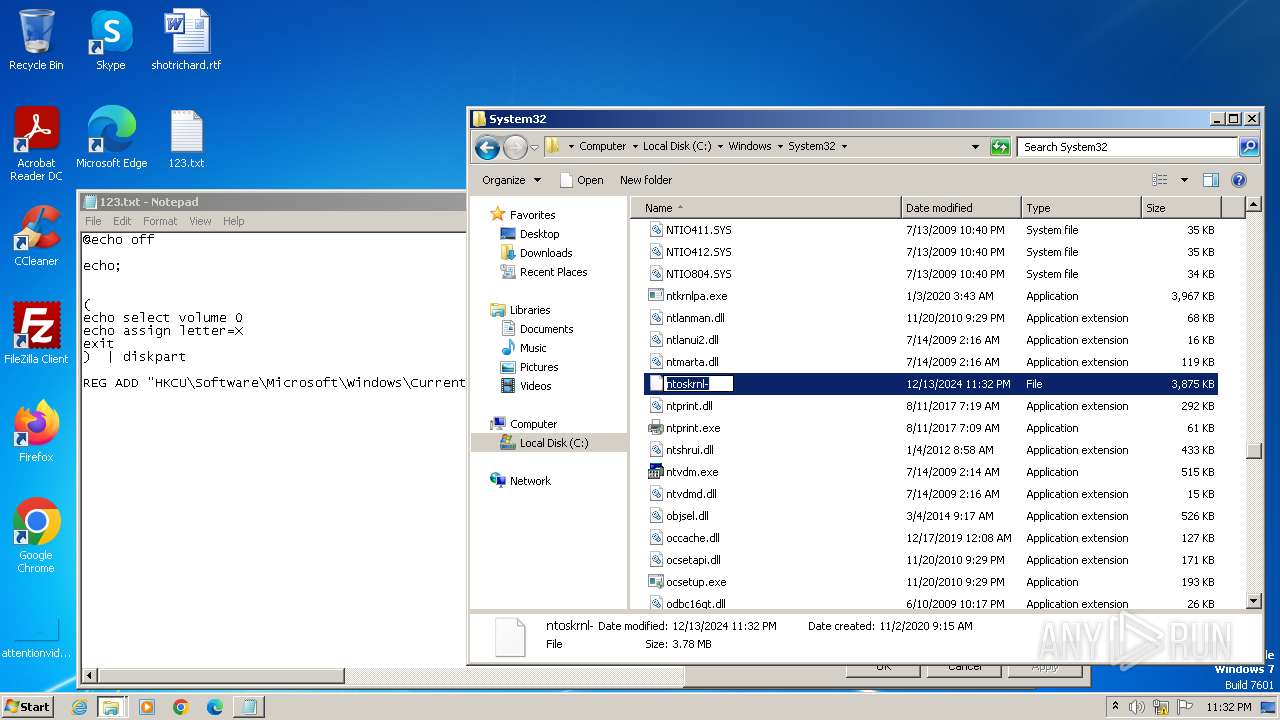
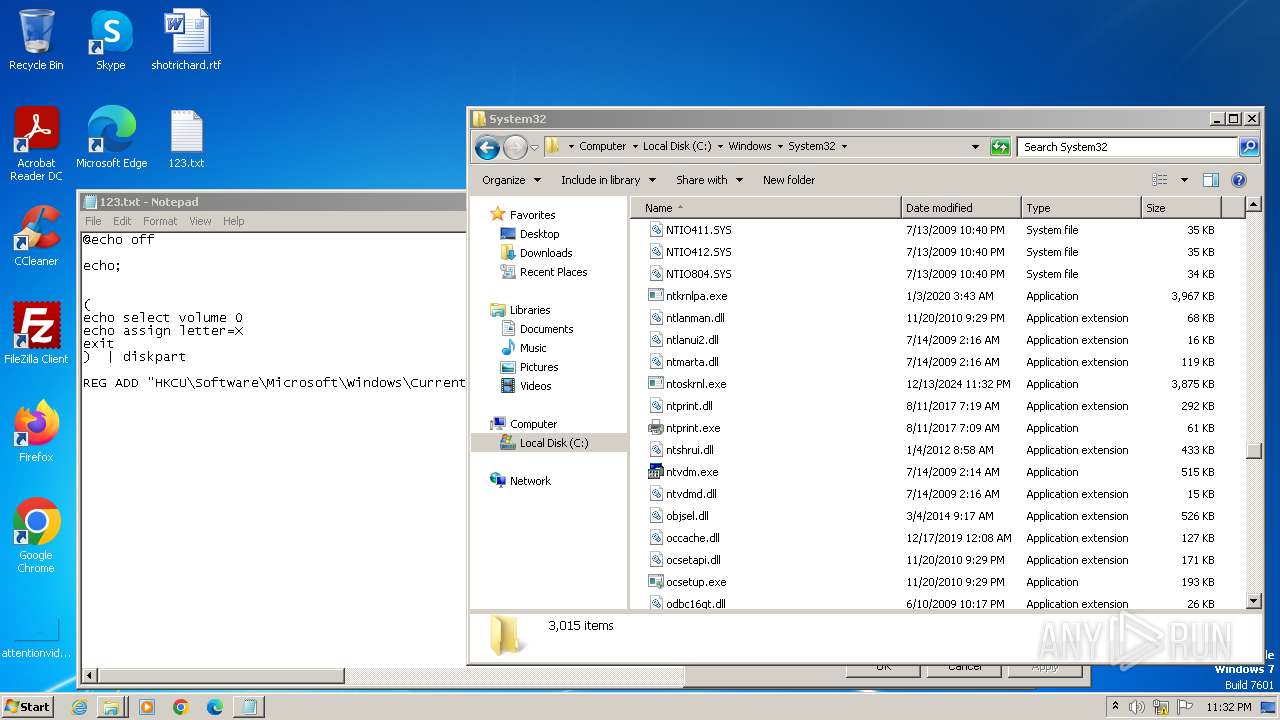
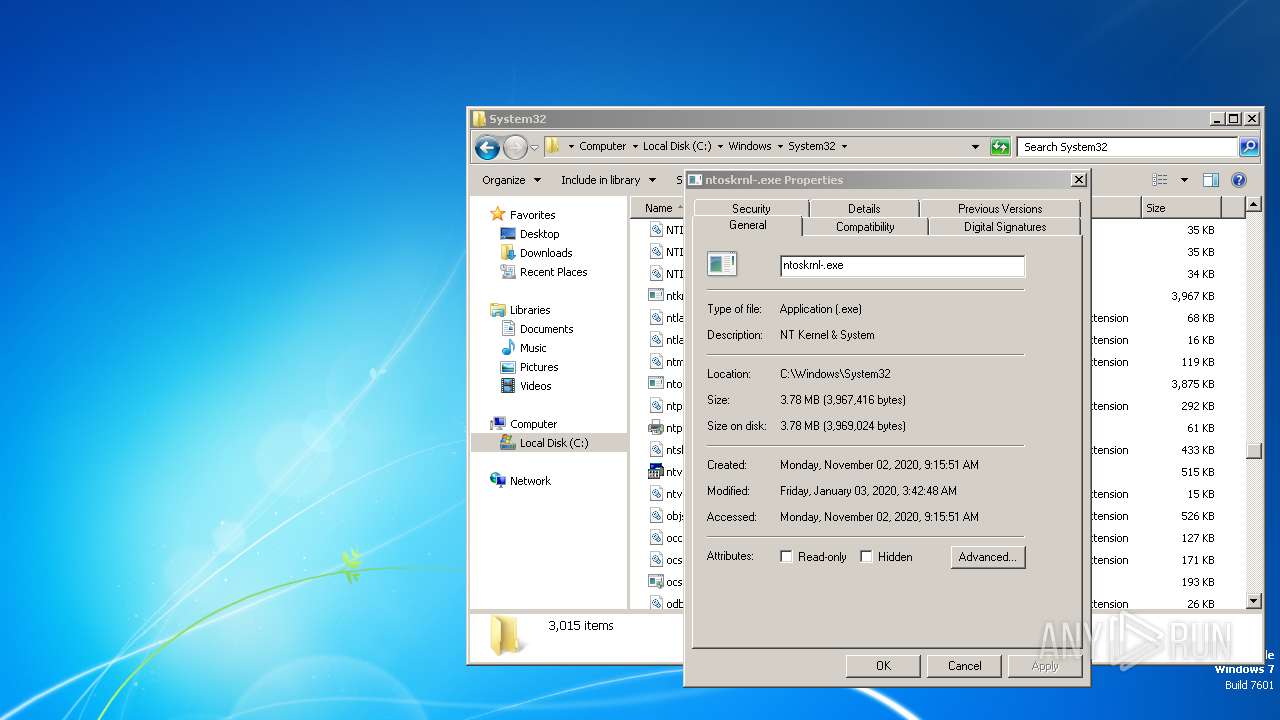
| 3732 | dllhost.exe | C:\Windows\System32\ntoskrnl- | executable | |
MD5:01CB6F291CC558576CDC94831E3A3439 | SHA256:FF71A6E015FD925594D612B7D53139A3EC6A55E4136E9C244E8D680E4D74D630 | |||
| 1552 | sipnotify.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\SipNotify\eoscontent\metadata.json | binary | |
MD5:E8A970BA6CE386EED9A5E724F26212A6 | SHA256:7E06107D585D8FC7870998F3856DCC3E35800AA97E4406AAB83BC8444B6CBDE3 | |||
| 1552 | sipnotify.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\SipNotify\eoscontent\styles.css | text | |
MD5:3383EEF350240253D7C2C2564381B3CB | SHA256:85443493D86D6D7FB0E07BC9705DFC9C858086FBA1B0E508092AB328D5F145E8 | |||
| 1552 | sipnotify.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\SipNotify\eoscontent\microsoft-logo.png | image | |
MD5:B7C73A0CFBA68CC70C35EF9C63703CE4 | SHA256:1D8B27A0266FF526CF95447F3701592A908848467D37C09A00A2516C1F29A013 | |||
| 1552 | sipnotify.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\SipNotify\eoscontent\en-us.html | html | |
MD5:9752942B57692148B9F614CF4C119A36 | SHA256:E31B834DD53FA6815F396FC09C726636ABF98F3367F0CF1590EF5EB3801C75D1 | |||
| 3780 | notepad.exe | C:\Windows\System32\ntoskrnl- | executable | |
MD5:118A13CF6F6A66A7FC0EA533F3AA3834 | SHA256:1FD6204E61E7C80DA49EB0EE7185622F97DCCCE07D20CCEF2A8363CADB41388F | |||
| 3548 | dllhost.exe | C:\Windows\System32\ntoskrnl-.exe | executable | |
MD5:01CB6F291CC558576CDC94831E3A3439 | SHA256:FF71A6E015FD925594D612B7D53139A3EC6A55E4136E9C244E8D680E4D74D630 | |||
| 1104 | dllhost.exe | C:\Windows\System32\ntoskrnl.exe | executable | |
MD5:118A13CF6F6A66A7FC0EA533F3AA3834 | SHA256:1FD6204E61E7C80DA49EB0EE7185622F97DCCCE07D20CCEF2A8363CADB41388F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
14
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1552 | sipnotify.exe | HEAD | 200 | 23.212.215.38:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133786063964210000 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1108 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
1444 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
1552 | sipnotify.exe | 23.212.215.38:80 | query.prod.cms.rt.microsoft.com | AKAMAI-AS | AU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
query.prod.cms.rt.microsoft.com |
| whitelisted |