| File name: | xbc_web_installer_4.5.2406.1808.exe |
| Full analysis: | https://app.any.run/tasks/178ce55b-bdfe-4a56-9447-3105593e4380 |
| Verdict: | Malicious activity |
| Analysis date: | August 06, 2024, 21:08:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | E311EEE1B807B0ADF6B2595FEB59D093 |
| SHA1: | 0AA22F9B05000B5D24BA26FDEA7E5441E4815151 |
| SHA256: | 07001C5D7B1153489670FA31AC816303BAC6363543406871A81CFDA1D880FD99 |
| SSDEEP: | 1536:R1Y36p8VYOlrcJeMPpFW/CwCTqj7uDbS3frDVbyNBmS7K:RSSfONcJeMP2/Cwn7uDbS3fRomSG |
MALICIOUS
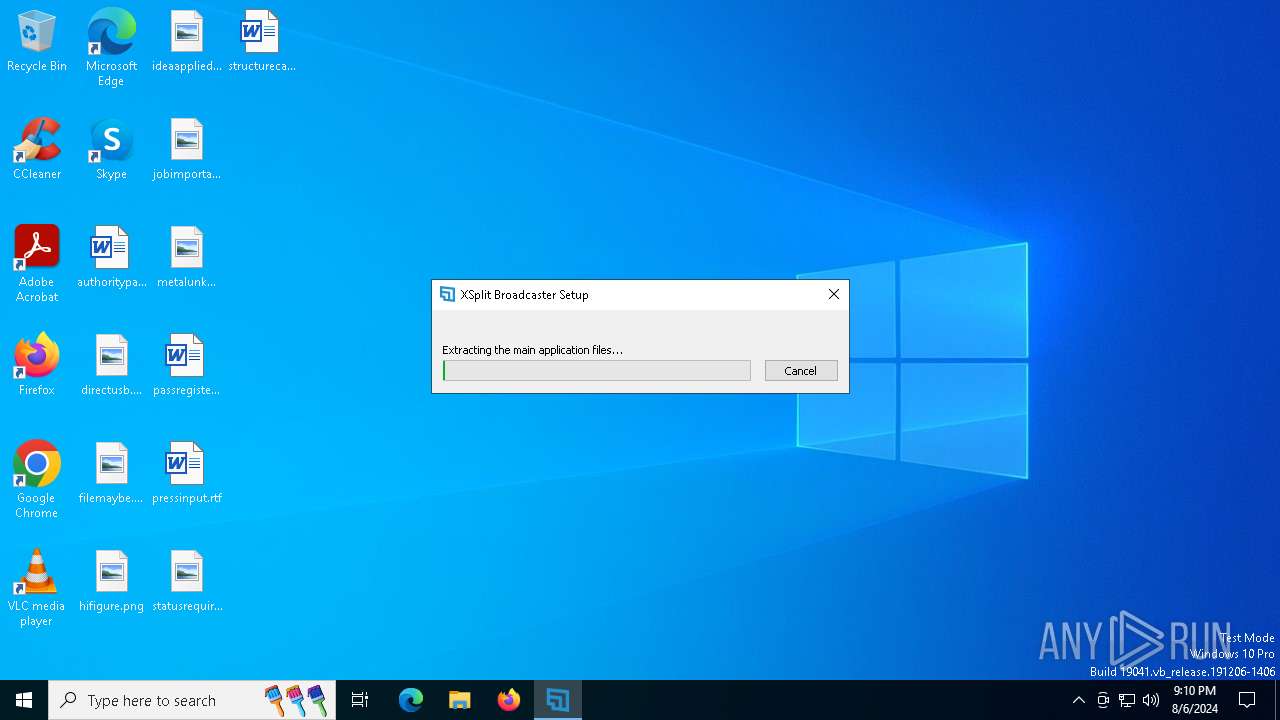
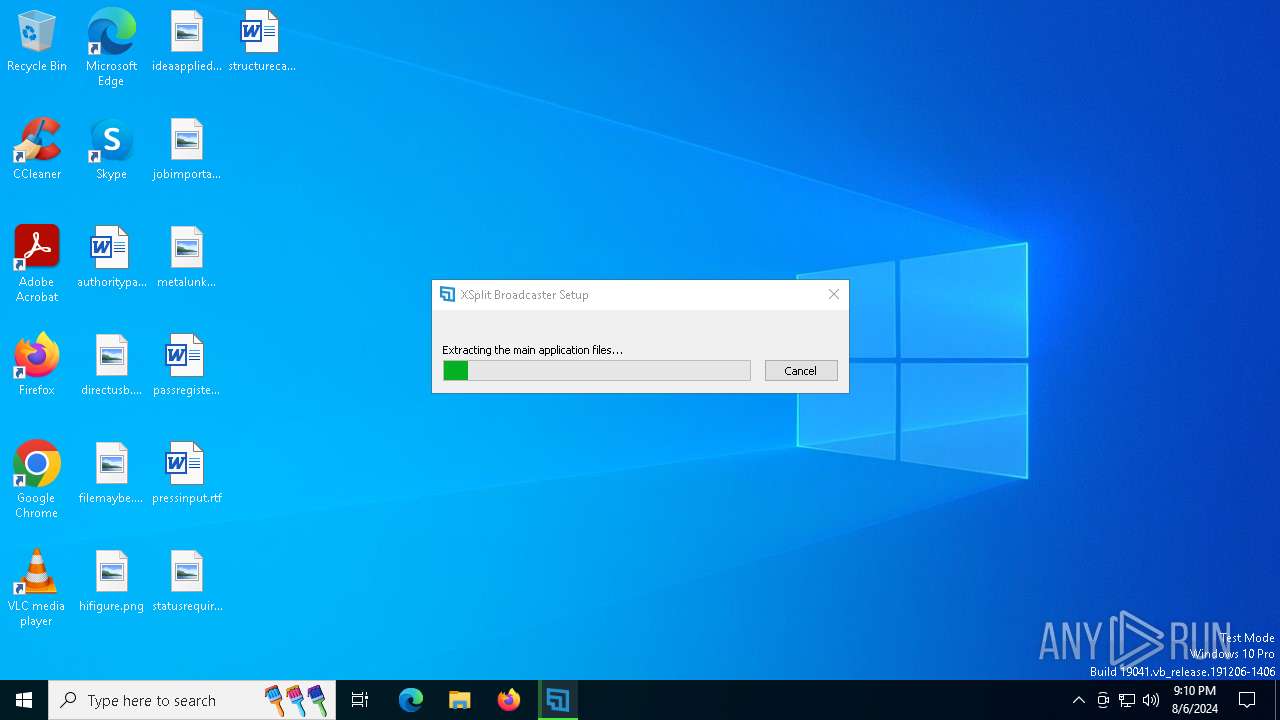
Drops the executable file immediately after the start
- xbc_web_installer_4.5.2406.1808.exe (PID: 6176)
- XSplit_Broadcaster_4.5.2406.1808.exe (PID: 6168)
SUSPICIOUS
Reads the date of Windows installation
- xbc_web_installer_4.5.2406.1808.exe (PID: 6176)
Malware-specific behavior (creating "System.dll" in Temp)
- xbc_web_installer_4.5.2406.1808.exe (PID: 6176)
The process creates files with name similar to system file names
- xbc_web_installer_4.5.2406.1808.exe (PID: 6176)
- XSplit_Broadcaster_4.5.2406.1808.exe (PID: 6168)
Executable content was dropped or overwritten
- xbc_web_installer_4.5.2406.1808.exe (PID: 6176)
- XSplit_Broadcaster_4.5.2406.1808.exe (PID: 6168)
Checks Windows Trust Settings
- xbc_web_installer_4.5.2406.1808.exe (PID: 6176)
Reads security settings of Internet Explorer
- xbc_web_installer_4.5.2406.1808.exe (PID: 6176)
Process drops legitimate windows executable
- XSplit_Broadcaster_4.5.2406.1808.exe (PID: 6168)
Drops a system driver (possible attempt to evade defenses)
- XSplit_Broadcaster_4.5.2406.1808.exe (PID: 6168)
INFO
Create files in a temporary directory
- xbc_web_installer_4.5.2406.1808.exe (PID: 6176)
Drops a (possible) Coronavirus decoy
- XSplit_Broadcaster_4.5.2406.1808.exe (PID: 6168)
Creates files or folders in the user directory
- XSplit_Broadcaster_4.5.2406.1808.exe (PID: 6168)
- xbc_web_installer_4.5.2406.1808.exe (PID: 6176)
Reads the computer name
- xbc_web_installer_4.5.2406.1808.exe (PID: 6176)
- XSplit_Broadcaster_4.5.2406.1808.exe (PID: 6168)
Checks proxy server information
- xbc_web_installer_4.5.2406.1808.exe (PID: 6176)
Checks supported languages
- xbc_web_installer_4.5.2406.1808.exe (PID: 6176)
- XSplit_Broadcaster_4.5.2406.1808.exe (PID: 6168)
Reads the software policy settings
- xbc_web_installer_4.5.2406.1808.exe (PID: 6176)
Reads the machine GUID from the registry
- xbc_web_installer_4.5.2406.1808.exe (PID: 6176)
Reads Environment values
- XSplit_Broadcaster_4.5.2406.1808.exe (PID: 6168)
Process checks computer location settings
- xbc_web_installer_4.5.2406.1808.exe (PID: 6176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:08:01 00:33:55+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x330d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.5.2406.1808 |
| ProductVersionNumber: | 4.5.2406.1808 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | SplitmediaLabs |
| FileDescription: | XSplit Broadcaster Web Installer |
| FileVersion: | 4.5.2406.1808 |
| LegalCopyright: | Copyright (C) 2023 SplitmediaLabs |
| ProductName: | XSplit Broadcaster Web Installer |
| ProductVersion: | 4.5.2406.1808 |
Total processes
130
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6168 | "C:\Users\admin\AppData\Local\Temp\xbc-web-installer\XSplit_Broadcaster_4.5.2406.1808.exe" | C:\Users\admin\AppData\Local\Temp\xbc-web-installer\XSplit_Broadcaster_4.5.2406.1808.exe | xbc_web_installer_4.5.2406.1808.exe | ||||||||||||
User: admin Company: XSplit Integrity Level: MEDIUM Description: XSplit Broadcaster Installer Version: 4.5.2406.1808 Modules
| |||||||||||||||
| 6176 | "C:\Users\admin\AppData\Local\Temp\xbc_web_installer_4.5.2406.1808.exe" | C:\Users\admin\AppData\Local\Temp\xbc_web_installer_4.5.2406.1808.exe | explorer.exe | ||||||||||||
User: admin Company: SplitmediaLabs Integrity Level: MEDIUM Description: XSplit Broadcaster Web Installer Exit code: 2 Version: 4.5.2406.1808 Modules
| |||||||||||||||
Total events
4 425
Read events
4 414
Write events
11
Delete events
0
Modification events
| (PID) Process: | (6176) xbc_web_installer_4.5.2406.1808.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6176) xbc_web_installer_4.5.2406.1808.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6176) xbc_web_installer_4.5.2406.1808.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6176) xbc_web_installer_4.5.2406.1808.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6176) xbc_web_installer_4.5.2406.1808.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6176) xbc_web_installer_4.5.2406.1808.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6176) xbc_web_installer_4.5.2406.1808.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
150
Suspicious files
651
Text files
106
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6176 | xbc_web_installer_4.5.2406.1808.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\AH8CR9J5\XSplit_Broadcaster_4.5.2406.1808[1].exe | — | |
MD5:— | SHA256:— | |||
| 6176 | xbc_web_installer_4.5.2406.1808.exe | C:\Users\admin\AppData\Local\Temp\xbc-web-installer\XSplit_Broadcaster_4.5.2406.1808.exe | — | |
MD5:— | SHA256:— | |||
| 6176 | xbc_web_installer_4.5.2406.1808.exe | C:\Users\admin\AppData\Local\Temp\nsr7F5E.tmp | binary | |
MD5:F6D8987F9E898E1F8380BA7040EC187A | SHA256:B3E1BE1535938BFA8C4005DA67C4C32F4886FBF7D6527329D5DE383BFCAD53CB | |||
| 6176 | xbc_web_installer_4.5.2406.1808.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\274469978BC6FDDEF203BC2B73AAB0D1 | binary | |
MD5:166DED1BA3E1CCC991EB0613B404D72E | SHA256:64215BE46BEE26D1977A242AC36BFE2F6190144041CC754FF719C91385111F2B | |||
| 6168 | XSplit_Broadcaster_4.5.2406.1808.exe | C:\Users\admin\AppData\Roaming\XSplit\Broadcaster\install\63C7359\cef3_5060\locales\am.pak | binary | |
MD5:F1B41D148DD1F9E02BB729F75564EB47 | SHA256:AE77C2A4E92DE311A121F42FD7D87968C54DDCC10621F3A21008C1A6C8A7AF69 | |||
| 6176 | xbc_web_installer_4.5.2406.1808.exe | C:\Users\admin\AppData\Local\Temp\nsw7F7E.tmp\INetC.dll | executable | |
MD5:92EC4DD8C0DDD8C4305AE1684AB65FB0 | SHA256:5520208A33E6409C129B4EA1270771F741D95AFE5B048C2A1E6A2CC2AD829934 | |||
| 6168 | XSplit_Broadcaster_4.5.2406.1808.exe | C:\Users\admin\AppData\Roaming\XSplit\Broadcaster\install\63C7359\cef3_5060\locales\ar.pak | binary | |
MD5:4AC067C588621471E465A1072B78CF3D | SHA256:4C24CCDC00E0AD21BAF179288FC6F0579590507201D5E0E74BB1C53A62C08911 | |||
| 6168 | XSplit_Broadcaster_4.5.2406.1808.exe | C:\Users\admin\AppData\Roaming\XSplit\Broadcaster\install\63C7359\cef3_5060\locales\bn.pak | binary | |
MD5:8271D14066EC65E00502F0727B0DBCB8 | SHA256:C141B66371B89143DBA0D1B35CB04ECE24C9926B27DA1578D3B68745D693A82A | |||
| 6176 | xbc_web_installer_4.5.2406.1808.exe | C:\Users\admin\AppData\Local\Temp\nsw7F7E.tmp\System.dll | executable | |
MD5:55A26D7800446F1373056064C64C3CE8 | SHA256:904FD5481D72F4E03B01A455F848DEDD095D0FB17E33608E0D849F5196FB6FF8 | |||
| 6176 | xbc_web_installer_4.5.2406.1808.exe | C:\Users\admin\AppData\Local\Temp\nsw7F7E.tmp\modern-header.bmp | image | |
MD5:7BCA166A6A03D4AF71EE9DFDE2696078 | SHA256:17463B8B94AE671BF35091537E16140044FA3AE0E81FCF4E15BCC1327C171923 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
31
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6176 | xbc_web_installer_4.5.2406.1808.exe | GET | 200 | 95.100.146.72:80 | http://r11.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBQaUrm0WeTDM5ghfoZtS72KO9ZnzgQUCLkRO6XQhRi06g%2BgrZ%2BGHo78OCcCEgRhb4uwiwmArGhA7Y2SCnxLaA%3D%3D | unknown | — | — | whitelisted |
2968 | svchost.exe | GET | 304 | 2.23.197.184:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
6552 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | unknown |
3068 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
5336 | SearchApp.exe | 95.100.146.33:443 | th.bing.com | Akamai International B.V. | CZ | unknown |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
4 | System | 192.168.100.255:137 | — | — | — | unknown |
1636 | svchost.exe | 20.190.159.0:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3068 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6176 | xbc_web_installer_4.5.2406.1808.exe | 138.199.36.9:443 | cdn2.xsplit.com | Datacamp Limited | DE | unknown |
6176 | xbc_web_installer_4.5.2406.1808.exe | 95.100.146.72:80 | r11.o.lencr.org | Akamai International B.V. | CZ | unknown |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
th.bing.com |
| unknown |
settings-win.data.microsoft.com |
| unknown |
cdn2.xsplit.com |
| unknown |
r11.o.lencr.org |
| unknown |
arc.msn.com |
| unknown |
slscr.update.microsoft.com |
| unknown |
fe3cr.delivery.mp.microsoft.com |
| unknown |
x1.c.lencr.org |
| unknown |
nexusrules.officeapps.live.com |
| unknown |
client.wns.windows.com |
| unknown |