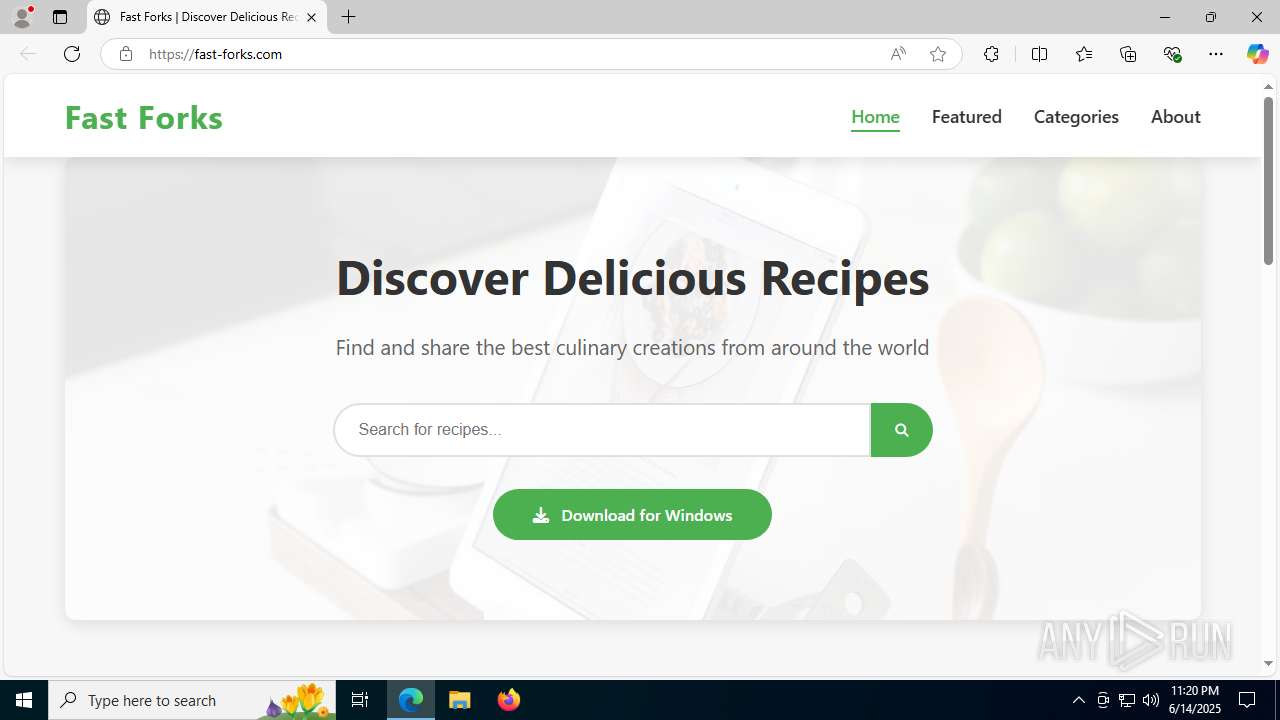
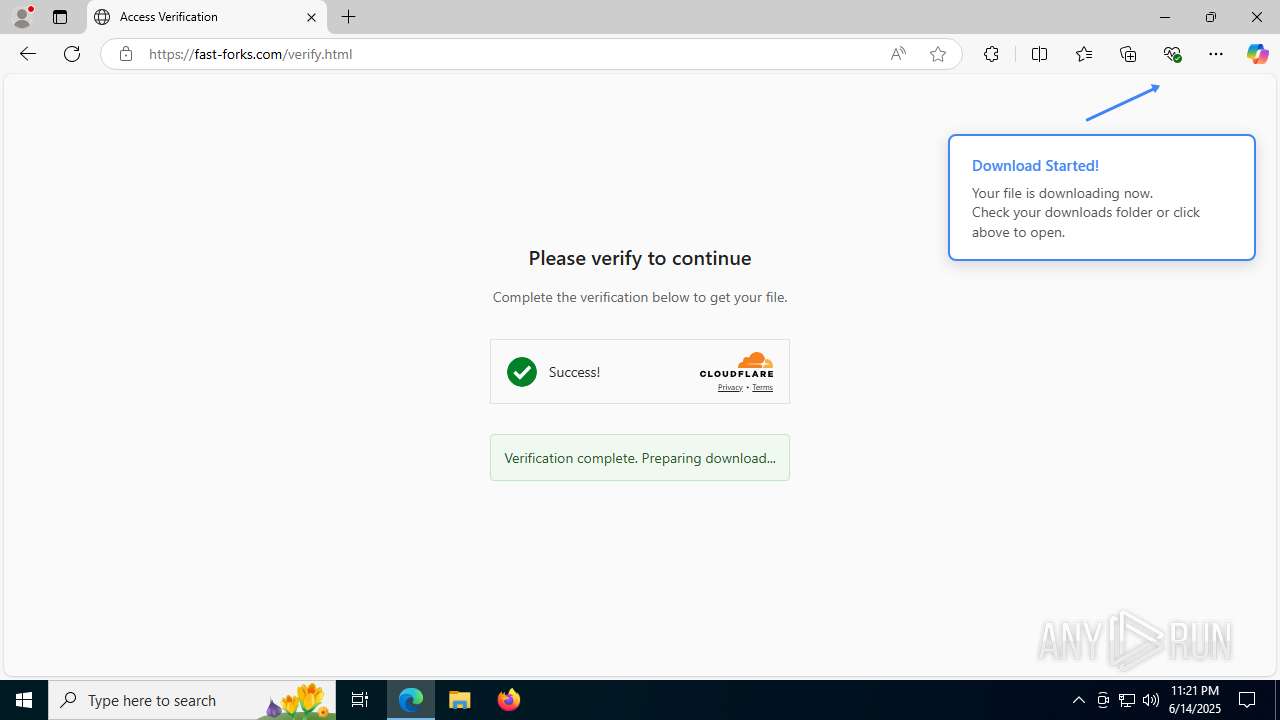
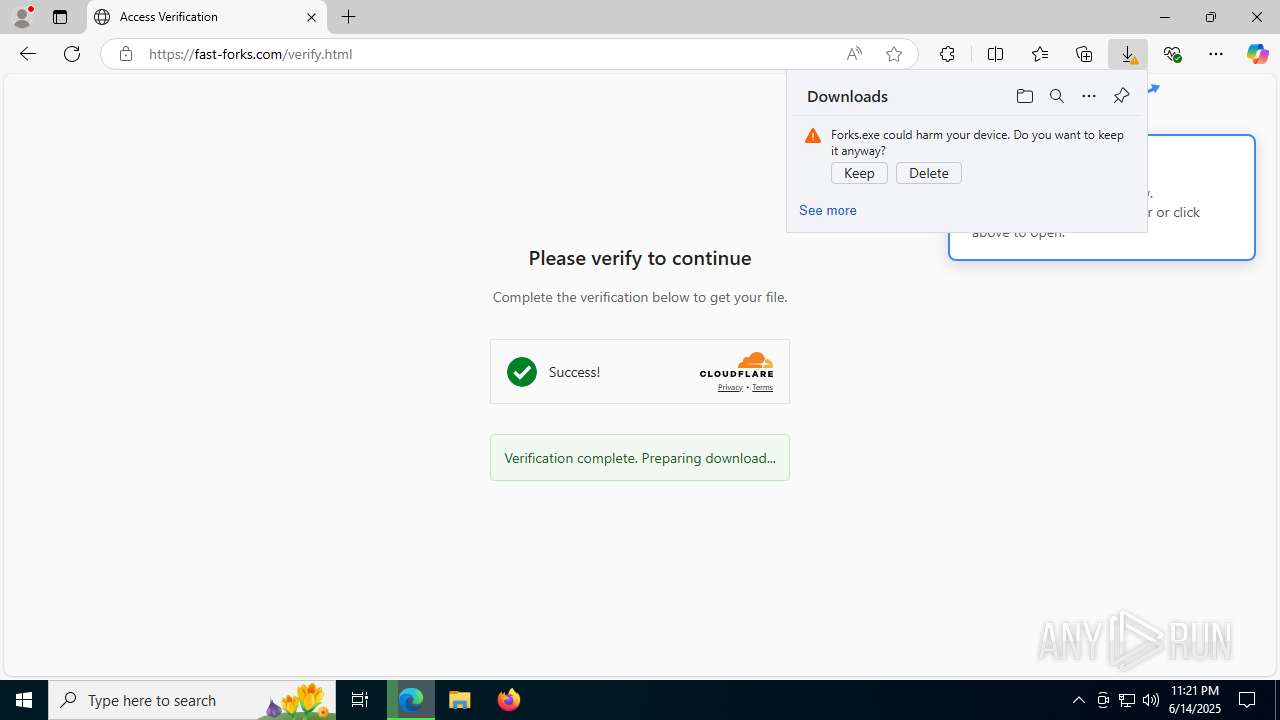
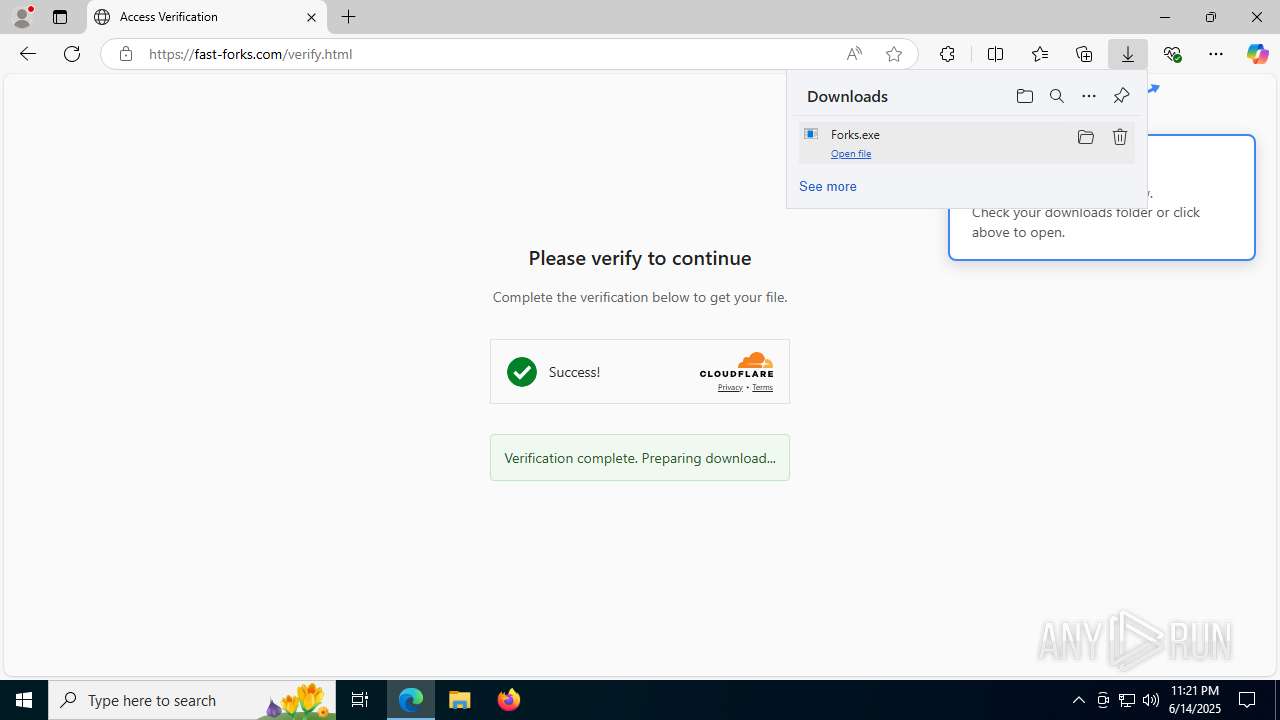
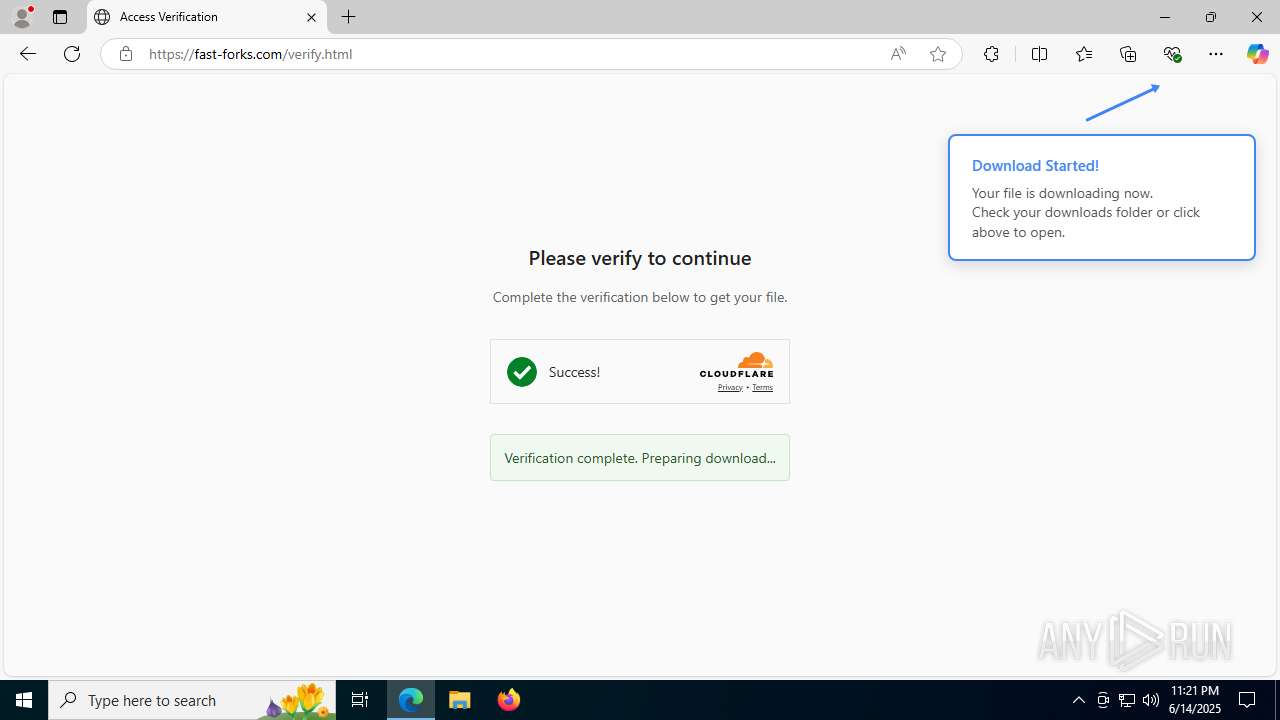
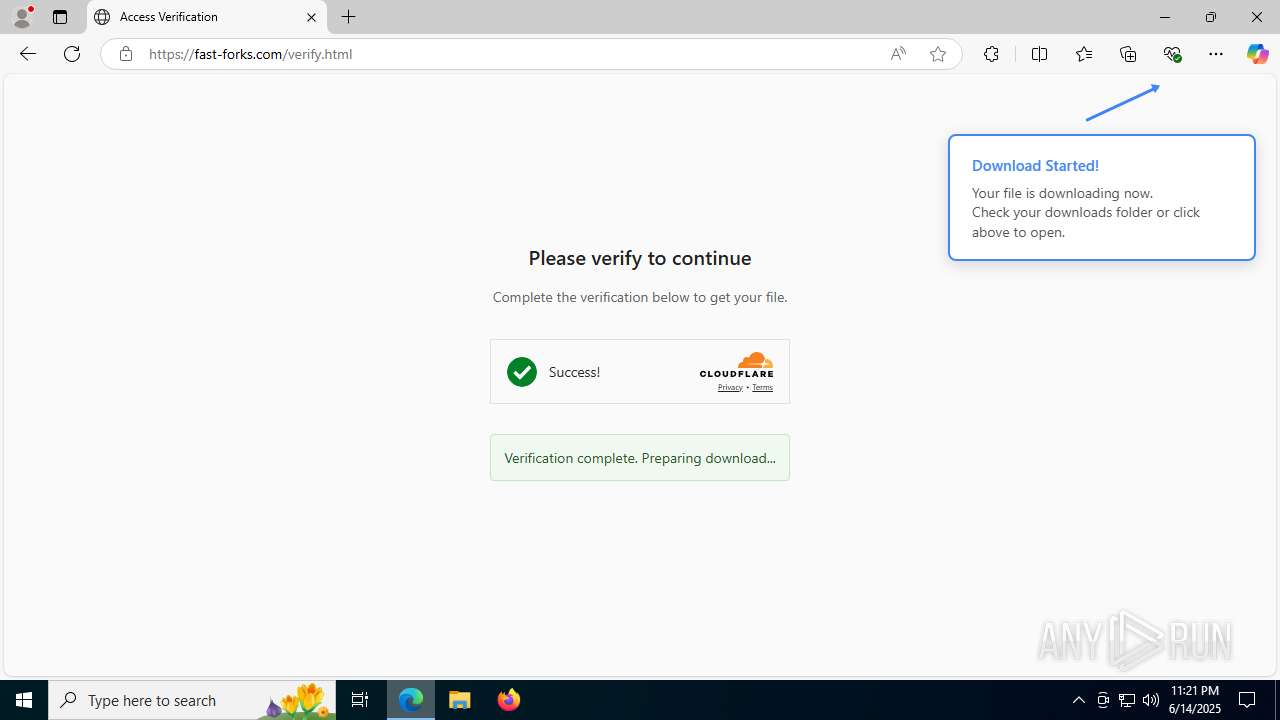
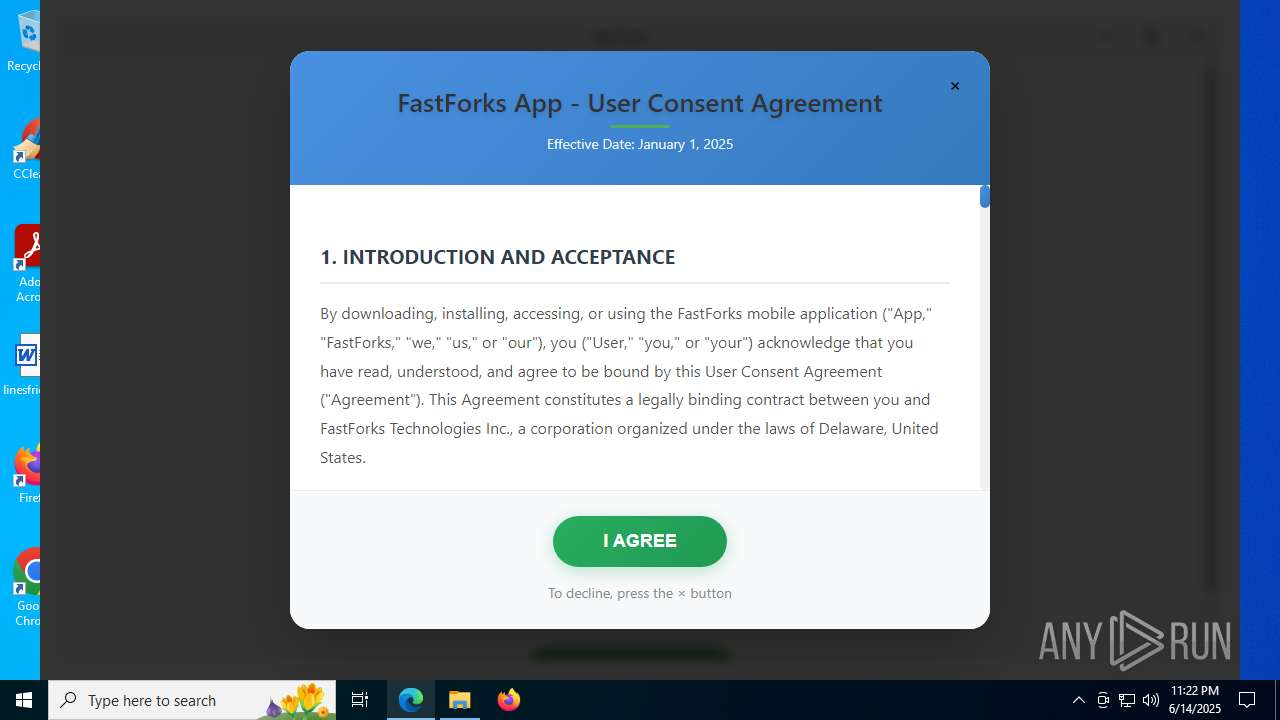
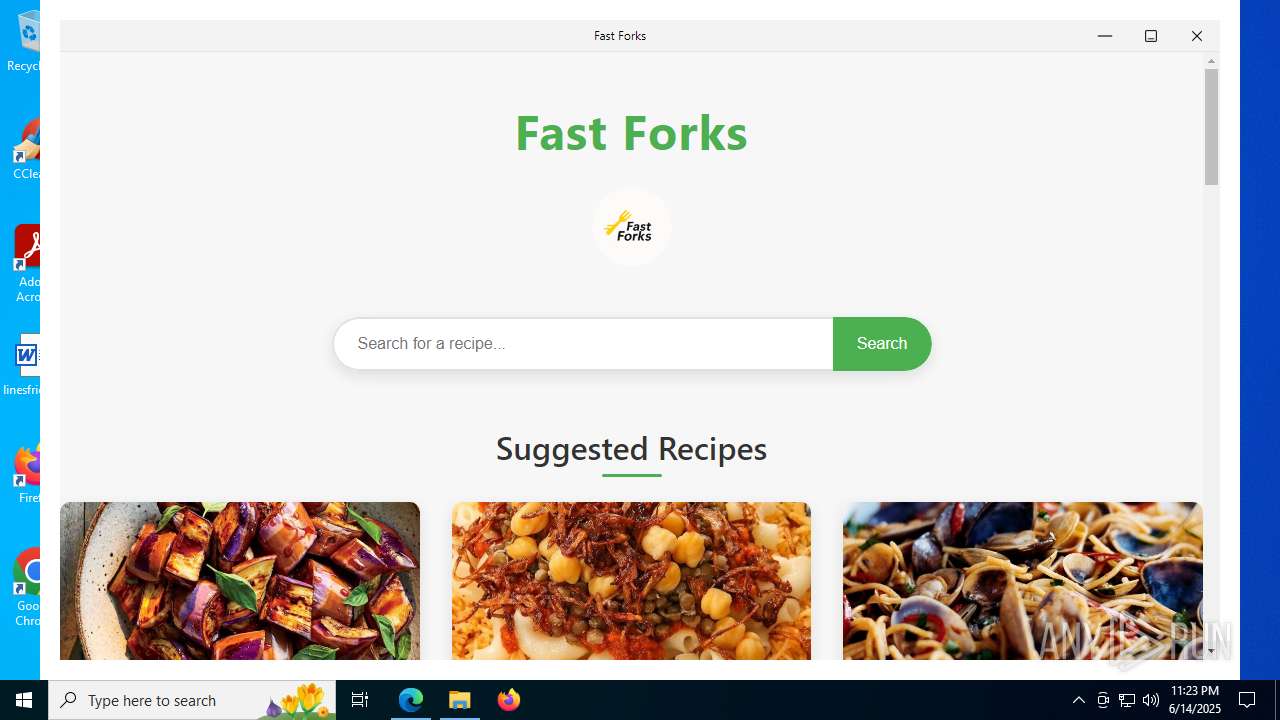
| URL: | fast-forks.com |
| Full analysis: | https://app.any.run/tasks/80821fcc-4fd6-4802-b5e9-f72322aaa34e |
| Verdict: | Malicious activity |
| Analysis date: | June 14, 2025, 23:20:46 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0AD0FB632E4773D7B6E9E7CD20CFC511 |
| SHA1: | 688C999D90B6DF367E9279843B9E6DFB238C3647 |
| SHA256: | 06D143D53B7C3EB9B17CDBB714872225DAF3970B3F05654D01261B82DD1CCB21 |
| SSDEEP: | 3:PXVGKI:vVGKI |
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops 7-zip archiver for unpacking
- Forks.exe (PID: 7204)
- Forks.exe (PID: 516)
Malware-specific behavior (creating "System.dll" in Temp)
- Forks.exe (PID: 7204)
- Forks.exe (PID: 516)
The process creates files with name similar to system file names
- Forks.exe (PID: 7204)
- Forks.exe (PID: 516)
Executable content was dropped or overwritten
- Forks.exe (PID: 7204)
- Forks.exe (PID: 516)
Process drops legitimate windows executable
- Forks.exe (PID: 7204)
- Forks.exe (PID: 516)
Reads security settings of Internet Explorer
- Forks.exe (PID: 7204)
- Forks.exe (PID: 516)
Application launched itself
- Recipe Finder - Fast Forks.exe (PID: 7952)
- Recipe Finder - Fast Forks.exe (PID: 1128)
There is functionality for taking screenshot (YARA)
- Forks.exe (PID: 7204)
- Recipe Finder - Fast Forks.exe (PID: 2512)
INFO
Checks supported languages
- identity_helper.exe (PID: 7684)
- Forks.exe (PID: 7204)
- Recipe Finder - Fast Forks.exe (PID: 7952)
- Recipe Finder - Fast Forks.exe (PID: 2512)
- Recipe Finder - Fast Forks.exe (PID: 7444)
- Forks.exe (PID: 516)
- Recipe Finder - Fast Forks.exe (PID: 6940)
Reads Environment values
- identity_helper.exe (PID: 7684)
- Recipe Finder - Fast Forks.exe (PID: 7952)
Application launched itself
- msedge.exe (PID: 3656)
Reads the computer name
- identity_helper.exe (PID: 7684)
- Forks.exe (PID: 7204)
- Recipe Finder - Fast Forks.exe (PID: 7952)
- Recipe Finder - Fast Forks.exe (PID: 2512)
- Recipe Finder - Fast Forks.exe (PID: 7444)
- Recipe Finder - Fast Forks.exe (PID: 6940)
- Forks.exe (PID: 516)
Create files in a temporary directory
- Forks.exe (PID: 7204)
- Recipe Finder - Fast Forks.exe (PID: 7952)
- Forks.exe (PID: 516)
Executable content was dropped or overwritten
- msedge.exe (PID: 3656)
Reads product name
- Recipe Finder - Fast Forks.exe (PID: 7952)
Checks proxy server information
- Recipe Finder - Fast Forks.exe (PID: 7952)
Process checks computer location settings
- Recipe Finder - Fast Forks.exe (PID: 7952)
- Recipe Finder - Fast Forks.exe (PID: 6940)
Creates files or folders in the user directory
- Recipe Finder - Fast Forks.exe (PID: 7444)
- Recipe Finder - Fast Forks.exe (PID: 7952)
Node.js compiler has been detected
- Recipe Finder - Fast Forks.exe (PID: 7952)
- Recipe Finder - Fast Forks.exe (PID: 2512)
- Recipe Finder - Fast Forks.exe (PID: 7444)
Reads the machine GUID from the registry
- Recipe Finder - Fast Forks.exe (PID: 7952)
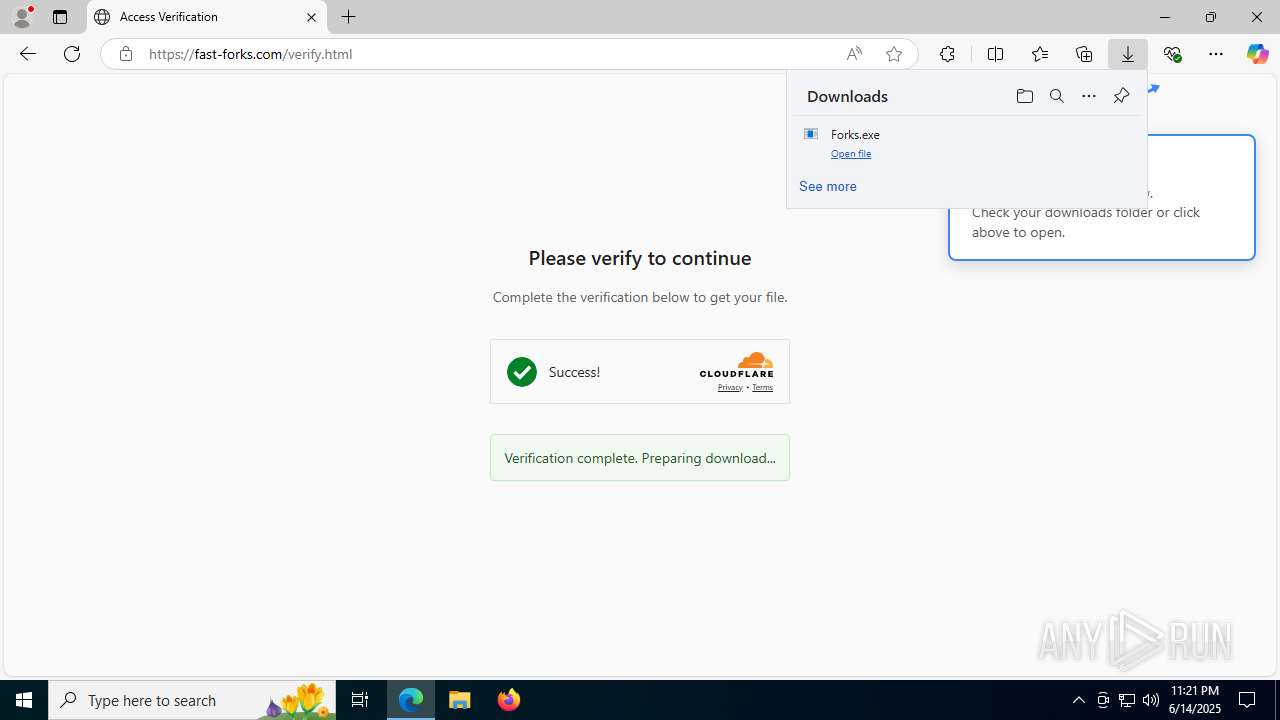
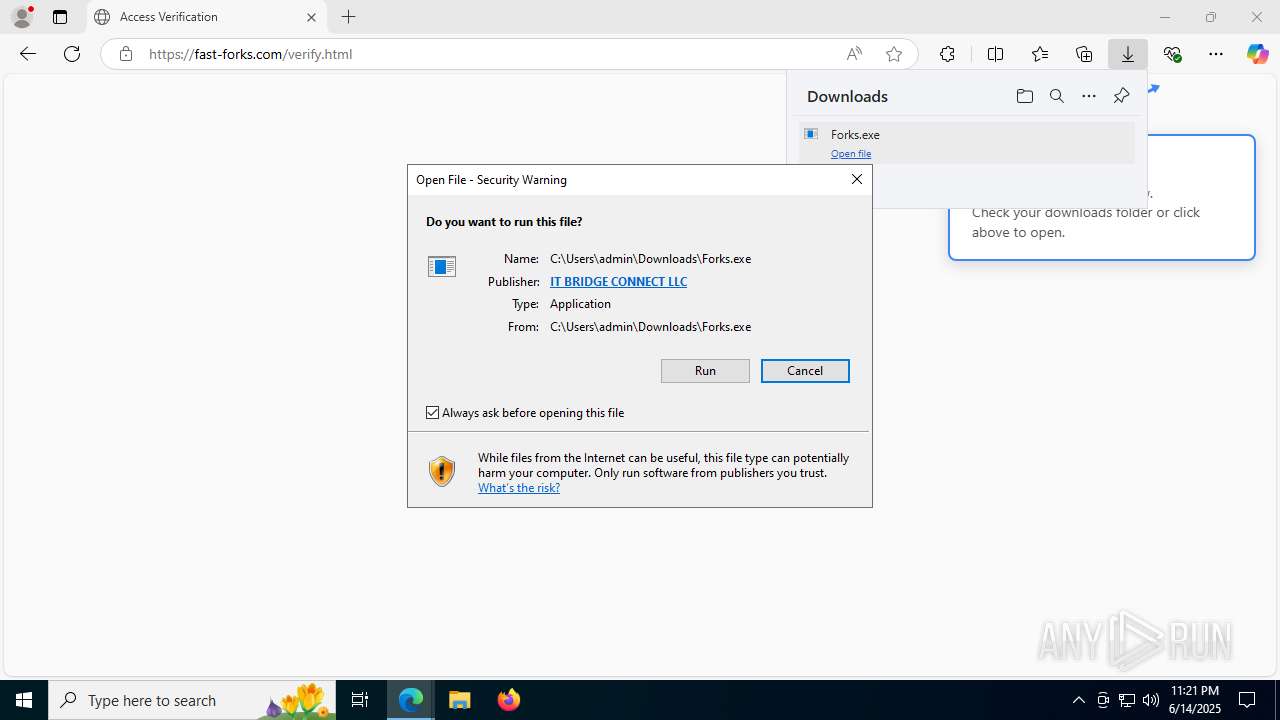
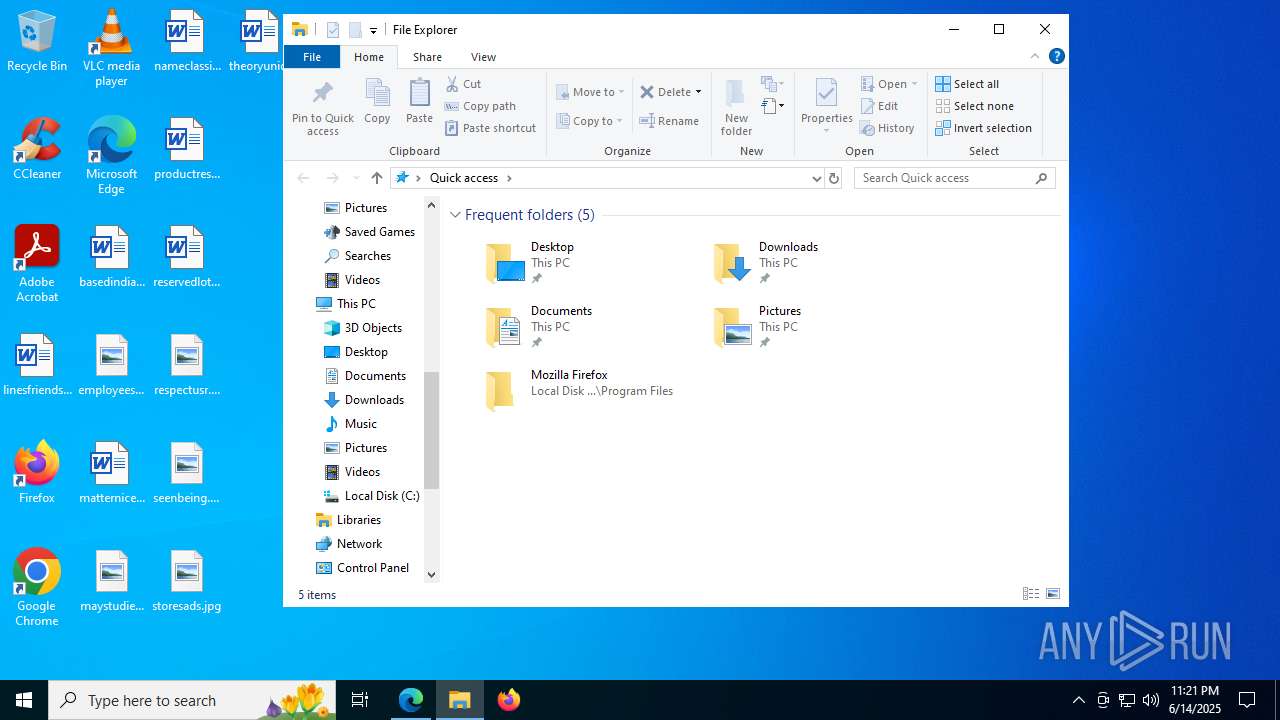
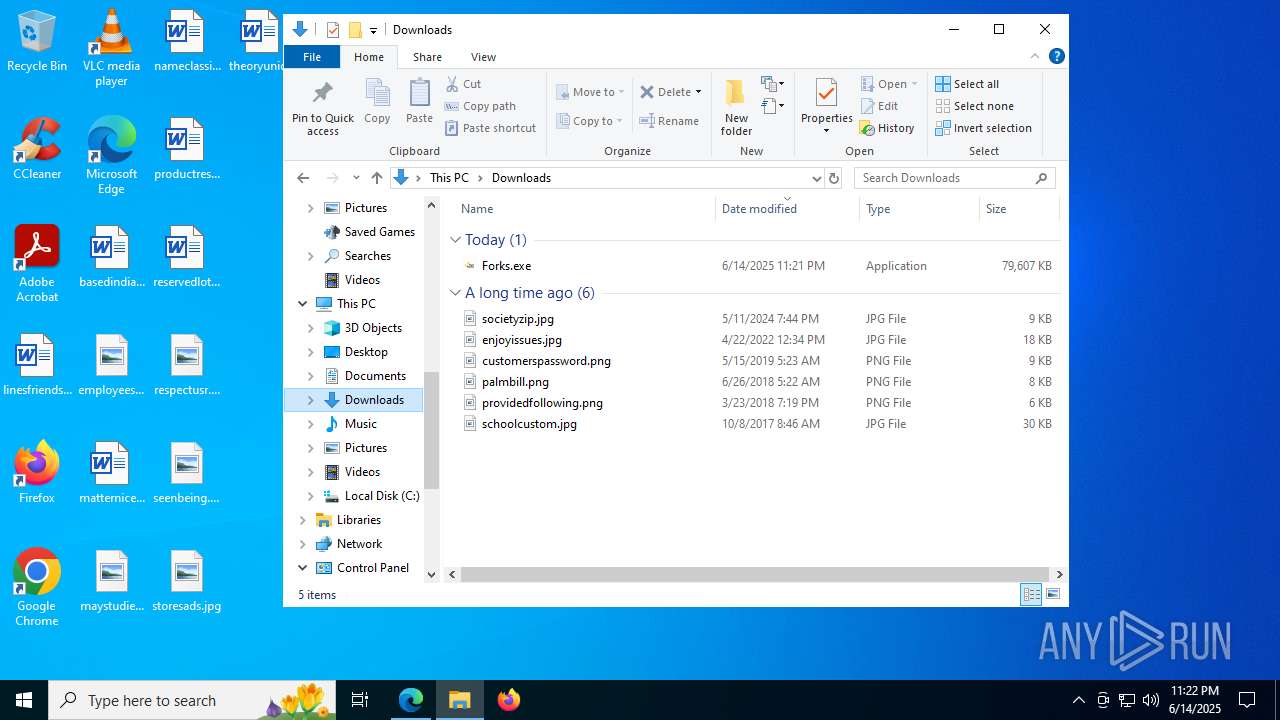
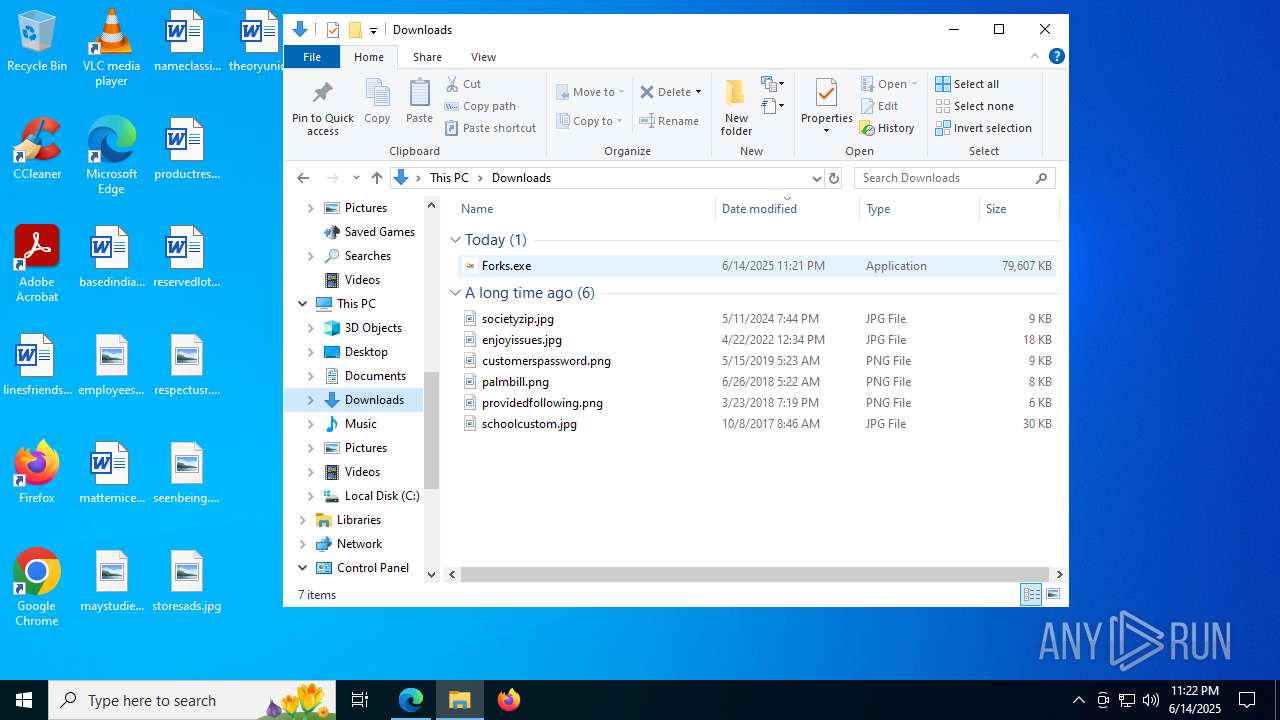
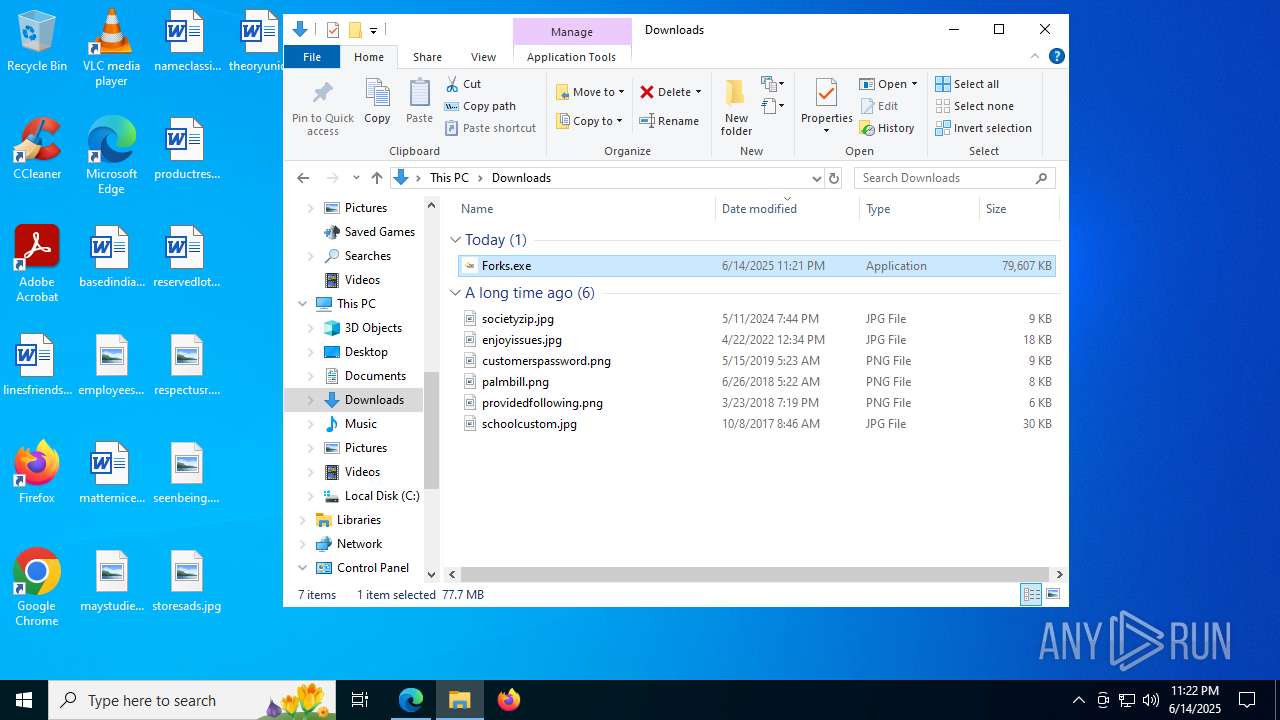
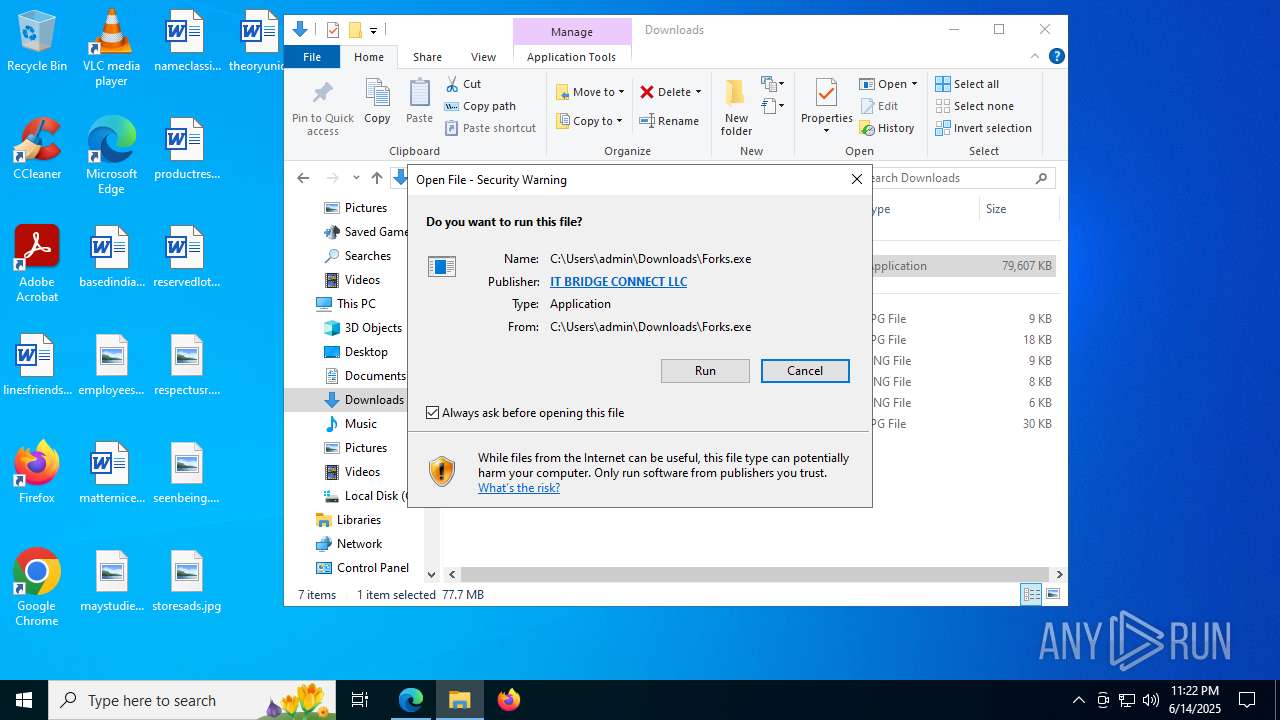
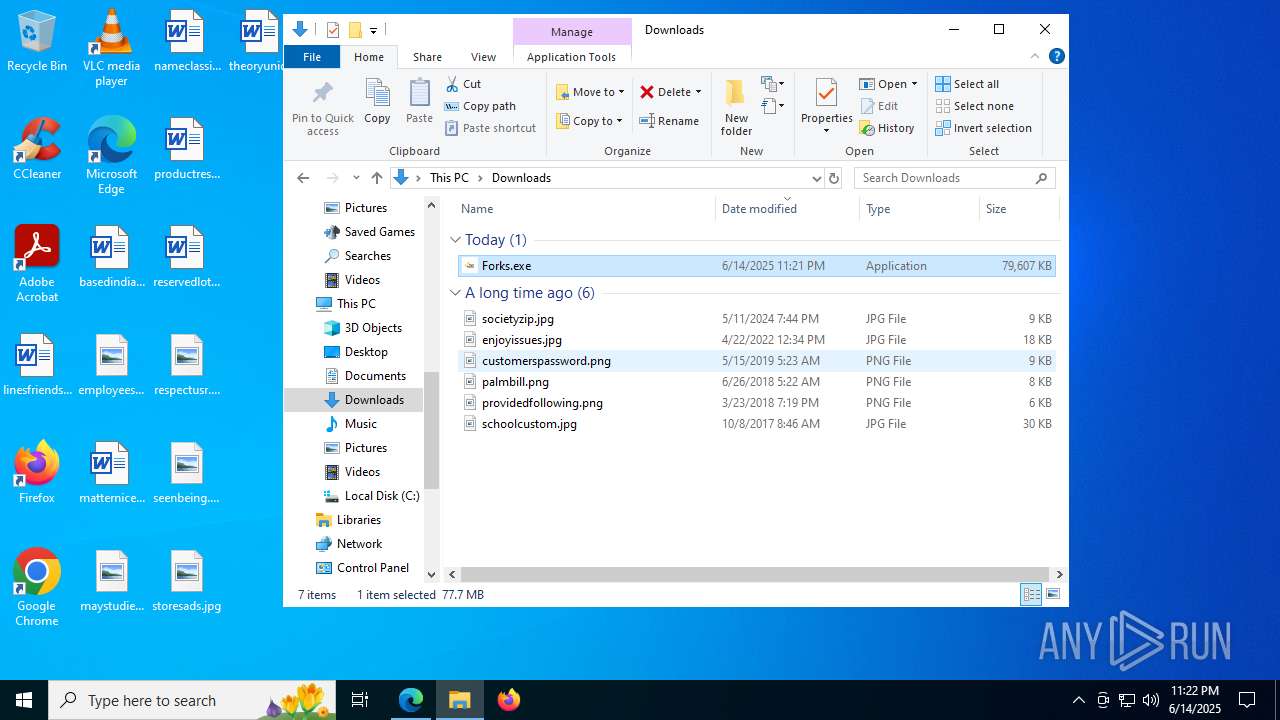
Manual execution by a user
- Forks.exe (PID: 516)
The sample compiled with english language support
- Forks.exe (PID: 516)
- Forks.exe (PID: 7204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
195
Monitored processes
51
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Users\admin\AppData\Local\Temp\2yEFuyYhhshON5bKrWYYOtEHbKd\Recipe Finder - Fast Forks.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\recipe-finder" --app-path="C:\Users\admin\AppData\Local\Temp\2yEFuyYhhshON5bKrWYYOtEHbKd\resources\app.asar" --no-sandbox --no-zygote --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=2496 --field-trial-handle=1708,i,11993691521840110009,2186209650445742063,262144 --enable-features=kWebSQLAccess --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version /prefetch:1 | C:\Users\admin\AppData\Local\Temp\2yEFuyYhhshON5bKrWYYOtEHbKd\Recipe Finder - Fast Forks.exe | Recipe Finder - Fast Forks.exe | ||||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: Recipe Finder - Fast Forks Version: 1.0.0 Modules
| |||||||||||||||
| 516 | "C:\Users\admin\Downloads\Forks.exe" | C:\Users\admin\Downloads\Forks.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Recipe finder app powered by fast-forks.com Version: 1.0.0 Modules
| |||||||||||||||
| 760 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3624,i,6686105159311981821,9159852968588737308,262144 --variations-seed-version --mojo-platform-channel-handle=3808 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1128 | "C:\Users\admin\AppData\Local\Temp\2yEFuyYhhshON5bKrWYYOtEHbKd\Recipe Finder - Fast Forks.exe" | C:\Users\admin\AppData\Local\Temp\2yEFuyYhhshON5bKrWYYOtEHbKd\Recipe Finder - Fast Forks.exe | — | Forks.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: Recipe Finder - Fast Forks Version: 1.0.0 Modules
| |||||||||||||||
| 1180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3616,i,6686105159311981821,9159852968588737308,262144 --variations-seed-version --mojo-platform-channel-handle=3640 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1352 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --always-read-main-dll --field-trial-handle=4560,i,6686105159311981821,9159852968588737308,262144 --variations-seed-version --mojo-platform-channel-handle=6868 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2148 | "C:\Users\admin\AppData\Local\Temp\2yEFuyYhhshON5bKrWYYOtEHbKd\Recipe Finder - Fast Forks.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --user-data-dir="C:\Users\admin\AppData\Roaming\recipe-finder" --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAACEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=3264 --field-trial-handle=1752,i,4331873472193699964,6189146088052012835,262144 --enable-features=kWebSQLAccess --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version /prefetch:8 | C:\Users\admin\AppData\Local\Temp\2yEFuyYhhshON5bKrWYYOtEHbKd\Recipe Finder - Fast Forks.exe | — | Recipe Finder - Fast Forks.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: Recipe Finder - Fast Forks Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 2512 | "C:\Users\admin\AppData\Local\Temp\2yEFuyYhhshON5bKrWYYOtEHbKd\Recipe Finder - Fast Forks.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\recipe-finder" --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1748 --field-trial-handle=1752,i,4331873472193699964,6189146088052012835,262144 --enable-features=kWebSQLAccess --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version /prefetch:2 | C:\Users\admin\AppData\Local\Temp\2yEFuyYhhshON5bKrWYYOtEHbKd\Recipe Finder - Fast Forks.exe | — | Recipe Finder - Fast Forks.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: LOW Description: Recipe Finder - Fast Forks Version: 1.0.0 Modules
| |||||||||||||||
| 2524 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=4108,i,6686105159311981821,9159852968588737308,262144 --variations-seed-version --mojo-platform-channel-handle=6824 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3288 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=6768,i,6686105159311981821,9159852968588737308,262144 --variations-seed-version --mojo-platform-channel-handle=5688 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
22 017
Read events
21 945
Write events
18
Delete events
54
Modification events
| (PID) Process: | (3656) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3656) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3656) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3656) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2737A4B226962F00 | |||
| (PID) Process: | (3656) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3656) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393930 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0535BC5C-4023-4C55-8F49-038244AE212F} | |||
| (PID) Process: | (3656) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393930 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9717191F-9405-4981-BE38-8CF4F17D0351} | |||
| (PID) Process: | (3656) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (3656) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 20E1CDB226962F00 | |||
| (PID) Process: | (3656) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393930 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5C087434-AD6B-4D13-BCEC-0A008FA9EC3B} | |||
Executable files
40
Suspicious files
606
Text files
214
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF176fd1.TMP | — | |
MD5:— | SHA256:— | |||
| 3656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF176fd1.TMP | — | |
MD5:— | SHA256:— | |||
| 3656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF176fd1.TMP | — | |
MD5:— | SHA256:— | |||
| 3656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF176fe0.TMP | — | |
MD5:— | SHA256:— | |||
| 3656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF176ff0.TMP | — | |
MD5:— | SHA256:— | |||
| 3656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
98
DNS requests
84
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6772 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:7dnPRWBWn6s6Kq4DK6fNy11FfluvPUjRbR2zCUkJQuc&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1652 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3656 | msedge.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgW3WQu2HUdhUx4%2Fde0%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7908 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3656 | msedge.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/gsgccr45evcodesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQaCbVYh07WONuW4e63Ydlu4AlbDAQUJZ3Q%2FFkJhmPF7POxEztXHAOSNhECDGCIxE6nDf9tsUoAXQ%3D%3D | unknown | — | — | whitelisted |
8032 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750195136&P2=404&P3=2&P4=JYmOobdvYJUvIwfyxkDzEWMszKjUVByCs4TXS863xaiFs%2bJqOAH08OD%2bsz%2biF38kwzZ2aRlwMNmCMybyMrI%2fUQ%3d%3d | unknown | — | — | whitelisted |
7908 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8032 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750195136&P2=404&P3=2&P4=JYmOobdvYJUvIwfyxkDzEWMszKjUVByCs4TXS863xaiFs%2bJqOAH08OD%2bsz%2biF38kwzZ2aRlwMNmCMybyMrI%2fUQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5476 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6772 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6772 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6772 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6772 | msedge.exe | 2.23.227.211:443 | copilot.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
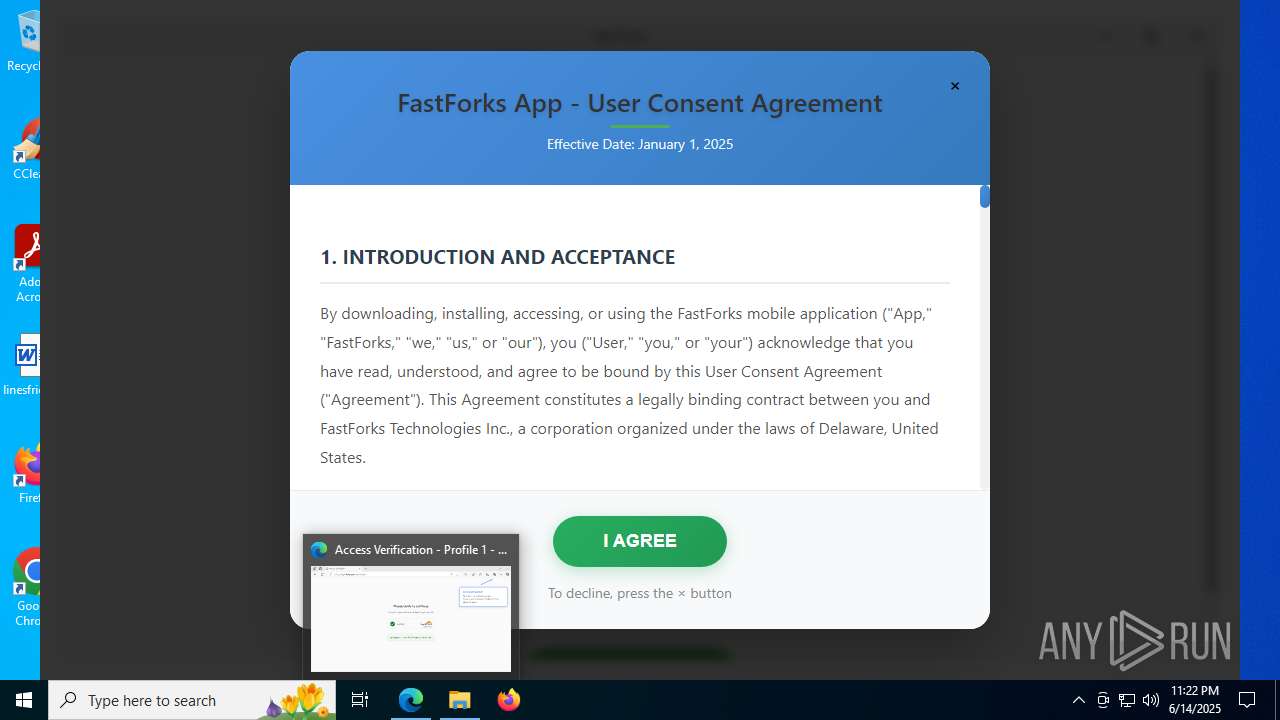
6772 | msedge.exe | 104.21.15.179:443 | fast-forks.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
fast-forks.com |
| unknown |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
images.unsplash.com |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
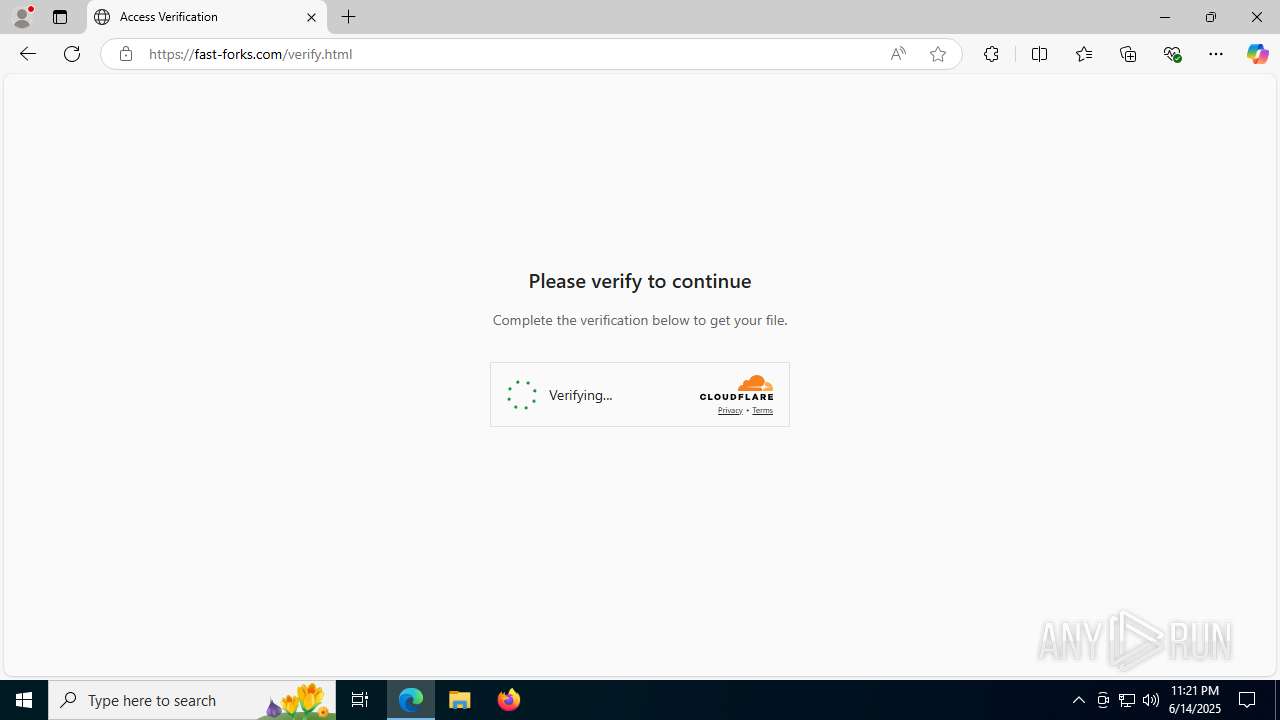
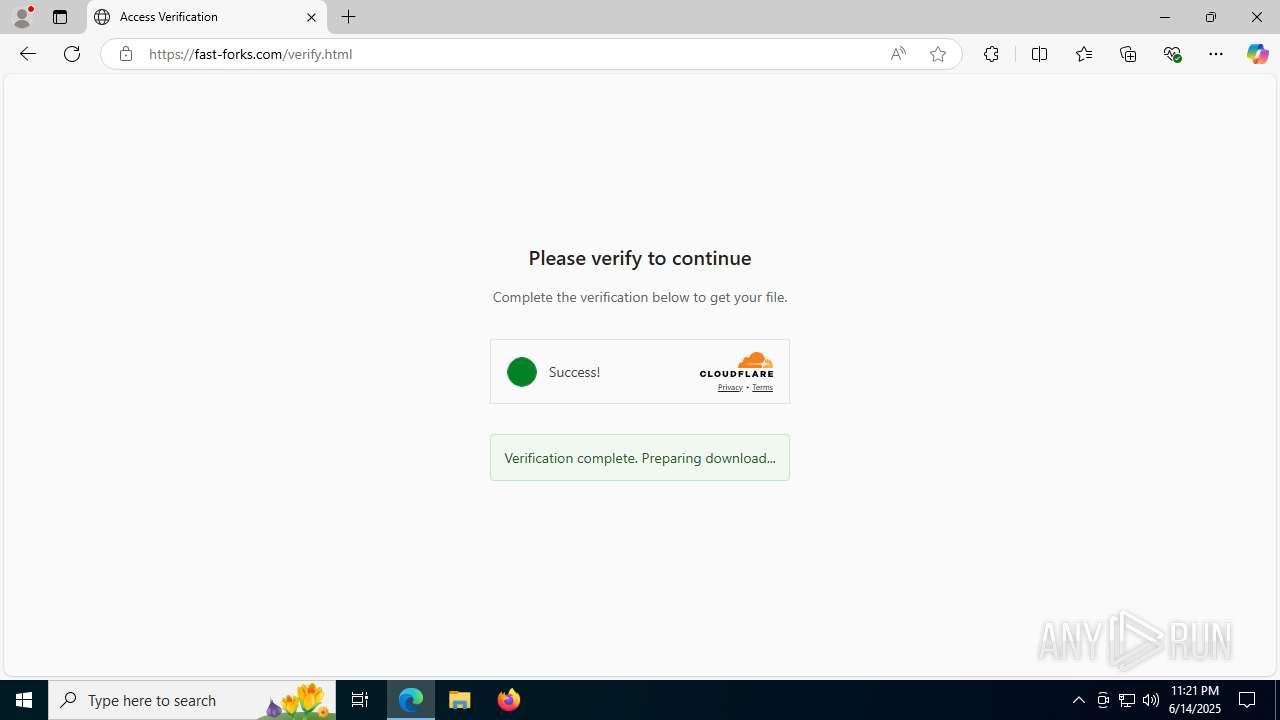
6772 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6772 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
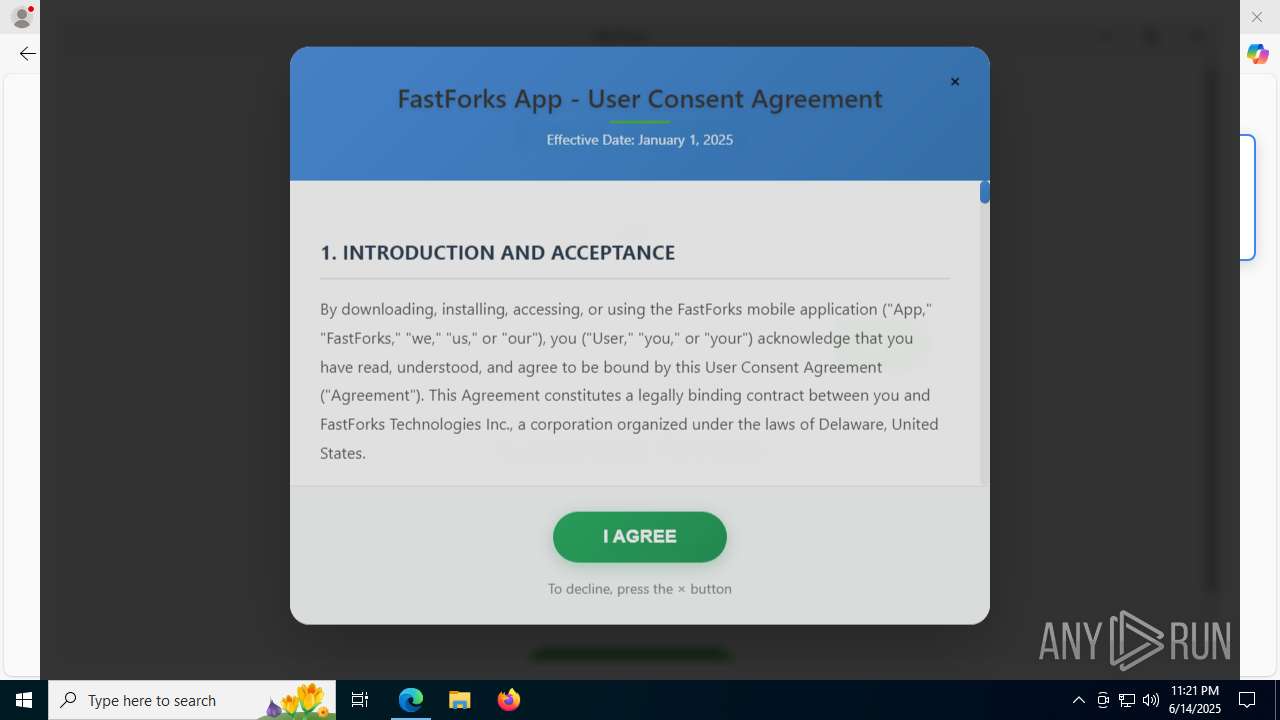
6772 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
6772 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |