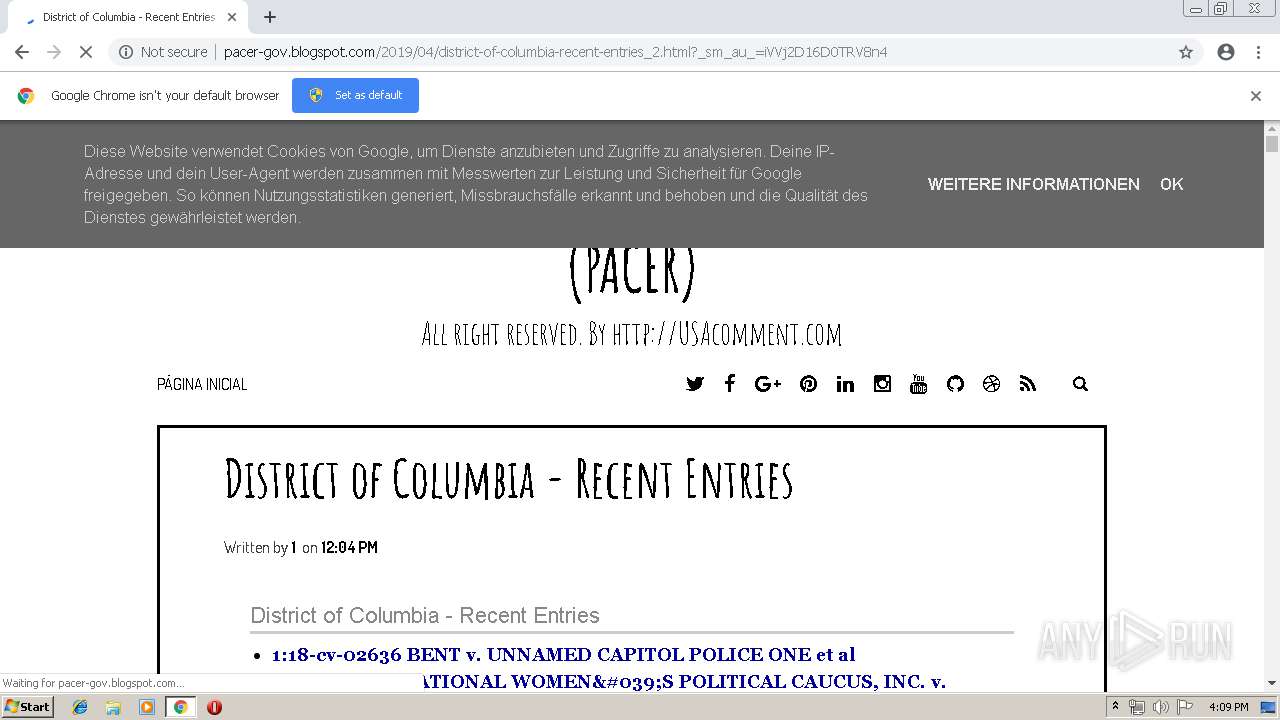
| URL: | http://pacer-gov.blogspot.com/2019/04/district-of-columbia-recent-entries_2.html?_sm_au_=iVVj2D16D0TRV8n4 |
| Full analysis: | https://app.any.run/tasks/44978441-03c3-419a-b0a6-eb0e3f347f69 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 15:09:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FE0015CEA23511B778F79CDF52EE1354 |
| SHA1: | 9D26D96B7A9C31E74C00835D57EDE3934B00812B |
| SHA256: | 06B8E999B151B382B25CB907EA4064915E48C5059749D6381198643F4A573A2F |
| SSDEEP: | 3:N1KOEGAOHXKMCHWXMNxMhMLzKA97qFeXLRn:COvAO3Kp2mKhMLX97qe1 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2516)
INFO
Application launched itself
- chrome.exe (PID: 2516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
15
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,5059443428091262702,2540024473480929749,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5122864448988055026 --mojo-platform-channel-handle=4080 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,5059443428091262702,2540024473480929749,131072 --enable-features=PasswordImport --service-pipe-token=15442039142464672994 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15442039142464672994 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1956 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fae0f18,0x6fae0f28,0x6fae0f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,5059443428091262702,2540024473480929749,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14978166986293661846 --mojo-platform-channel-handle=3936 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,5059443428091262702,2540024473480929749,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4001971168394082640 --mojo-platform-channel-handle=4136 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,5059443428091262702,2540024473480929749,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13406303070824521295 --mojo-platform-channel-handle=3676 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,5059443428091262702,2540024473480929749,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17081062767553694029 --mojo-platform-channel-handle=4120 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://pacer-gov.blogspot.com/2019/04/district-of-columbia-recent-entries_2.html?_sm_au_=iVVj2D16D0TRV8n4 | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,5059443428091262702,2540024473480929749,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10220178820563939720 --mojo-platform-channel-handle=4052 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,5059443428091262702,2540024473480929749,131072 --enable-features=PasswordImport --service-pipe-token=10570409212713995402 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10570409212713995402 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2000 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
530
Read events
461
Write events
65
Delete events
4
Modification events
| (PID) Process: | (3360) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2516-13200505768660125 |
Value: 259 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2516-13200505768660125 |
Value: 259 | |||
Executable files
0
Suspicious files
32
Text files
120
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\de7873dd-f626-4b1c-892e-5bb0b52e0726.tmp | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
34
DNS requests
39
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2516 | chrome.exe | GET | 301 | 100.25.91.149:80 | http://smarturl.it/304567 | US | — | — | whitelisted |
2516 | chrome.exe | GET | 200 | 172.217.22.1:80 | http://pacer-gov.blogspot.com/2019/04/district-of-columbia-recent-entries_2.html?_sm_au_=iVVj2D16D0TRV8n4 | US | html | 76.6 Kb | whitelisted |
2516 | chrome.exe | GET | 200 | 172.217.22.1:80 | http://pacer-gov.blogspot.com/feeds/posts/summary?alt=json-in-script&orderby=updated&start-index=3393&max-results=5&callback=showRelatedPost | US | text | 1.48 Kb | whitelisted |
2516 | chrome.exe | GET | 200 | 172.217.22.1:80 | http://pacer-gov.blogspot.com/feeds/posts/summary?alt=json-in-script&orderby=updated&max-results=0&callback=randomRelatedIndex | US | text | 776 b | whitelisted |
2516 | chrome.exe | GET | 200 | 109.236.93.206:80 | http://cdncash.net/optout/get?jsonp=__twb_cb_57214894&key=13fdb1e5ae9a9b3a61&t=1556032174385 | NL | text | 143 b | malicious |
2516 | chrome.exe | GET | 200 | 94.31.29.128:80 | http://cdn.popcash.net/pop.js | GB | text | 27.7 Kb | whitelisted |
2516 | chrome.exe | GET | 200 | 109.236.93.206:80 | http://cdncash.net/addons/lnkr5.min.js | NL | text | 5.50 Kb | malicious |
2516 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 510 b | whitelisted |
2516 | chrome.exe | GET | 200 | 216.58.205.225:80 | http://2.bp.blogspot.com/-7AENugBR218/V9L-aGlAvOI/AAAAAAAAA_g/crgZxY3QSGM/s000/no_image.jpg | US | image | 9.15 Kb | whitelisted |
2516 | chrome.exe | GET | 200 | 87.245.198.13:80 | http://r2---sn-gxuog0-axqe.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=91.221.66.140&mm=28&mn=sn-gxuog0-axqe&ms=nvh&mt=1556031801&mv=u&pl=23&shardbypass=yes | RU | crx | 842 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2516 | chrome.exe | 207.241.227.110:443 | ia601500.us.archive.org | Internet Archive | US | suspicious |
2516 | chrome.exe | 100.25.91.149:80 | smarturl.it | — | US | unknown |
2516 | chrome.exe | 207.241.227.116:443 | ia601506.us.archive.org | Internet Archive | US | unknown |
2516 | chrome.exe | 172.217.23.138:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2516 | chrome.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2516 | chrome.exe | 207.241.227.124:443 | ia601404.us.archive.org | Internet Archive | US | suspicious |
2516 | chrome.exe | 207.241.224.2:443 | archive.org | Internet Archive | US | malicious |
2516 | chrome.exe | 172.217.16.137:443 | www.blogger.com | Google Inc. | US | unknown |
2516 | chrome.exe | 207.241.230.84:443 | ia800804.us.archive.org | Internet Archive | US | unknown |
2516 | chrome.exe | 94.31.29.128:80 | cdn.popcash.net | netDNA | GB | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pacer-gov.blogspot.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.blogger.com |
| shared |
fonts.googleapis.com |
| whitelisted |
ia601500.us.archive.org |
| suspicious |
maxcdn.bootstrapcdn.com |
| whitelisted |
ia601506.us.archive.org |
| unknown |
smarturl.it |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2516 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |