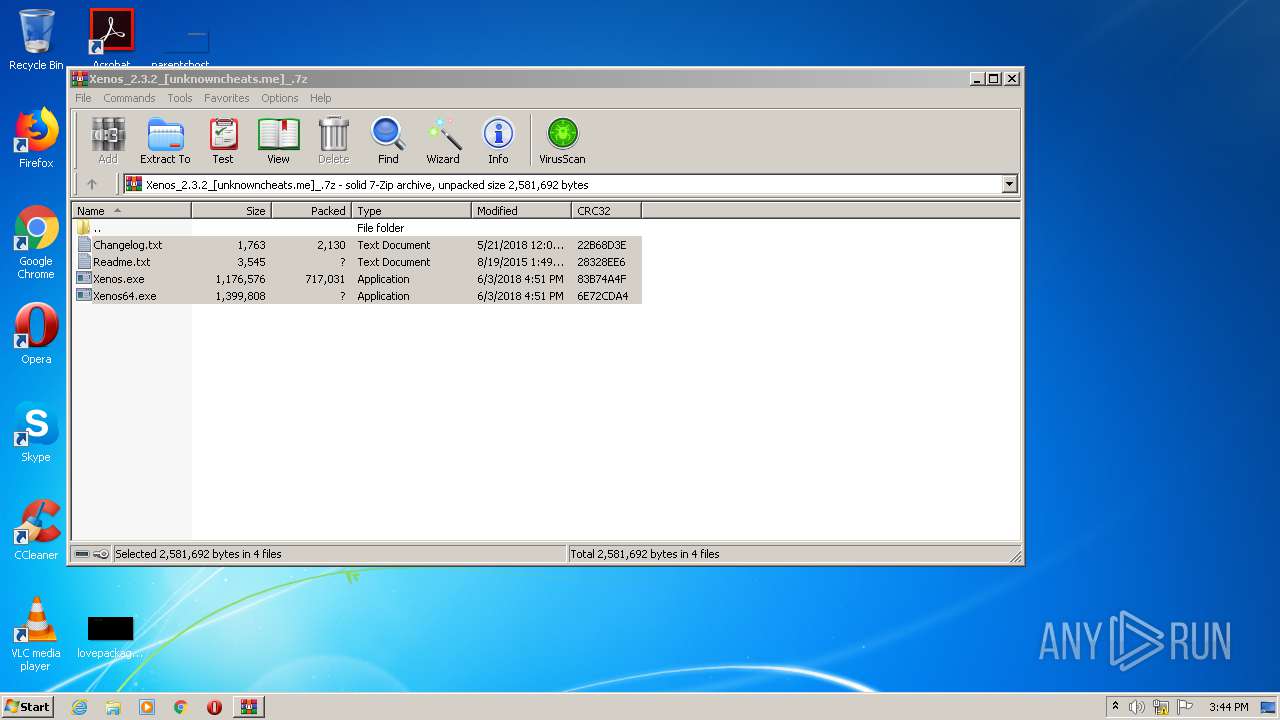
| File name: | Xenos_2.3.2_[unknowncheats.me]_.7z |
| Full analysis: | https://app.any.run/tasks/0d66b8e1-724f-4431-bb02-ed54a58fd5e7 |
| Verdict: | Suspicious activity |
| Analysis date: | October 05, 2020, 14:43:33 |
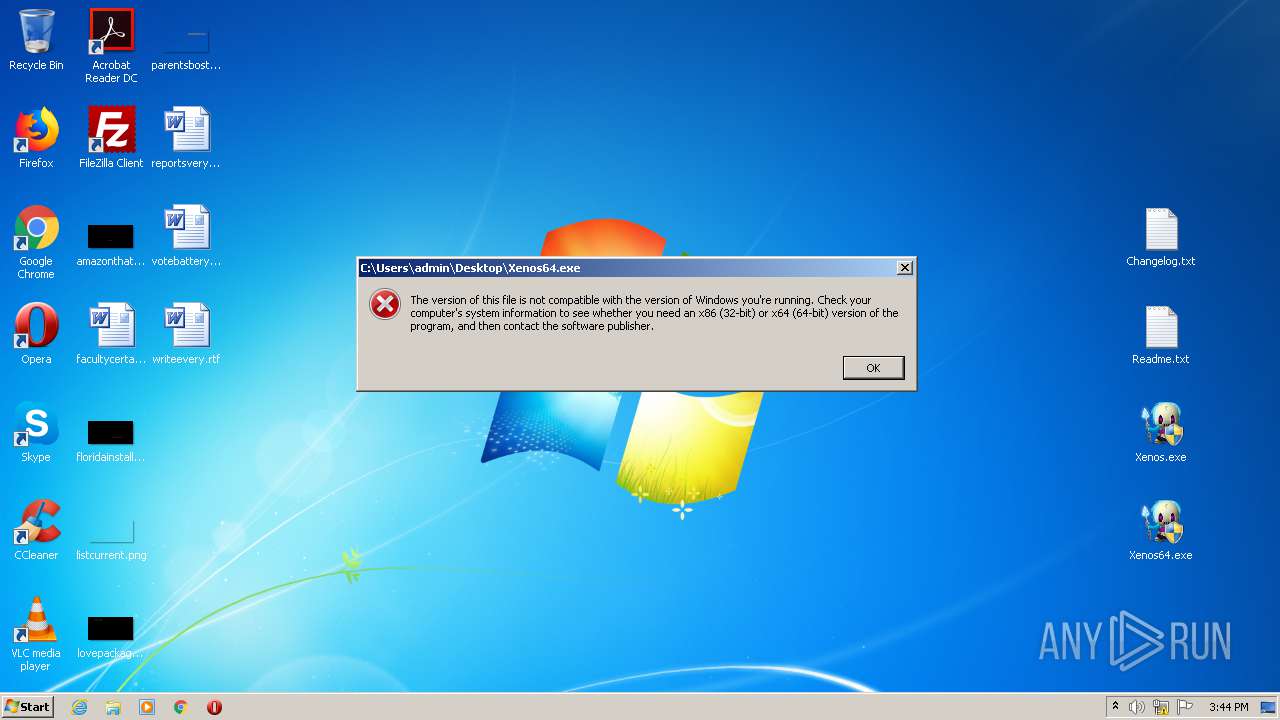
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
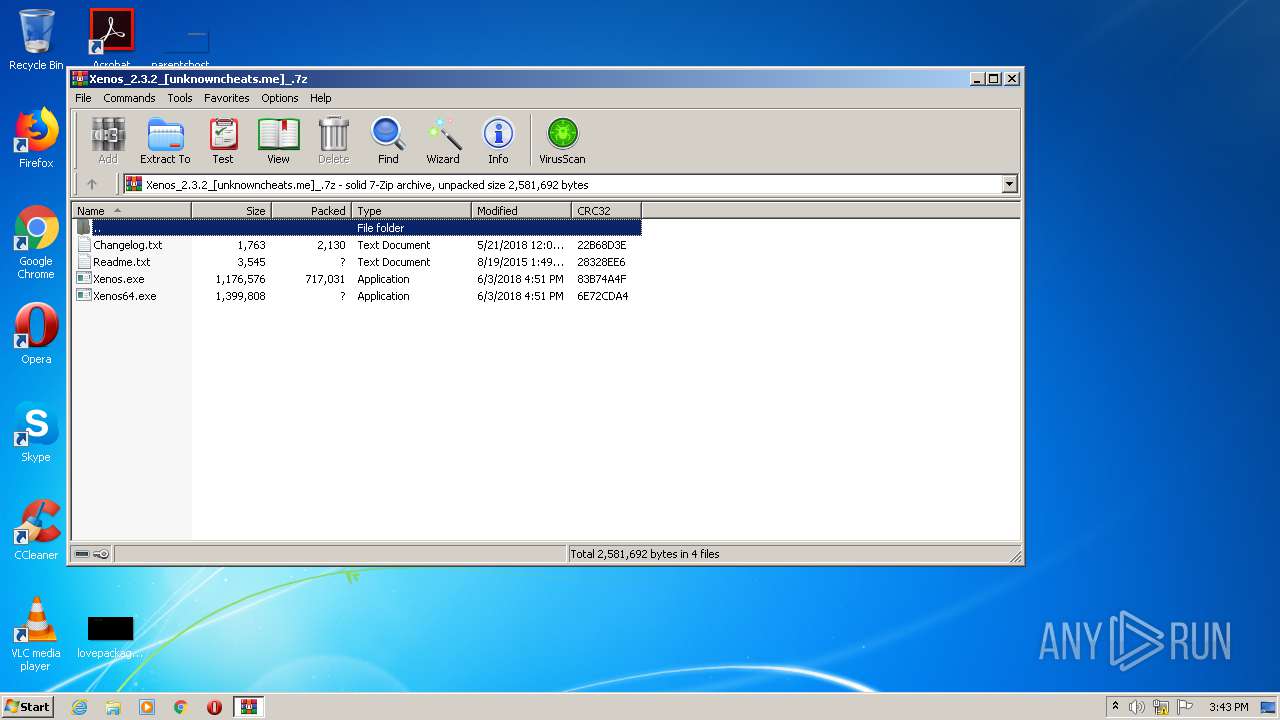
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | D435194B6BB80B407E48573E2ECE9094 |
| SHA1: | 7C7416E2857C1D4F8823CA0A18AA2449FB34E1A1 |
| SHA256: | 06B12C6D7ECE840A3B805E7A498A4AF695F793A053A63B887F6C7395B3138BAD |
| SSDEEP: | 12288:hcJOckMtEdbHb8VOTmND+UBRWe5j8w0t/3LVsEolETti+3qxsmLXbI5h5SQr/k:hcJOckMtIsQTCvWe5j8fLVsFlAiBPTUc |
MALICIOUS
Application was dropped or rewritten from another process
- Xenos.exe (PID: 3140)
- Xenos.exe (PID: 1456)
SUSPICIOUS
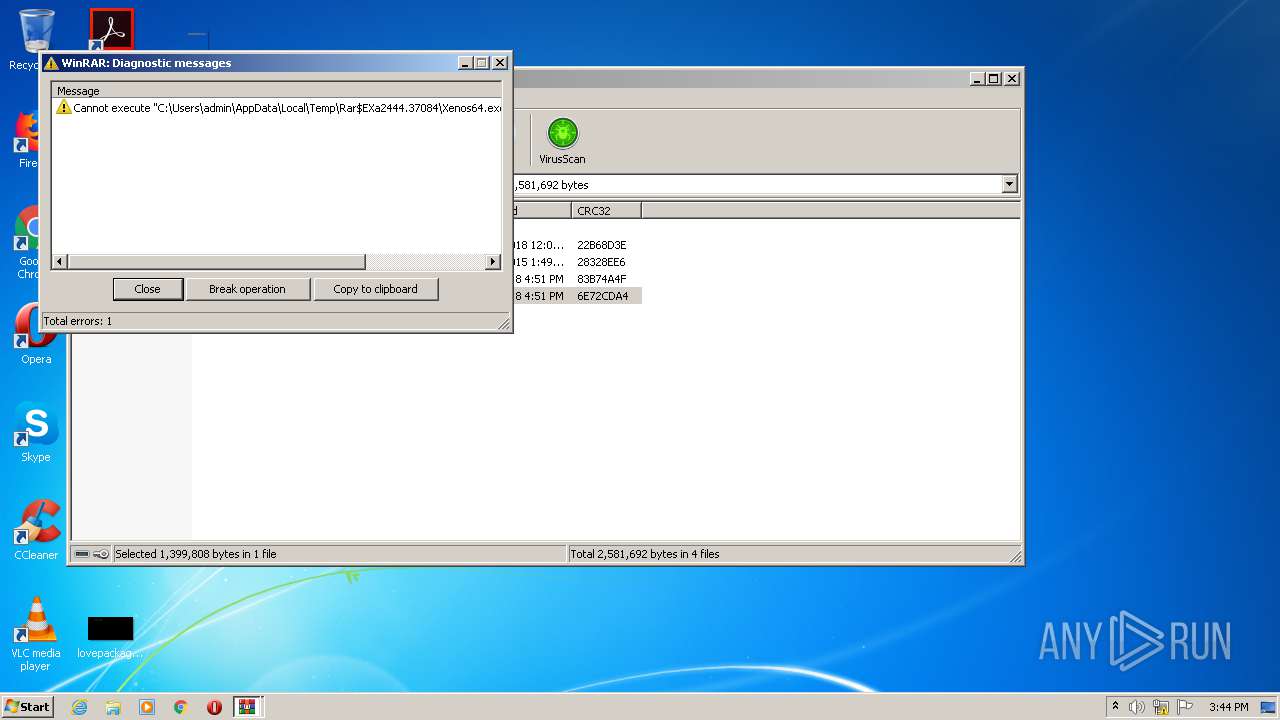
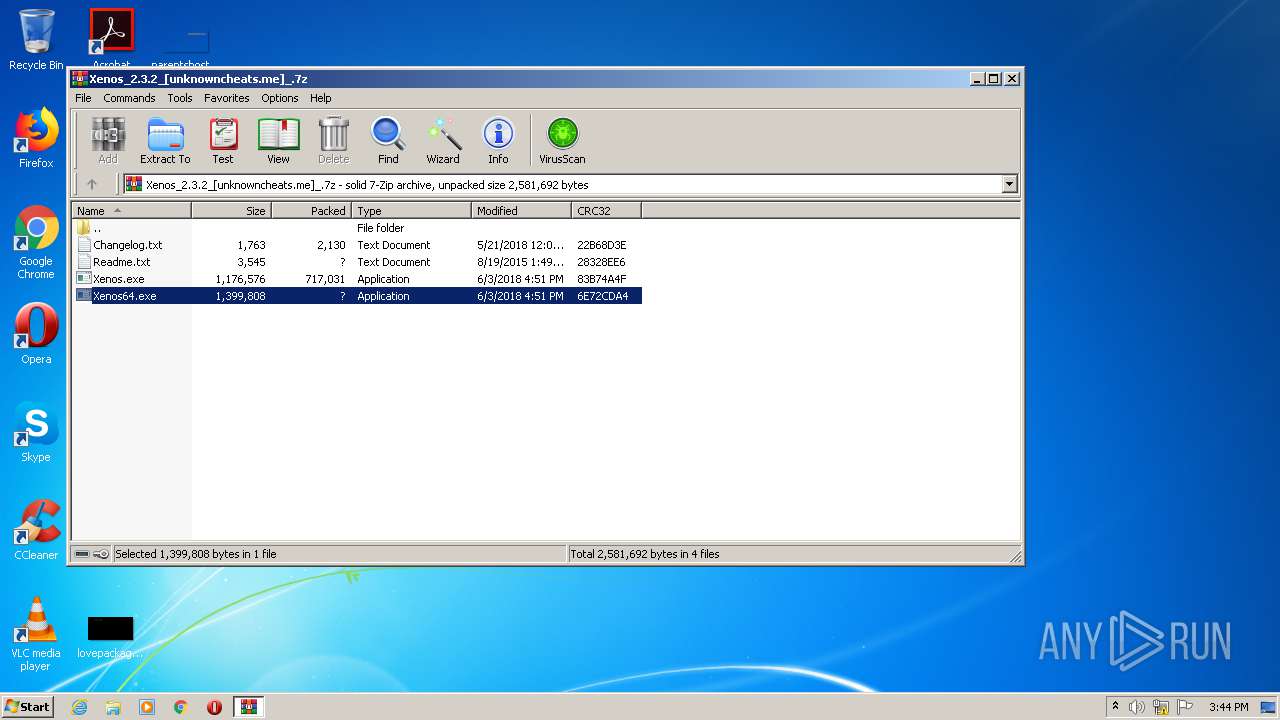
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2444)
INFO
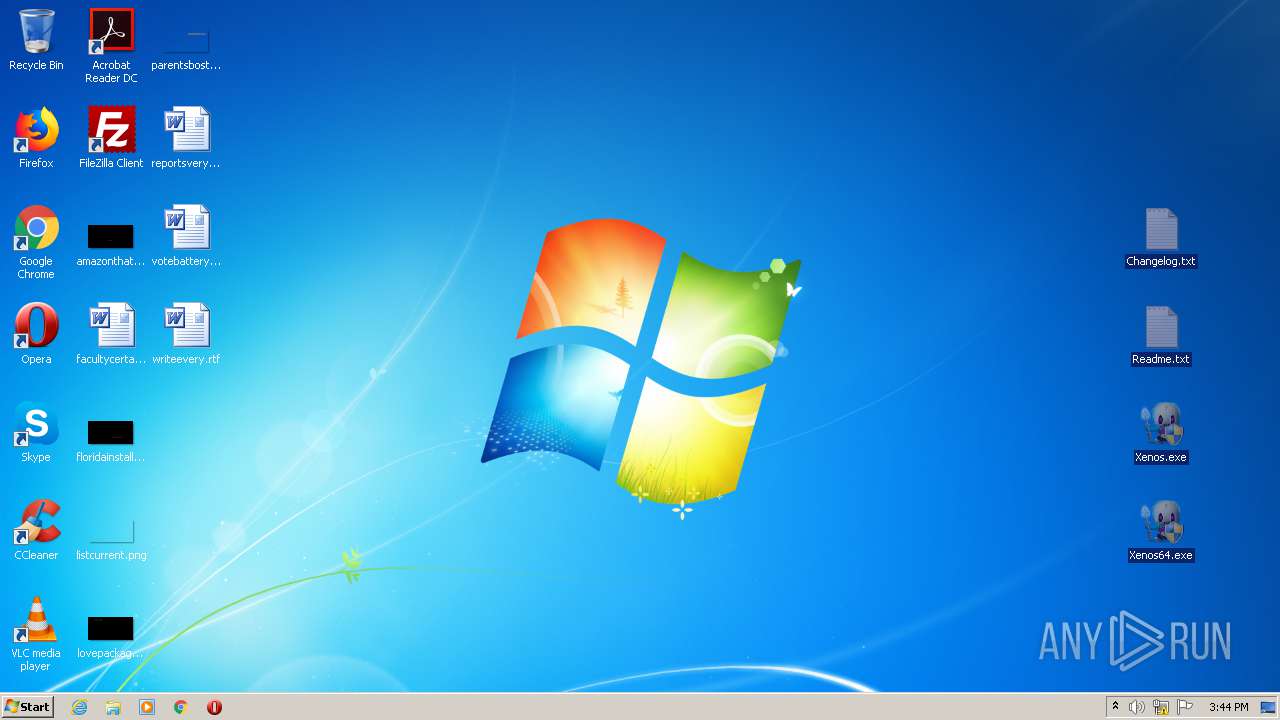
Manual execution by user
- Xenos.exe (PID: 3140)
- Xenos.exe (PID: 1456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
43
Monitored processes
3
Malicious processes
1
Suspicious processes
0
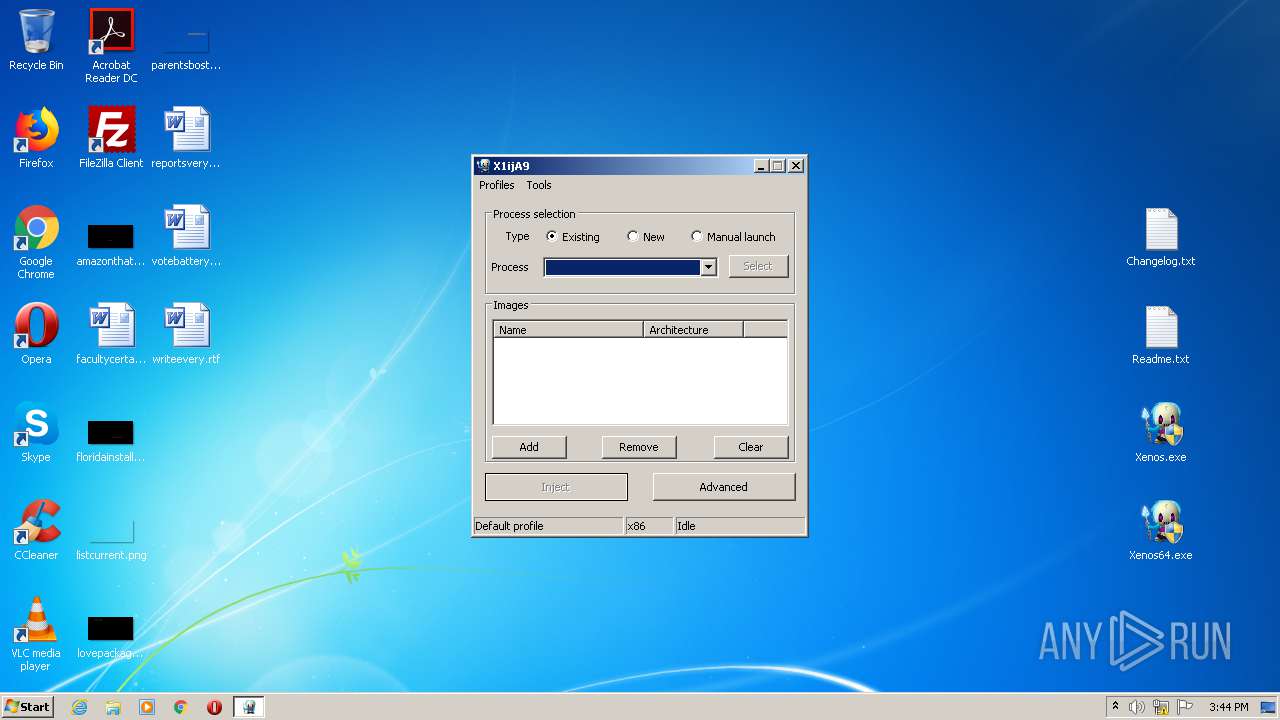
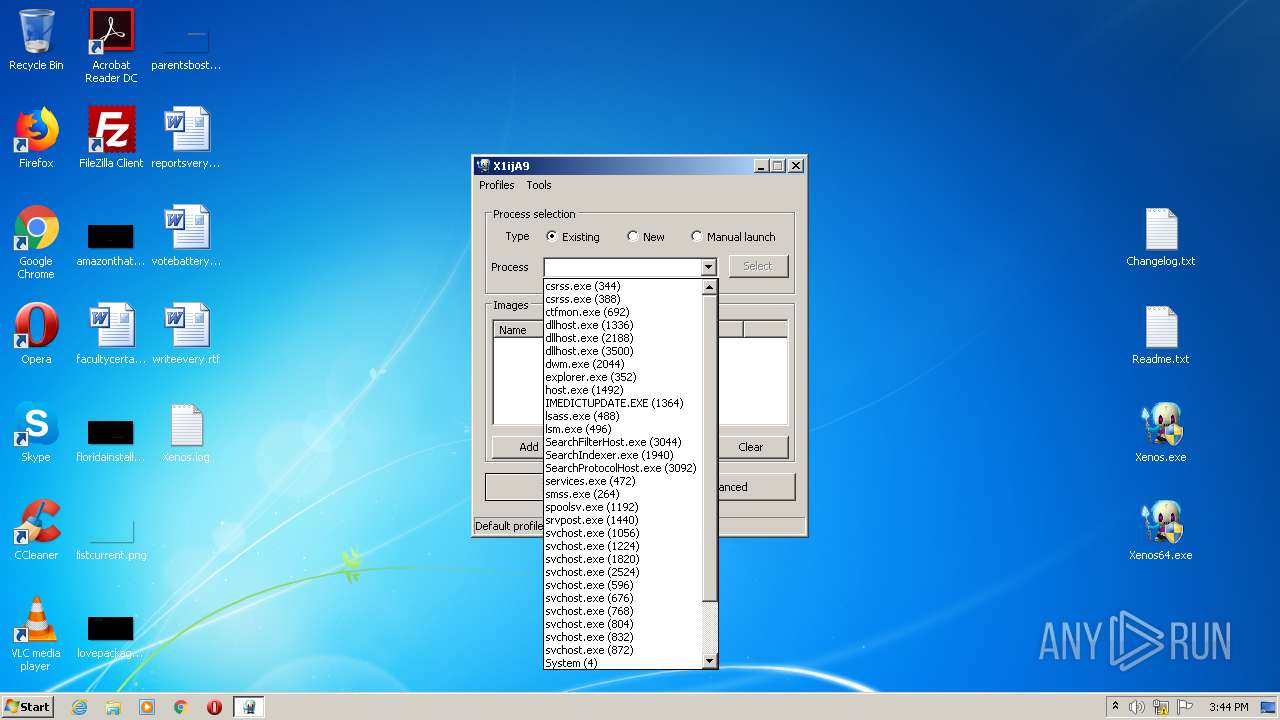
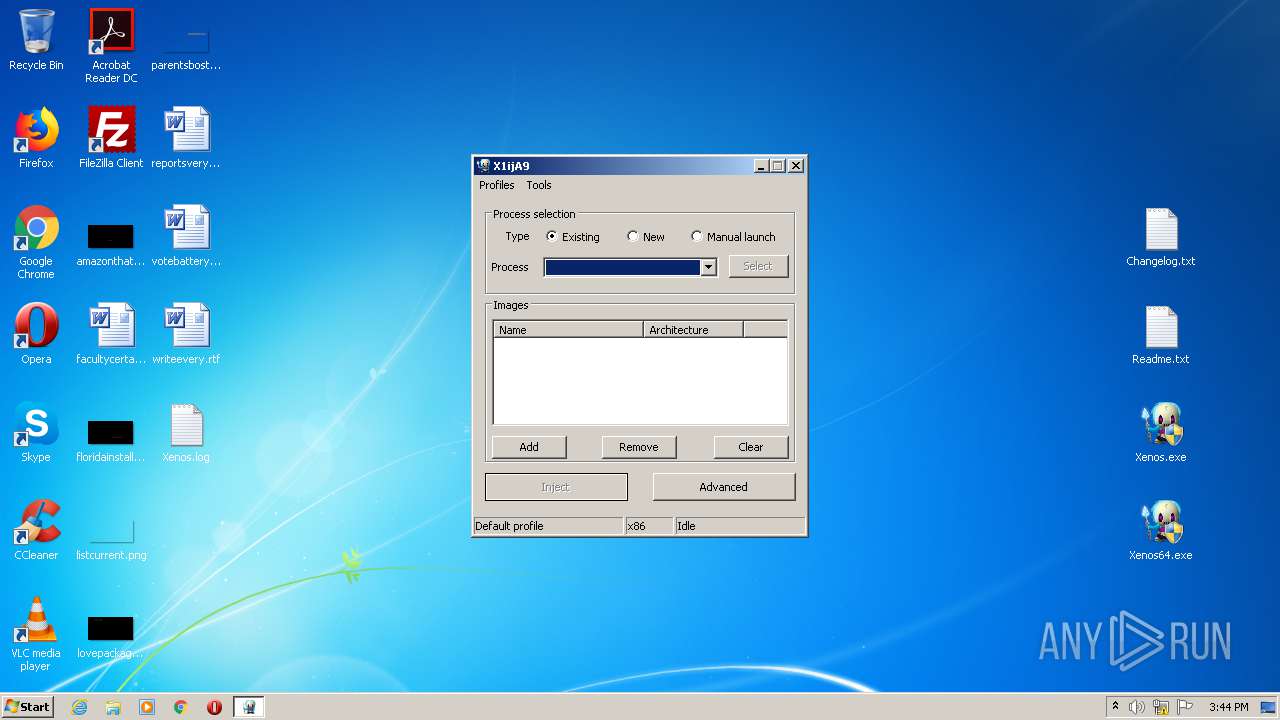
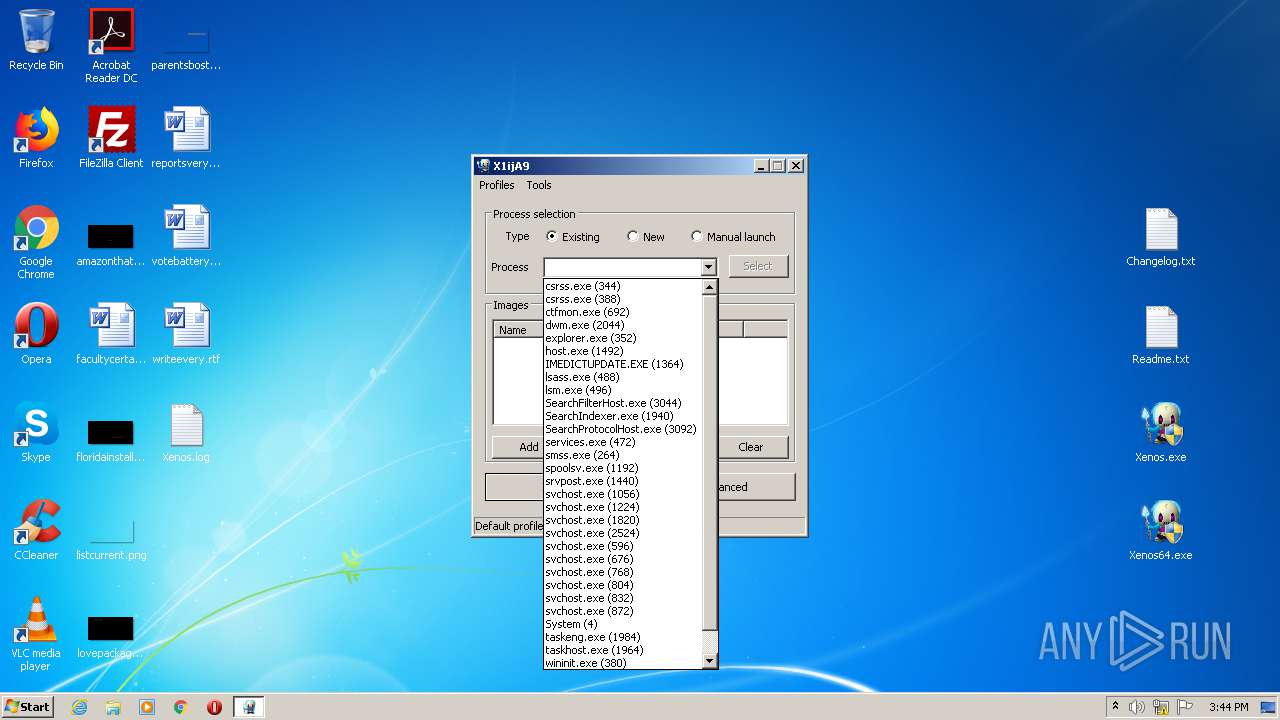
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1456 | "C:\Users\admin\Desktop\Xenos.exe" | C:\Users\admin\Desktop\Xenos.exe | explorer.exe | ||||||||||||
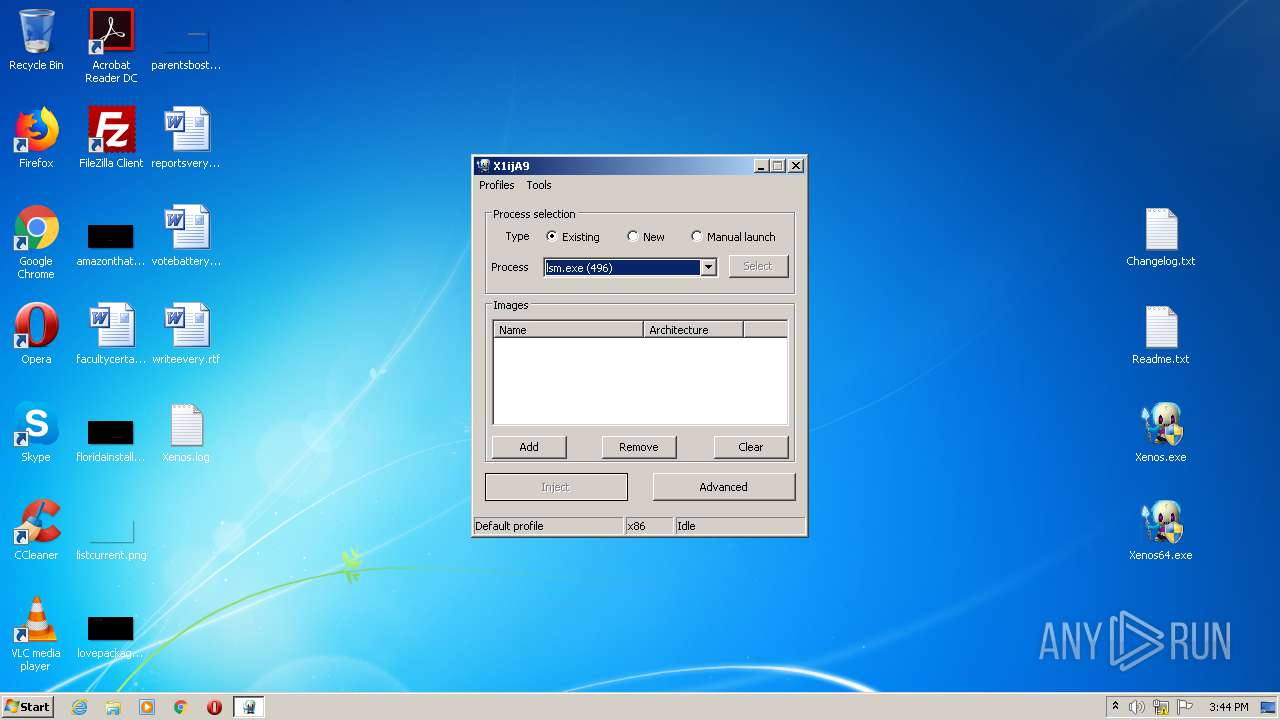
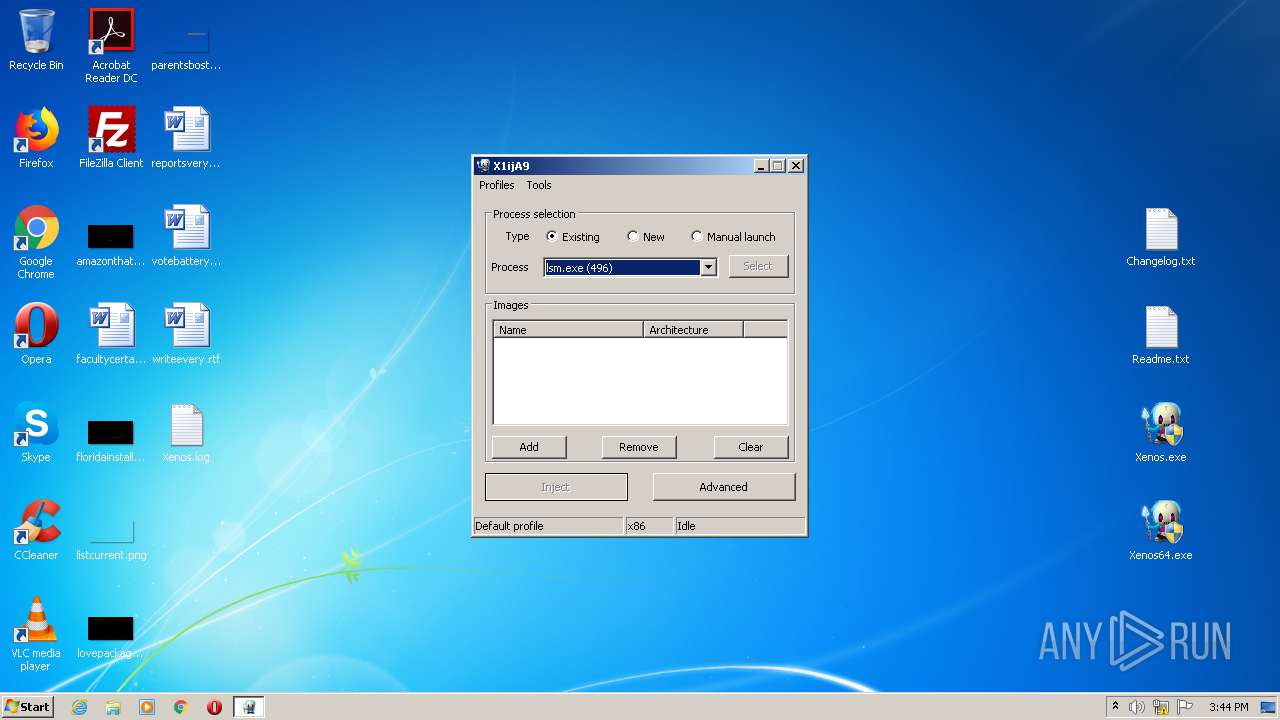
User: admin Integrity Level: HIGH Description: PE injector Exit code: 1 Version: 2.3.2.0 Modules
| |||||||||||||||
| 2444 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Xenos_2.3.2_[unknowncheats.me]_.7z" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3140 | "C:\Users\admin\Desktop\Xenos.exe" | C:\Users\admin\Desktop\Xenos.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PE injector Exit code: 3221226540 Version: 2.3.2.0 Modules
| |||||||||||||||
Total events
455
Read events
423
Write events
32
Delete events
0
Modification events
| (PID) Process: | (2444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2444) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Xenos_2.3.2_[unknowncheats.me]_.7z | |||
| (PID) Process: | (2444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2444) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
| (PID) Process: | (2444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
0
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2444 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2444.37581\Xenos.exe | — | |
MD5:— | SHA256:— | |||
| 2444 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2444.37581\Xenos64.exe | — | |
MD5:— | SHA256:— | |||
| 1456 | Xenos.exe | C:\Users\admin\Desktop\Xenos.log | text | |
MD5:— | SHA256:— | |||
| 2444 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2444.37581\Changelog.txt | text | |
MD5:EDE4BF15A21F34E4E80CEF77903D17D9 | SHA256:6F0A8D0B2EED24CADB3FE998782516179DE8A51FDDB3545BD6E6F34CB87EF3D6 | |||
| 2444 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2444.37084\Changelog.txt | text | |
MD5:EDE4BF15A21F34E4E80CEF77903D17D9 | SHA256:6F0A8D0B2EED24CADB3FE998782516179DE8A51FDDB3545BD6E6F34CB87EF3D6 | |||
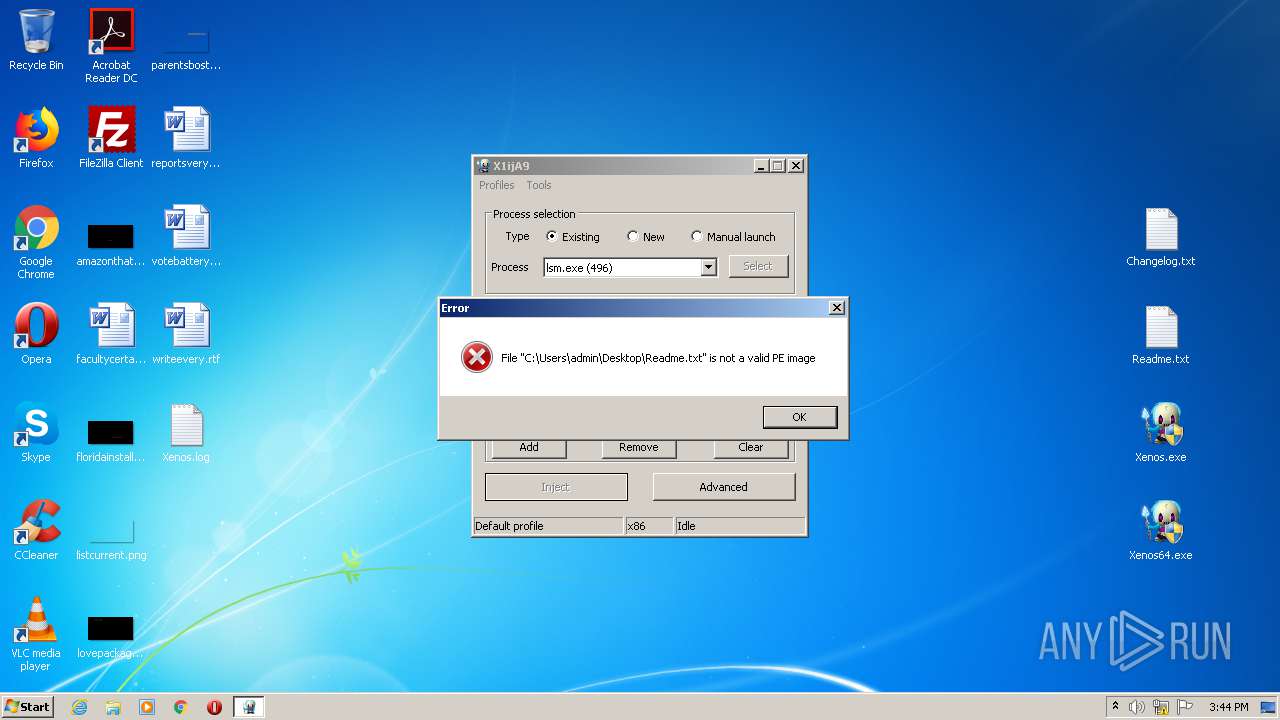
| 2444 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2444.37581\Readme.txt | text | |
MD5:9B159C1881EF3F331F132251D5D0DC87 | SHA256:9760B735A55147BA0B2C329C5ECFC22249B9F0378A6D4E793C171AC4F50246E7 | |||
| 2444 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2444.37084\Xenos64.exe | executable | |
MD5:6F0DD4150EFDDFC20B70401479964211 | SHA256:0E6D59FCDF8F143E23B076CC8380D6D23324839AE4F91793133B600E7EB76EB9 | |||
| 2444 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2444.37084\Readme.txt | text | |
MD5:9B159C1881EF3F331F132251D5D0DC87 | SHA256:9760B735A55147BA0B2C329C5ECFC22249B9F0378A6D4E793C171AC4F50246E7 | |||
| 2444 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2444.37084\Xenos.exe | executable | |
MD5:216C3EAE24901482BFD26CB9DCA1A833 | SHA256:8BDB3CE10DEE7A3249A186050D7F804BCA19859F292DDAD7AE8C5AFBB649A07B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report