| File name: | xp-MU.exe |
| Full analysis: | https://app.any.run/tasks/c0247dde-7089-4a30-806a-ae7f861bc9c6 |
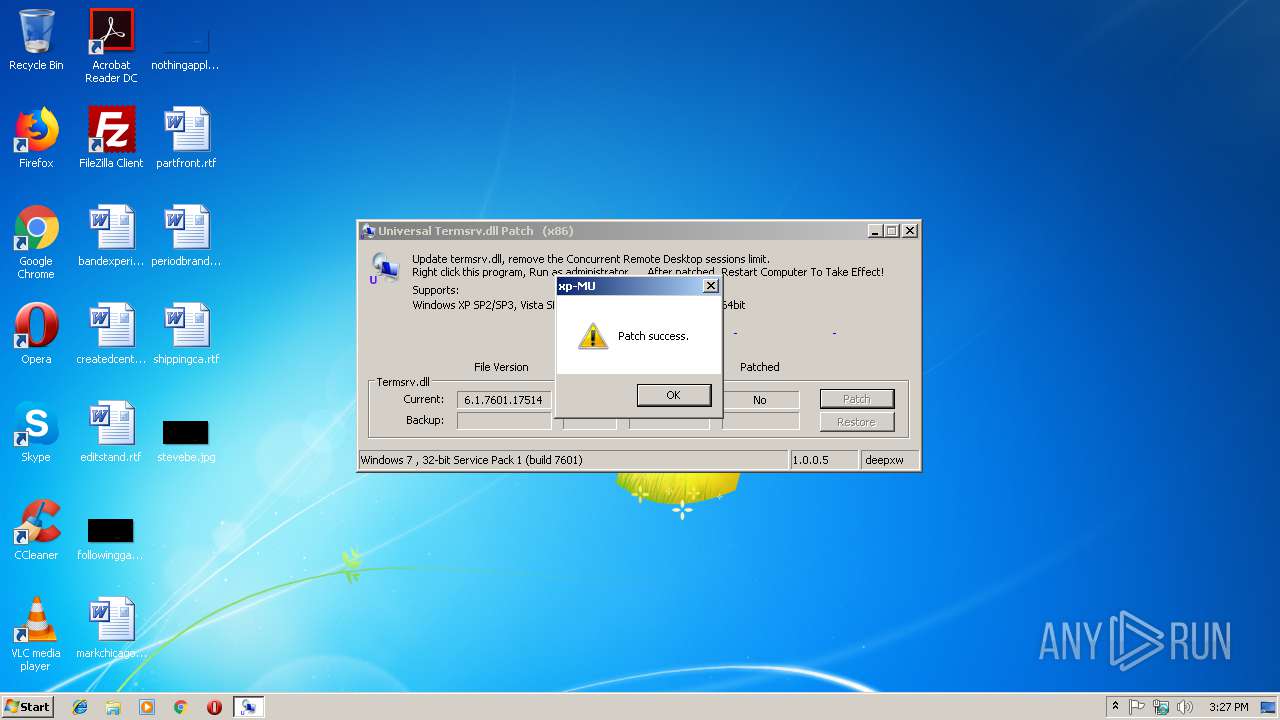
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2019, 15:27:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E4C5B750E3F0ACDA5F176FC9B20C75D6 |
| SHA1: | B734359379D76B8EE9847D67FD75DAF0B582C359 |
| SHA256: | 06A77E6299C0E38C5BFFDC5760B78D4E3FB5049D7849B50598BCCEF298AF2D8B |
| SSDEEP: | 768:jE85L0/e4mYouQY9ot+3qennVG6ci4glF7buCq1FpwEDhEXpZwoHCspvaEhuBWdE:wHNF7buCq1FpZeeMppvfcSI9A5Nv3++C |
MALICIOUS
Loads dropped or rewritten executable
- xp-MU.exe (PID: 3916)
SUSPICIOUS
Uses ICACLS.EXE to modify access control list
- xp-MU.exe (PID: 3916)
Executable content was dropped or overwritten
- xp-MU.exe (PID: 3916)
Creates files in the Windows directory
- xp-MU.exe (PID: 3916)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:04:16 20:45:27+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 35328 |
| InitializedDataSize: | 27136 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x80b7 |
| OSVersion: | 5.2 |
| ImageVersion: | 5.2 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.5 |
| ProductVersionNumber: | 1.0.0.5 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
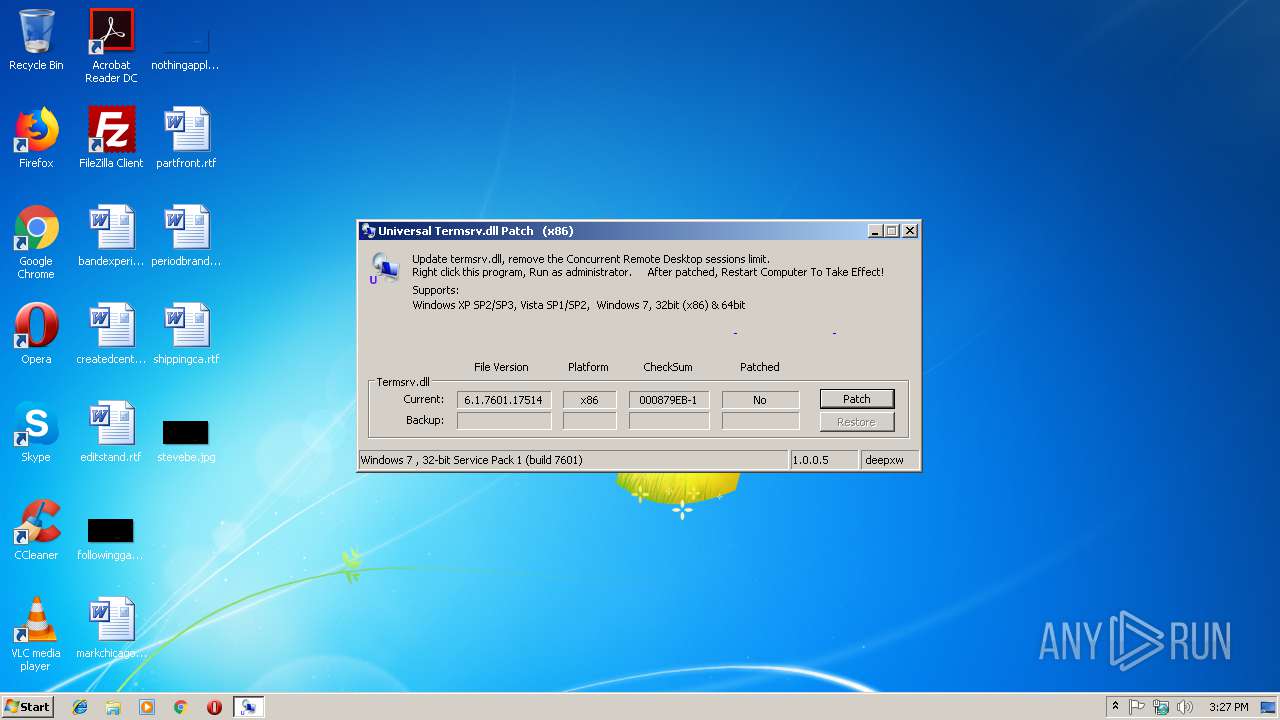
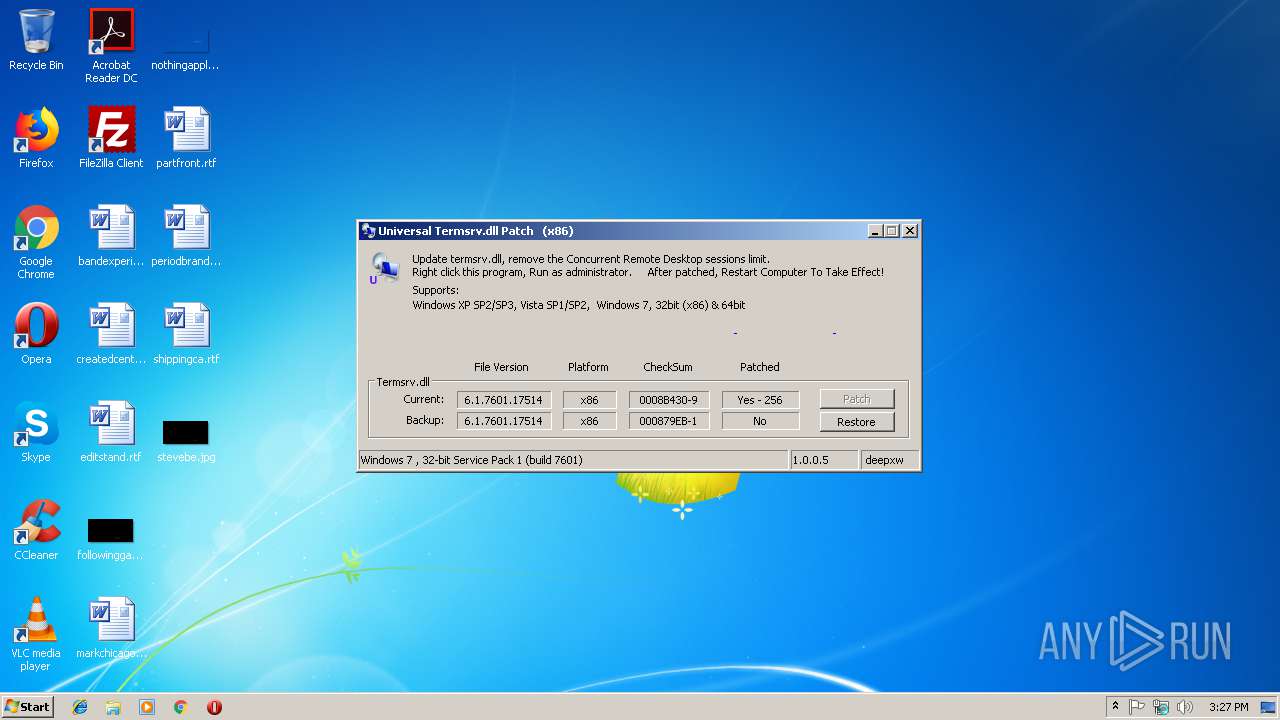
| Comments: | Crack termsrv.dll, remove the Concurrent Remote Desktop sessions limit. |
| CompanyName: | deepxw |
| FileDescription: | Universal termsrv.dll Patch |
| FileVersion: | 1.0.0.5 |
| InternalName: | UniversalTermsrvPatch.exe |
| LegalCopyright: | Copyright (C) 2008-2009. All rights reserved. |
| OriginalFileName: | UniversalTermsrvPatch.exe |
| ProductName: | Universal termsrv.dll Patch |
| ProductVersion: | 1.0.0.5 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Apr-2009 18:45:27 |
| Detected languages: |
|
| Debug artifacts: |
|
| Comments: | Crack termsrv.dll, remove the Concurrent Remote Desktop sessions limit. |
| CompanyName: | deepxw |
| FileDescription: | Universal termsrv.dll Patch |
| FileVersion: | 1.0.0.5 |
| InternalName: | UniversalTermsrvPatch.exe |
| LegalCopyright: | Copyright (C) 2008-2009. All rights reserved. |
| OriginalFilename: | UniversalTermsrvPatch.exe |
| ProductName: | Universal termsrv.dll Patch |
| ProductVersion: | 1.0.0.5 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 16-Apr-2009 18:45:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000089C2 | 0x00008A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.93817 |
.data | 0x0000A000 | 0x000009F4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.05735 |
.rsrc | 0x0000B000 | 0x00005E30 | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.80485 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00067 | 842 | UNKNOWN | Chinese - PRC | RT_MANIFEST |
2 | 5.01493 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 5.33619 | 1128 | UNKNOWN | English - United States | RT_ICON |
13 | 5.78714 | 384 | UNKNOWN | Chinese - PRC | RT_STRING |
14 | 5.94198 | 276 | UNKNOWN | Chinese - PRC | RT_STRING |
15 | 4.82573 | 158 | UNKNOWN | Chinese - PRC | RT_STRING |
100 | 3.32826 | 884 | UNKNOWN | UNKNOWN | RT_DIALOG |
102 | 3.49729 | 1452 | UNKNOWN | UNKNOWN | RT_DIALOG |
103 | 3.17471 | 364 | UNKNOWN | UNKNOWN | RT_DIALOG |
128 | 2.45849 | 48 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
MFC42u.dll |
NETAPI32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
VERSION.dll |
Total processes
43
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2056 | "C:\Windows\System32\icacls.exe" C:\Windows\System32\termsrv.dll /grant *S-1-1-0:(F) | C:\Windows\System32\icacls.exe | — | xp-MU.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2716 | "C:\Windows\System32\icacls.exe" C:\Windows\System32\termsrv.dll /grant %username%:F | C:\Windows\System32\icacls.exe | — | xp-MU.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 1332 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3068 | "C:\Users\admin\AppData\Local\Temp\xp-MU.exe" | C:\Users\admin\AppData\Local\Temp\xp-MU.exe | — | explorer.exe | |||||||||||
User: admin Company: deepxw Integrity Level: MEDIUM Description: Universal termsrv.dll Patch Exit code: 3221226540 Version: 1.0.0.5 Modules
| |||||||||||||||
| 3656 | "C:\Windows\System32\takeown.exe" /f C:\Windows\System32\termsrv.dll | C:\Windows\System32\takeown.exe | — | xp-MU.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3916 | "C:\Users\admin\AppData\Local\Temp\xp-MU.exe" | C:\Users\admin\AppData\Local\Temp\xp-MU.exe | explorer.exe | ||||||||||||
User: admin Company: deepxw Integrity Level: HIGH Description: Universal termsrv.dll Patch Exit code: 1073807364 Version: 1.0.0.5 Modules
| |||||||||||||||
Total events
76
Read events
61
Write events
15
Delete events
0
Modification events
| (PID) Process: | (3916) xp-MU.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3916) xp-MU.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3916) xp-MU.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
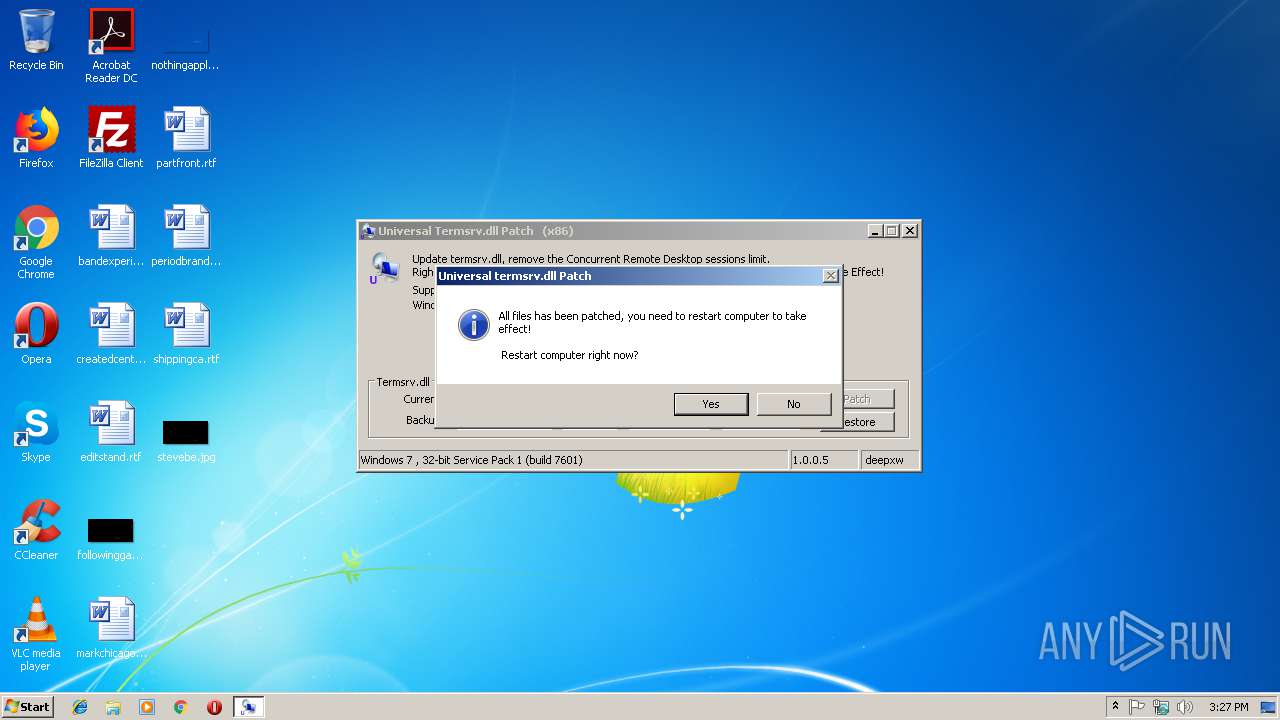
| (PID) Process: | (3916) xp-MU.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | PendingFileRenameOperations |
Value: \??\C:\_@255C.tmp | |||
Executable files
4
Suspicious files
4
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3916 | xp-MU.exe | C:\Users\admin\AppData\Local\Temp\CabD0F.tmp | — | |
MD5:— | SHA256:— | |||
| 3916 | xp-MU.exe | C:\Users\admin\AppData\Local\Temp\TarD10.tmp | — | |
MD5:— | SHA256:— | |||
| 3916 | xp-MU.exe | C:\Windows\System32\termsrv.dll.tmp | — | |
MD5:— | SHA256:— | |||
| 3916 | xp-MU.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B8CC409ACDBF2A2FE04C56F2875B1FD6 | binary | |
MD5:— | SHA256:— | |||
| 3916 | xp-MU.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F90F18257CBB4D84216AC1E1F3BB2C76 | der | |
MD5:— | SHA256:— | |||
| 3916 | xp-MU.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F90F18257CBB4D84216AC1E1F3BB2C76 | binary | |
MD5:— | SHA256:— | |||
| 3916 | xp-MU.exe | C:\Windows\System32\termsrv.dll.backup | executable | |
MD5:— | SHA256:— | |||
| 3916 | xp-MU.exe | C:\_@255C.tmp | executable | |
MD5:— | SHA256:— | |||
| 3916 | xp-MU.exe | C:\Windows\System32\termsrv.dll | executable | |
MD5:— | SHA256:— | |||
| 3916 | xp-MU.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B8CC409ACDBF2A2FE04C56F2875B1FD6 | der | |
MD5:5E275DB761AA5A23AC651AF8F6C4A000 | SHA256:3B9B2F75B724FE5354D24A0EF729B8A2AAA8A9313166EAFB1F73B07CF1A745EF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3916 | xp-MU.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/WinPCA.crl | unknown | der | 530 b | whitelisted |
3916 | xp-MU.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | der | 550 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3916 | xp-MU.exe | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
3916 | xp-MU.exe | 2.16.186.120:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |