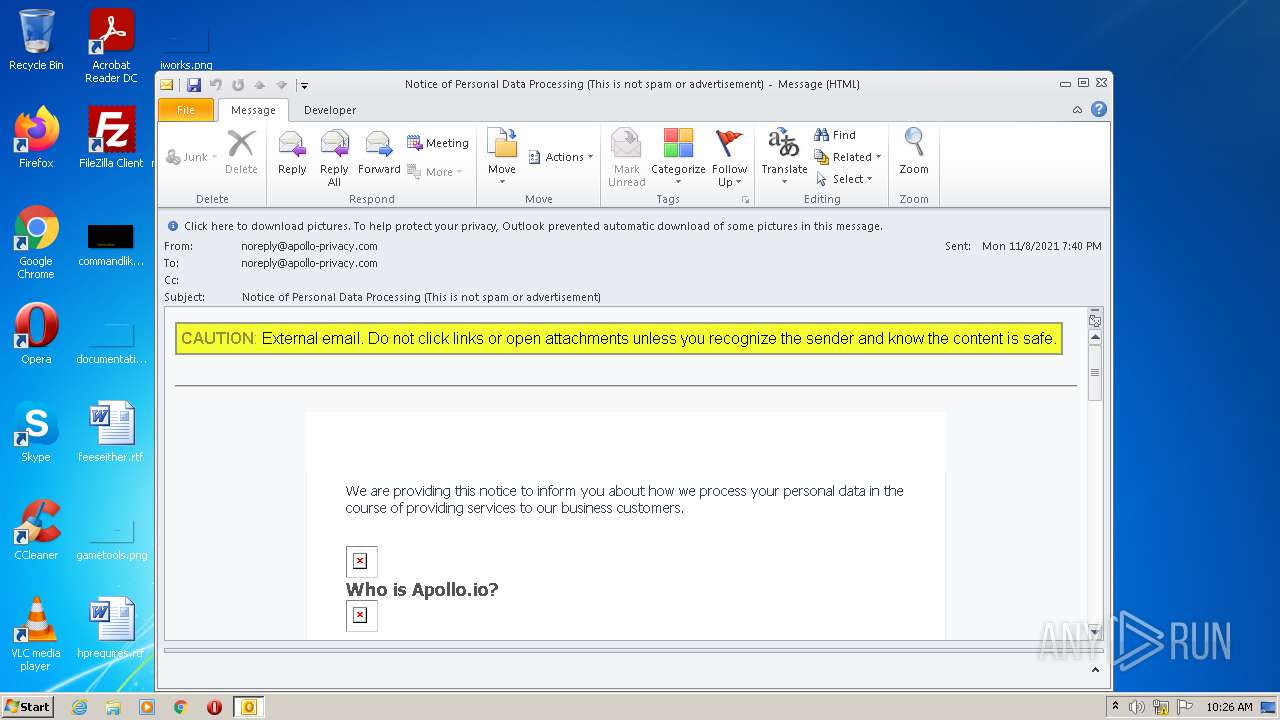
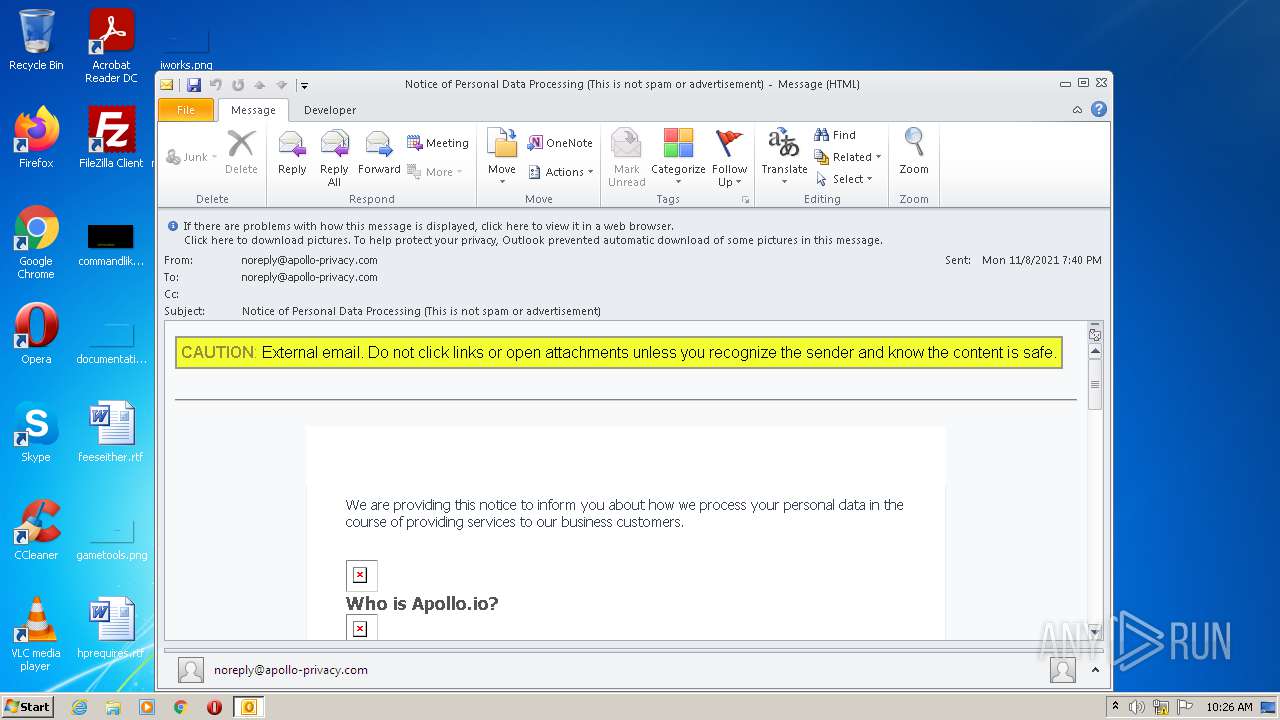
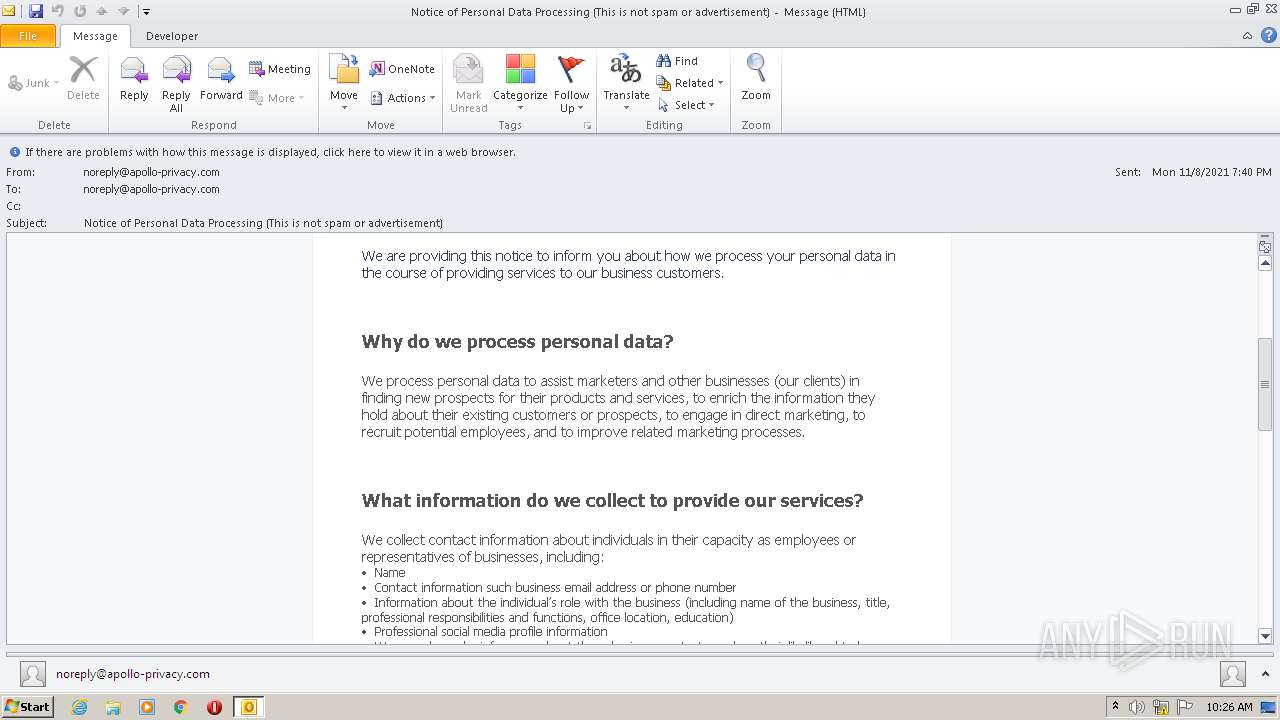
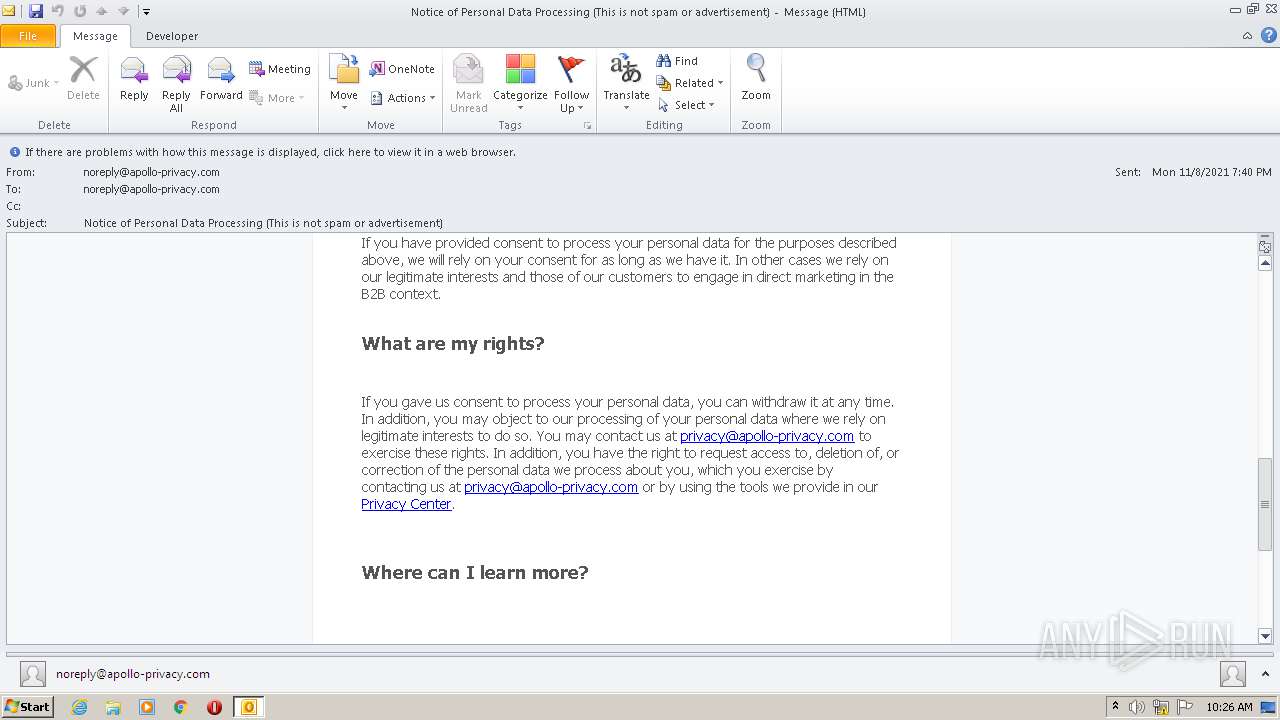
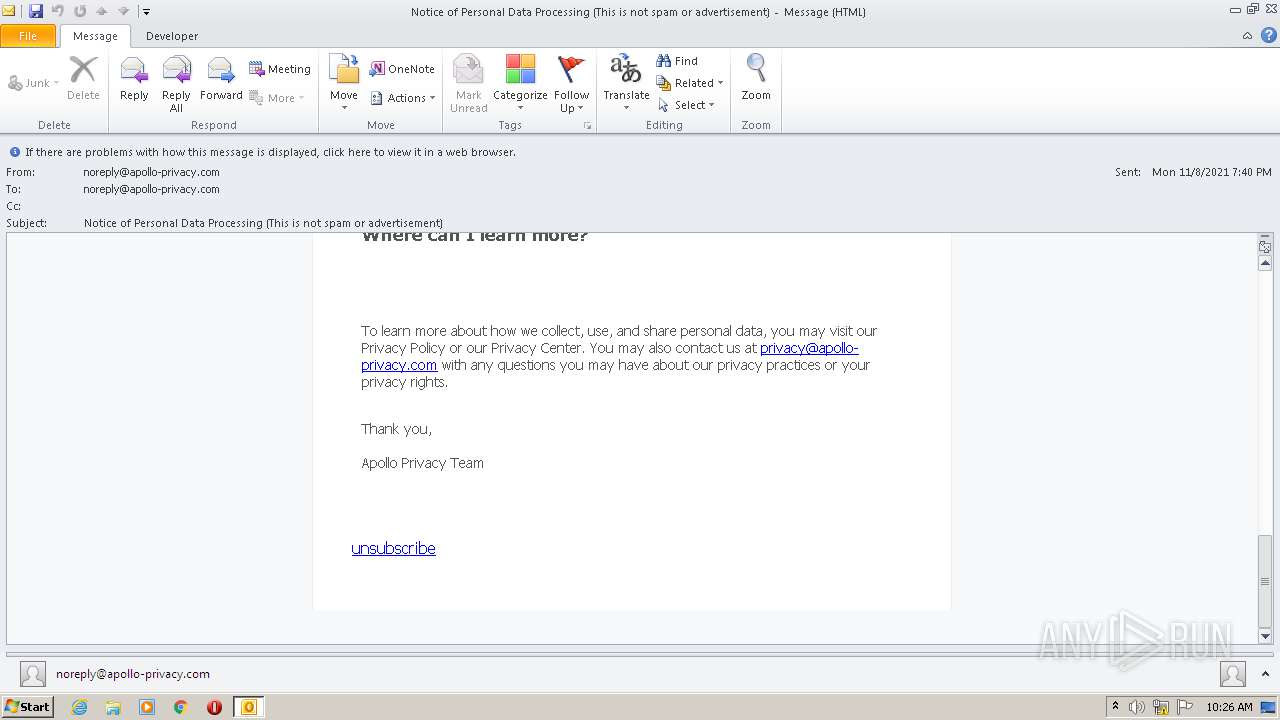
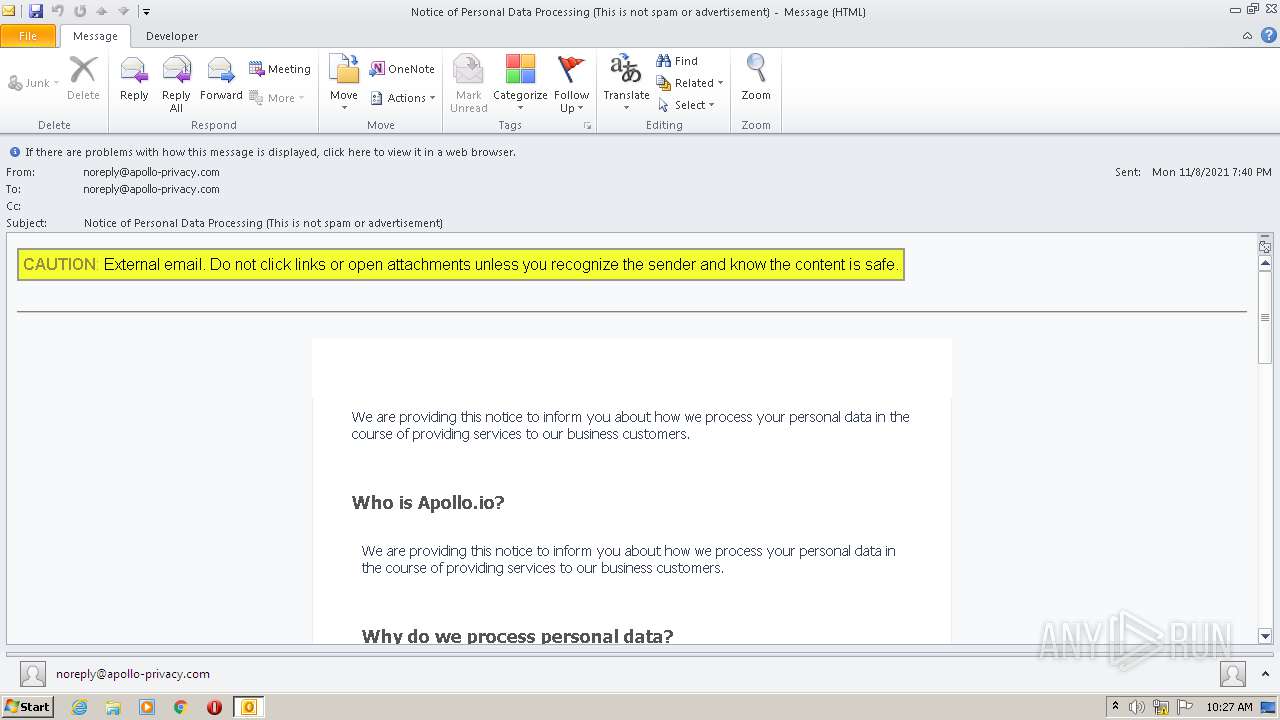
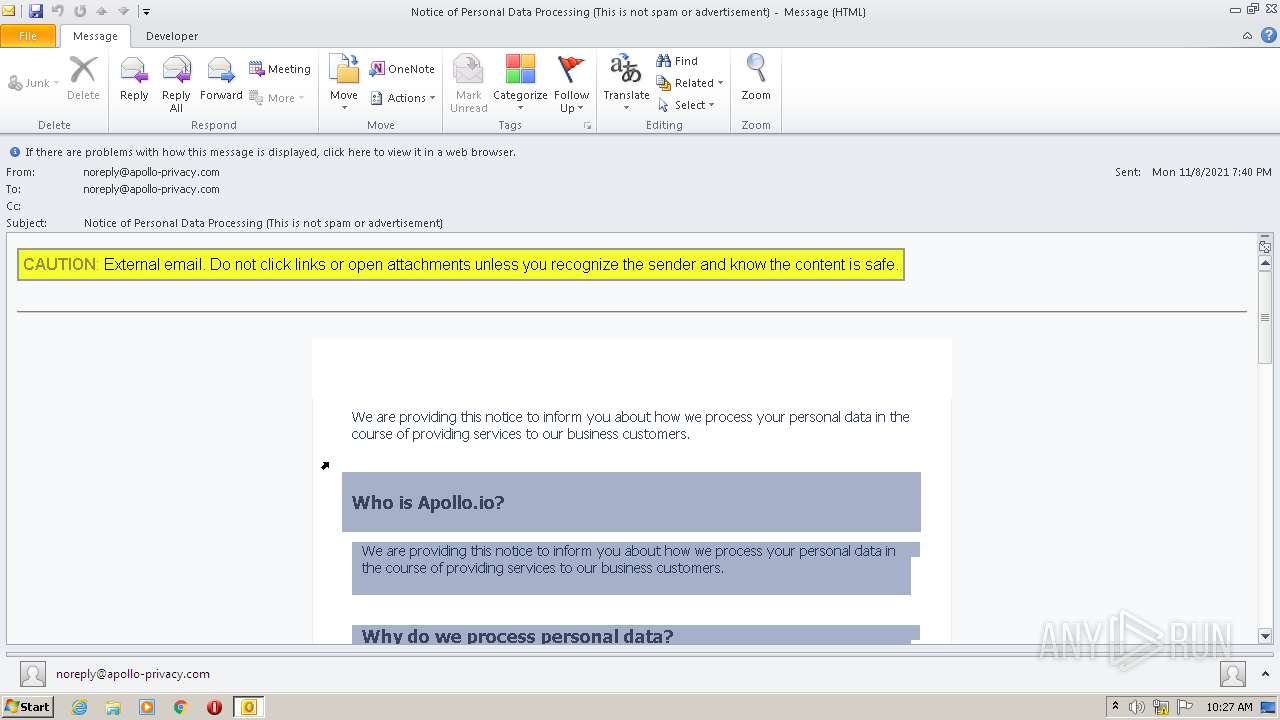
| File name: | Notice of Personal Data Processing (This is not spam or advertisement).msg |
| Full analysis: | https://app.any.run/tasks/3bcbde69-4839-47c6-9e2e-e585566968fb |
| Verdict: | Malicious activity |
| Analysis date: | November 22, 2021, 10:26:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 58FB01DA971C9A195D8C688C9CC00868 |
| SHA1: | 70BC02277866B4030510B78029D7F3CBAAE3CDE5 |
| SHA256: | 069B6EDCEE9B03EF8AF88EEFB5215E7365C369ECDE107D96C62CDFA8E36B911B |
| SSDEEP: | 1536:y8csWlmN37XQy0QJcLjjdcRCG1eCWPZMetVc3WkWA6cQzTqME5tZpWzR1:DcHlM7XQy0McLv01WdM6cQAj8R1 |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 1384)
SUSPICIOUS
Checks supported languages
- OUTLOOK.EXE (PID: 1232)
Starts itself from another location
- OUTLOOK.EXE (PID: 1384)
INFO
Reads the computer name
- OUTLOOK.EXE (PID: 1384)
Searches for installed software
- OUTLOOK.EXE (PID: 1384)
Checks Windows Trust Settings
- OUTLOOK.EXE (PID: 1384)
Checks supported languages
- OUTLOOK.EXE (PID: 1384)
Dropped object may contain Bitcoin addresses
- OUTLOOK.EXE (PID: 1384)
Creates files in the user directory
- OUTLOOK.EXE (PID: 1384)
Reads settings of System Certificates
- OUTLOOK.EXE (PID: 1384)
Reads Microsoft Outlook installation path
- OUTLOOK.EXE (PID: 1384)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 1232)
- OUTLOOK.EXE (PID: 1384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
38
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
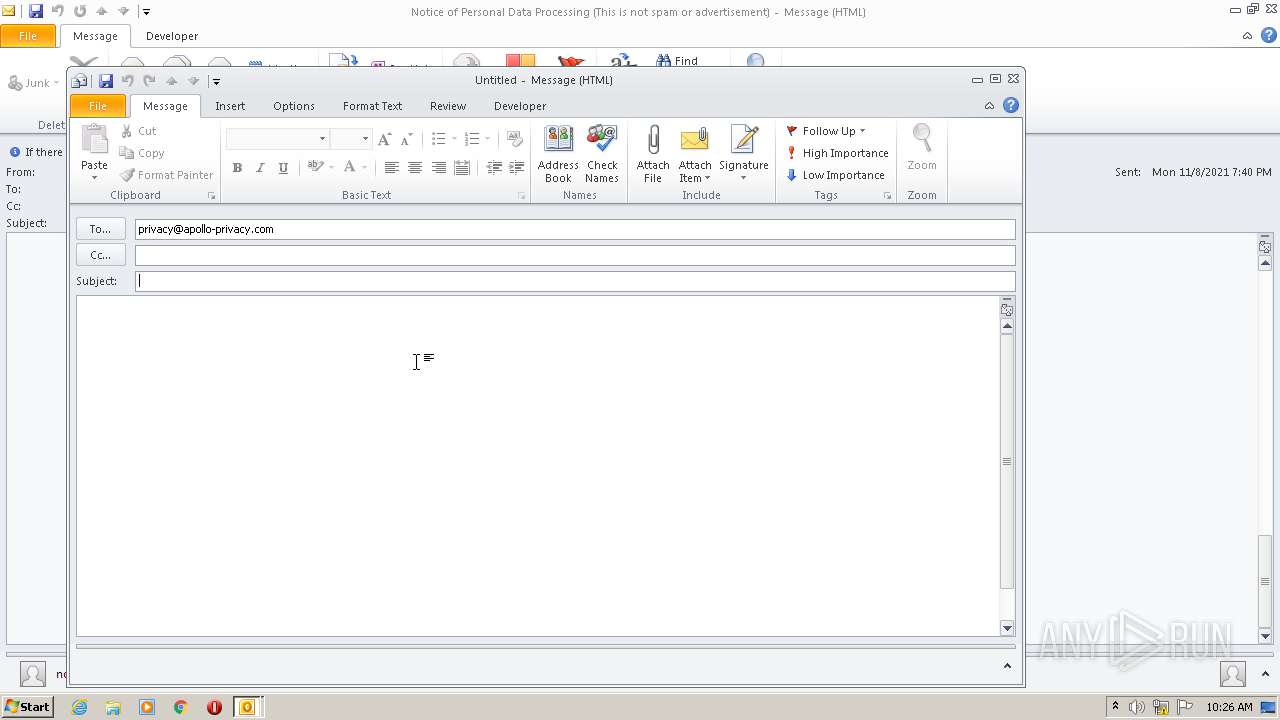
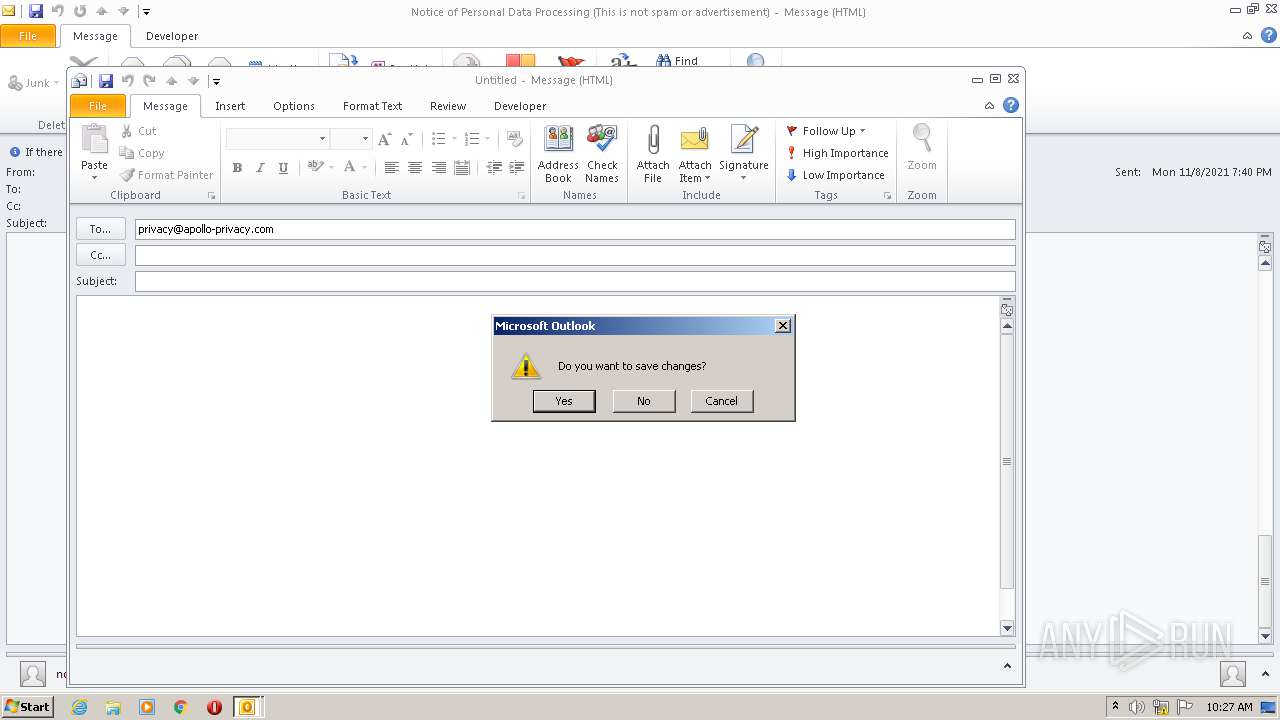
| 1232 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" -c IPM.Note /m "mailto:privacy@apollo-privacy.com" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 1384 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Notice of Personal Data Processing (This is not spam or advertisement).msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
22 555
Read events
21 927
Write events
599
Delete events
29
Modification events
| (PID) Process: | (1384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (1384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
8
Text files
24
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRAFCA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1384 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 1384 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1384 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | der | |
MD5:— | SHA256:— | |||
| 1384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 1384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 1384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_RssRule_2_04E91B8506A45045B9FD52F8341936BC.dat | xml | |
MD5:D8B37ED0410FB241C283F72B76987F18 | SHA256:31E68049F6B7F21511E70CD7F2D95B9CF1354CF54603E8F47C1FC40F40B7A114 | |||
| 1384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\eJwdzEkOwjAMQNHTNDsqO0MbL7LlGlUGByoSuYoqELdnWP7F-yUQFEek9qBBIyJ4JAvazJAAClbDxYPLiJOFeEhrcjnG_oz5PWfp6h4Qki3Wp2Vx1ay-Iv8ik84c15VJjTAk8Ti3R-Pe-fvpOVbmvz_Da9JX2Z[1].gif | image | |
MD5:DB04C7B378CB2DB912C3BA8A5A774EE3 | SHA256:98B3D9D20E032F90ACA49E9B116225D539FF6FBDB7E42C3C363F63896AC03D2A | |||
| 1384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_49F92BB05049264AB06ACE1F1063FF1B.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
| 1384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ConversationPrefs_2_24B8FC84C2BEE24EAE038AC4D7616B20.dat | xml | |
MD5:57F30B1BCA811C2FCB81F4C13F6A927B | SHA256:612BAD93621991CB09C347FF01EC600B46617247D5C041311FF459E247D8C2D3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
33
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1384 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
1384 | OUTLOOK.EXE | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertGlobalRootCA.crl | US | der | 631 b | whitelisted |
1384 | OUTLOOK.EXE | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.68 Kb | whitelisted |
1384 | OUTLOOK.EXE | GET | 200 | 13.225.84.49:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
1384 | OUTLOOK.EXE | GET | 200 | 13.225.84.145:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
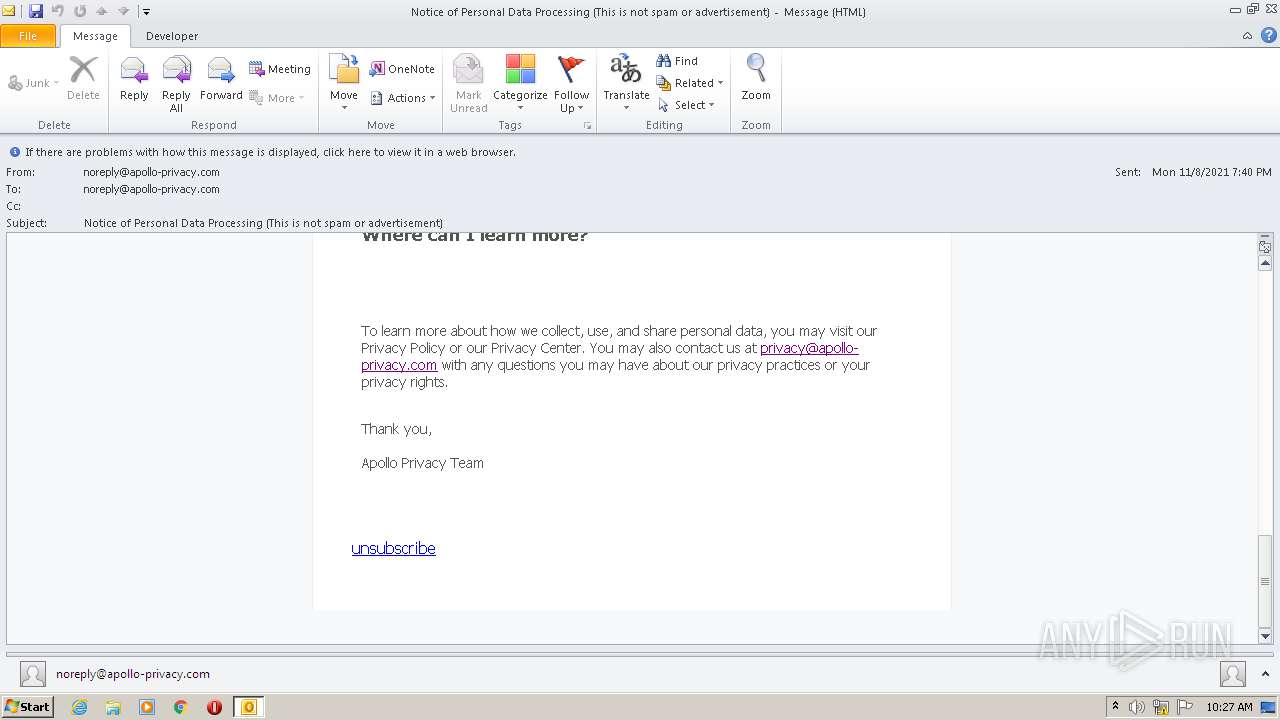
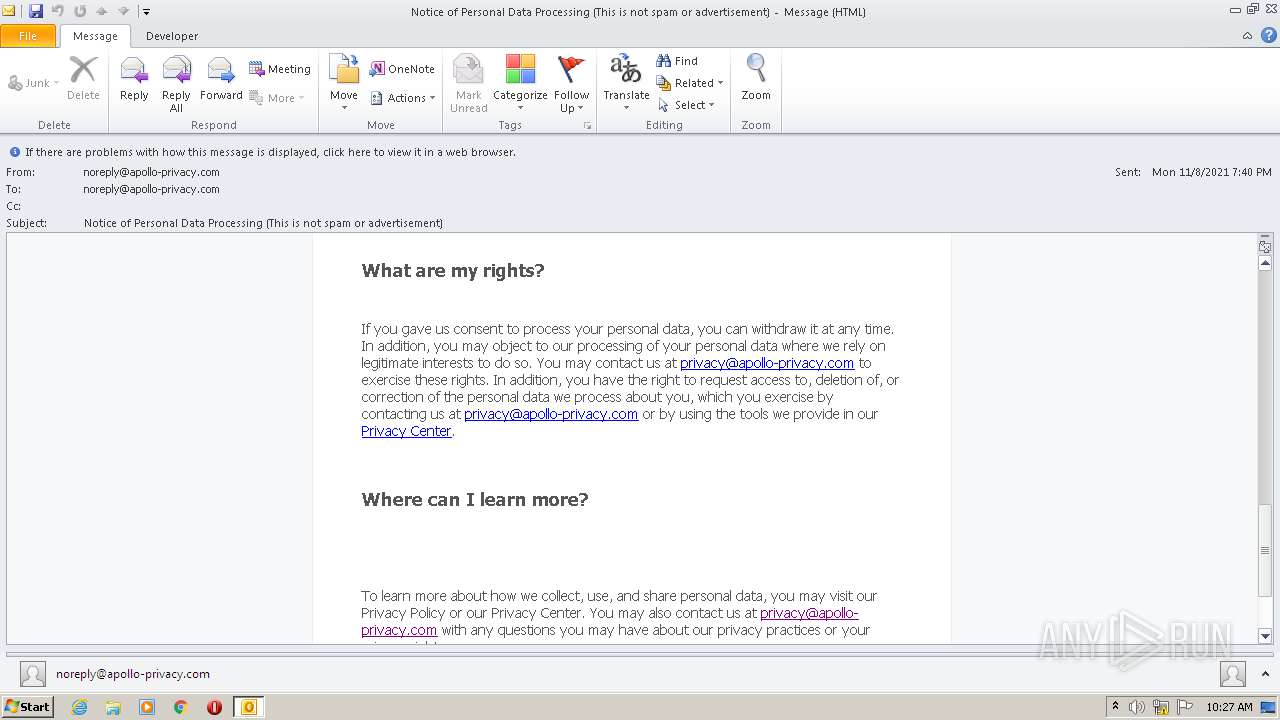
1384 | OUTLOOK.EXE | GET | 302 | 216.239.34.21:80 | http://apollo-privacy.com/data-protection | US | html | 234 b | malicious |
1384 | OUTLOOK.EXE | GET | 302 | 216.239.34.21:80 | http://apollo-privacy.com/data-terms | US | html | 234 b | malicious |
1384 | OUTLOOK.EXE | GET | 302 | 216.239.34.21:80 | http://apollo-privacy.com/data-retro | US | html | 234 b | malicious |
— | — | GET | 200 | 178.79.242.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f9aa1c5aab88a431 | DE | compressed | 4.70 Kb | whitelisted |
— | — | GET | 200 | 178.79.242.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?940381ca76fd82fc | DE | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1384 | OUTLOOK.EXE | 91.198.174.208:443 | upload.wikimedia.org | Wikimedia Foundation, Inc. | NL | suspicious |
1384 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
1384 | OUTLOOK.EXE | 216.239.34.21:80 | apollo-privacy.com | Google Inc. | US | whitelisted |
1384 | OUTLOOK.EXE | 76.223.86.4:443 | rb.gy | AT&T Services, Inc. | US | suspicious |
1384 | OUTLOOK.EXE | 104.26.13.210:443 | sensorstechforum.com | Cloudflare Inc | US | unknown |
1384 | OUTLOOK.EXE | 54.81.26.69:80 | email.apollo-privacy.com | Amazon.com, Inc. | US | unknown |
1384 | OUTLOOK.EXE | 13.225.84.51:443 | d2v9ipibika81v.cloudfront.net | — | US | unknown |
1384 | OUTLOOK.EXE | 104.20.192.9:443 | www.apollo.io | Cloudflare Inc | US | unknown |
1384 | OUTLOOK.EXE | 13.225.84.145:80 | ocsp.rootg2.amazontrust.com | — | US | whitelisted |
1384 | OUTLOOK.EXE | 13.225.84.42:80 | o.ss2.us | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
d2v9ipibika81v.cloudfront.net |
| whitelisted |
upload.wikimedia.org |
| whitelisted |
apollo-privacy.com |
| malicious |
sensorstechforum.com |
| whitelisted |
rb.gy |
| whitelisted |
email.apollo-privacy.com |
| suspicious |
www.apollo.io |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |