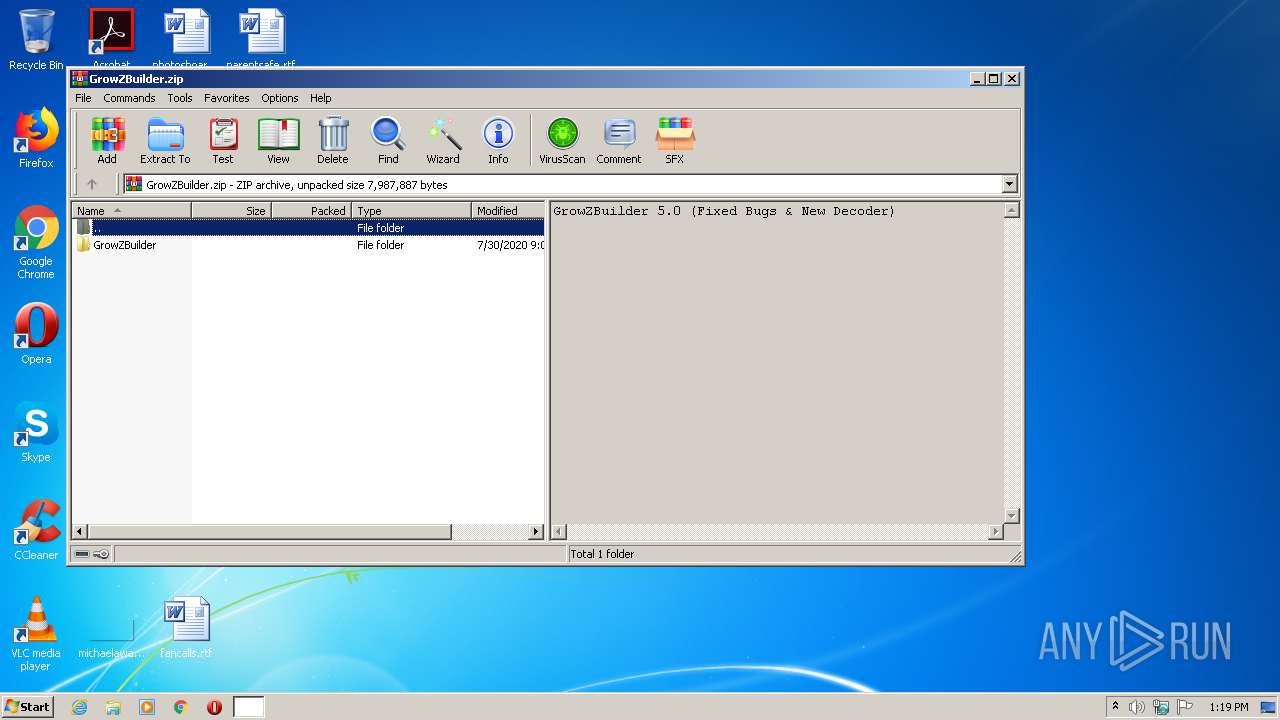
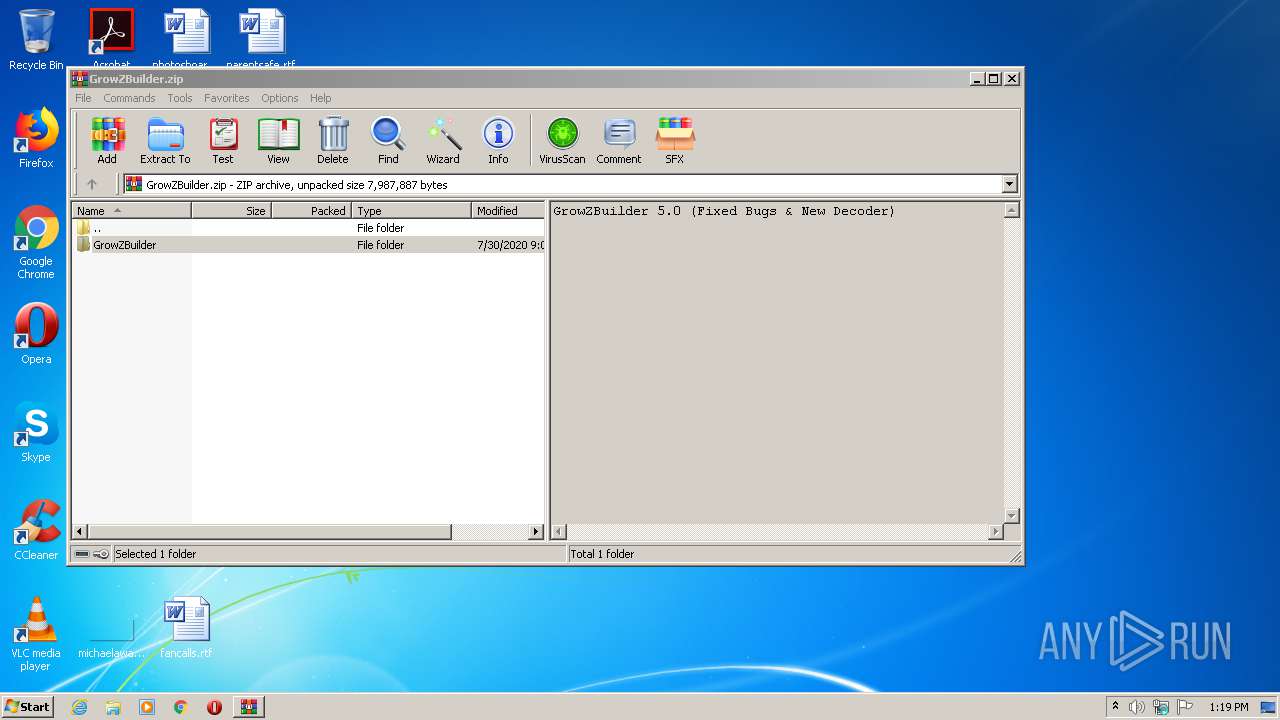
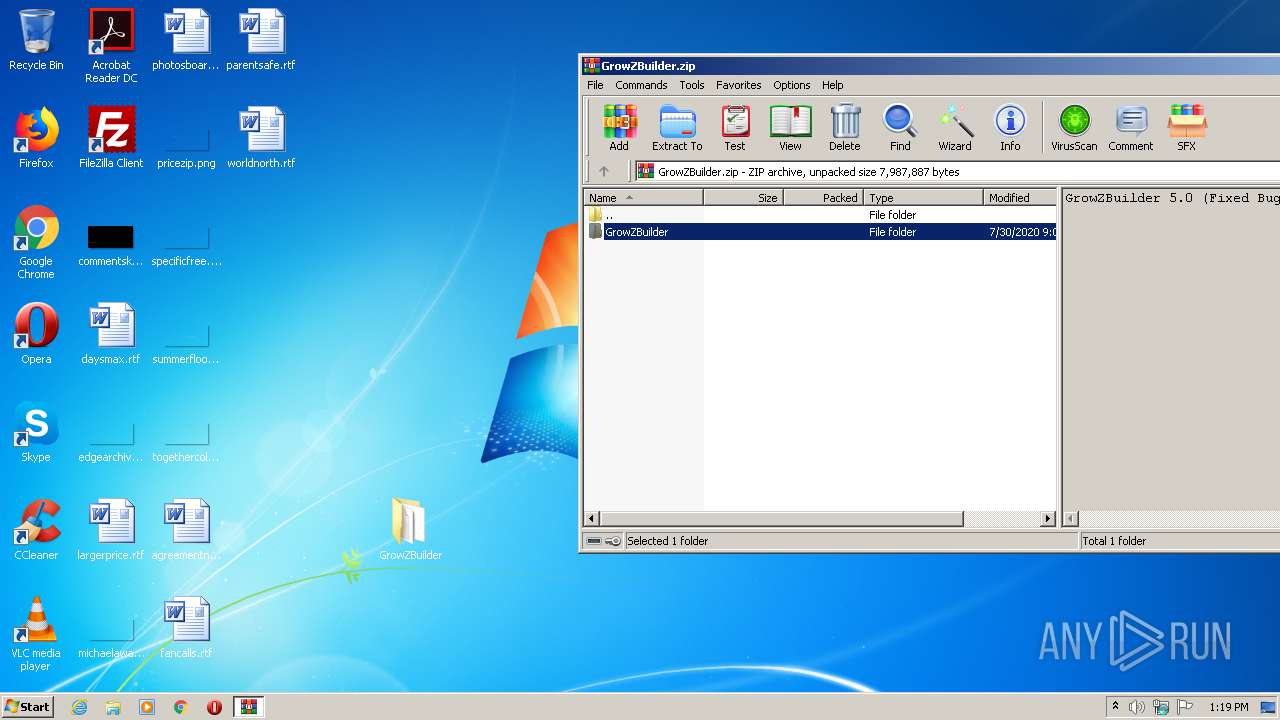
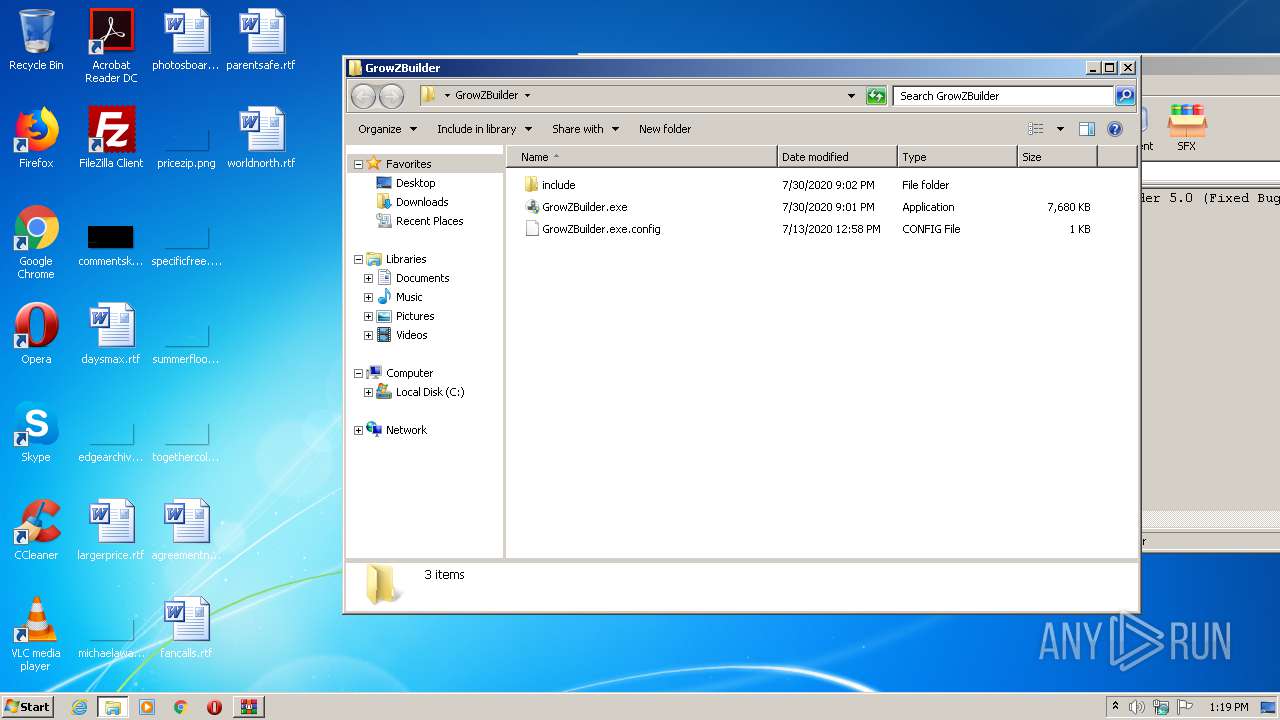
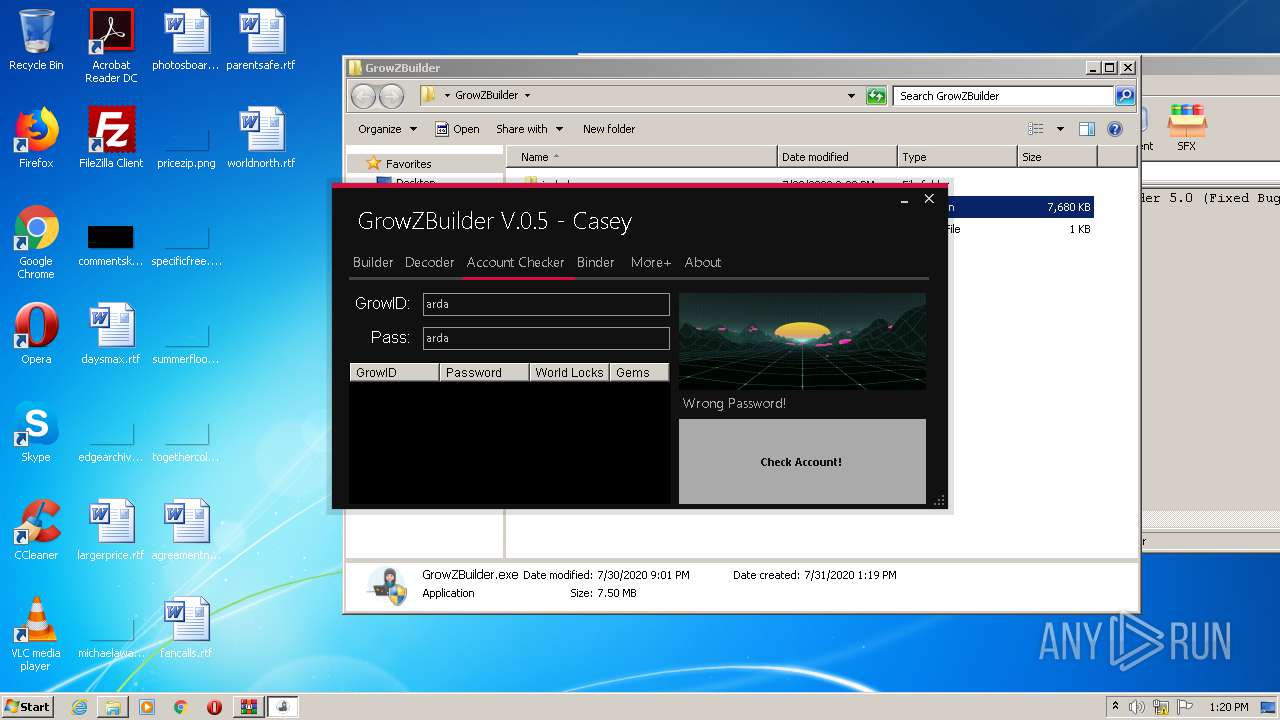
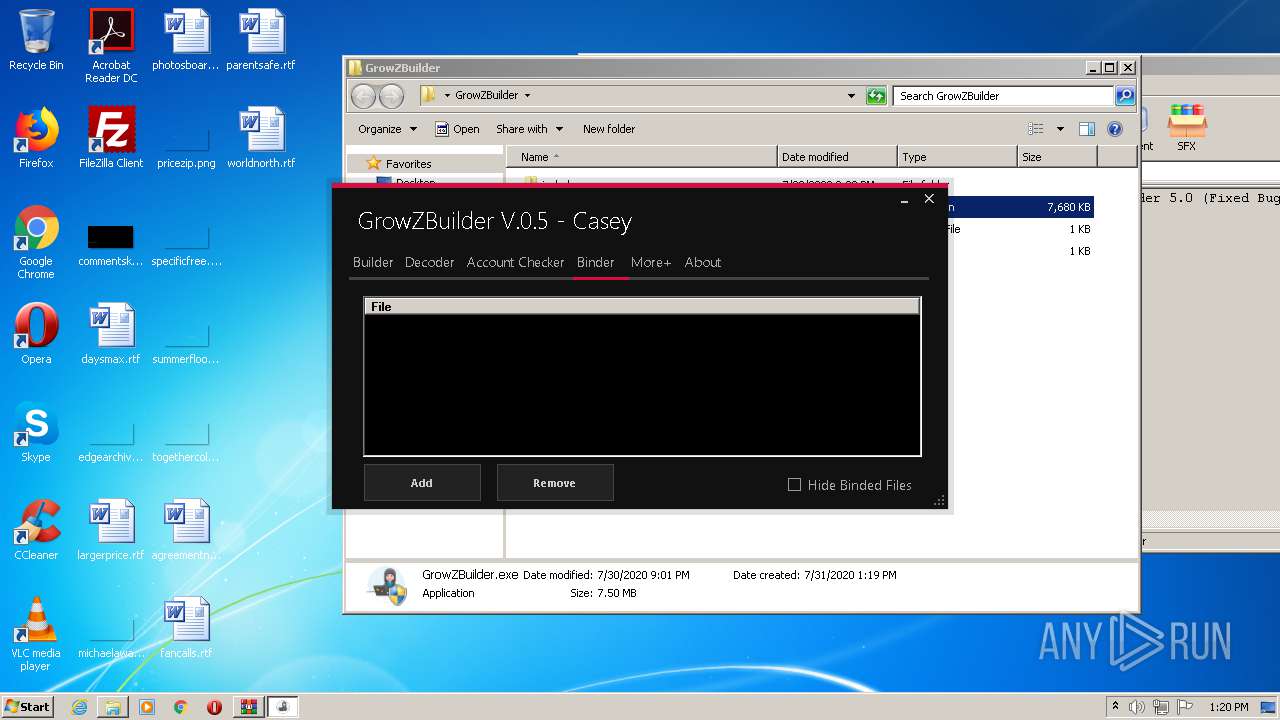
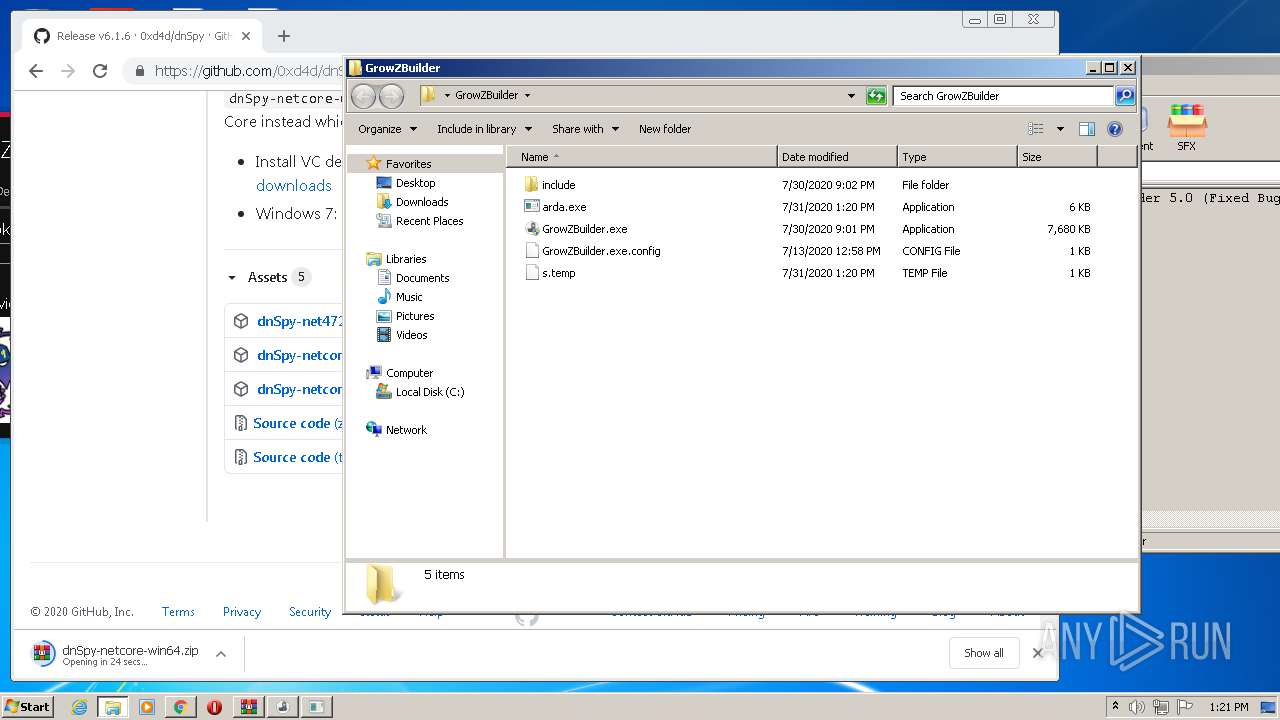
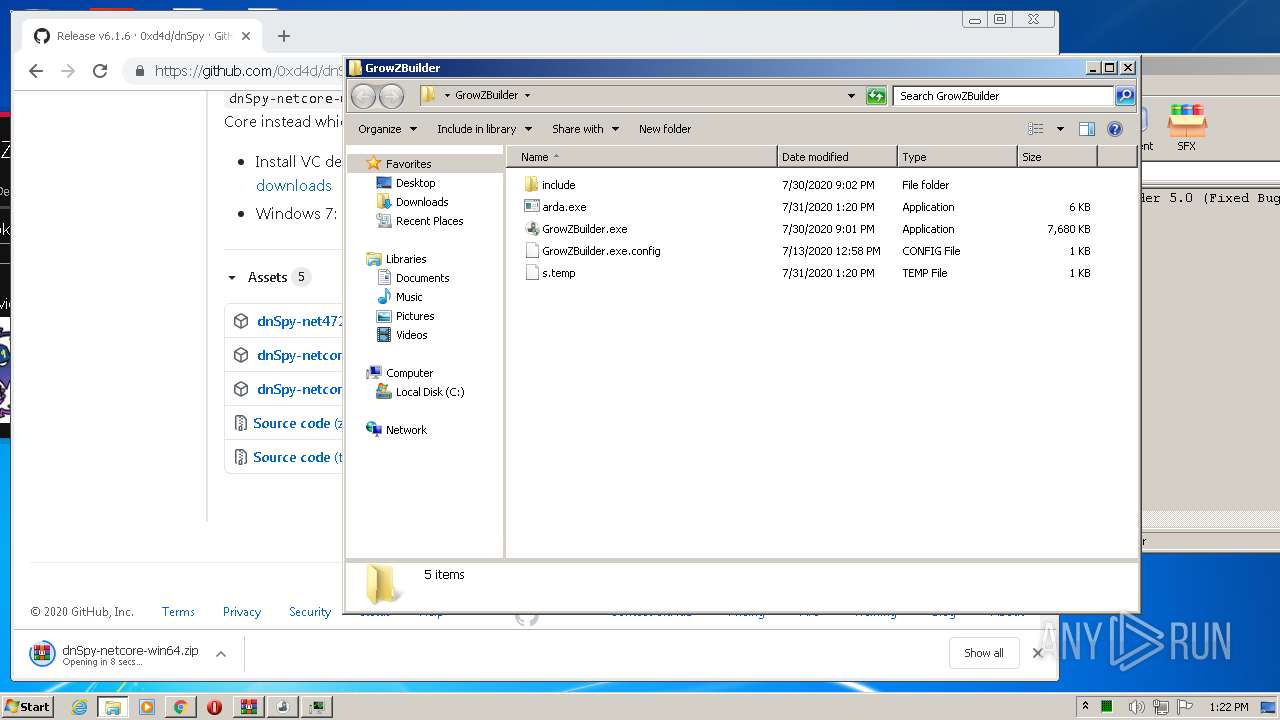
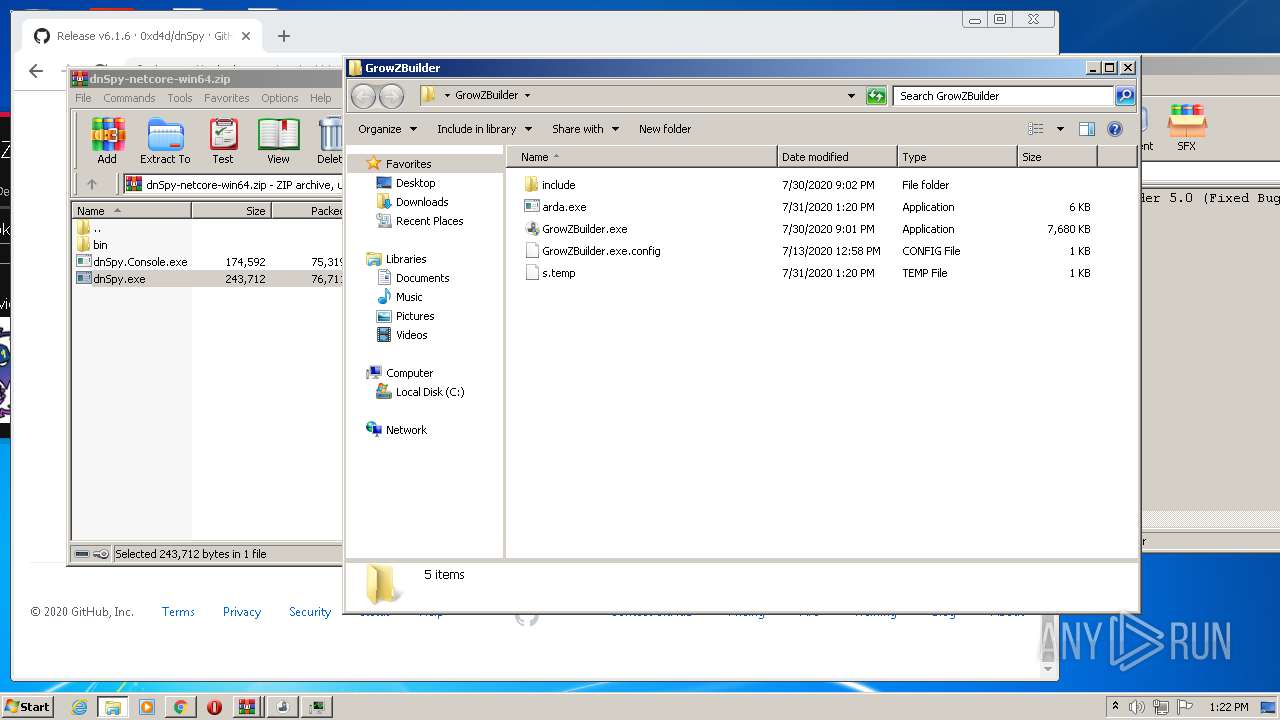
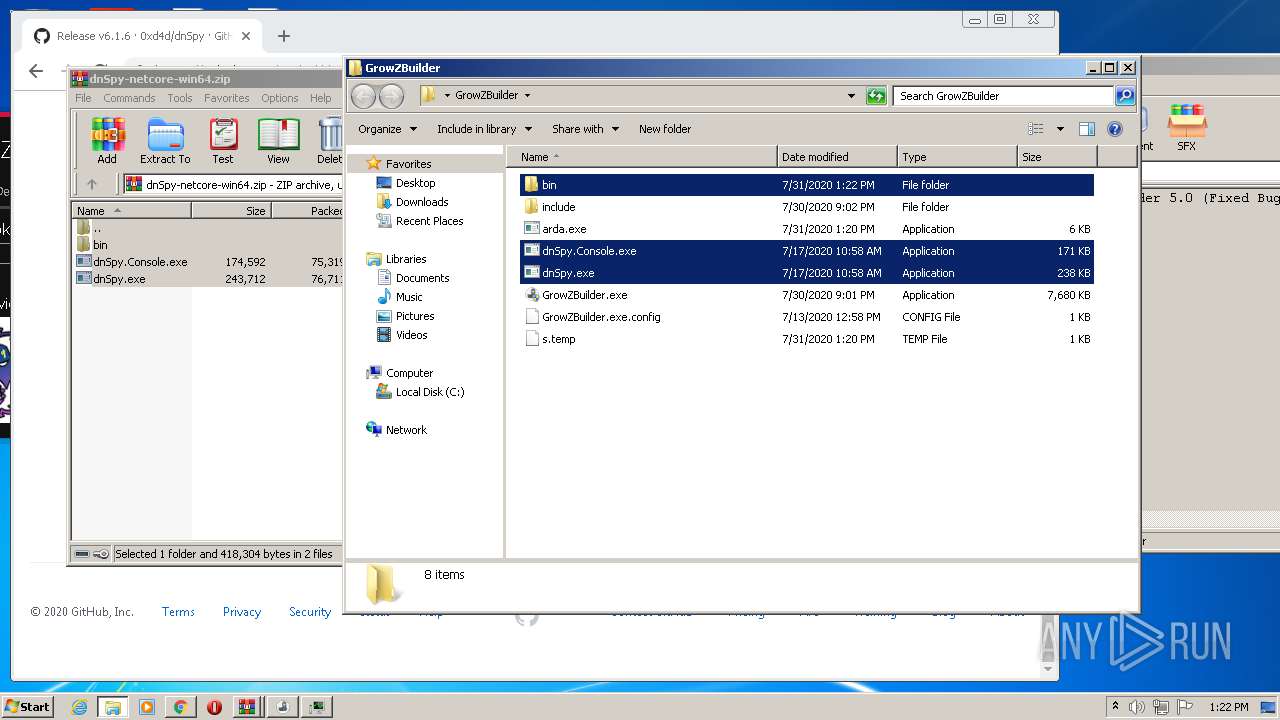
| download: | GrowZBuilder.zip |
| Full analysis: | https://app.any.run/tasks/9bb9b225-abe6-4d90-bf3e-58dcfdc19fa7 |
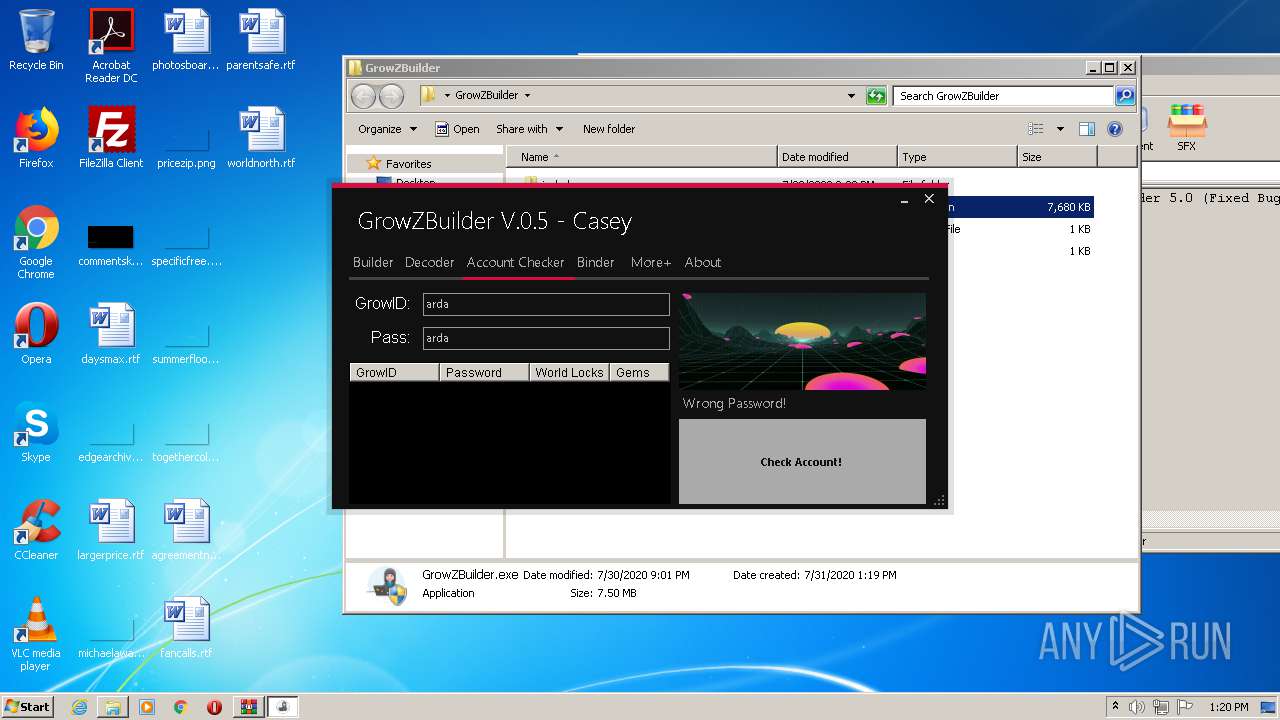
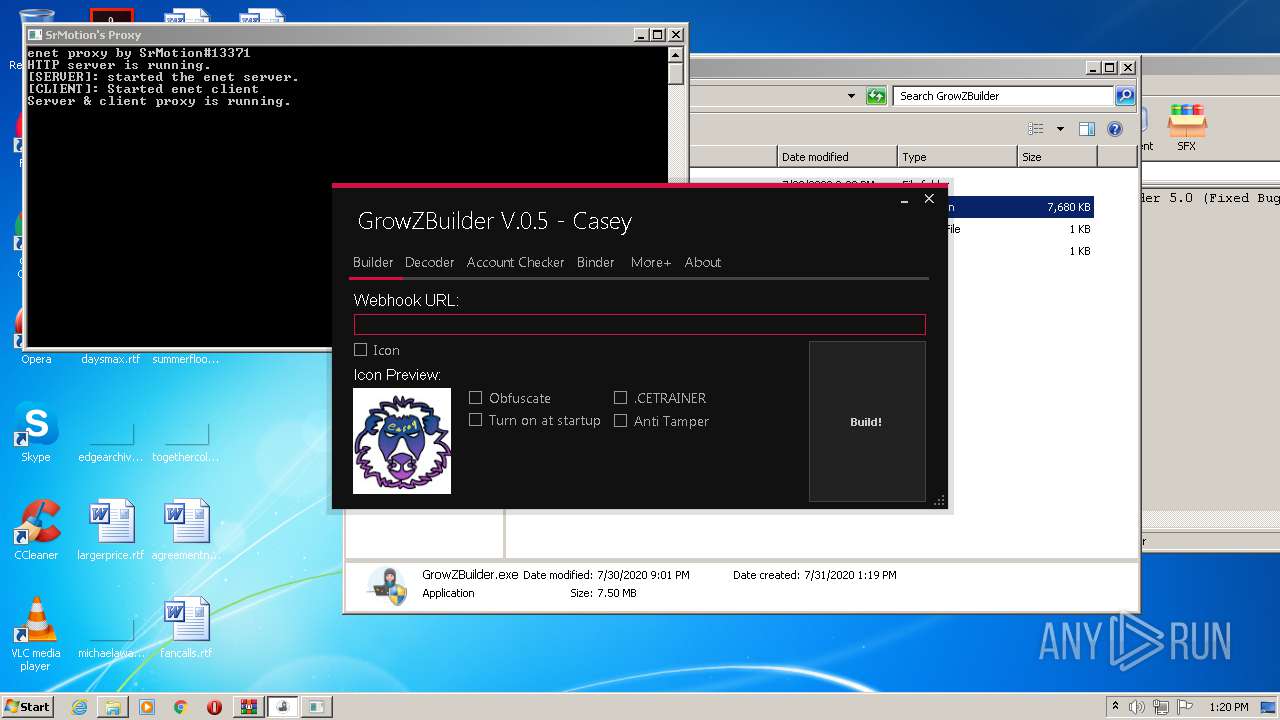
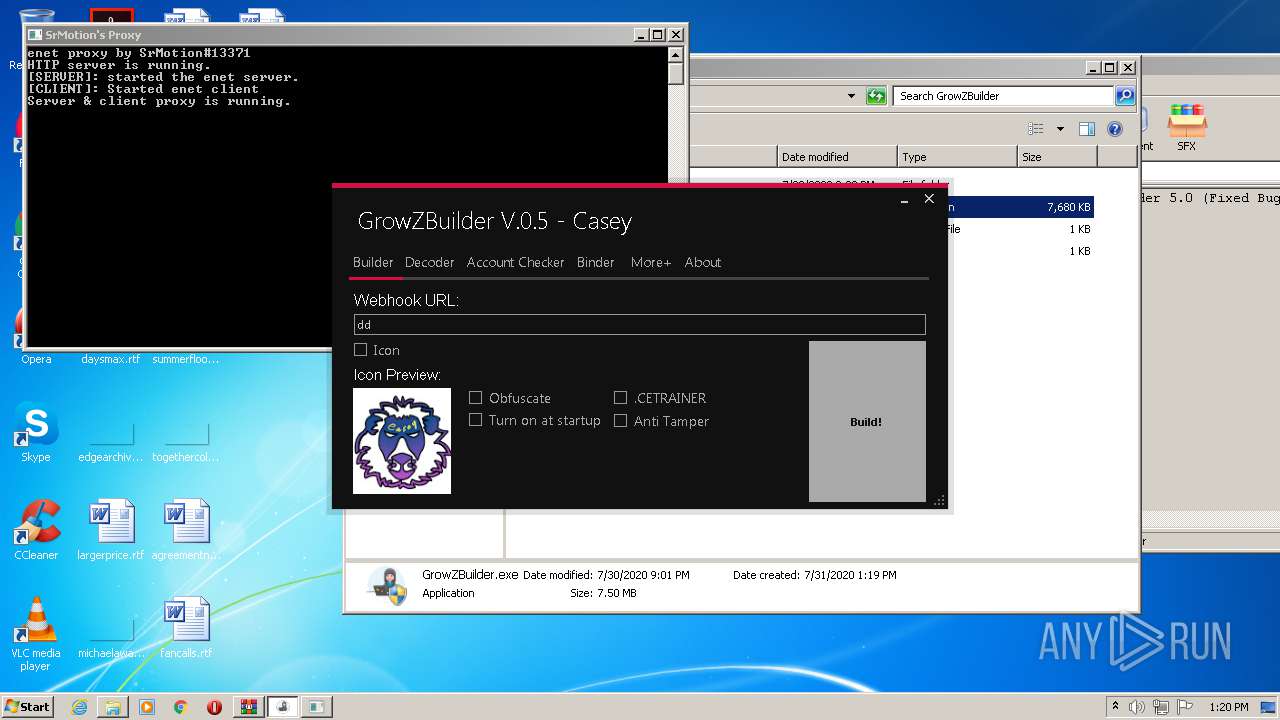
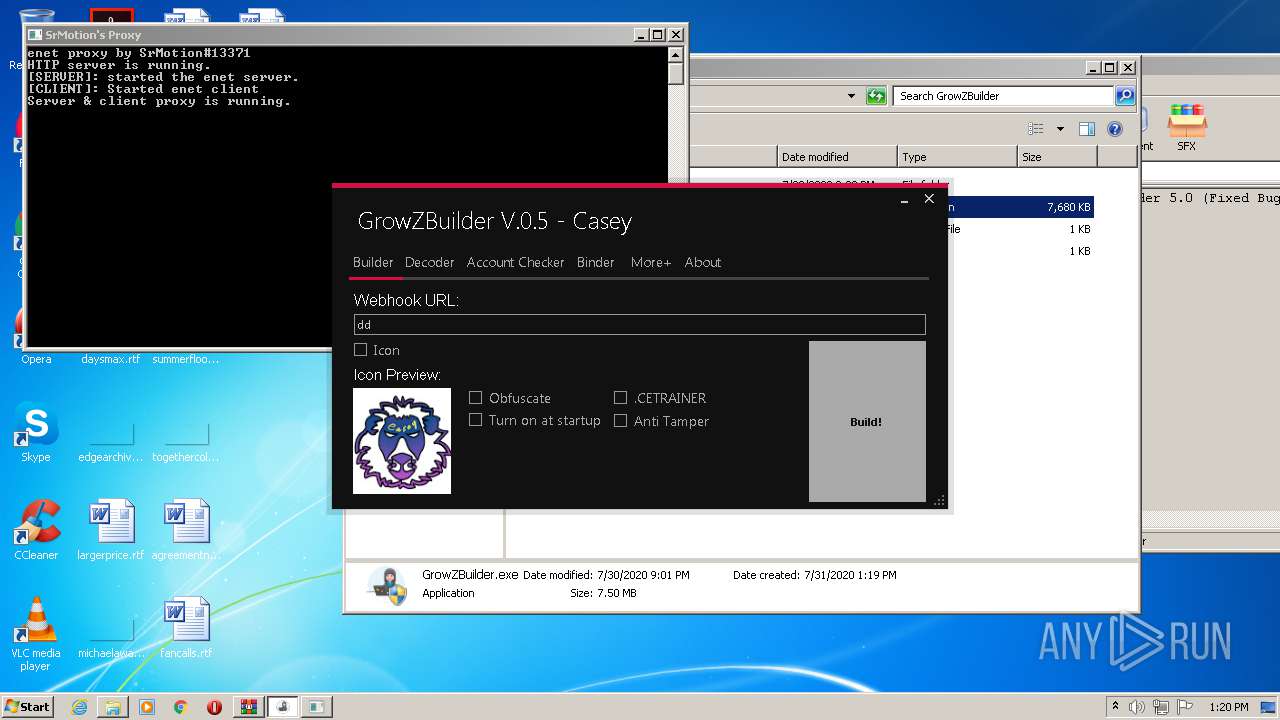
| Verdict: | Malicious activity |
| Analysis date: | July 31, 2020, 12:18:42 |
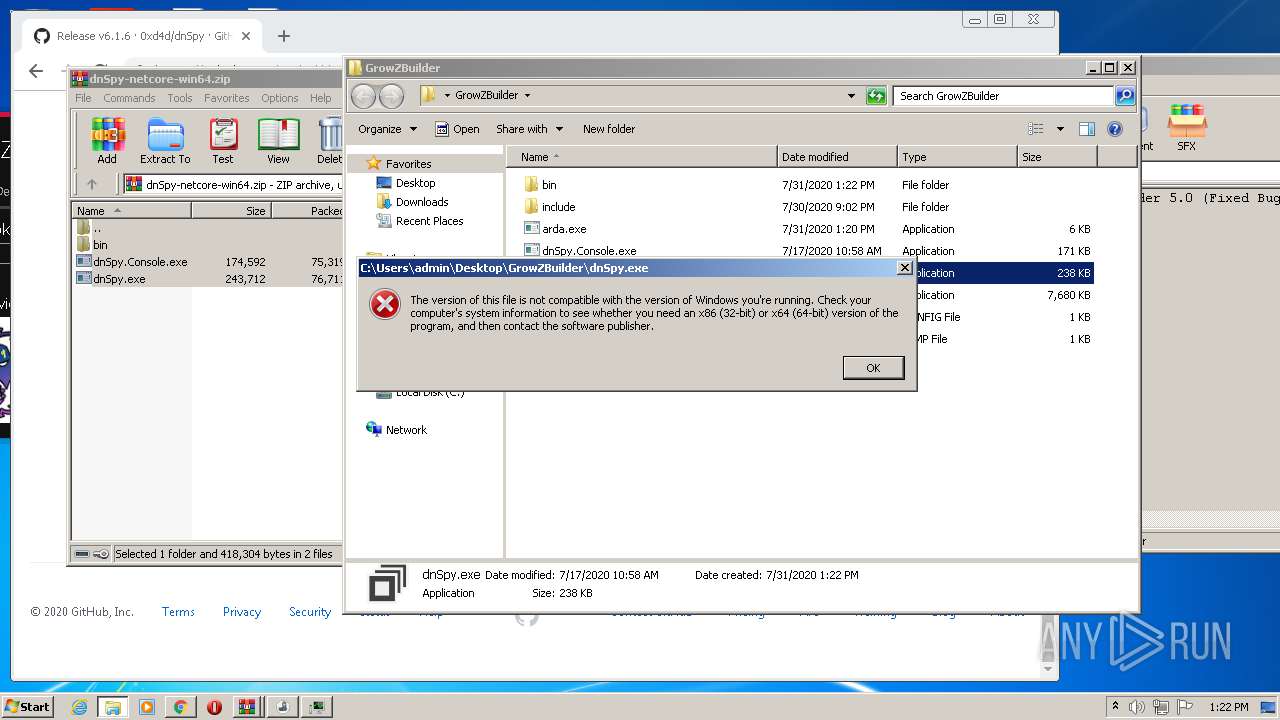
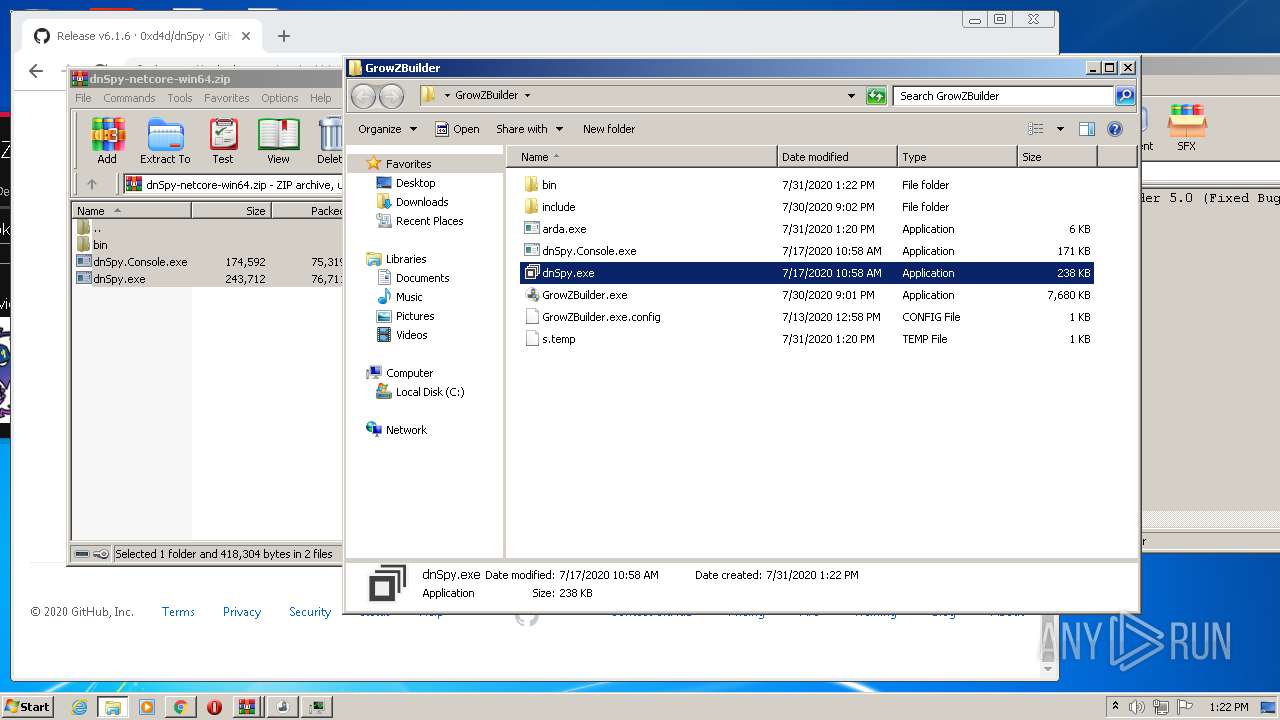
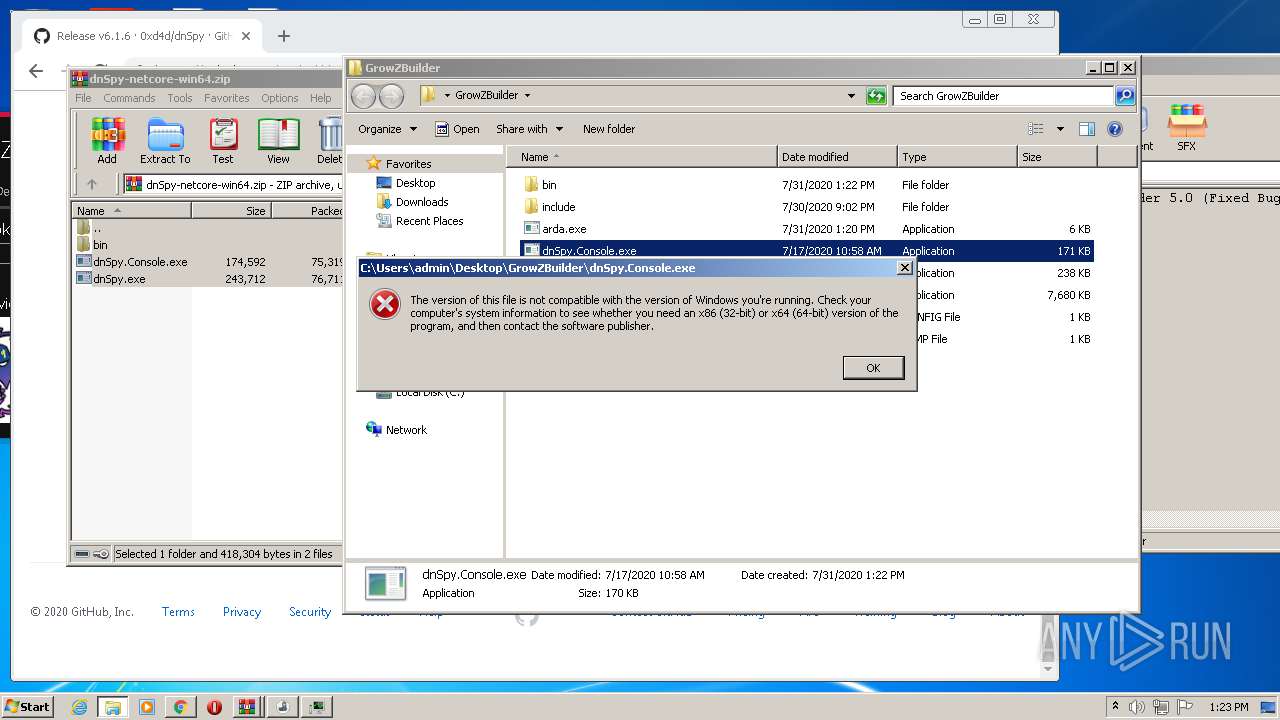
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | FAC5C4F6EA94283B124CBD02F3F20AAF |
| SHA1: | 6197BDD032383CC35968A11E03D47B72A8C964CC |
| SHA256: | 06959CB3AA7D13EB76CD18C1E3CF8ACC9BDCE0F03F0448FD993477E2711FA462 |
| SSDEEP: | 196608:+SyT/bIJ2vMbm7OVRS0FGfJkbPV4bsDXdQW2k+q5:+SyT/bq2vMy7Oy0FGfJkbV4QDtQ2 |
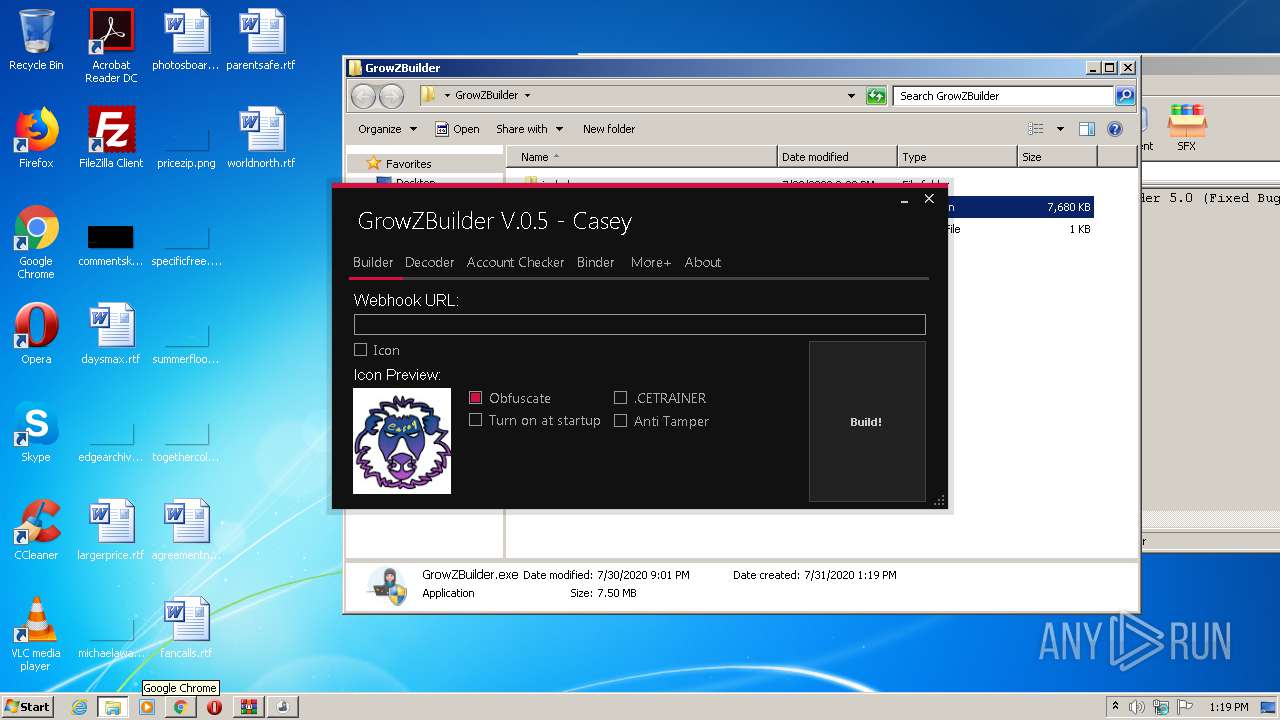
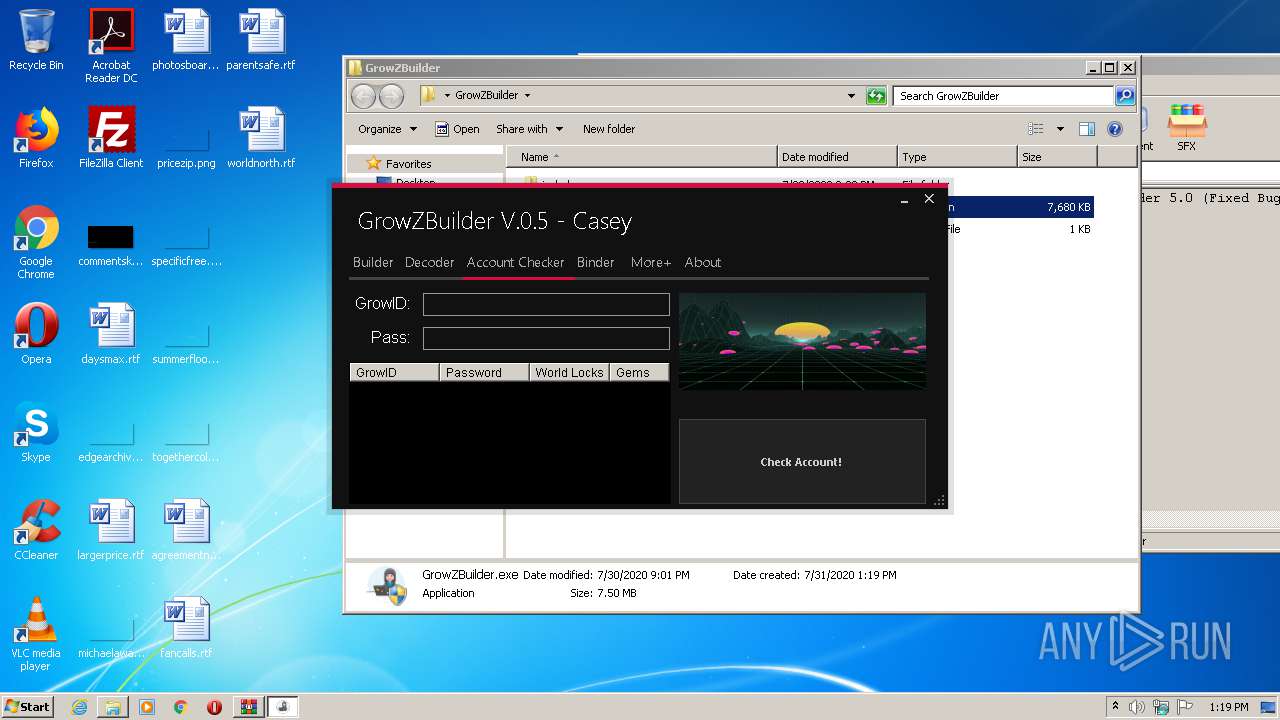
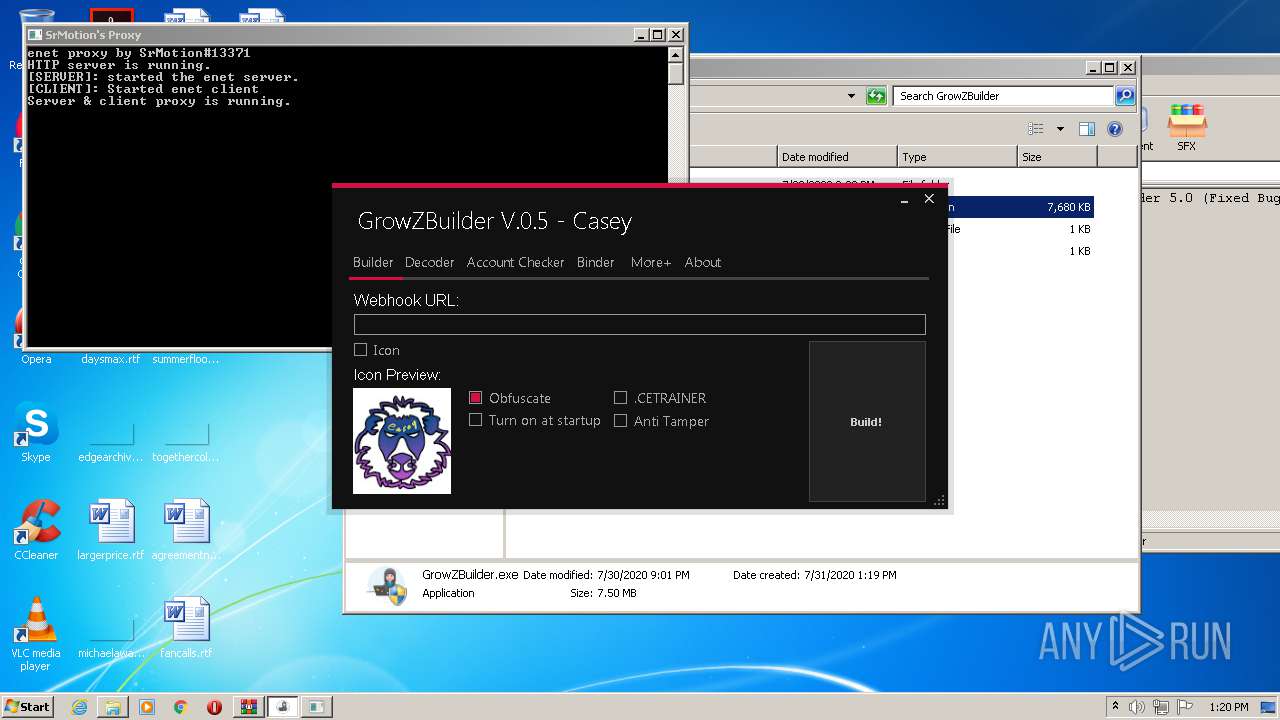
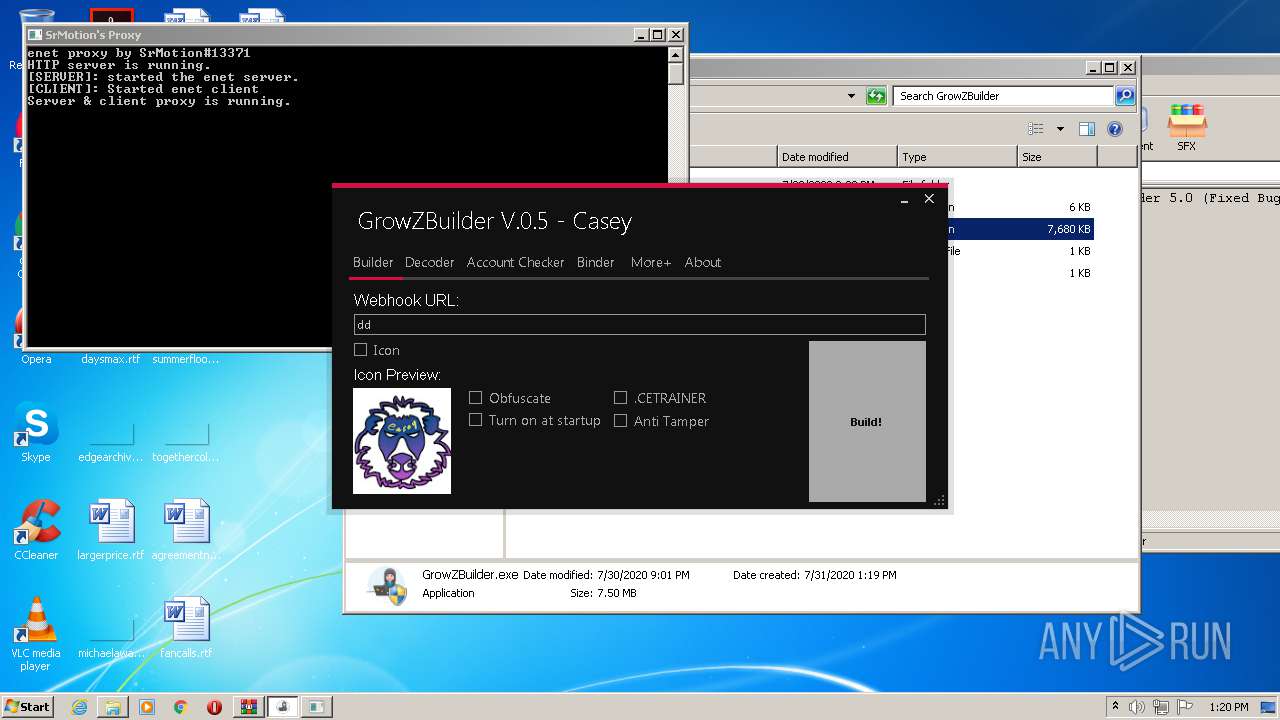
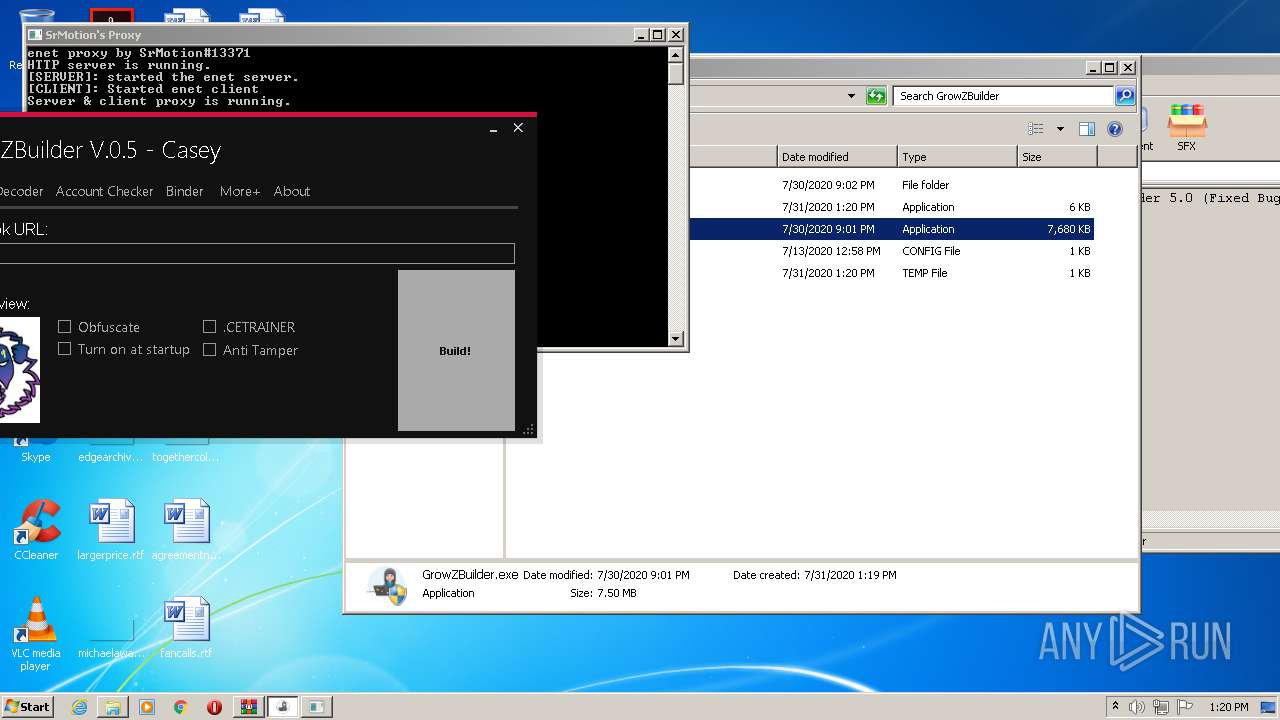
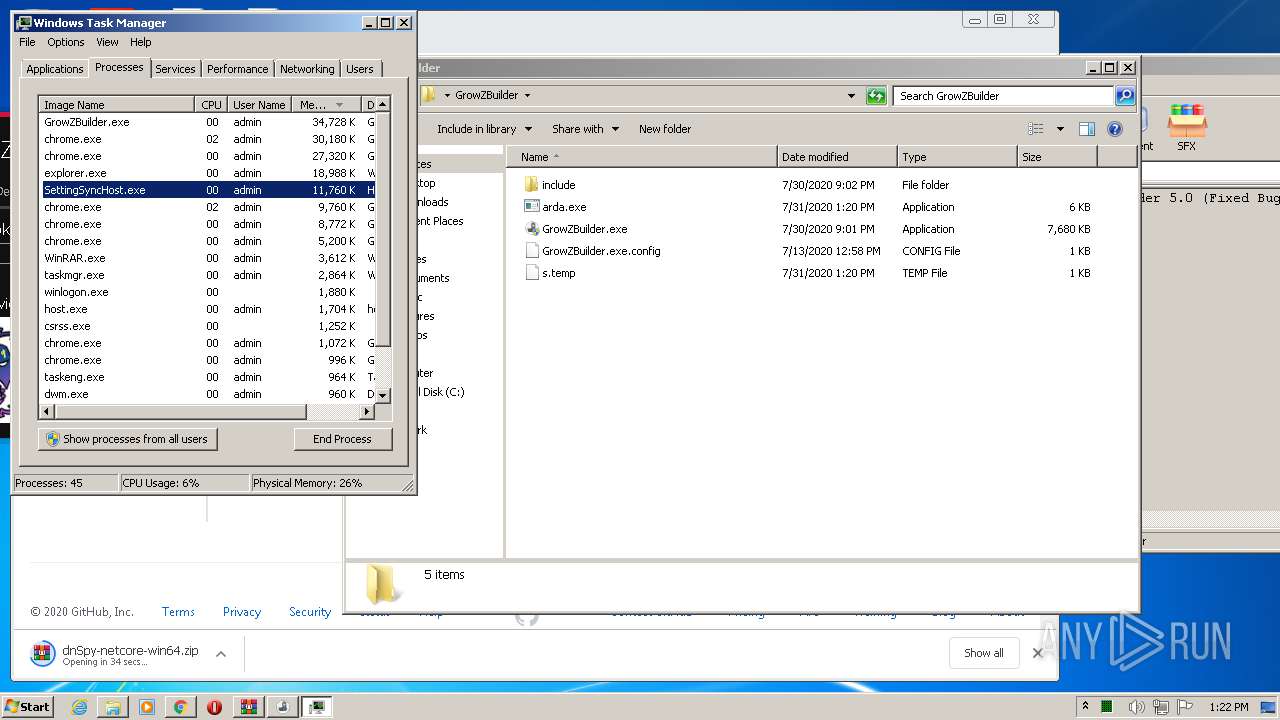
MALICIOUS
Changes settings of System certificates
- SettingSyncHost.exe (PID: 1516)
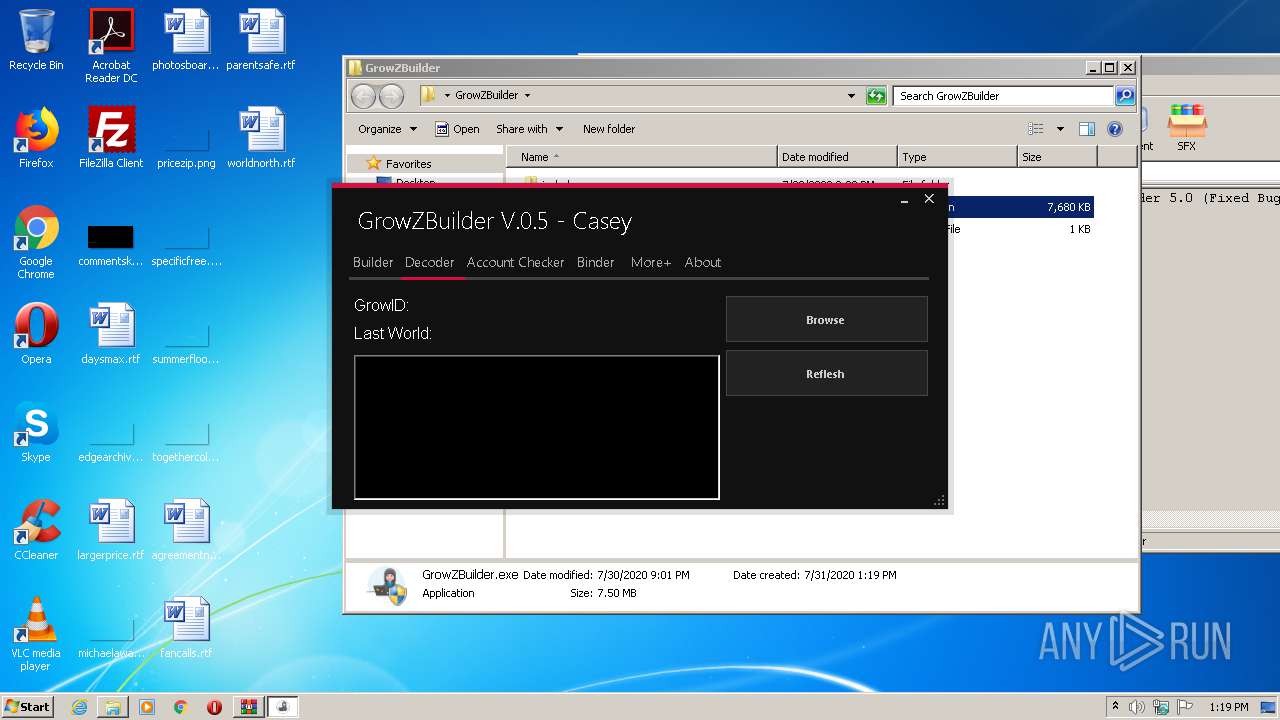
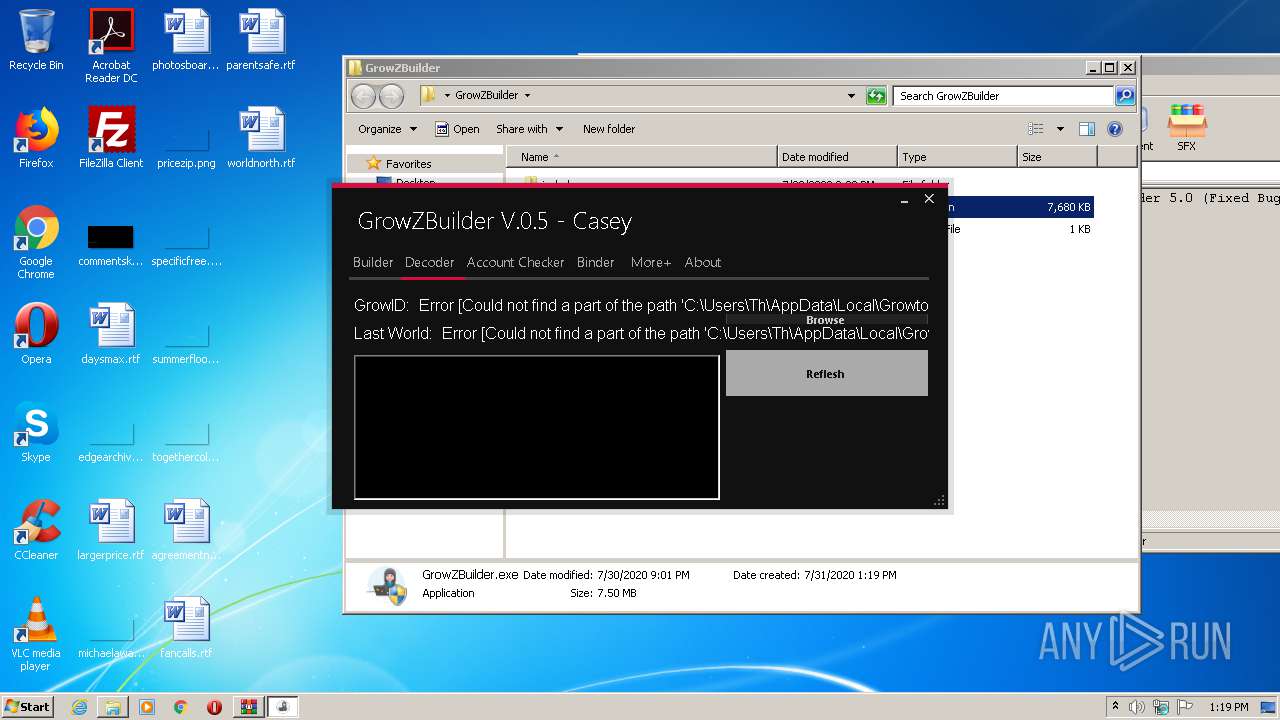
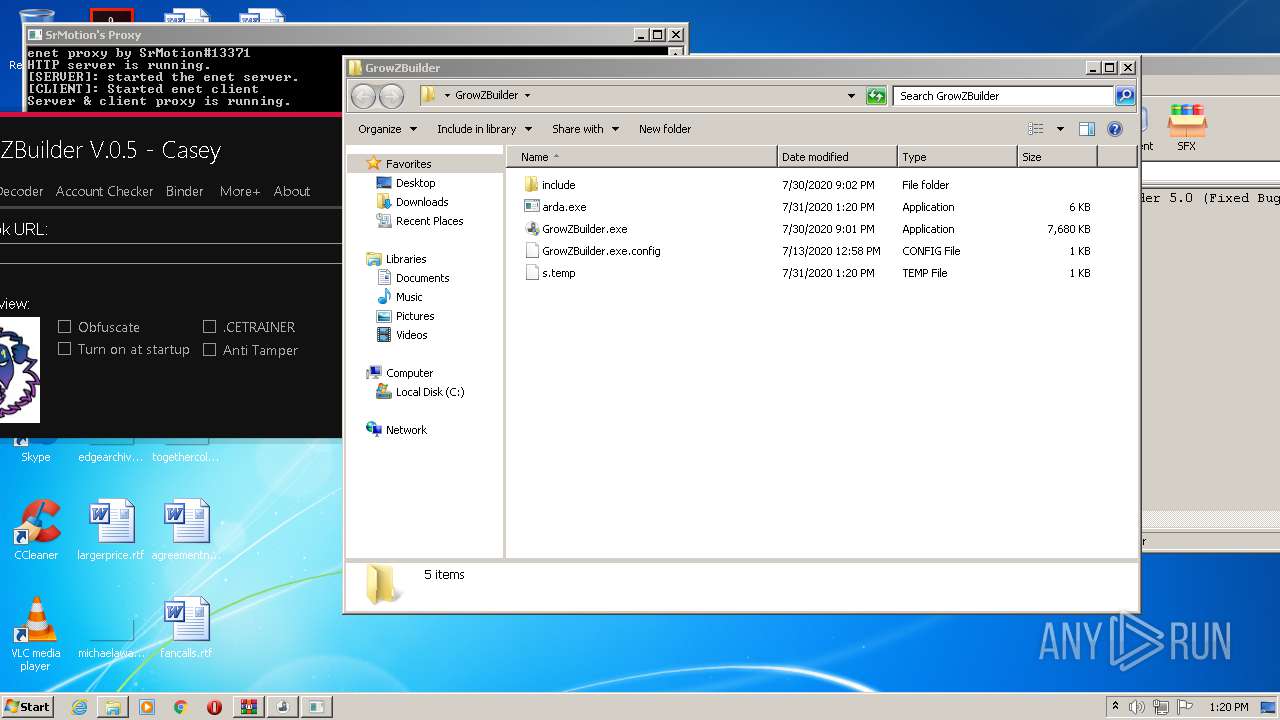
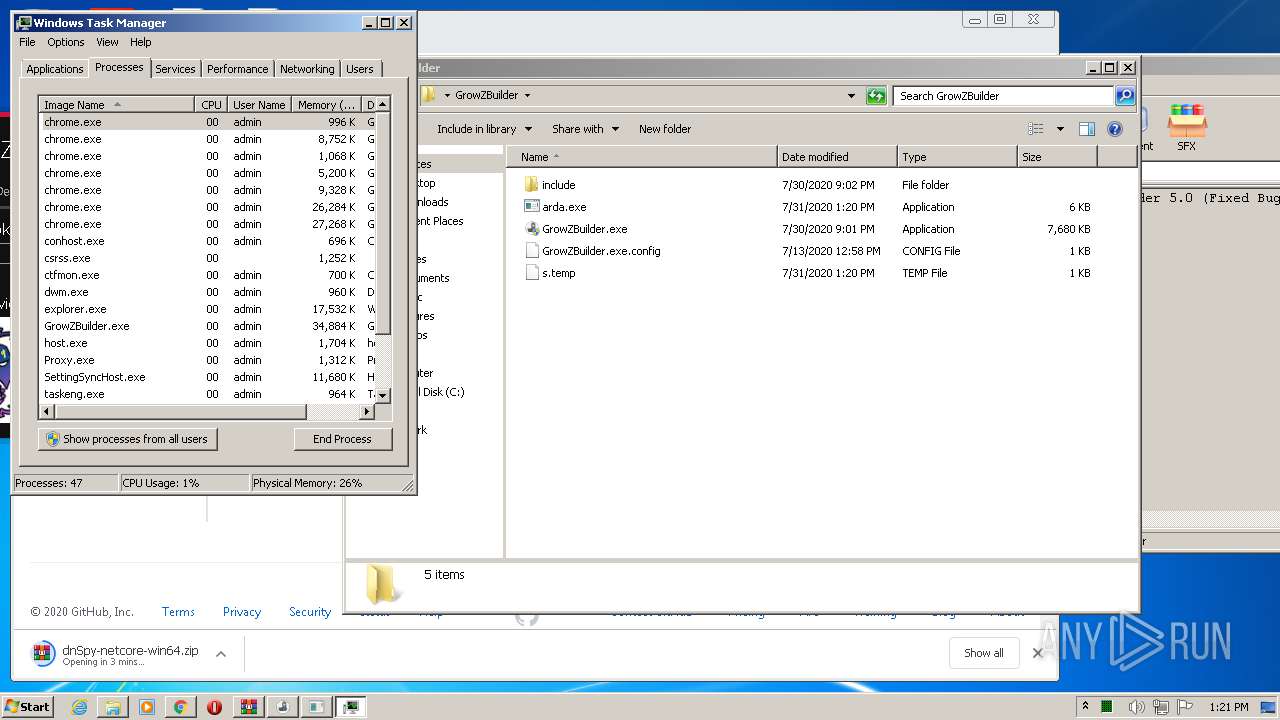
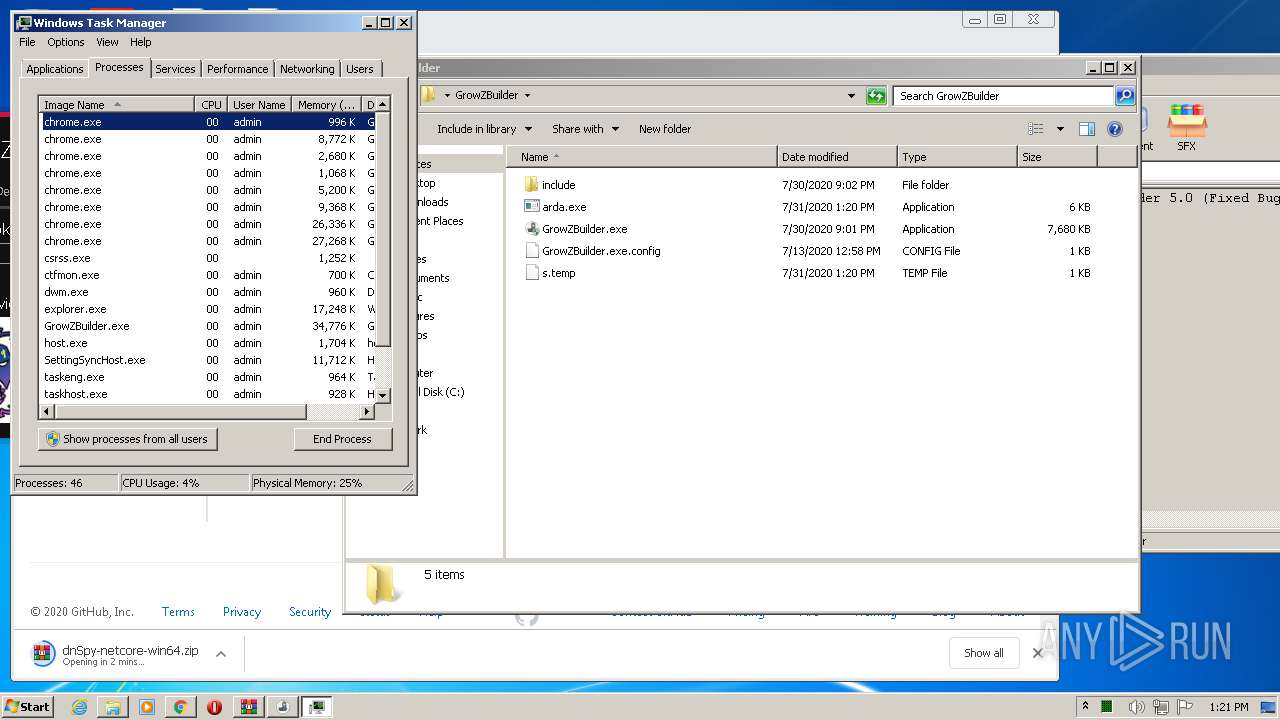
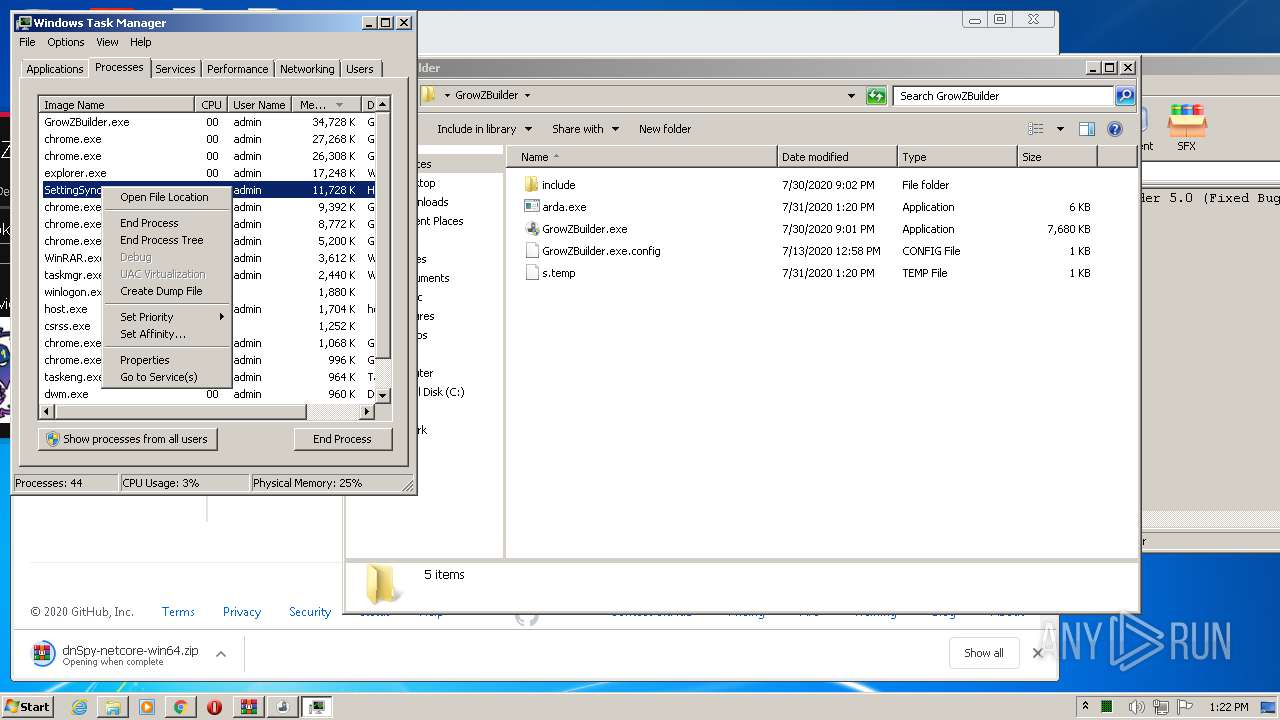
Application was dropped or rewritten from another process
- GrowZBuilder.exe (PID: 3816)
- SettingSyncHost.exe (PID: 1516)
Loads dropped or rewritten executable
- GrowZBuilder.exe (PID: 3816)
- SearchProtocolHost.exe (PID: 3500)
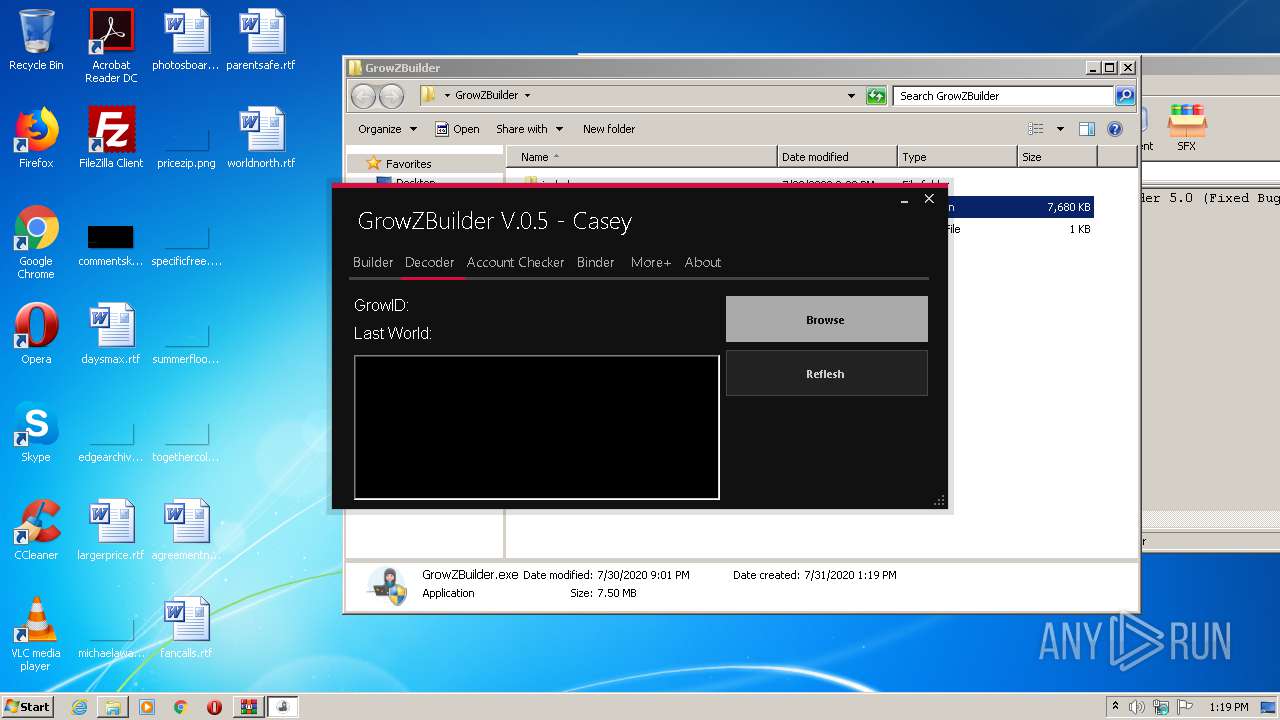
Starts Visual C# compiler
- GrowZBuilder.exe (PID: 3816)
Changes the autorun value in the registry
- SettingSyncHost.exe (PID: 1516)
SUSPICIOUS
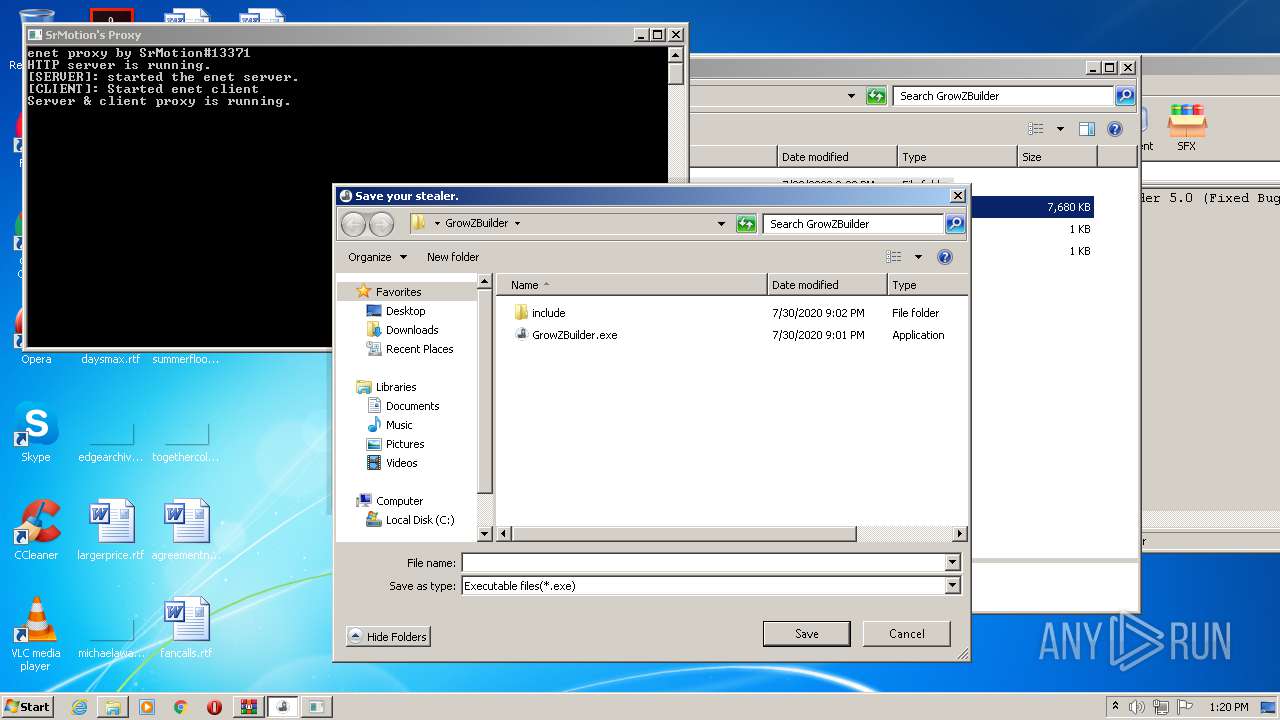
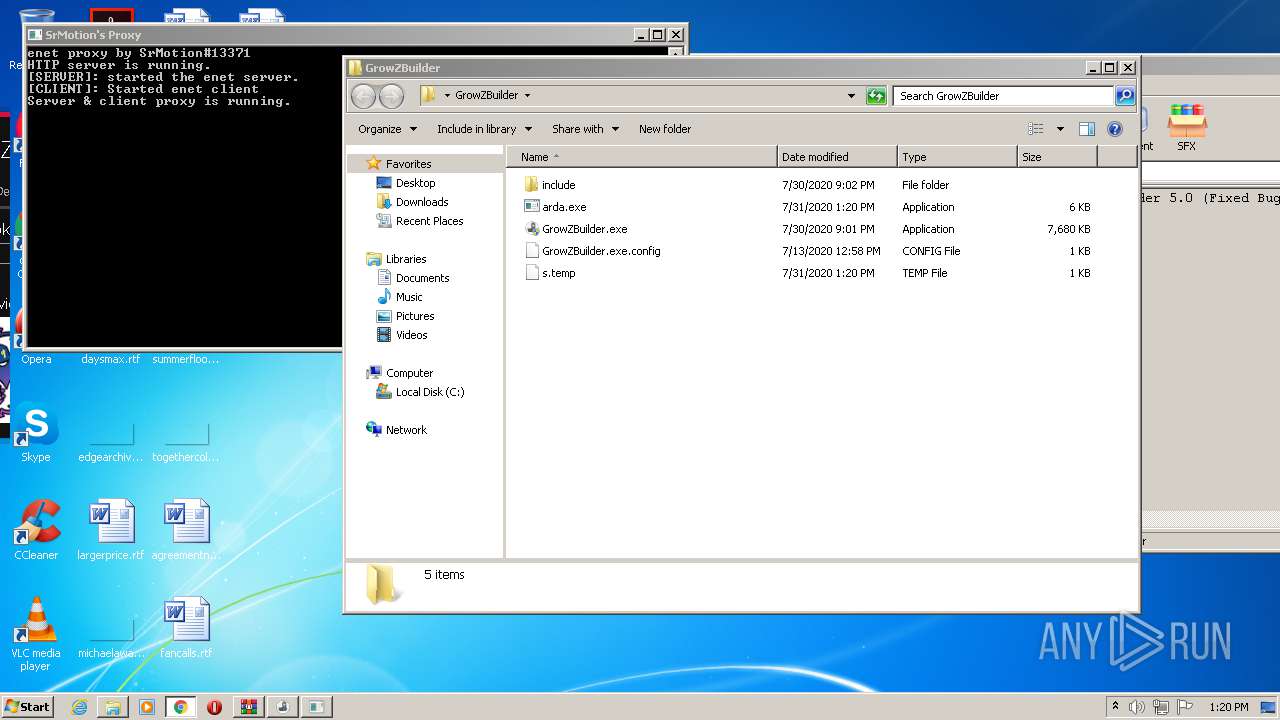
Executable content was dropped or overwritten
- GrowZBuilder.exe (PID: 3308)
- GrowZBuilder.exe (PID: 3816)
- csc.exe (PID: 3132)
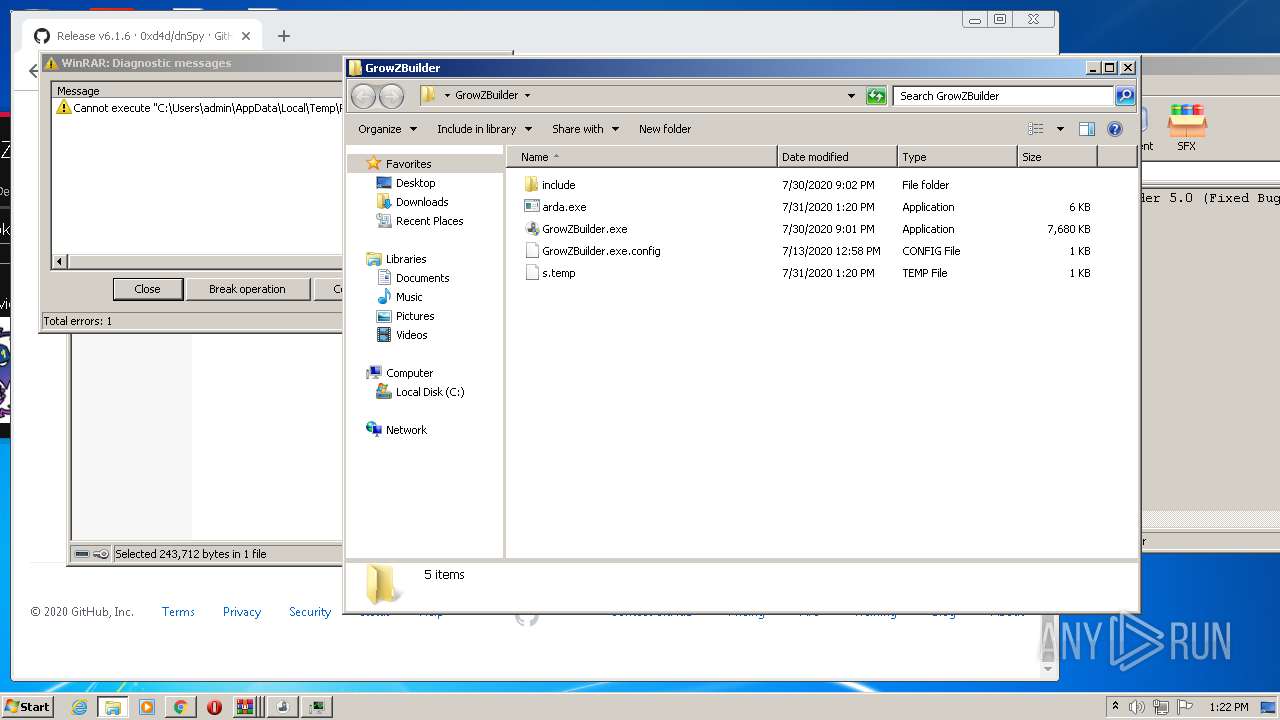
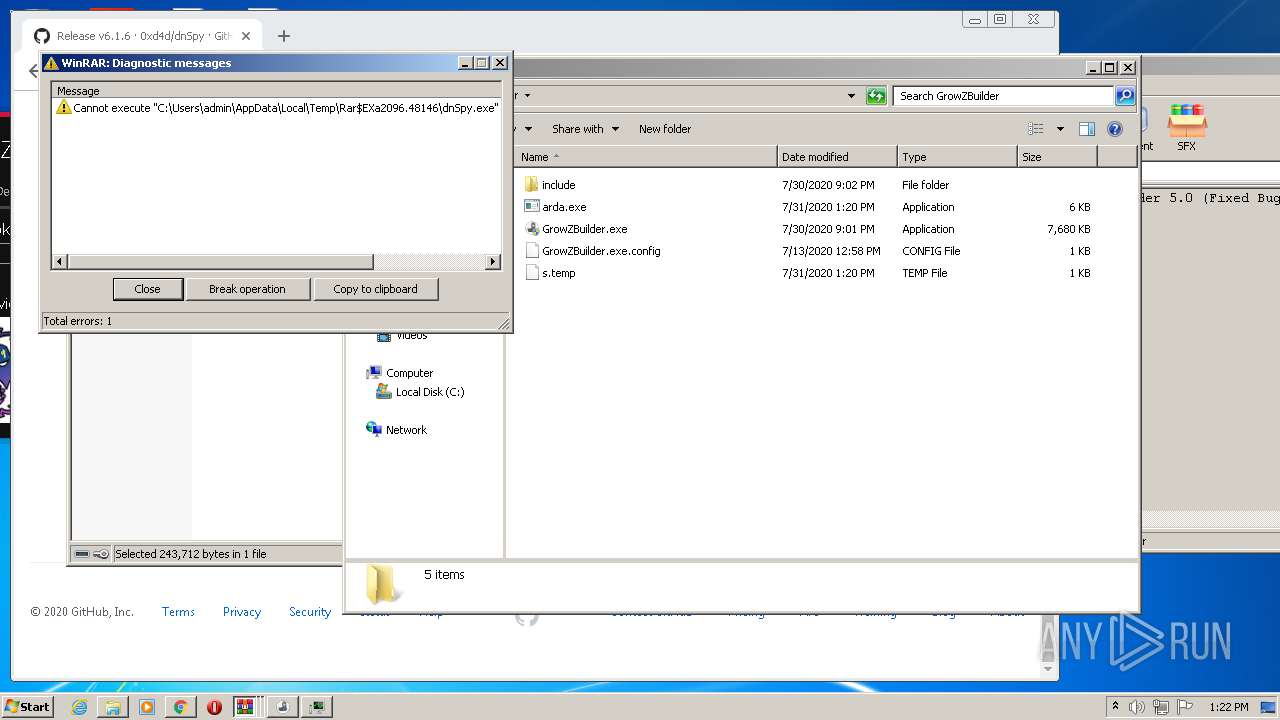
- WinRAR.exe (PID: 2096)
Adds / modifies Windows certificates
- SettingSyncHost.exe (PID: 1516)
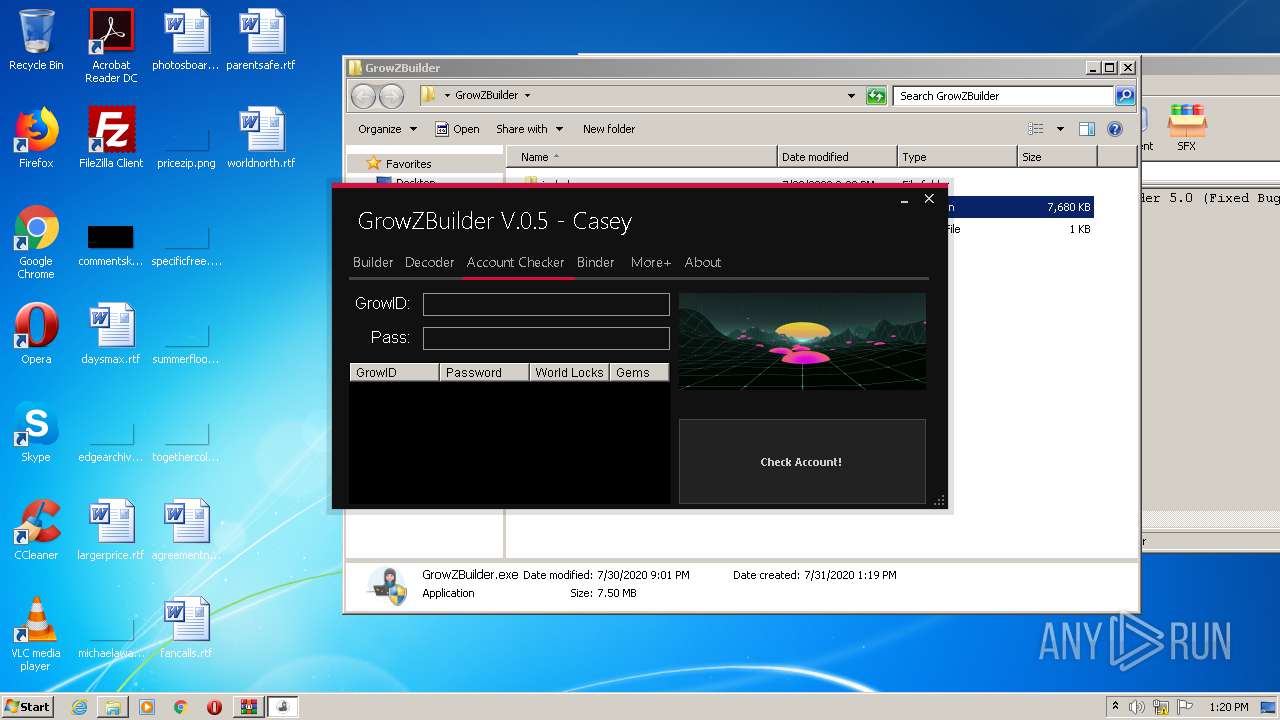
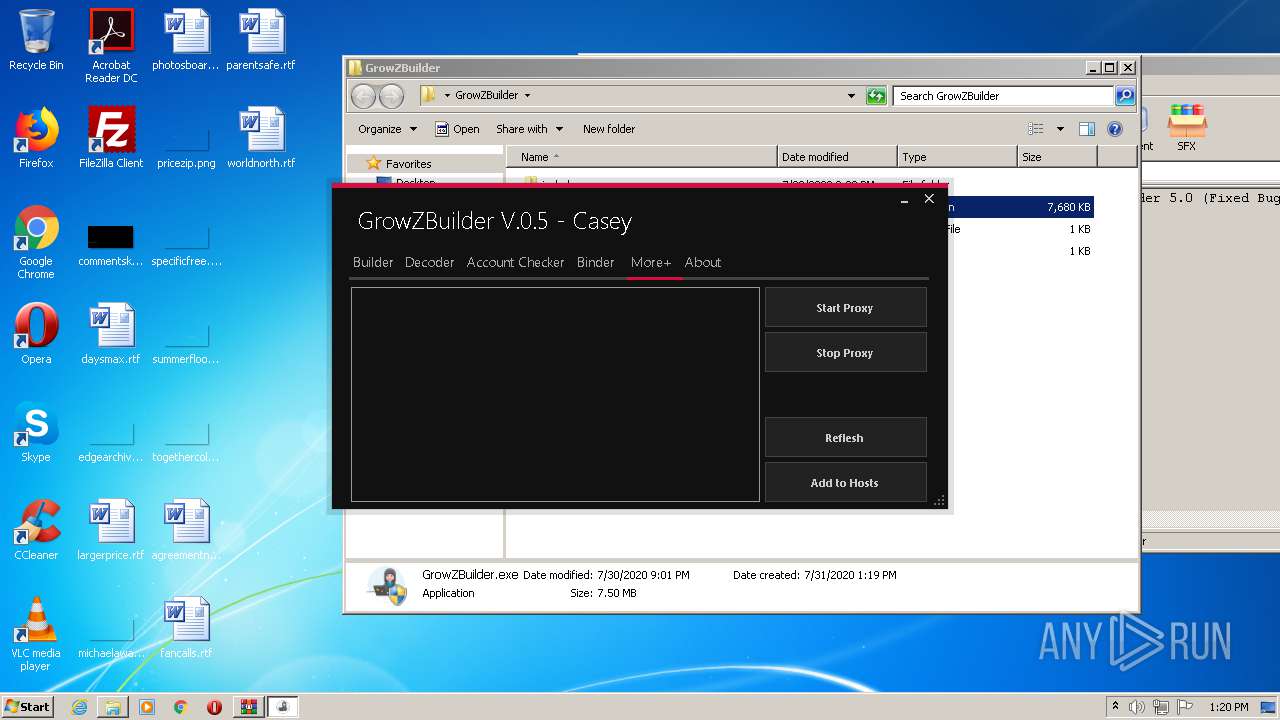
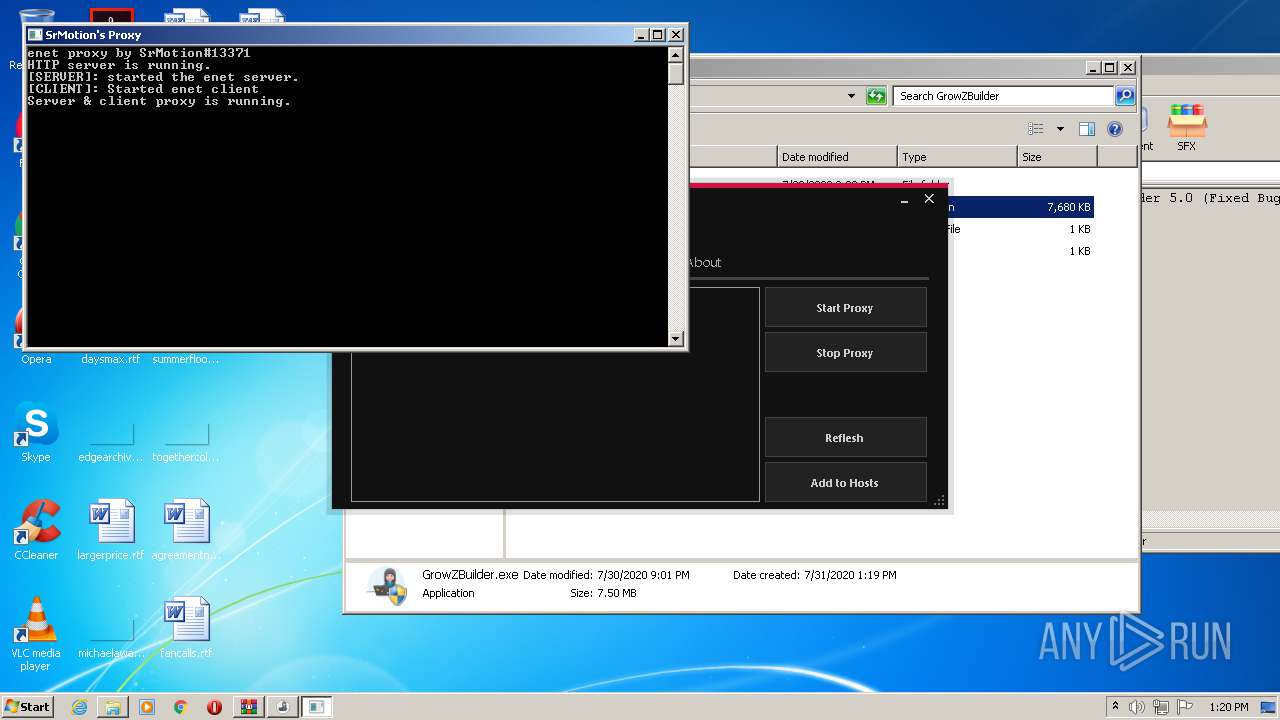
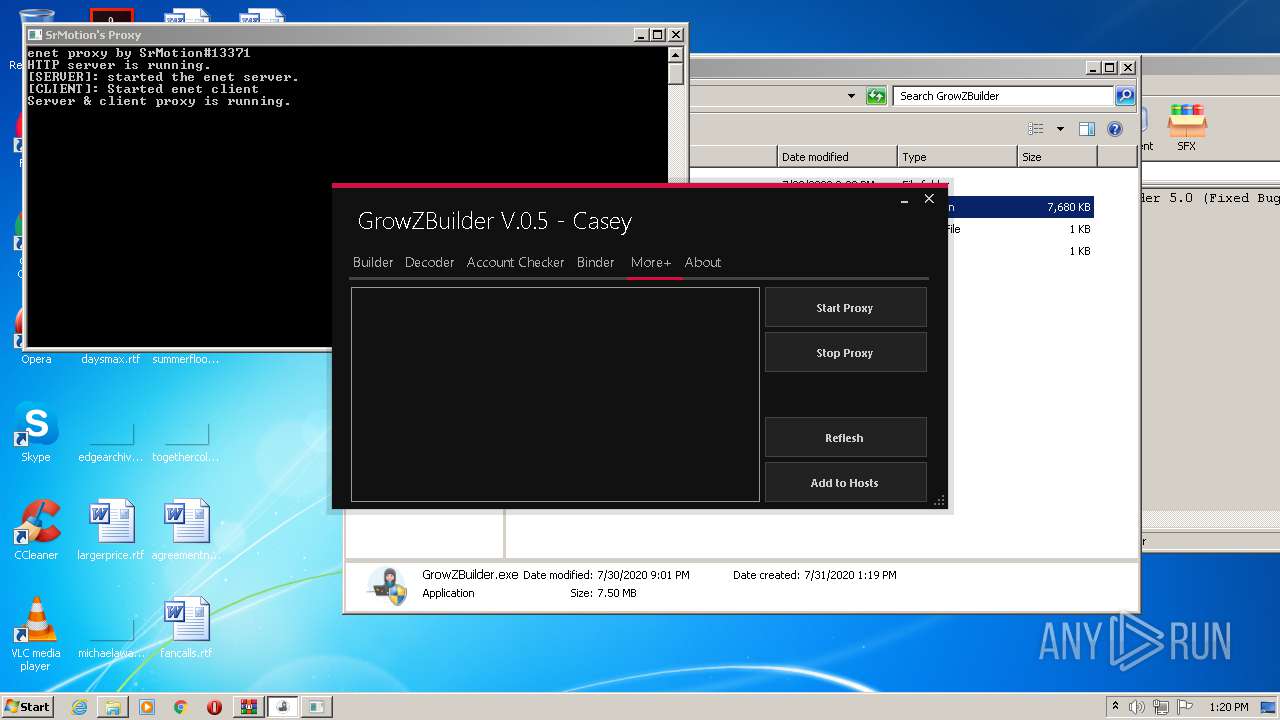
Checks for external IP
- SettingSyncHost.exe (PID: 1516)
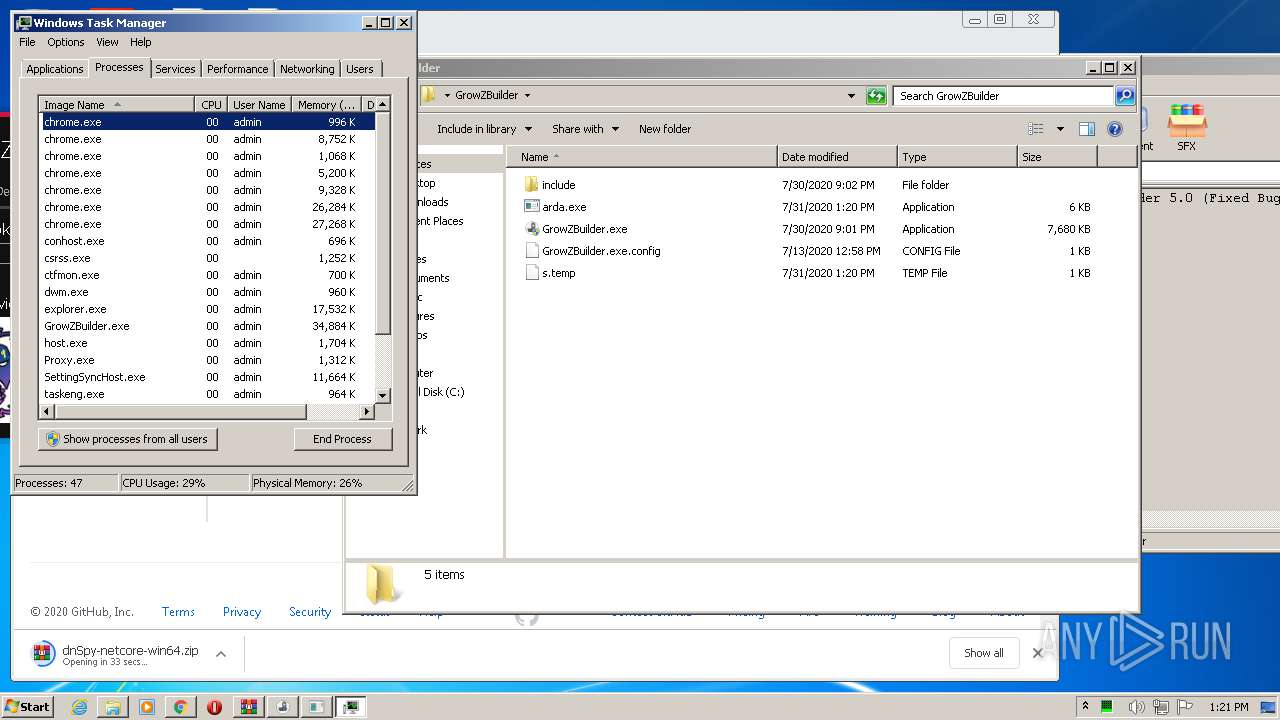
INFO
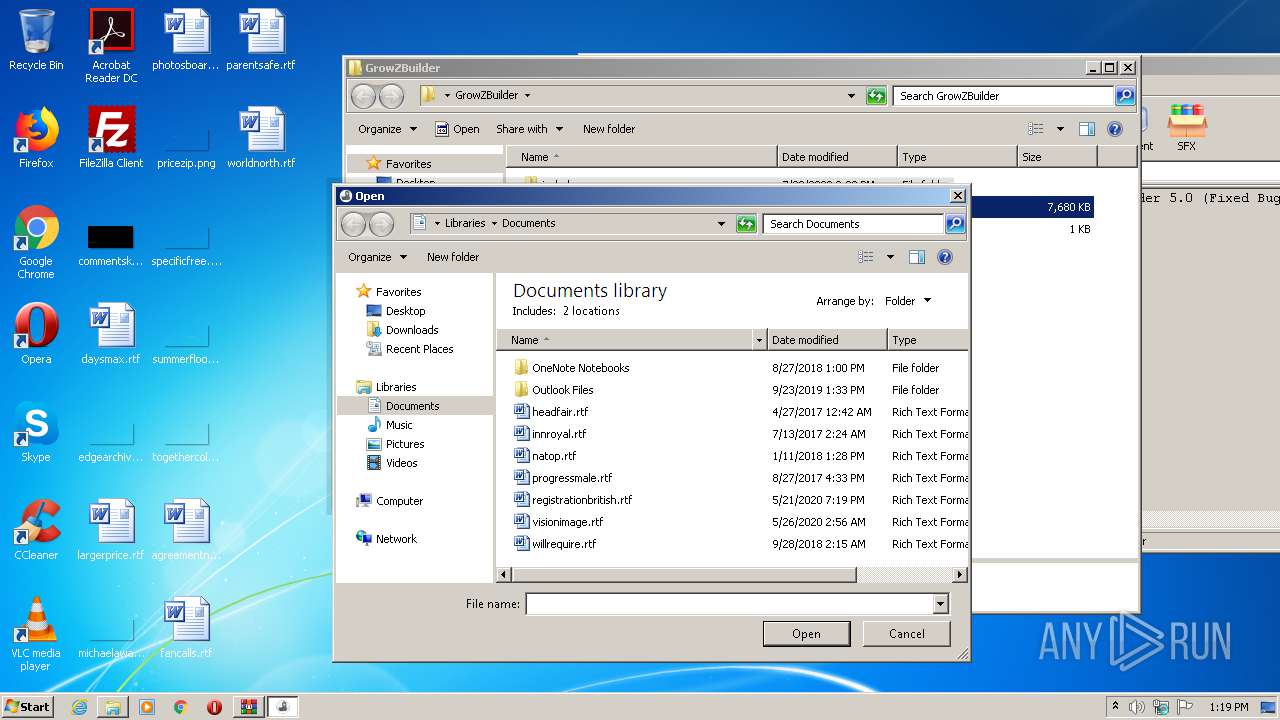
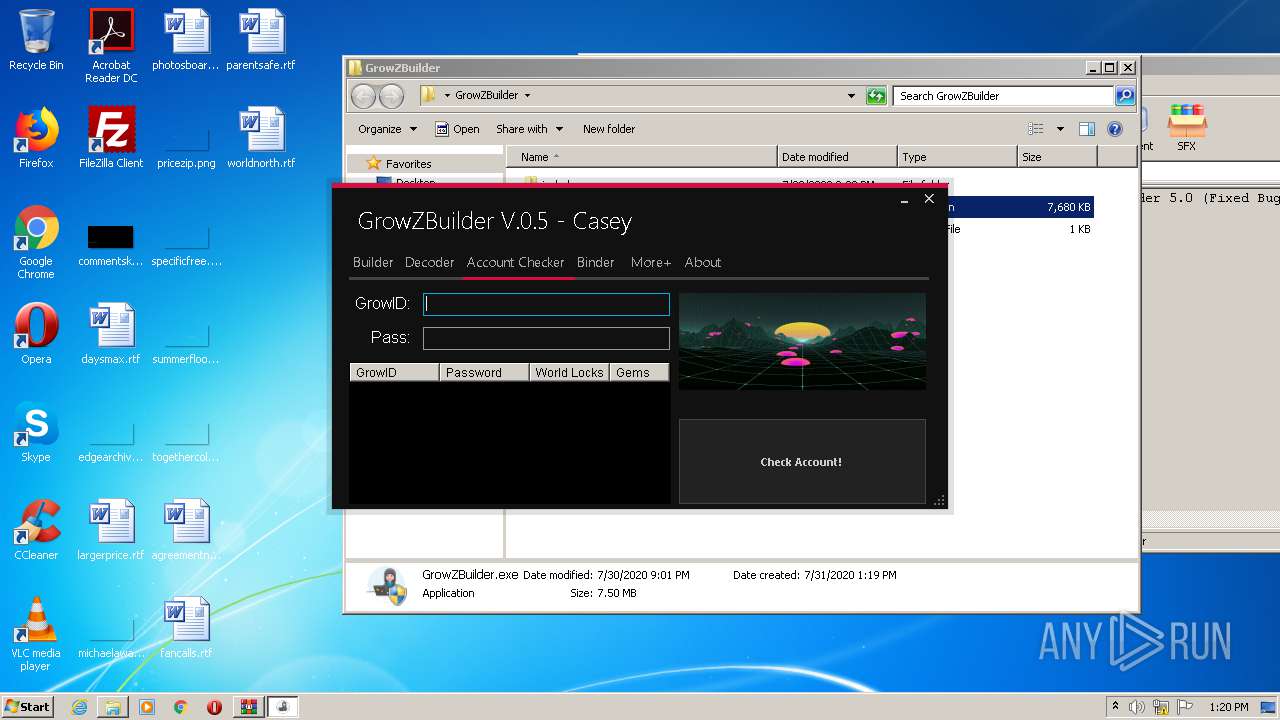
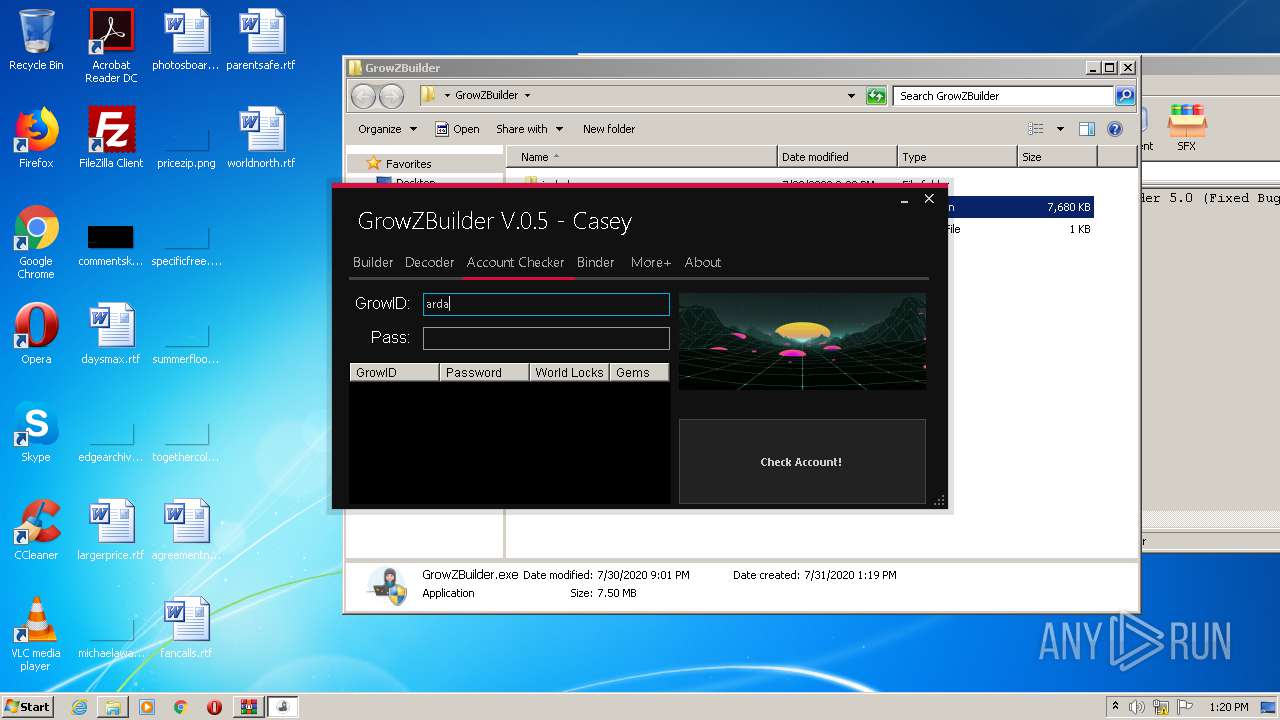
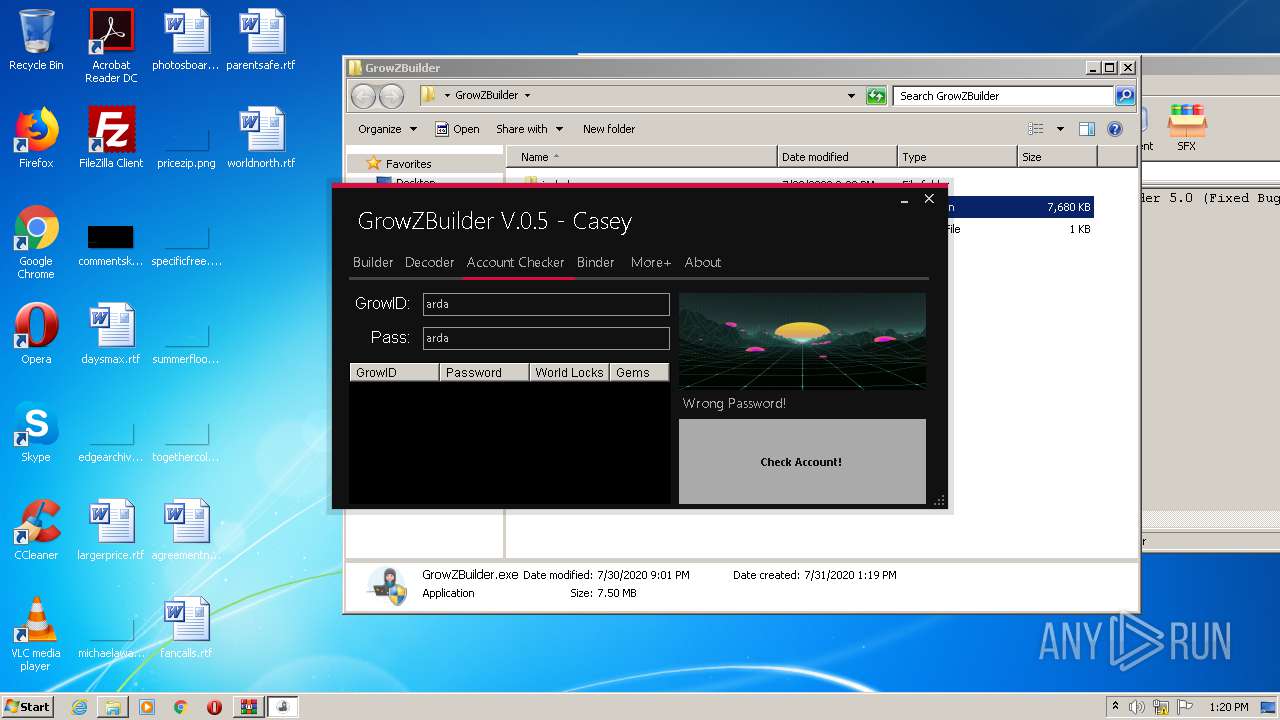
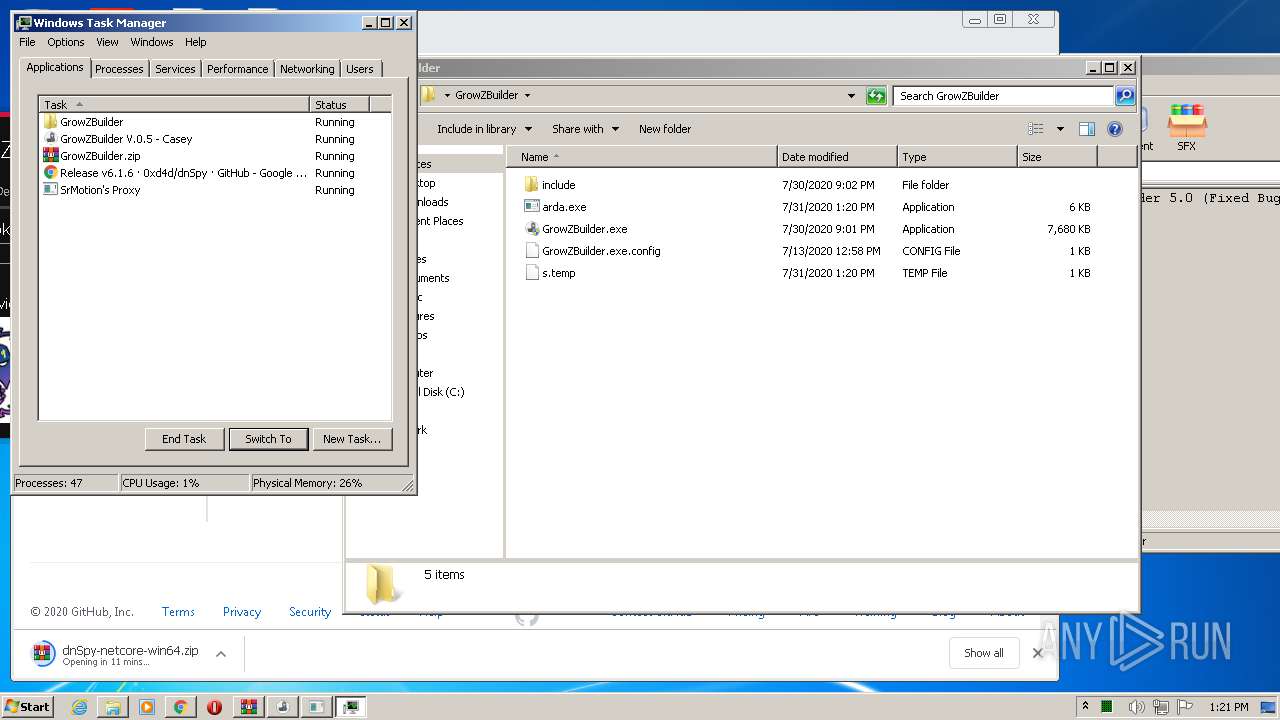
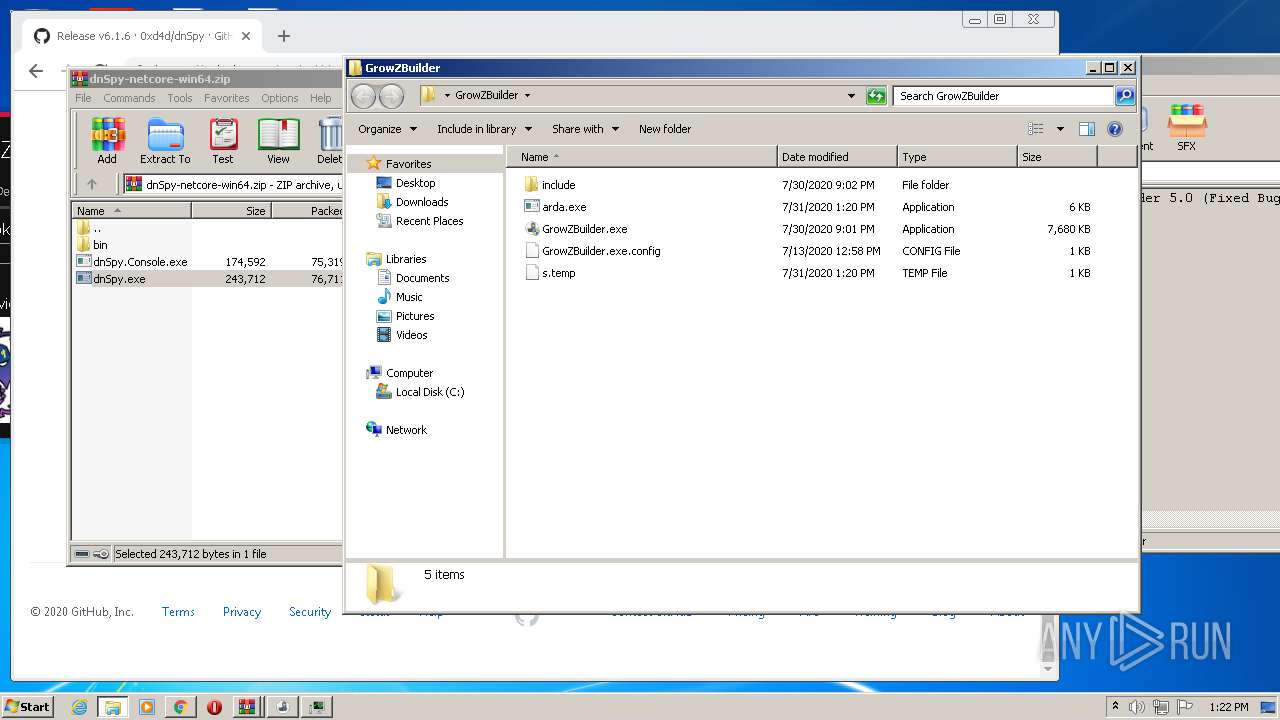
Manual execution by user
- GrowZBuilder.exe (PID: 2584)
- GrowZBuilder.exe (PID: 3308)
- chrome.exe (PID: 3040)
- taskmgr.exe (PID: 3716)
Reads the hosts file
- chrome.exe (PID: 3040)
- chrome.exe (PID: 2312)
Application launched itself
- chrome.exe (PID: 3040)
Reads settings of System Certificates
- chrome.exe (PID: 2312)
Reads Internet Cache Settings
- chrome.exe (PID: 3040)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 2096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2020:07:30 23:02:12 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | GrowZBuilder/ |
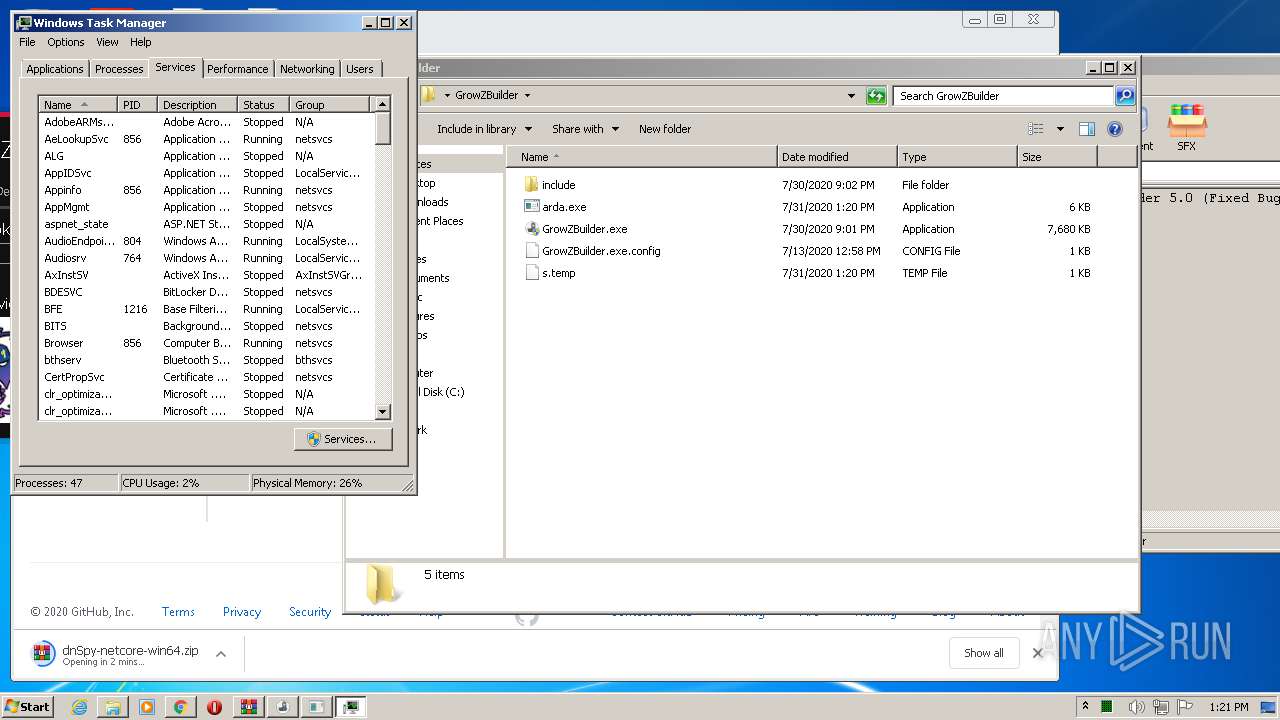
Total processes
78
Monitored processes
31
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,13406324713067582549,5466167442611071974,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13159601546352460948 --mojo-platform-channel-handle=1176 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,13406324713067582549,5466167442611071974,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=325534687609469573 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2444 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x69d5a9d0,0x69d5a9e0,0x69d5a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,13406324713067582549,5466167442611071974,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11431979351863658347 --mojo-platform-channel-handle=3420 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,13406324713067582549,5466167442611071974,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3160831078349017674 --mojo-platform-channel-handle=1004 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
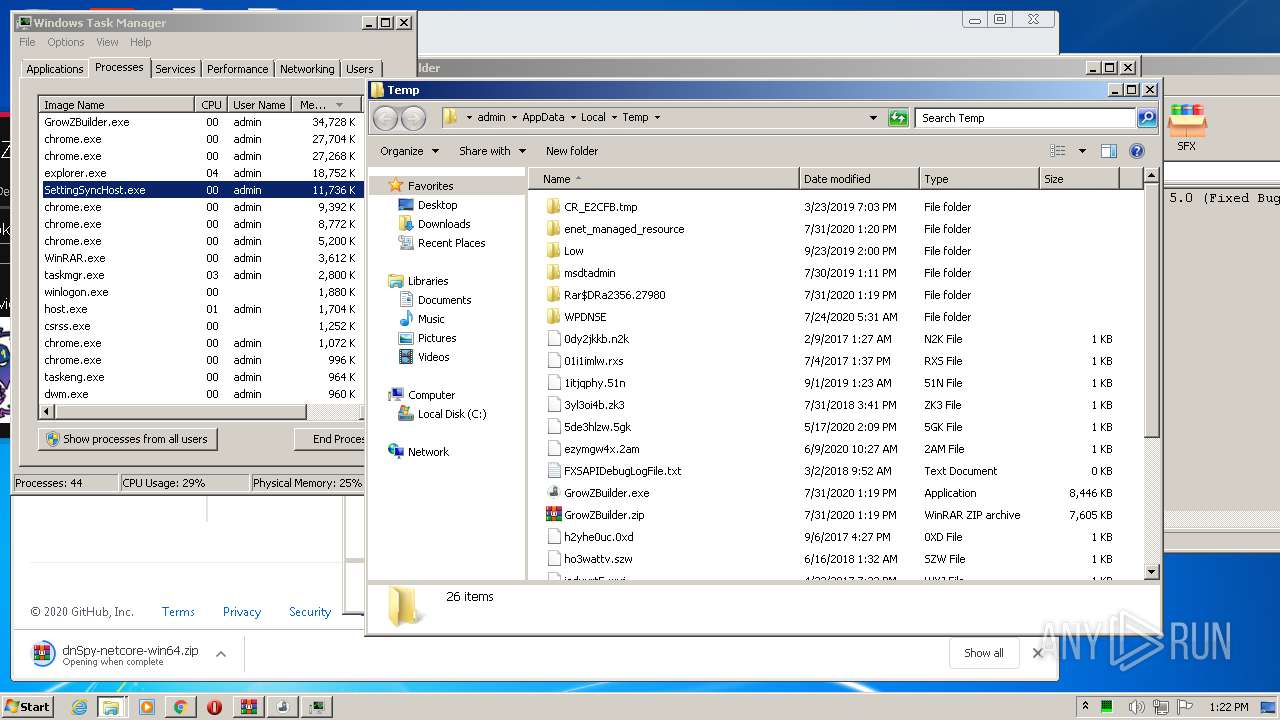
| 1516 | "C:\Users\admin\AppData\Local\Temp\SettingSyncHost.exe" | C:\Users\admin\AppData\Local\Temp\SettingSyncHost.exe | GrowZBuilder.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Setting Synchronization Exit code: 0 Version: 10.0.18362.239 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,13406324713067582549,5466167442611071974,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10716594499376323039 --mojo-platform-channel-handle=500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1008 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
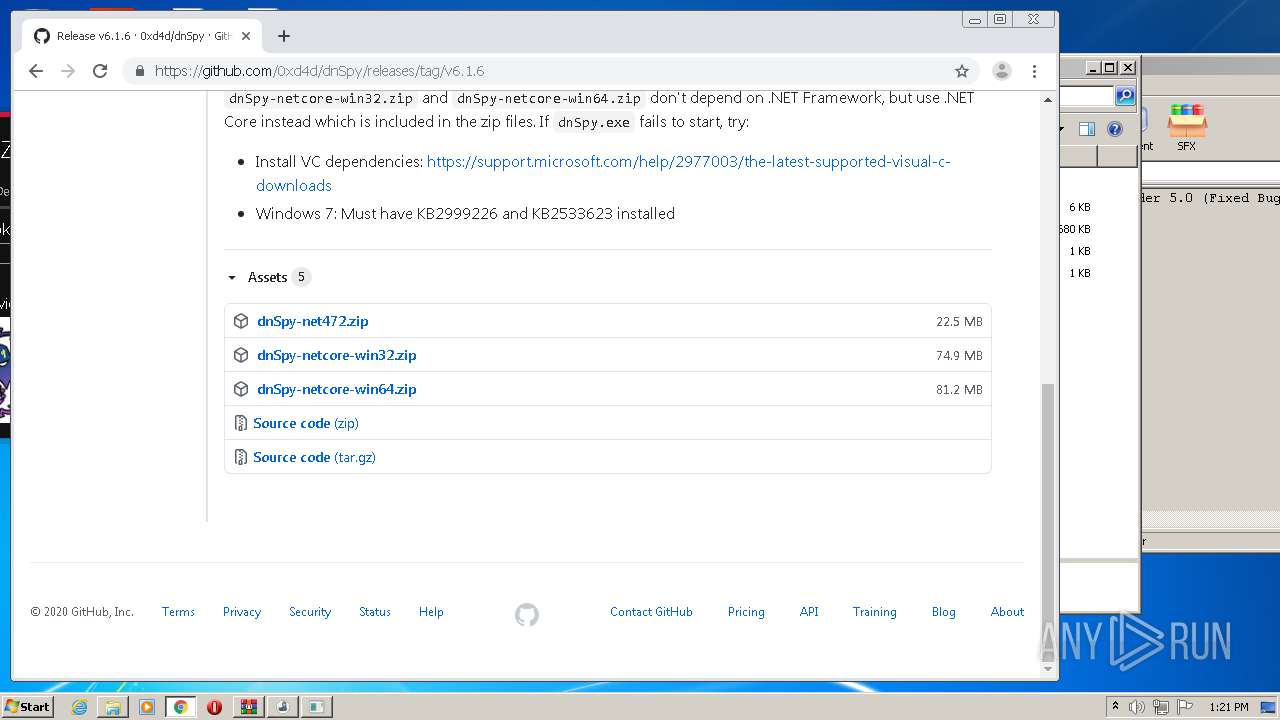
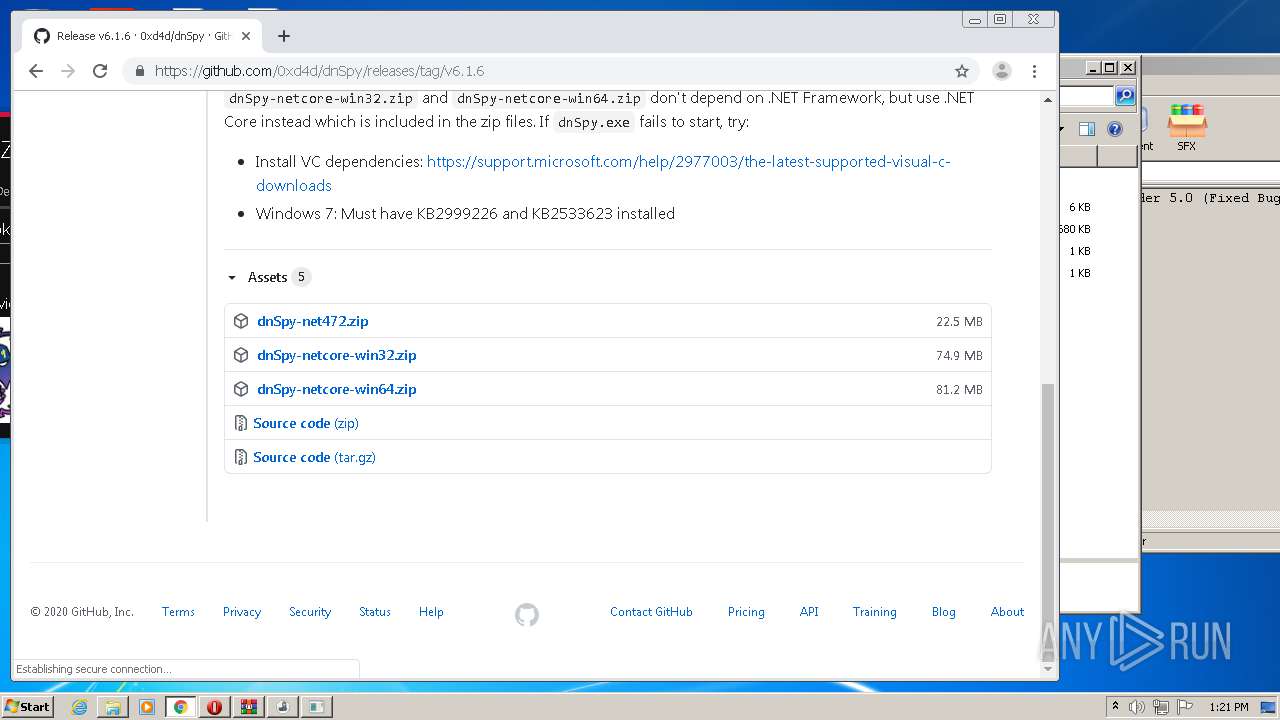
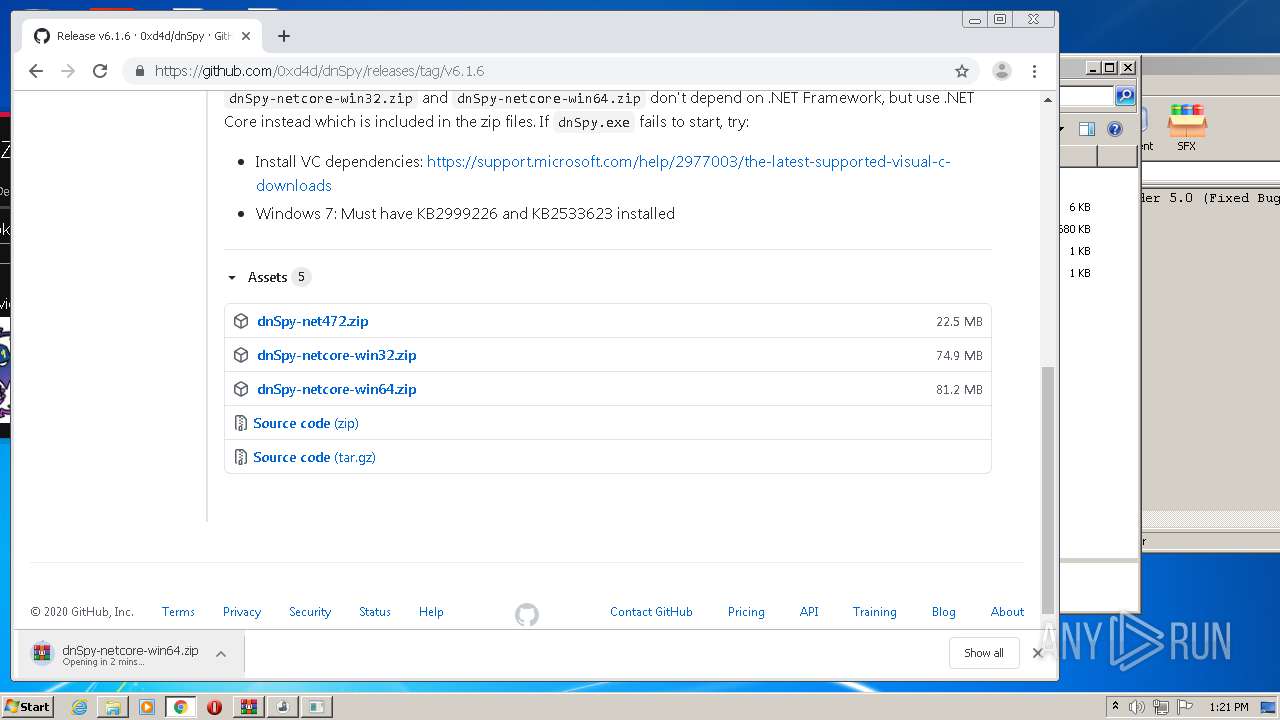
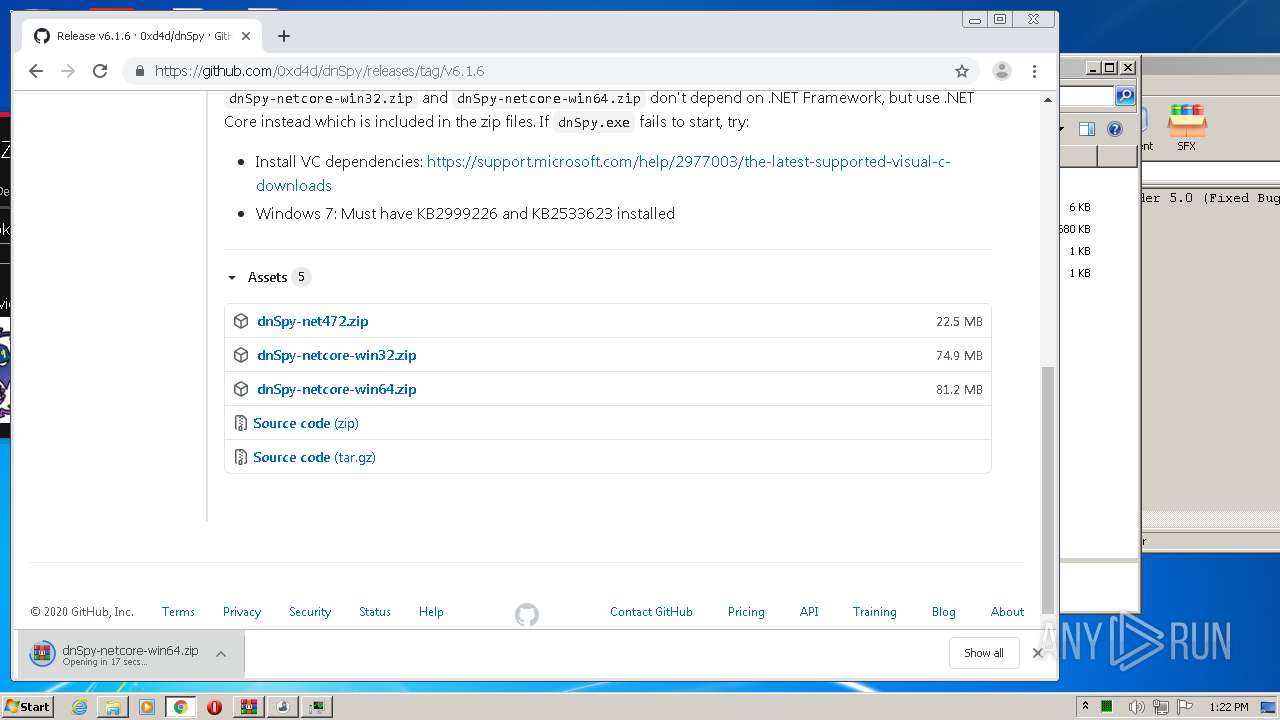
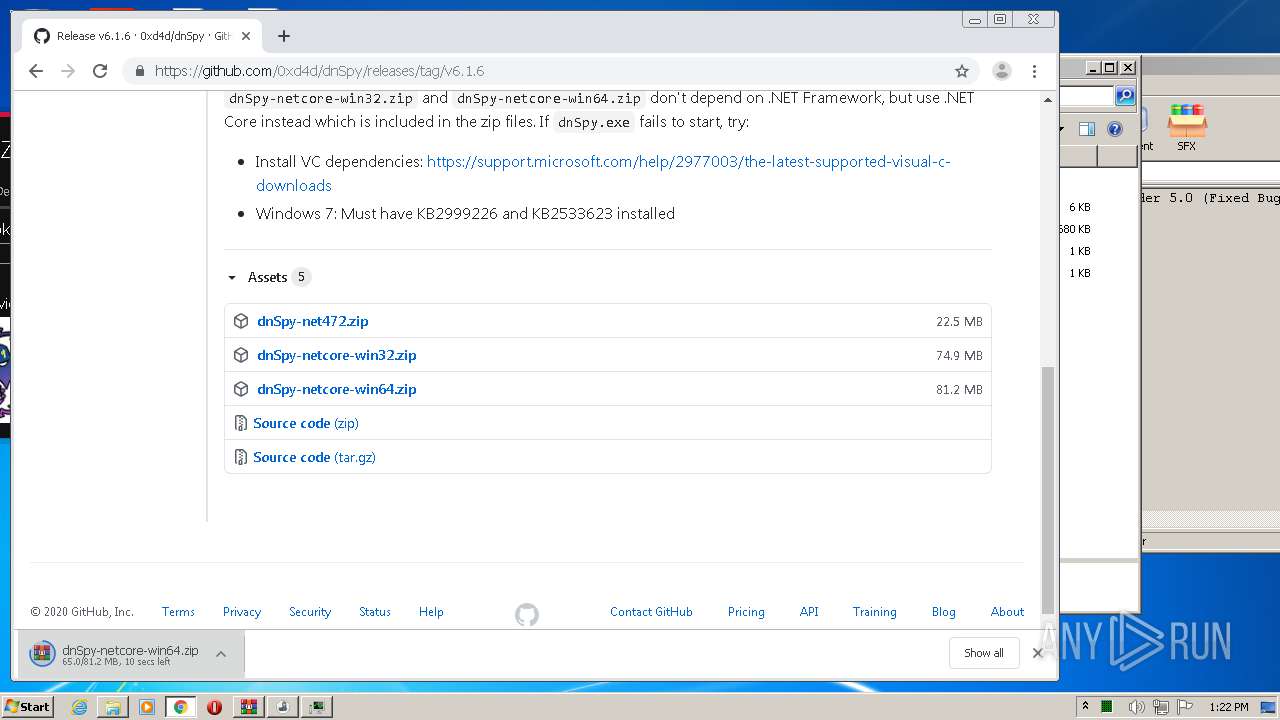
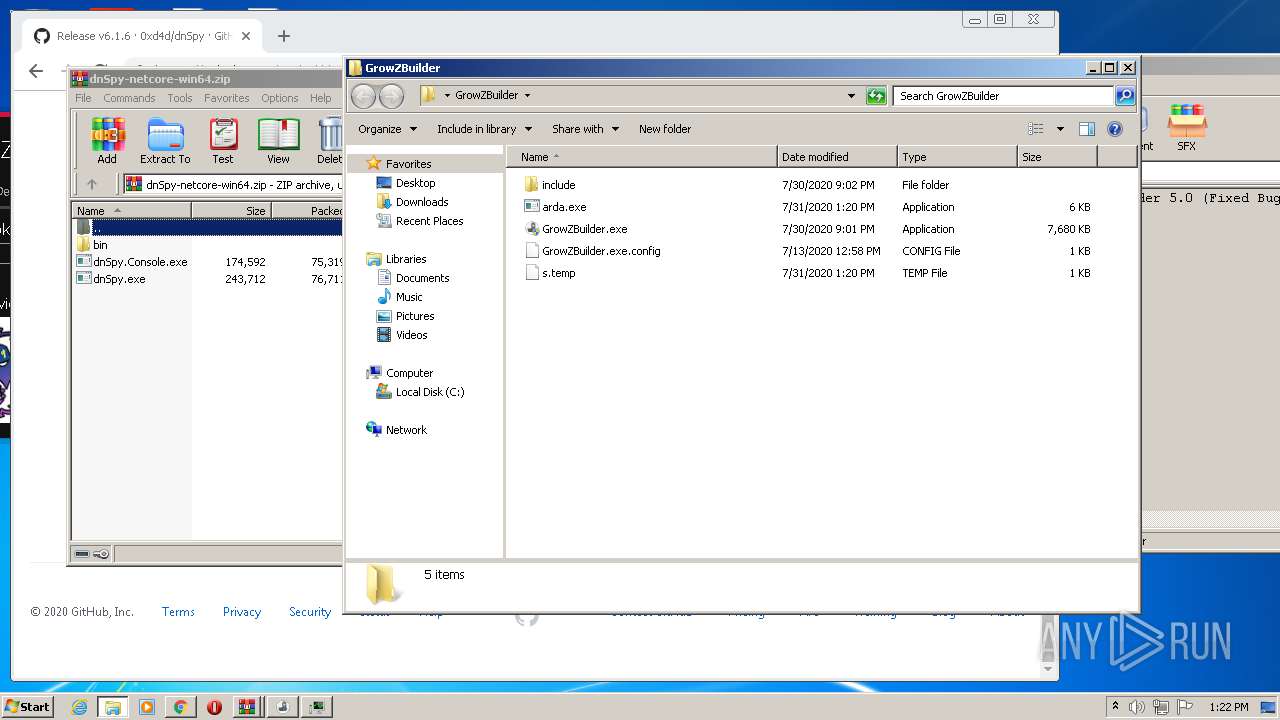
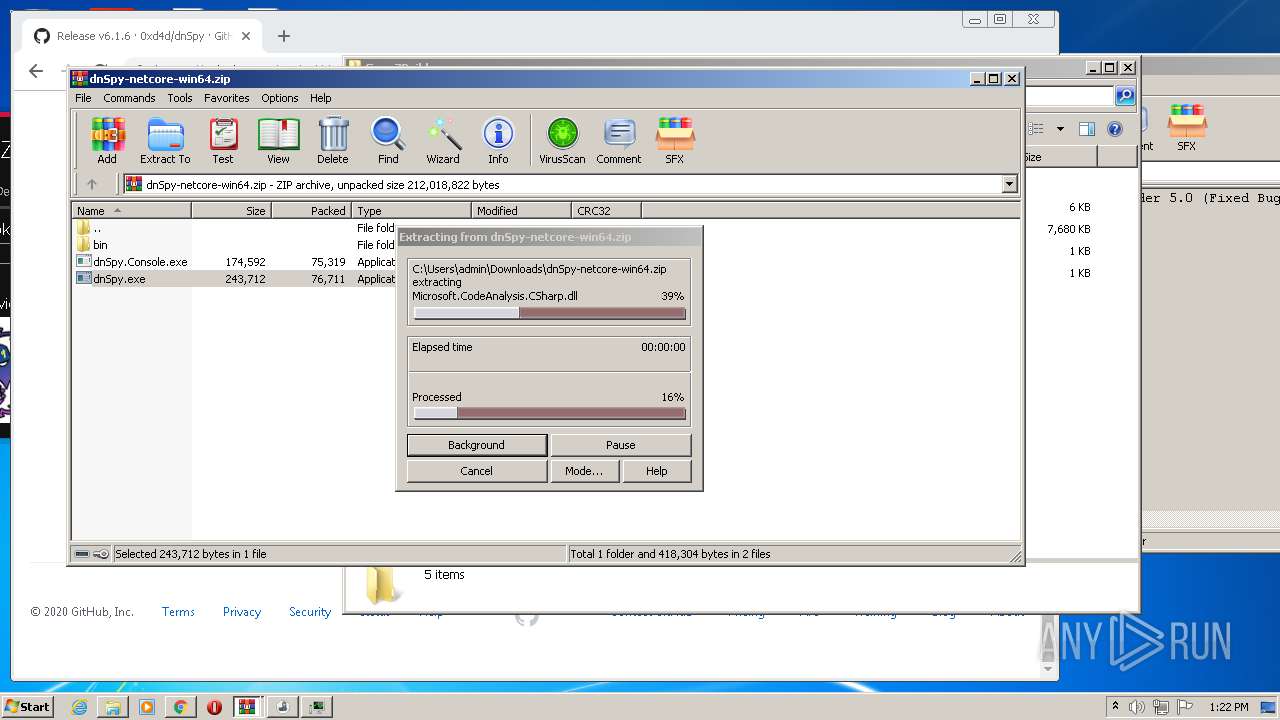
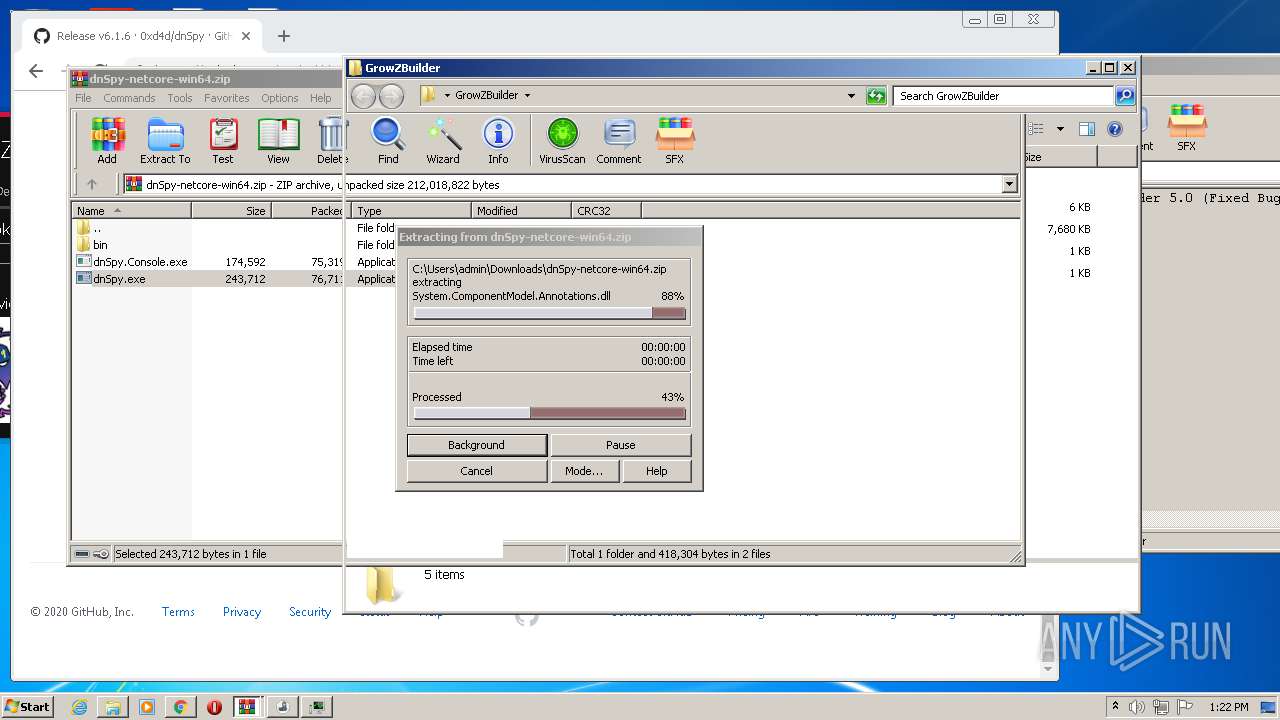
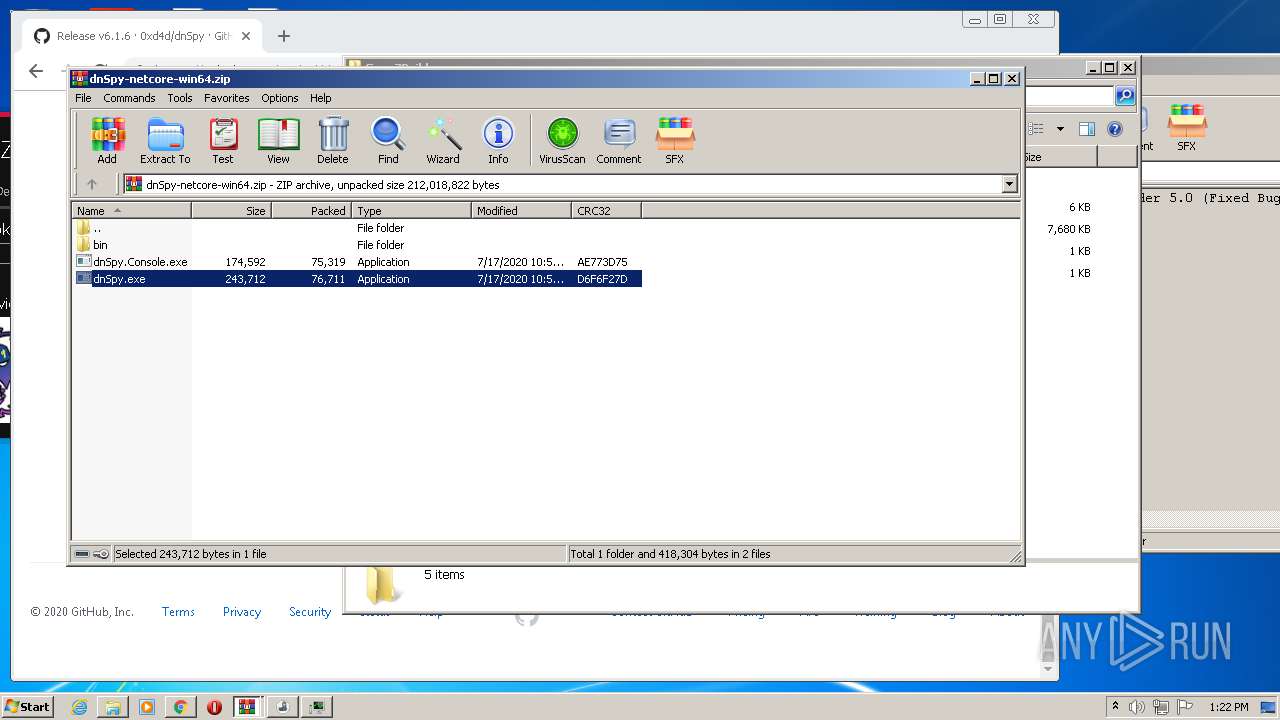
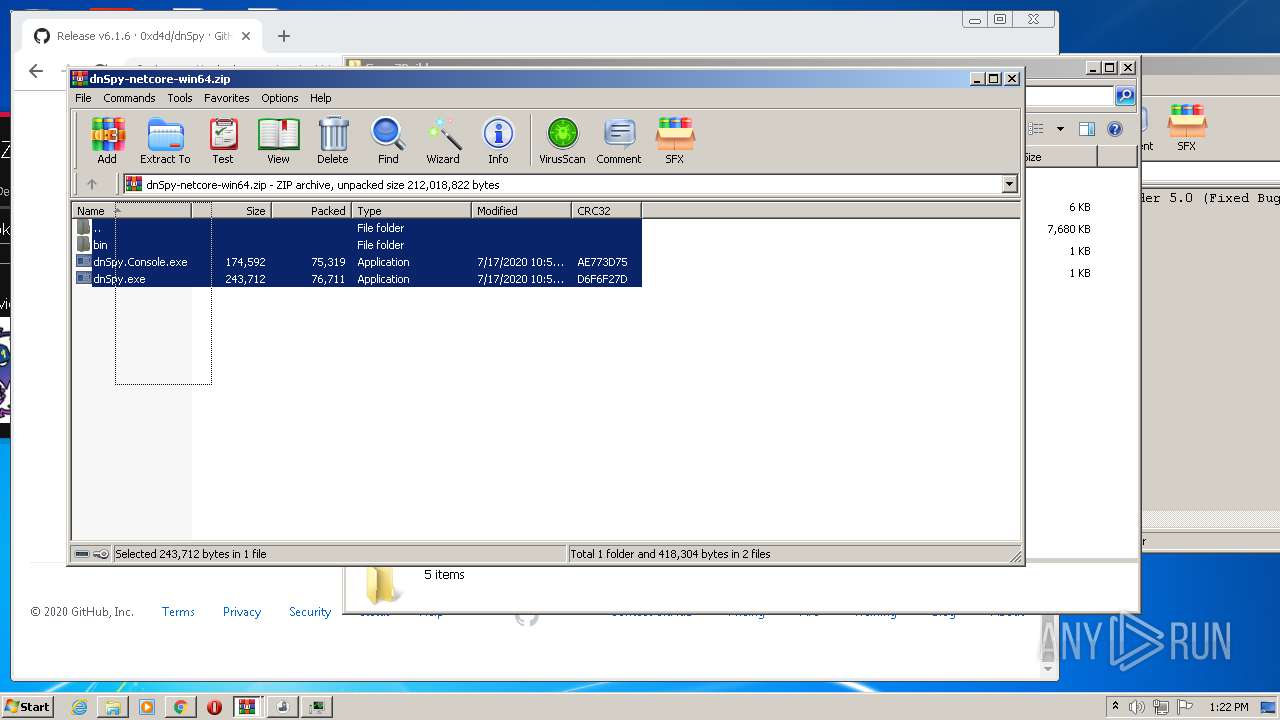
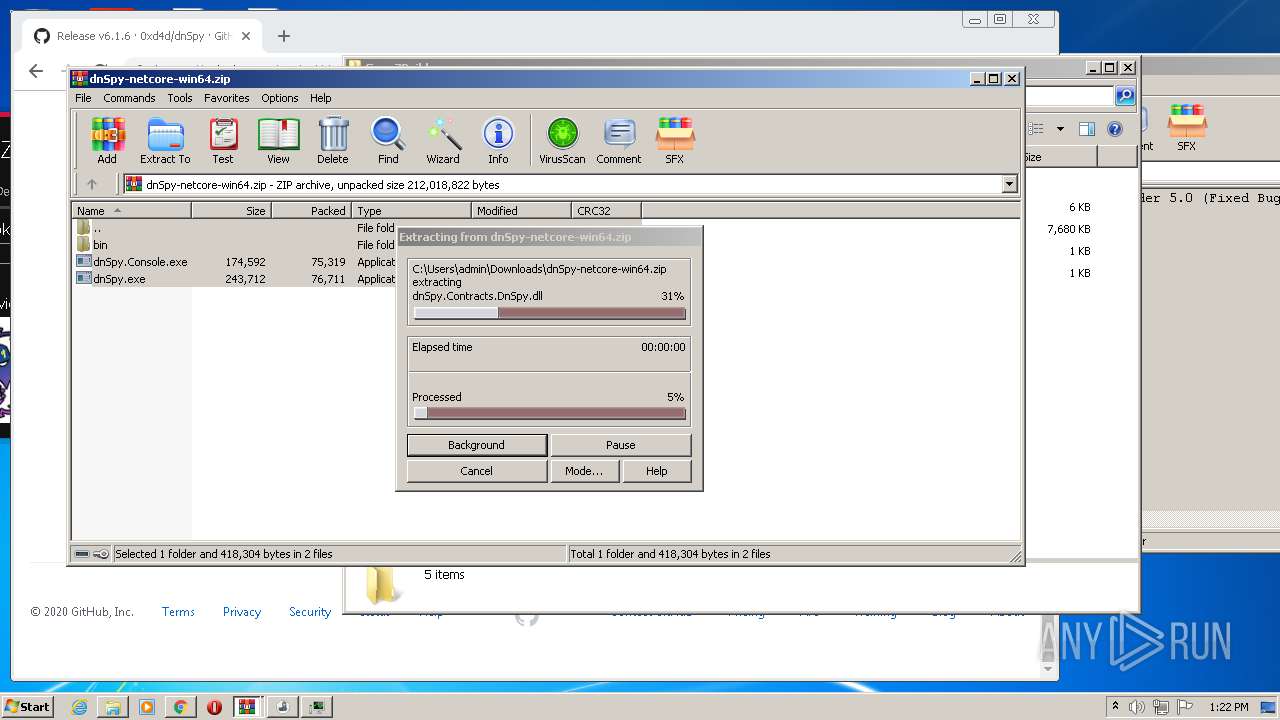
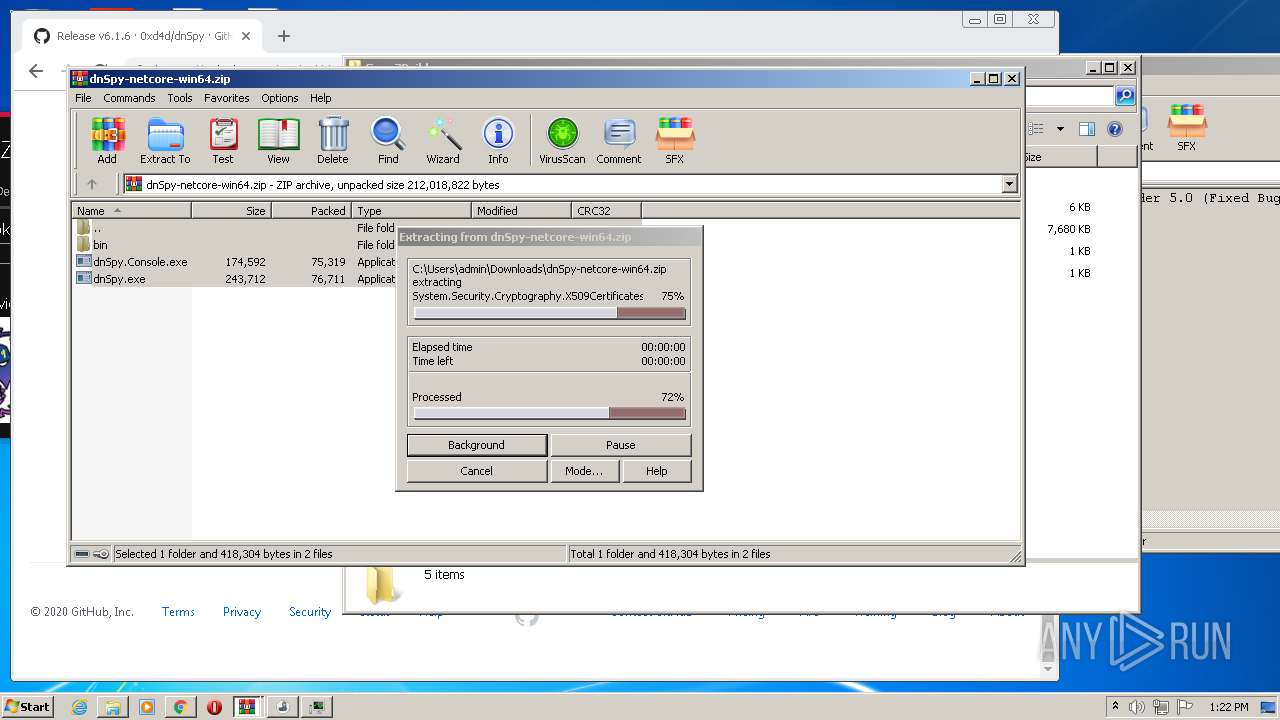
| 2096 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\dnSpy-netcore-win64.zip" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,13406324713067582549,5466167442611071974,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12807667195939759656 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3940 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 175
Read events
3 943
Write events
222
Delete events
10
Modification events
| (PID) Process: | (2356) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2356) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2356) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2356) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\GrowZBuilder.zip | |||
| (PID) Process: | (2356) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2356) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2356) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2356) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3308) GrowZBuilder.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3308) GrowZBuilder.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1 523
Suspicious files
133
Text files
164
Unknown types
4
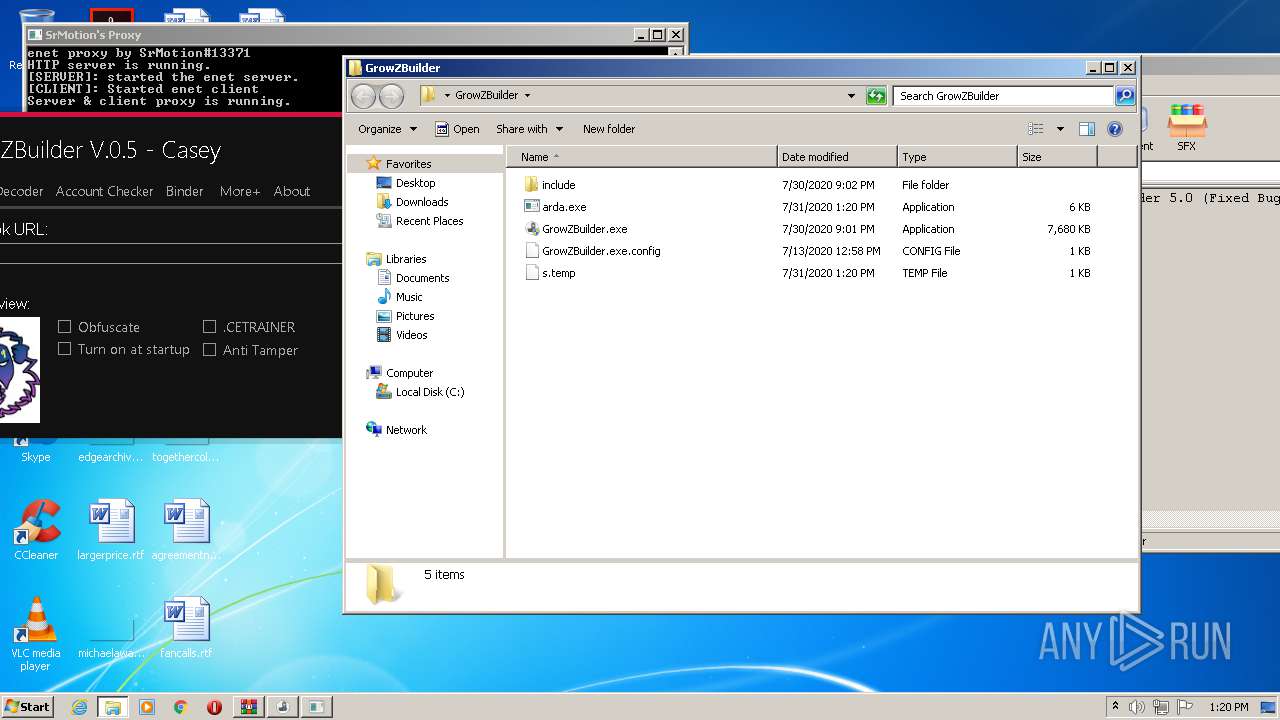
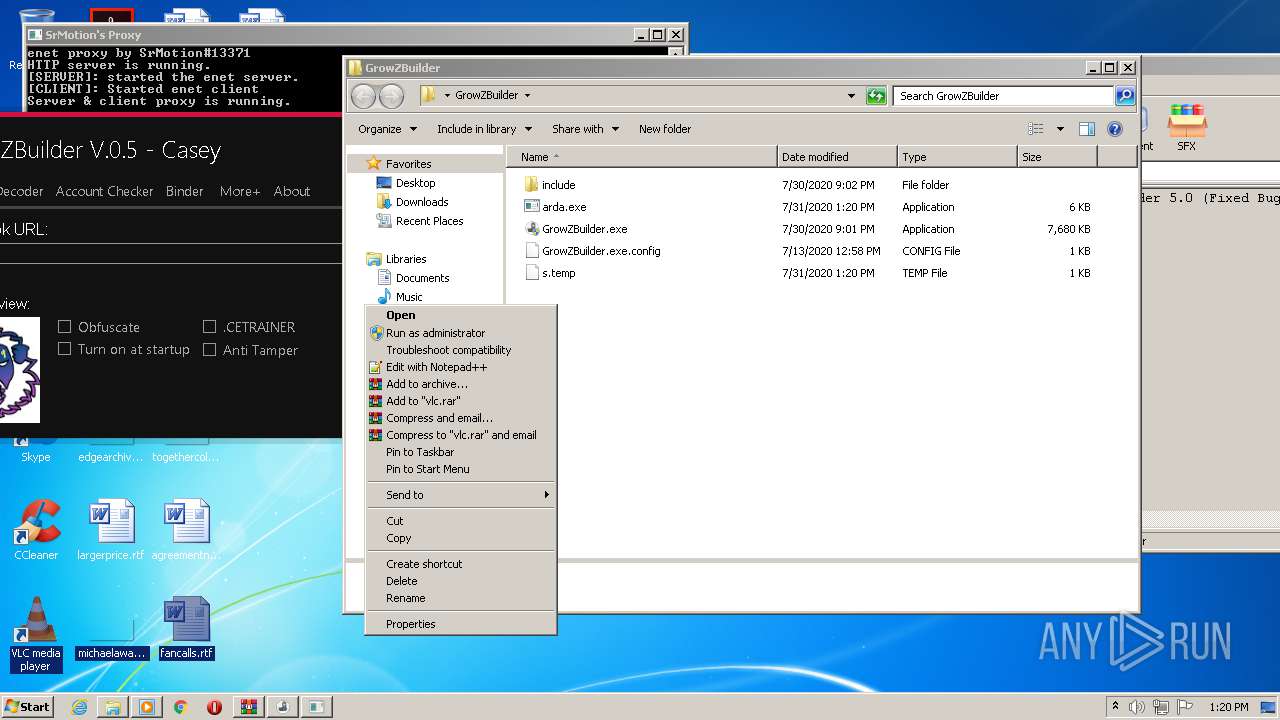
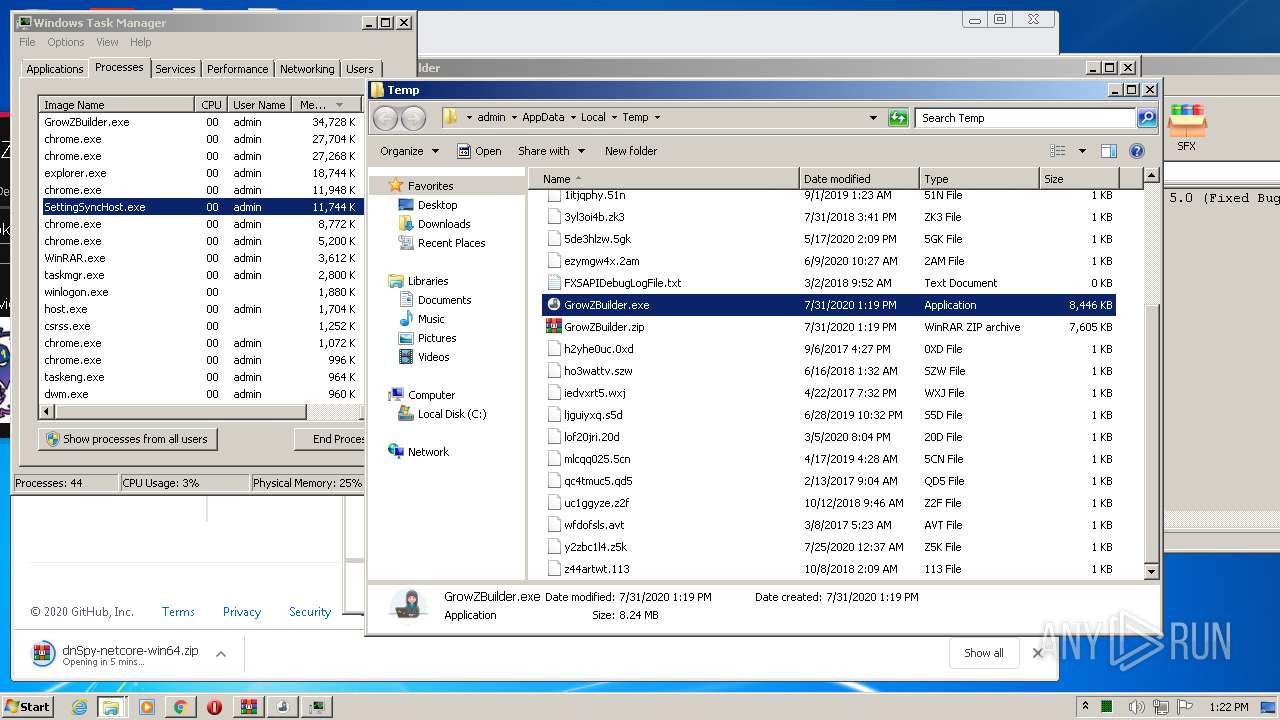
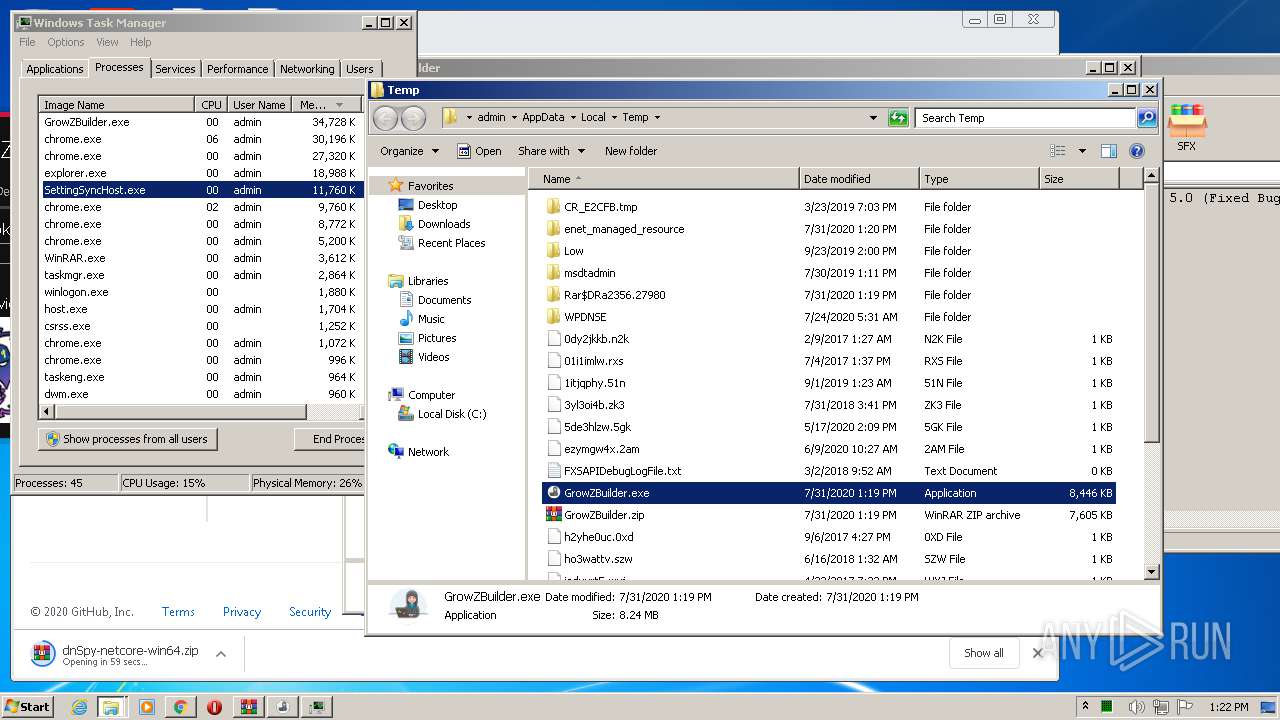
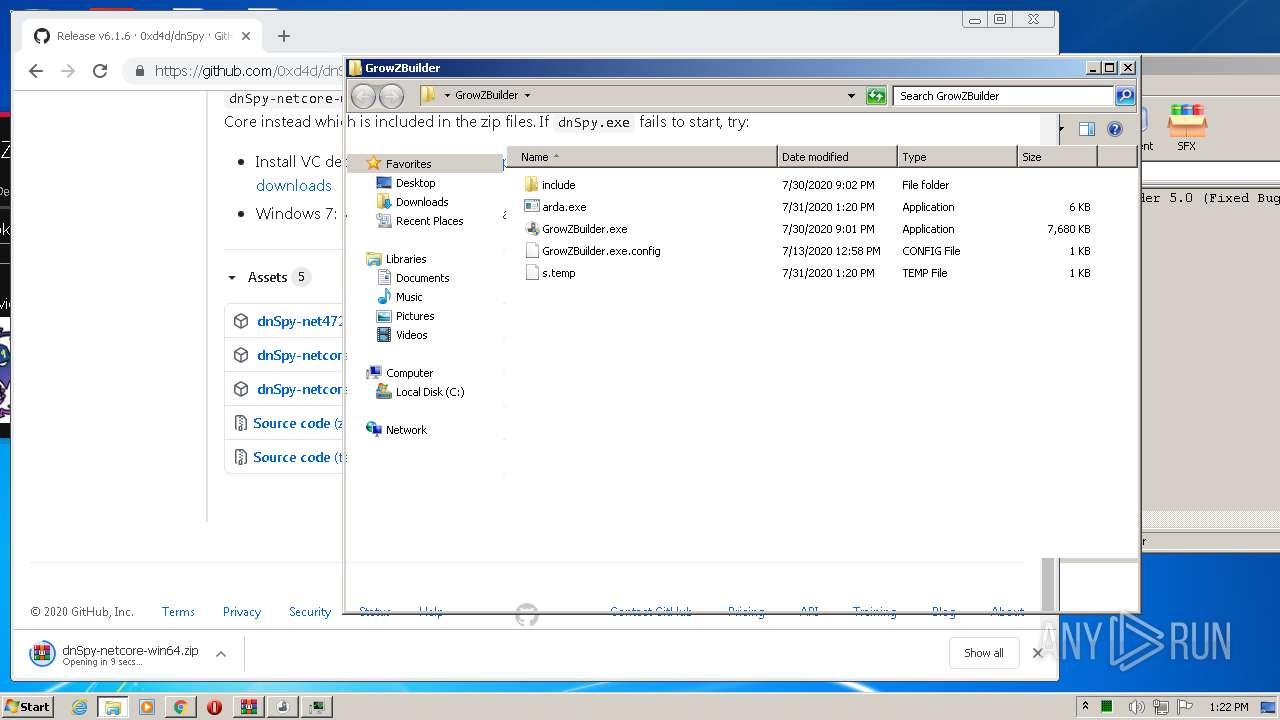
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
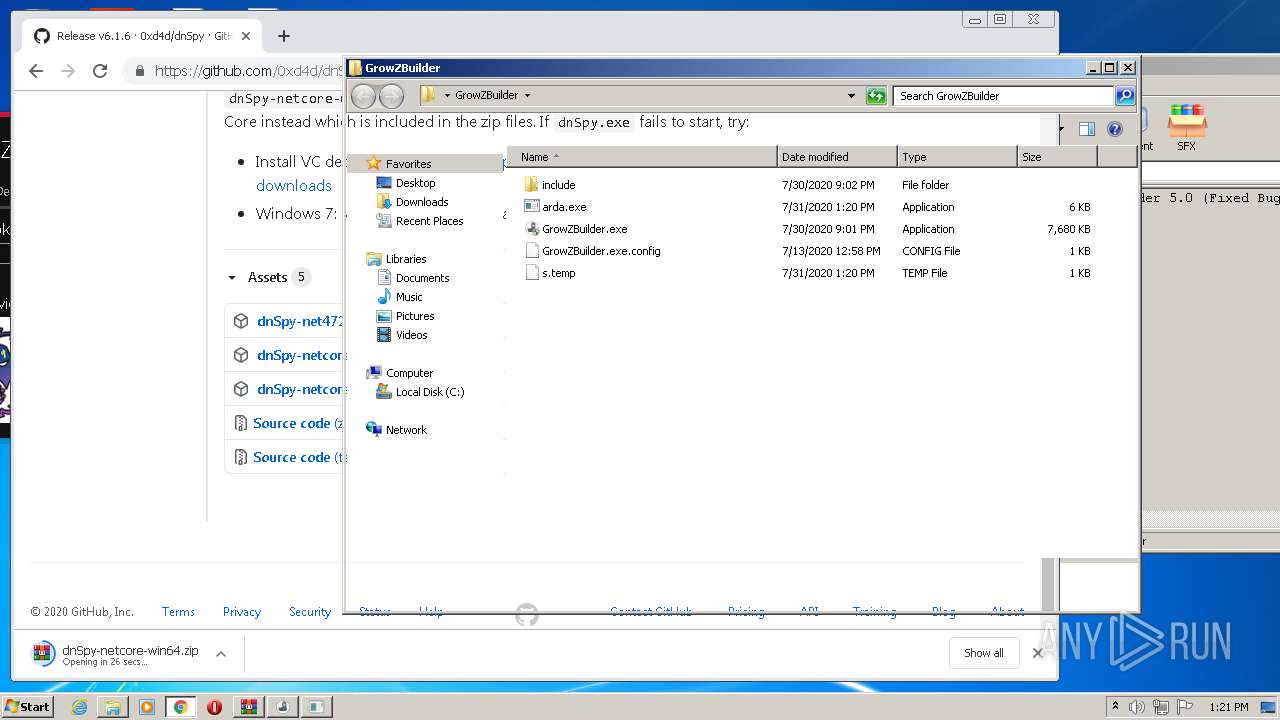
| 2356 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2356.27980\GrowZBuilder\GrowZBuilder.exe | — | |
MD5:— | SHA256:— | |||
| 2356 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2356.27980\GrowZBuilder\GrowZBuilder.exe.config | — | |
MD5:— | SHA256:— | |||
| 2356 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2356.27980\GrowZBuilder\include\Builder.CETRAINER | — | |
MD5:— | SHA256:— | |||
| 2356 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2356.27980\GrowZBuilder\include\Proxy.exe | — | |
MD5:— | SHA256:— | |||
| 3816 | GrowZBuilder.exe | C:\Users\admin\AppData\Local\Temp\ocaodo1y\ocaodo1y.0.cs | — | |
MD5:— | SHA256:— | |||
| 3816 | GrowZBuilder.exe | C:\Users\admin\AppData\Local\Temp\ocaodo1y\ocaodo1y.cmdline | — | |
MD5:— | SHA256:— | |||
| 3132 | csc.exe | C:\Users\admin\Desktop\GrowZBuilder\CSC159FBDE865804E77B95ACD7BC59110.TMP | — | |
MD5:— | SHA256:— | |||
| 2420 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RESF5E5.tmp | — | |
MD5:— | SHA256:— | |||
| 3132 | csc.exe | C:\Users\admin\AppData\Local\Temp\ocaodo1y\ocaodo1y.out | — | |
MD5:— | SHA256:— | |||
| 3040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\57335dfd-e574-4ba1-95e2-82b5e0ffa6e4.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
54
DNS requests
40
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1516 | SettingSyncHost.exe | GET | 200 | 116.202.244.153:80 | http://icanhazip.com/ | IN | text | 16 b | shared |
1516 | SettingSyncHost.exe | GET | 200 | 116.202.244.153:80 | http://icanhazip.com/ | IN | text | 16 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1516 | SettingSyncHost.exe | 116.202.244.153:80 | icanhazip.com | 334,Udyog Vihar | IN | malicious |
1516 | SettingSyncHost.exe | 172.67.214.70:443 | nusumu.wtf | — | US | malicious |
3816 | GrowZBuilder.exe | 213.179.209.168:17279 | — | i3D.net B.V | NL | unknown |
2312 | chrome.exe | 216.58.210.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2312 | chrome.exe | 172.217.22.4:443 | www.google.com | Google Inc. | US | whitelisted |
— | — | 216.58.210.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2312 | chrome.exe | 216.58.212.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2312 | chrome.exe | 172.217.18.110:443 | ogs.google.com | Google Inc. | US | whitelisted |
2312 | chrome.exe | 216.58.212.142:443 | apis.google.com | Google Inc. | US | whitelisted |
2312 | chrome.exe | 172.217.22.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
icanhazip.com |
| shared |
nusumu.wtf |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1516 | SettingSyncHost.exe | Attempted Information Leak | ET POLICY IP Check Domain (icanhazip. com in HTTP Host) |
1516 | SettingSyncHost.exe | Attempted Information Leak | ET POLICY IP Check Domain (icanhazip. com in HTTP Host) |