| File name: | LatiteClientbetter.exe |
| Full analysis: | https://app.any.run/tasks/9a20b611-0ad7-47be-8784-7e4c45729096 |
| Verdict: | Malicious activity |
| Threats: | XWorm is a remote access trojan (RAT) sold as a malware-as-a-service. It possesses an extensive hacking toolset and is capable of gathering private information and files from the infected computer, hijacking MetaMask and Telegram accounts, and tracking user activity. XWorm is typically delivered to victims' computers through multi-stage attacks that start with phishing emails. |
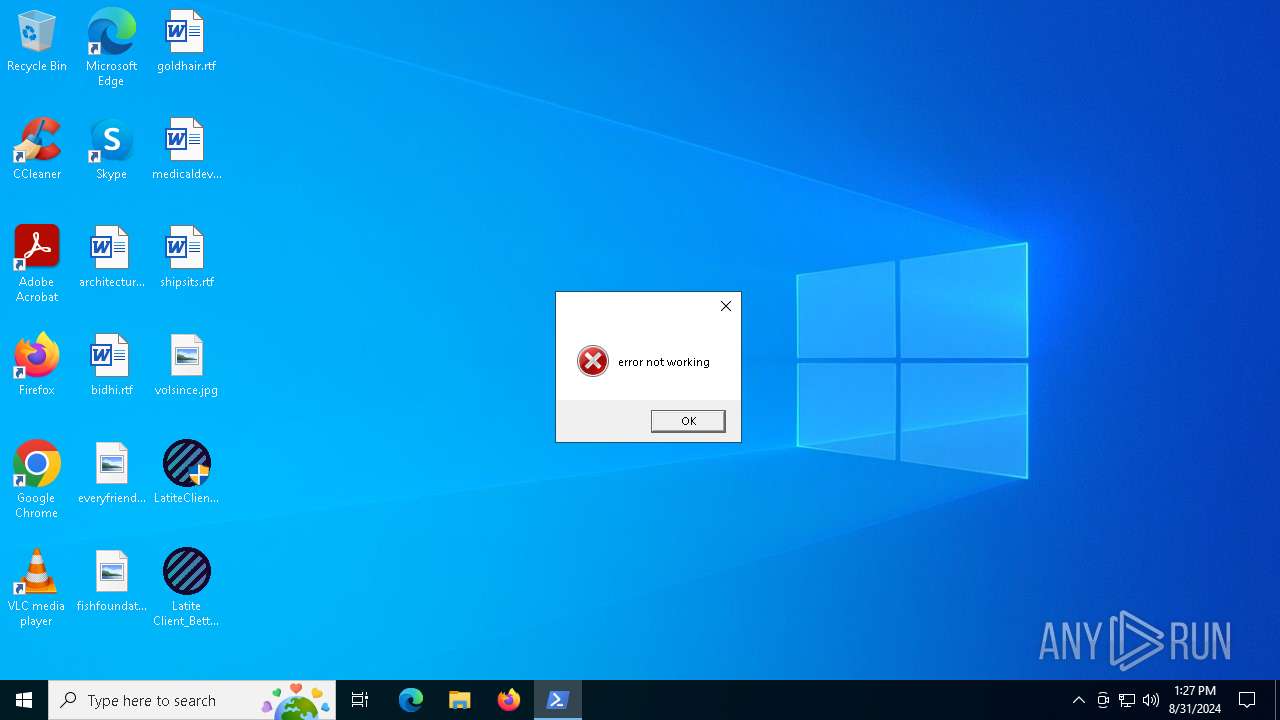
| Analysis date: | August 31, 2024, 13:27:36 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 20CE45B6E38C75A12BF724CDA0D8F358 |
| SHA1: | 64553397763B008F0C5264B72B23A6158EB66A07 |
| SHA256: | 06936FD3521A466EA38D410DA28420766A2531CD37E3F7C45EC630FB417A8484 |
| SSDEEP: | 6144:4GDbbZxbV2Ayp37tOcKW2H7ZPUl9EpJB:4GDHbQAKQdH7ZPfp |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 4824)
- powershell.exe (PID: 5400)
- powershell.exe (PID: 2016)
- powershell.exe (PID: 6404)
- powershell.exe (PID: 1168)
- powershell.exe (PID: 5532)
- powershell.exe (PID: 5704)
Adds process to the Windows Defender exclusion list
- Latite Client_BetterV3.exe (PID: 5940)
Changes powershell execution policy (Bypass)
- Latite Client_BetterV3.exe (PID: 5940)
Adds path to the Windows Defender exclusion list
- Latite Client_BetterV3.exe (PID: 5940)
Uses Task Scheduler to run other applications
- Latite Client_BetterV3.exe (PID: 5940)
XWORM has been detected (YARA)
- Latite Client_BetterV3.exe (PID: 5940)
XWORM has been detected (SURICATA)
- Latite Client_BetterV3.exe (PID: 5940)
Connects to the CnC server
- Latite Client_BetterV3.exe (PID: 5940)
Changes the autorun value in the registry
- Latite Client_BetterV3.exe (PID: 5940)
Create files in the Startup directory
- Latite Client_BetterV3.exe (PID: 5940)
SUSPICIOUS
Reads security settings of Internet Explorer
- LatiteClientbetter.exe (PID: 2700)
- Latite Client_BetterV3.exe (PID: 5940)
Reads the date of Windows installation
- LatiteClientbetter.exe (PID: 2700)
- Latite Client_BetterV3.exe (PID: 5940)
BASE64 encoded PowerShell command has been detected
- LatiteClientbetter.exe (PID: 2700)
Starts POWERSHELL.EXE for commands execution
- LatiteClientbetter.exe (PID: 2700)
- Latite Client_BetterV3.exe (PID: 5940)
Base64-obfuscated command line is found
- LatiteClientbetter.exe (PID: 2700)
Drops the executable file immediately after the start
- LatiteClientbetter.exe (PID: 2700)
- Latite Client_BetterV3.exe (PID: 5940)
Executable content was dropped or overwritten
- LatiteClientbetter.exe (PID: 2700)
- Latite Client_BetterV3.exe (PID: 5940)
Script adds exclusion process to Windows Defender
- Latite Client_BetterV3.exe (PID: 5940)
Script adds exclusion path to Windows Defender
- Latite Client_BetterV3.exe (PID: 5940)
Checks for external IP
- svchost.exe (PID: 2256)
- Latite Client_BetterV3.exe (PID: 5940)
Connects to unusual port
- Latite Client_BetterV3.exe (PID: 5940)
Contacting a server suspected of hosting an CnC
- Latite Client_BetterV3.exe (PID: 5940)
The process executes via Task Scheduler
- WindowsDefender (PID: 1164)
- WindowsDefender (PID: 6252)
INFO
Reads the computer name
- LatiteClientbetter.exe (PID: 2700)
- Latite Client_BetterV3.exe (PID: 5940)
- WindowsDefender (PID: 1164)
- WindowsDefender (PID: 6252)
Checks supported languages
- LatiteClientbetter.exe (PID: 2700)
- Latite Client_BetterV3.exe (PID: 5940)
- WindowsDefender (PID: 1164)
- WindowsDefender (PID: 6252)
The process uses the downloaded file
- LatiteClientbetter.exe (PID: 2700)
- Latite Client_BetterV3.exe (PID: 5940)
Process checks computer location settings
- LatiteClientbetter.exe (PID: 2700)
- Latite Client_BetterV3.exe (PID: 5940)
Reads the machine GUID from the registry
- LatiteClientbetter.exe (PID: 2700)
- Latite Client_BetterV3.exe (PID: 5940)
Reads Environment values
- Latite Client_BetterV3.exe (PID: 5940)
Disables trace logs
- Latite Client_BetterV3.exe (PID: 5940)
Checks proxy server information
- Latite Client_BetterV3.exe (PID: 5940)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5548)
- powershell.exe (PID: 4824)
- powershell.exe (PID: 5400)
- powershell.exe (PID: 2016)
- powershell.exe (PID: 6404)
- powershell.exe (PID: 1168)
- powershell.exe (PID: 5532)
- powershell.exe (PID: 5704)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5548)
- powershell.exe (PID: 4824)
- powershell.exe (PID: 5400)
- powershell.exe (PID: 2016)
- powershell.exe (PID: 6404)
- powershell.exe (PID: 5532)
- powershell.exe (PID: 5704)
- powershell.exe (PID: 1168)
Creates files in the program directory
- Latite Client_BetterV3.exe (PID: 5940)
Reads the software policy settings
- Latite Client_BetterV3.exe (PID: 5940)
Creates files or folders in the user directory
- Latite Client_BetterV3.exe (PID: 5940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
XWorm
(PID) Process(5940) Latite Client_BetterV3.exe
C2since-searching.gl.at.ply.gg:64197
Keys
AES7777
Options
Splitter<Xwormmm>
Sleep time3
USB drop nameBlackHat
MutexHCVrXj7OBhz1qvdU
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:08:28 03:21:42+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 153088 |
| InitializedDataSize: | 24064 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x274ce |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | lafdsfds.exe |
| LegalCopyright: | |
| OriginalFileName: | lafdsfds.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
151
Monitored processes
28
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1164 | "C:\ProgramData\WindowsDefender" | C:\ProgramData\WindowsDefender | — | svchost.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1168 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionPath 'C:\ProgramData\WindowsDefender' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Latite Client_BetterV3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1828 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2016 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionPath 'C:\Users\admin\Desktop\Latite Client_BetterV3.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Latite Client_BetterV3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2700 | "C:\Users\admin\Desktop\LatiteClientbetter.exe" | C:\Users\admin\Desktop\LatiteClientbetter.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 3164 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3164 | "C:\Windows\System32\schtasks.exe" /create /f /RL HIGHEST /sc minute /mo 1 /tn "WindowsDefender" /tr "C:\ProgramData\WindowsDefender" | C:\Windows\System32\schtasks.exe | — | Latite Client_BetterV3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3984 | "C:\Users\admin\Desktop\LatiteClientbetter.exe" | C:\Users\admin\Desktop\LatiteClientbetter.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 3221226540 Version: 0.0.0.0 Modules
| |||||||||||||||
| 4444 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
60 178
Read events
60 147
Write events
31
Delete events
0
Modification events
| (PID) Process: | (2700) LatiteClientbetter.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2700) LatiteClientbetter.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2700) LatiteClientbetter.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2700) LatiteClientbetter.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (5940) Latite Client_BetterV3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Latite Client_BetterV3_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5940) Latite Client_BetterV3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Latite Client_BetterV3_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5940) Latite Client_BetterV3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Latite Client_BetterV3_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (5940) Latite Client_BetterV3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Latite Client_BetterV3_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (5940) Latite Client_BetterV3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Latite Client_BetterV3_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (5940) Latite Client_BetterV3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Latite Client_BetterV3_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
3
Suspicious files
2
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5704 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_eglvd4iv.p0p.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5548 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:40C67F790C640CDC8246D529050F1D02 | SHA256:75525F970251B04378655AAD490467478D58FCCD3E195178AAE3A2C71AFF6972 | |||
| 5704 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_plt042wf.tgn.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2700 | LatiteClientbetter.exe | C:\Users\admin\Desktop\Latite Client_BetterV3.exe | executable | |
MD5:A677D044CC4D2FE27653F8F285996134 | SHA256:960D607391F69A4213108DFD0BEB8ACD0278E6DBEFD74DBCB70CAC38FC1BDE58 | |||
| 5548 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_laocavrz.ybu.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4824 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_s1vx3c4j.mrk.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4824 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bqepycna.hsi.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5548 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ggxnvhvb.m5v.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5400 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_pylw2eo1.y21.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5400 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ymucaq5v.yqr.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
17
DNS requests
8
Threats
35
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5940 | Latite Client_BetterV3.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | US | text | 6 b | shared |
— | — | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | US | text | 6 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
6612 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6280 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5940 | Latite Client_BetterV3.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | shared |
6612 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4324 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5940 | Latite Client_BetterV3.exe | 104.40.65.56:443 | insellerate.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ip-api.com |
| shared |
insellerate.net |
| malicious |
since-searching.gl.at.ply.gg |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2256 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
5940 | Latite Client_BetterV3.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
5940 | Latite Client_BetterV3.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
— | — | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
2256 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |
2256 | svchost.exe | Misc activity | ET INFO Tunneling Service in DNS Lookup (* .ply .gg) |
5940 | Latite Client_BetterV3.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Xworm Network Packet |
27 ETPRO signatures available at the full report