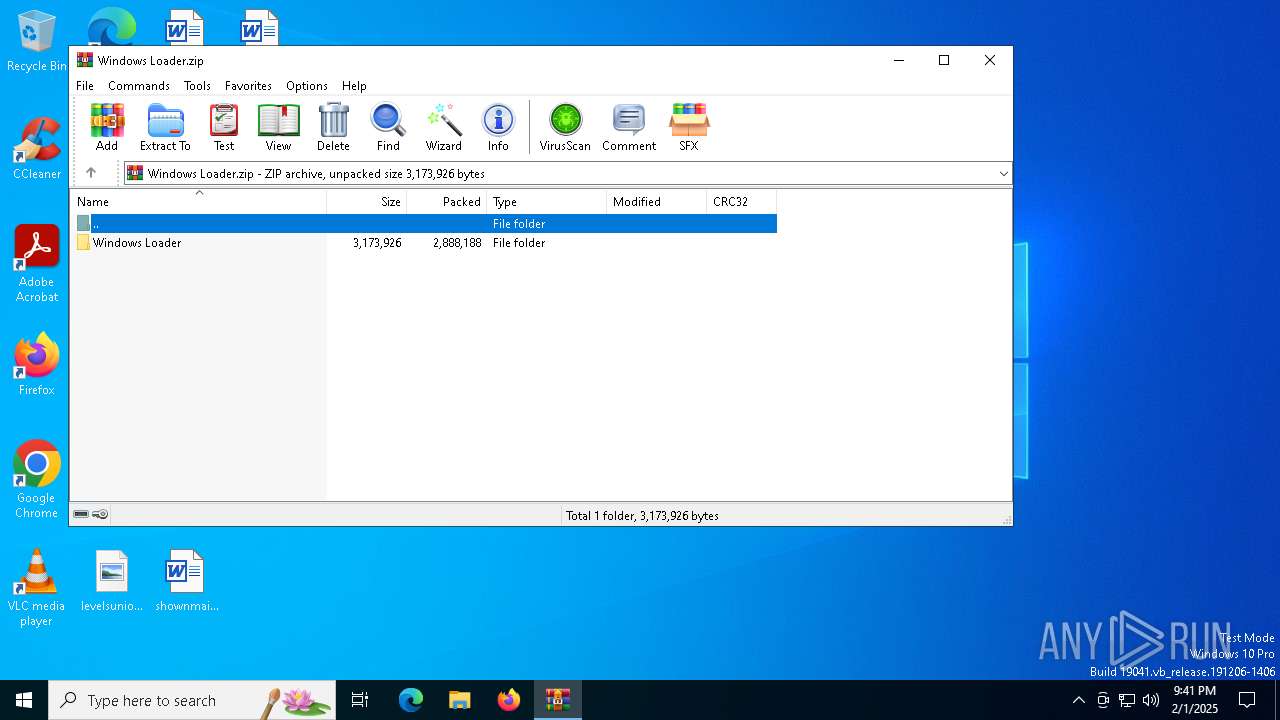
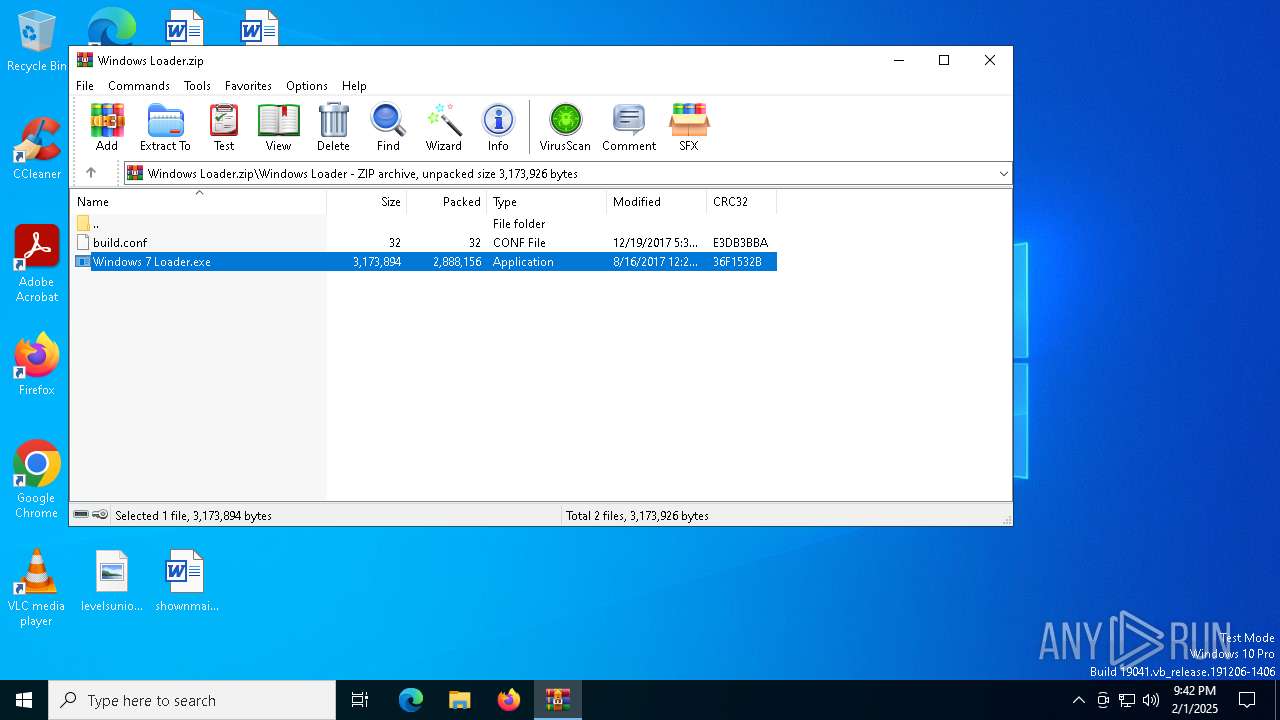
| File name: | Windows Loader.zip |
| Full analysis: | https://app.any.run/tasks/4e61202b-017a-4078-bfd8-c3b3522ddebe |
| Verdict: | Malicious activity |
| Analysis date: | February 01, 2025, 21:41:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 9371F45062600A31E649BF8EA5015984 |
| SHA1: | B5AAE20DBFAD02A67A816CC2A7F026626140C1C9 |
| SHA256: | 068FDE02DABA0CB8BCB99EEFB99DFAF76B2681286F0FF0C9433F7BEA030B454D |
| SSDEEP: | 98304:KmoO2RTBiBcUUh69fPXTHXlab+RLtW5xtsJ5m35j4HVsjOErMll6OyD2+zcUFQLN:H1 |
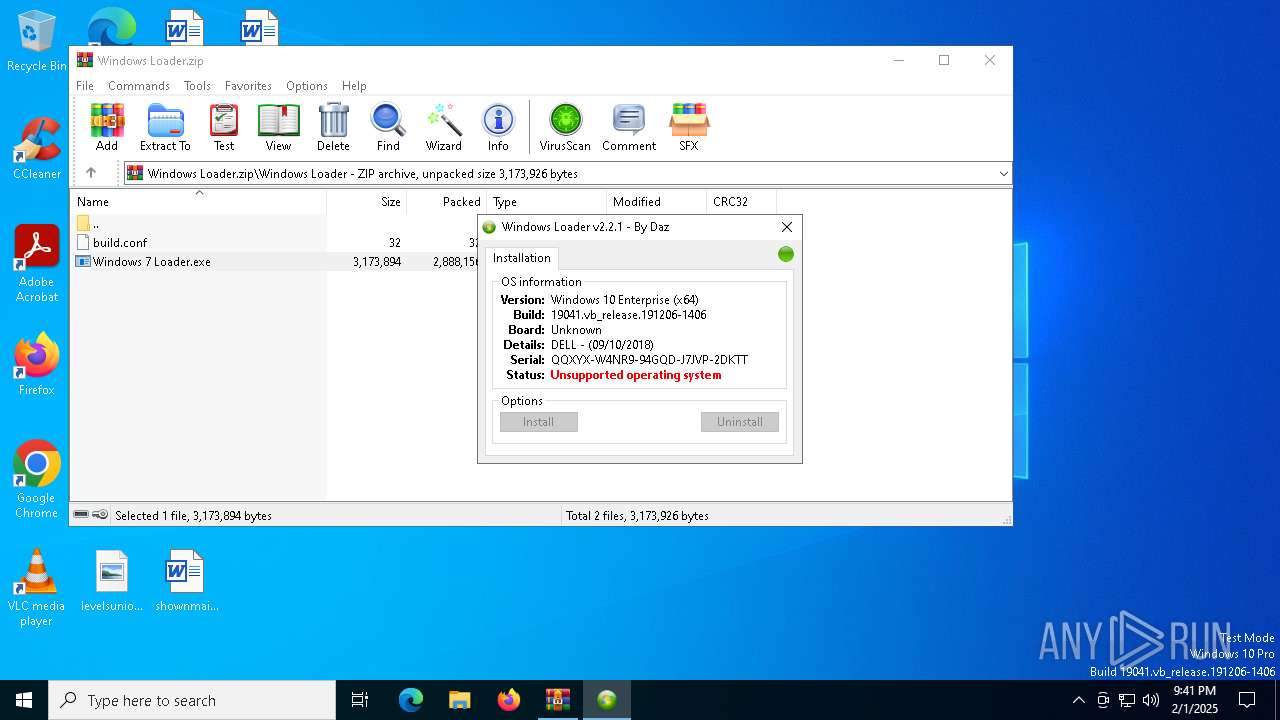
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 5208)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 440)
SUSPICIOUS
Reads security settings of Internet Explorer
- Windows 7 Loader.exe (PID: 6460)
- taskmg.exe (PID: 6632)
- WinRAR.exe (PID: 5208)
Reads the BIOS version
- Windows 7 Loader.exe (PID: 6752)
- taskmg.exe (PID: 6632)
Starts CMD.EXE for commands execution
- taskmg.exe (PID: 6632)
There is functionality for taking screenshot (YARA)
- Windows 7 Loader.exe (PID: 6752)
There is functionality for communication over UDP network (YARA)
- Windows 7 Loader.exe (PID: 6752)
Executable content was dropped or overwritten
- Windows 7 Loader.exe (PID: 6460)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5208)
The sample compiled with english language support
- WinRAR.exe (PID: 5208)
- Windows 7 Loader.exe (PID: 6460)
Checks supported languages
- Windows 7 Loader.exe (PID: 6460)
- taskmg.exe (PID: 6632)
- Windows 7 Loader.exe (PID: 6752)
Reads the computer name
- Windows 7 Loader.exe (PID: 6460)
- Windows 7 Loader.exe (PID: 6752)
- taskmg.exe (PID: 6632)
Process checks computer location settings
- Windows 7 Loader.exe (PID: 6460)
- taskmg.exe (PID: 6632)
Reads security settings of Internet Explorer
- explorer.exe (PID: 6664)
Reads Environment values
- Windows 7 Loader.exe (PID: 6752)
UPX packer has been detected
- Windows 7 Loader.exe (PID: 6752)
Creates files or folders in the user directory
- Windows 7 Loader.exe (PID: 6460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2017:12:19 17:36:34 |
| ZipCRC: | 0xe3db3bba |
| ZipCompressedSize: | 32 |
| ZipUncompressedSize: | 32 |
| ZipFileName: | Windows Loader/build.conf |
Total processes
141
Monitored processes
14
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | "C:\Windows\System32\cmd.exe" /c schtasks /create /sc onlogon /f /tn "UpdateChecker" /tr "C:\Users\admin\AppData\Roaming\taskmg.exe" | C:\Windows\SysWOW64\cmd.exe | taskmg.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1544 | schtasks /create /sc onlogon /f /tn "UpdateChecker" /tr "C:\Users\admin\AppData\Roaming\taskmg.exe" | C:\Windows\SysWOW64\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4328 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4540 | "C:\Windows\System32\cmd.exe" /c del /S /Q "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent" | C:\Windows\SysWOW64\cmd.exe | — | taskmg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4672 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5208 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Windows Loader.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6408 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5208.38775\Windows Loader\Windows 7 Loader.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5208.38775\Windows Loader\Windows 7 Loader.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Windows 7 Loader Installation Exit code: 3221226540 Modules
| |||||||||||||||
| 6460 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5208.38775\Windows Loader\Windows 7 Loader.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5208.38775\Windows Loader\Windows 7 Loader.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Windows 7 Loader Installation Exit code: 0 Modules
| |||||||||||||||
| 6612 | "C:\Windows\System32\explorer.exe" C:\Users\admin\AppData\Roaming\WindowsLoader\Windows 7 Loader.exe | C:\Windows\SysWOW64\explorer.exe | — | Windows 7 Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 185
Read events
4 166
Write events
19
Delete events
0
Modification events
| (PID) Process: | (5208) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5208) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5208) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5208) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Windows Loader.zip | |||
| (PID) Process: | (5208) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5208) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5208) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5208) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6664) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (5208) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
3
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
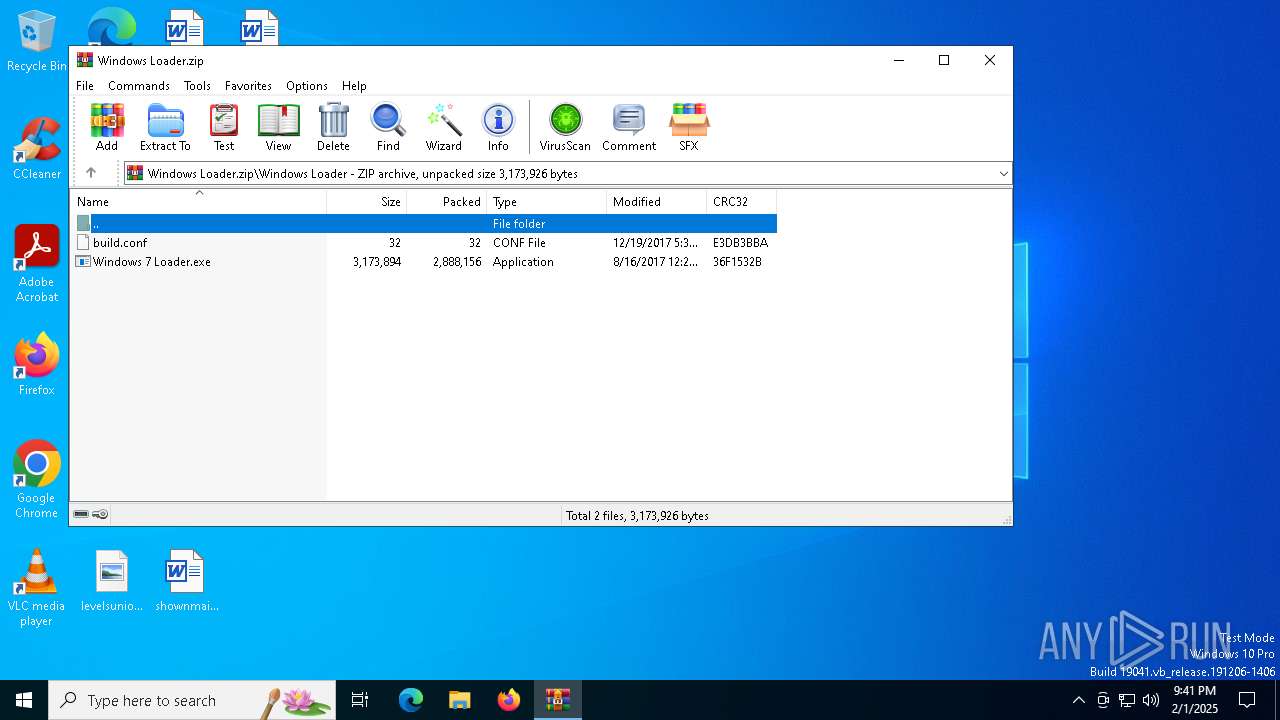
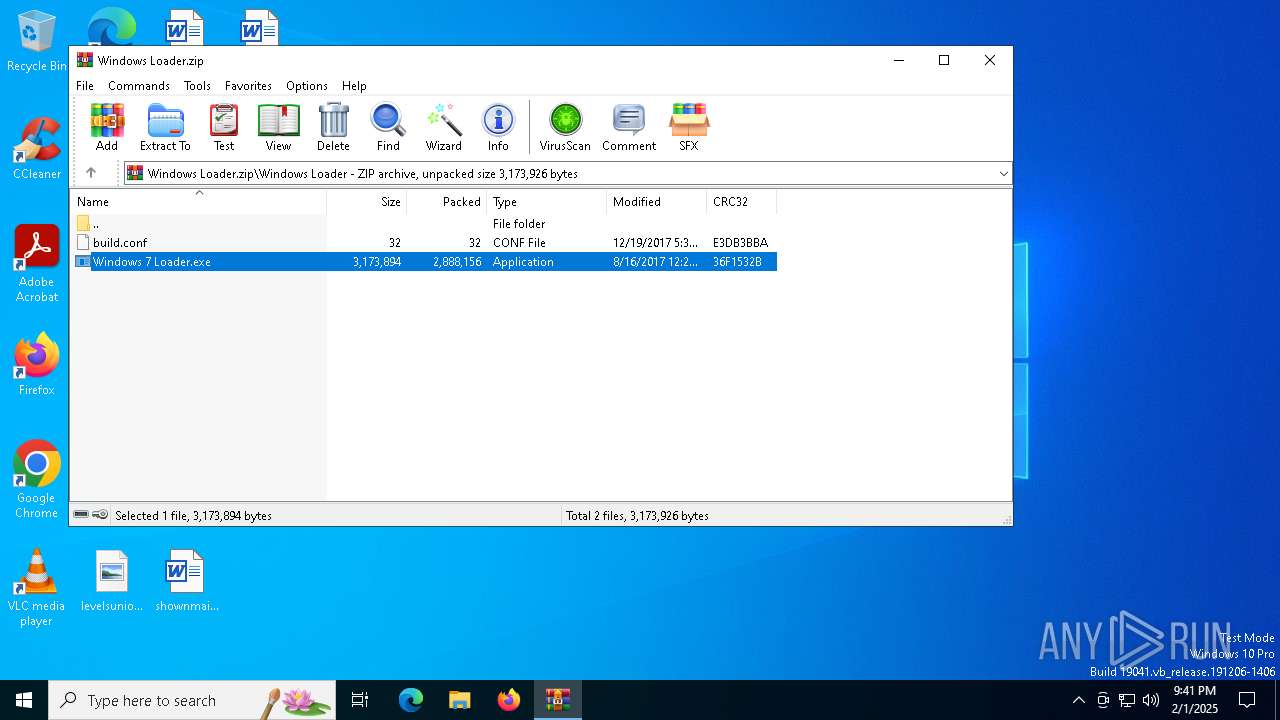
| 5208 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5208.38775\Windows Loader\Windows 7 Loader.exe | executable | |
MD5:C219FDB4E5C327D16913D78D844AA1AB | SHA256:CC30186F3768FB29155BFE7DE70A3B296AFC863511DF36EFBFB0B1DB3D64D962 | |||
| 5208 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5208.38775\Windows Loader\build.conf | text | |
MD5:EF5000CA3BA844E6BDBC3DE5D7DBE721 | SHA256:09BC56D00B7993146B99C2D1EFF75B0823CF6962D559686854544DEC9F6CA9D3 | |||
| 6460 | Windows 7 Loader.exe | C:\Users\admin\AppData\Roaming\taskmg.exe | executable | |
MD5:6A64C60E4F98E35B74676D0844D23AC3 | SHA256:CE08048FA45E9CB8C3A799712EC5A235C05AB70251AE9996C53734B39370BDE3 | |||
| 6460 | Windows 7 Loader.exe | C:\Users\admin\AppData\Roaming\WindowsLoader\Windows 7 Loader.exe | executable | |
MD5:3976BD5FCBB7CD13F0C12BB69AFC2ADC | SHA256:BF5070EF8CF03A11D25460B3E09A479183CC0FA03D0EA32E4499998F509B1A40 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
32
DNS requests
19
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3544 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3544 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6944 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.21.65.153:443 | — | Akamai International B.V. | NL | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
448 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.21.65.132:443 | — | Akamai International B.V. | NL | unknown |
1176 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |