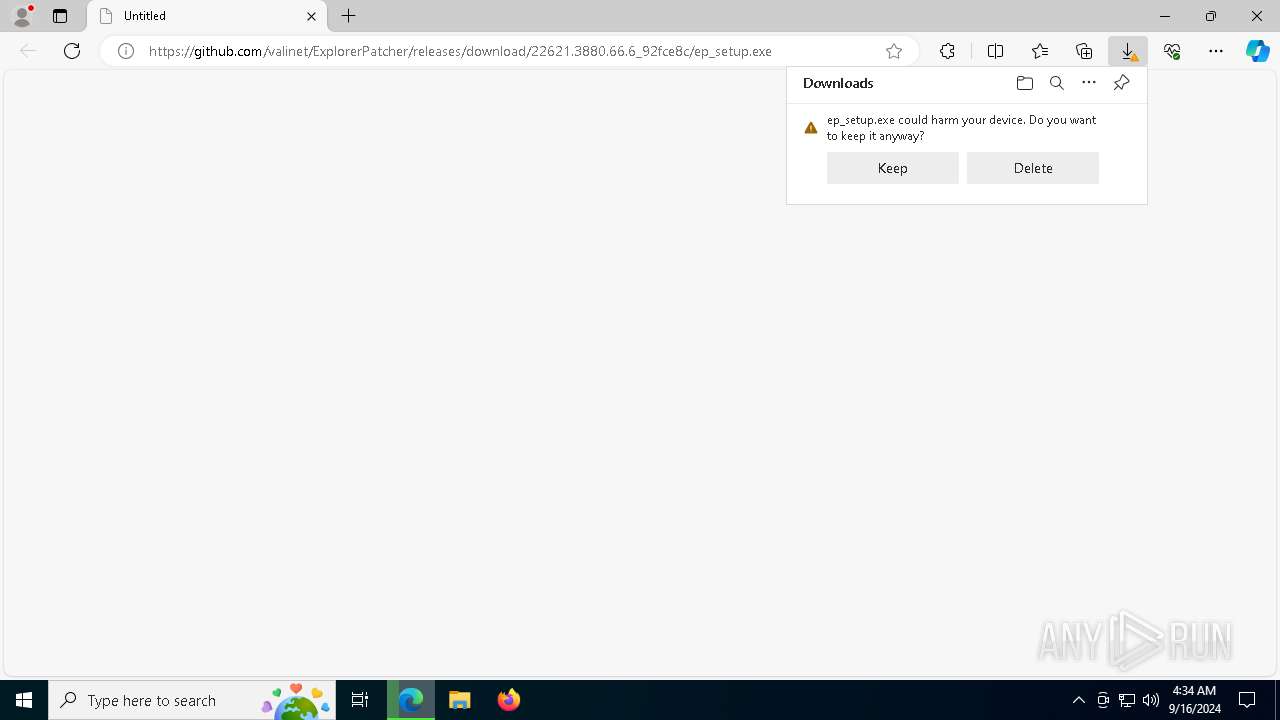
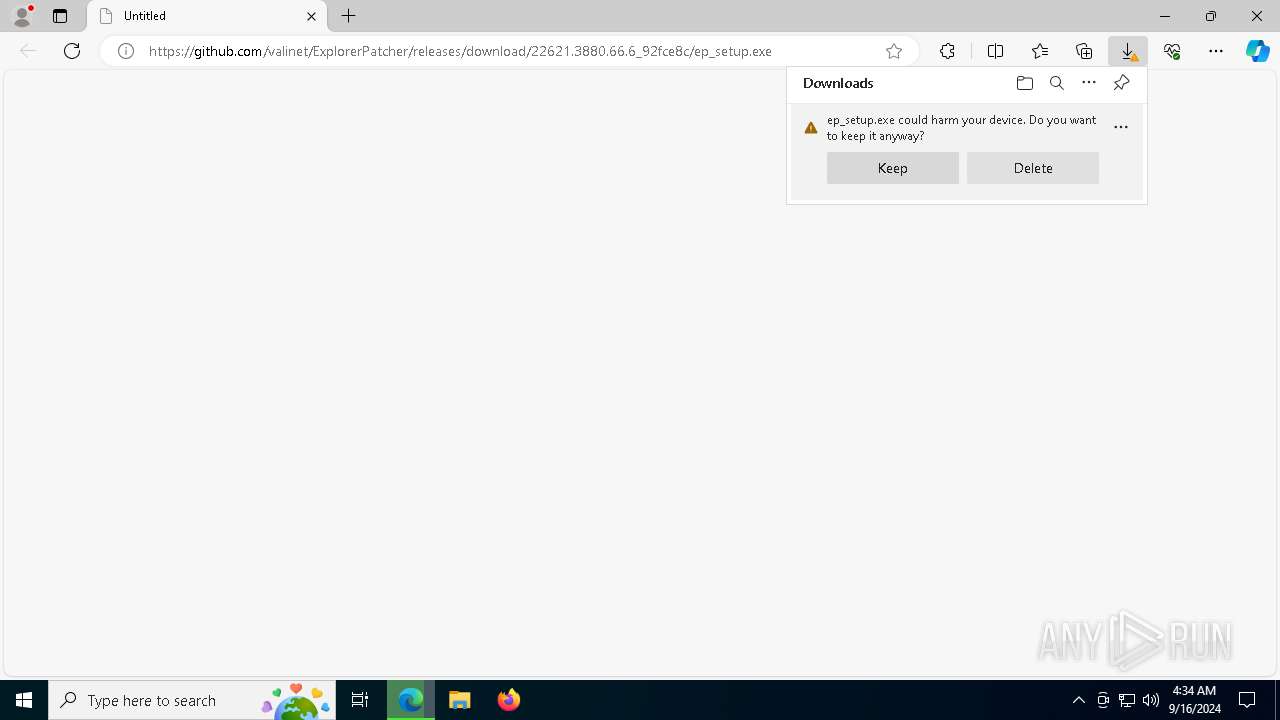
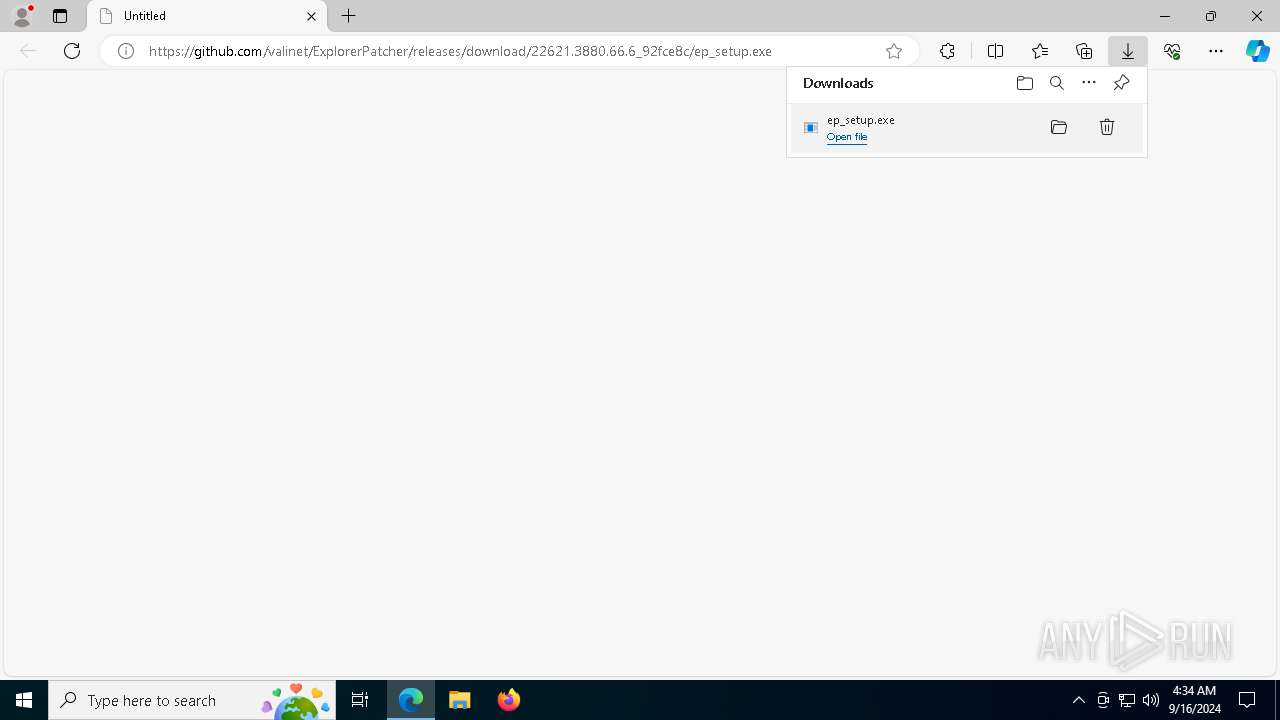
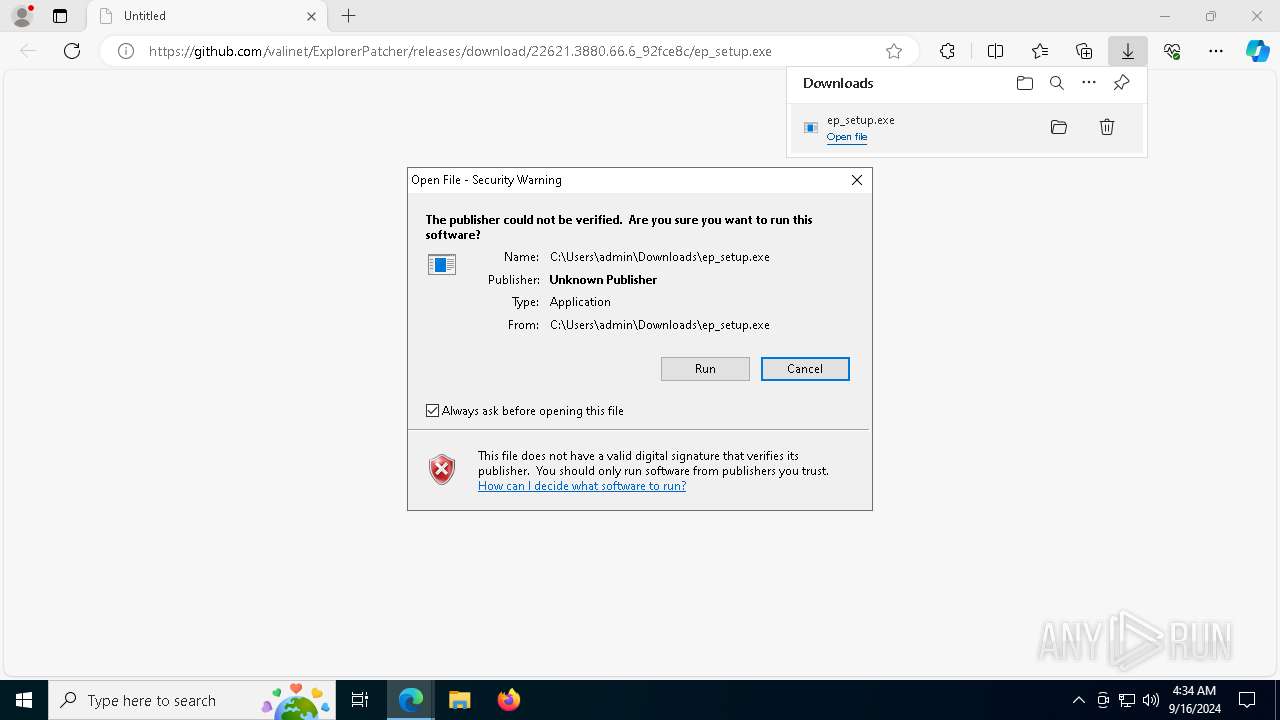
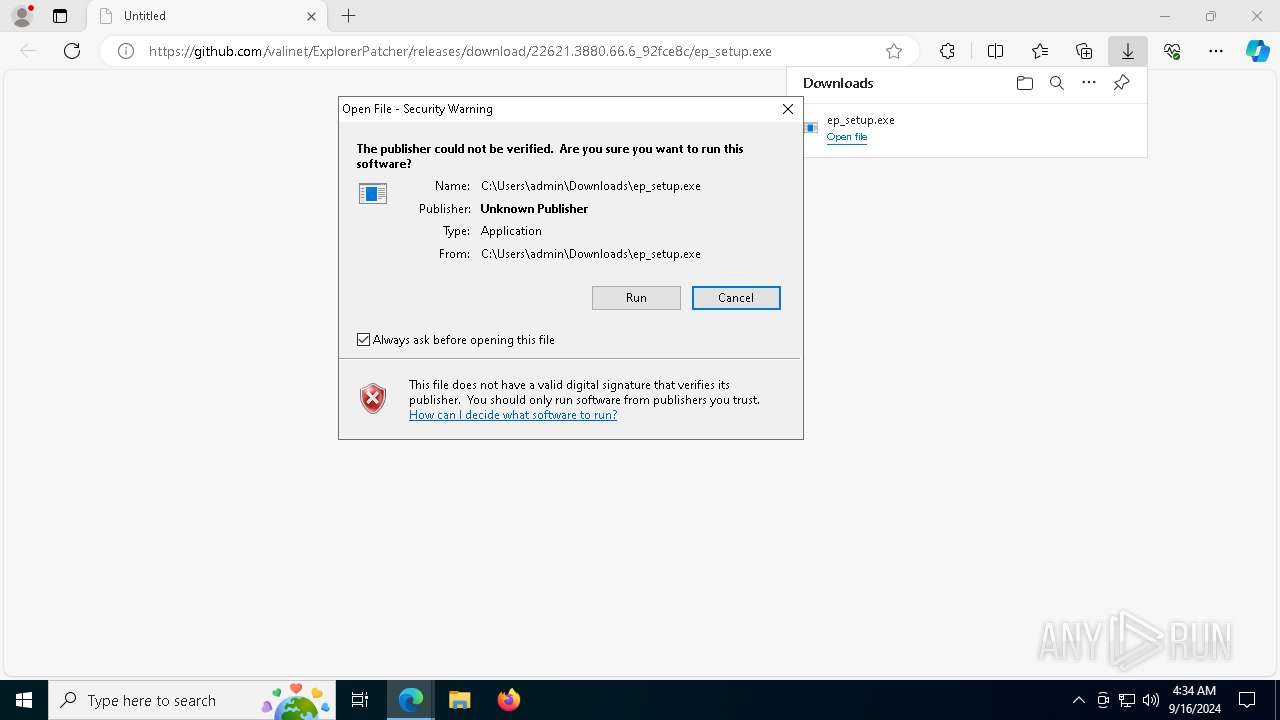
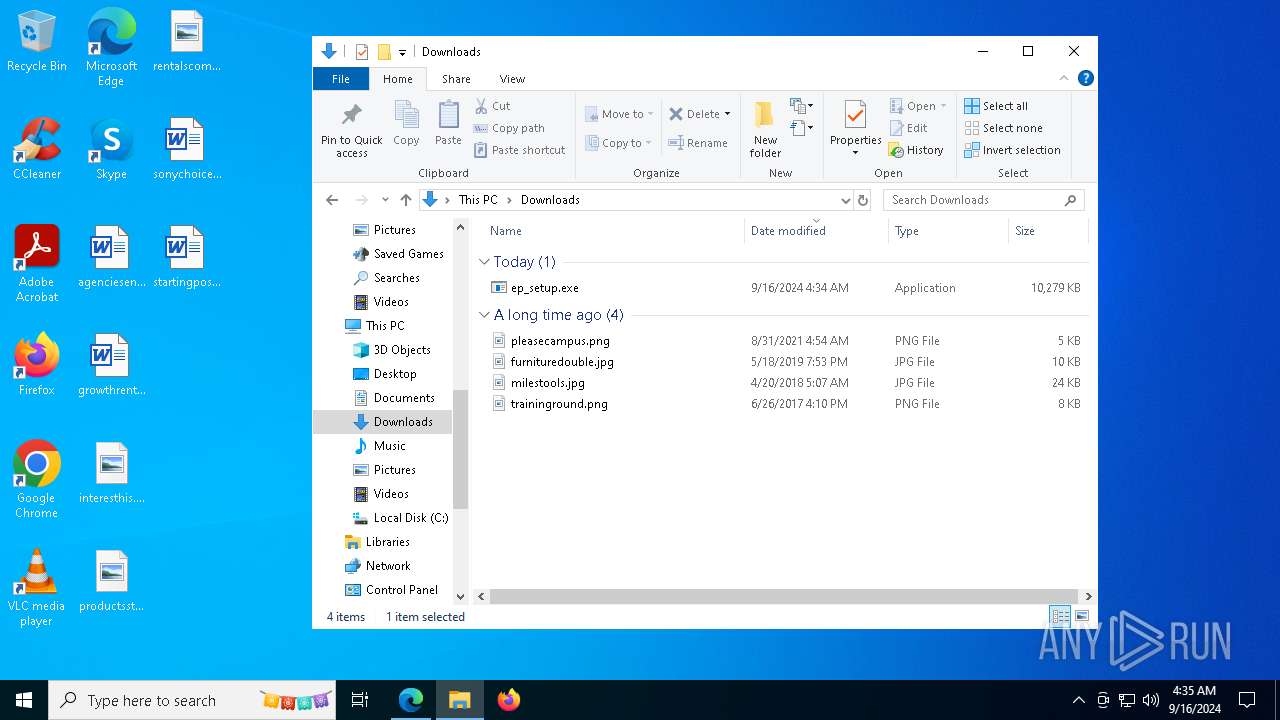
| URL: | https://github.com/valinet/ExplorerPatcher/releases/download/22621.3880.66.6_92fce8c/ep_setup.exe |
| Full analysis: | https://app.any.run/tasks/68ab7ecb-e886-4bca-863c-2dd43c1d465e |
| Verdict: | Malicious activity |
| Analysis date: | September 16, 2024, 04:34:19 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 3EA857D8AE7AEB90B4372E1ADCFF0F43 |
| SHA1: | 63556776CB3DB8C350886932E0F9906EC9D89AD5 |
| SHA256: | 068EA59F1A748116CC3901ACBF7059876DF5154D645B0EDC297A9FCAD912644E |
| SSDEEP: | 3:N8tEdjFzY2QeRcE2kCXgLWfhS+pu4A:2uPzY1eRcr0WFpu4A |
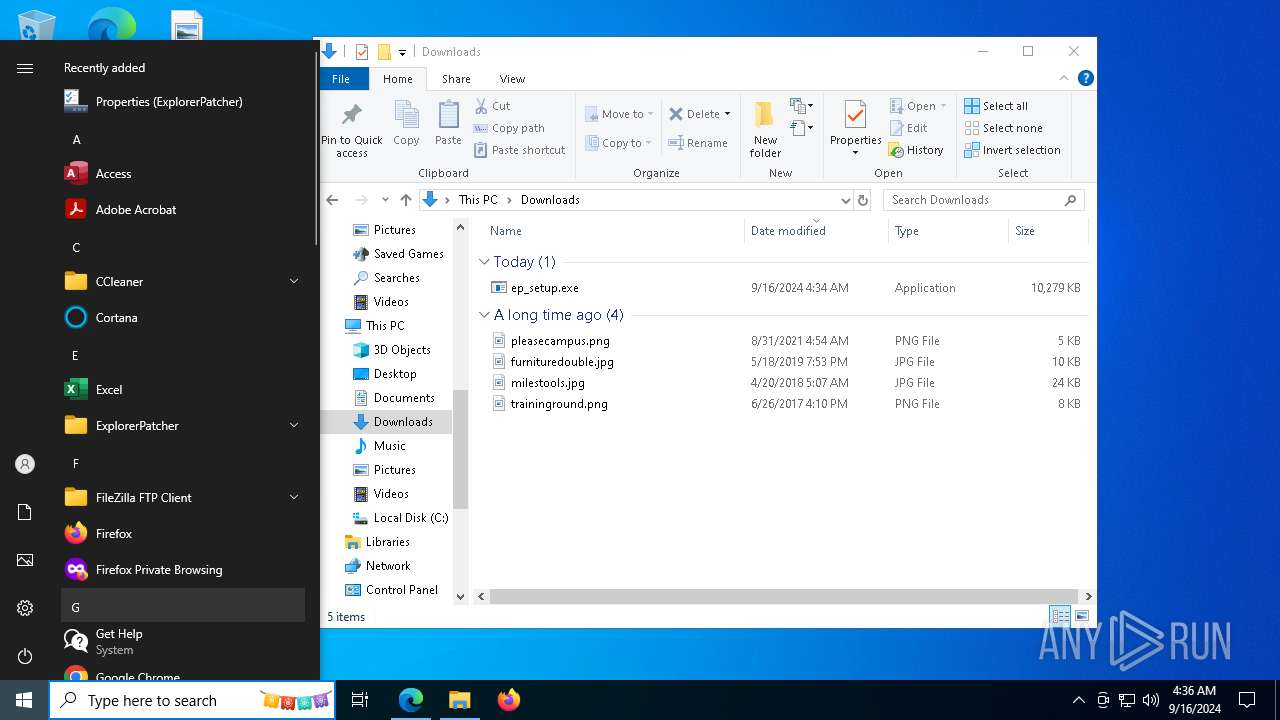
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- ep_setup.exe (PID: 7244)
- rundll32.exe (PID: 7236)
SUSPICIOUS
Reads security settings of Internet Explorer
- ep_setup.exe (PID: 8136)
- ep_setup.exe (PID: 7244)
- StartMenuExperienceHost.exe (PID: 6368)
- StartMenuExperienceHost.exe (PID: 944)
Reads the date of Windows installation
- ep_setup.exe (PID: 8136)
- StartMenuExperienceHost.exe (PID: 6368)
- ep_setup.exe (PID: 7244)
- SearchApp.exe (PID: 7212)
- StartMenuExperienceHost.exe (PID: 944)
- SearchApp.exe (PID: 400)
Application launched itself
- ep_setup.exe (PID: 8136)
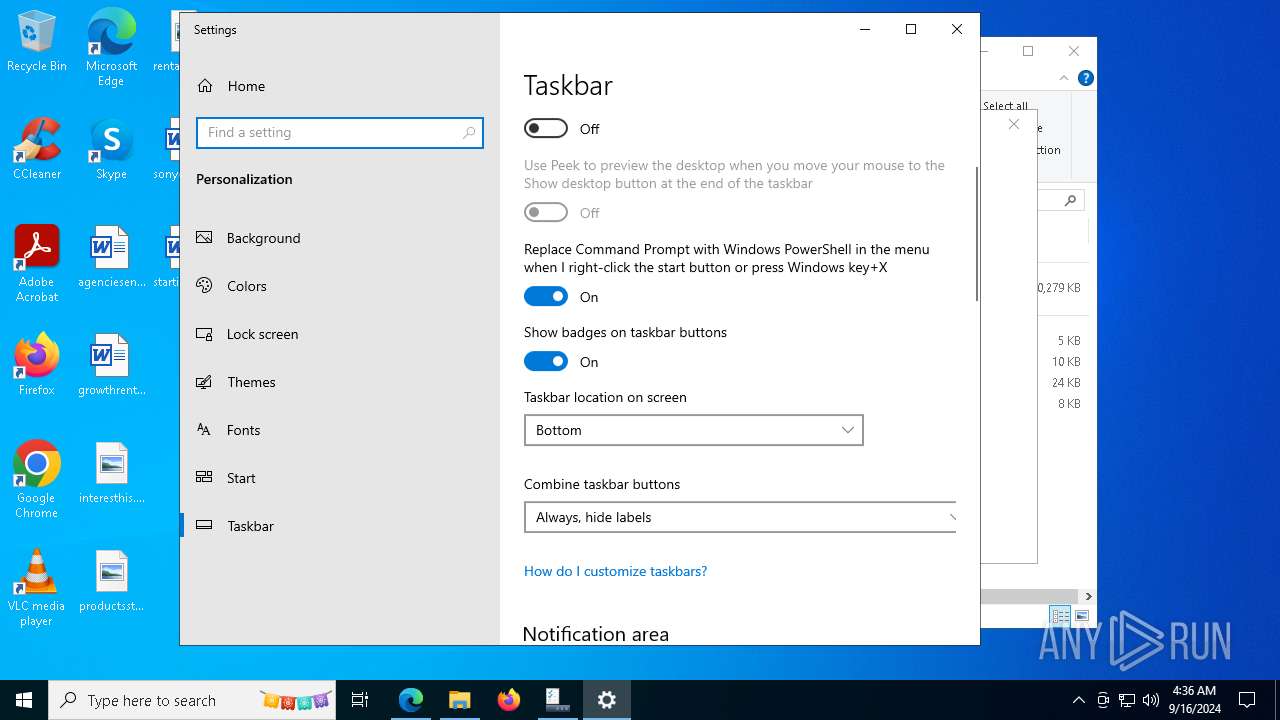
The process creates files with name similar to system file names
- ep_setup.exe (PID: 7244)
Starts SC.EXE for service management
- ep_setup.exe (PID: 7244)
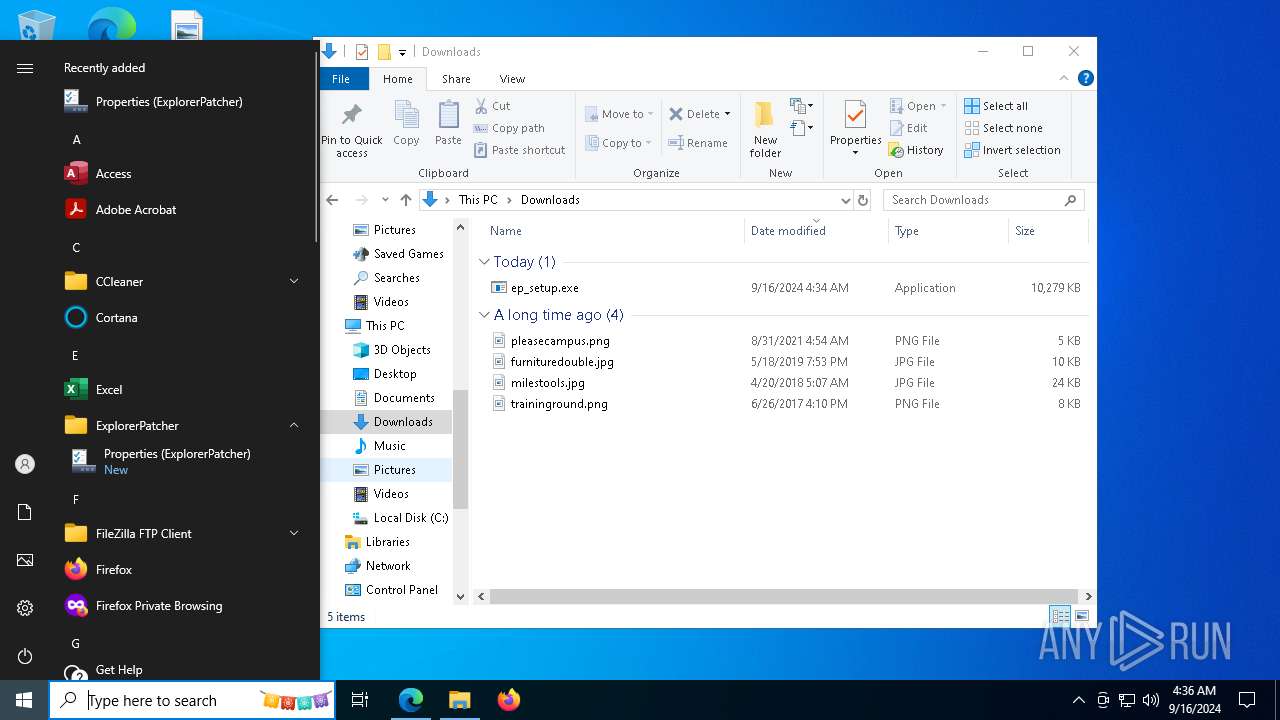
Creates a software uninstall entry
- ep_setup.exe (PID: 7244)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 7672)
- regsvr32.exe (PID: 7560)
- regsvr32.exe (PID: 1148)
Uses TASKKILL.EXE to kill process
- ep_setup.exe (PID: 7244)
- rundll32.exe (PID: 7236)
Executable content was dropped or overwritten
- ep_setup.exe (PID: 7244)
The process executes via Task Scheduler
- explorer.exe (PID: 6928)
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 6928)
INFO
The process uses the downloaded file
- iexplore.exe (PID: 5264)
- msedge.exe (PID: 7816)
- msedge.exe (PID: 3584)
- ep_setup.exe (PID: 8136)
- ep_setup.exe (PID: 7244)
- explorer.exe (PID: 6928)
- rundll32.exe (PID: 7236)
Checks supported languages
- identity_helper.exe (PID: 3332)
- ep_setup.exe (PID: 8136)
- ep_setup.exe (PID: 7244)
- StartMenuExperienceHost.exe (PID: 6368)
- SearchApp.exe (PID: 7212)
- TextInputHost.exe (PID: 6644)
- TextInputHost.exe (PID: 1596)
- StartMenuExperienceHost.exe (PID: 944)
- SearchApp.exe (PID: 400)
Reads Environment values
- identity_helper.exe (PID: 3332)
- SearchApp.exe (PID: 7212)
- SearchApp.exe (PID: 400)
Reads the computer name
- identity_helper.exe (PID: 3332)
- ep_setup.exe (PID: 8136)
- ep_setup.exe (PID: 7244)
- StartMenuExperienceHost.exe (PID: 6368)
- SearchApp.exe (PID: 7212)
- TextInputHost.exe (PID: 6644)
- TextInputHost.exe (PID: 1596)
- StartMenuExperienceHost.exe (PID: 944)
- SearchApp.exe (PID: 400)
Executable content was dropped or overwritten
- msedge.exe (PID: 6968)
- msedge.exe (PID: 3584)
- msedge.exe (PID: 4248)
Application launched itself
- msedge.exe (PID: 3584)
Process checks computer location settings
- ep_setup.exe (PID: 8136)
- ep_setup.exe (PID: 7244)
- StartMenuExperienceHost.exe (PID: 6368)
- SearchApp.exe (PID: 7212)
- StartMenuExperienceHost.exe (PID: 944)
- SearchApp.exe (PID: 400)
Creates files in the program directory
- ep_setup.exe (PID: 7244)
Reads security settings of Internet Explorer
- explorer.exe (PID: 6928)
- rundll32.exe (PID: 7236)
- explorer.exe (PID: 3036)
Sends debugging messages
- StartMenuExperienceHost.exe (PID: 6368)
- StartMenuExperienceHost.exe (PID: 944)
Reads the software policy settings
- explorer.exe (PID: 6928)
- SearchApp.exe (PID: 7212)
- SearchApp.exe (PID: 400)
- explorer.exe (PID: 3036)
Checks proxy server information
- SearchApp.exe (PID: 7212)
- explorer.exe (PID: 6928)
- explorer.exe (PID: 3036)
- SearchApp.exe (PID: 400)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 7212)
- SearchApp.exe (PID: 400)
Creates files or folders in the user directory
- explorer.exe (PID: 6928)
- explorer.exe (PID: 3036)
Manual execution by a user
- rundll32.exe (PID: 4888)
- dllhost.exe (PID: 7616)
- TextInputHost.exe (PID: 6644)
- dllhost.exe (PID: 7492)
- StartMenuExperienceHost.exe (PID: 944)
- WmiPrvSE.exe (PID: 4888)
- TextInputHost.exe (PID: 1596)
- TiWorker.exe (PID: 4644)
- SearchApp.exe (PID: 400)
- mobsync.exe (PID: 5060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
218
Monitored processes
79
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 400 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 944 | "C:\WINDOWS\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe" -ServerName:App.AppXywbrabmsek0gm3tkwpr5kwzbs55tkqay.mca | C:\Windows\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 1140 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3720 --field-trial-handle=2416,i,208157802836797010,12990071208640013470,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1148 | "C:\WINDOWS\system32\regsvr32.exe" "C:\Program Files\ExplorerPatcher\ExplorerPatcher.amd64.dll" | C:\Windows\System32\regsvr32.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1596 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 1616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x290,0x294,0x298,0x288,0x2a0,0x7fffd20e5fd8,0x7fffd20e5fe4,0x7fffd20e5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2684 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2720 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6380 --field-trial-handle=2416,i,208157802836797010,12990071208640013470,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2824 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5620 --field-trial-handle=2416,i,208157802836797010,12990071208640013470,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3036 | "C:\WINDOWS\explorer.exe" | C:\Windows\explorer.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
80 875
Read events
79 979
Write events
829
Delete events
67
Modification events
| (PID) Process: | (5264) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5264) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5264) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5264) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (5264) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (5264) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (3584) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3584) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3584) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3584) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
20
Suspicious files
476
Text files
541
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF129f74.TMP | — | |
MD5:— | SHA256:— | |||
| 3584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF129f74.TMP | — | |
MD5:— | SHA256:— | |||
| 3584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF129f84.TMP | — | |
MD5:— | SHA256:— | |||
| 3584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF129fd2.TMP | — | |
MD5:— | SHA256:— | |||
| 3584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF129fe2.TMP | — | |
MD5:— | SHA256:— | |||
| 3584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
61
TCP/UDP connections
99
DNS requests
78
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6928 | explorer.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCEQDzZE5rbgBQI34JRr174fUd | unknown | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1404 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6928 | explorer.exe | GET | 302 | 204.79.197.219:80 | http://msdl.microsoft.com/download/symbols/twinui.pcshell.pdb/3F0945AE4BC25ECE16353588B05D30B61/twinui.pcshell.pdb | unknown | — | — | whitelisted |
6988 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1726547983&P2=404&P3=2&P4=RDzE8lyxbnQVfSdJ3HtCkohokDWg4JU300LzmThnjRCqhrV8v5MMxd%2b0gxHgZ4LVccys%2bb5jS%2fY6dI7oVJPSPw%3d%3d | unknown | — | — | whitelisted |
6928 | explorer.exe | GET | 302 | 204.79.197.219:80 | http://msdl.microsoft.com/download/symbols/StartUI.pdb/0B81EEDEEB6FF49A7EC7F23C15C216771/StartUI.pdb | unknown | — | — | whitelisted |
6988 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1726547983&P2=404&P3=2&P4=RDzE8lyxbnQVfSdJ3HtCkohokDWg4JU300LzmThnjRCqhrV8v5MMxd%2b0gxHgZ4LVccys%2bb5jS%2fY6dI7oVJPSPw%3d%3d | unknown | — | — | whitelisted |
6988 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1726547983&P2=404&P3=2&P4=RDzE8lyxbnQVfSdJ3HtCkohokDWg4JU300LzmThnjRCqhrV8v5MMxd%2b0gxHgZ4LVccys%2bb5jS%2fY6dI7oVJPSPw%3d%3d | unknown | — | — | whitelisted |
6988 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1726547983&P2=404&P3=2&P4=RDzE8lyxbnQVfSdJ3HtCkohokDWg4JU300LzmThnjRCqhrV8v5MMxd%2b0gxHgZ4LVccys%2bb5jS%2fY6dI7oVJPSPw%3d%3d | unknown | — | — | whitelisted |
6988 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1726547983&P2=404&P3=2&P4=RDzE8lyxbnQVfSdJ3HtCkohokDWg4JU300LzmThnjRCqhrV8v5MMxd%2b0gxHgZ4LVccys%2bb5jS%2fY6dI7oVJPSPw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6516 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6276 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6968 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3584 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6968 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
github.com |
| shared |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |