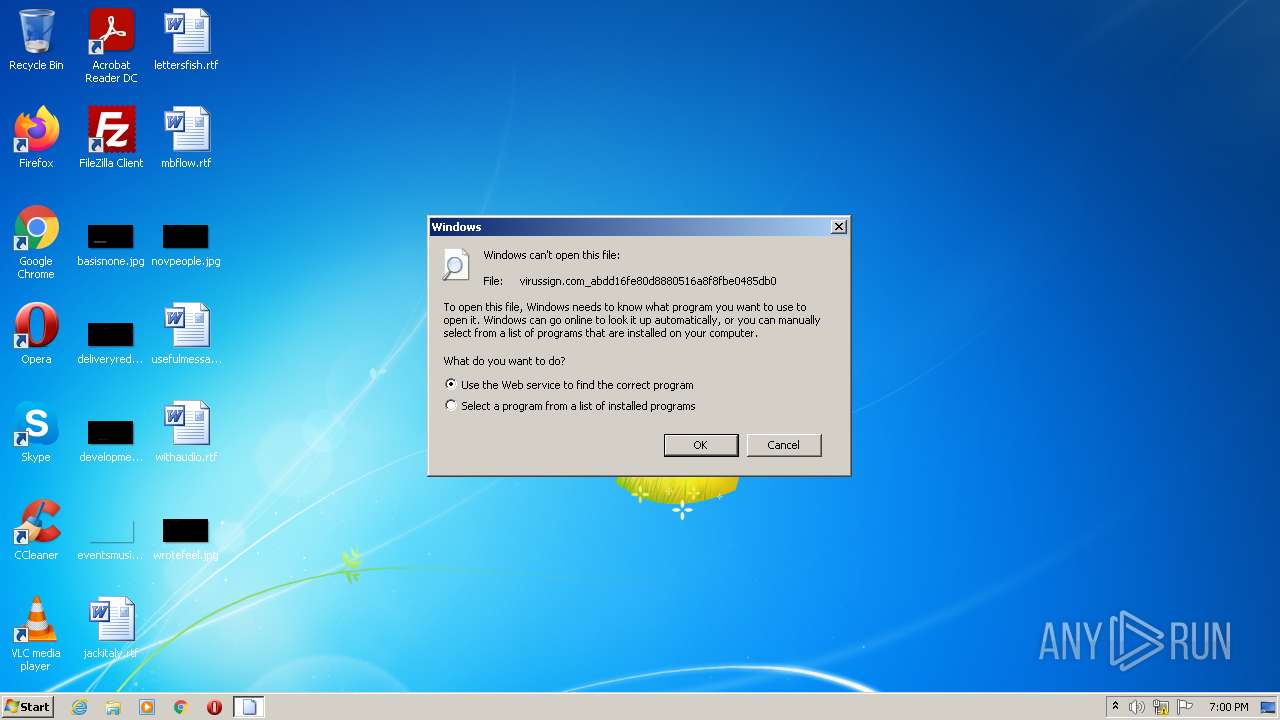
| File name: | virussign.com_abdd16fe80d8880516a8f8fbe0485db0 |
| Full analysis: | https://app.any.run/tasks/4ab656b0-dea0-4c4d-bdd8-bb897c638de8 |
| Verdict: | Malicious activity |
| Analysis date: | July 22, 2022, 18:00:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | ABDD16FE80D8880516A8F8FBE0485DB0 |
| SHA1: | 07CF57583DCA5544A6D80EBC77342AC3DC45C057 |
| SHA256: | 068CF2147CB6023891FF23C287027733422824EAB28E3AF2F2572755F30635F7 |
| SSDEEP: | 24576:Ymt72OUYl1HquvS++fvsA0Q1fx4E1mz/R2JPhBhfVB2vLR+6J6P661rBez:Ymtl1LKfiL/K2CPXA |
MALICIOUS
Application was dropped or rewritten from another process
- ioYQQQIE.exe (PID: 3820)
- bIcksoAA.exe (PID: 3400)
Changes the login/logoff helper path in the registry
- virussign.com_abdd16fe80d8880516a8f8fbe0485db0.exe (PID: 3968)
Changes the autorun value in the registry
- virussign.com_abdd16fe80d8880516a8f8fbe0485db0.exe (PID: 3968)
- bIcksoAA.exe (PID: 3400)
- ioYQQQIE.exe (PID: 3820)
Drops executable file immediately after starts
- virussign.com_abdd16fe80d8880516a8f8fbe0485db0.exe (PID: 3968)
- ioYQQQIE.exe (PID: 3820)
Modifies files in Chrome extension folder
- ioYQQQIE.exe (PID: 3820)
SUSPICIOUS
Creates files in the program directory
- virussign.com_abdd16fe80d8880516a8f8fbe0485db0.exe (PID: 3968)
- ioYQQQIE.exe (PID: 3820)
Reads the computer name
- virussign.com_abdd16fe80d8880516a8f8fbe0485db0.exe (PID: 3968)
- cmd.exe (PID: 2092)
- bIcksoAA.exe (PID: 3400)
- ioYQQQIE.exe (PID: 3820)
Checks supported languages
- virussign.com_abdd16fe80d8880516a8f8fbe0485db0.exe (PID: 3968)
- cmd.exe (PID: 2092)
- ioYQQQIE.exe (PID: 3820)
- bIcksoAA.exe (PID: 3400)
Starts CMD.EXE for commands execution
- virussign.com_abdd16fe80d8880516a8f8fbe0485db0.exe (PID: 3968)
Uses REG.EXE to modify Windows registry
- virussign.com_abdd16fe80d8880516a8f8fbe0485db0.exe (PID: 3968)
Executable content was dropped or overwritten
- virussign.com_abdd16fe80d8880516a8f8fbe0485db0.exe (PID: 3968)
- ioYQQQIE.exe (PID: 3820)
Drops a file with a compile date too recent
- virussign.com_abdd16fe80d8880516a8f8fbe0485db0.exe (PID: 3968)
- ioYQQQIE.exe (PID: 3820)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 2092)
INFO
Checks supported languages
- reg.exe (PID: 1780)
- reg.exe (PID: 1860)
- reg.exe (PID: 2008)
- rundll32.exe (PID: 3300)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1000 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 256876 |
| CodeSize: | 692224 |
| LinkerVersion: | 5.12 |
| PEType: | PE32 |
| TimeStamp: | 2016:03:22 09:16:05+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Mar-2016 08:16:05 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 22-Mar-2016 08:16:05 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000A9000 | 0x000A9000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.13009 |
.rdata | 0x000AA000 | 0x00002000 | 0x00002800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.187937 |
.data | 0x000AC000 | 0x00154000 | 0x00154000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.8292 |
.rsrc | 0x00200000 | 0x00001200 | 0x00001200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_LOCKED, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.65929 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 1.94375 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
kernel32.dll |
Total processes
45
Monitored processes
8
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1780 | reg add HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System /v EnableLUA /d 0 /t REG_DWORD /f | C:\Windows\system32\reg.exe | — | virussign.com_abdd16fe80d8880516a8f8fbe0485db0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1860 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced /f /v Hidden /t REG_DWORD /d 2 | C:\Windows\system32\reg.exe | — | virussign.com_abdd16fe80d8880516a8f8fbe0485db0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2008 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced /f /v HideFileExt /t REG_DWORD /d 1 | C:\Windows\system32\reg.exe | — | virussign.com_abdd16fe80d8880516a8f8fbe0485db0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2092 | C:\Windows\system32\cmd.exe /c "C:\Users\admin\AppData\Local\Temp\virussign.com_abdd16fe80d8880516a8f8fbe0485db0" | C:\Windows\system32\cmd.exe | — | virussign.com_abdd16fe80d8880516a8f8fbe0485db0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3300 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\virussign.com_abdd16fe80d8880516a8f8fbe0485db0 | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3400 | "C:\ProgramData\iucYkoME\bIcksoAA.exe" | C:\ProgramData\iucYkoME\bIcksoAA.exe | virussign.com_abdd16fe80d8880516a8f8fbe0485db0.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3820 | "C:\Users\admin\JesgMEYI\ioYQQQIE.exe" | C:\Users\admin\JesgMEYI\ioYQQQIE.exe | virussign.com_abdd16fe80d8880516a8f8fbe0485db0.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3968 | "C:\Users\admin\AppData\Local\Temp\virussign.com_abdd16fe80d8880516a8f8fbe0485db0.exe" | C:\Users\admin\AppData\Local\Temp\virussign.com_abdd16fe80d8880516a8f8fbe0485db0.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 010
Read events
2 002
Write events
8
Delete events
0
Modification events
| (PID) Process: | (3968) virussign.com_abdd16fe80d8880516a8f8fbe0485db0.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | ioYQQQIE.exe |
Value: C:\Users\admin\JesgMEYI\ioYQQQIE.exe | |||
| (PID) Process: | (3968) virussign.com_abdd16fe80d8880516a8f8fbe0485db0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | bIcksoAA.exe |
Value: C:\ProgramData\iucYkoME\bIcksoAA.exe | |||
| (PID) Process: | (3968) virussign.com_abdd16fe80d8880516a8f8fbe0485db0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Userinit |
Value: C:\Windows\system32\userinit.exe,C:\ProgramData\iucYkoME\bIcksoAA.exe, | |||
| (PID) Process: | (2008) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced |
| Operation: | write | Name: | HideFileExt |
Value: 1 | |||
| (PID) Process: | (1860) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced |
| Operation: | write | Name: | Hidden |
Value: 2 | |||
| (PID) Process: | (3820) ioYQQQIE.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | ioYQQQIE.exe |
Value: C:\Users\admin\JesgMEYI\ioYQQQIE.exe | |||
| (PID) Process: | (3400) bIcksoAA.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | bIcksoAA.exe |
Value: C:\ProgramData\iucYkoME\bIcksoAA.exe | |||
Executable files
209
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3968 | virussign.com_abdd16fe80d8880516a8f8fbe0485db0.exe | C:\ProgramData\iucYkoME\bIcksoAA.exe | executable | |
MD5:— | SHA256:— | |||
| 3968 | virussign.com_abdd16fe80d8880516a8f8fbe0485db0.exe | C:\Users\admin\JesgMEYI\ioYQQQIE.exe | executable | |
MD5:— | SHA256:— | |||
| 3820 | ioYQQQIE.exe | C:\MSOCache\All Users\{90140000-006E-0411-0000-0000000FF1CE}-C\DW20.EXE.exe | executable | |
MD5:— | SHA256:— | |||
| 3820 | ioYQQQIE.exe | C:\MSOCache\All Users\{90140000-006E-040C-0000-0000000FF1CE}-C\DW20.EXE.exe | executable | |
MD5:— | SHA256:— | |||
| 3820 | ioYQQQIE.exe | C:\MSOCache\All Users\{90140000-003D-0000-0000-0000000FF1CE}-C\setup.exe | executable | |
MD5:— | SHA256:— | |||
| 3820 | ioYQQQIE.exe | C:\Users\admin\JesgMEYI\EcMY.exe | executable | |
MD5:— | SHA256:— | |||
| 3820 | ioYQQQIE.exe | C:\Users\admin\JesgMEYI\GkoS.exe | executable | |
MD5:— | SHA256:— | |||
| 3820 | ioYQQQIE.exe | C:\Users\admin\JesgMEYI\GAsm.exe | executable | |
MD5:— | SHA256:— | |||
| 3820 | ioYQQQIE.exe | C:\MSOCache\All Users\{90140000-006E-0407-0000-0000000FF1CE}-C\DW20.EXE.exe | executable | |
MD5:— | SHA256:— | |||
| 3820 | ioYQQQIE.exe | C:\Users\admin\JesgMEYI\cQsC.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
7
DNS requests
0
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3820 | ioYQQQIE.exe | GET | — | 172.217.16.206:80 | http://172.217.16.206:80/ | US | — | — | whitelisted |
3400 | bIcksoAA.exe | GET | 200 | 172.217.16.206:80 | http://172.217.16.206:80/ | US | html | 48.4 Kb | whitelisted |
3400 | bIcksoAA.exe | GET | 200 | 172.217.16.206:80 | http://172.217.16.206:80/ | US | html | 48.4 Kb | whitelisted |
3820 | ioYQQQIE.exe | GET | 200 | 172.217.16.206:80 | http://172.217.16.206:80/ | US | html | 48.4 Kb | whitelisted |
3820 | ioYQQQIE.exe | GET | — | 172.217.16.206:80 | http://172.217.16.206:80/ | US | — | — | whitelisted |
3400 | bIcksoAA.exe | GET | 301 | 172.217.16.206:80 | http://google.com/ | US | html | 219 b | whitelisted |
3820 | ioYQQQIE.exe | GET | 301 | 172.217.16.206:80 | http://google.com/ | US | html | 219 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3820 | ioYQQQIE.exe | 172.217.16.206:80 | — | Google Inc. | US | whitelisted |
3400 | bIcksoAA.exe | 172.217.16.206:80 | — | Google Inc. | US | whitelisted |
— | — | 172.217.16.206:80 | — | Google Inc. | US | whitelisted |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
3820 | ioYQQQIE.exe | Generic Protocol Command Decode | SURICATA HTTP missing Host header |
3820 | ioYQQQIE.exe | Generic Protocol Command Decode | SURICATA HTTP missing Host header |
3820 | ioYQQQIE.exe | Generic Protocol Command Decode | SURICATA HTTP missing Host header |
3400 | bIcksoAA.exe | Generic Protocol Command Decode | SURICATA HTTP missing Host header |
3400 | bIcksoAA.exe | Generic Protocol Command Decode | SURICATA HTTP missing Host header |
3820 | ioYQQQIE.exe | A Network Trojan was detected | ET INFO Terse Unencrypted Request for Google - Likely Connectivity Check |
3400 | bIcksoAA.exe | A Network Trojan was detected | ET INFO Terse Unencrypted Request for Google - Likely Connectivity Check |
3400 | bIcksoAA.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible automated connectivity check (www.google.com) |