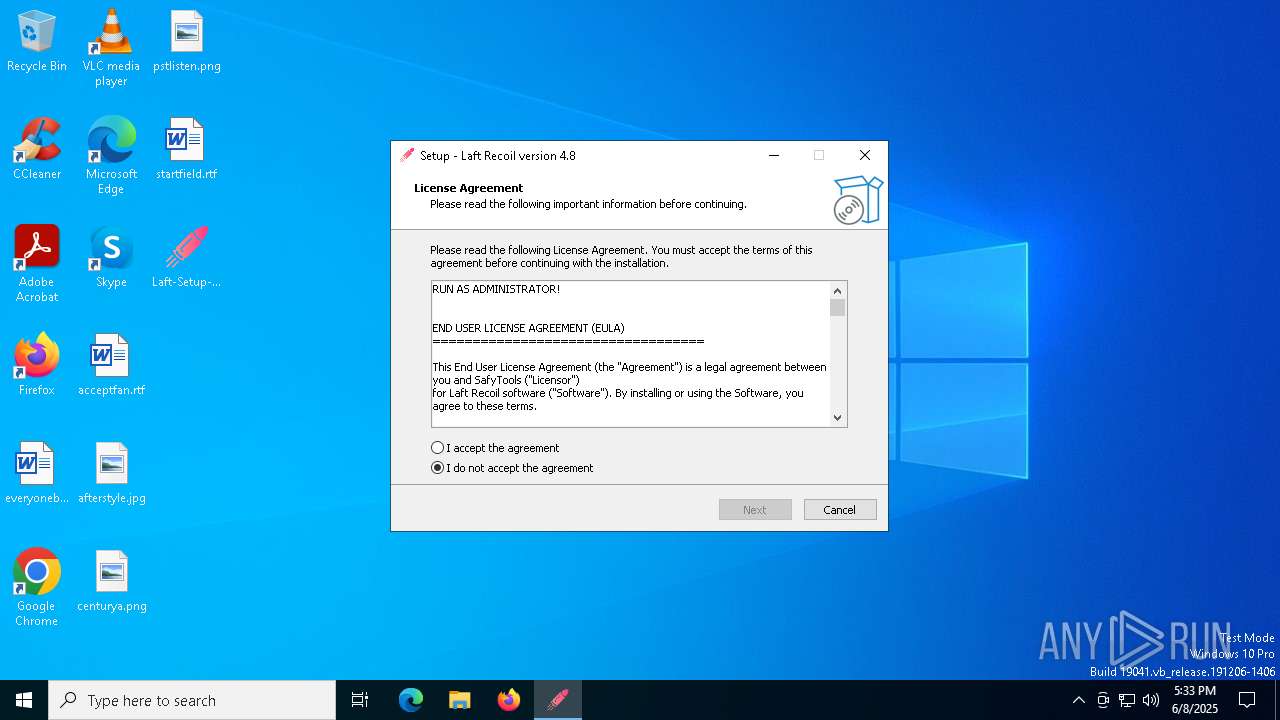
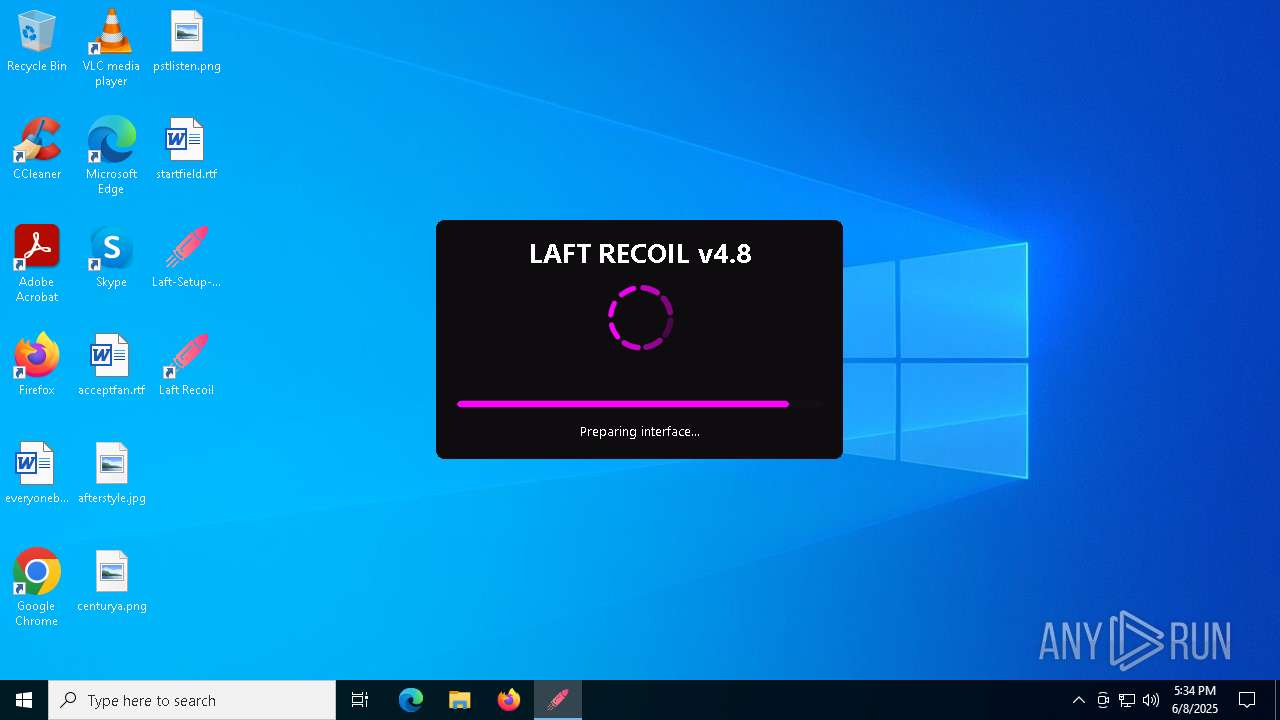
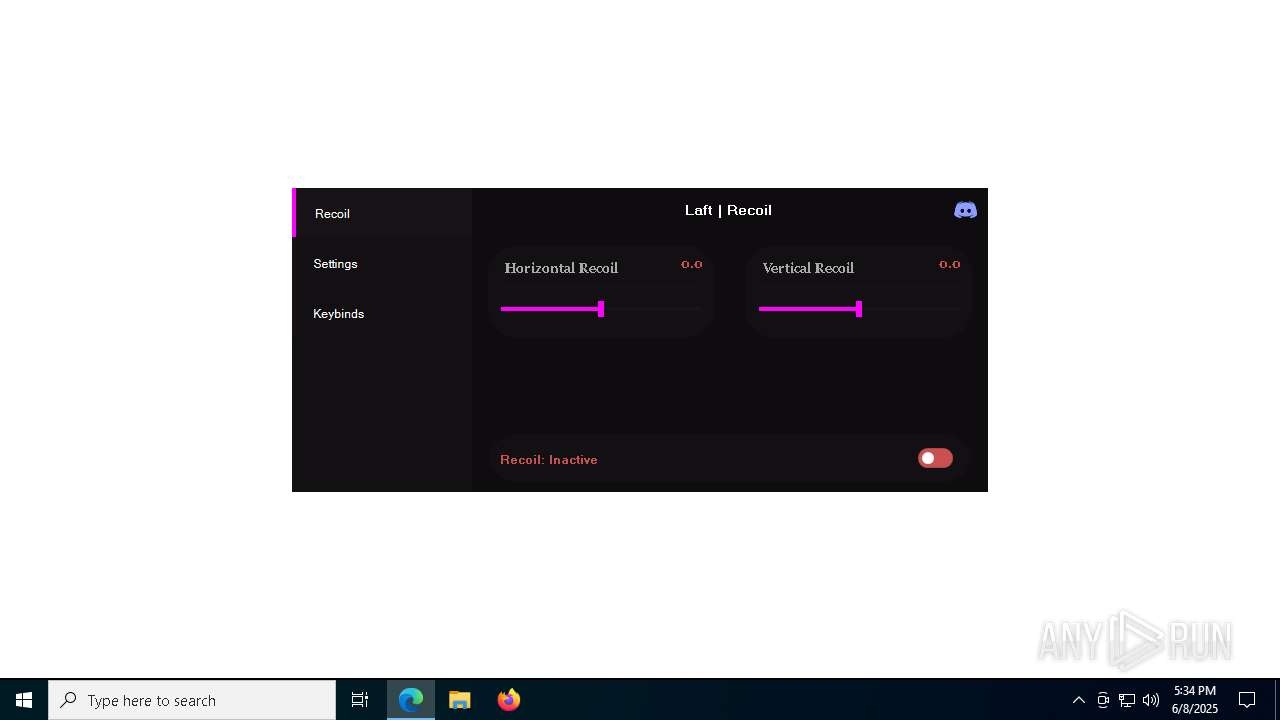
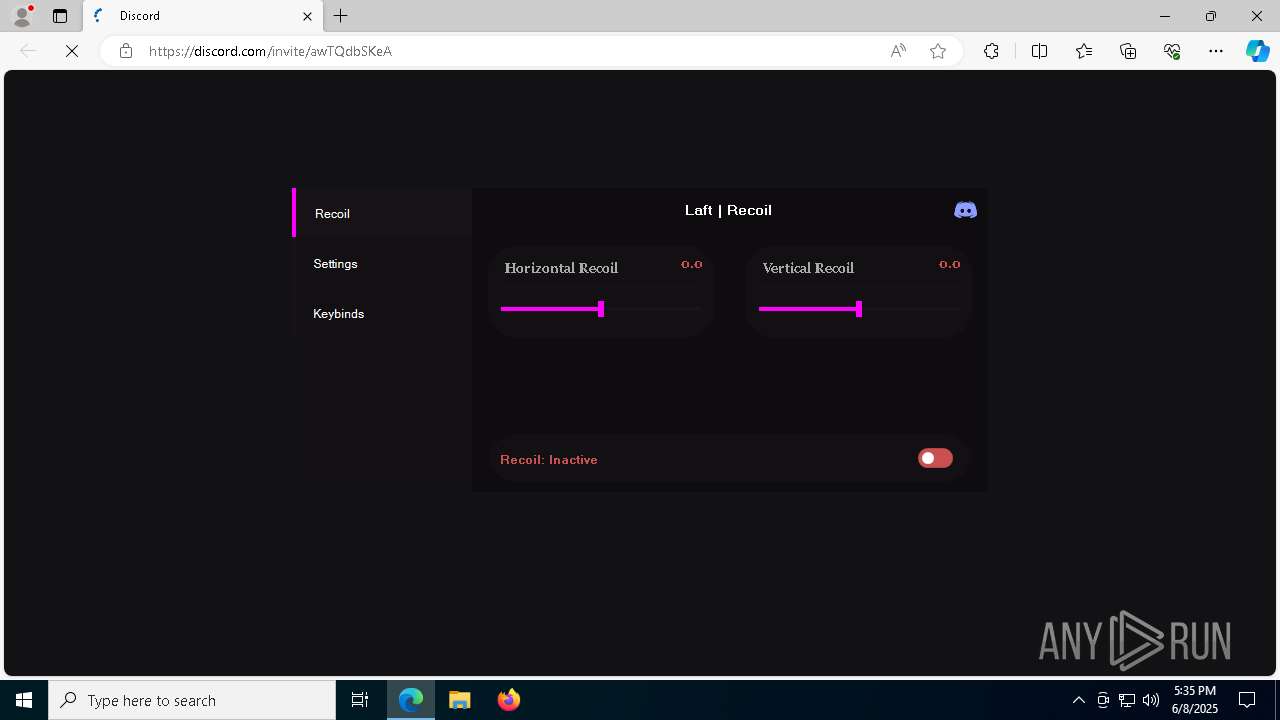
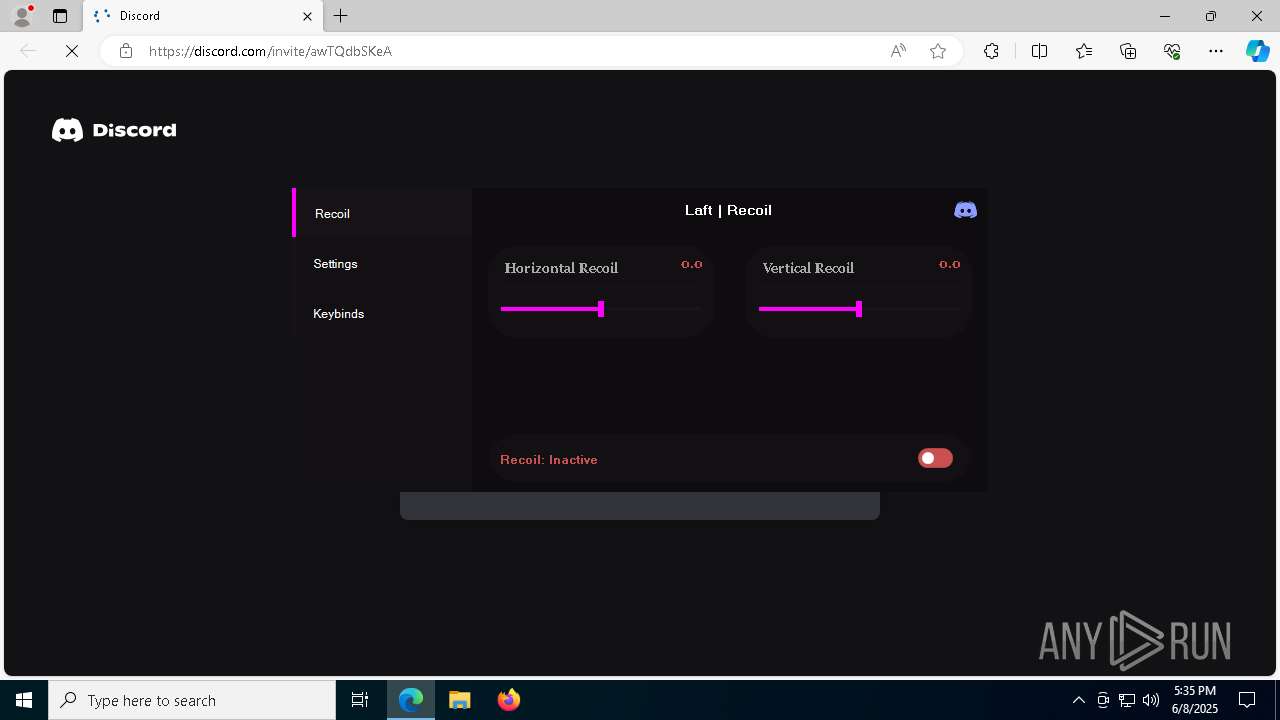
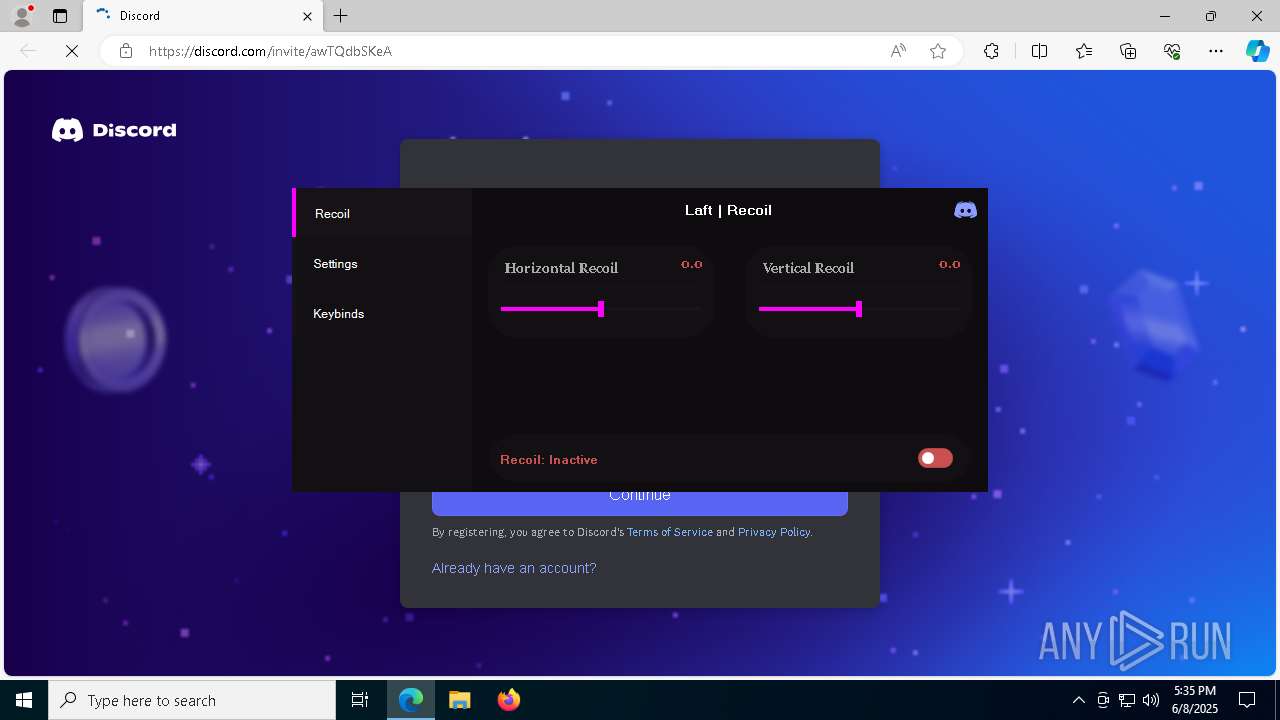
| File name: | Laft-Setup-4.8.exe |
| Full analysis: | https://app.any.run/tasks/491313b1-50f9-468f-baa7-afd401509568 |
| Verdict: | Malicious activity |
| Analysis date: | June 08, 2025, 17:33:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 11 sections |
| MD5: | 1856B45FEBF8D6154EBDBAC33EFD2439 |
| SHA1: | 8A6FFADD37A93B1BAF1D5D4E5F6779255E255917 |
| SHA256: | 067D1852E4237D4C6938BA9404144CE9A9F1CC81087047ED8FE561EF55EC985D |
| SSDEEP: | 786432:YlLykeGDYyf2R+i1H5exQB8pHenCSZ+XdQbDs:YlmkeCYyf8/H5exQGHenCSZ+tQbDs |
MALICIOUS
No malicious indicators.SUSPICIOUS
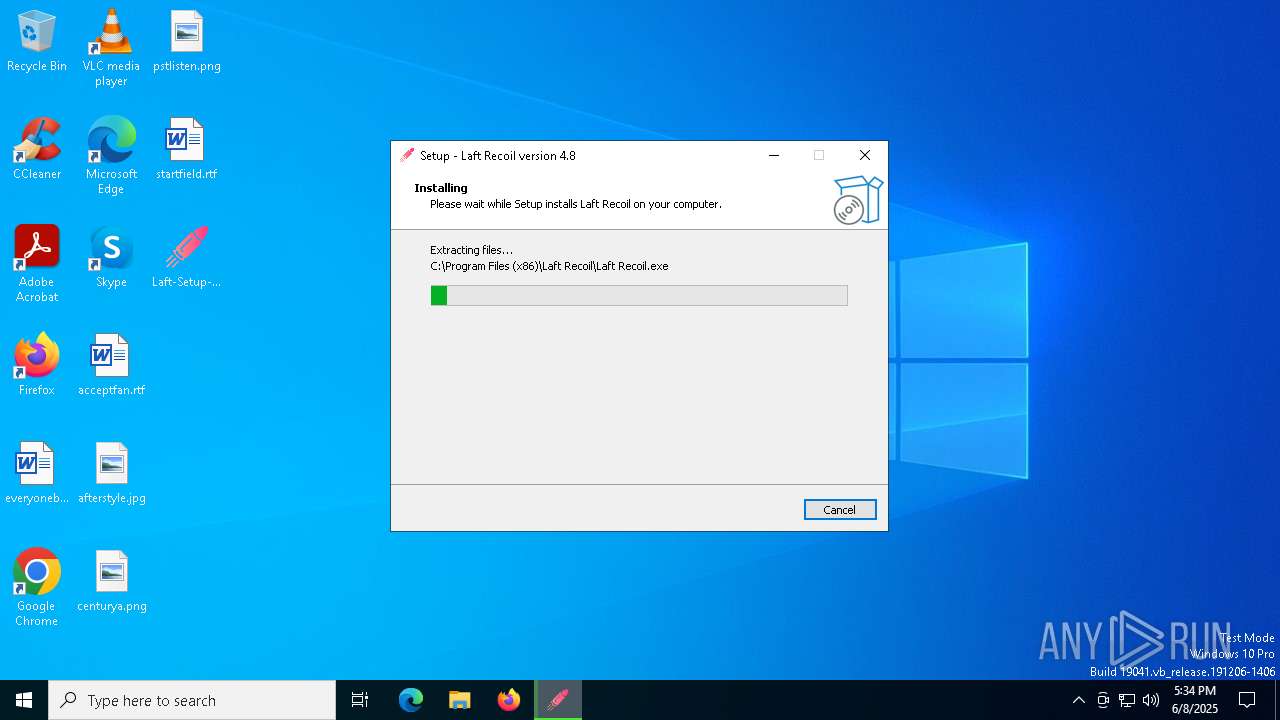
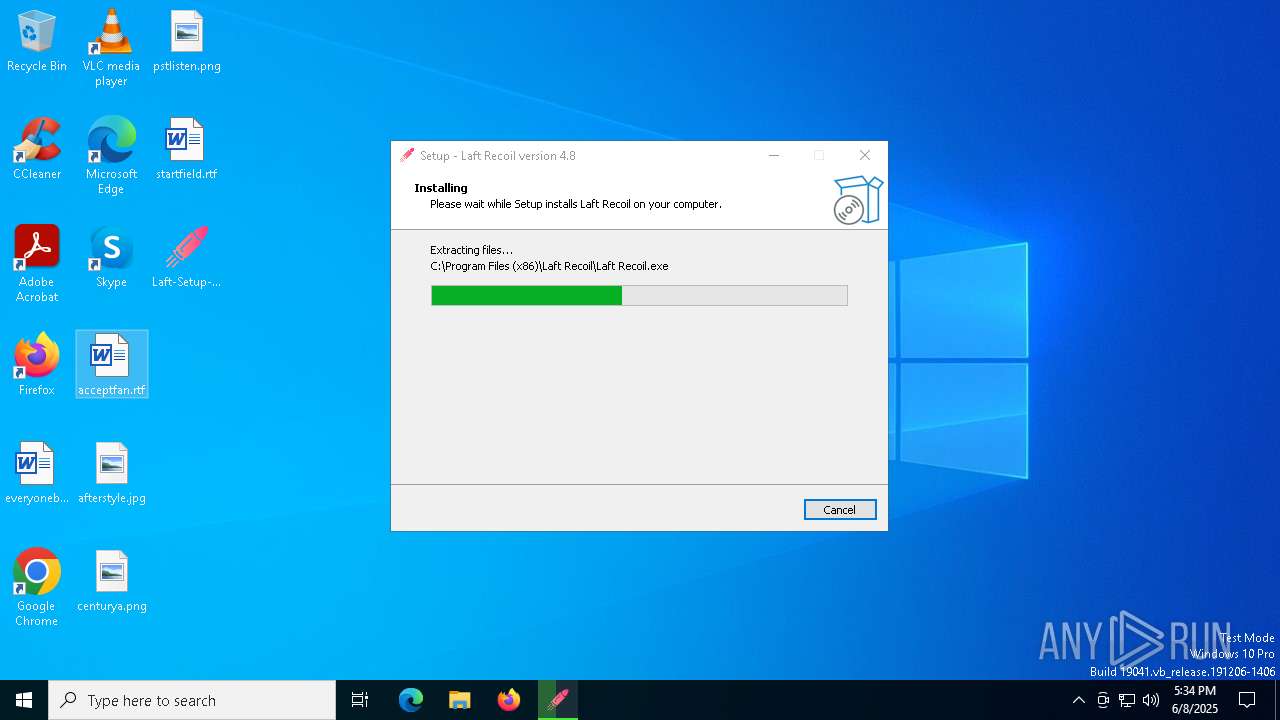
Executable content was dropped or overwritten
- Laft-Setup-4.8.exe (PID: 3968)
- Laft-Setup-4.8.tmp (PID: 7496)
- Laft-Setup-4.8.exe (PID: 5064)
Reads the Windows owner or organization settings
- Laft-Setup-4.8.tmp (PID: 7496)
Reads security settings of Internet Explorer
- Laft-Setup-4.8.tmp (PID: 7484)
- Laft Recoil.exe (PID: 4300)
The process drops C-runtime libraries
- Laft-Setup-4.8.tmp (PID: 7496)
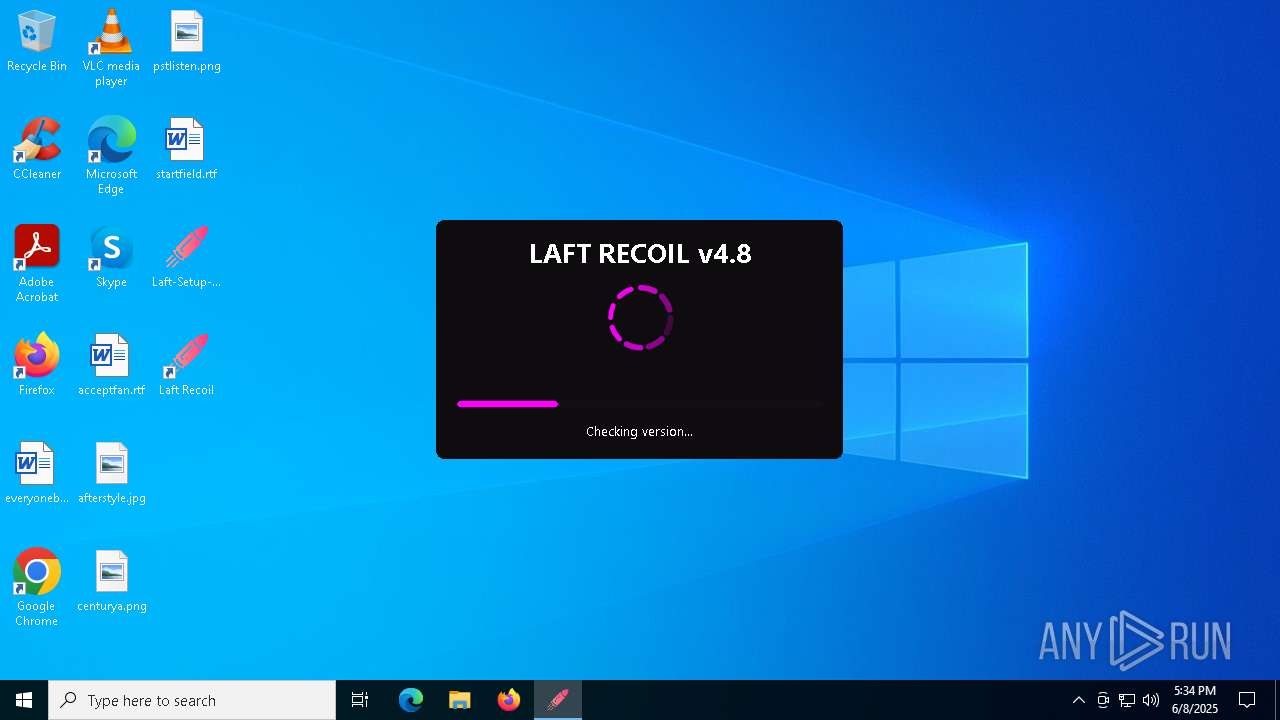
Checks for external IP
- Laft Recoil.exe (PID: 4300)
Potential Corporate Privacy Violation
- Laft Recoil.exe (PID: 4300)
Process drops legitimate windows executable
- Laft-Setup-4.8.tmp (PID: 7496)
INFO
Create files in a temporary directory
- Laft-Setup-4.8.exe (PID: 3968)
- Laft-Setup-4.8.exe (PID: 5064)
- Laft-Setup-4.8.tmp (PID: 7496)
- Laft Recoil.exe (PID: 4300)
Process checks computer location settings
- Laft-Setup-4.8.tmp (PID: 7484)
- Laft Recoil.exe (PID: 4300)
Checks supported languages
- Laft-Setup-4.8.exe (PID: 3968)
- Laft-Setup-4.8.tmp (PID: 7484)
- Laft-Setup-4.8.exe (PID: 5064)
- Laft-Setup-4.8.tmp (PID: 7496)
- Laft Recoil.exe (PID: 4300)
- identity_helper.exe (PID: 6900)
Reads the computer name
- Laft-Setup-4.8.tmp (PID: 7484)
- Laft-Setup-4.8.tmp (PID: 7496)
- Laft Recoil.exe (PID: 4300)
- identity_helper.exe (PID: 6900)
- Laft-Setup-4.8.exe (PID: 5064)
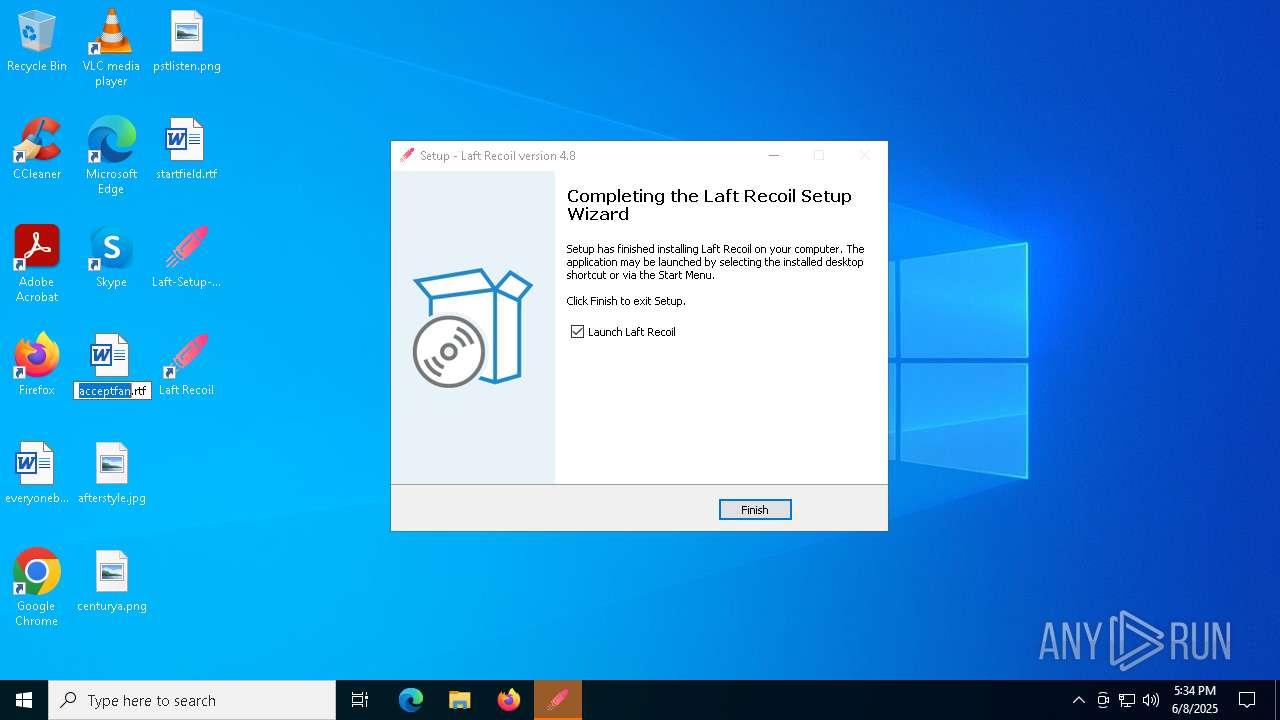
Detects InnoSetup installer (YARA)
- Laft-Setup-4.8.exe (PID: 3968)
- Laft-Setup-4.8.tmp (PID: 7484)
- Laft-Setup-4.8.exe (PID: 5064)
- Laft-Setup-4.8.tmp (PID: 7496)
Compiled with Borland Delphi (YARA)
- Laft-Setup-4.8.tmp (PID: 7484)
- Laft-Setup-4.8.exe (PID: 3968)
- Laft-Setup-4.8.exe (PID: 5064)
- Laft-Setup-4.8.tmp (PID: 7496)
The sample compiled with english language support
- Laft-Setup-4.8.tmp (PID: 7496)
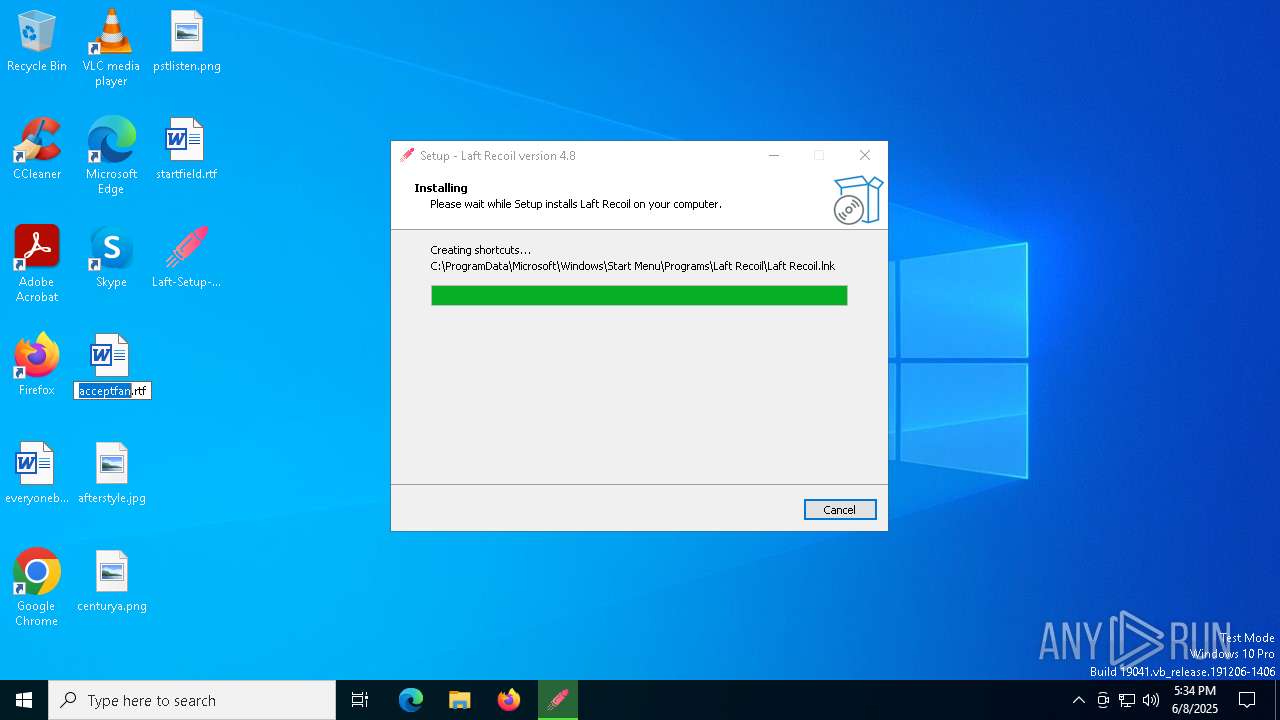
Creates a software uninstall entry
- Laft-Setup-4.8.tmp (PID: 7496)
Creates files in the program directory
- Laft Recoil.exe (PID: 4300)
- Laft-Setup-4.8.tmp (PID: 7496)
Reads the software policy settings
- Laft Recoil.exe (PID: 4300)
- slui.exe (PID: 208)
Checks proxy server information
- Laft Recoil.exe (PID: 4300)
- slui.exe (PID: 208)
Reads the machine GUID from the registry
- Laft Recoil.exe (PID: 4300)
Application launched itself
- msedge.exe (PID: 7852)
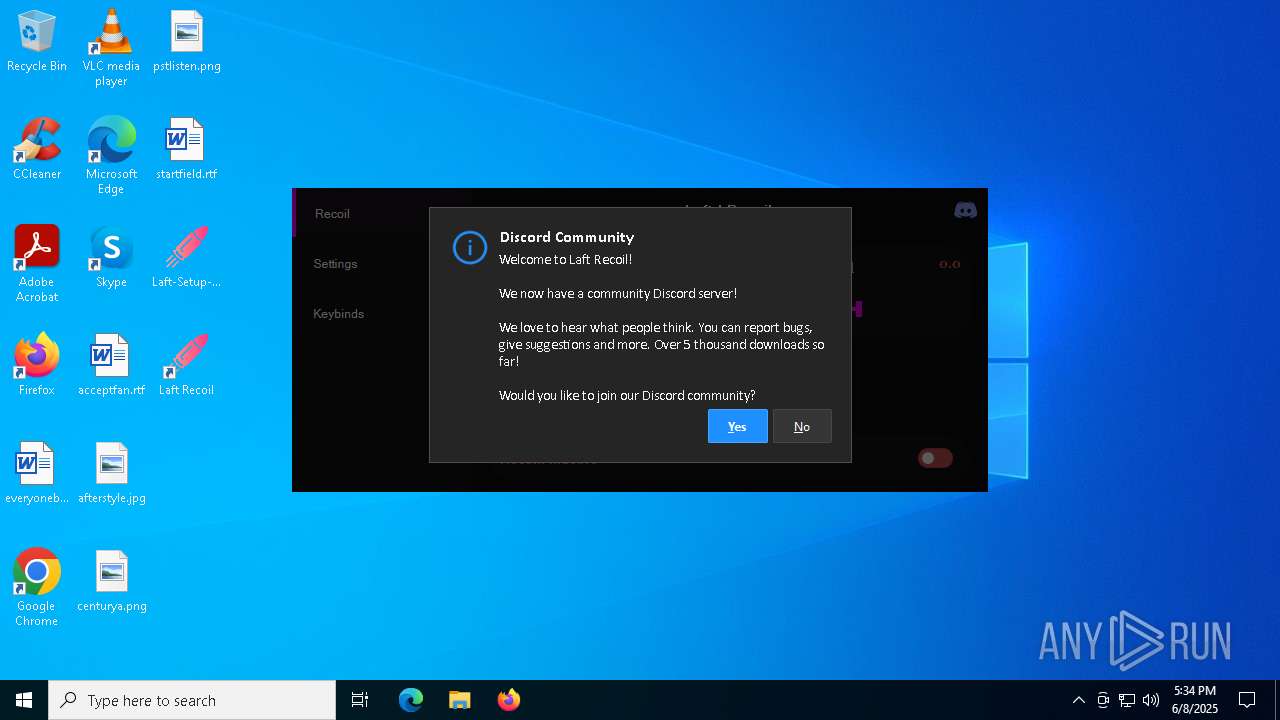
Attempting to use instant messaging service
- msedge.exe (PID: 8088)
Reads Environment values
- identity_helper.exe (PID: 6900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (65.1) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (24.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.9) |
| .exe | | | Win32 Executable (generic) (2.6) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:03:13 06:55:45+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 704512 |
| InitializedDataSize: | 121344 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xacfe0 |
| OSVersion: | 6.1 |
| ImageVersion: | - |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | SafyTools |
| FileDescription: | Laft Recoil Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | Laft Recoil |
| ProductVersion: | 4.8 |
Total processes
167
Monitored processes
44
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=video_capture.mojom.VideoCaptureService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5544 --field-trial-handle=2372,i,6127870024676318782,2562241164482293864,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 660 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5984 --field-trial-handle=2372,i,6127870024676318782,2562241164482293864,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5916 --field-trial-handle=2372,i,6127870024676318782,2562241164482293864,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3856 --field-trial-handle=2372,i,6127870024676318782,2562241164482293864,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6000 --field-trial-handle=2372,i,6127870024676318782,2562241164482293864,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2772 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5408 --field-trial-handle=2372,i,6127870024676318782,2562241164482293864,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2896 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=7272 --field-trial-handle=2372,i,6127870024676318782,2562241164482293864,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2908 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3476 --field-trial-handle=2372,i,6127870024676318782,2562241164482293864,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3016 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6800 --field-trial-handle=2372,i,6127870024676318782,2562241164482293864,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
12 456
Read events
12 412
Write events
44
Delete events
0
Modification events
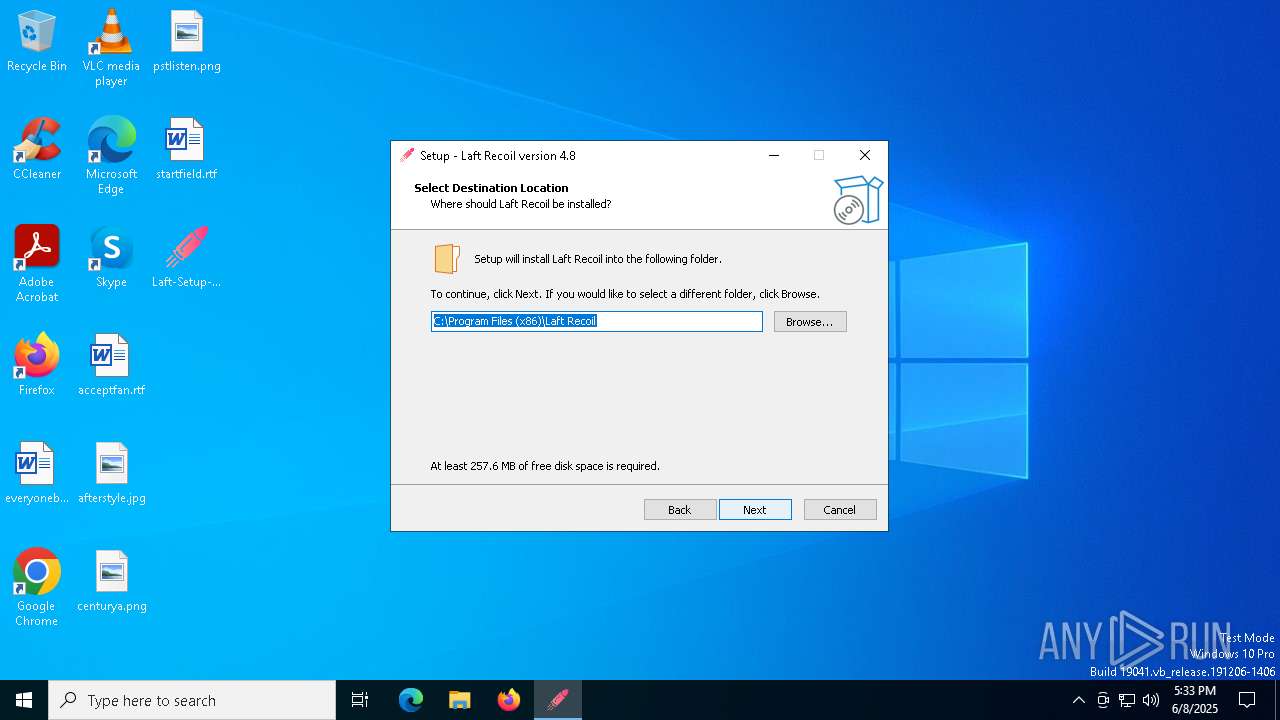
| (PID) Process: | (7496) Laft-Setup-4.8.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{F8D91E42-8C2D-4AC3-B76A-C7E0E2857421}}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.4.2 | |||
| (PID) Process: | (7496) Laft-Setup-4.8.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{F8D91E42-8C2D-4AC3-B76A-C7E0E2857421}}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files (x86)\Laft Recoil | |||
| (PID) Process: | (7496) Laft-Setup-4.8.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{F8D91E42-8C2D-4AC3-B76A-C7E0E2857421}}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files (x86)\Laft Recoil\ | |||
| (PID) Process: | (7496) Laft-Setup-4.8.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{F8D91E42-8C2D-4AC3-B76A-C7E0E2857421}}_is1 |
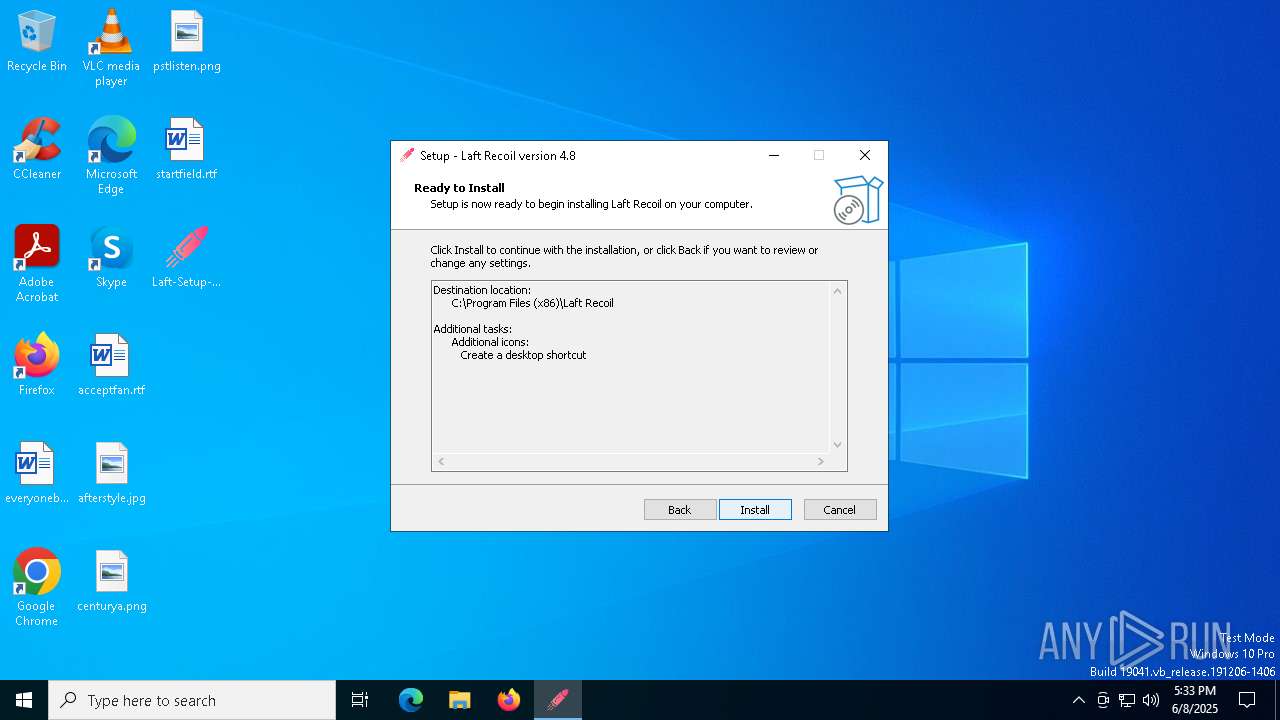
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Laft Recoil | |||
| (PID) Process: | (7496) Laft-Setup-4.8.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{F8D91E42-8C2D-4AC3-B76A-C7E0E2857421}}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (7496) Laft-Setup-4.8.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{F8D91E42-8C2D-4AC3-B76A-C7E0E2857421}}_is1 |
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: desktopicon | |||
| (PID) Process: | (7496) Laft-Setup-4.8.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{F8D91E42-8C2D-4AC3-B76A-C7E0E2857421}}_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: | |||
| (PID) Process: | (7496) Laft-Setup-4.8.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{F8D91E42-8C2D-4AC3-B76A-C7E0E2857421}}_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: english | |||
| (PID) Process: | (7496) Laft-Setup-4.8.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{F8D91E42-8C2D-4AC3-B76A-C7E0E2857421}}_is1 |
| Operation: | write | Name: | DisplayName |
Value: Laft Recoil | |||
| (PID) Process: | (7496) Laft-Setup-4.8.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{F8D91E42-8C2D-4AC3-B76A-C7E0E2857421}}_is1 |
| Operation: | write | Name: | DisplayIcon |
Value: .\bullet.ico | |||
Executable files
23
Suspicious files
340
Text files
15
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7496 | Laft-Setup-4.8.tmp | C:\Program Files (x86)\Laft Recoil\is-GVUHN.tmp | — | |
MD5:— | SHA256:— | |||
| 7496 | Laft-Setup-4.8.tmp | C:\Program Files (x86)\Laft Recoil\Laft Recoil.exe | — | |
MD5:— | SHA256:— | |||
| 3968 | Laft-Setup-4.8.exe | C:\Users\admin\AppData\Local\Temp\is-EA7ND.tmp\Laft-Setup-4.8.tmp | executable | |
MD5:A532B76EA432F3E5E38BB2EBEF0A1A10 | SHA256:7C9C1EEBF37C123E56CEDC2DA2AA204B8DFF5FC3F96B5BEC6DAE187BBC920162 | |||
| 7496 | Laft-Setup-4.8.tmp | C:\Program Files (x86)\Laft Recoil\is-NV6LA.tmp | executable | |
MD5:183763CD15CBACA2E3837D56F5F6FA74 | SHA256:18C96F5A1AAC13418E6D1A449985620D70AD29CA3905737123EC803AC2469731 | |||
| 7496 | Laft-Setup-4.8.tmp | C:\Users\admin\AppData\Local\Temp\is-3BM0J.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 5064 | Laft-Setup-4.8.exe | C:\Users\admin\AppData\Local\Temp\is-B3HTH.tmp\Laft-Setup-4.8.tmp | executable | |
MD5:A532B76EA432F3E5E38BB2EBEF0A1A10 | SHA256:7C9C1EEBF37C123E56CEDC2DA2AA204B8DFF5FC3F96B5BEC6DAE187BBC920162 | |||
| 7496 | Laft-Setup-4.8.tmp | C:\Program Files (x86)\Laft Recoil\unins000.exe | executable | |
MD5:A9ACC44395AA48E86C74586A1DDD322A | SHA256:558D47A9082C4FB31276E6E8C927C736009928F66D1DE67B11EDDF700A643A1A | |||
| 7496 | Laft-Setup-4.8.tmp | C:\Program Files (x86)\Laft Recoil\is-EL82D.tmp | executable | |
MD5:A9ACC44395AA48E86C74586A1DDD322A | SHA256:558D47A9082C4FB31276E6E8C927C736009928F66D1DE67B11EDDF700A643A1A | |||
| 7852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF133636.TMP | — | |
MD5:— | SHA256:— | |||
| 7496 | Laft-Setup-4.8.tmp | C:\Program Files (x86)\Laft Recoil\bullet.ico | image | |
MD5:F79D7F99AAFE585CD82F359236004400 | SHA256:F9E867FC915C75298284C978FD40FEA22D8433FB1E35D74BFD795A451C39841F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
256
TCP/UDP connections
76
DNS requests
53
Threats
62
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
— | — | GET | 200 | 104.26.13.205:443 | https://api.ipify.org/ | US | text | 13 b | malicious |
— | — | GET | 200 | 172.67.74.152:443 | https://api.ipify.org/ | US | text | 13 b | malicious |
— | — | GET | 200 | 104.26.13.205:443 | https://api.ipify.org/ | US | text | 13 b | malicious |
— | — | GET | 200 | 104.26.12.205:443 | https://api.ipify.org/ | US | text | 13 b | malicious |
— | — | GET | 200 | 64.233.167.84:443 | https://laft-832d0-default-rtdb.firebaseio.com/users.json?auth=AIzaSyAStwwjBFncDBGPKCBoaugi5eiC7G28E88 | US | binary | 1.12 Mb | whitelisted |
— | — | GET | 200 | 142.250.185.170:443 | https://firestore.googleapis.com/v1/projects/laft-832d0/databases/(default)/documents/admin_settings/app_status | US | binary | 368 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7680 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4300 | Laft Recoil.exe | 104.26.12.205:443 | api.ipify.org | CLOUDFLARENET | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
api.ipify.org |
| shared |
firestore.googleapis.com |
| whitelisted |
laft-832d0-default-rtdb.firebaseio.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
4300 | Laft Recoil.exe | Potential Corporate Privacy Violation | ET INFO Possible IP Check api.ipify.org |
4300 | Laft Recoil.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
— | — | Device Retrieving External IP Address Detected | ET INFO External IP Lookup api.ipify.org |
— | — | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External IP Lookup by HTTP (api .ipify .org) |
— | — | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
— | — | Device Retrieving External IP Address Detected | ET INFO External IP Lookup api.ipify.org |
— | — | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External IP Lookup by HTTP (api .ipify .org) |
— | — | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
— | — | Device Retrieving External IP Address Detected | ET INFO External IP Lookup api.ipify.org |