| download: | index.html |
| Full analysis: | https://app.any.run/tasks/571f65c7-6298-4116-9783-1d374a25214f |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2020, 20:56:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | 7DCBA60D89BD6E8339361A029158ED2C |
| SHA1: | A873B6203F20797CE114DD29B2FF9B62AA2A4940 |
| SHA256: | 067C5735B2E44CB31E576F7885E48521935CADCBC2B441E35A3D6CD753367DC9 |
| SSDEEP: | 384:yz4C0FlLL36l4ebeg3sIC/rbZfUxqIH0UbI/QyzfpfaSweYMIuH:yz4bBLqpbeg2fRUxzH0MI//z43e8Y |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2860)
INFO
Application launched itself
- chrome.exe (PID: 2860)
- iexplore.exe (PID: 896)
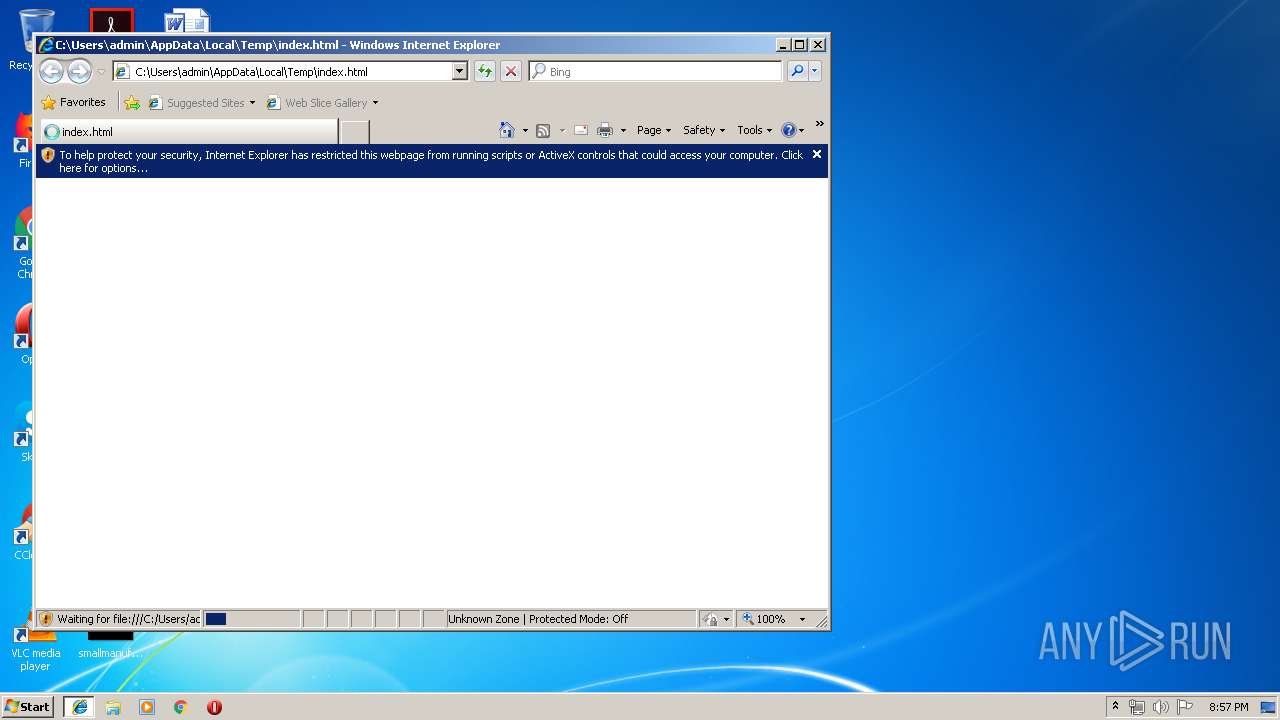
Changes internet zones settings
- iexplore.exe (PID: 896)
Reads the hosts file
- chrome.exe (PID: 2860)
- chrome.exe (PID: 1724)
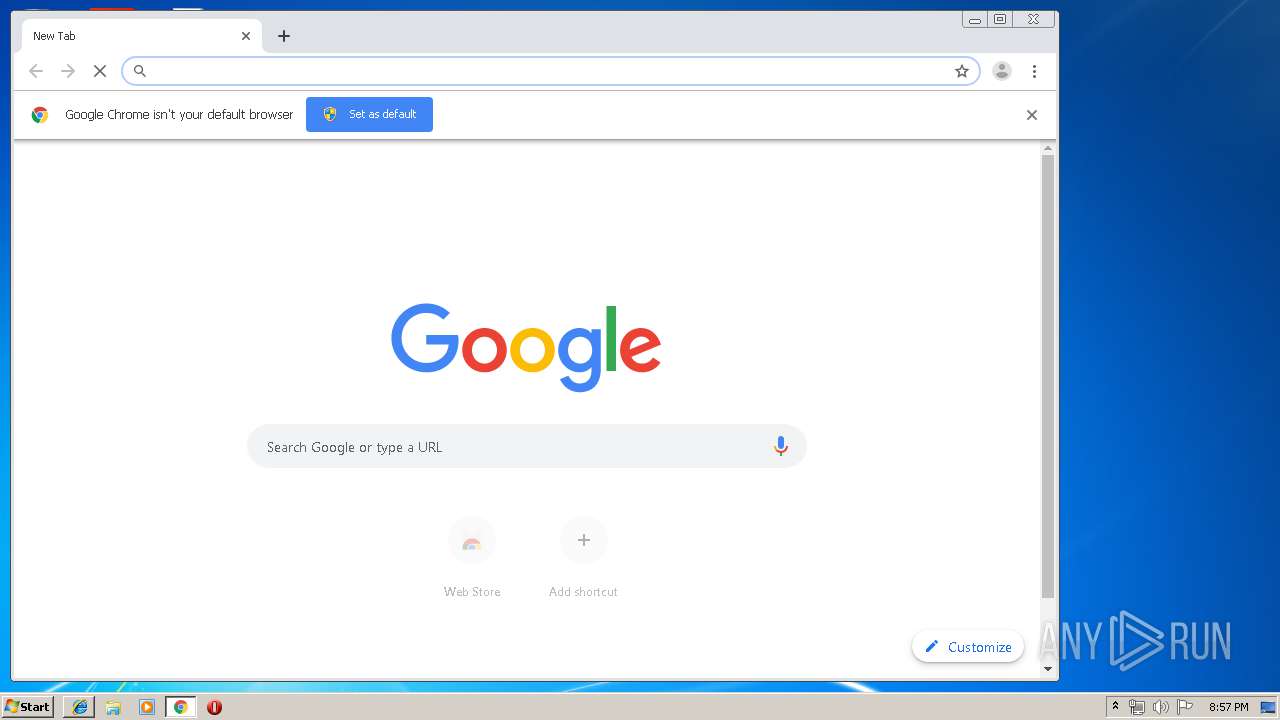
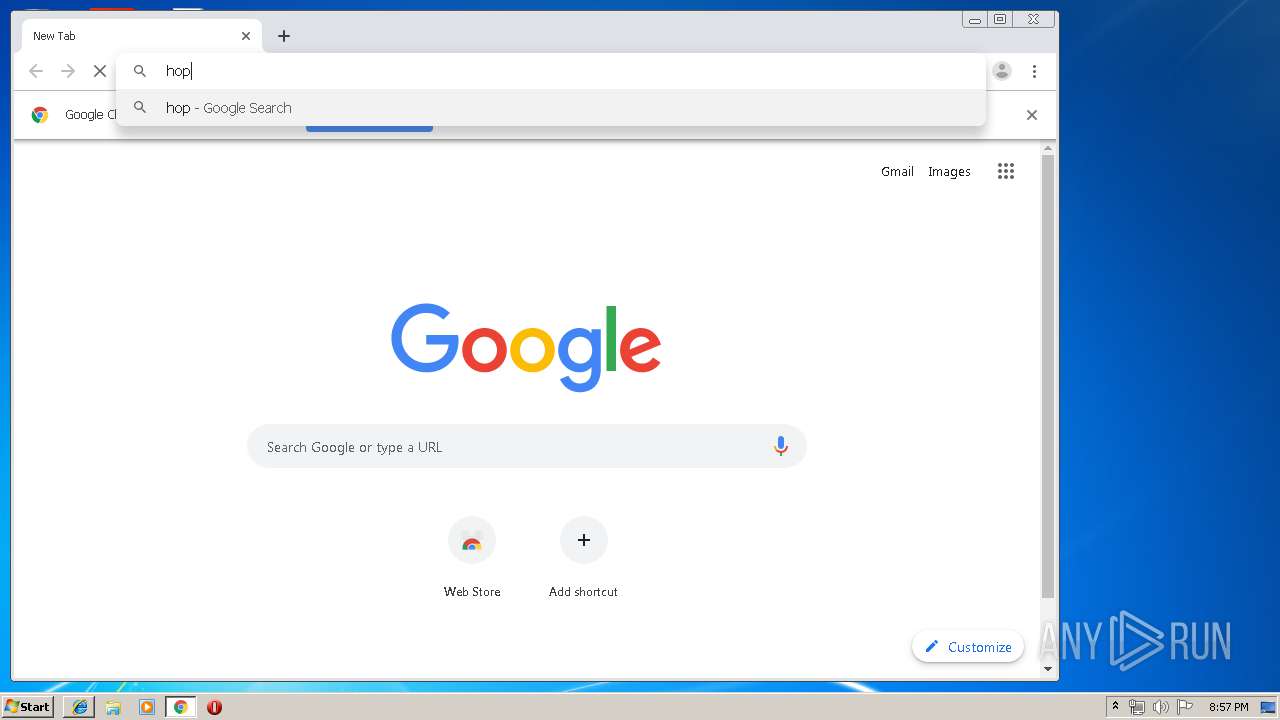
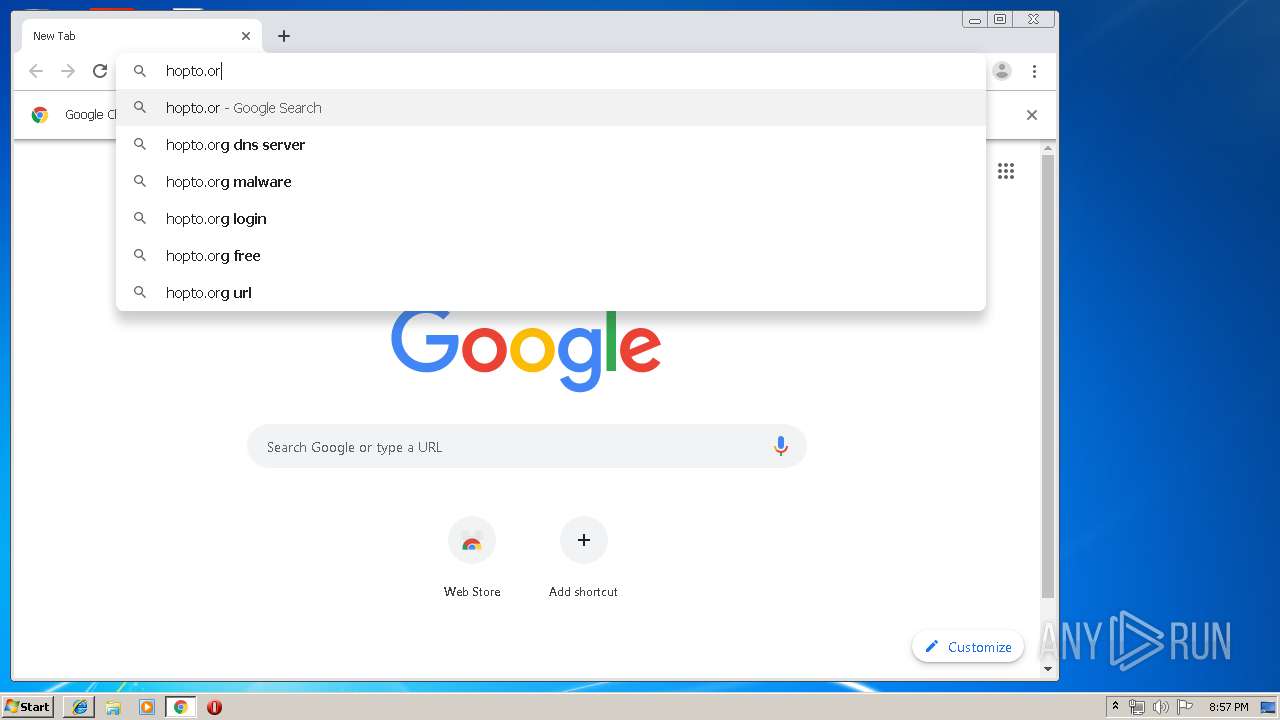
Manual execution by user
- chrome.exe (PID: 2860)
Reads internet explorer settings
- iexplore.exe (PID: 2556)
Reads Internet Cache Settings
- iexplore.exe (PID: 2556)
Creates files in the user directory
- iexplore.exe (PID: 2556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
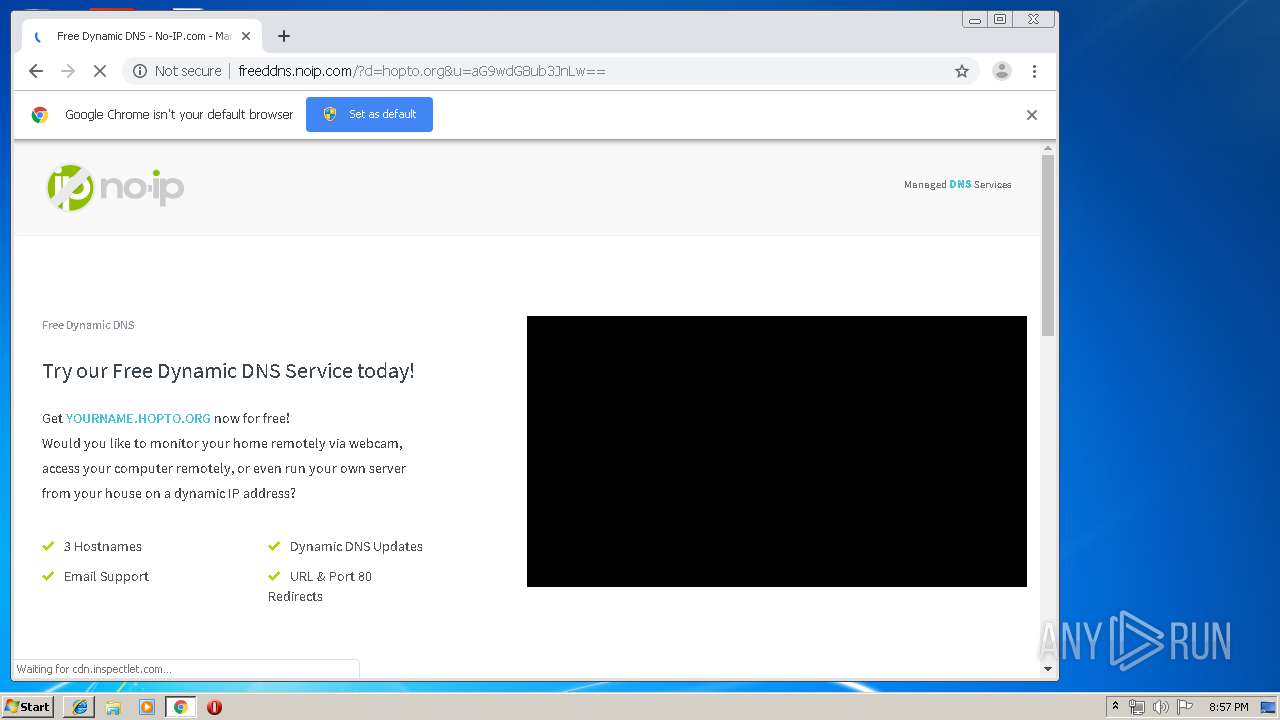
| Title: | Free Dynamic DNS - No-IP.com - Managed DNS Services |
|---|
Total processes
78
Monitored processes
43
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,6593063078537325953,15303477680397975639,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17165619098929225921 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3392 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,6593063078537325953,15303477680397975639,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13325046813395390680 --mojo-platform-channel-handle=4108 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,6593063078537325953,15303477680397975639,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12710667485168550486 --mojo-platform-channel-handle=4100 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1048 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,6593063078537325953,15303477680397975639,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6738549559007895657 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2452 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,6593063078537325953,15303477680397975639,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15748754158621884630 --mojo-platform-channel-handle=4156 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,6593063078537325953,15303477680397975639,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16051132274934675426 --mojo-platform-channel-handle=4772 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,6593063078537325953,15303477680397975639,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=16138864026535568 --mojo-platform-channel-handle=1624 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,6593063078537325953,15303477680397975639,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4502092531678724369 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2200 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,6593063078537325953,15303477680397975639,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1819114197629873844 --mojo-platform-channel-handle=4408 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
943
Read events
791
Write events
147
Delete events
5
Modification events
| (PID) Process: | (896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {E312D4CF-396B-11EA-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E4070100050011001400380035003002 | |||
Executable files
0
Suspicious files
49
Text files
343
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 896 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 896 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\90d2a4f5-cffc-4d6f-b0ae-83d9c48b3aef.tmp | — | |
MD5:— | SHA256:— | |||
| 2860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF3a31d3.TMP | text | |
MD5:— | SHA256:— | |||
| 2860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF3a31c4.TMP | text | |
MD5:— | SHA256:— | |||
| 2860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF3a31c4.TMP | text | |
MD5:— | SHA256:— | |||
| 2860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
81
DNS requests
53
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
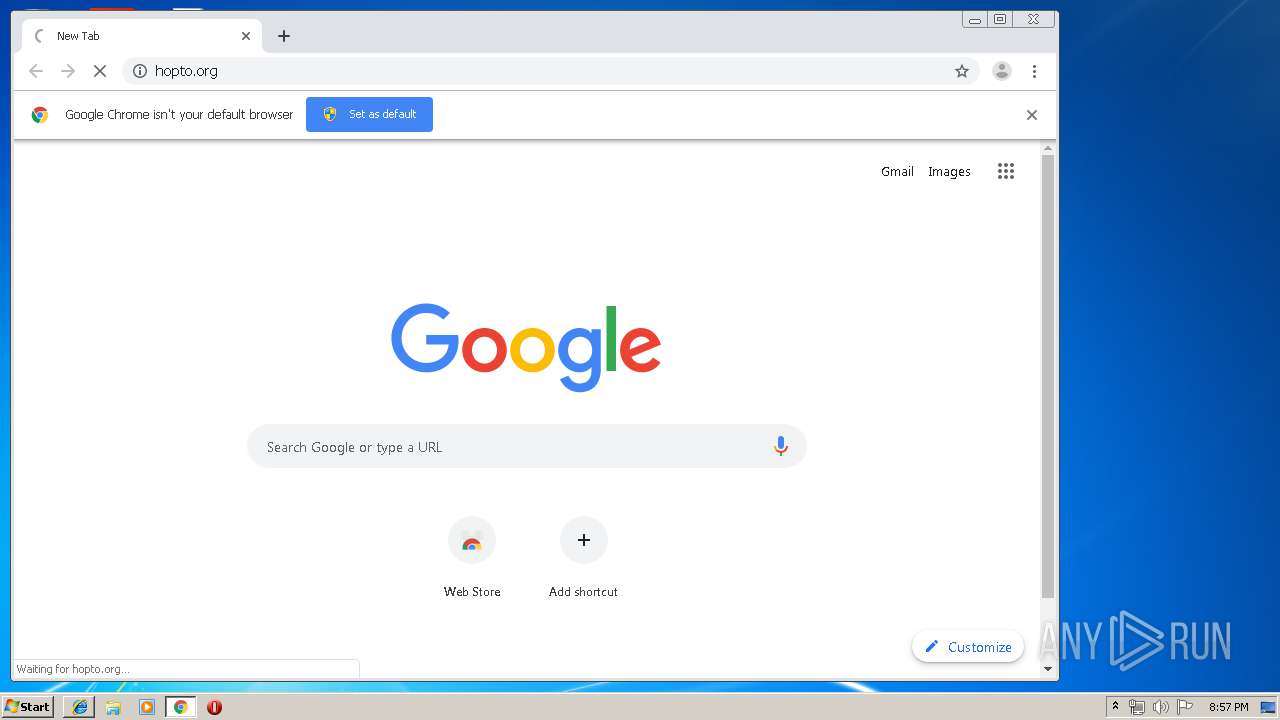
1724 | chrome.exe | GET | 301 | 8.23.224.108:80 | http://hopto.org/ | US | — | — | suspicious |
1724 | chrome.exe | GET | 301 | 172.217.21.238:80 | http://www.youtube.com/embed/HHK6bZeLhME?rel=0&autohide=1&showinfo=0&wmode=Opaque&wmode=transparent | US | — | — | whitelisted |
1724 | chrome.exe | GET | 200 | 172.217.16.194:80 | http://www.googleadservices.com/pagead/conversion.js | US | text | 9.62 Kb | whitelisted |
1724 | chrome.exe | GET | 200 | 13.35.254.61:80 | http://d2np5nlsc31ci5.cloudfront.net/assets/build/css/shortstar.css?id=6a6c85b87acc73c4ca8b | US | text | 73.7 Kb | whitelisted |
1724 | chrome.exe | GET | 200 | 216.58.206.14:80 | http://translate.google.com/translate_a/element.js?cb=googleTranslateElementInit | US | text | 798 b | whitelisted |
1724 | chrome.exe | GET | 200 | 13.35.254.61:80 | http://d2np5nlsc31ci5.cloudfront.net/assets/build/js/shortstar.js?id=00ce438aefa7441dd996 | US | text | 68.9 Kb | whitelisted |
1724 | chrome.exe | GET | 200 | 8.23.224.108:80 | http://freeddns.noip.com/?d=hopto.org&u=aG9wdG8ub3JnLw== | US | html | 11.0 Kb | suspicious |
1724 | chrome.exe | GET | 200 | 204.79.197.200:80 | http://bat.bing.com/bat.js | US | text | 6.98 Kb | whitelisted |
1724 | chrome.exe | GET | 204 | 204.79.197.200:80 | http://bat.bing.com/action/0?ti=56003172&Ver=2&mid=c11769ce-05c1-ba78-07bb-9a63b39745f3&pi=1200101525&lg=en-US&sw=1280&sh=720&sc=24&tl=Free%20Dynamic%20DNS%20-%20No-IP.com%20-%20Managed%20DNS%20Services&p=http%3A%2F%2Ffreeddns.noip.com%2F%3Fd%3Dhopto.org%26u%3DaG9wdG8ub3JnLw%3D%3D&r=<=2298&evt=pageLoad&msclkid=N&rn=406555 | US | compressed | 6.98 Kb | whitelisted |
1724 | chrome.exe | GET | 302 | 216.58.210.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 13.35.254.144:445 | d2np5nlsc31ci5.cloudfront.net | — | US | unknown |
896 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4 | System | 13.35.254.97:445 | d2np5nlsc31ci5.cloudfront.net | — | US | malicious |
4 | System | 13.35.254.61:445 | d2np5nlsc31ci5.cloudfront.net | — | US | malicious |
4 | System | 13.35.254.61:139 | d2np5nlsc31ci5.cloudfront.net | — | US | malicious |
4 | System | 172.217.18.168:139 | www.googletagmanager.com | Google Inc. | US | whitelisted |
1724 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1724 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
1724 | chrome.exe | 216.239.36.117:443 | www.google.com.ua | Google Inc. | US | whitelisted |
1724 | chrome.exe | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
d2np5nlsc31ci5.cloudfront.net |
| whitelisted |
www.bing.com |
| whitelisted |
dns.msftncsi.com |
| shared |
www.googletagmanager.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
16 ETPRO signatures available at the full report