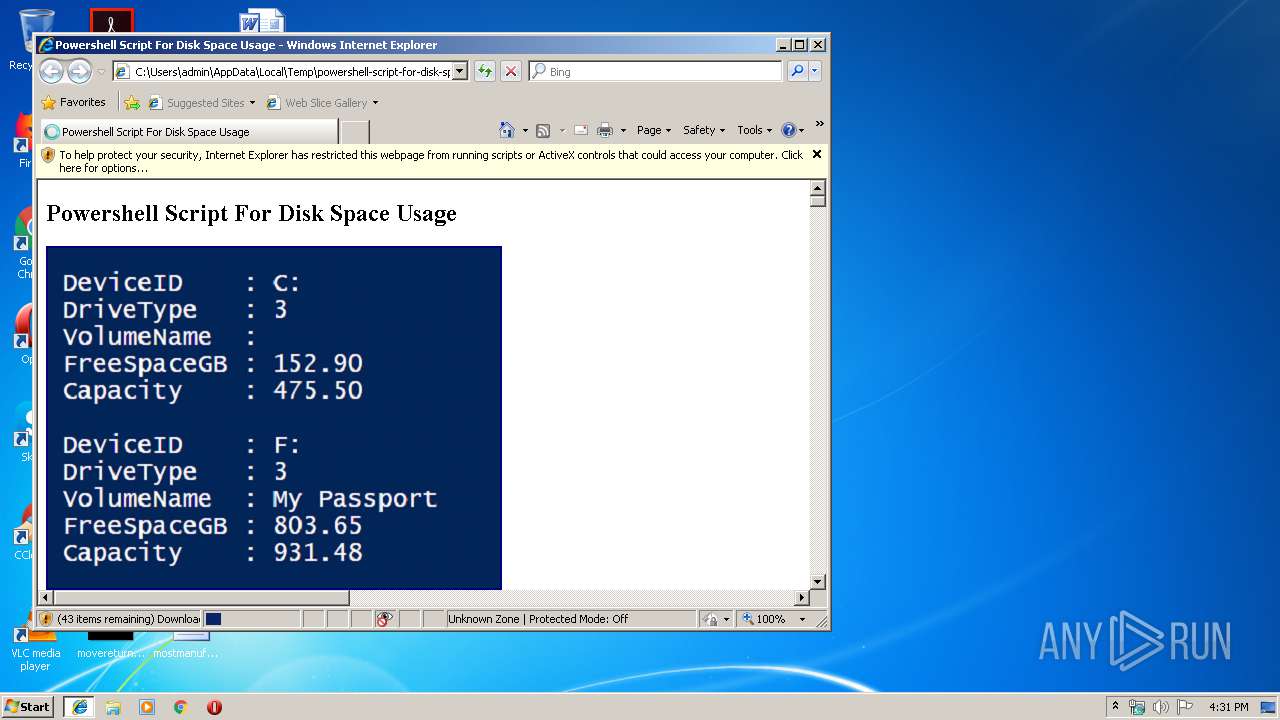
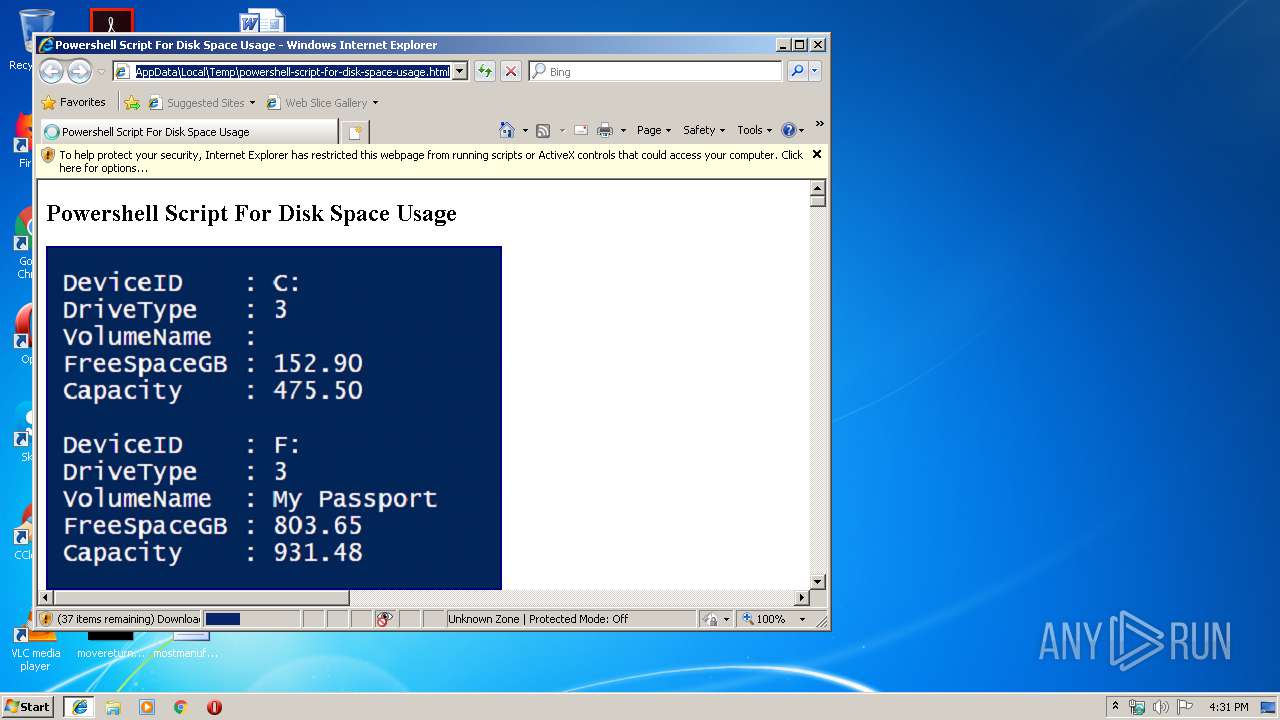
| download: | powershell-script-for-disk-space-usage.html |
| Full analysis: | https://app.any.run/tasks/021d9b12-a8c3-4f45-9306-b391e043eac6 |
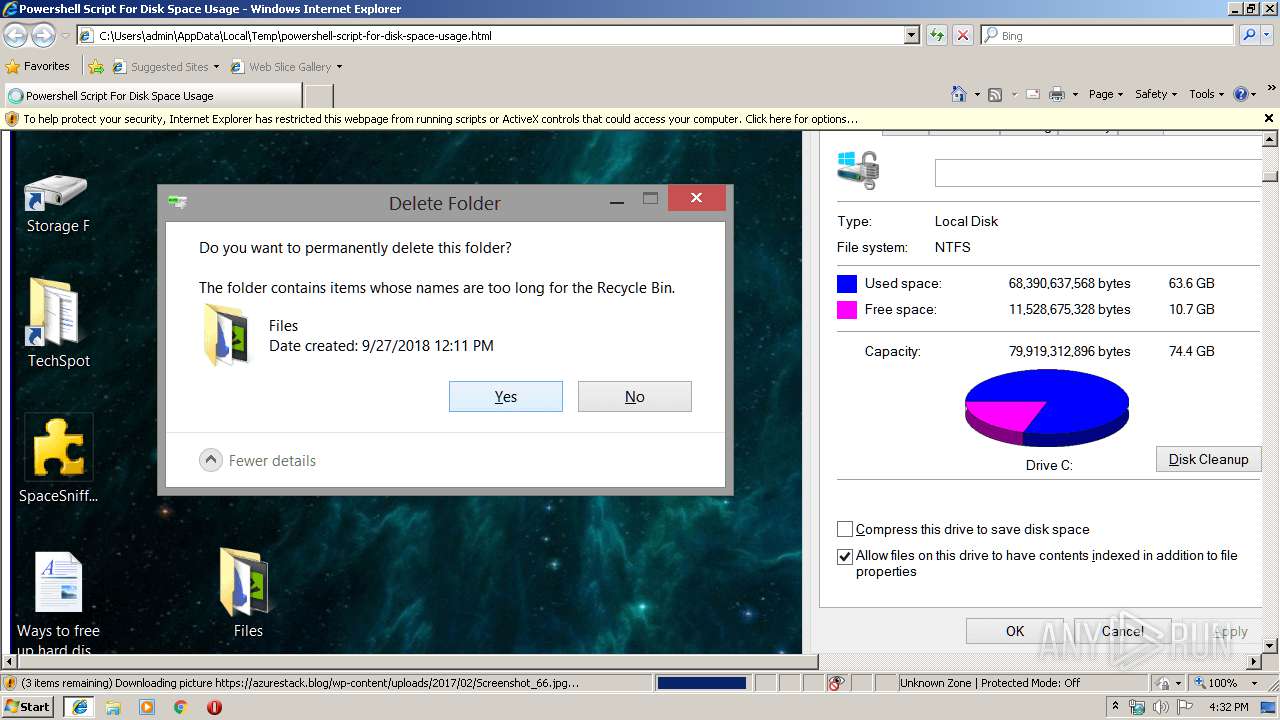
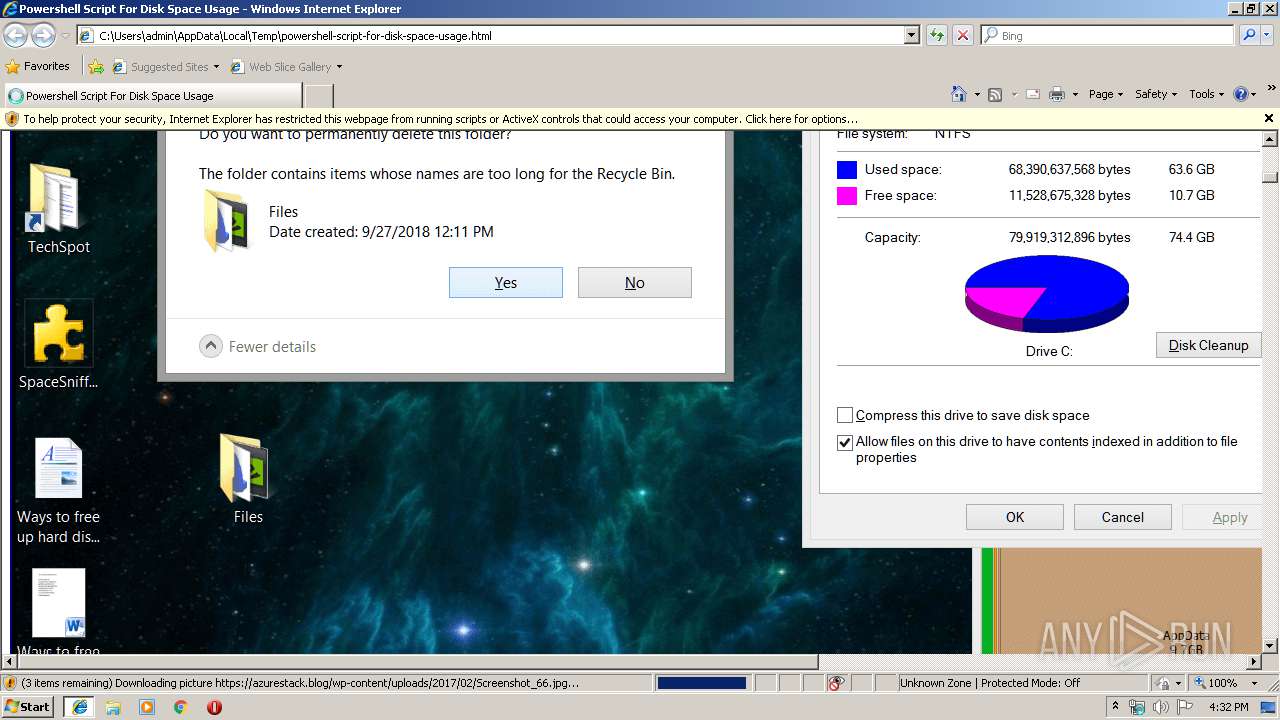
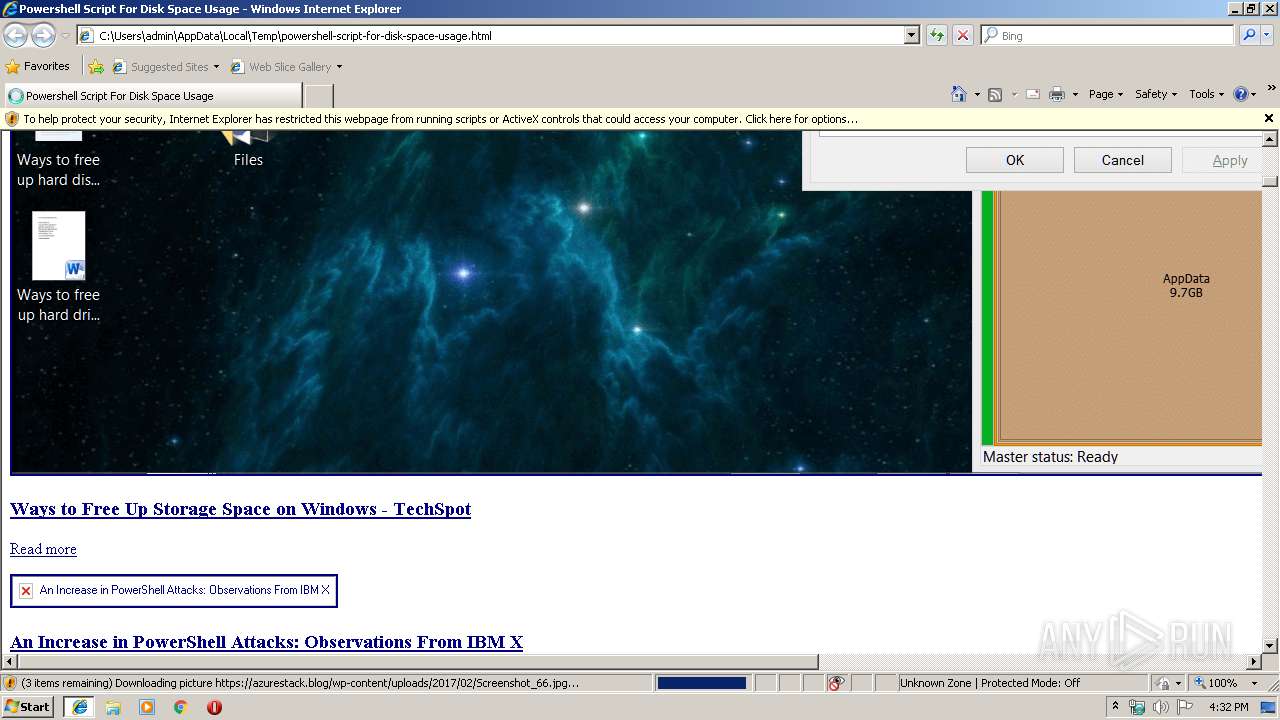
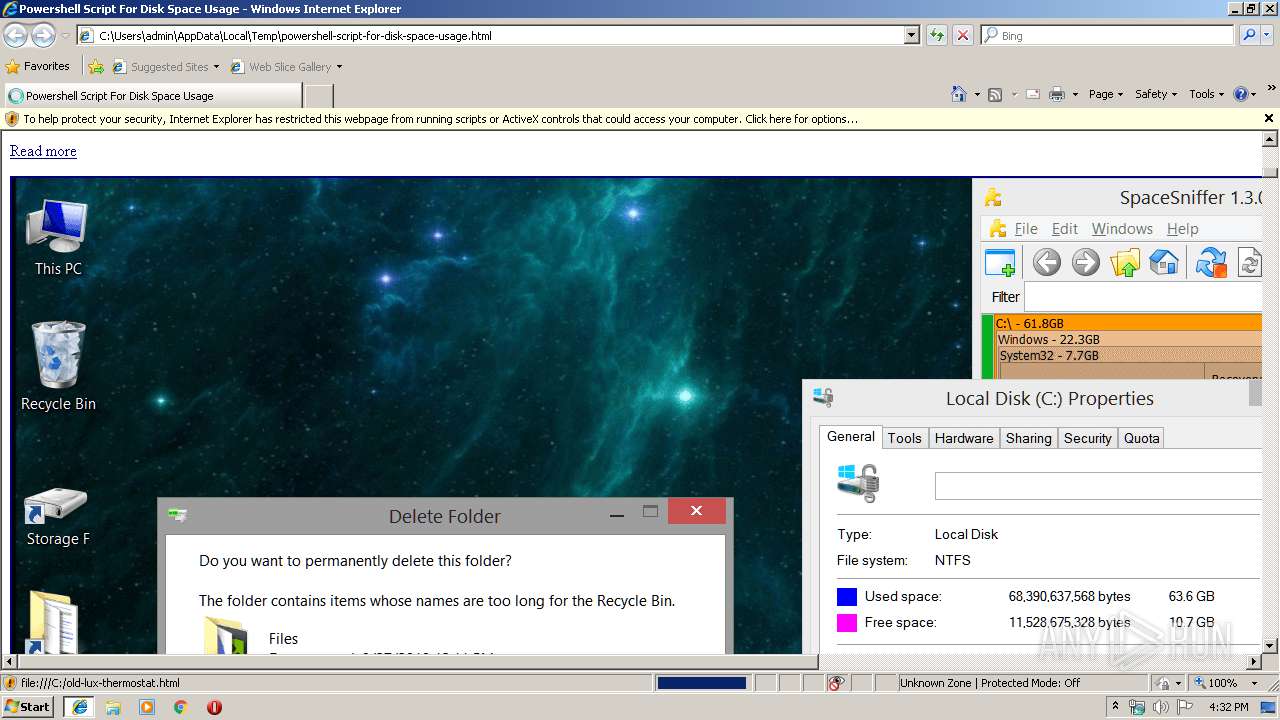
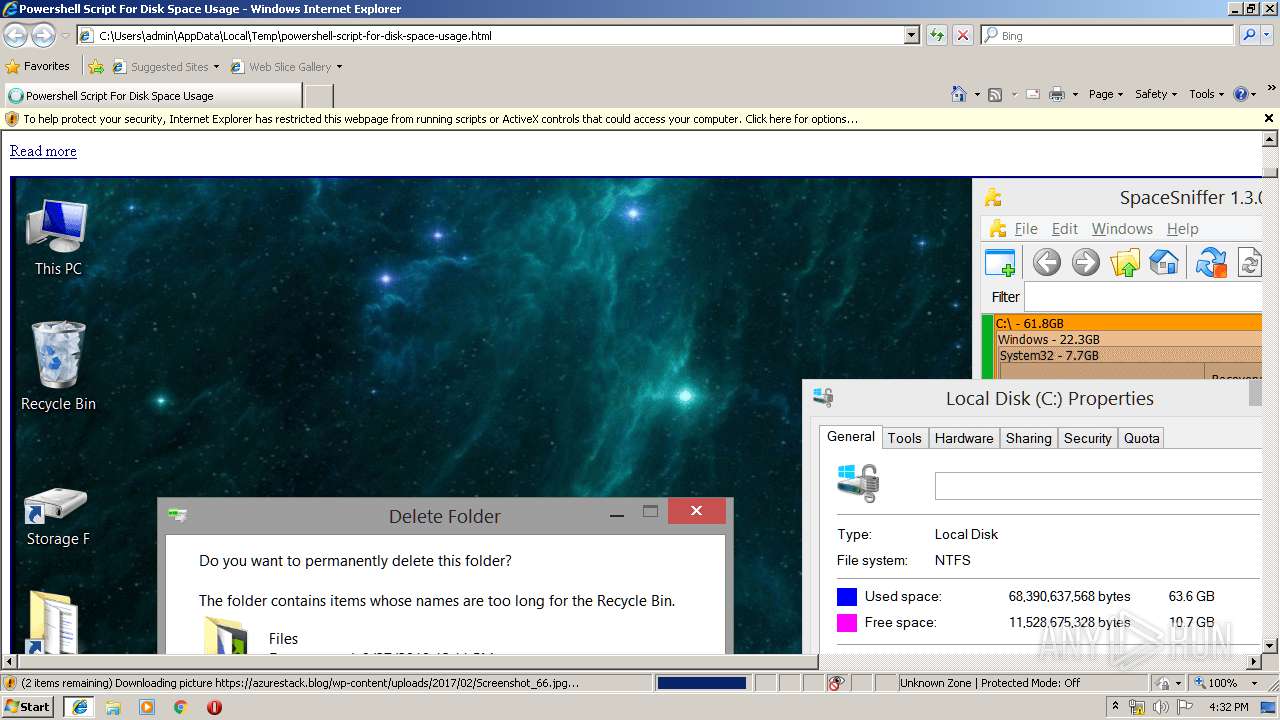
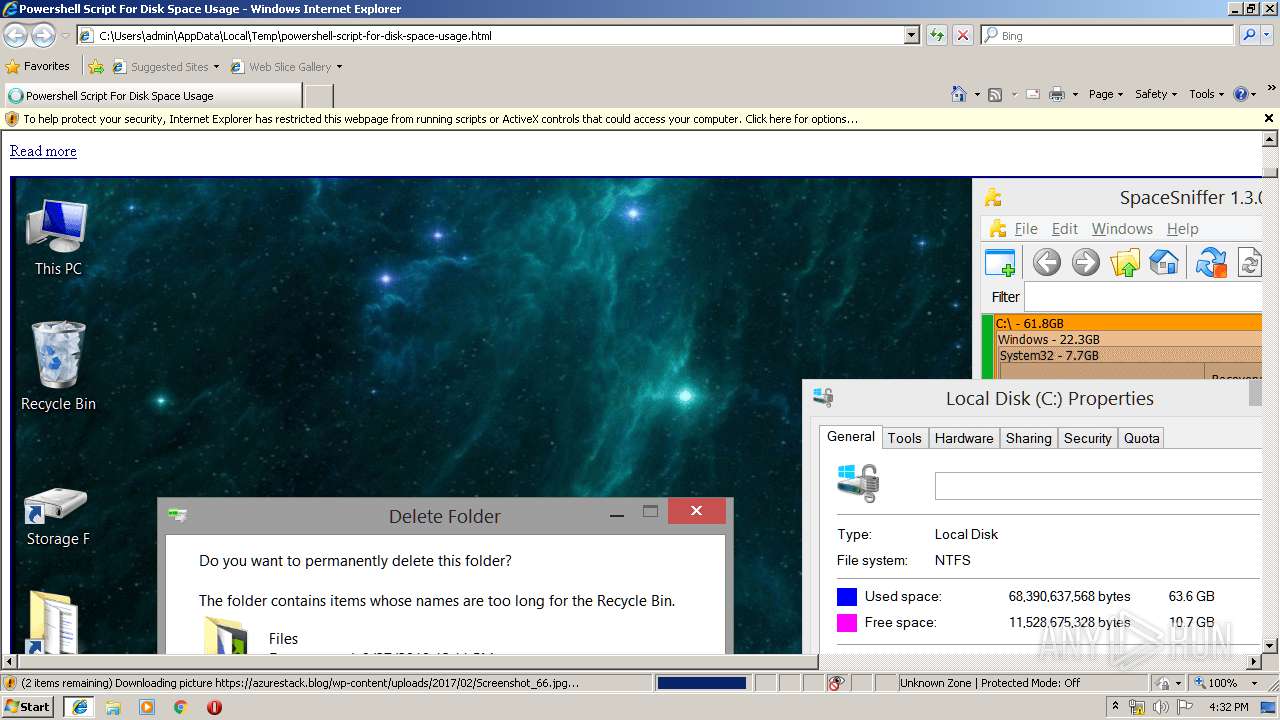
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 15:31:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text |
| MD5: | 2C12B1CEFF08CFF0569EBAD8C0981D53 |
| SHA1: | 0332B5B20A6093E72C49F15CBE245757C9C516EB |
| SHA256: | 0671C04107332BF45B12355E6A93A08E7B0FCF116656231A96CA0CCF25C10E58 |
| SSDEEP: | 768:zxE50oclPUYVzxbaJ6W+UmkhYqsnMH0WZd/k3Qi:VEulZlbaJ6WKusnMH/d/6 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 1324)
Creates files in the user directory
- iexplore.exe (PID: 2384)
- iexplore.exe (PID: 3224)
- iexplore.exe (PID: 1324)
Reads internet explorer settings
- iexplore.exe (PID: 2384)
- iexplore.exe (PID: 3224)
Changes internet zones settings
- iexplore.exe (PID: 1324)
Reads Internet Cache Settings
- iexplore.exe (PID: 3224)
Changes settings of System certificates
- iexplore.exe (PID: 2384)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2384)
Reads settings of System Certificates
- iexplore.exe (PID: 2384)
- iexplore.exe (PID: 3224)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
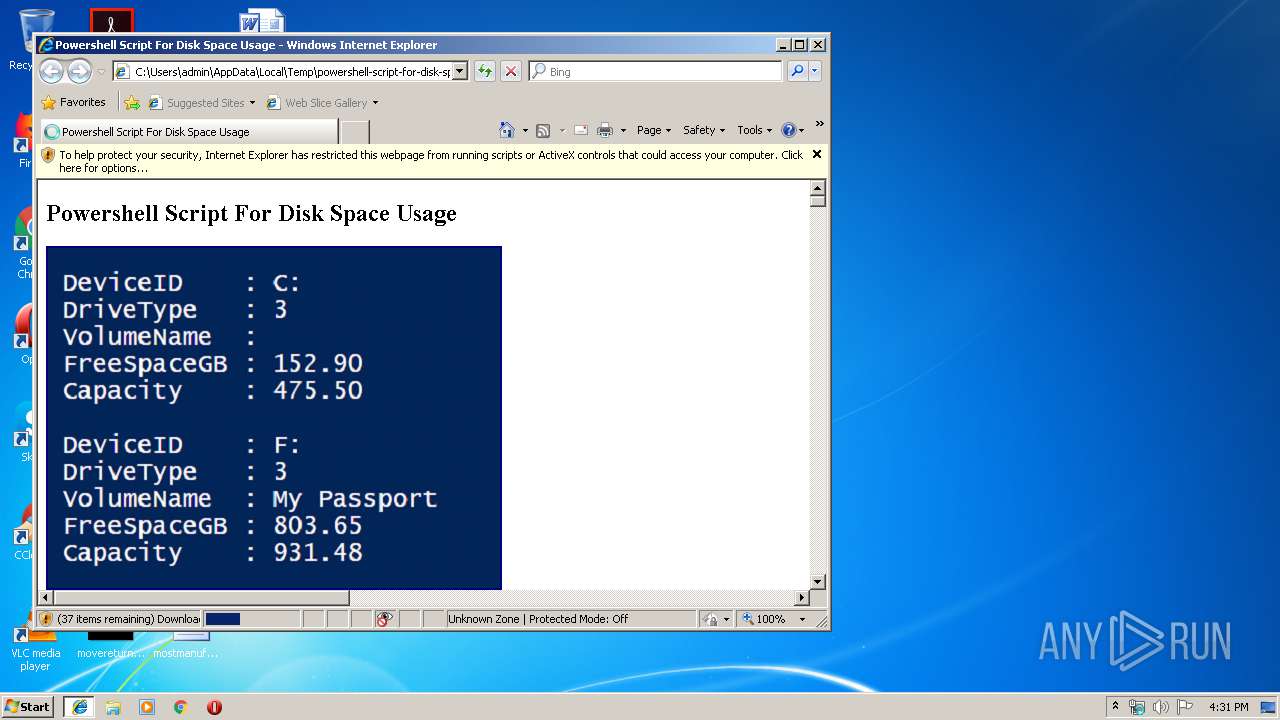
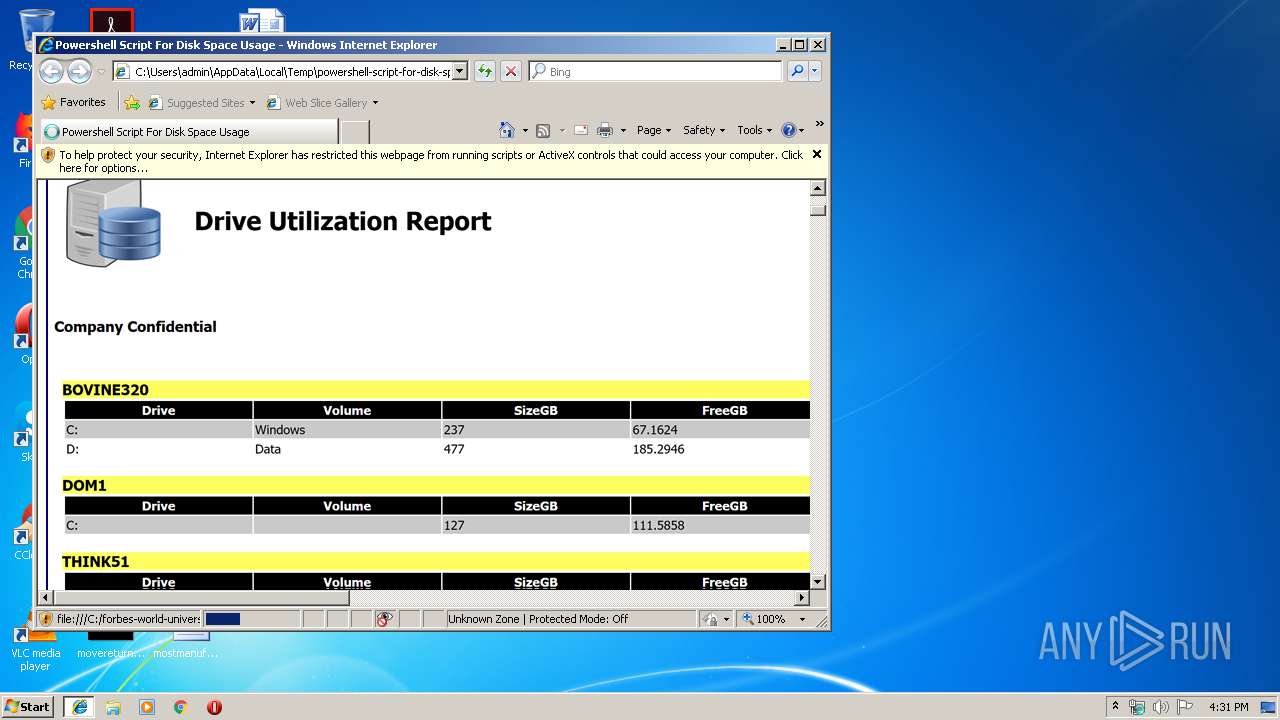
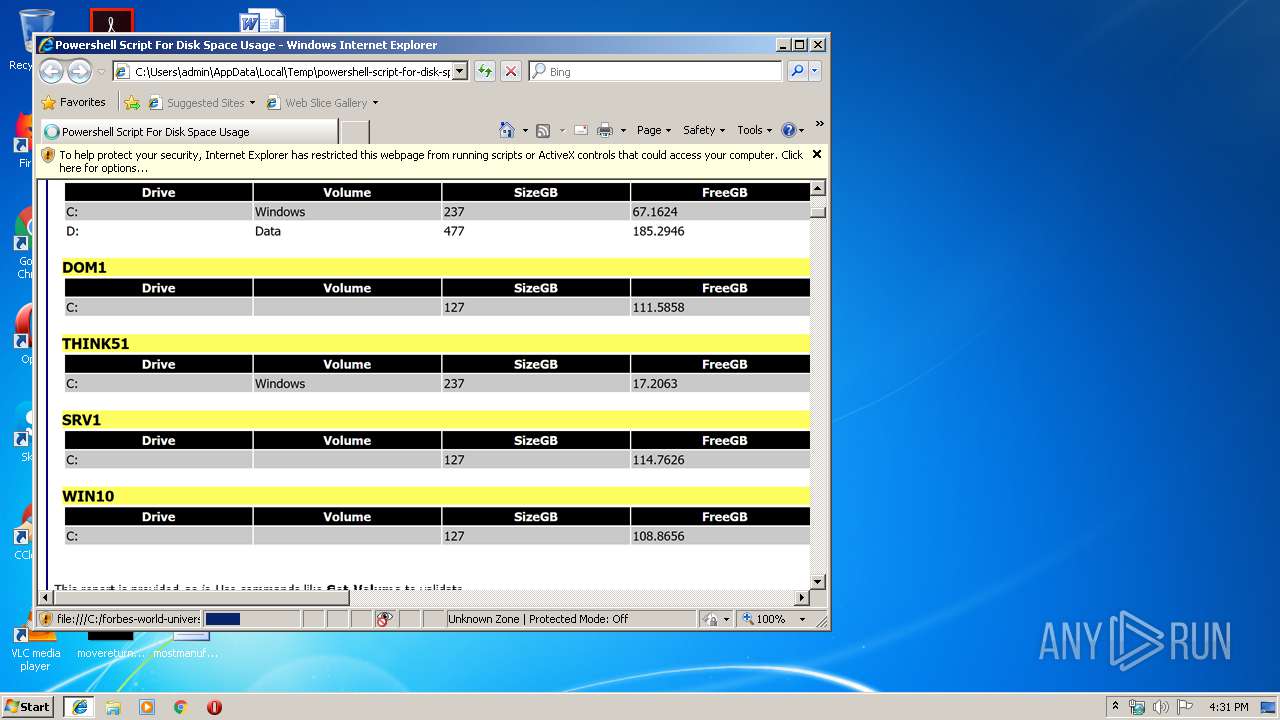
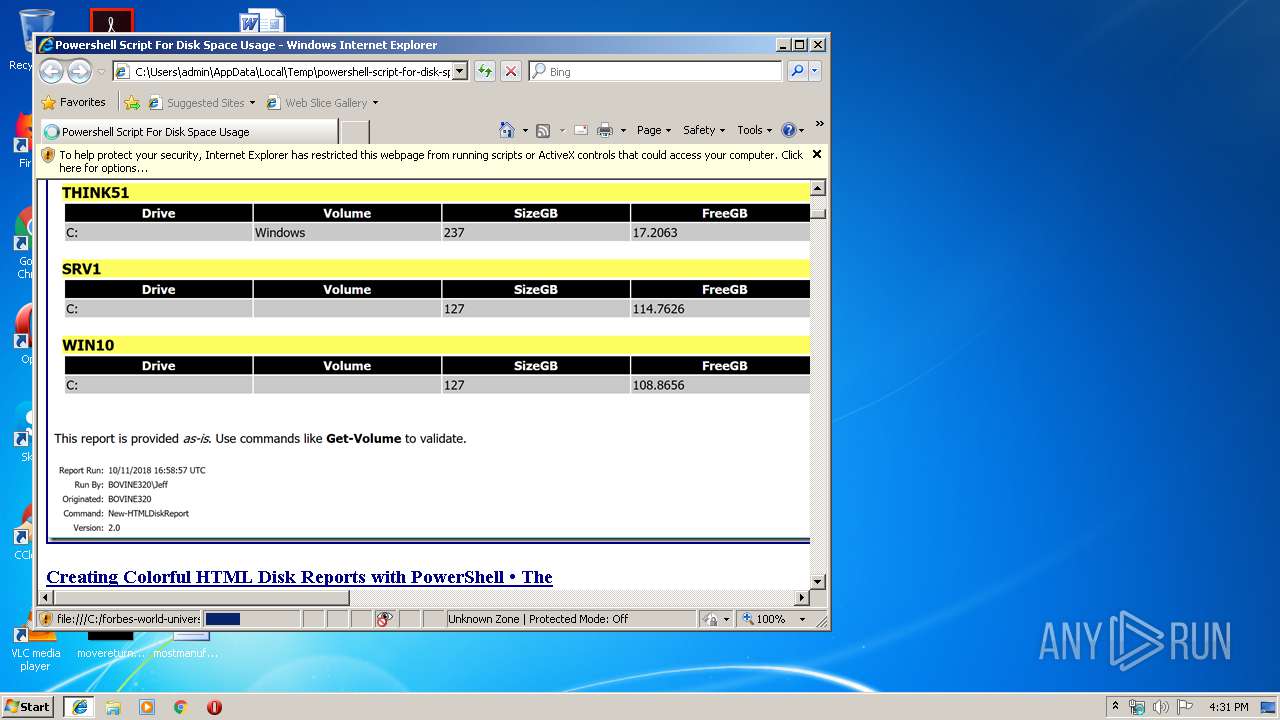
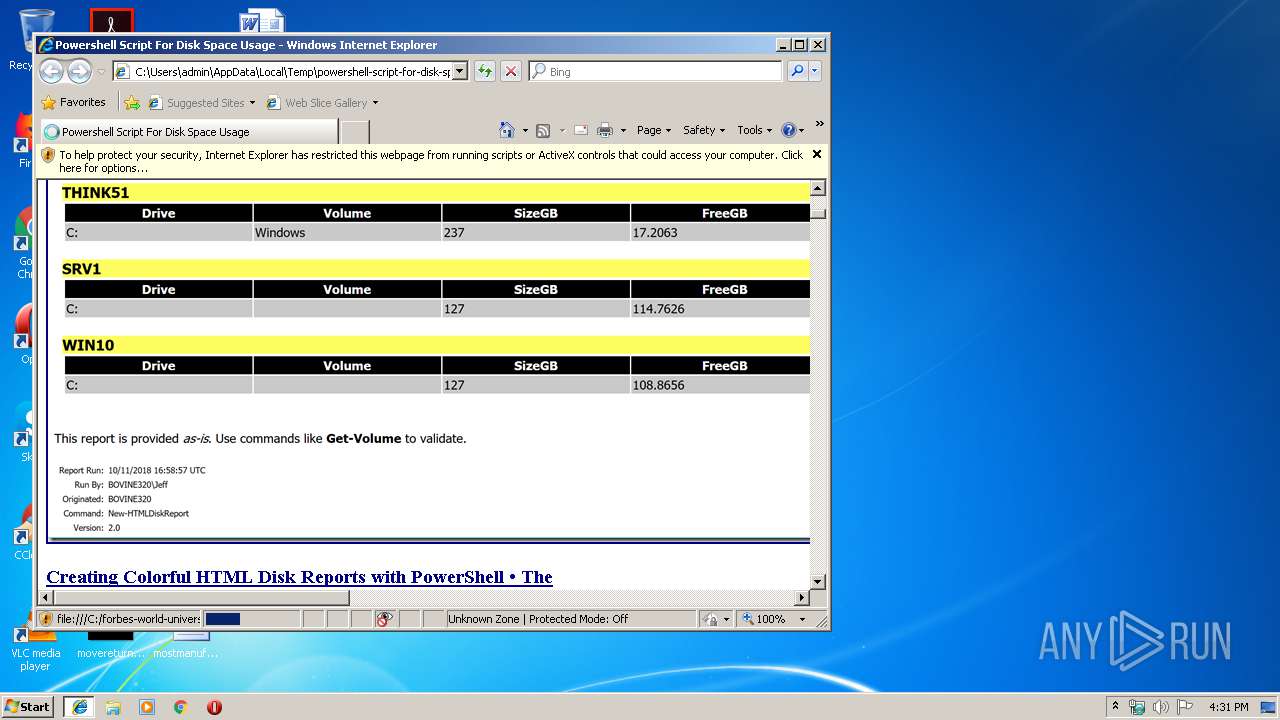
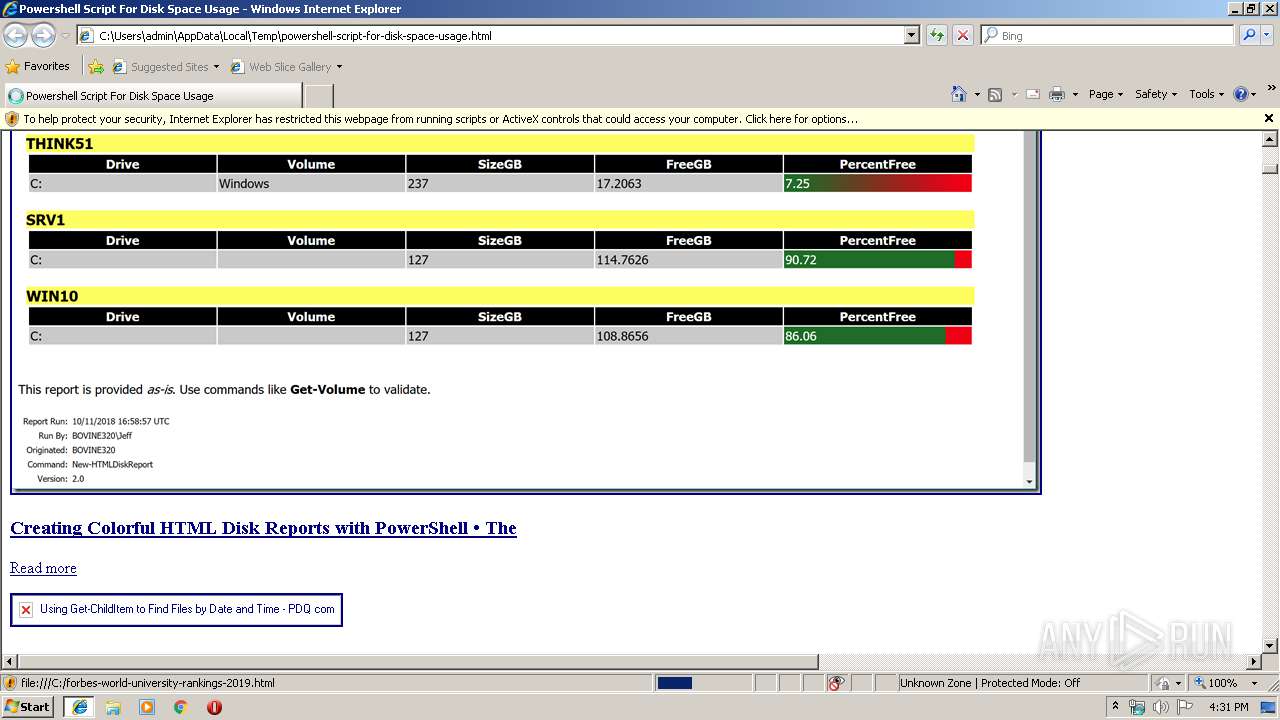
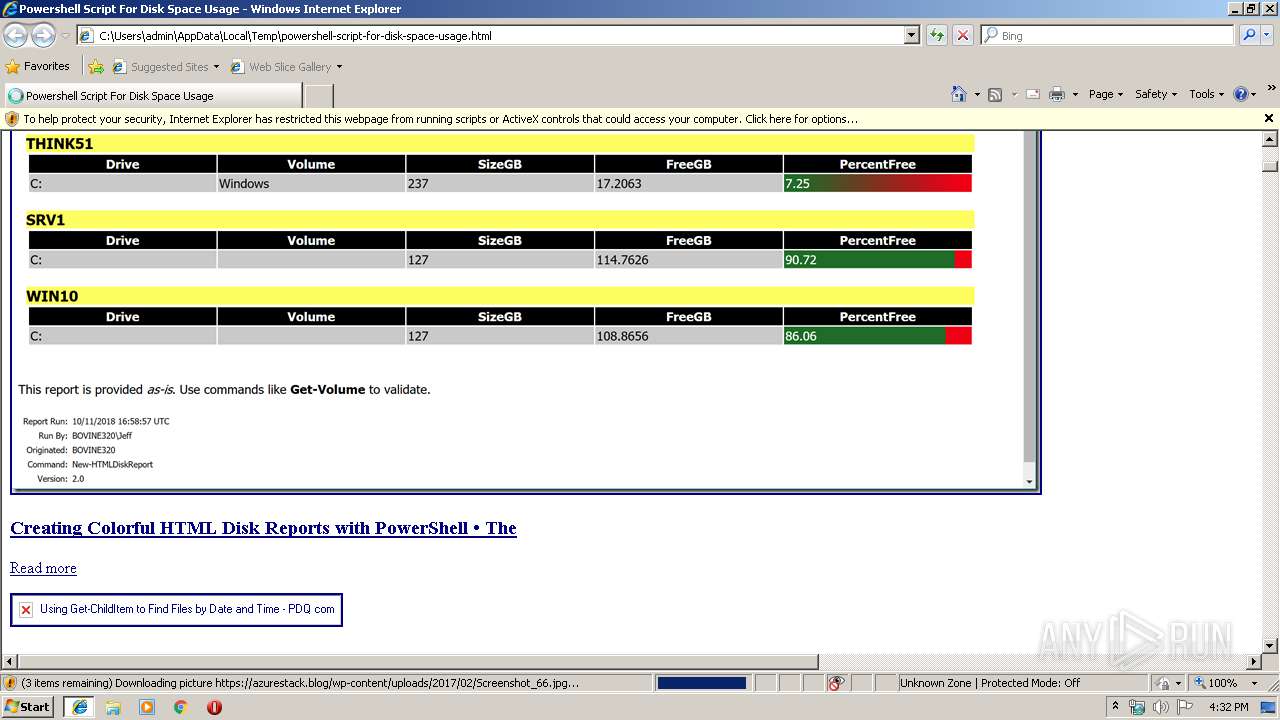
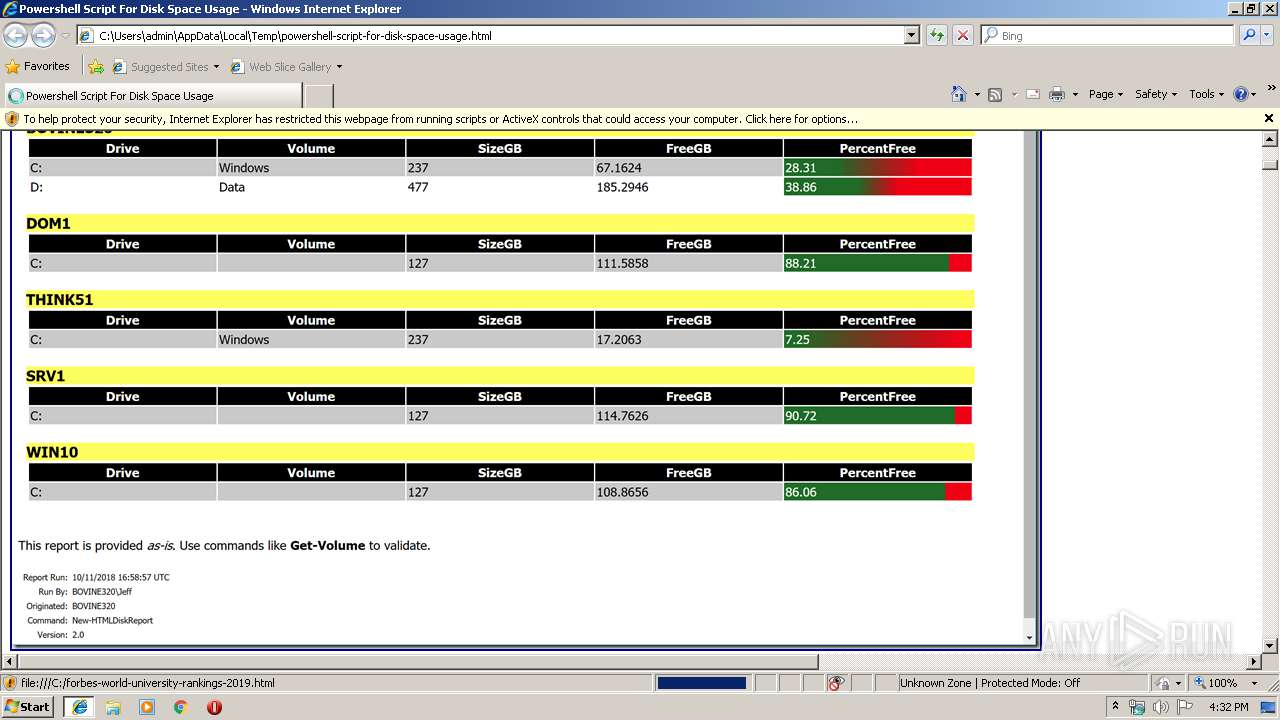
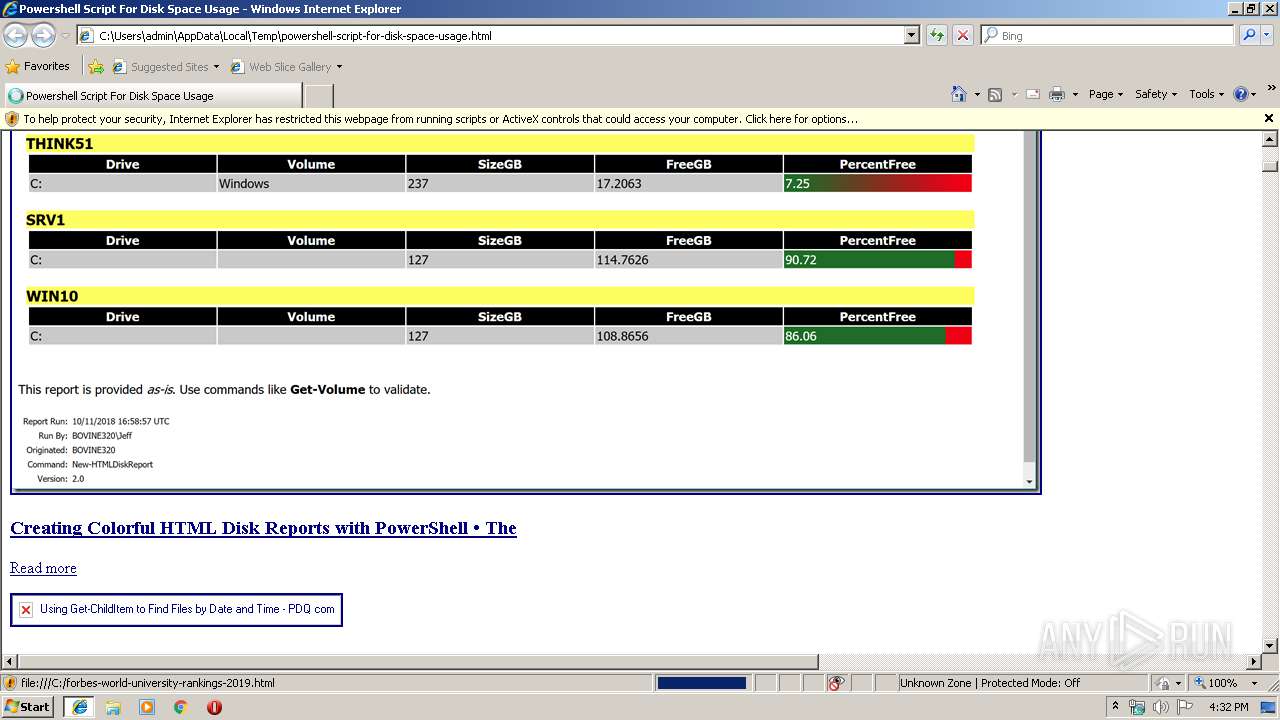
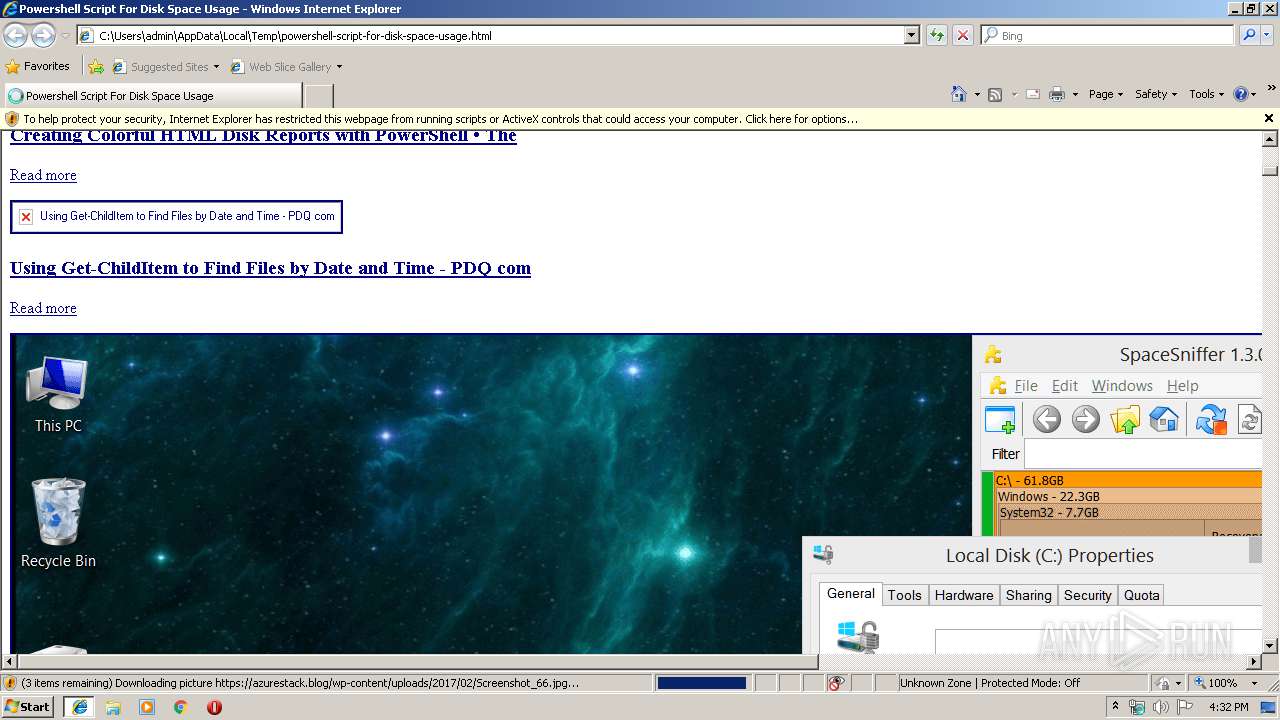
| Title: | Powershell Script For Disk Space Usage |
|---|---|
| viewport: | width=device-width, initial-scale=1, shrink-to-fit=no |
Total processes
38
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1324 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\powershell-script-for-disk-space-usage.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2384 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1324 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3224 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1324 CREDAT:203009 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 307
Read events
2 162
Write events
135
Delete events
10
Modification events
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {B4FAC41D-EE97-11E9-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070A0001000E000F001F0024005B03 | |||
Executable files
0
Suspicious files
6
Text files
168
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2384 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabC1C4.tmp | — | |
MD5:— | SHA256:— | |||
| 2384 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarC1D4.tmp | — | |
MD5:— | SHA256:— | |||
| 2384 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabC224.tmp | — | |
MD5:— | SHA256:— | |||
| 2384 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarC225.tmp | — | |
MD5:— | SHA256:— | |||
| 2384 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\Grafana-Example-2[1].png | image | |
MD5:— | SHA256:— | |||
| 2384 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\css[1].txt | text | |
MD5:— | SHA256:— | |||
| 2384 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\3c6e9a8bda09daaf24564a314a673b2550eb606d-menu[1].png | image | |
MD5:— | SHA256:— | |||
| 2384 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabC40A.tmp | — | |
MD5:— | SHA256:— | |||
| 2384 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarC40B.tmp | — | |
MD5:— | SHA256:— | |||
| 2384 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\SPHC04[1].png | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
354
DNS requests
155
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2384 | iexplore.exe | GET | 200 | 104.27.189.10:80 | http://cdn.techgenix.com/media/upls/image001_219.jpg | US | image | 41.3 Kb | suspicious |
2384 | iexplore.exe | GET | 200 | 91.216.107.92:80 | http://www.luteus.biz/Download/LoriotPro_Doc/SMS_Manager_Documentation/img/PythonScript_message.png | FR | image | 24.0 Kb | unknown |
2384 | iexplore.exe | GET | 200 | 217.160.0.125:80 | http://get-cmd.com/wp-content/uploads/2018/07/starwind_powershell1.png | DE | image | 104 Kb | malicious |
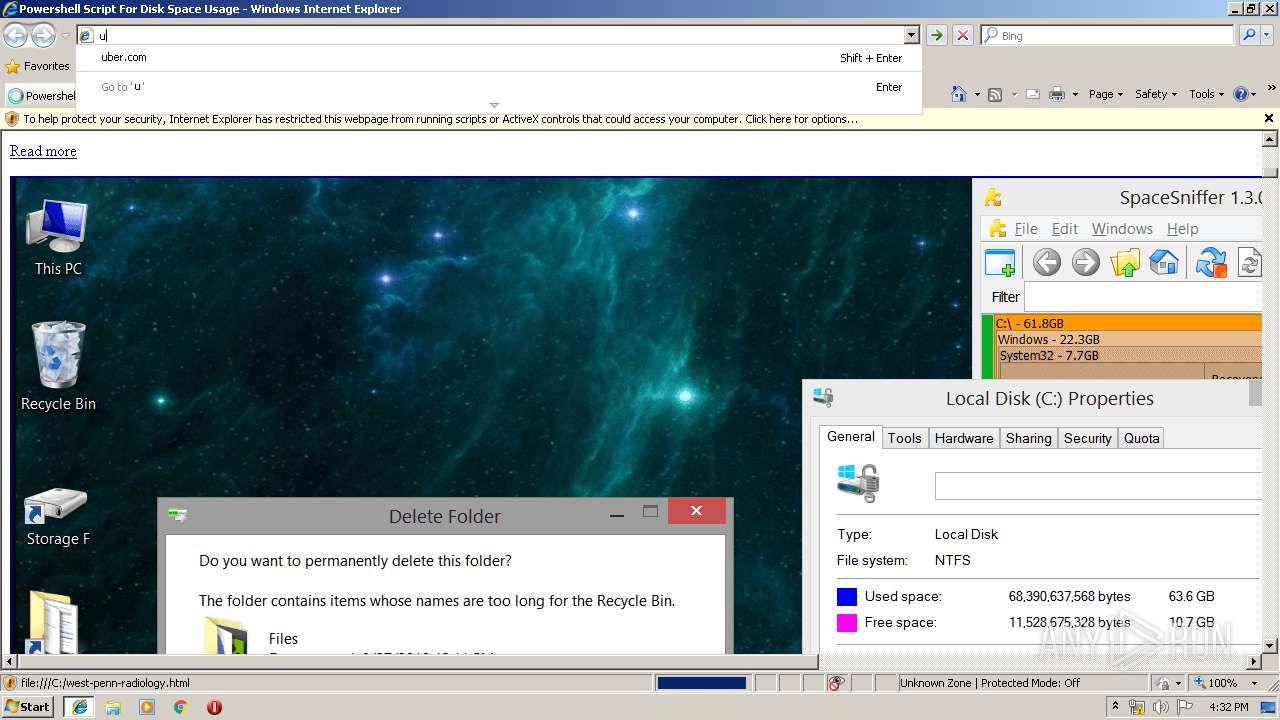
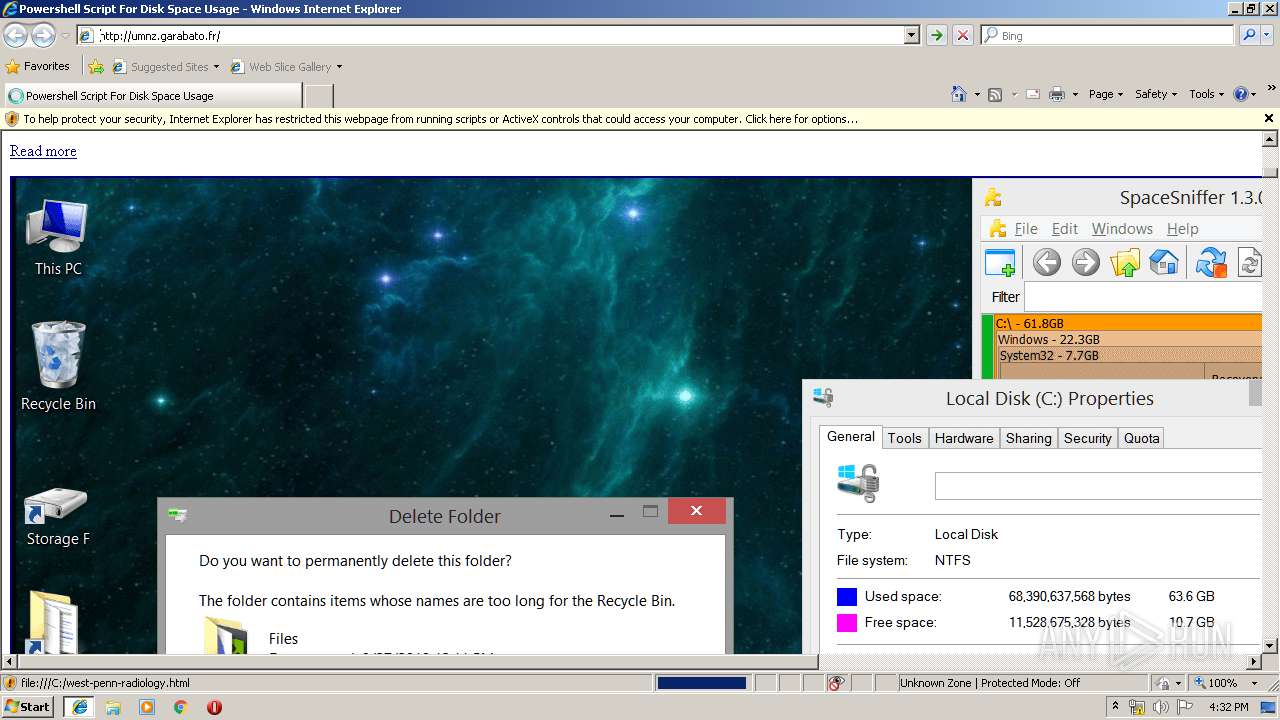
3224 | iexplore.exe | GET | 200 | 104.28.29.99:80 | http://umnz.garabato.fr/ | US | html | 10.6 Kb | suspicious |
2384 | iexplore.exe | GET | 200 | 185.103.156.5:80 | http://www.darrylvanderpeijl.com/wp-content/uploads/overview_iopath-1024x722.png | NL | image | 77.2 Kb | suspicious |
3224 | iexplore.exe | GET | 200 | 104.24.122.82:80 | http://images.mini-ielts.com/images/1/18/evolution-tree_thumbpad.jpg | US | image | 7.60 Kb | suspicious |
3224 | iexplore.exe | GET | 200 | 104.24.122.82:80 | http://images.mini-ielts.com/images/1/2/scientific-english_thumbpad.jpeg | US | image | 6.80 Kb | suspicious |
2384 | iexplore.exe | GET | 200 | 68.171.216.220:80 | http://www.powershellneedfulthings.com/wp-content/gallery/eas2003/e2k3scrn.jpg | US | image | 140 Kb | unknown |
2384 | iexplore.exe | GET | 200 | 13.35.254.54:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
1324 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2384 | iexplore.exe | 108.161.188.153:443 | img.netwrix.com | netDNA | US | unknown |
2384 | iexplore.exe | 216.58.207.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2384 | iexplore.exe | 151.139.241.2:443 | static.techspot.com | netDNA | US | unknown |
2384 | iexplore.exe | 104.31.77.155:443 | jdhitsolutions.com | Cloudflare Inc | US | unknown |
2384 | iexplore.exe | 13.32.158.244:443 | communities.sas.com | Amazon.com, Inc. | US | unknown |
2384 | iexplore.exe | 66.77.93.35:443 | mcpmag.com | Qwest Communications Company, LLC | US | unknown |
2384 | iexplore.exe | 66.77.93.49:443 | redmondmag.com | Qwest Communications Company, LLC | US | unknown |
2384 | iexplore.exe | 192.0.72.24:443 | gregramsey.files.wordpress.com | Automattic, Inc | US | suspicious |
2384 | iexplore.exe | 35.239.147.27:443 | blogvaronis2.wpengine.com | — | US | unknown |
1324 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fonts.googleapis.com |
| whitelisted |
communities.sas.com |
| malicious |
img.netwrix.com |
| suspicious |
www.itprotoday.com |
| unknown |
jdhitsolutions.com |
| unknown |
mcpmag.com |
| whitelisted |
cdn.pdq.com |
| malicious |
static.techspot.com |
| suspicious |
original.securityintelligence.com |
| unknown |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
2384 | iexplore.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |