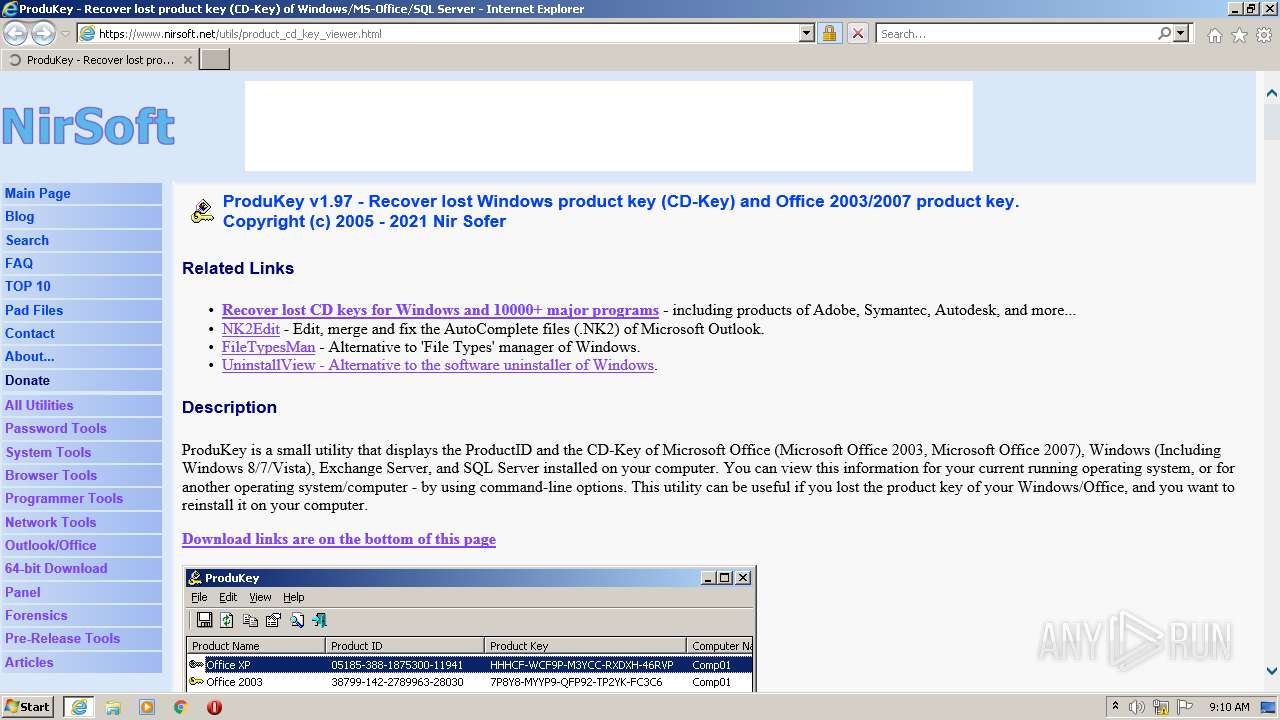
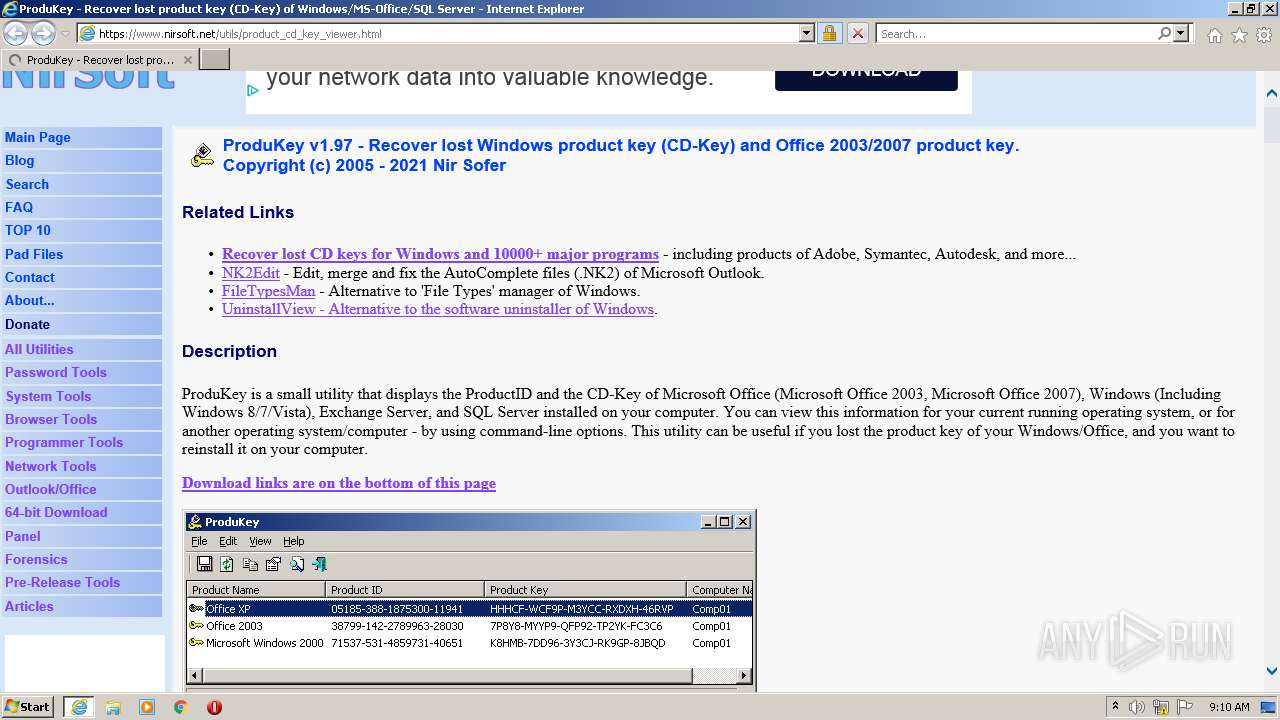
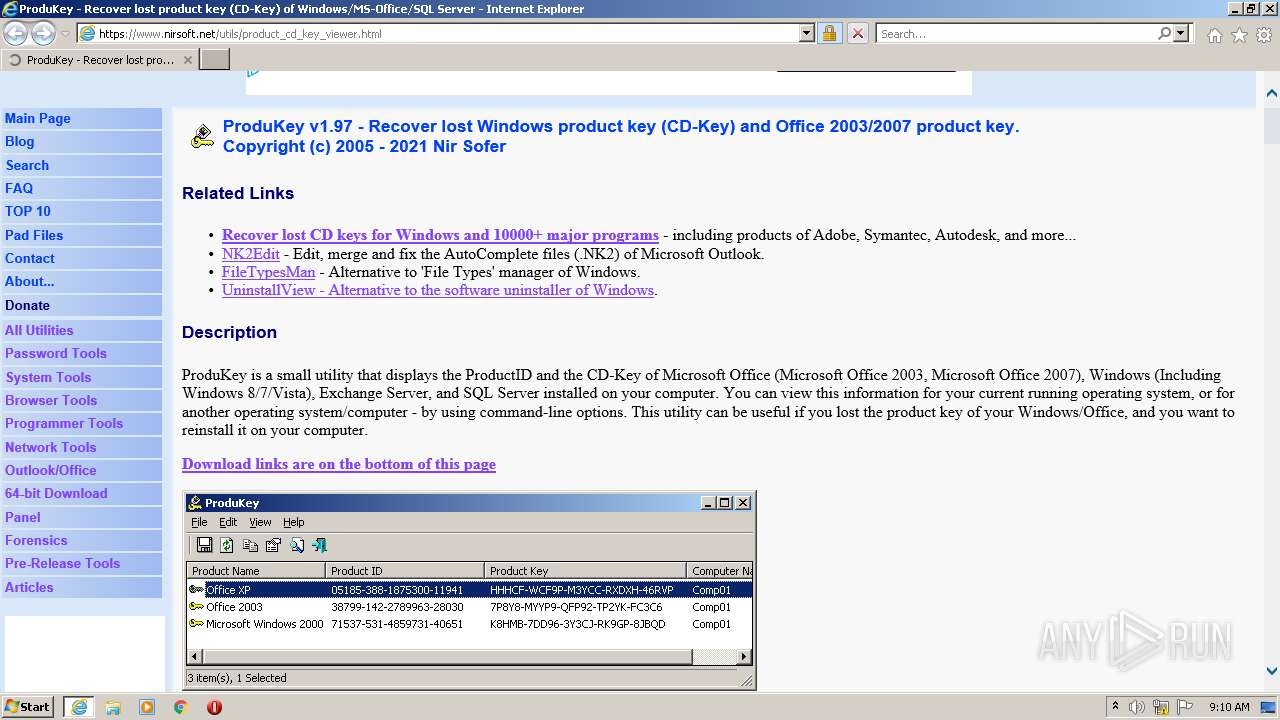
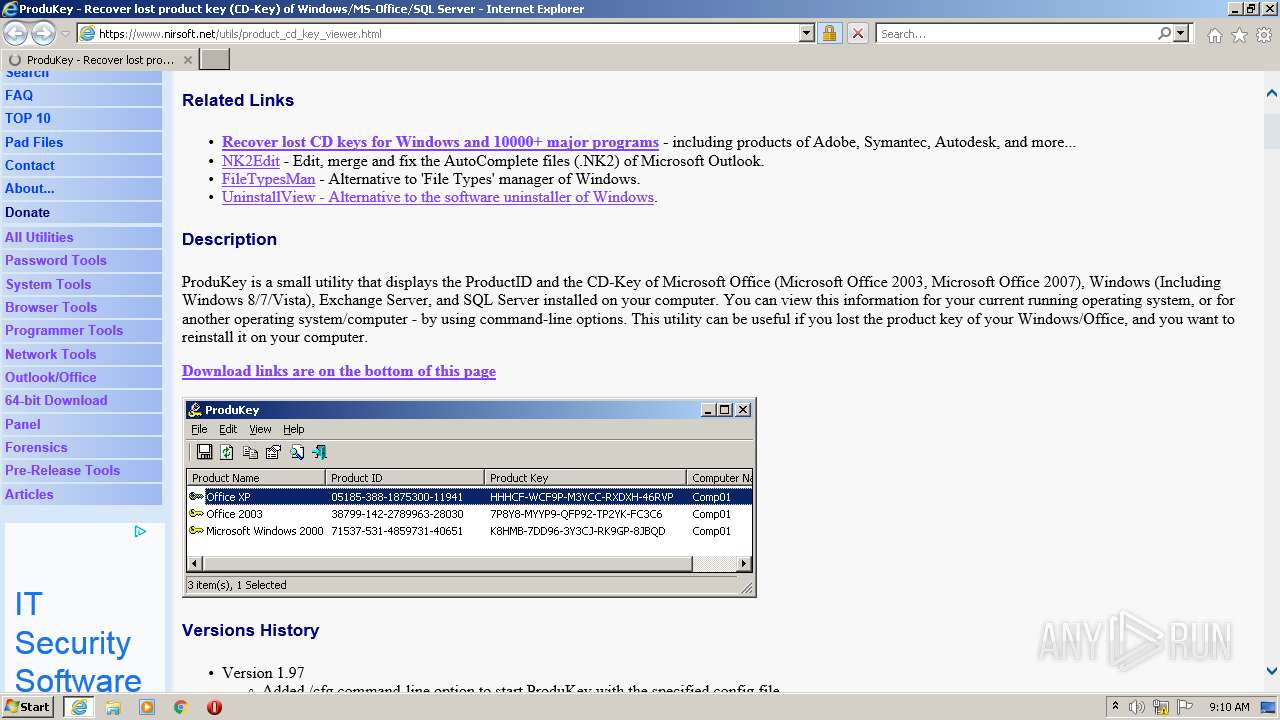
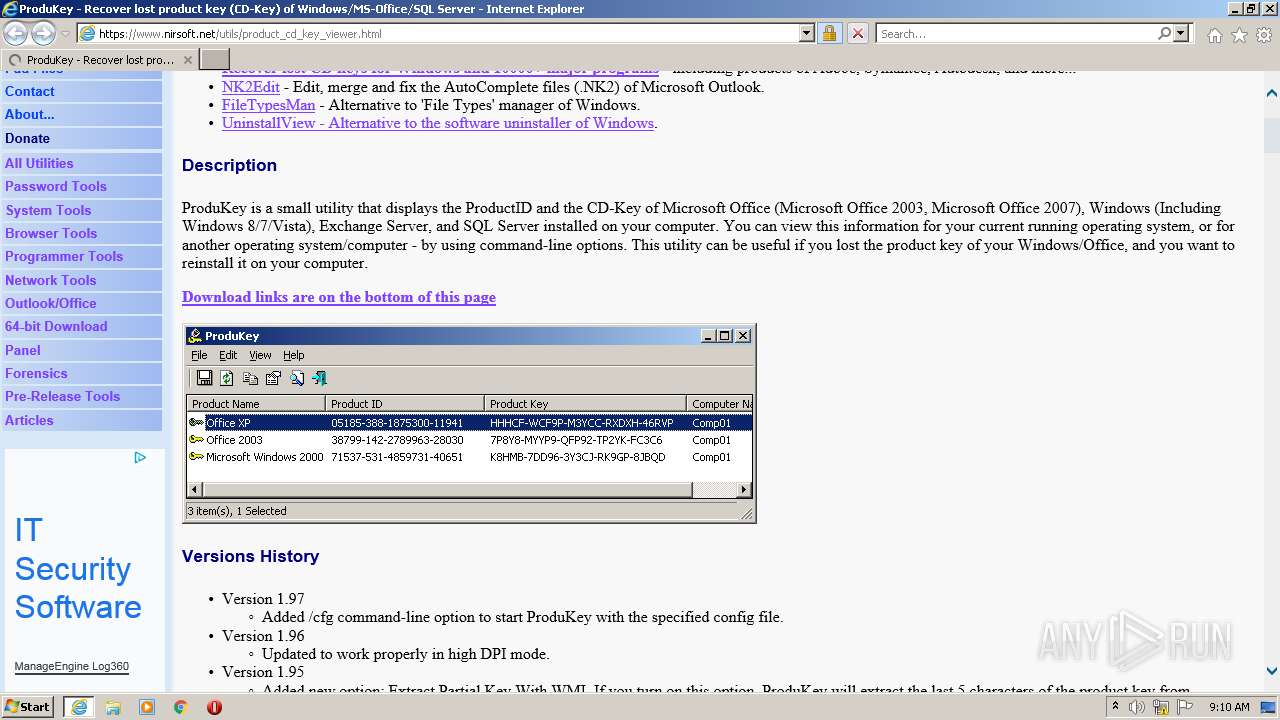
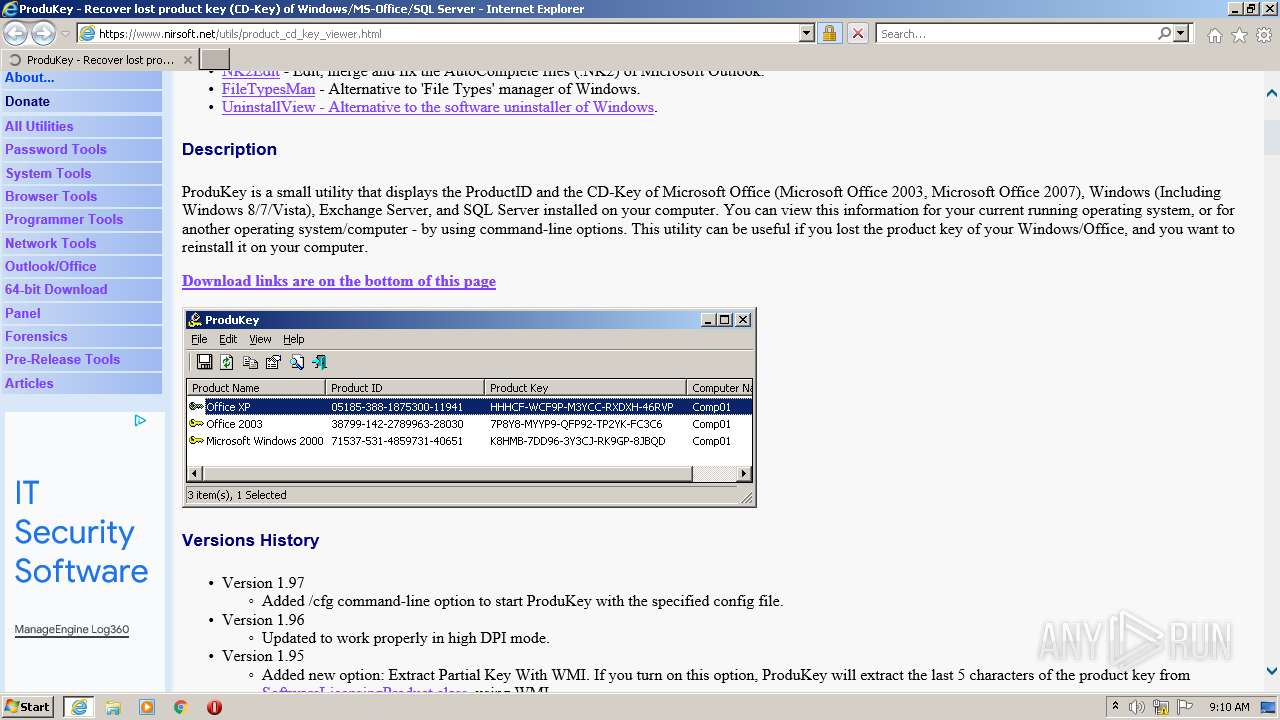
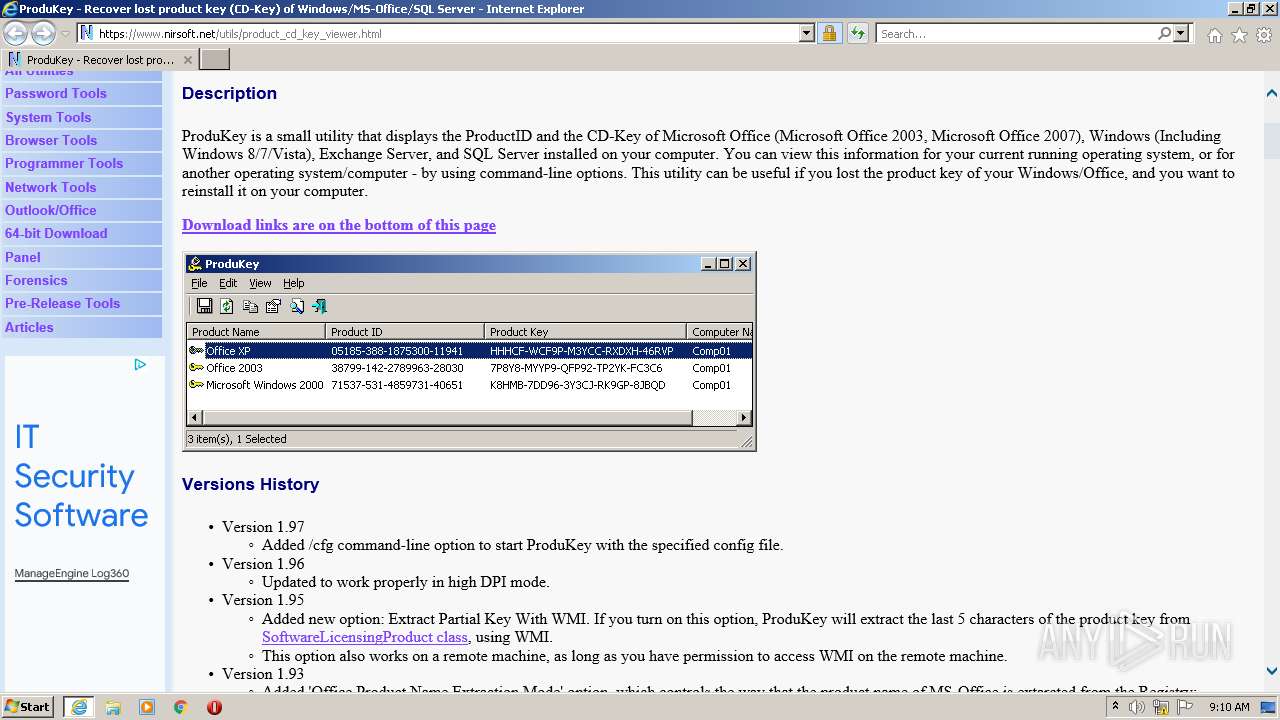
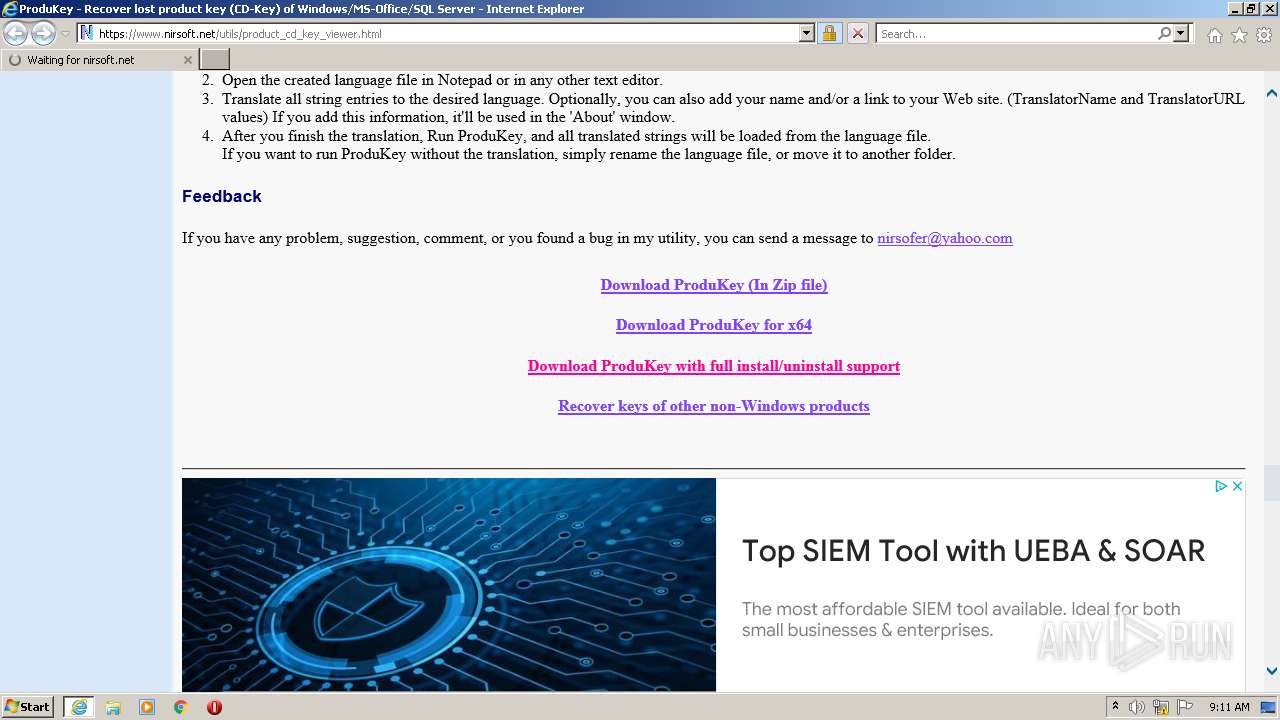
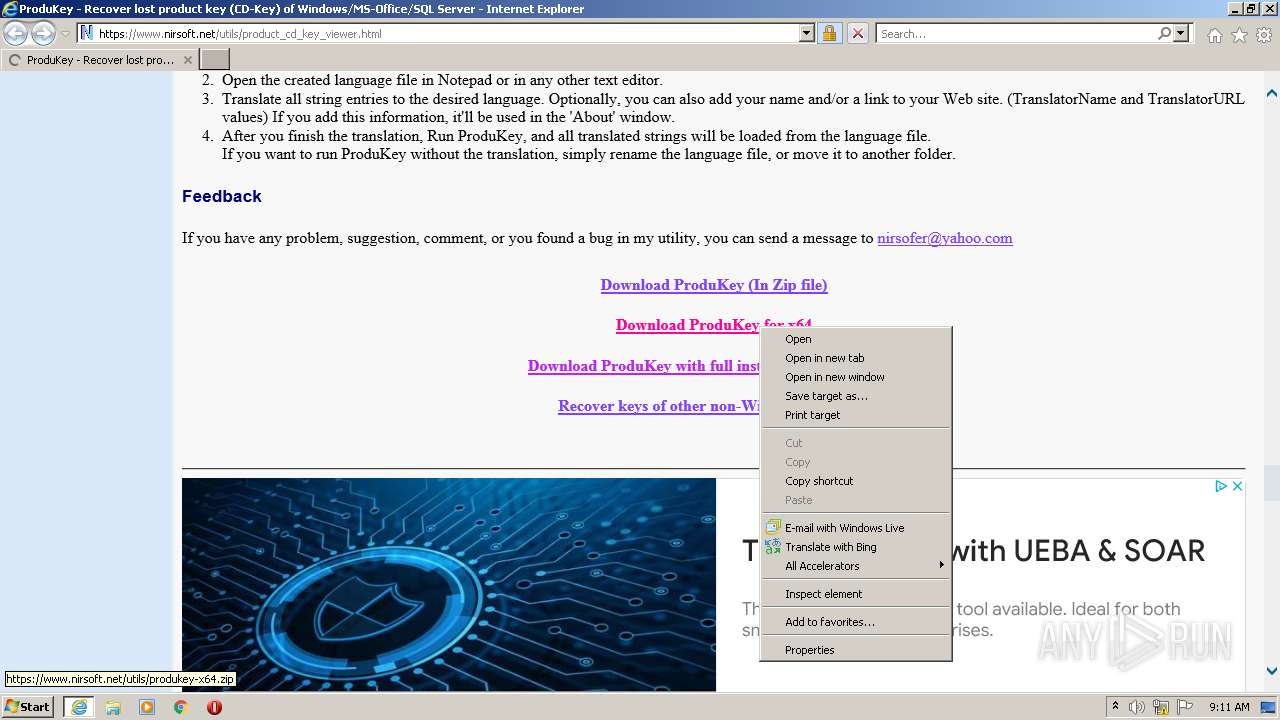
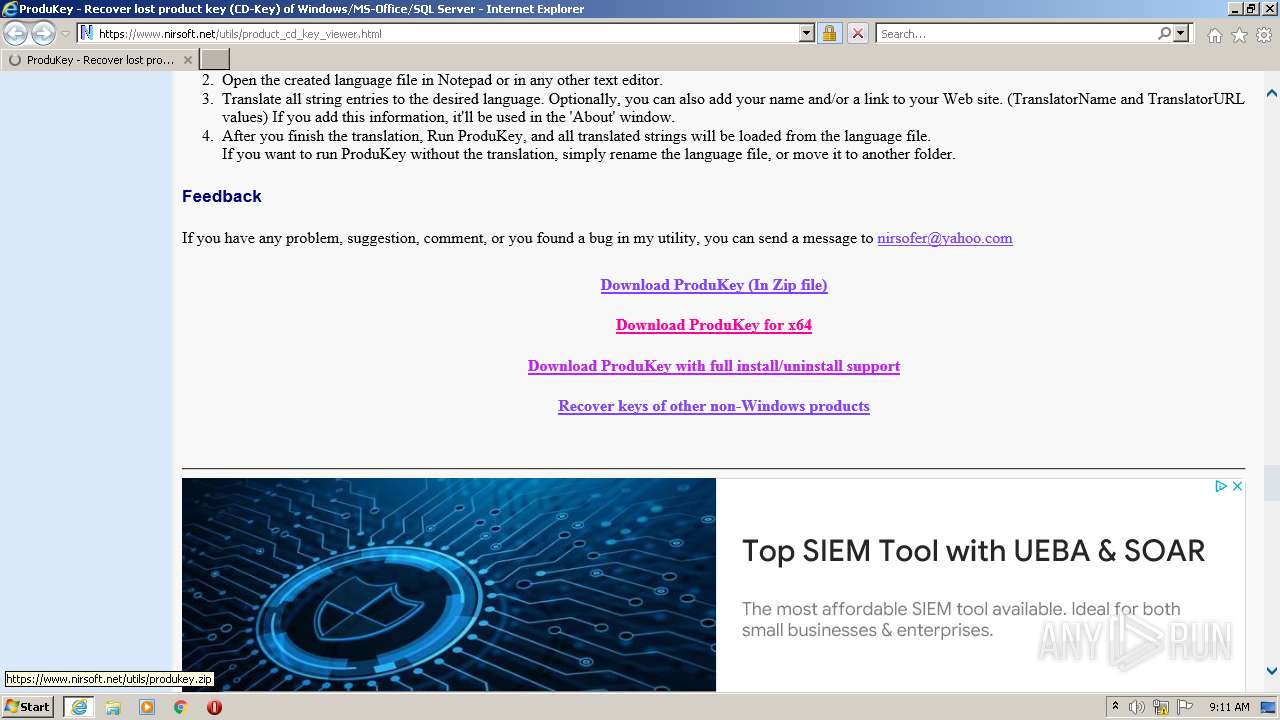
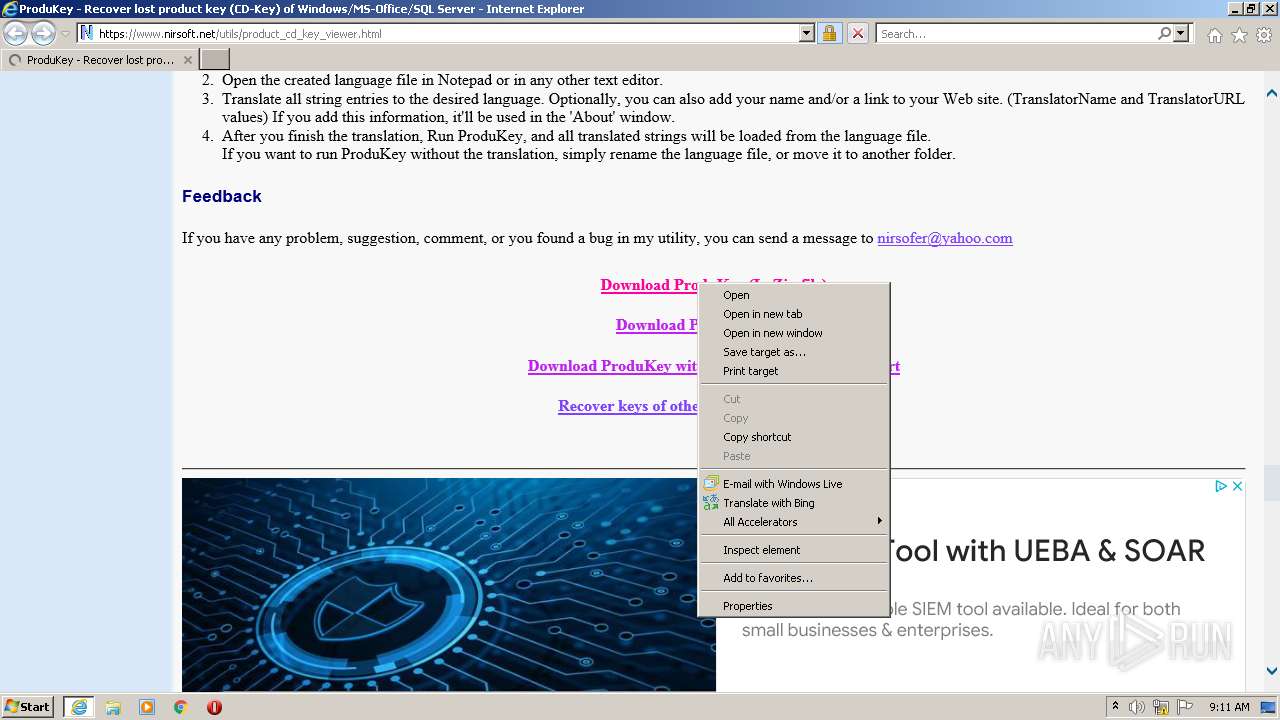
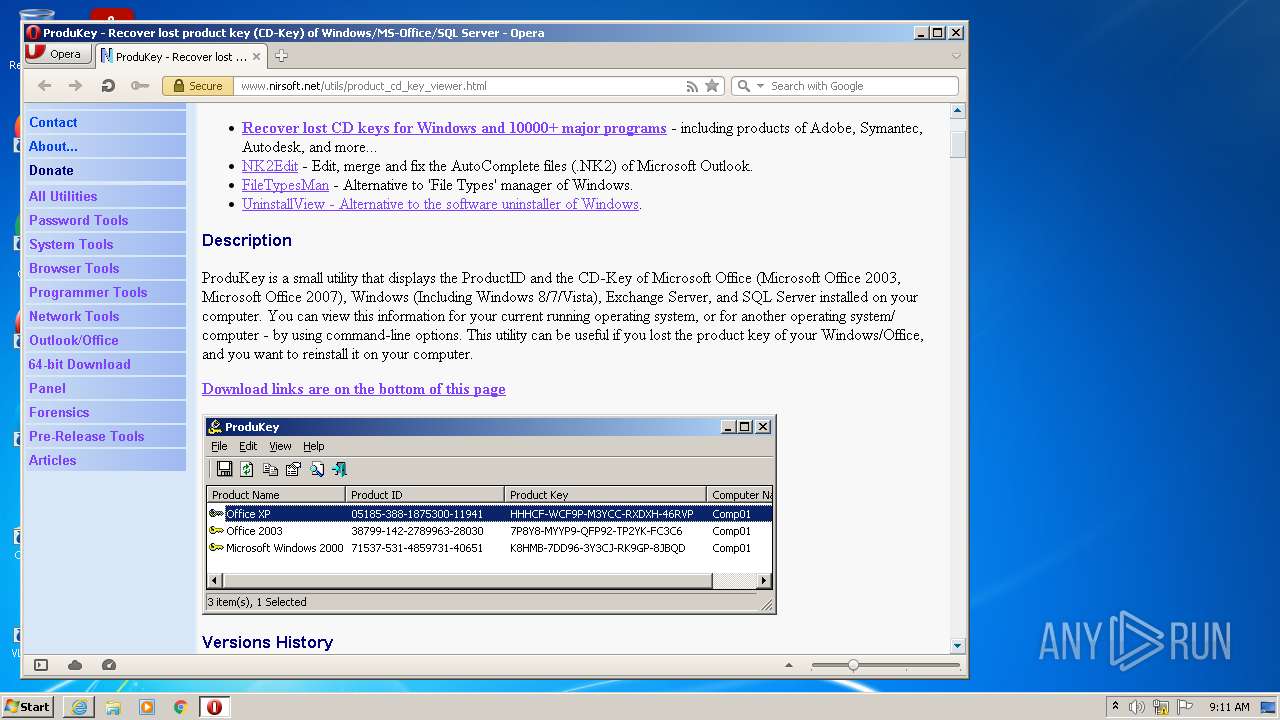
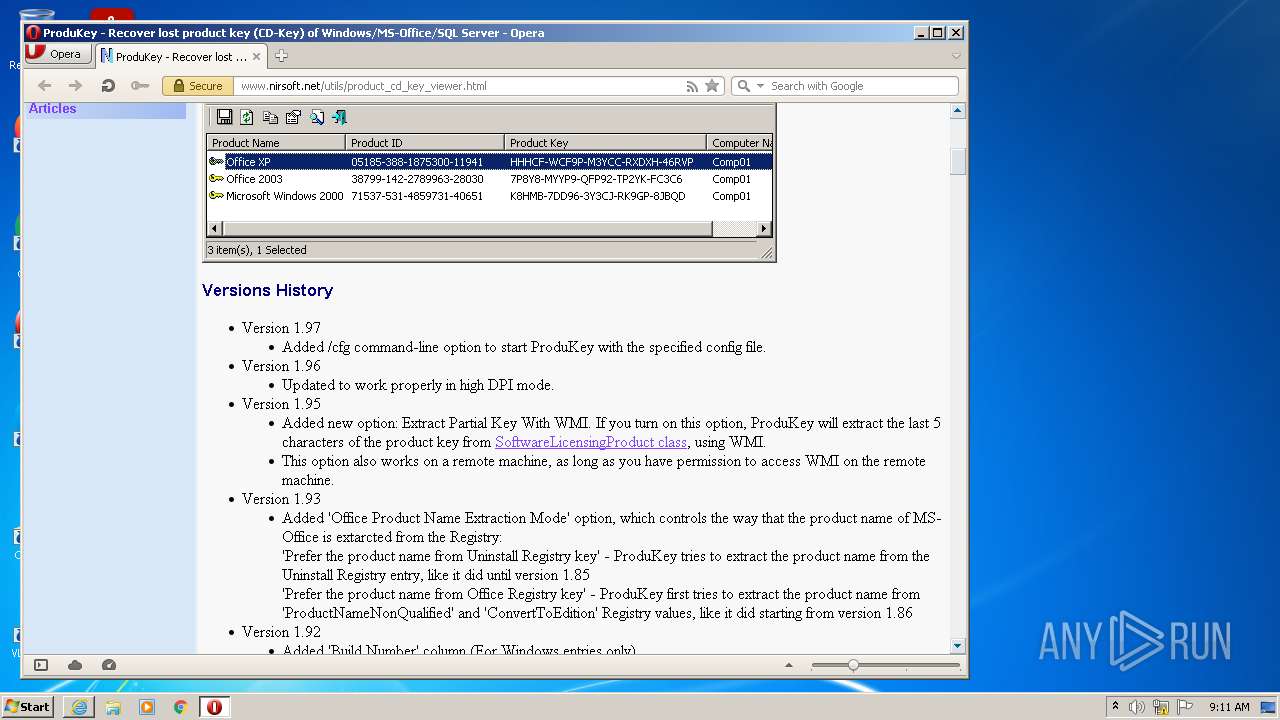
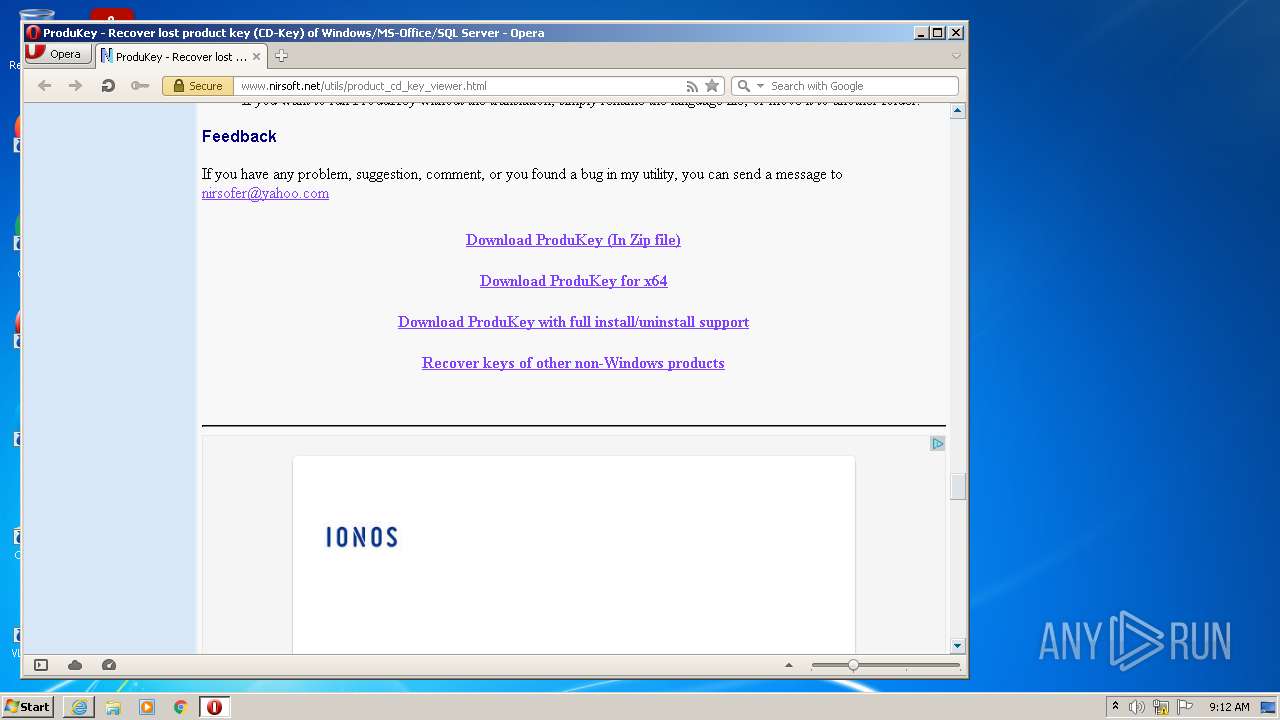
| URL: | https://www.nirsoft.net/utils/product_cd_key_viewer.html |
| Full analysis: | https://app.any.run/tasks/63ee0f19-1c74-48b8-a318-49153ce5eb78 |
| Verdict: | Malicious activity |
| Analysis date: | February 07, 2022, 09:10:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 337DF0F3D0B055F09316BC56B6737D90 |
| SHA1: | 21097DFD4E9C80FDF9A17FE814875818E5BCACDC |
| SHA256: | 066DDDF6605358941AB0751D94D2A59141CA7D10750628C2FAC3A64D084D5EF5 |
| SSDEEP: | 3:N8DSL4BR/N9aTR6GB6vLA3guJ:2OL4BgR6GMvLA3v |
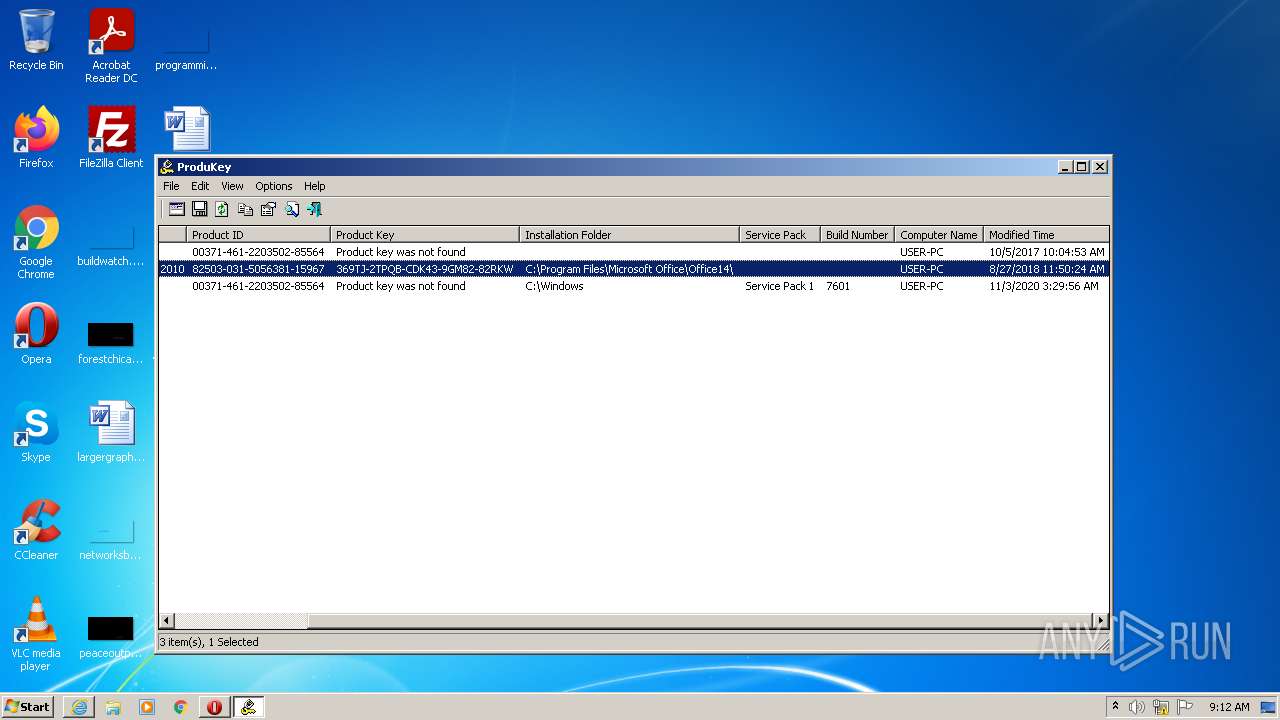
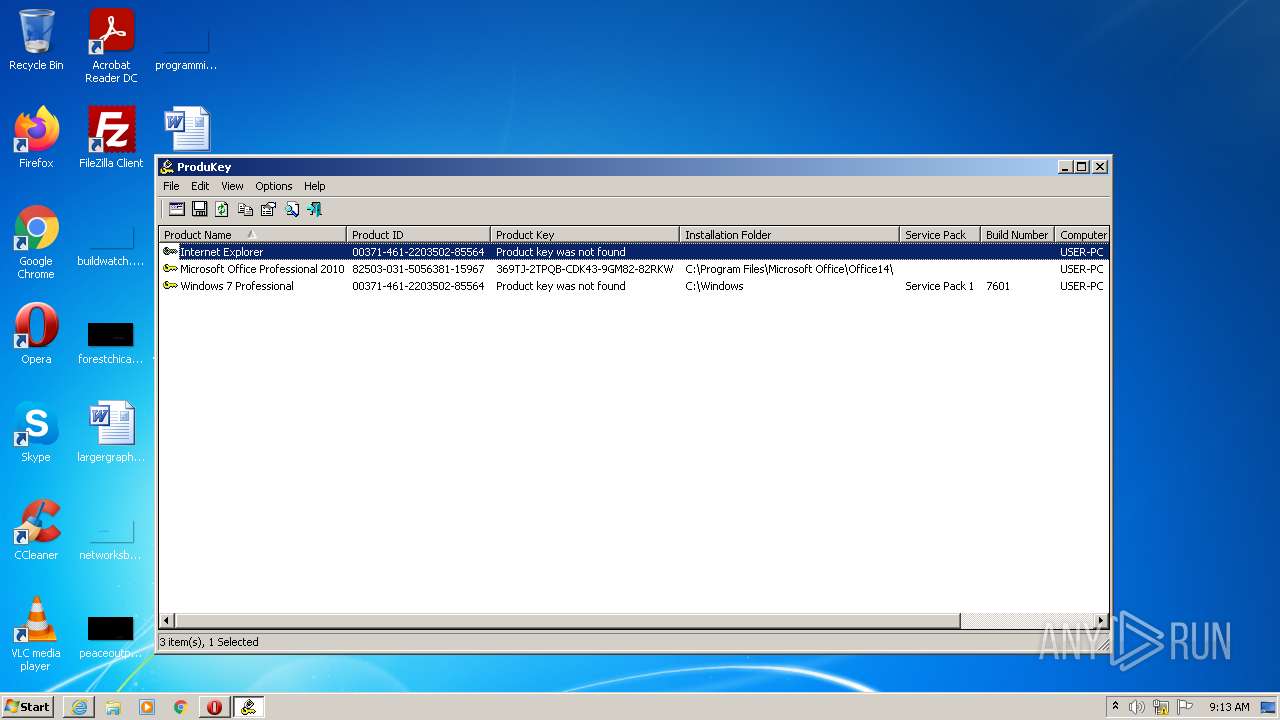
MALICIOUS
Application was dropped or rewritten from another process
- produkey_setup.exe (PID: 2696)
- produkey_setup.exe (PID: 2924)
- ProduKey.exe (PID: 1340)
- ProduKey.exe (PID: 3860)
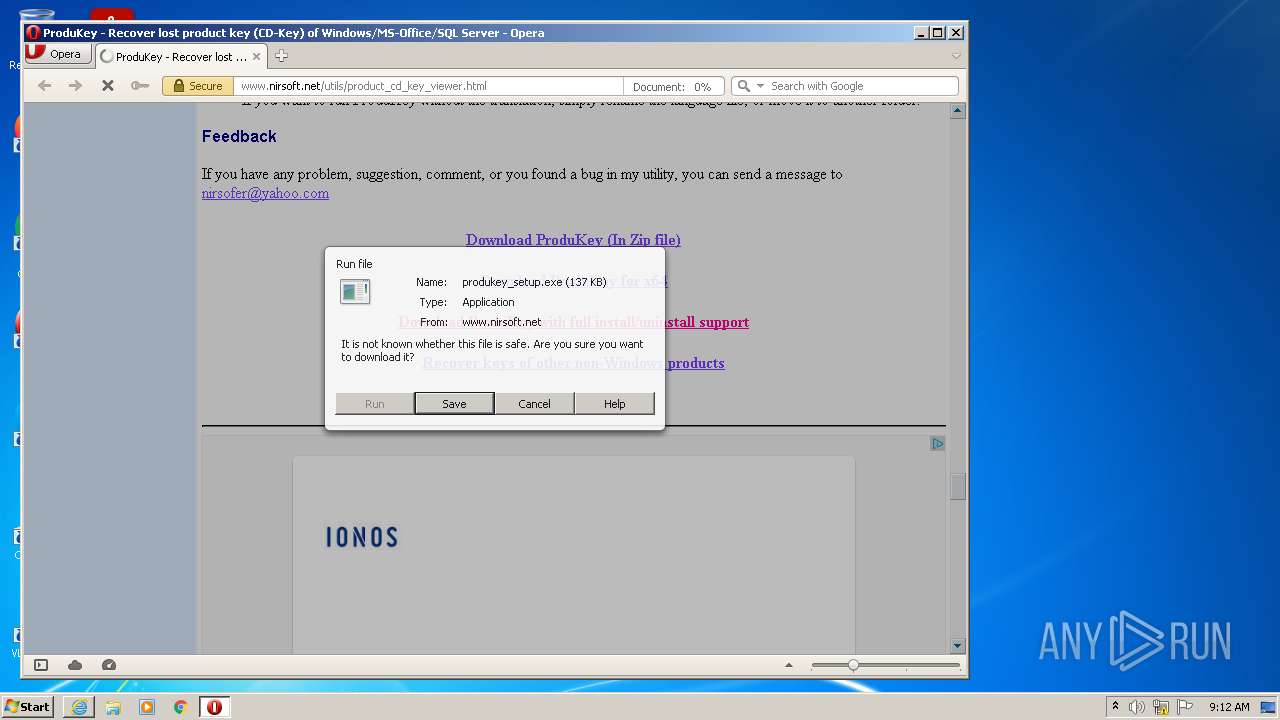
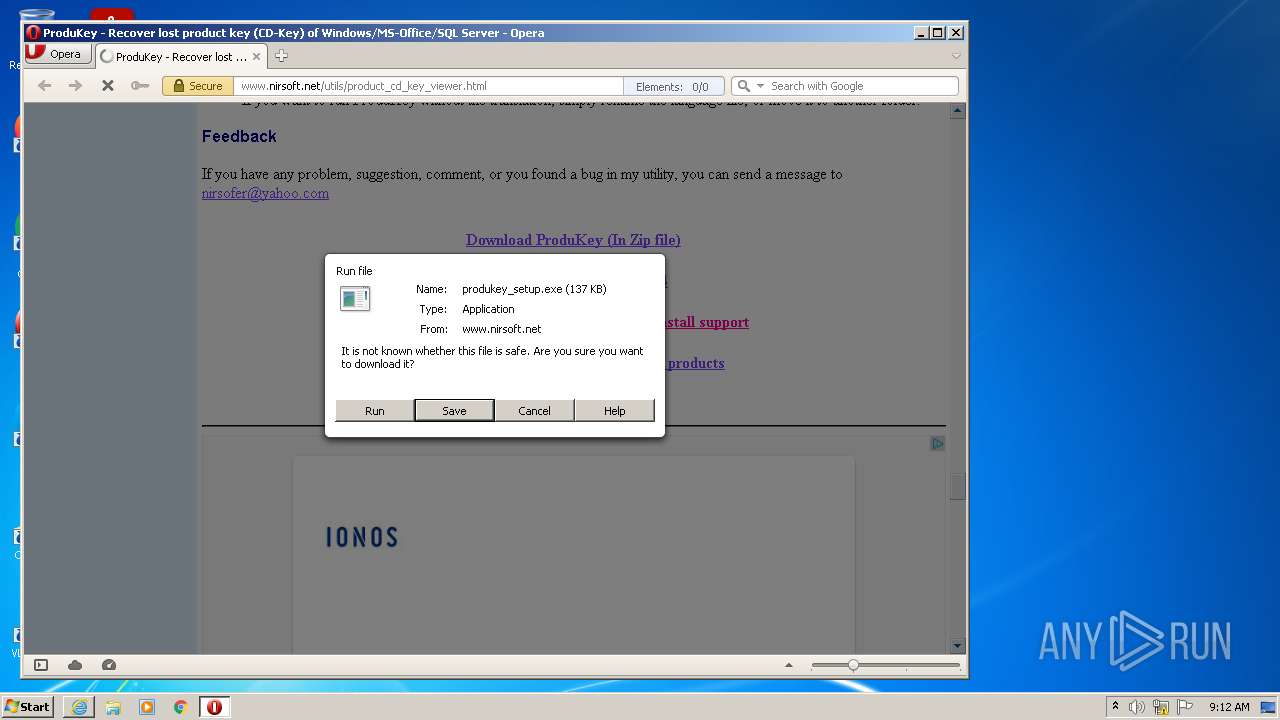
Drops executable file immediately after starts
- produkey_setup.exe (PID: 2924)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3432)
Drops a file with too old compile date
- opera.exe (PID: 2684)
- produkey_setup.exe (PID: 2924)
Executable content was dropped or overwritten
- opera.exe (PID: 2684)
- produkey_setup.exe (PID: 2924)
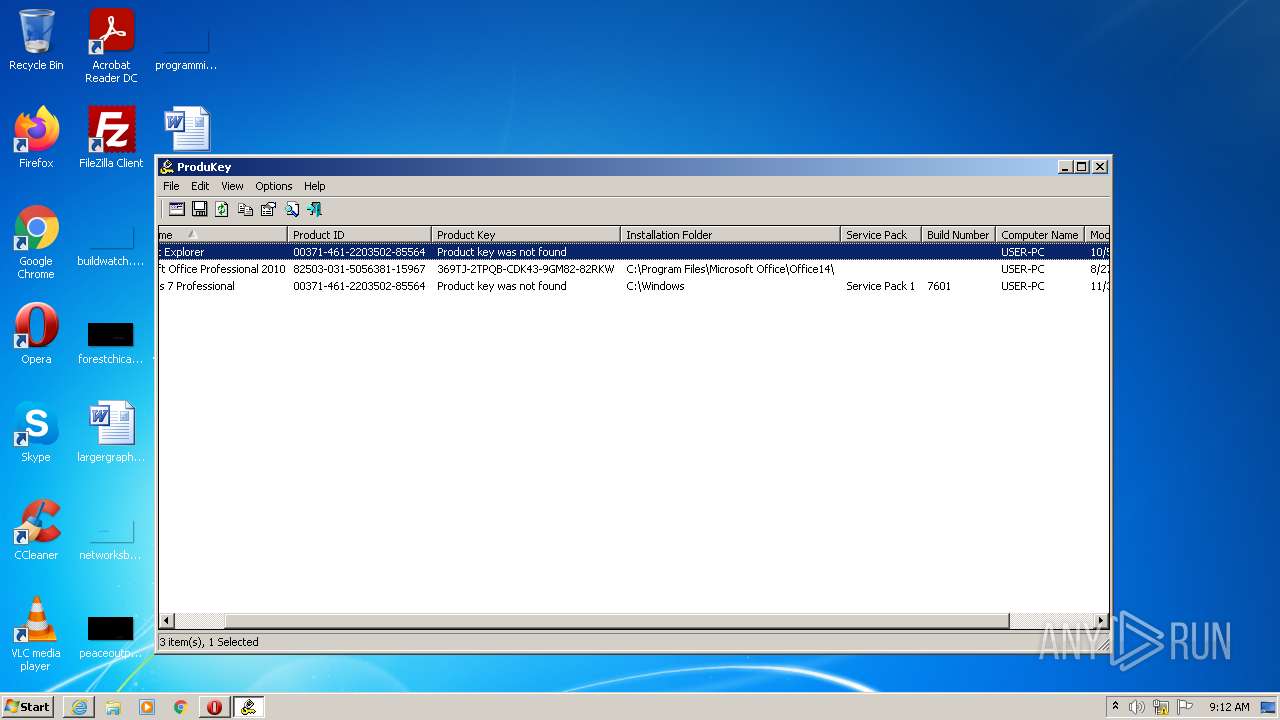
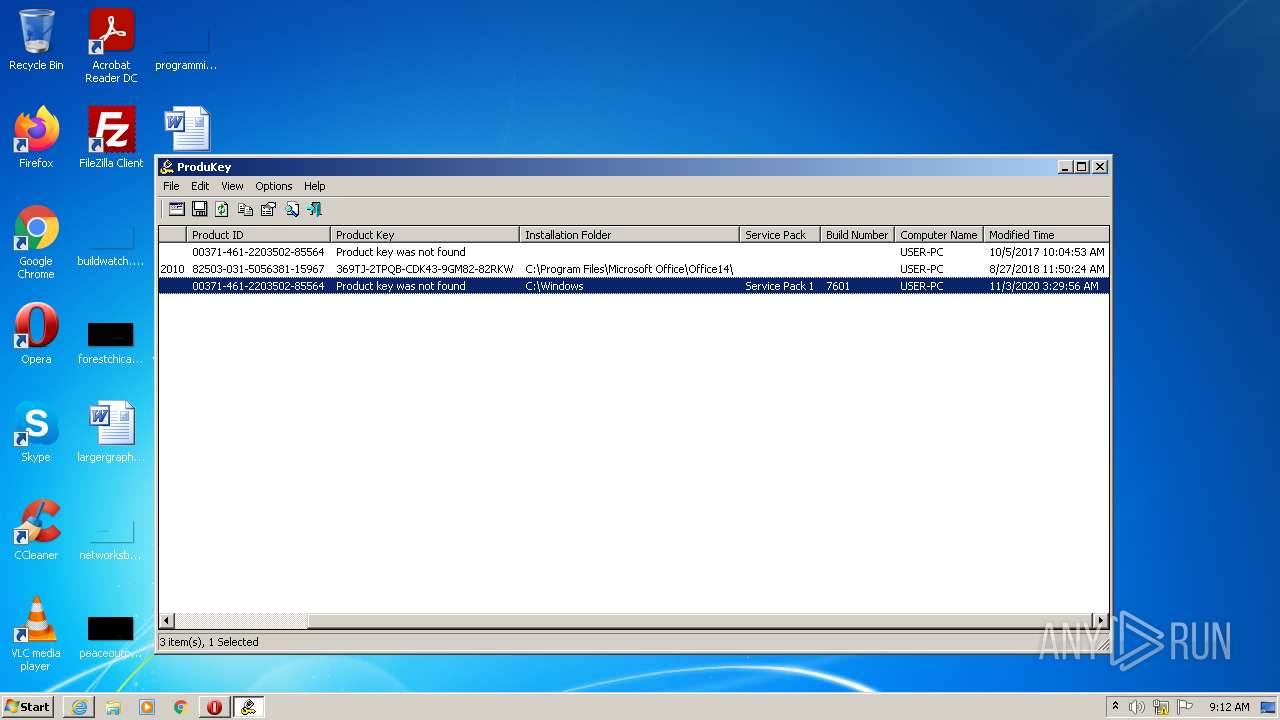
Reads the computer name
- produkey_setup.exe (PID: 2924)
- ProduKey.exe (PID: 1340)
- ProduKey.exe (PID: 3860)
Checks supported languages
- produkey_setup.exe (PID: 2924)
- ProduKey.exe (PID: 1340)
- ProduKey.exe (PID: 3860)
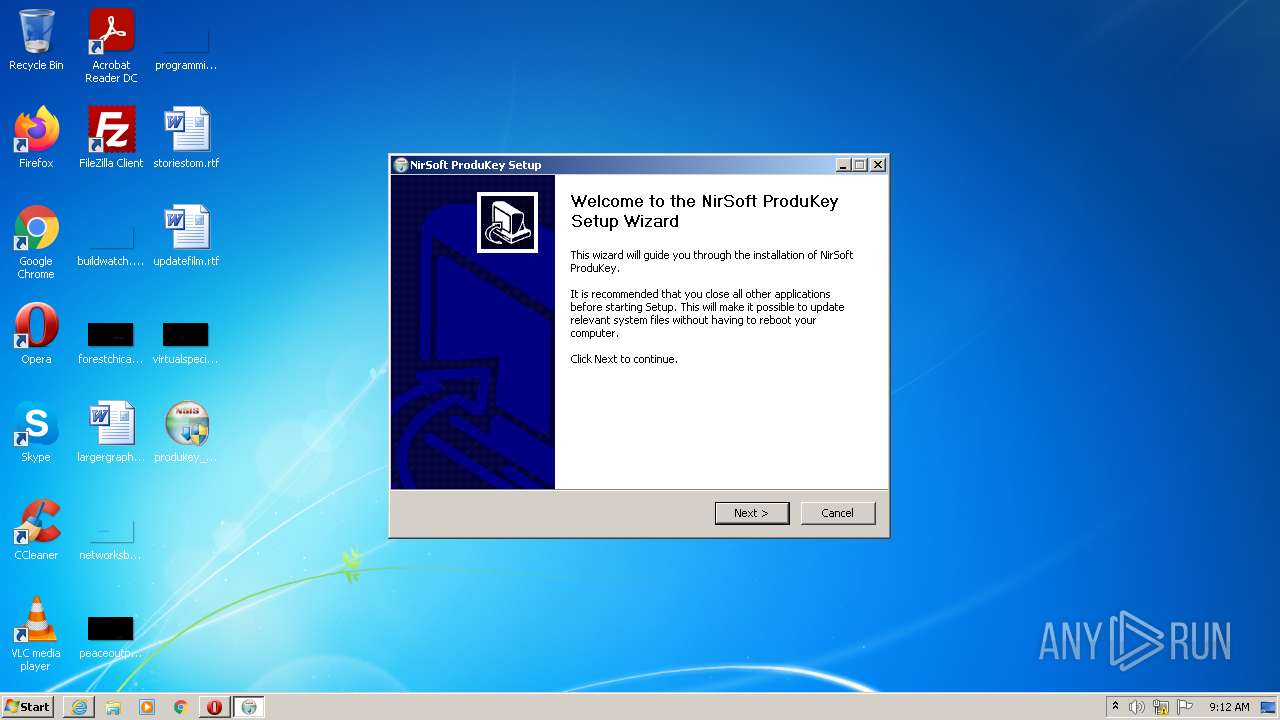
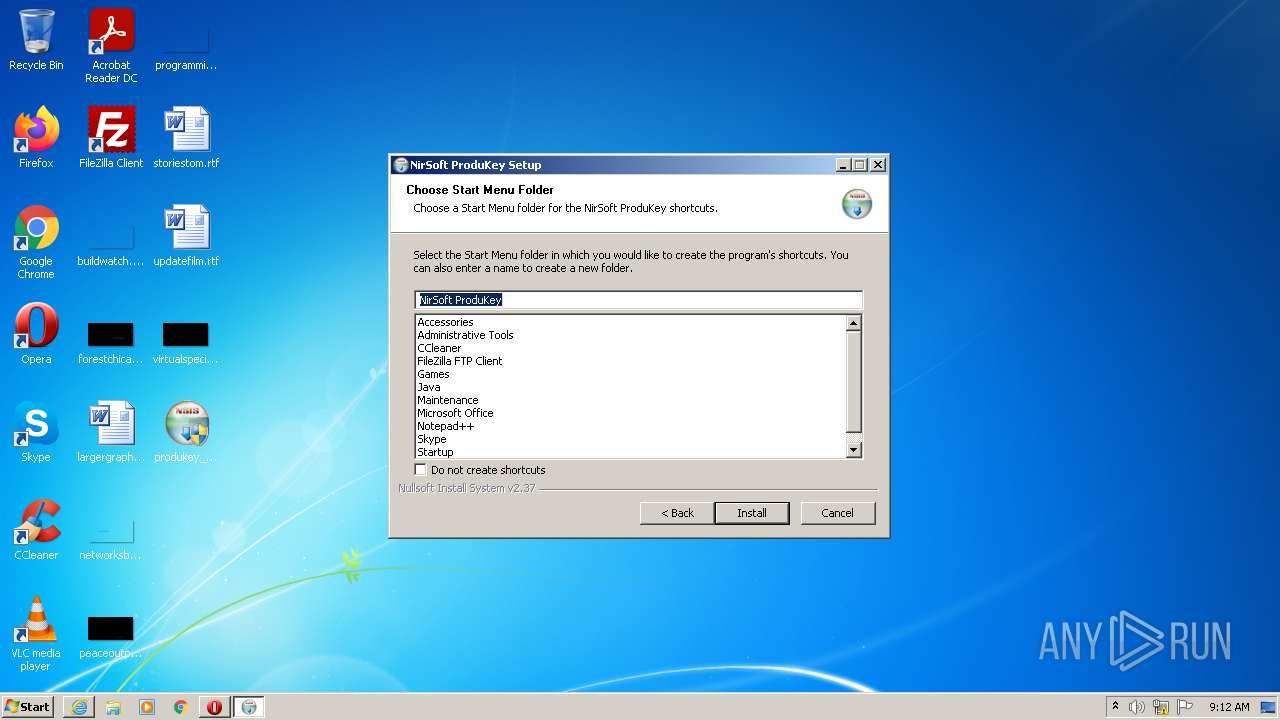
Creates a software uninstall entry
- produkey_setup.exe (PID: 2924)
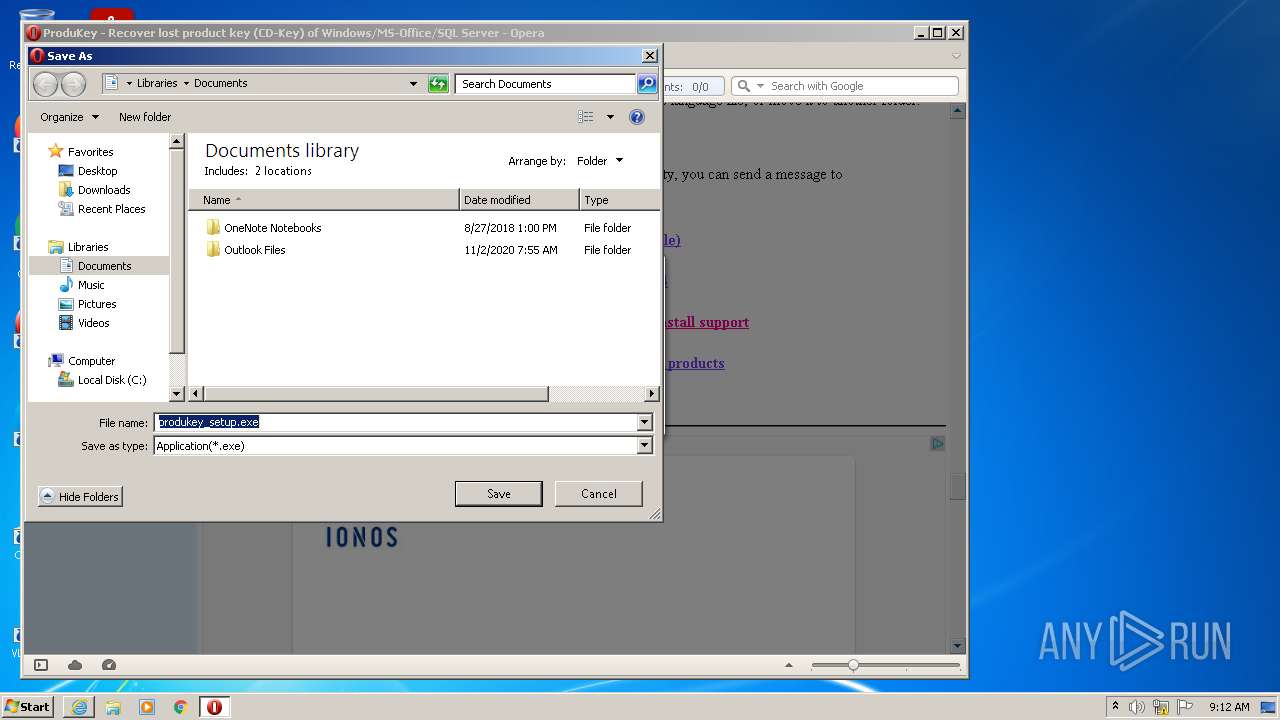
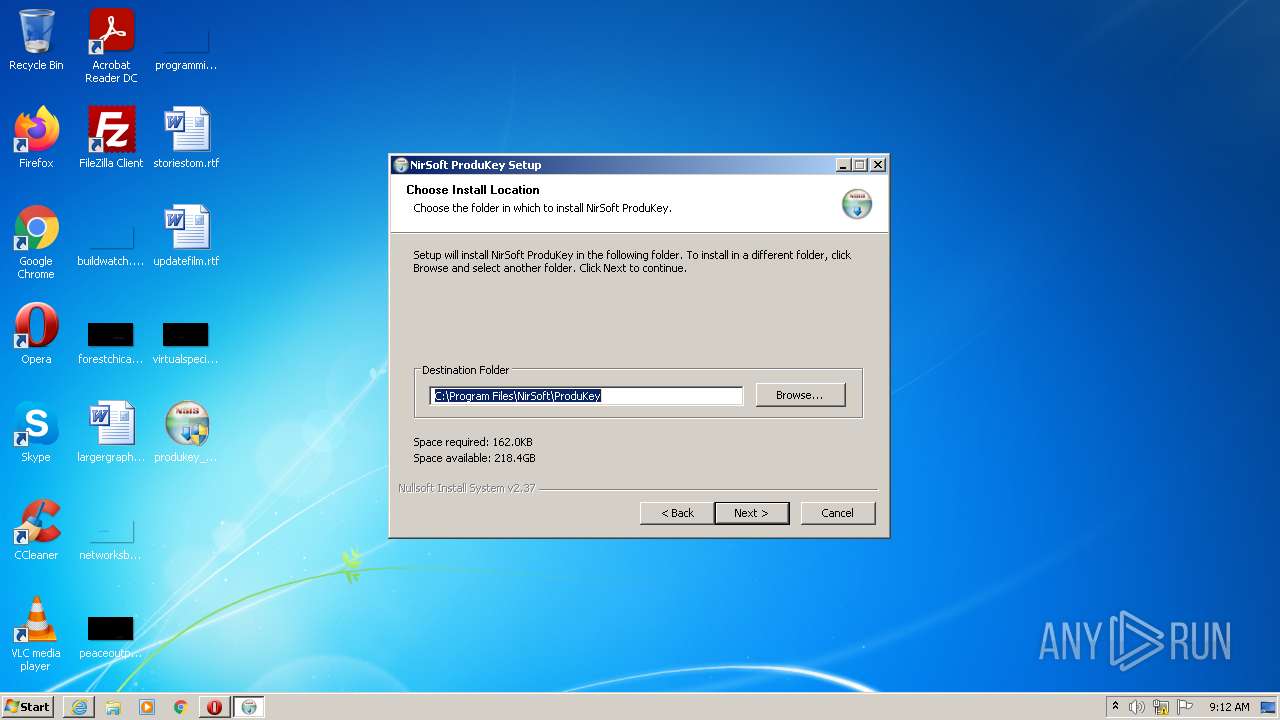
Creates a directory in Program Files
- produkey_setup.exe (PID: 2924)
Creates files in the program directory
- produkey_setup.exe (PID: 2924)
- ProduKey.exe (PID: 1340)
Creates files in the user directory
- produkey_setup.exe (PID: 2924)
Reads Environment values
- ProduKey.exe (PID: 1340)
- ProduKey.exe (PID: 3860)
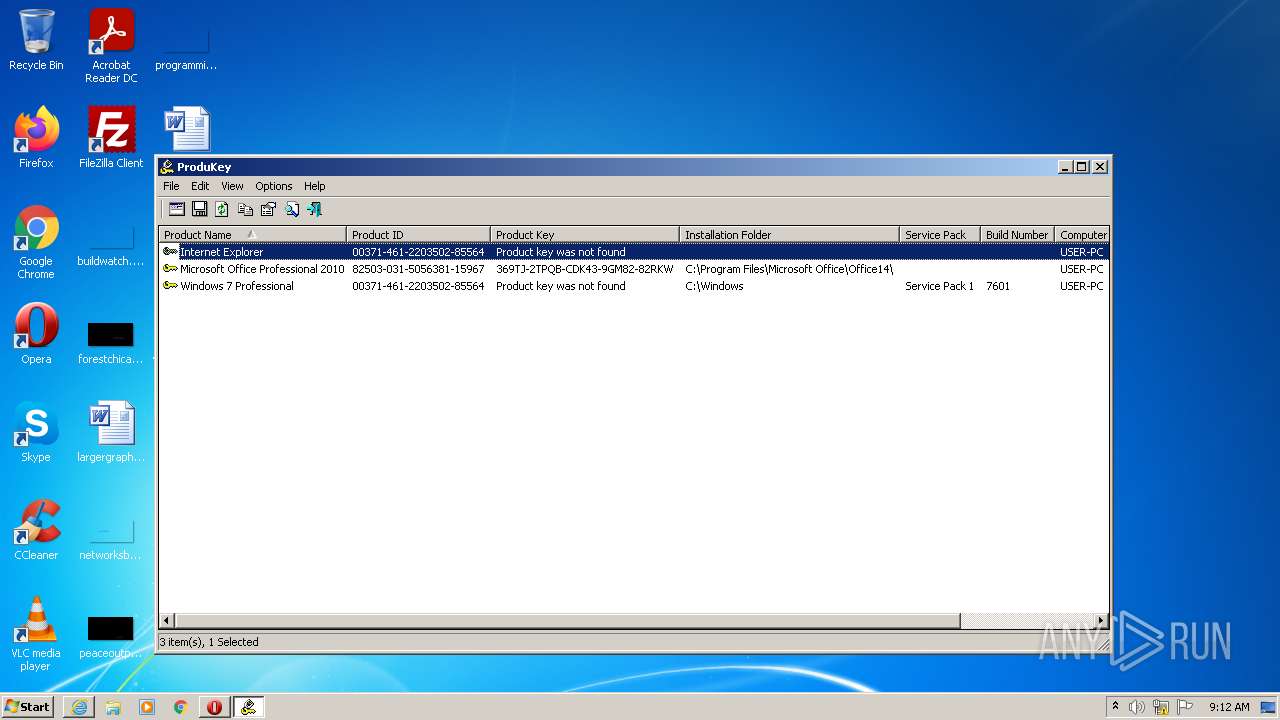
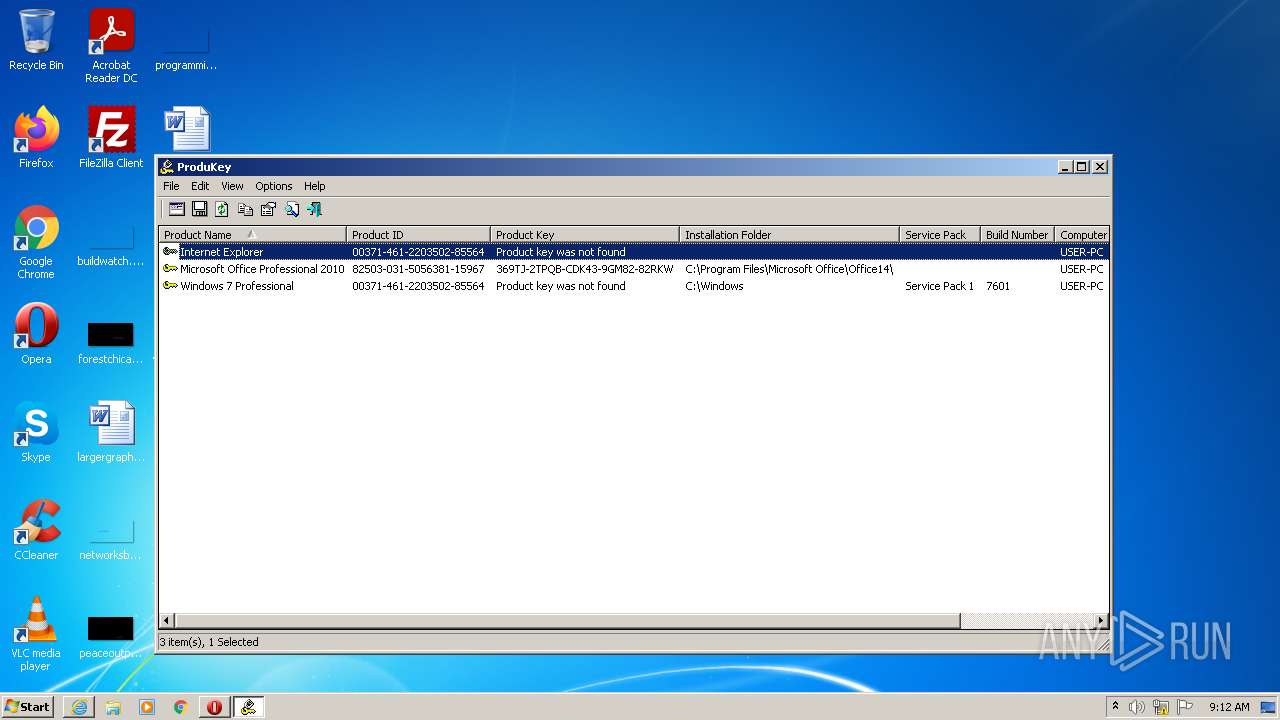
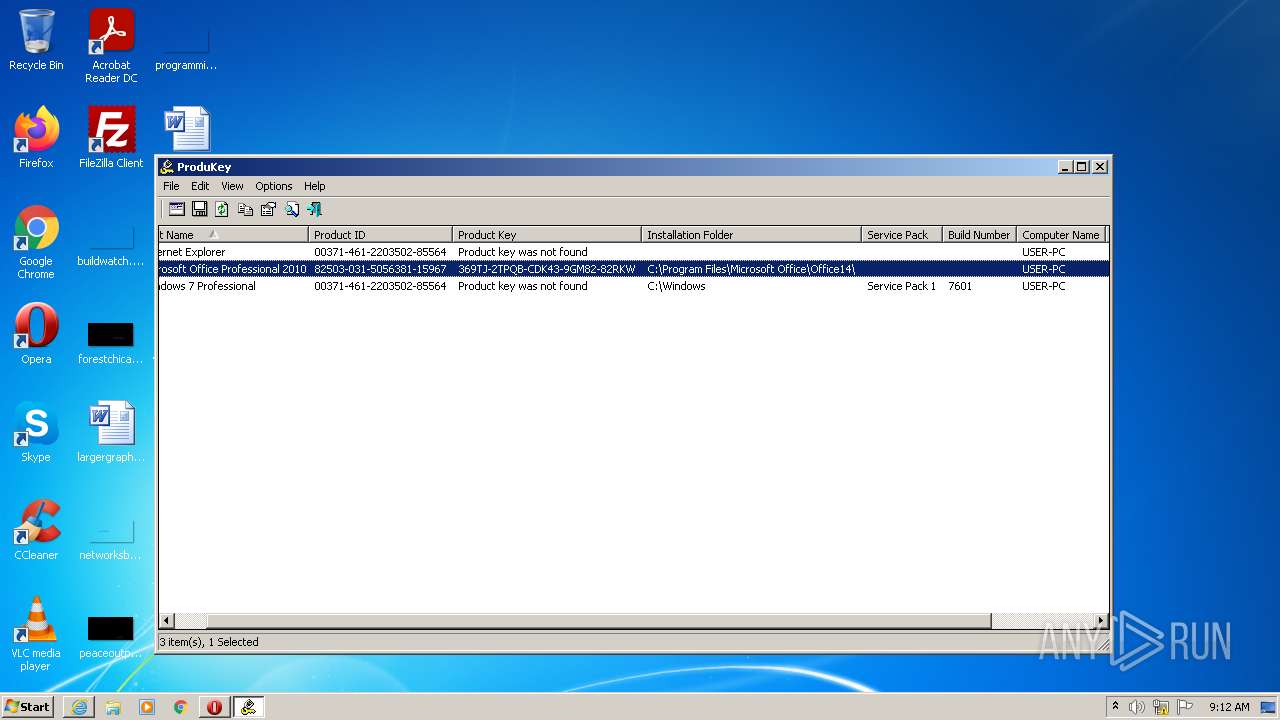
Reads Windows Product ID
- ProduKey.exe (PID: 1340)
- ProduKey.exe (PID: 3860)
INFO
Reads the computer name
- iexplore.exe (PID: 2900)
- iexplore.exe (PID: 3432)
- opera.exe (PID: 2684)
Changes internet zones settings
- iexplore.exe (PID: 2900)
Checks supported languages
- iexplore.exe (PID: 3432)
- opera.exe (PID: 2684)
- iexplore.exe (PID: 2900)
Checks Windows Trust Settings
- iexplore.exe (PID: 2900)
- iexplore.exe (PID: 3432)
Reads settings of System Certificates
- iexplore.exe (PID: 2900)
- iexplore.exe (PID: 3432)
Reads internet explorer settings
- iexplore.exe (PID: 3432)
Creates files in the user directory
- iexplore.exe (PID: 3432)
- opera.exe (PID: 2684)
- iexplore.exe (PID: 2900)
Changes settings of System certificates
- iexplore.exe (PID: 2900)
Check for Java to be installed
- opera.exe (PID: 2684)
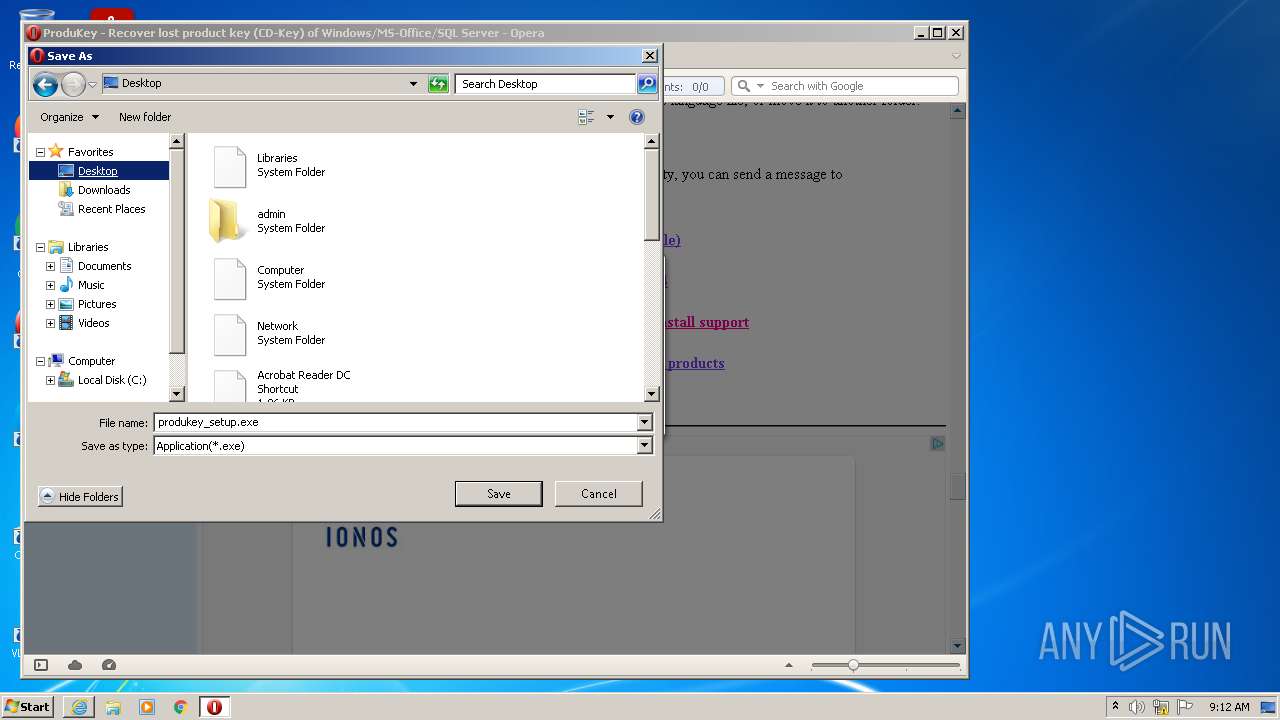
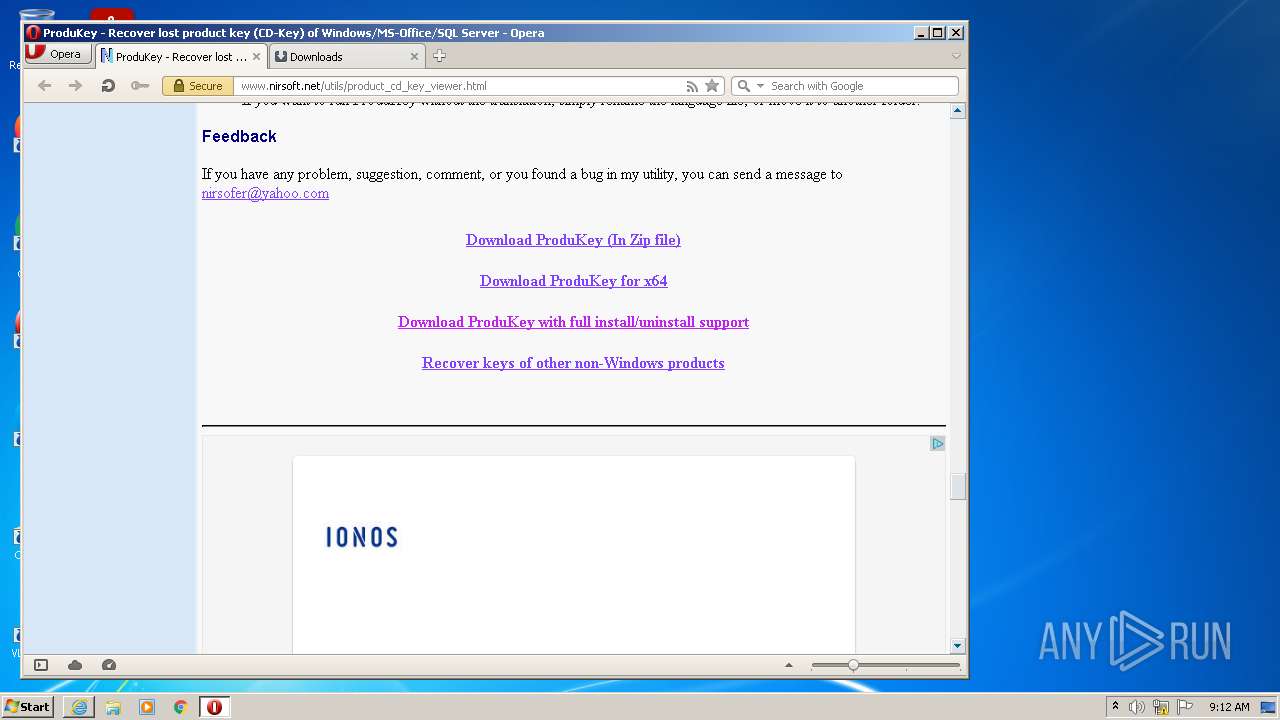
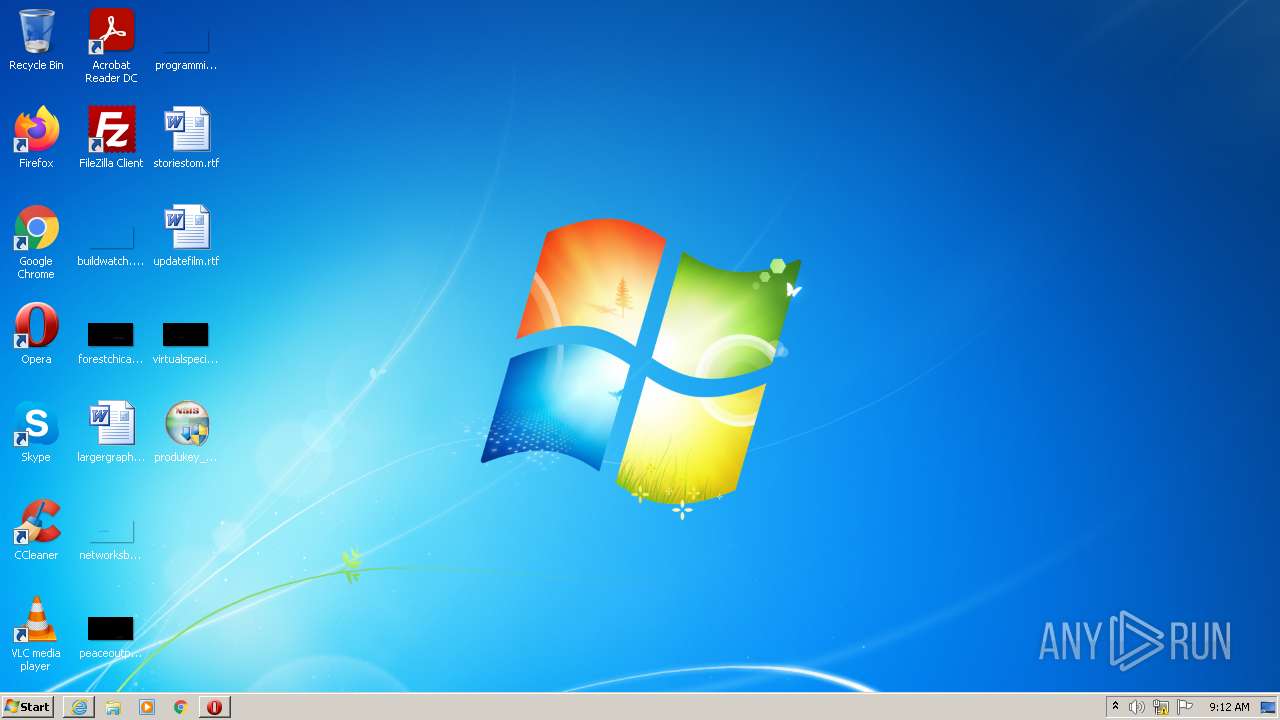
Manual execution by user
- opera.exe (PID: 2684)
- produkey_setup.exe (PID: 2924)
- produkey_setup.exe (PID: 2696)
- ProduKey.exe (PID: 3860)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2900)
Reads the date of Windows installation
- opera.exe (PID: 2684)
Application launched itself
- iexplore.exe (PID: 2900)
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 2684)
Reads Microsoft Office registry keys
- ProduKey.exe (PID: 1340)
- ProduKey.exe (PID: 3860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
7
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
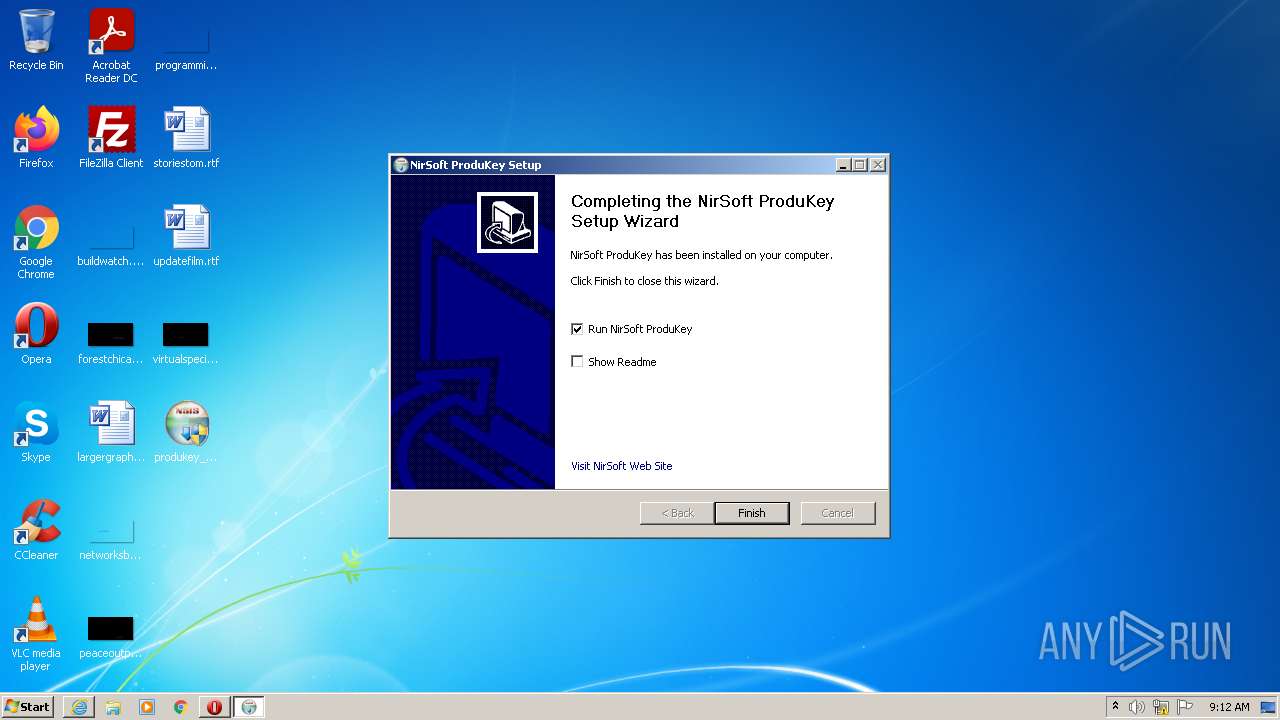
| 1340 | "C:\Program Files\NirSoft\ProduKey\ProduKey.exe" | C:\Program Files\NirSoft\ProduKey\ProduKey.exe | — | produkey_setup.exe | |||||||||||
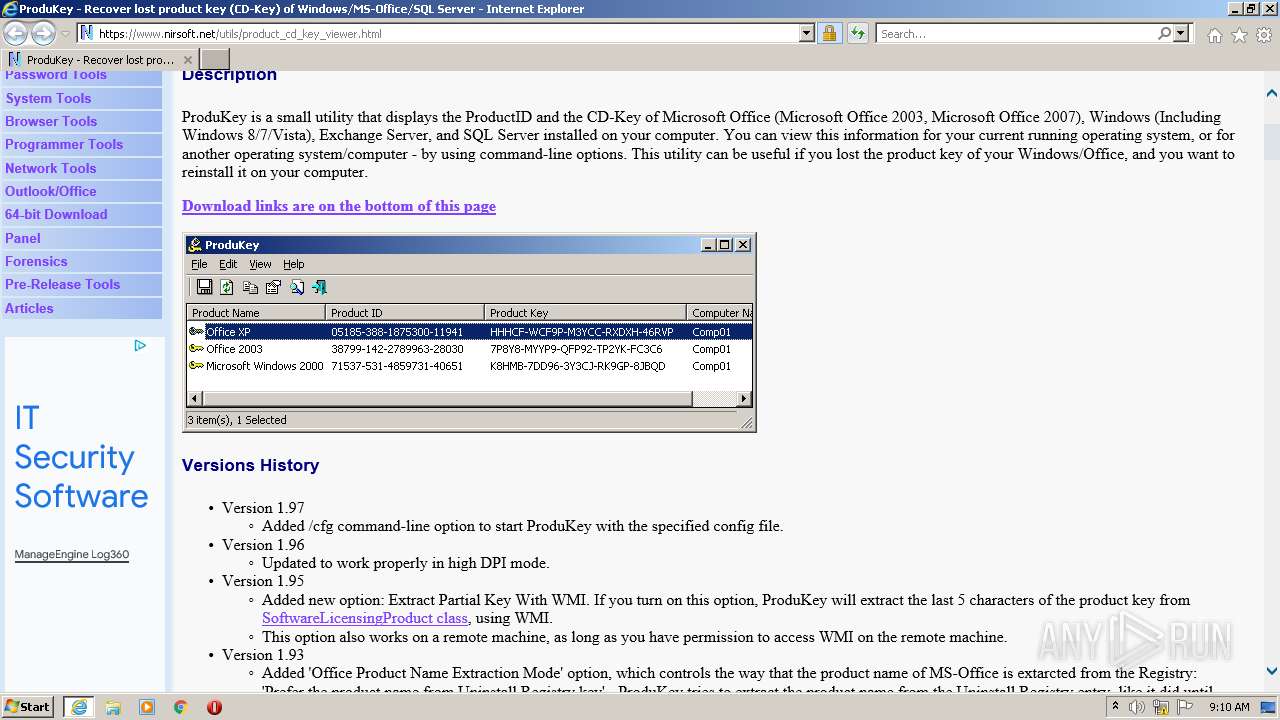
User: admin Company: NirSoft Integrity Level: HIGH Description: Shows Windows / Office product keys stored in the Registry Exit code: 0 Version: 1.97 Modules
| |||||||||||||||
| 2684 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | Explorer.EXE | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 2696 | "C:\Users\admin\Desktop\produkey_setup.exe" | C:\Users\admin\Desktop\produkey_setup.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2900 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.nirsoft.net/utils/product_cd_key_viewer.html" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2924 | "C:\Users\admin\Desktop\produkey_setup.exe" | C:\Users\admin\Desktop\produkey_setup.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3432 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2900 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3860 | "C:\Program Files\NirSoft\ProduKey\ProduKey.exe" | C:\Program Files\NirSoft\ProduKey\ProduKey.exe | — | Explorer.EXE | |||||||||||
User: admin Company: NirSoft Integrity Level: MEDIUM Description: Shows Windows / Office product keys stored in the Registry Exit code: 0 Version: 1.97 Modules
| |||||||||||||||
Total events
22 322
Read events
21 926
Write events
388
Delete events
8
Modification events
| (PID) Process: | (2900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30940162 | |||
| (PID) Process: | (2900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30940162 | |||
| (PID) Process: | (2900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
6
Suspicious files
86
Text files
151
Unknown types
46
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\5080DC7A65DB6A5960ECD874088F3328_862BA1770B2FEE013603D2FF9ABEAFDA | binary | |
MD5:FFBD623148EB308FC8D37FA23E15B6C8 | SHA256:52190C1D46884AD5BC38BC1662370D1D1060577F88353E36FFA9C311AA1BCE80 | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | binary | |
MD5:13BEAA5191465B94769A4299C9BBAD5A | SHA256:1C23EC6F1CCCA8682F3943605AFEA3CF4D5551BF92E8D872388C54E1AB5153EB | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5080DC7A65DB6A5960ECD874088F3328_862BA1770B2FEE013603D2FF9ABEAFDA | der | |
MD5:2E93F471312572F080AF8AFAEF3E53E6 | SHA256:43282A986B7D68DCC036D49F7695F0F705E29047685C8F95E1433B1DD5F9A3D7 | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:E5B488BE294E236E7E18BA6C9BFB375B | SHA256:222E9ED42BBB7D234E7E900A91958E8BECF9632BBA23C6E6B53229263901A1CE | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | der | |
MD5:40921730553B14F01DE1976350469541 | SHA256:441BEAAA0EE00144775B4BA447501435FFE1BE74DC0EB84AAA939DB6BD0AFDBF | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | binary | |
MD5:A2CCAA7CC18C4F6A876BE1CF793F0F71 | SHA256:16A2FF179A05B08432630B330C0878726292C05231638CF42ADC123D71DEE562 | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_2DBE917624E9880FE0C7C5570D56E691 | binary | |
MD5:C4904CA165C75F10527F0100DAD82526 | SHA256:E281D20ECEDC0621FEB146A88BE7EE04222D5353F54D50239E98A225413F9337 | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\nirsoft2[1].gif | image | |
MD5:2E7F628850F2705DDFCA2FB210322B00 | SHA256:0C4F483B95CFCE5C4E78F32946ED302502F365C272094950B254B6226C16C7F5 | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\product_cd_key_viewer[1].htm | html | |
MD5:01EB7A20EE8095D9C7952B4E2F0FD0FB | SHA256:F03239123097C98912CCA468D9F925C14F6753FCFB4B5021F213F1FC9965AD22 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
61
TCP/UDP connections
237
DNS requests
79
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3432 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3432 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEChvvh2IMBBwCgAAAAEuBFM%3D | US | der | 471 b | whitelisted |
3432 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCEQDwHUvue3yjezwFZqwFlyRY | US | der | 728 b | whitelisted |
3432 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDgBTRQd6qpTgoAAAABLgJY | US | der | 472 b | whitelisted |
3432 | iexplore.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEowSDBGMEQwQjAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCQDmOjriYr4IsA%3D%3D | US | der | 1.74 Kb | whitelisted |
3432 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCLHtDCfO2bBwoAAAABLgJa | US | der | 472 b | whitelisted |
3432 | iexplore.exe | GET | 200 | 104.117.200.9:80 | http://x1.c.lencr.org/ | US | der | 717 b | whitelisted |
3432 | iexplore.exe | GET | 200 | 23.32.238.219:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?7ea875a846600f57 | US | compressed | 59.9 Kb | whitelisted |
3432 | iexplore.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
3432 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDKa002niAMOQoAAAABLgV0 | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3432 | iexplore.exe | 104.18.30.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
2900 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2900 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3432 | iexplore.exe | 72.251.249.9:443 | ap.lijit.com | Voxel Dot Net, Inc. | NL | unknown |
3432 | iexplore.exe | 142.250.184.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3432 | iexplore.exe | 192.124.249.23:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
3432 | iexplore.exe | 104.75.88.126:443 | s7.addthis.com | Akamai Technologies, Inc. | NL | suspicious |
3432 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3432 | iexplore.exe | 142.250.186.162:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3432 | iexplore.exe | 216.58.212.168:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.nirsoft.net |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
ap.lijit.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2684 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2684 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2684 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2684 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2684 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2684 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |