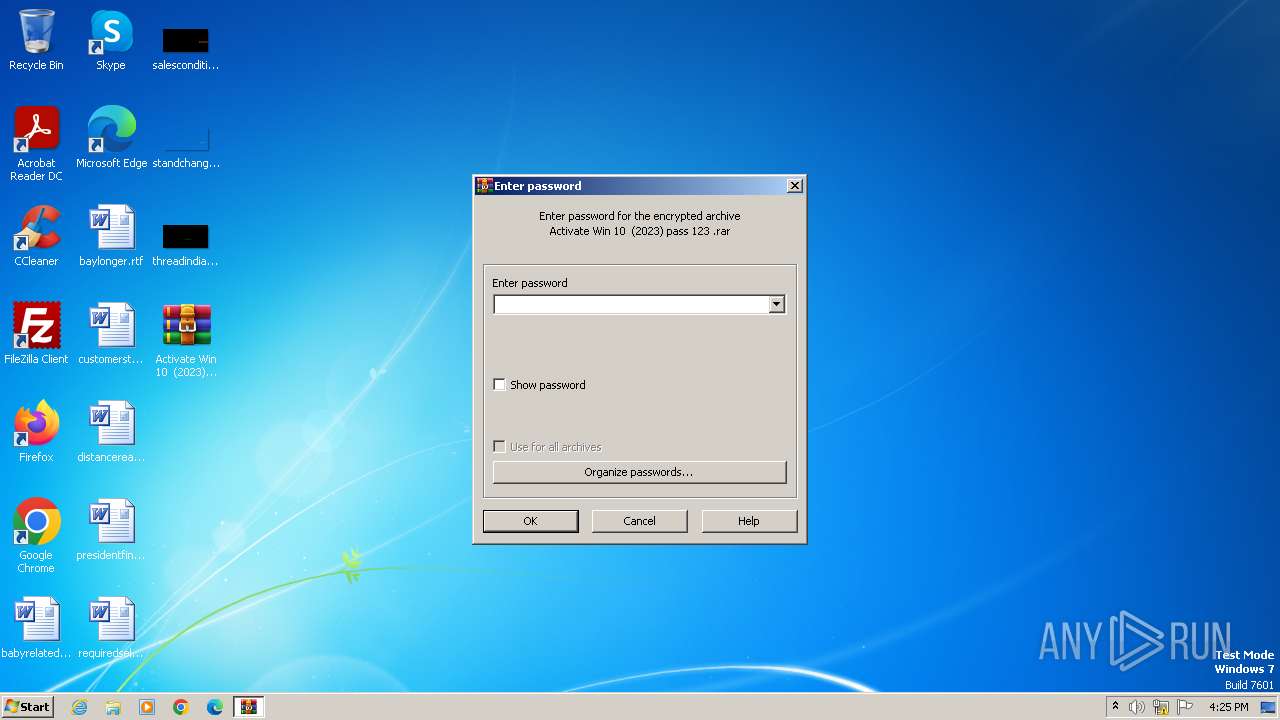
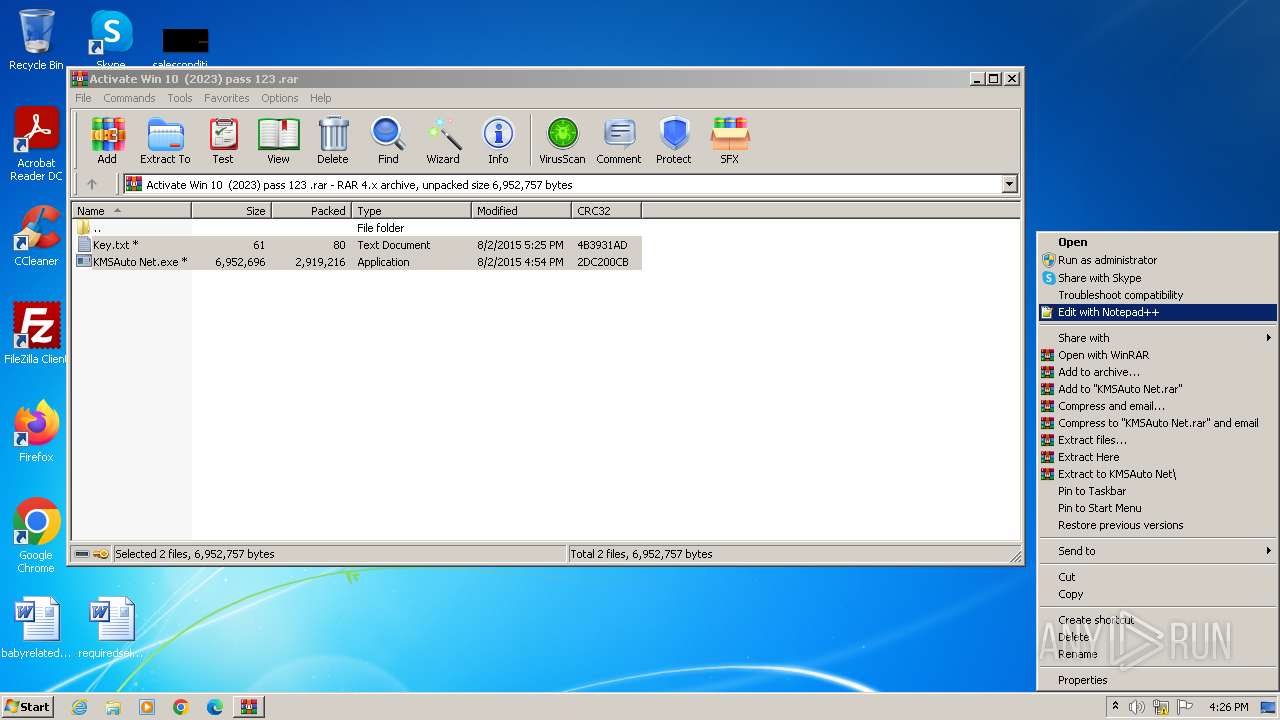
| File name: | Activate Win 10 (2023) pass 123 .rar |
| Full analysis: | https://app.any.run/tasks/dbc41d41-b3d4-4098-946a-420f8bc7f1aa |
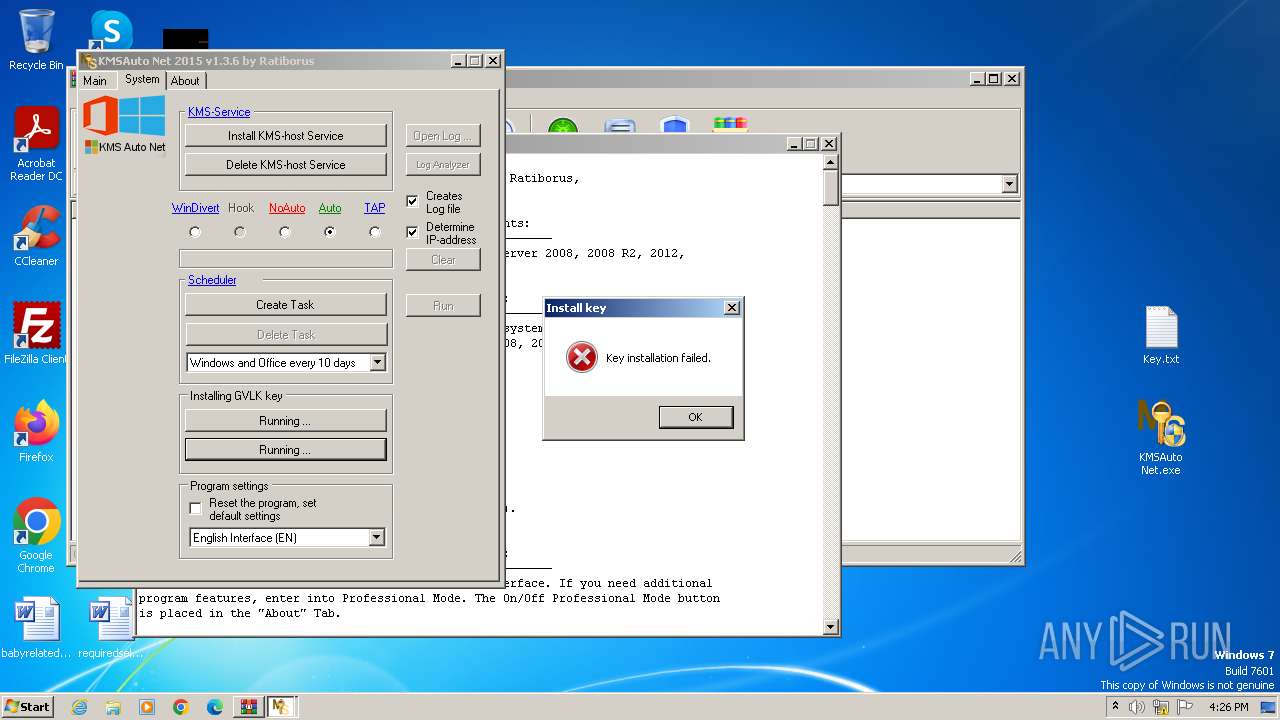
| Verdict: | Malicious activity |
| Analysis date: | December 01, 2023, 16:25:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, flags: EncryptedBlockHeader |
| MD5: | 3AECAE9768BF935511C54023A2F6C796 |
| SHA1: | DDDBA757D9FC2B9B6CC297CC3B3F27455CC89523 |
| SHA256: | 066CA65217C2D3B01796D9EA6FD843F2EEAF3A34CD9FB617D461209C6A26BD30 |
| SSDEEP: | 98304:GYoZuaZlEZAxS5Bgsmfd0JDRcyYGC0I/Mzhp4GX61DnpU81471mSKWBX2xTjf/Jt:GFF |
MALICIOUS
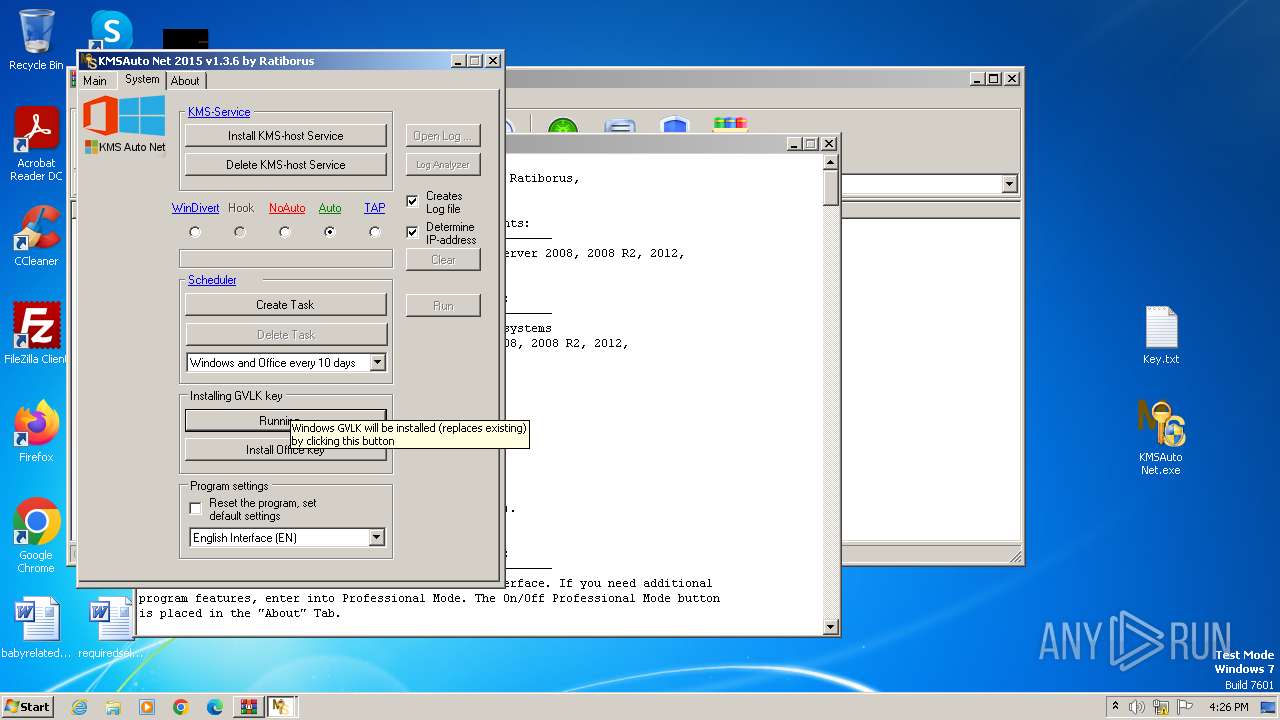
Opens a text file (SCRIPT)
- cscript.exe (PID: 2988)
SUSPICIOUS
Reads Internet Explorer settings
- KMSAuto Net.exe (PID: 2928)
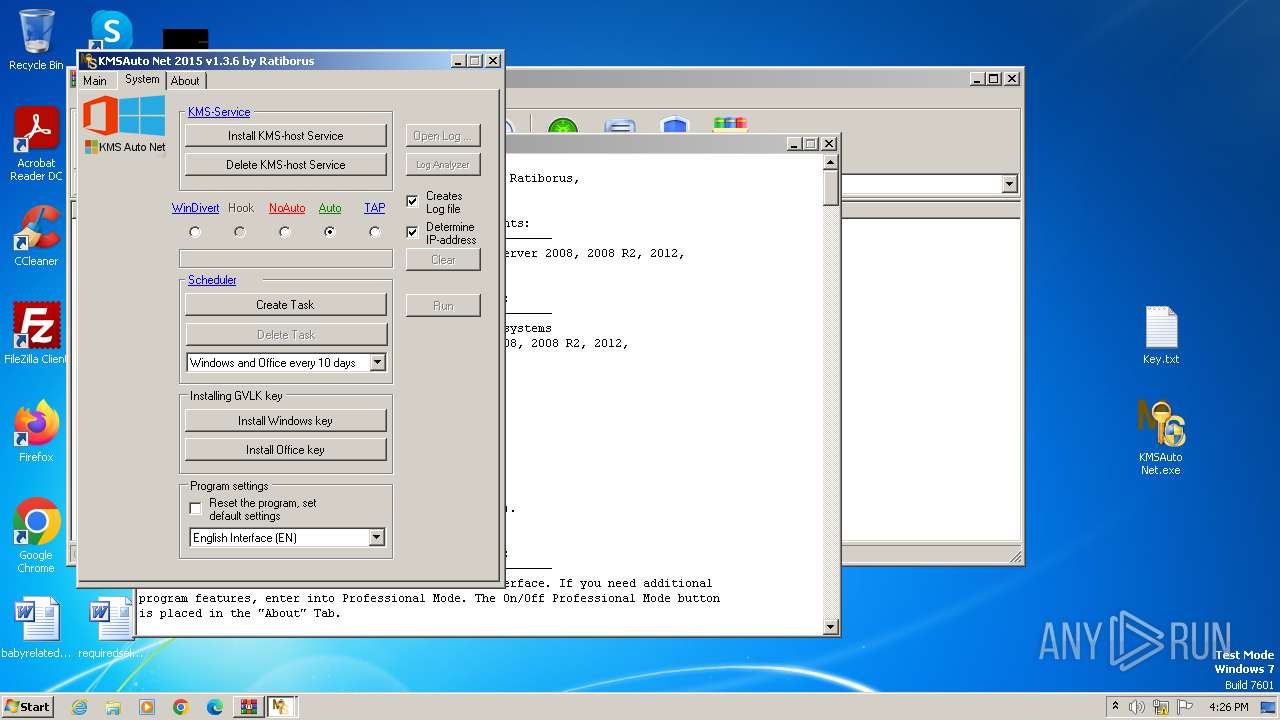
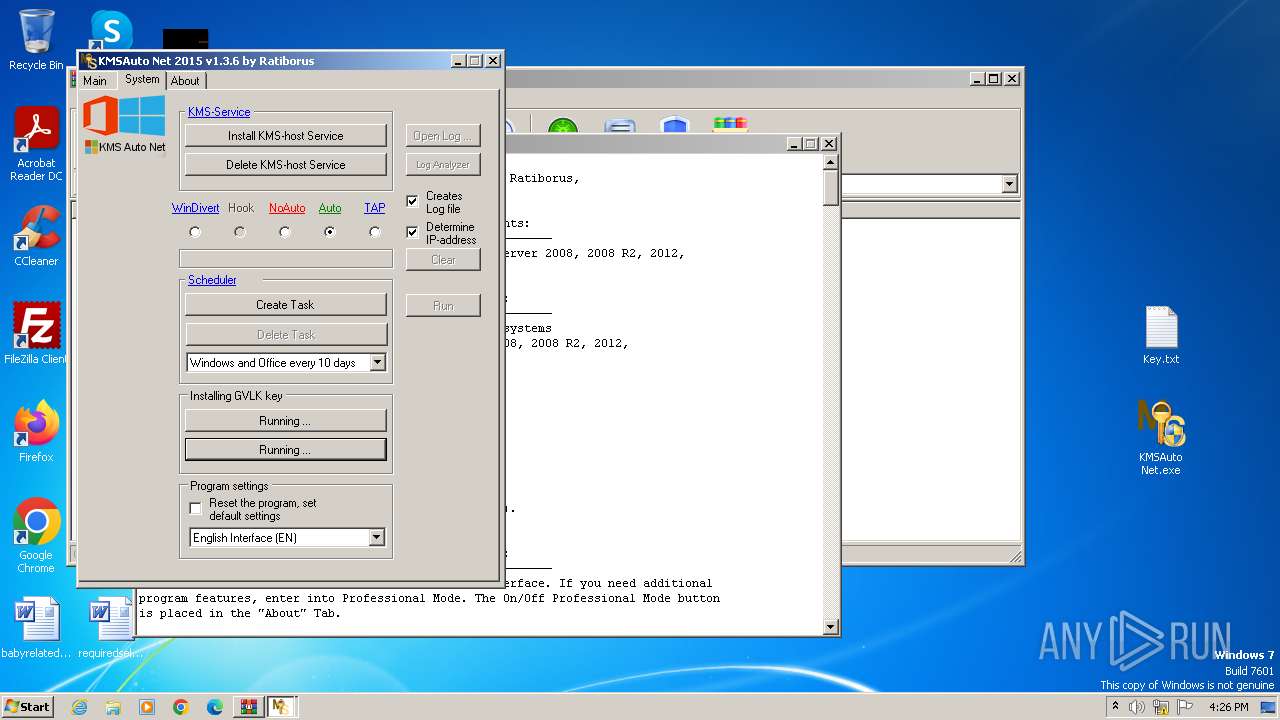
Starts CMD.EXE for commands execution
- KMSAuto Net.exe (PID: 2928)
The process executes VB scripts
- KMSAuto Net.exe (PID: 2928)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- cscript.exe (PID: 2988)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 2988)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 2988)
Checks whether a specific file exists (SCRIPT)
- cscript.exe (PID: 2988)
Reads data from a binary Stream object (SCRIPT)
- cscript.exe (PID: 2988)
Executes WMI query (SCRIPT)
- cscript.exe (PID: 2988)
INFO
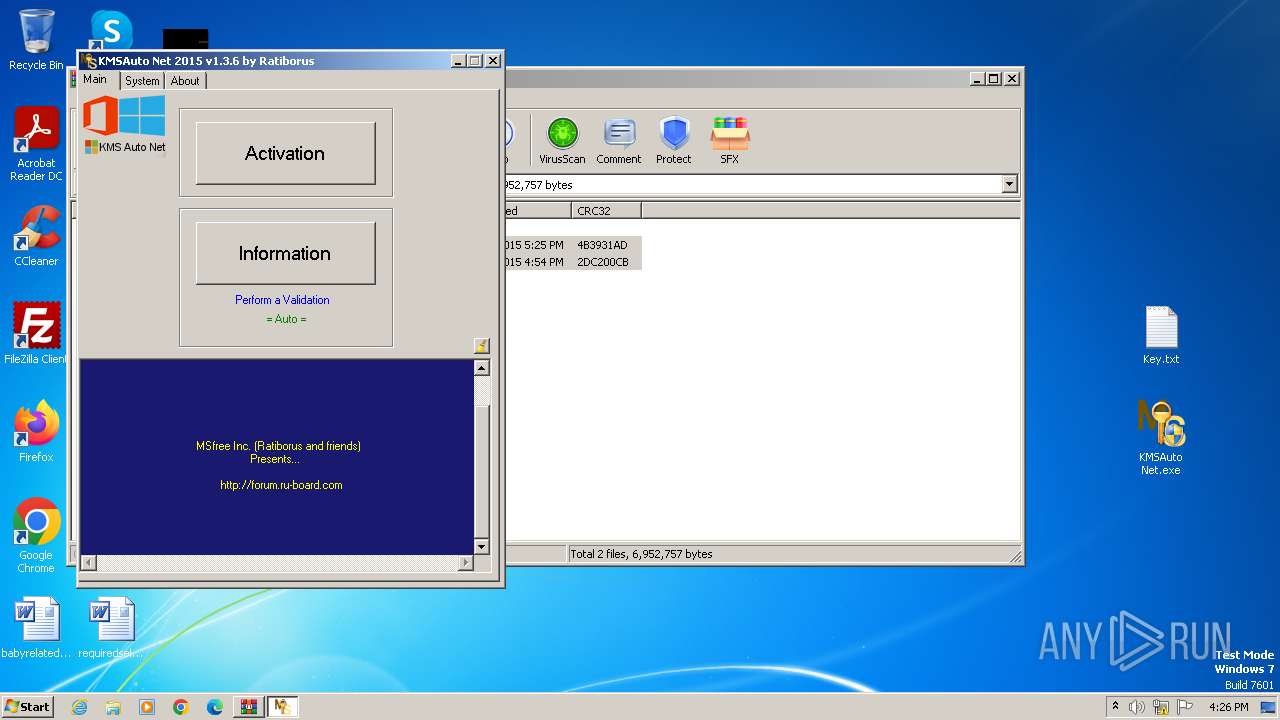
Manual execution by a user
- KMSAuto Net.exe (PID: 2928)
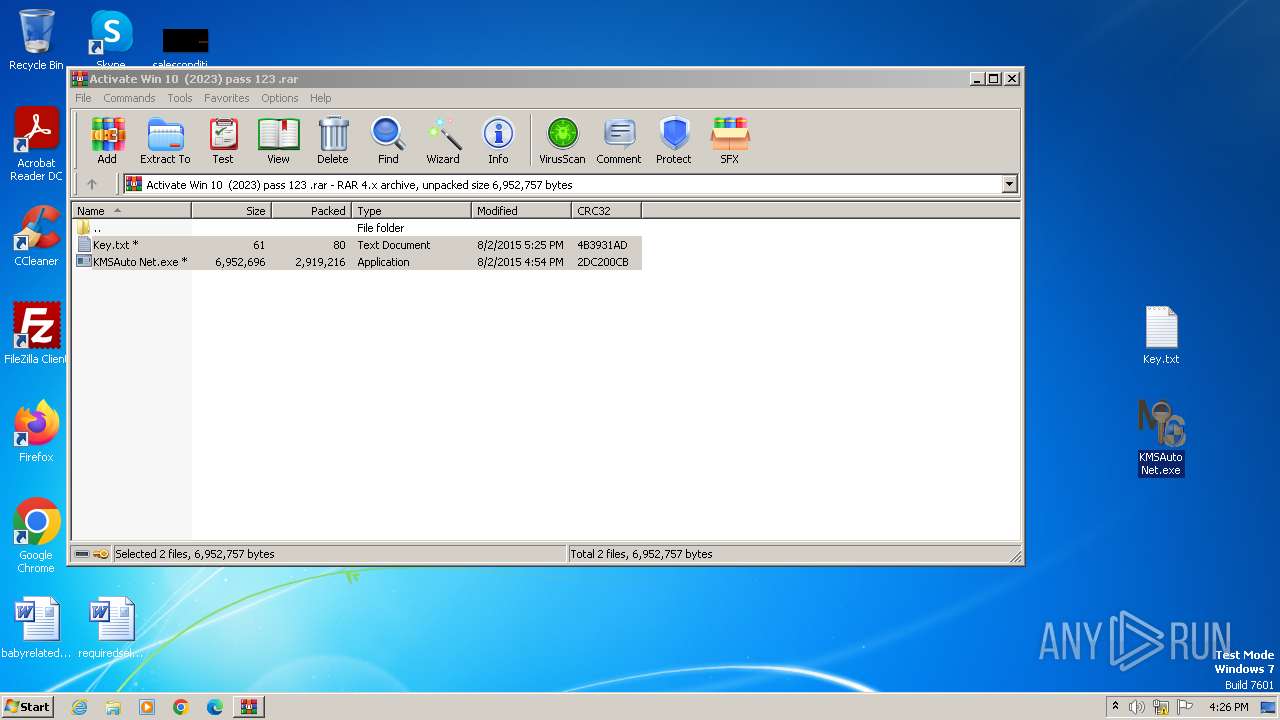
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2644)
Checks supported languages
- KMSAuto Net.exe (PID: 2928)
Reads the computer name
- KMSAuto Net.exe (PID: 2928)
Creates files or folders in the user directory
- KMSAuto Net.exe (PID: 2928)
Reads Environment values
- KMSAuto Net.exe (PID: 2928)
Reads product name
- KMSAuto Net.exe (PID: 2928)
Reads the machine GUID from the registry
- KMSAuto Net.exe (PID: 2928)
Reads security settings of Internet Explorer
- cscript.exe (PID: 2988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
Total processes
55
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 600 | cmd /c echo test>>"C:\Users\admin\Desktop\test.test" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1328 | cmd /c md "C:\Users\admin\AppData\Local\MSfree Inc" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
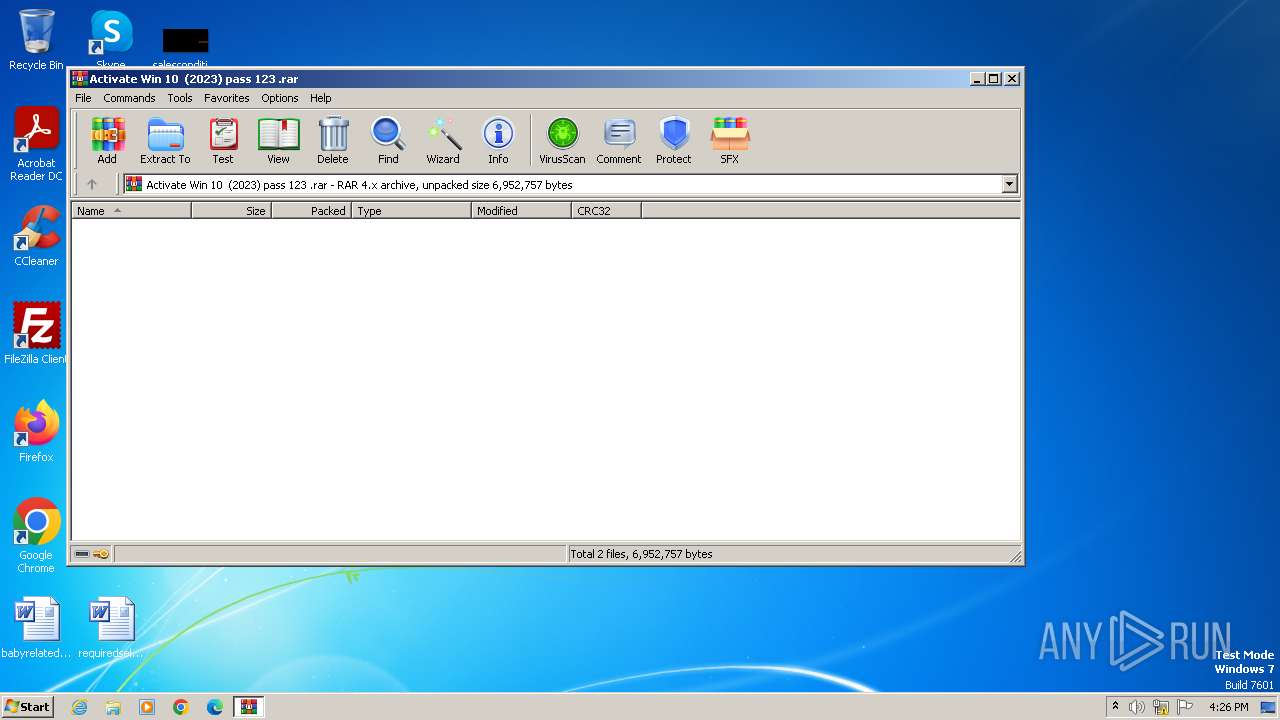
| 2644 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Activate Win 10 (2023) pass 123 .rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
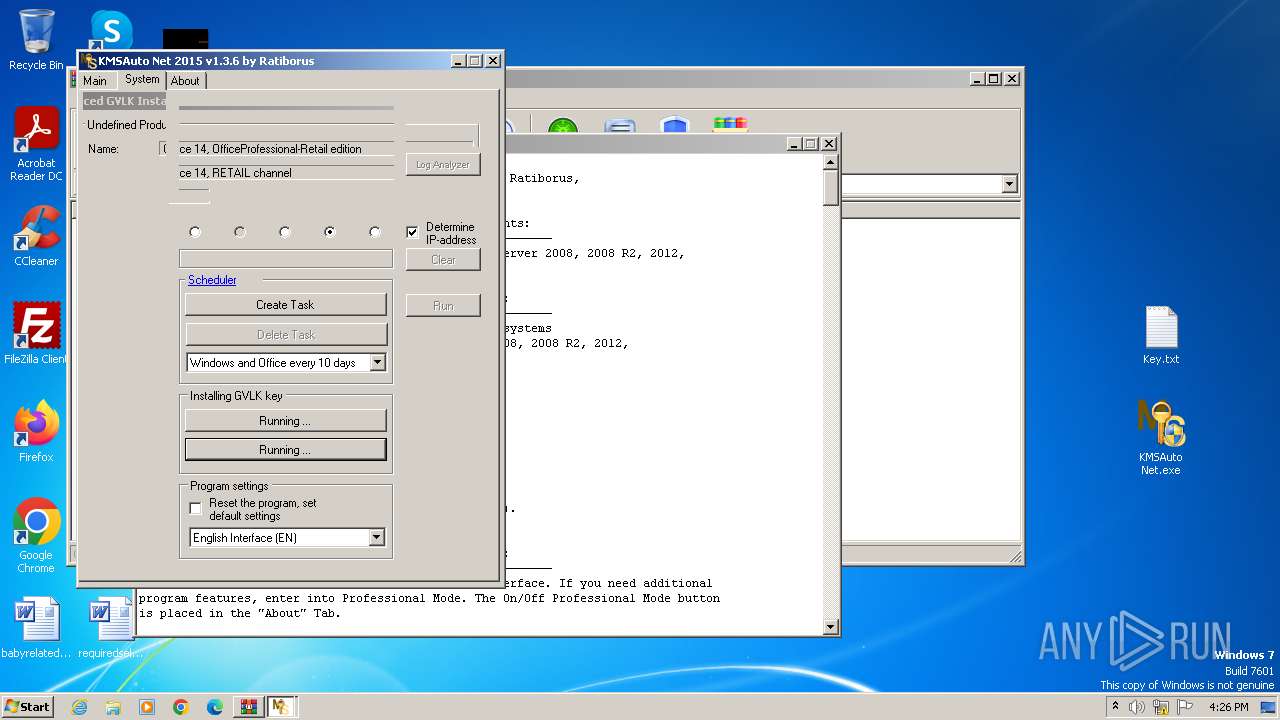
| 2928 | "C:\Users\admin\Desktop\KMSAuto Net.exe" | C:\Users\admin\Desktop\KMSAuto Net.exe | explorer.exe | ||||||||||||
User: admin Company: MSFree Inc. Integrity Level: HIGH Description: KMSAuto Net Exit code: 0 Version: 1.3.6 Modules
| |||||||||||||||
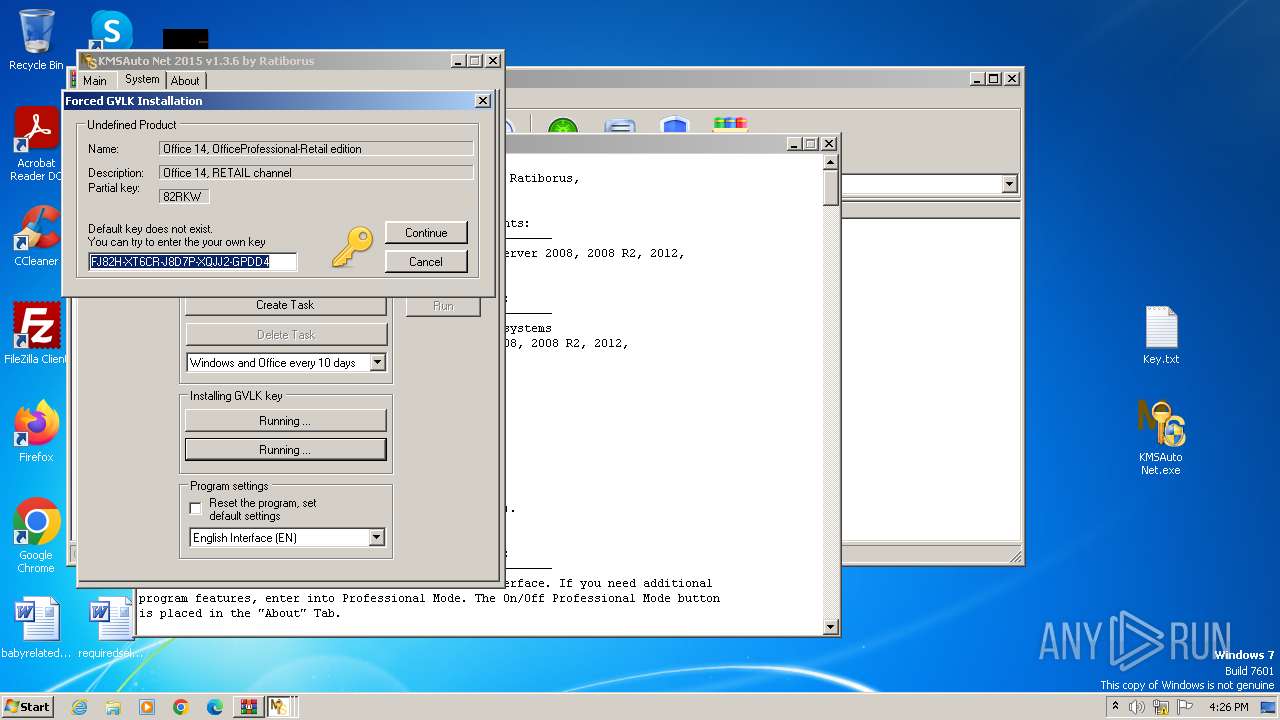
| 2988 | "cscript.exe" /nologo C:\Windows\system32\slmgr.vbs /ipk FJ82H-XT6CR-J8D7P-XQJJ2-GPDD4 | C:\Windows\System32\cscript.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3856 | C:\Windows\System32\cmd.exe /c del /F /Q "test.test" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 153
Read events
1 144
Write events
9
Delete events
0
Modification events
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
1
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 600 | cmd.exe | C:\Users\admin\Desktop\test.test | text | |
MD5:9F06243ABCB89C70E0C331C61D871FA7 | SHA256:837CCB607E312B170FAC7383D7CCFD61FA5072793F19A25E75FBACB56539B86B | |||
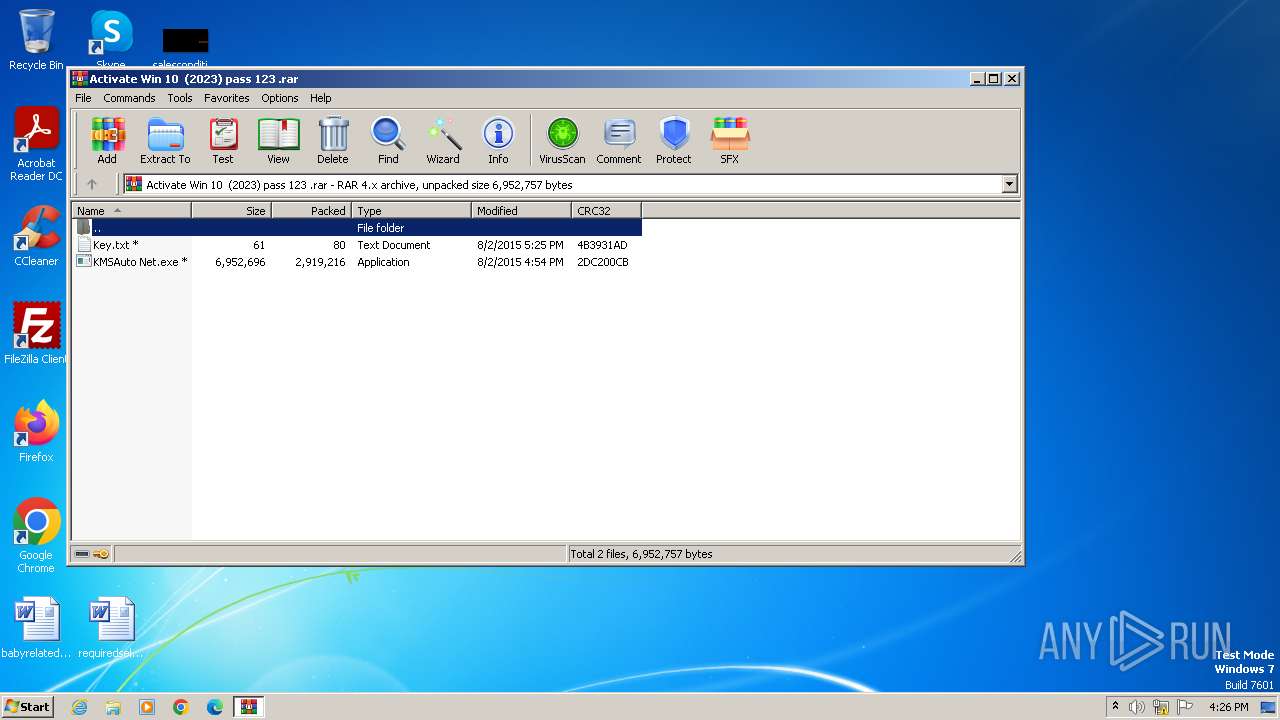
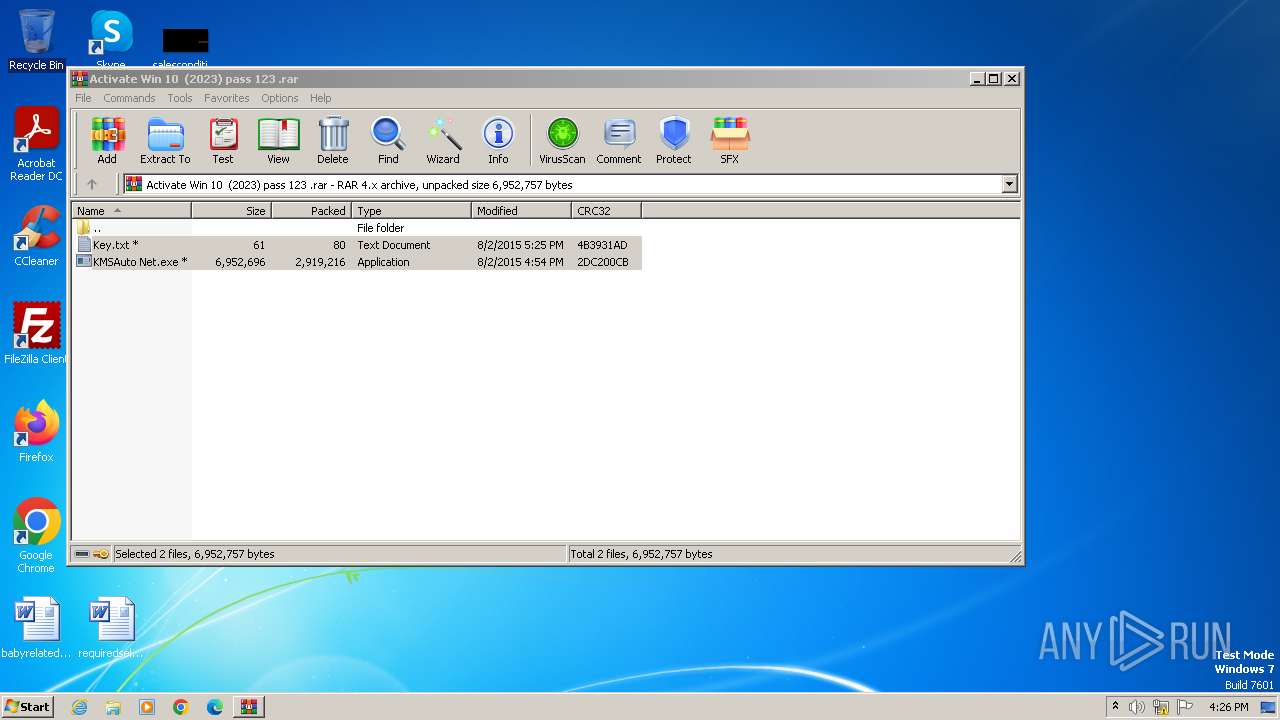
| 2644 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2644.45279\Key.txt | text | |
MD5:88633B84DBD7584161666089EA27FBCB | SHA256:4A0A48B790A63A5BA8234FAAFCCB56689105A42304B4EB5B82B3F43B9A836DC2 | |||
| 2928 | KMSAuto Net.exe | C:\Users\admin\AppData\Local\MSfree Inc\kmsauto.ini | text | |
MD5:33C2F031B8C6D6CB29F964A54FEDAA13 | SHA256:54BC7607535F2EC23A258FDD96257B2CE4374705599EF3E09A7B5643B08035E8 | |||
| 2644 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2644.45279\KMSAuto Net.exe | executable | |
MD5:DBDDA4670CF42B040BFD731DBFE95C7A | SHA256:DA4D393A59722019C2176C6897171758CEA344A9EF34C5AFD219488B304368C2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |