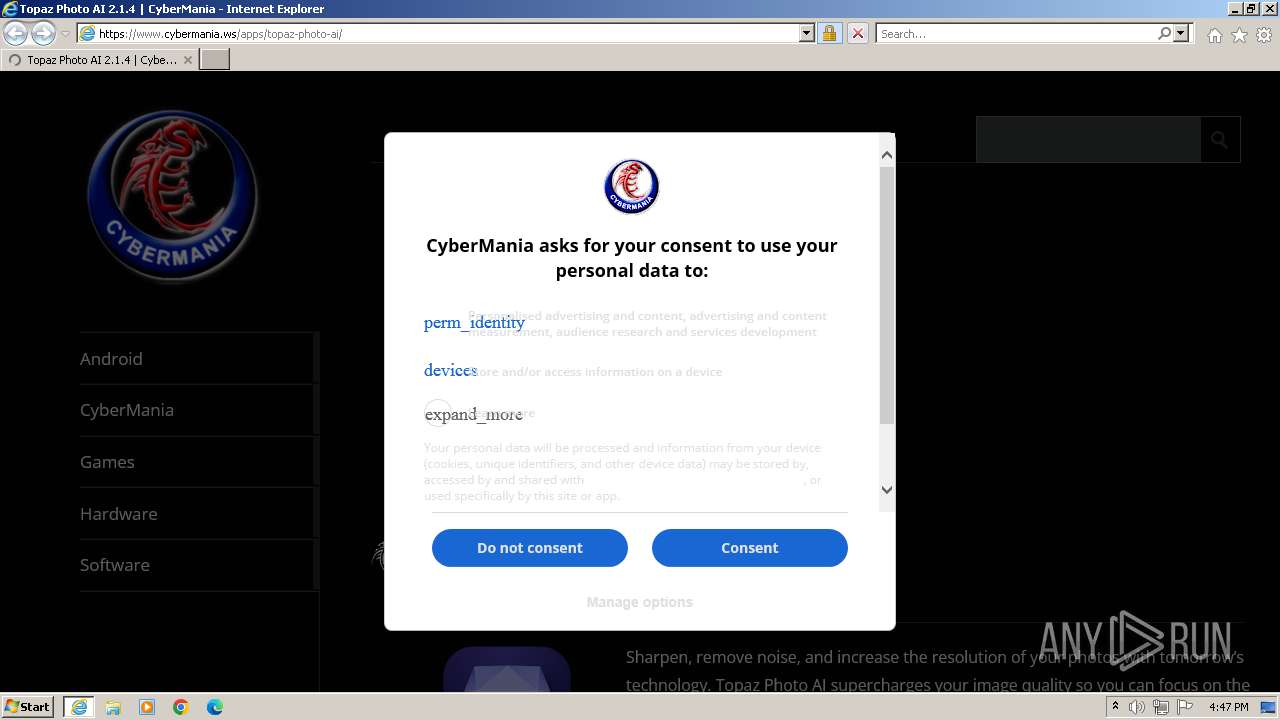
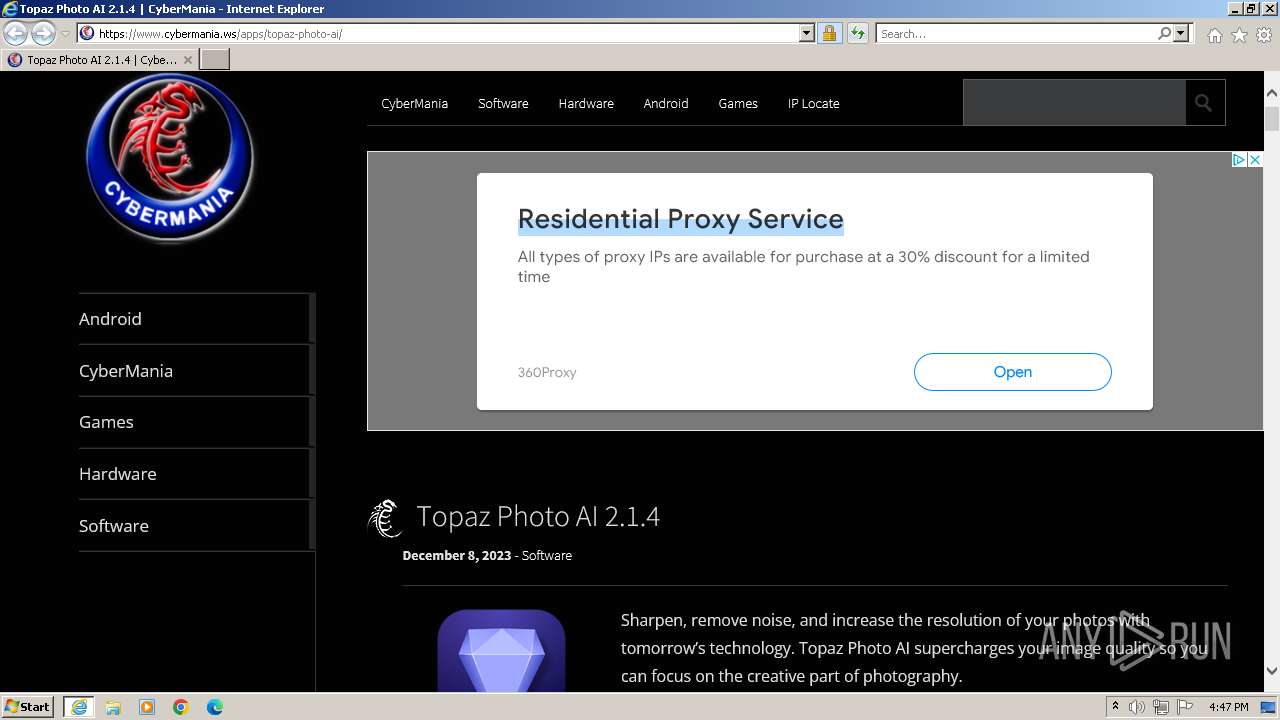
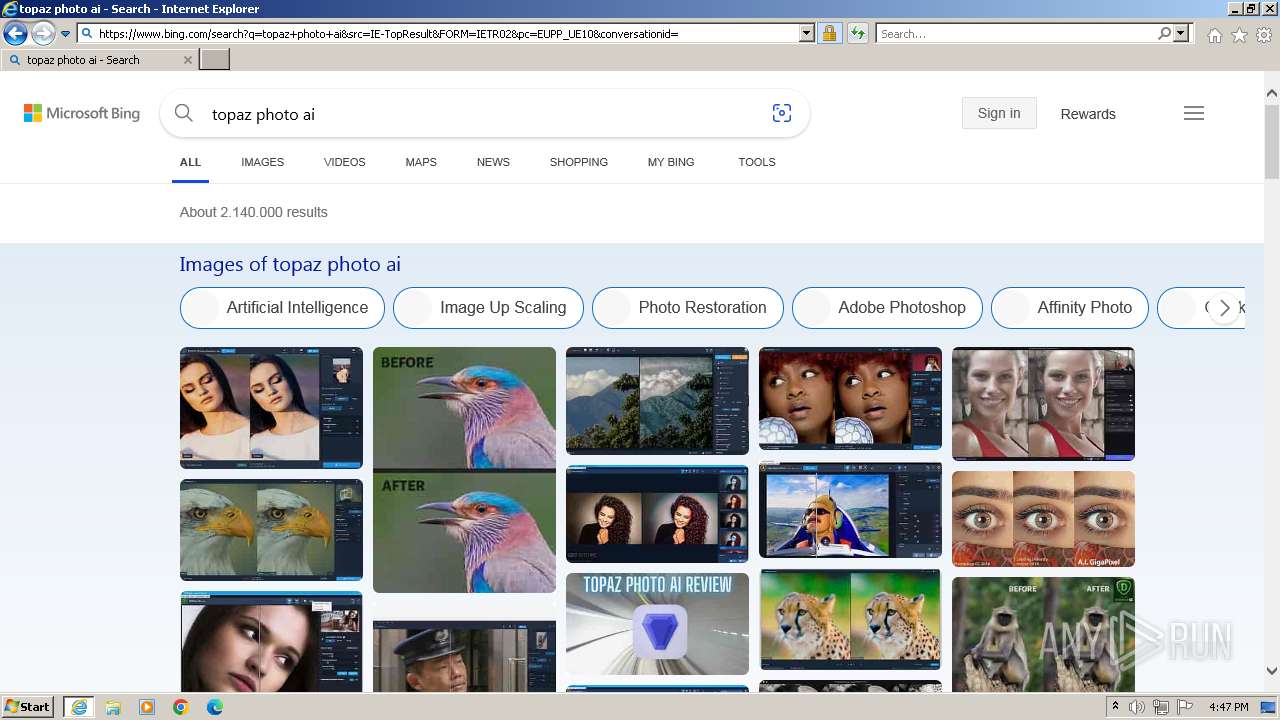
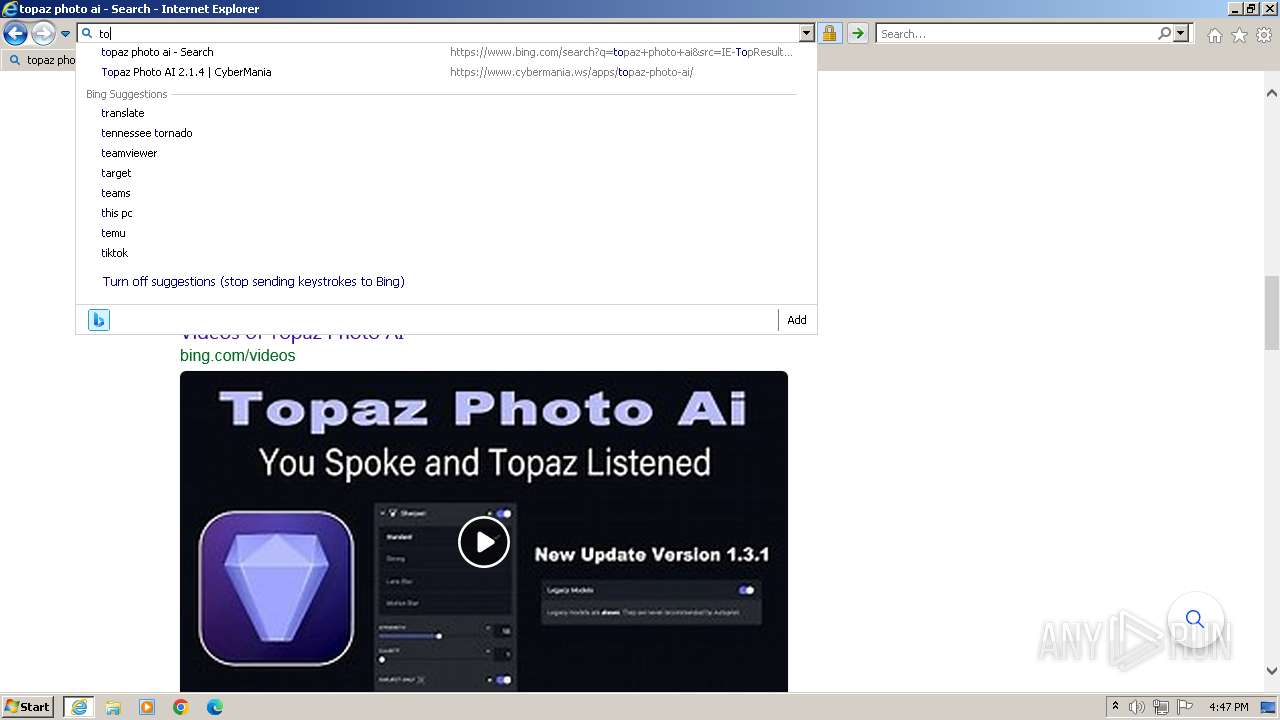
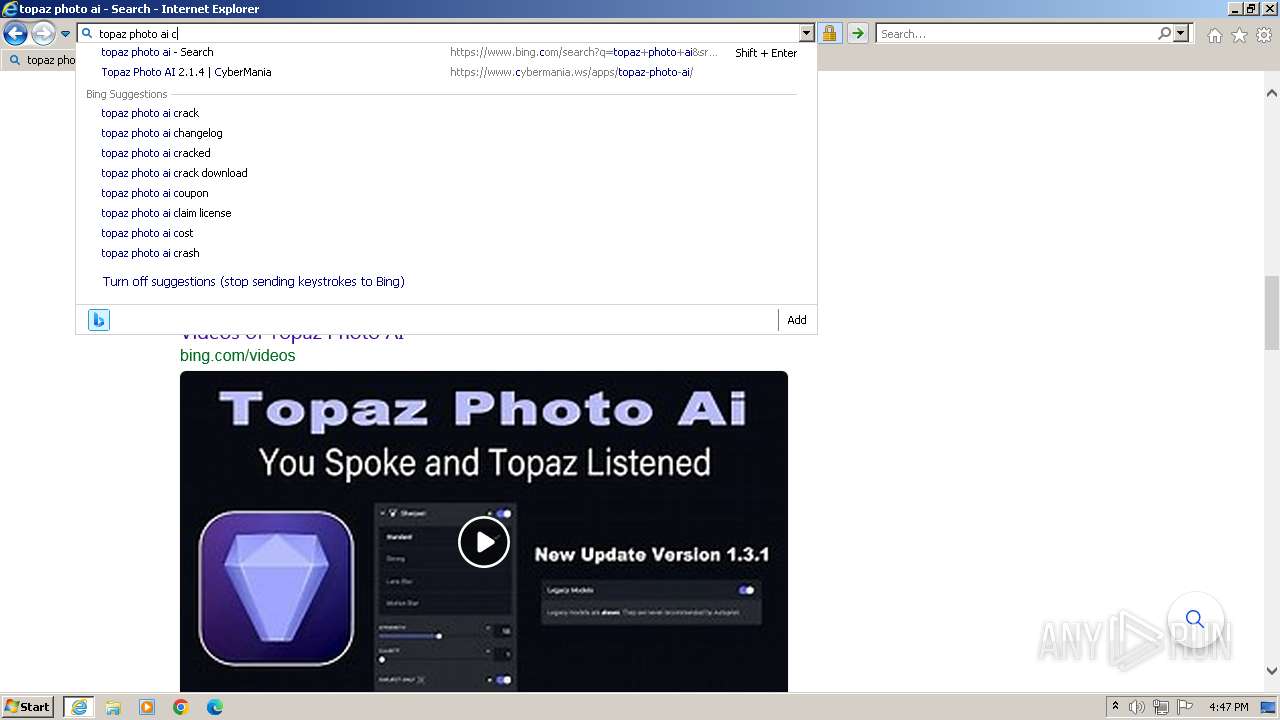
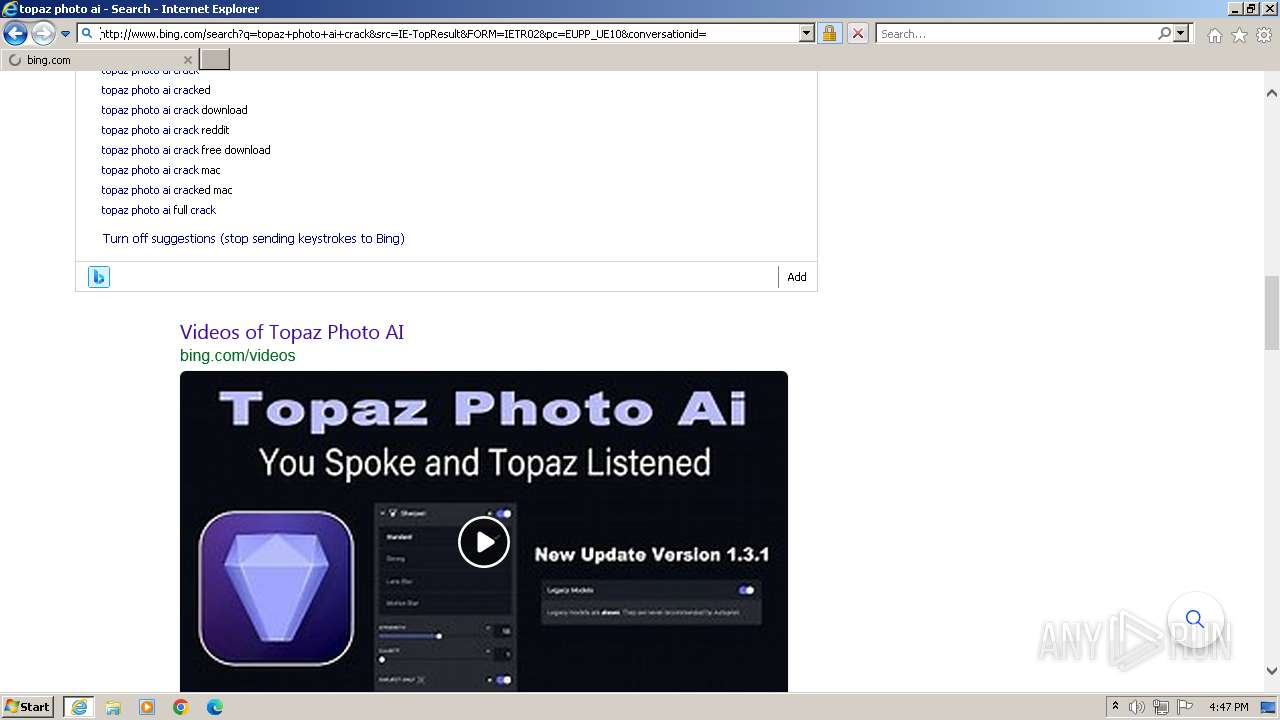
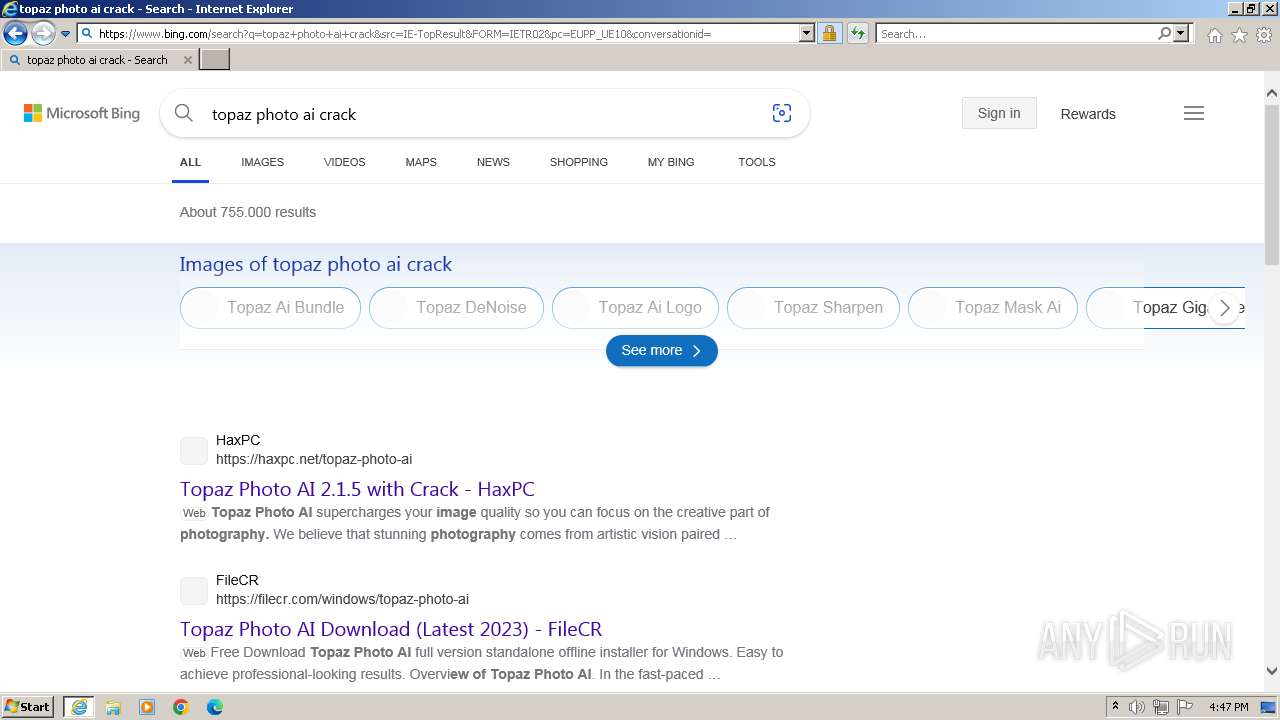
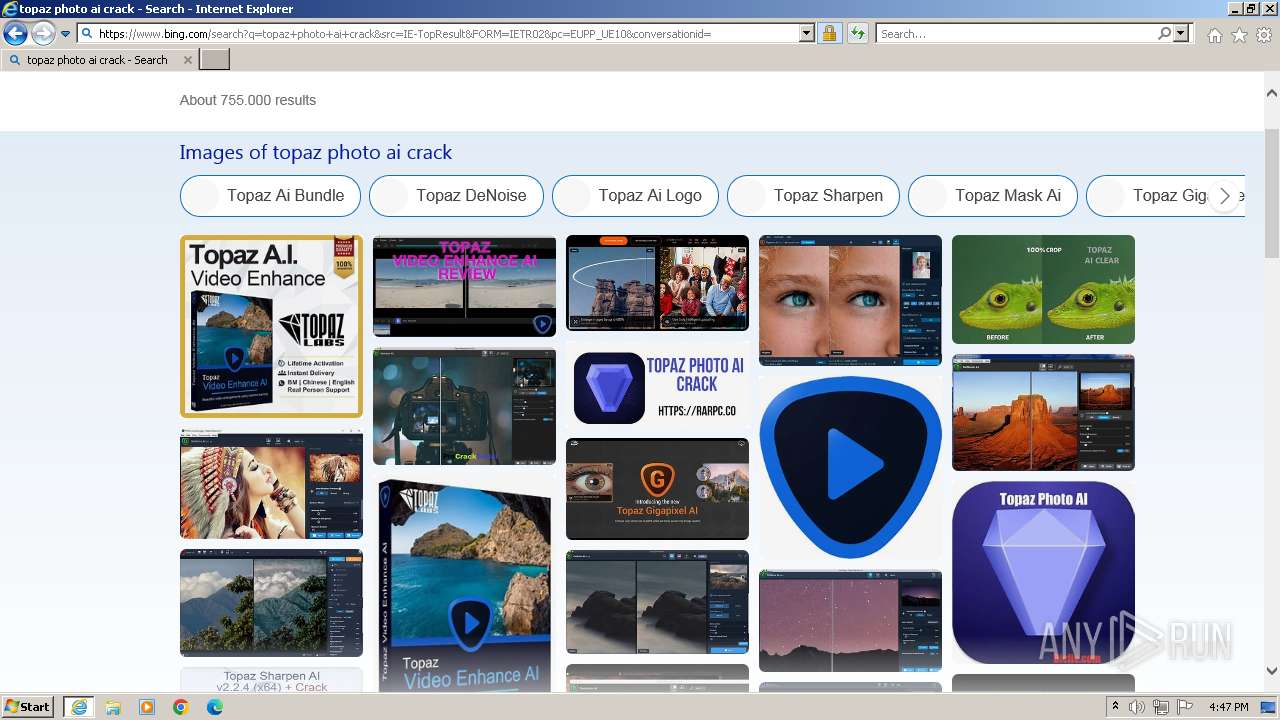
| URL: | https://www.cybermania.ws/apps/topaz-photo-ai/ |
| Full analysis: | https://app.any.run/tasks/cbc37e80-213d-4bb5-bea9-41e78cd72fbc |
| Verdict: | Malicious activity |
| Analysis date: | December 10, 2023, 16:46:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EE80AFBA572AD0F4CE278A6E446041BF |
| SHA1: | F2FC98940857E3AA8563F3936AF5FFD757106A90 |
| SHA256: | 066851342B9F8B4052CEB74251927028E7019AEEA82EF6D057955BCA5D8EA262 |
| SSDEEP: | 3:N8DSLzAXnR/N02InLLn:2OLsH9IHn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Manual execution by a user
- wmpnscfg.exe (PID: 3832)
Checks supported languages
- wmpnscfg.exe (PID: 3832)
Reads the computer name
- wmpnscfg.exe (PID: 3832)
The process uses the downloaded file
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 4080)
Application launched itself
- iexplore.exe (PID: 3048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3028 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3048 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3048 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.cybermania.ws/apps/topaz-photo-ai/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3832 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4080 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\System32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
Total events
25 648
Read events
25 515
Write events
127
Delete events
6
Modification events
| (PID) Process: | (3048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (3048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (3048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (3048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
104
Text files
451
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\e58aaa284dee0052ff68912e4d2a0706[1].css | text | |
MD5:B7E190E2CEA10CEBDEA8EAEED1AE9814 | SHA256:243B1746CACF7C674F05F82C5E27EEDD620CA143AA6EA78C8AC9FECC9C92CAA6 | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:8202A1CD02E7D69597995CABBE881A12 | SHA256:58F381C3A0A0ACE6321DA22E40BD44A597BD98B9C9390AB9258426B5CF75A7A5 | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\a11684c3323dad378dbfd2cd7045e6d7[1].css | text | |
MD5:A14B2980A2368B056ADC0B0CAE1DD804 | SHA256:F1B875FE8868C894F20A8C48777195B88C764AF61BE864A9EA7709F2BFD24192 | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:912DA5501E73CD4914950C3A5116E993 | SHA256:054E67302F4319B1B3768FF1F1E80D8F2C4D45E0D60F5C48BEFE2D89935D244C | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:41FF3625B90B75348D1313E787E41CD1 | SHA256:E79D41C0938399B745F9AA779E5606CC5554907B1D01C75CC77FF04F8DD1C15C | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:066B1847FE6A3E5CDF6ED801564B7576 | SHA256:1C362CAC0B367D34217F1D65B15F78A76E2B64B31481026B948B6D446FA2E6BC | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\cybermaniabtc[1].png | image | |
MD5:BB867F57F28F39B858F48A35E7CB7196 | SHA256:901E8A5124D4DD1E1C03B7D1746304659CF9DAEDC13D454B254FBF0FF0EE5CF5 | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\e4be08a4350526ab67828007d817b3ba[1].css | text | |
MD5:8EFB54808A4EE449D6E4FF225477D425 | SHA256:AF479C59921431B82A82F7CAAC93C70D89E319FDAC45F35408CEAD99A7A7CB32 | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\topaz-photo-ai[1].htm | html | |
MD5:1CEE3621280A360E89A1687FB9C2DD73 | SHA256:8E1B1A95C0C8FE941E72BBDF893188347456AAE00559D214AE18466DDE64D335 | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\jquery.min[1].js | text | |
MD5:826EB77E86B02AB7724FE3D0141FF87C | SHA256:CB6F2D32C49D1C2B25E9FFC9AAAFA3F83075346C01BCD4AE6EB187392A4292CF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
129
DNS requests
51
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3028 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?282a5f2988aaef25 | unknown | compressed | 4.66 Kb | unknown |
3028 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b27ea2cbe4dcc735 | unknown | compressed | 4.66 Kb | unknown |
3028 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
3028 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | binary | 724 b | unknown |
3028 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?2ff75b6e0c2a2ae7 | unknown | compressed | 65.2 Kb | unknown |
3028 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | binary | 1.47 Kb | unknown |
3028 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?72d19b2671a063fc | unknown | compressed | 65.2 Kb | unknown |
3028 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | binary | 724 b | unknown |
3028 | iexplore.exe | GET | — | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGupzMnM%2BqGaCjIQPyd58u0%3D | unknown | — | — | unknown |
3028 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3028 | iexplore.exe | 104.21.74.121:443 | www.cybermania.ws | CLOUDFLARENET | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3028 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3028 | iexplore.exe | 142.250.185.131:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
3028 | iexplore.exe | 142.250.185.238:443 | fundingchoicesmessages.google.com | GOOGLE | US | whitelisted |
3028 | iexplore.exe | 142.250.186.42:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
3028 | iexplore.exe | 142.250.185.168:443 | www.googletagmanager.com | GOOGLE | US | unknown |
3028 | iexplore.exe | 216.58.206.34:443 | pagead2.googlesyndication.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
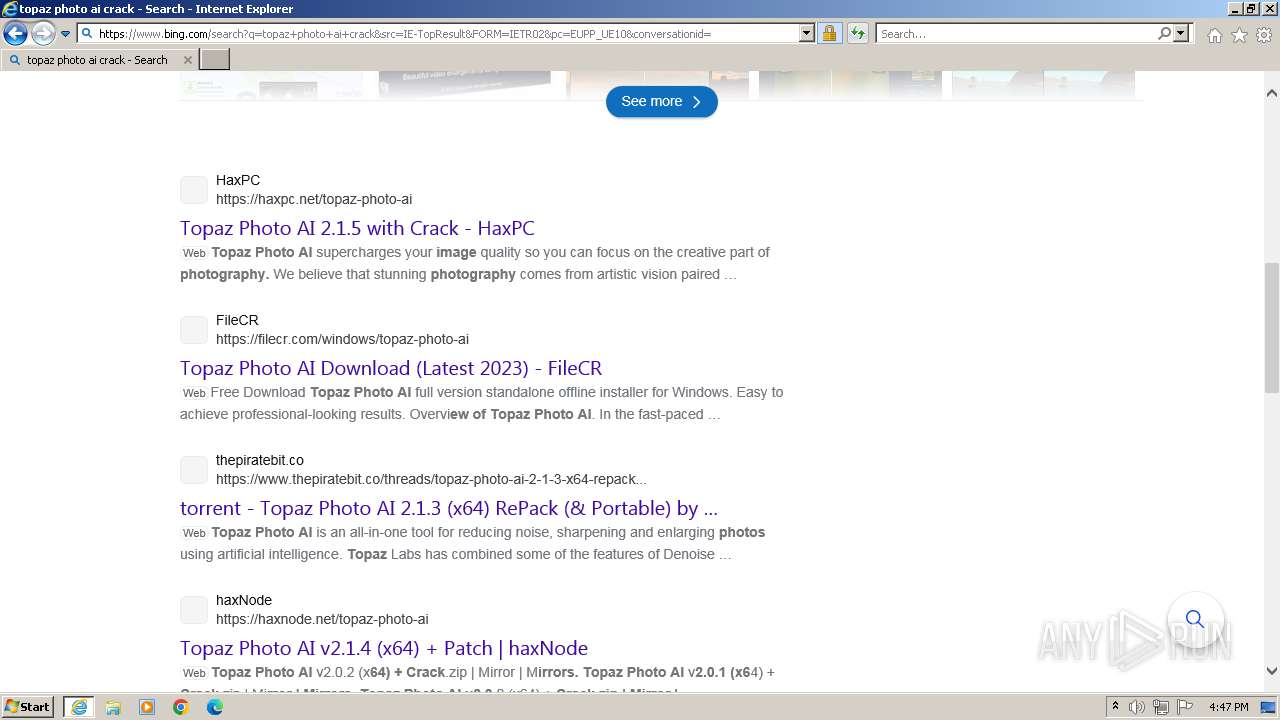
www.cybermania.ws |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fundingchoicesmessages.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
www.paypalobjects.com |
| whitelisted |
storage.ko-fi.com |
| unknown |
rf.revolvermaps.com |
| unknown |