| File name: | 066706b9ea10c6d19a27dab9abc82f204299260d7e1fbfae768e0e4252684bc9 |
| Full analysis: | https://app.any.run/tasks/e99a52fa-4b0e-4953-8950-e3ac9641d911 |
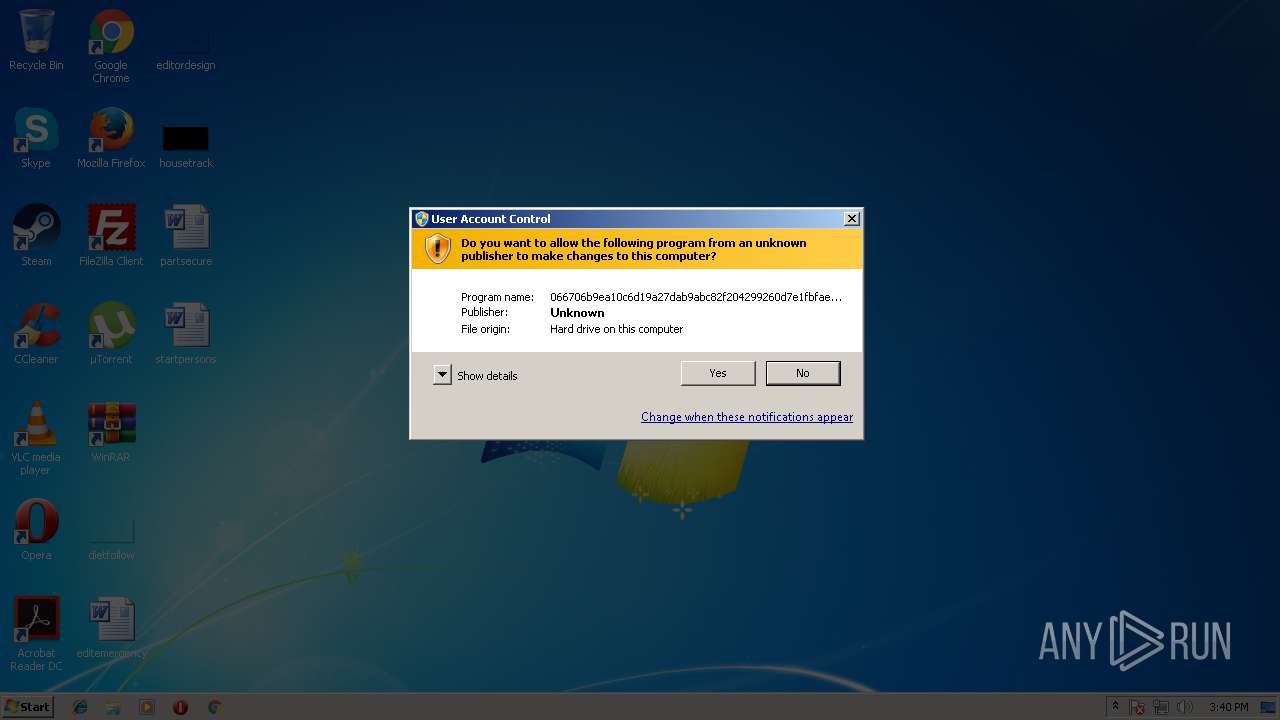
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2018, 14:40:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | 08EC21075DF33B9275233BE239E851A3 |
| SHA1: | 528036C8380FA636866FB03F34025A51A28904A8 |
| SHA256: | 066706B9EA10C6D19A27DAB9ABC82F204299260D7E1FBFAE768E0E4252684BC9 |
| SSDEEP: | 6144:iME1nmg1tDbJ5621YNA+A16raSz4hRQRFi:zgnJeraSz4Sni |
MALICIOUS
Uses SVCHOST.EXE for hidden code execution
- HRB.exe (PID: 2372)
Loads dropped or rewritten executable
- HRB.exe (PID: 3712)
- HRB.exe (PID: 2372)
- HRB.exe (PID: 1328)
Application was dropped or rewritten from another process
- HRB.exe (PID: 1328)
- HRB.exe (PID: 2372)
- HRB.exe (PID: 3712)
SUSPICIOUS
Executable content was dropped or overwritten
- 066706b9ea10c6d19a27dab9abc82f204299260d7e1fbfae768e0e4252684bc9.exe (PID: 2648)
- HRB.exe (PID: 3712)
Starts itself from another location
- HRB.exe (PID: 3712)
Creates files in the program directory
- HRB.exe (PID: 1328)
- HRB.exe (PID: 3712)
Connects to unusual port
- svchost.exe (PID: 2360)
INFO
Dropped object may contain URL's
- HRB.exe (PID: 3712)
- 066706b9ea10c6d19a27dab9abc82f204299260d7e1fbfae768e0e4252684bc9.exe (PID: 2648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | WinRAR Self Extracting archive (94.8) |
|---|---|---|
| .scr | | | Windows screen saver (2.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.2) |
| .exe | | | Win32 Executable (generic) (0.8) |
| .exe | | | Generic Win/DOS Executable (0.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2005:10:07 11:05:22+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 77824 |
| InitializedDataSize: | 28672 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Oct-2005 09:05:22 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000200 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 07-Oct-2005 09:05:22 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00013000 | 0x00012600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45699 |
.data | 0x00014000 | 0x00007000 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.73447 |
.idata | 0x0001B000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.02033 |
.rsrc | 0x0001C000 | 0x00003200 | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17656 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10885 | 531 | UNKNOWN | Chinese - PRC | RT_MANIFEST |
2 | 3.88998 | 1384 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 4.12176 | 744 | UNKNOWN | Chinese - PRC | RT_ICON |
4 | 4.68705 | 2216 | UNKNOWN | Chinese - PRC | RT_ICON |
7 | 5.31352 | 226 | UNKNOWN | Chinese - PRC | RT_STRING |
8 | 5.70413 | 360 | UNKNOWN | Chinese - PRC | RT_STRING |
9 | 5.51373 | 216 | UNKNOWN | Chinese - PRC | RT_STRING |
10 | 4.80037 | 420 | UNKNOWN | Chinese - PRC | RT_STRING |
100 | 2.6902 | 62 | UNKNOWN | Chinese - PRC | RT_GROUP_ICON |
101 | 4.19099 | 2998 | UNKNOWN | Chinese - PRC | RT_BITMAP |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
COMDLG32.DLL |
GDI32.DLL |
KERNEL32.DLL |
OLE32.DLL |
SHELL32.DLL |
USER32.DLL |
Total processes
45
Monitored processes
7
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1328 | "C:\ProgramData\SxS\HRB.exe" 100 3712 | C:\ProgramData\SxS\HRB.exe | HRB.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: NVIDIA Smart Maximise Helper Host Exit code: 1223 Version: 6.14.10.100.01 Modules
| |||||||||||||||
| 2360 | C:\Windows\system32\svchost.exe 201 0 | C:\Windows\system32\svchost.exe | HRB.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2372 | "C:\ProgramData\SxS\HRB.exe" 200 0 | C:\ProgramData\SxS\HRB.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: NVIDIA Smart Maximise Helper Host Exit code: 1223 Version: 6.14.10.100.01 Modules
| |||||||||||||||
| 2576 | "C:\Users\admin\AppData\Local\Temp\066706b9ea10c6d19a27dab9abc82f204299260d7e1fbfae768e0e4252684bc9.exe" | C:\Users\admin\AppData\Local\Temp\066706b9ea10c6d19a27dab9abc82f204299260d7e1fbfae768e0e4252684bc9.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2648 | "C:\Users\admin\AppData\Local\Temp\066706b9ea10c6d19a27dab9abc82f204299260d7e1fbfae768e0e4252684bc9.exe" | C:\Users\admin\AppData\Local\Temp\066706b9ea10c6d19a27dab9abc82f204299260d7e1fbfae768e0e4252684bc9.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2696 | C:\Windows\system32\msiexec.exe 209 2360 | C:\Windows\system32\msiexec.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3712 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\HRB.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\HRB.exe | 066706b9ea10c6d19a27dab9abc82f204299260d7e1fbfae768e0e4252684bc9.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: NVIDIA Smart Maximise Helper Host Exit code: 0 Version: 6.14.10.100.01 Modules
| |||||||||||||||
Total events
402
Read events
378
Write events
24
Delete events
0
Modification events
| (PID) Process: | (2648) 066706b9ea10c6d19a27dab9abc82f204299260d7e1fbfae768e0e4252684bc9.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2648) 066706b9ea10c6d19a27dab9abc82f204299260d7e1fbfae768e0e4252684bc9.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2360) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\FAST |
| Operation: | write | Name: | CLSID |
Value: 44003400450035003400320030003900390041004300360037003500340030000000 | |||
| (PID) Process: | (2360) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2360) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2360) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2360) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2360) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2360) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2360) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
4
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1328 | HRB.exe | C:\ProgramData\SxS\bug.log | binary | |
MD5:— | SHA256:— | |||
| 2360 | svchost.exe | C:\ProgramData\SxS\bug.log | binary | |
MD5:— | SHA256:— | |||
| 2648 | 066706b9ea10c6d19a27dab9abc82f204299260d7e1fbfae768e0e4252684bc9.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\HRB.exe | executable | |
MD5:09B8B54F78A10C435CD319070AA13C28 | SHA256:523D28DF917F9D265CD2C0D38DF26277BC56A535145100ED82E6F5FDEAAE7256 | |||
| 2648 | 066706b9ea10c6d19a27dab9abc82f204299260d7e1fbfae768e0e4252684bc9.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\HRB.bmp | binary | |
MD5:B10A738D22F9D5F4D6462C9286EB3F75 | SHA256:632A2B37B5B6AA35FDB867F5006075E909AC82E7629D984A60F1C9077D6B692A | |||
| 2648 | 066706b9ea10c6d19a27dab9abc82f204299260d7e1fbfae768e0e4252684bc9.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\NvSmartMax.dll | executable | |
MD5:FA51E652FB3A34106F0E85D715EEE39D | SHA256:BB8241F762D31E0F5BFB381F9E9209022075BDB52C1362D478FD6A233D39AF6A | |||
| 3712 | HRB.exe | C:\ProgramData\SxS\NvSmartMax.dll | executable | |
MD5:FA51E652FB3A34106F0E85D715EEE39D | SHA256:BB8241F762D31E0F5BFB381F9E9209022075BDB52C1362D478FD6A233D39AF6A | |||
| 3712 | HRB.exe | C:\ProgramData\SxS\HRB.exe | executable | |
MD5:09B8B54F78A10C435CD319070AA13C28 | SHA256:523D28DF917F9D265CD2C0D38DF26277BC56A535145100ED82E6F5FDEAAE7256 | |||
| 3712 | HRB.exe | C:\ProgramData\SxS\HRB.bmp | binary | |
MD5:B10A738D22F9D5F4D6462C9286EB3F75 | SHA256:632A2B37B5B6AA35FDB867F5006075E909AC82E7629D984A60F1C9077D6B692A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
5
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2360 | svchost.exe | 174.128.255.253:8018 | ras-ru.oicp.net | Sharktech | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ras-ru.oicp.net |
| unknown |
dns.msftncsi.com |
| shared |
Threats
Process | Message |
|---|---|
svchost.exe | Protocol:[ TCP], Host: [ras-ru.oicp.net:8018], Proxy: [0::0::]
|
HRB.exe | file: XInstall.cpp, line: 182, error: [1053]The service did not respond to the start or control request in a timely fashion.
|
svchost.exe | Protocol:[HTTP], Host: [ras-ru.oicp.net:8018], Proxy: [0::0::]
|
svchost.exe | file: XSoTcpHttp.cpp, line: 623, error: [12029]*
|
svchost.exe | Protocol:[ UDP], Host: [ras-ru.oicp.net:8018], Proxy: [0::0::]
|