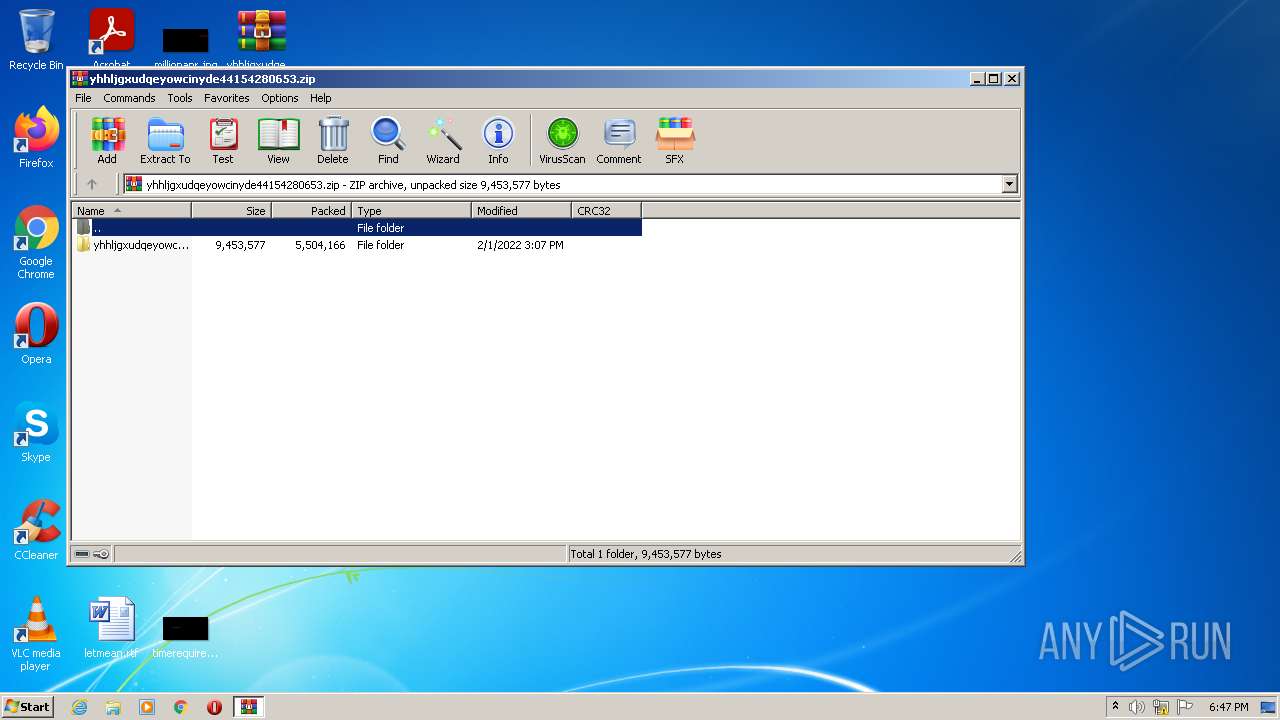
| File name: | yhhljgxudqeyowcinyde44154280653.zip |
| Full analysis: | https://app.any.run/tasks/953068dd-bf0c-4026-954c-bff4082bcc6a |
| Verdict: | Malicious activity |
| Analysis date: | February 01, 2022, 18:46:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | AEDBA99F0502F4DBA07145AD6B161FEB |
| SHA1: | 57B09BF79CC216DE98EF787B5112AD1351B4F316 |
| SHA256: | 06521C5730AF4EFC5E8C6D9517E6DA154BC653131DC22AF44271D740B45AE7EB |
| SSDEEP: | 98304:GsQF7Qqn5v+W5Hbx+OD35XPRRLaBtmbdqNjXuWro+76A3Ykkc/g9fKd/c9oFZgyz:vG7Zn5/gsLVaBtmkN6Ao+Vokhg4dUCjR |
MALICIOUS
Application was dropped or rewritten from another process
- smss.exe (PID: 2740)
- smss.exe (PID: 4048)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3064)
Uses SVCHOST.EXE for hidden code execution
- smss.exe (PID: 4048)
- smss.exe (PID: 2740)
SUSPICIOUS
Drops a file with a compile date too recent
- WinRAR.exe (PID: 872)
Checks supported languages
- smss.exe (PID: 2740)
- WinRAR.exe (PID: 872)
- smss.exe (PID: 4048)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 872)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 872)
Reads the computer name
- WinRAR.exe (PID: 872)
- smss.exe (PID: 2740)
- smss.exe (PID: 4048)
Reads mouse settings
- smss.exe (PID: 2740)
- smss.exe (PID: 4048)
INFO
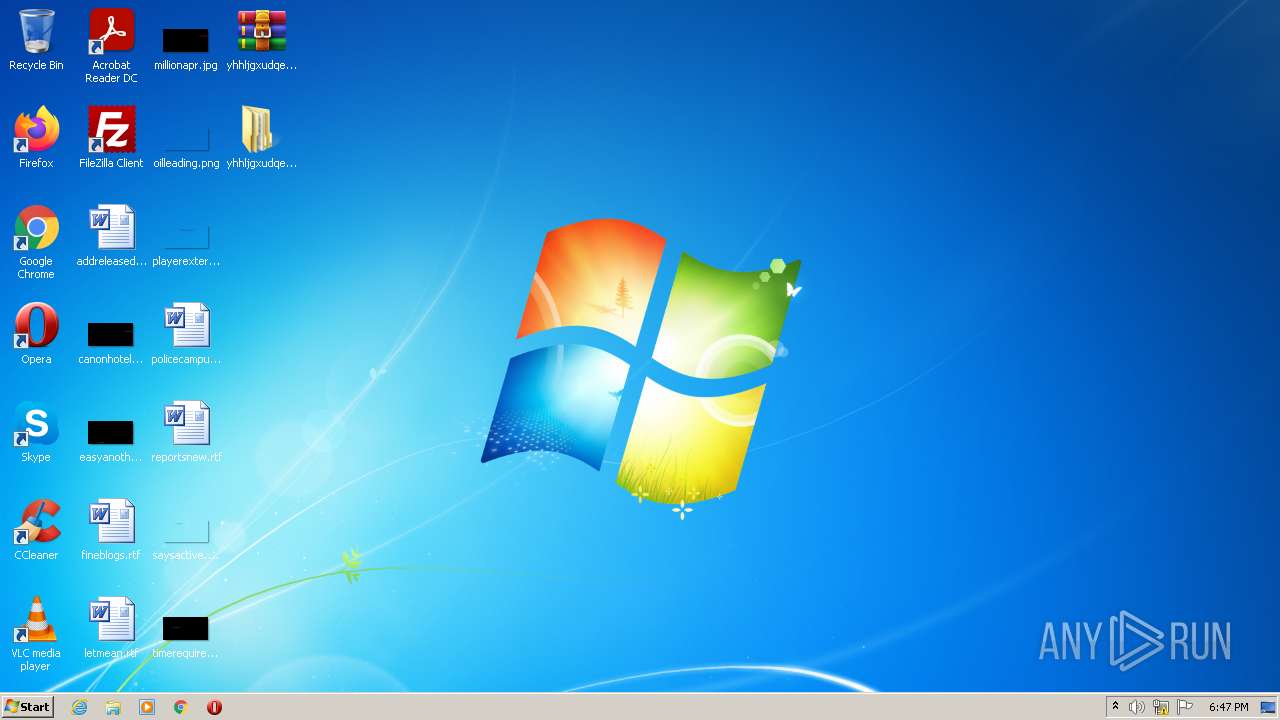
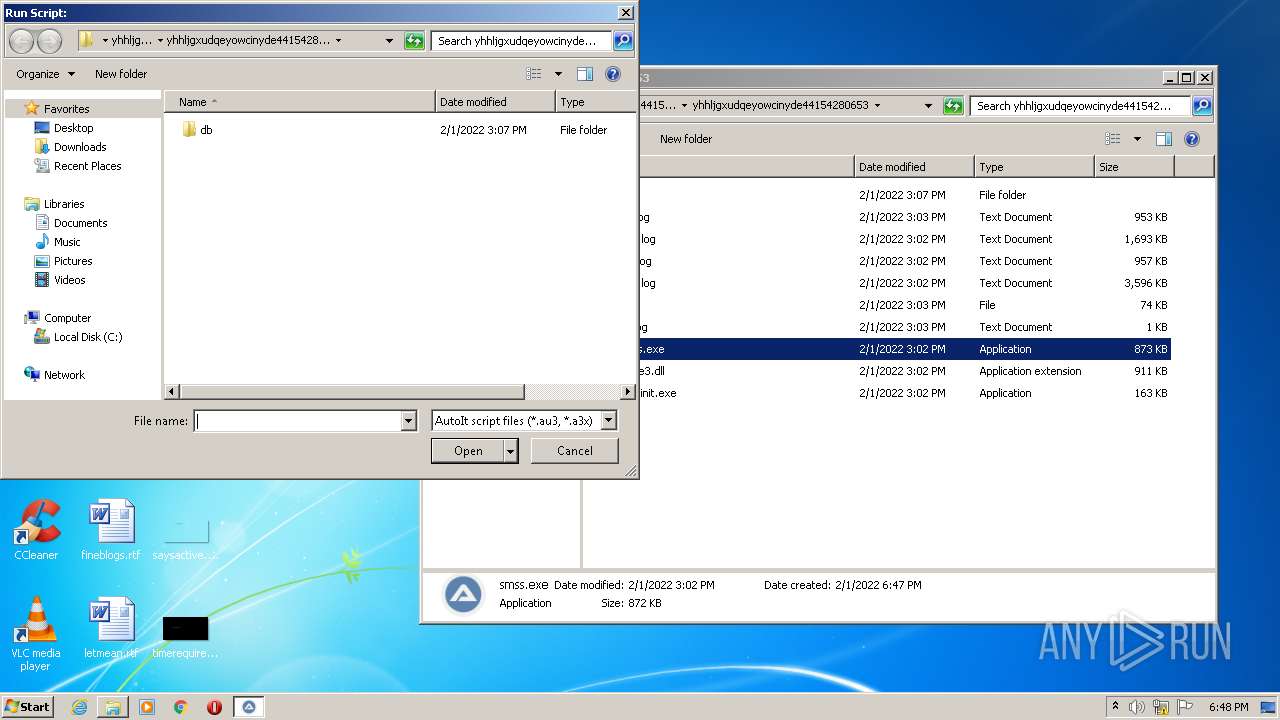
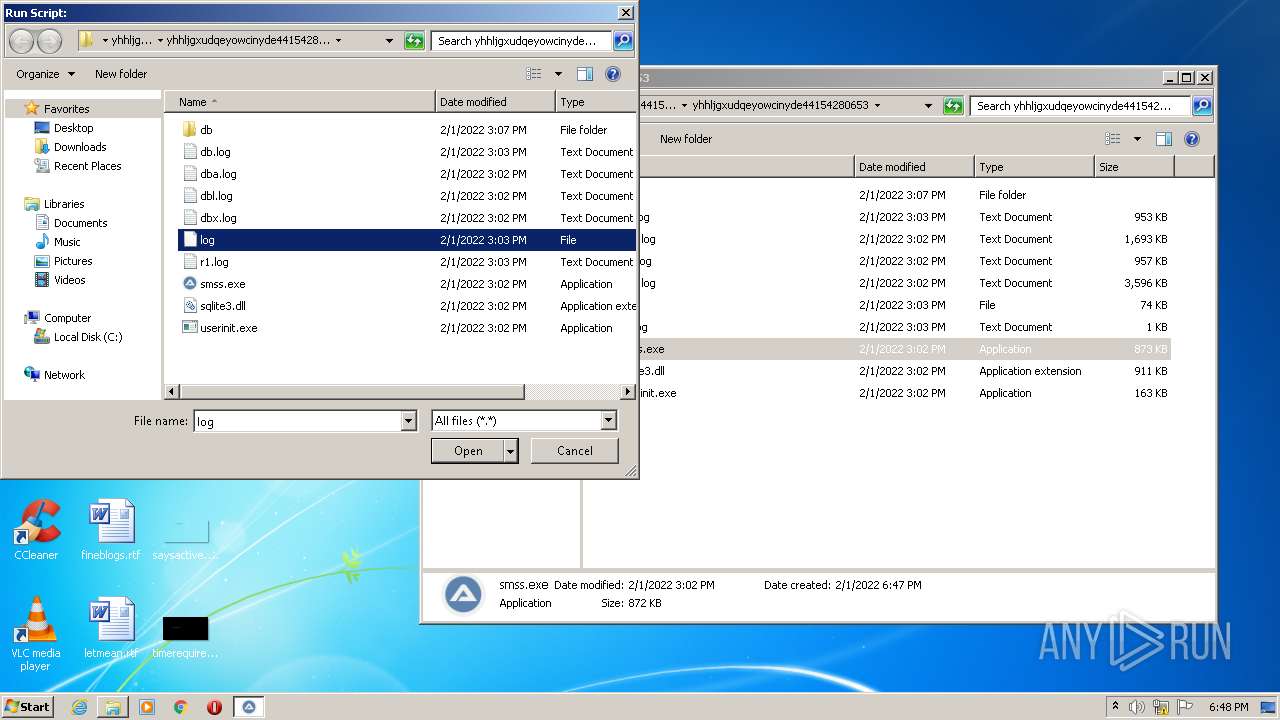
Manual execution by user
- smss.exe (PID: 2740)
- smss.exe (PID: 4048)
Checks supported languages
- svchost.exe (PID: 2636)
- svchost.exe (PID: 3096)
Reads the computer name
- svchost.exe (PID: 2636)
- svchost.exe (PID: 3096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
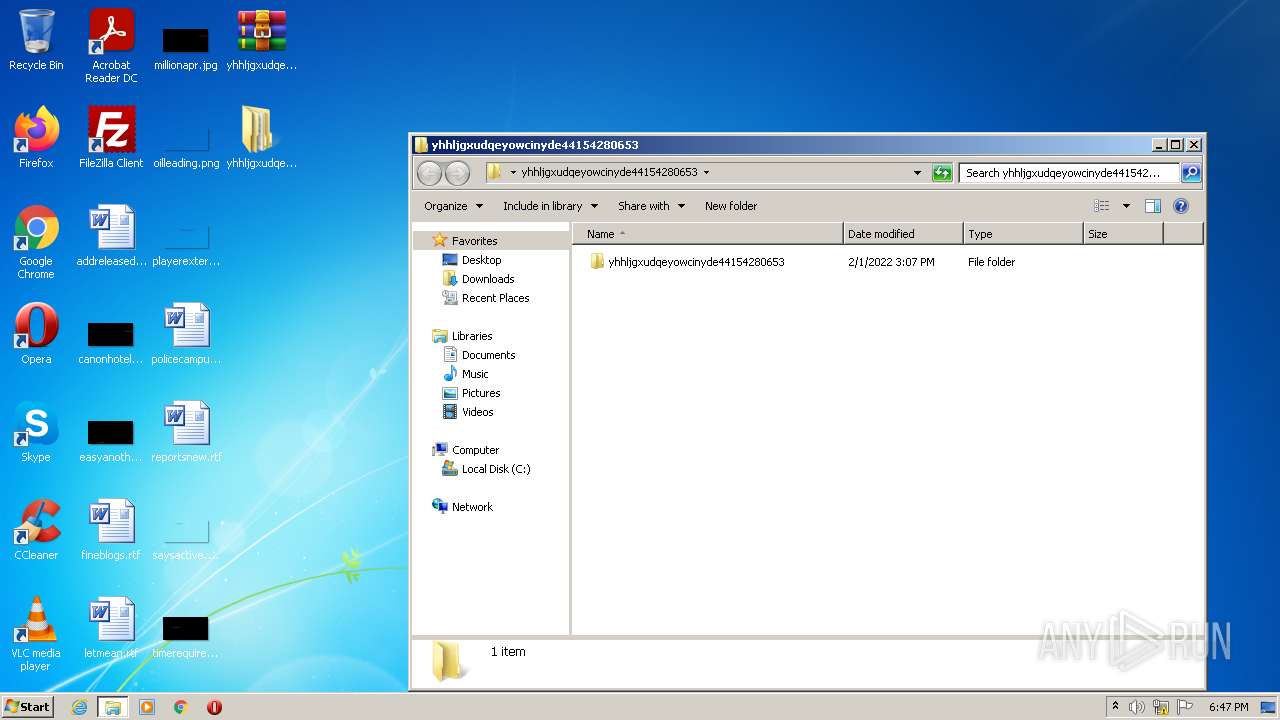
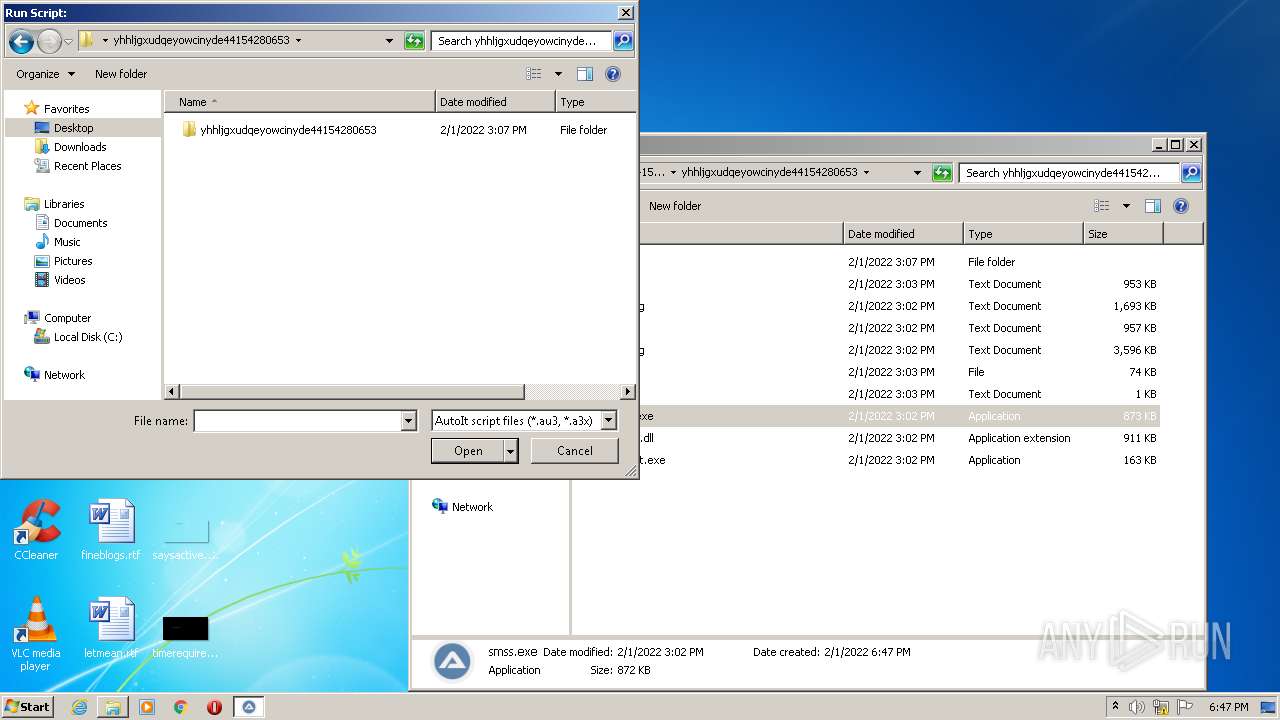
| ZipFileName: | yhhljgxudqeyowcinyde44154280653/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | - |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2022:02:01 12:07:07 |
| ZipCompression: | None |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
41
Monitored processes
6
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
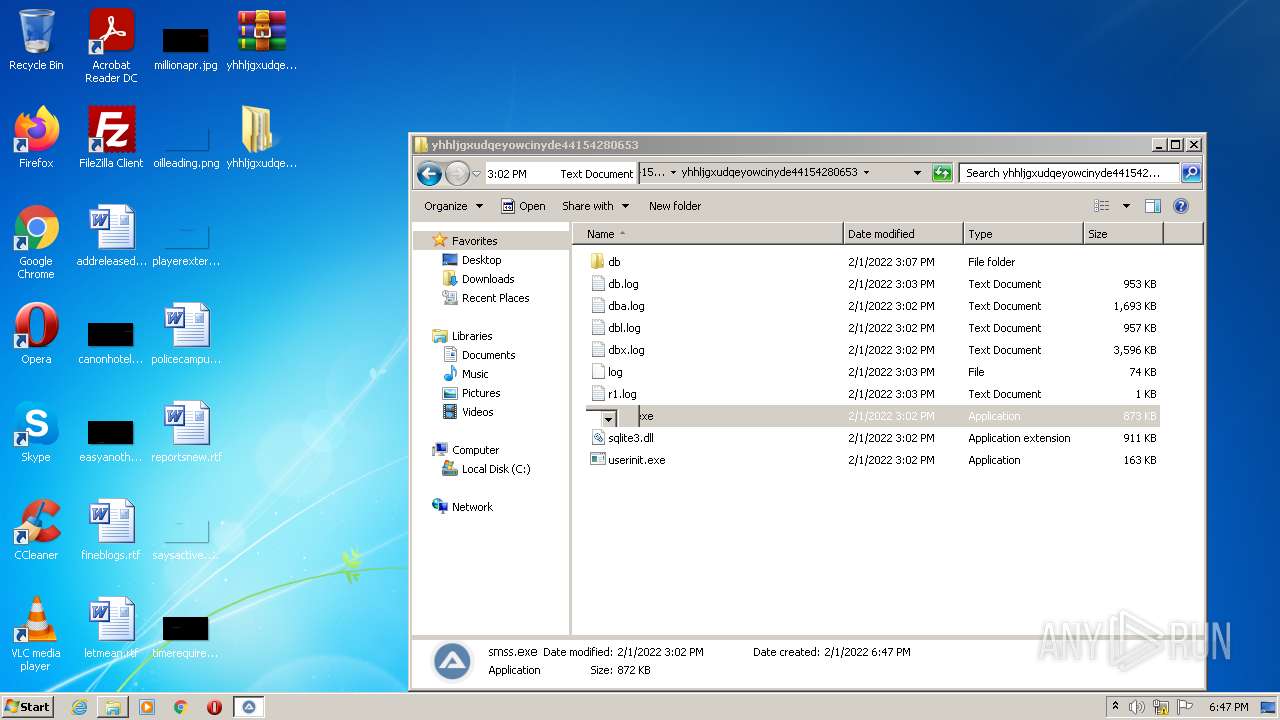
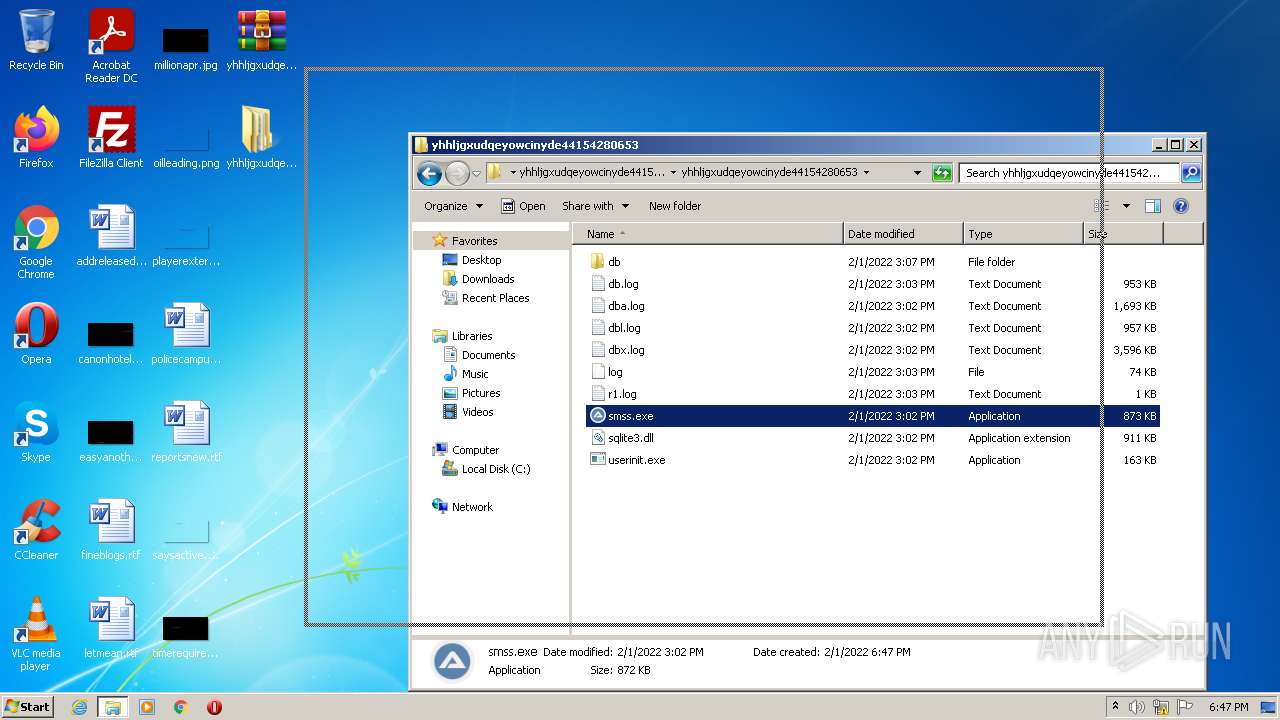
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
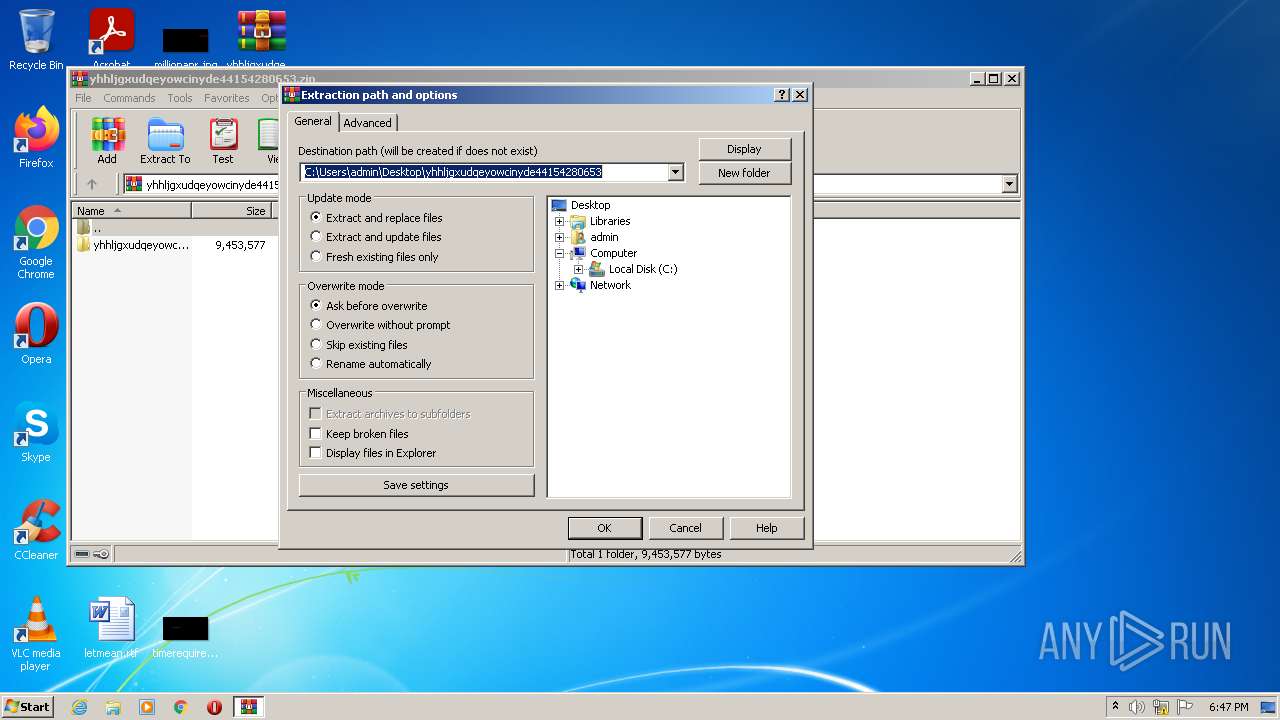
| 872 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\yhhljgxudqeyowcinyde44154280653.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2636 | "C:\Windows\System32\svchost.exe" | C:\Windows\System32\svchost.exe | smss.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
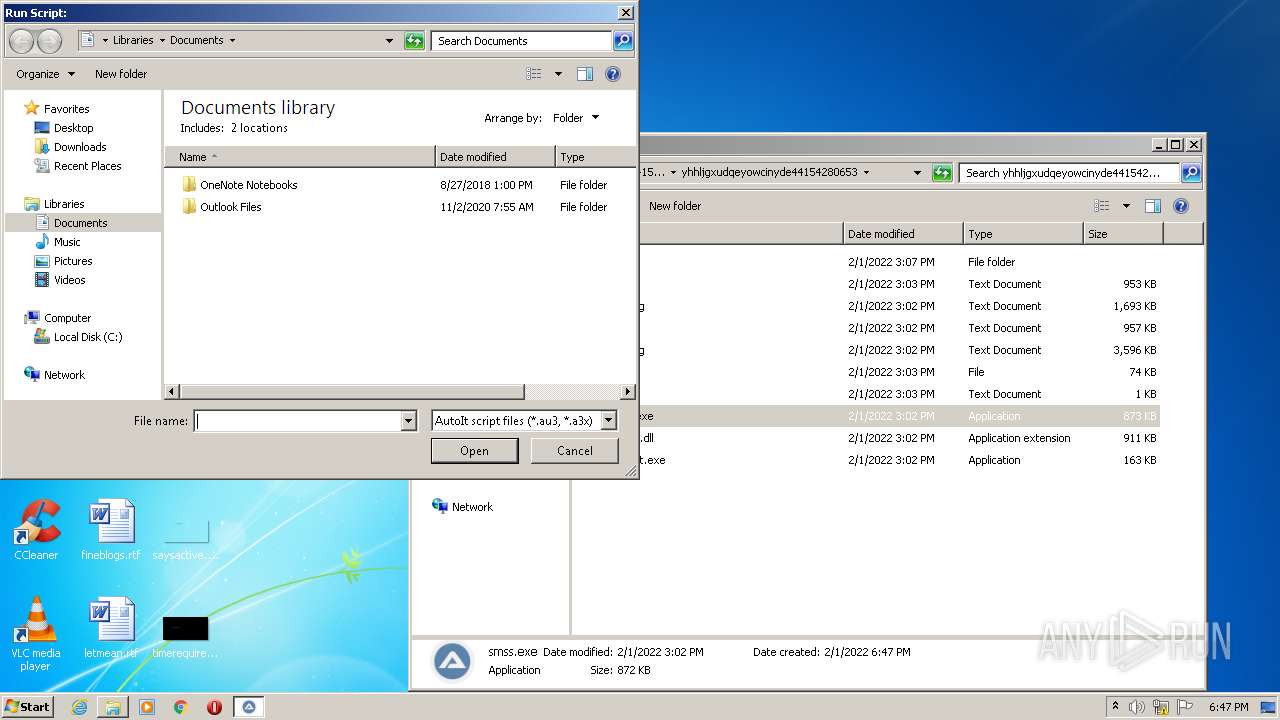
| 2740 | "C:\Users\admin\Desktop\yhhljgxudqeyowcinyde44154280653\yhhljgxudqeyowcinyde44154280653\smss.exe" | C:\Users\admin\Desktop\yhhljgxudqeyowcinyde44154280653\yhhljgxudqeyowcinyde44154280653\smss.exe | — | Explorer.EXE | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 14, 5 Modules
| |||||||||||||||
| 3064 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 3096 | "C:\Windows\System32\svchost.exe" | C:\Windows\System32\svchost.exe | smss.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4048 | "C:\Users\admin\Desktop\yhhljgxudqeyowcinyde44154280653\yhhljgxudqeyowcinyde44154280653\smss.exe" | C:\Users\admin\Desktop\yhhljgxudqeyowcinyde44154280653\yhhljgxudqeyowcinyde44154280653\smss.exe | — | Explorer.EXE | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 14, 5 Modules
| |||||||||||||||
Total events
8 958
Read events
8 781
Write events
173
Delete events
4
Modification events
| (PID) Process: | (872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (872) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\yhhljgxudqeyowcinyde44154280653.zip | |||
| (PID) Process: | (872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
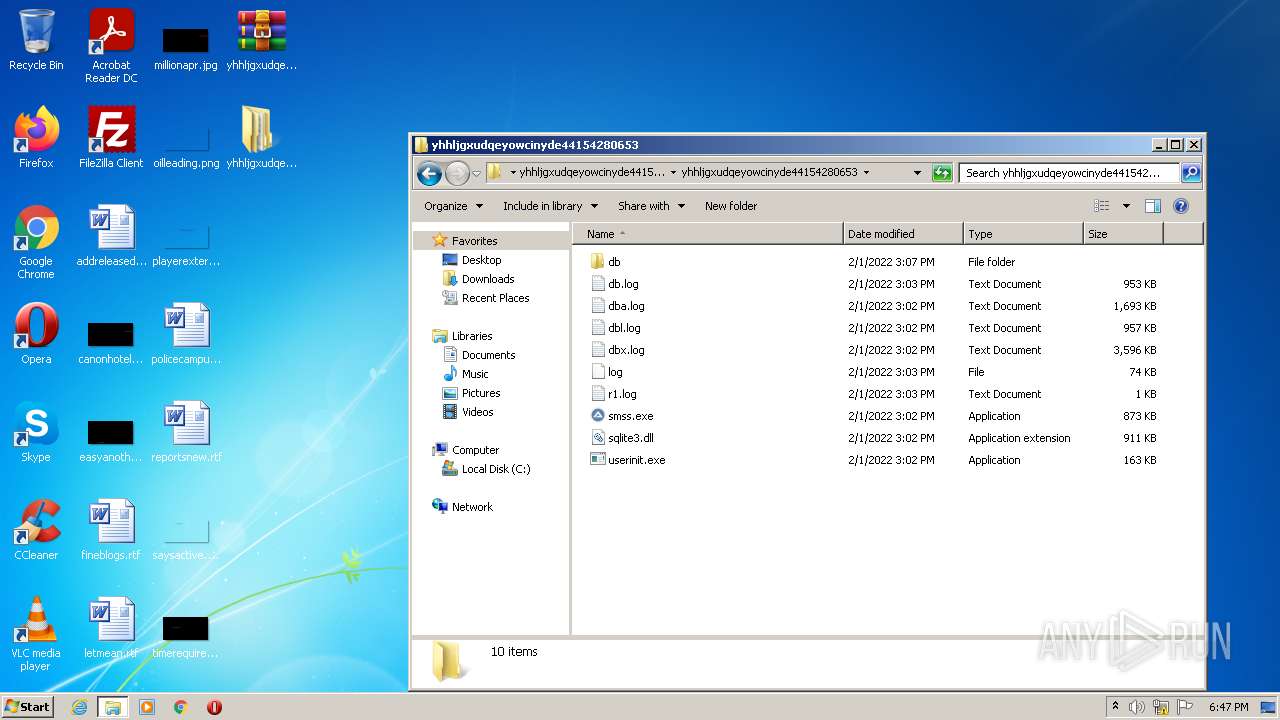
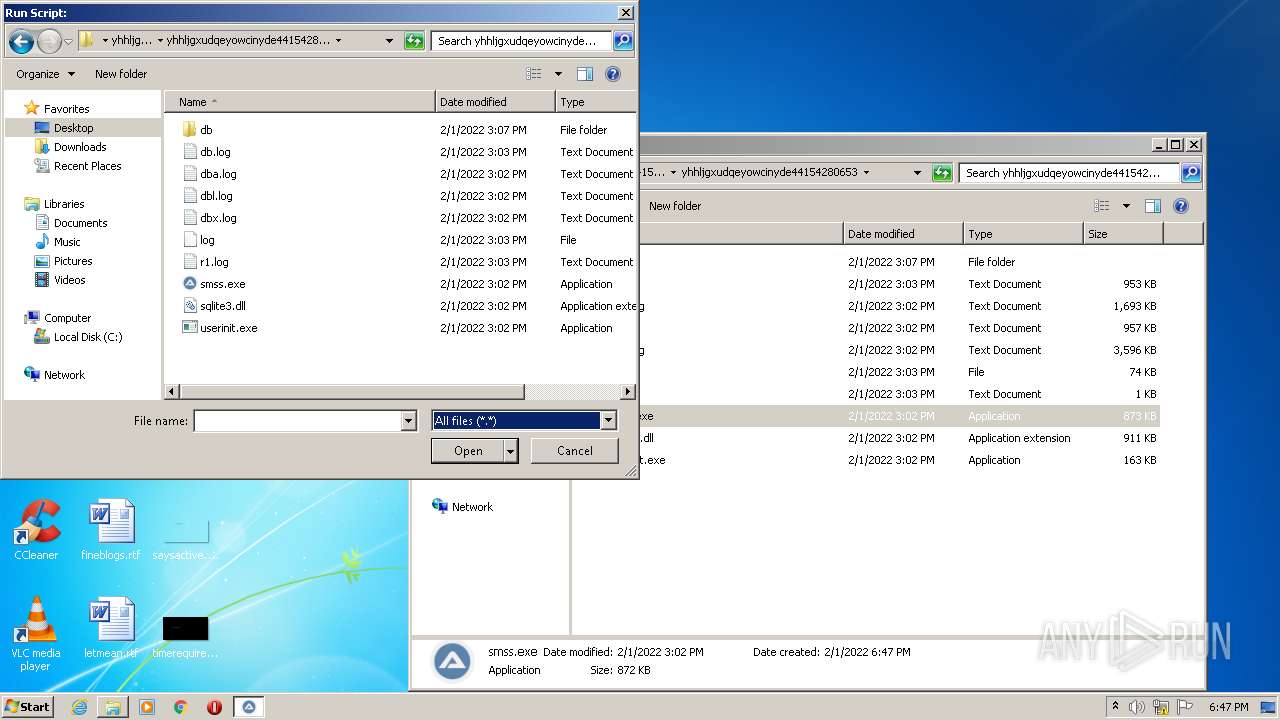
Executable files
5
Suspicious files
2
Text files
3
Unknown types
0
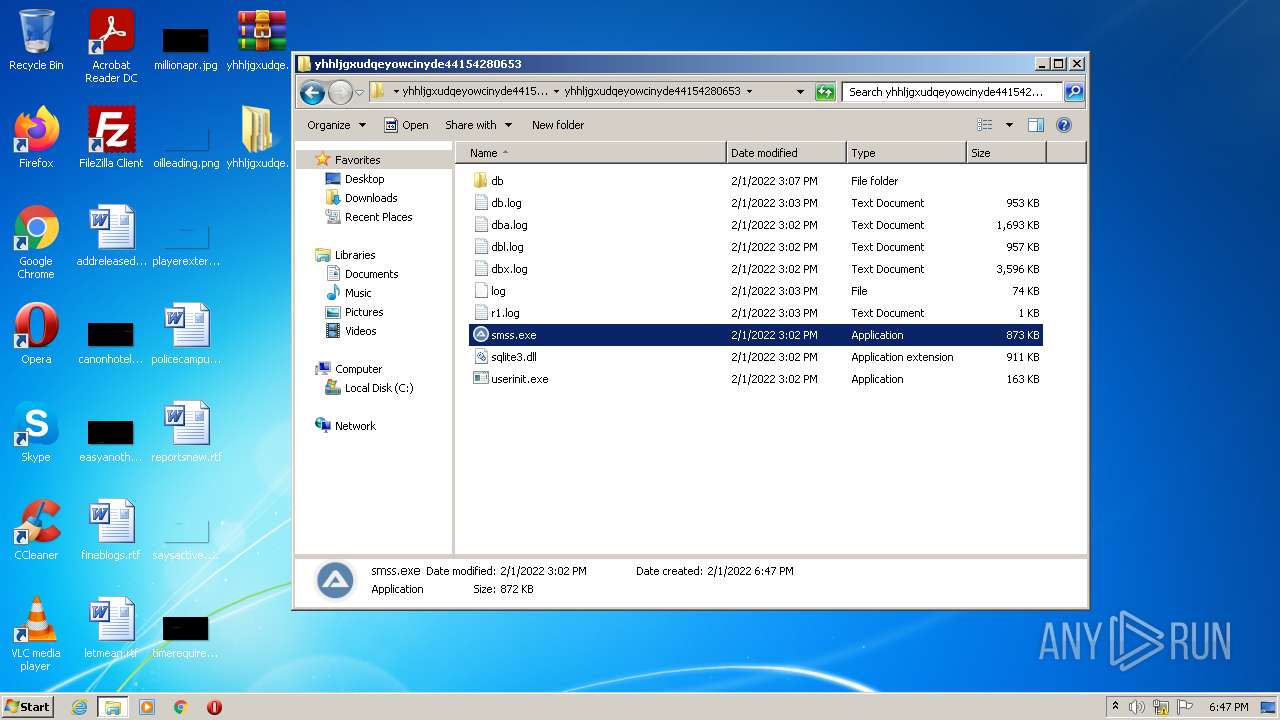
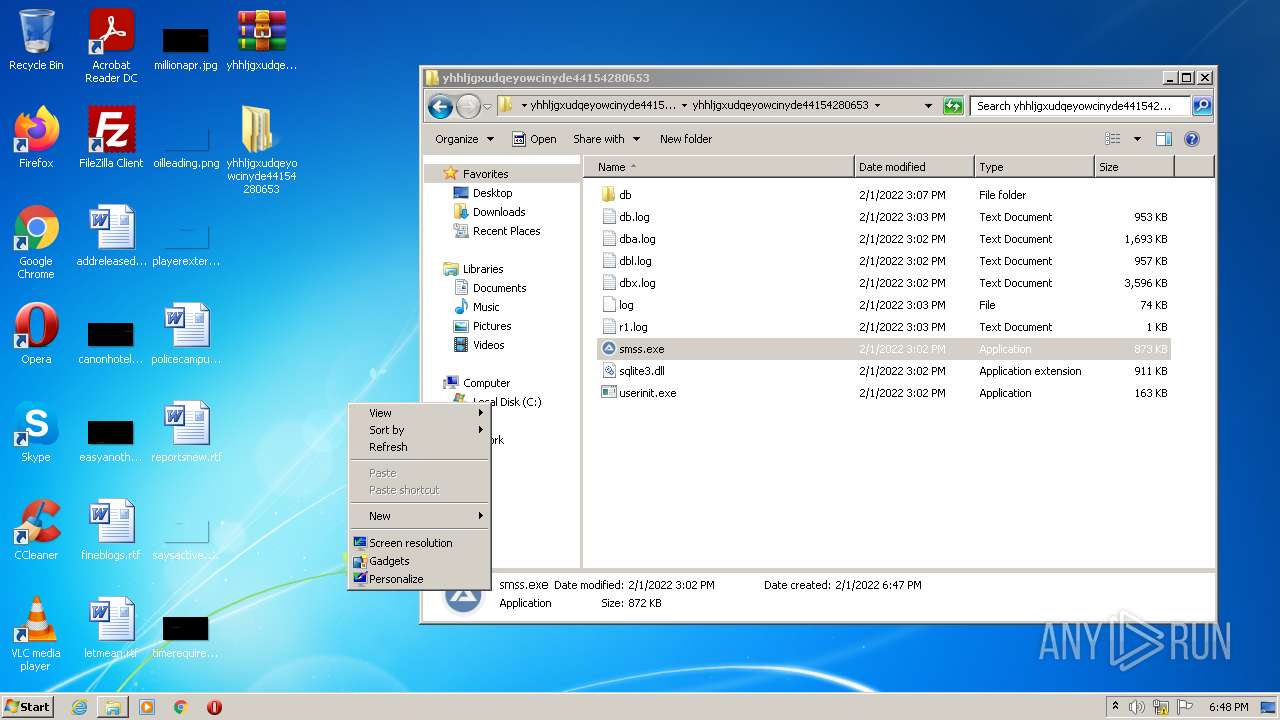
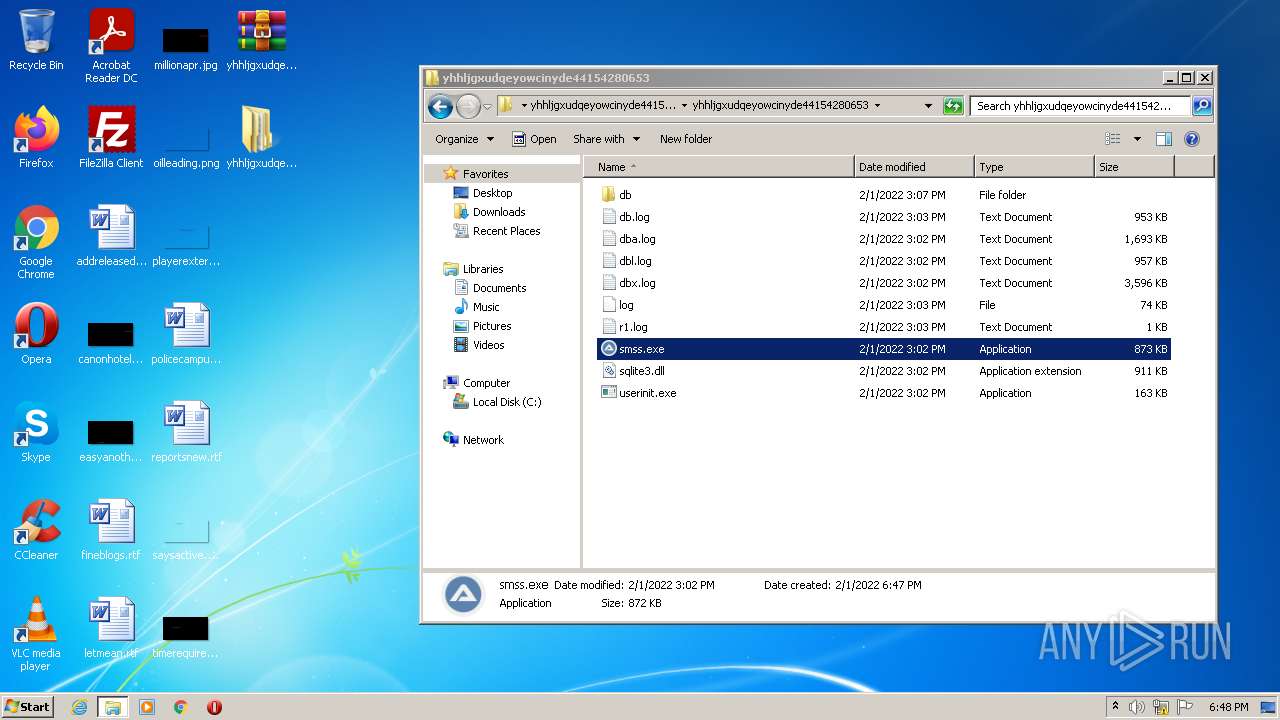
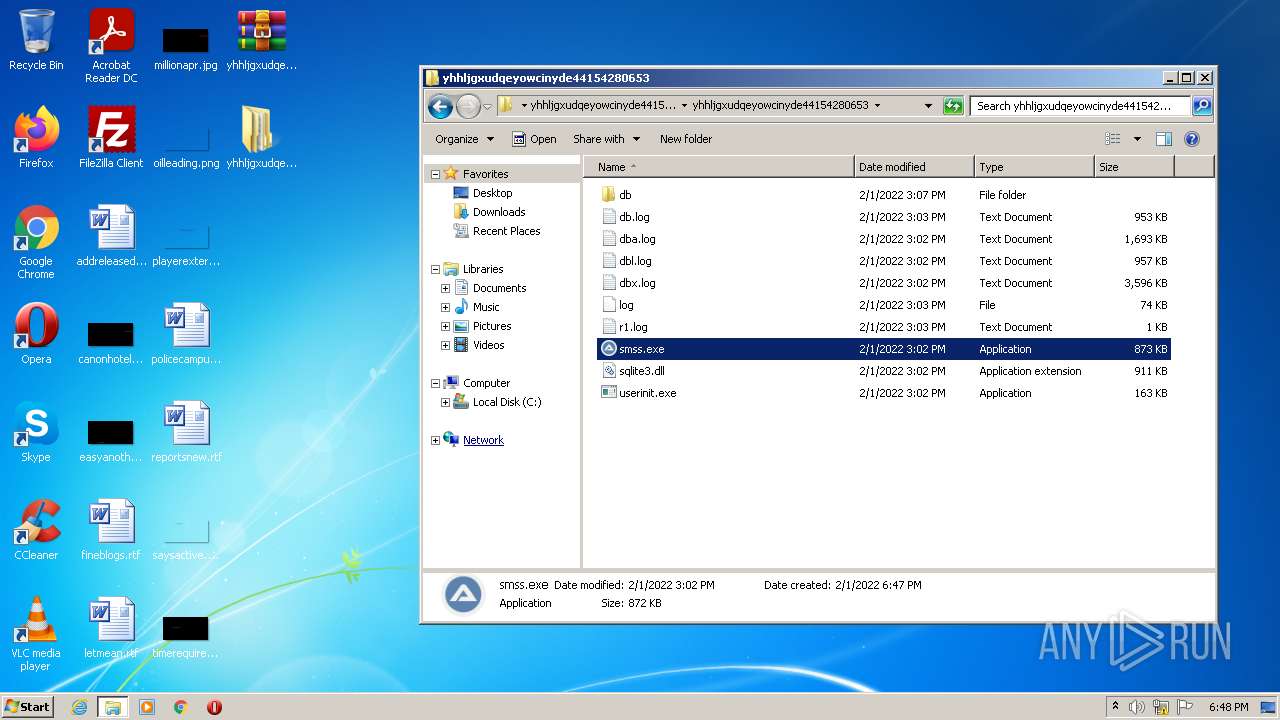
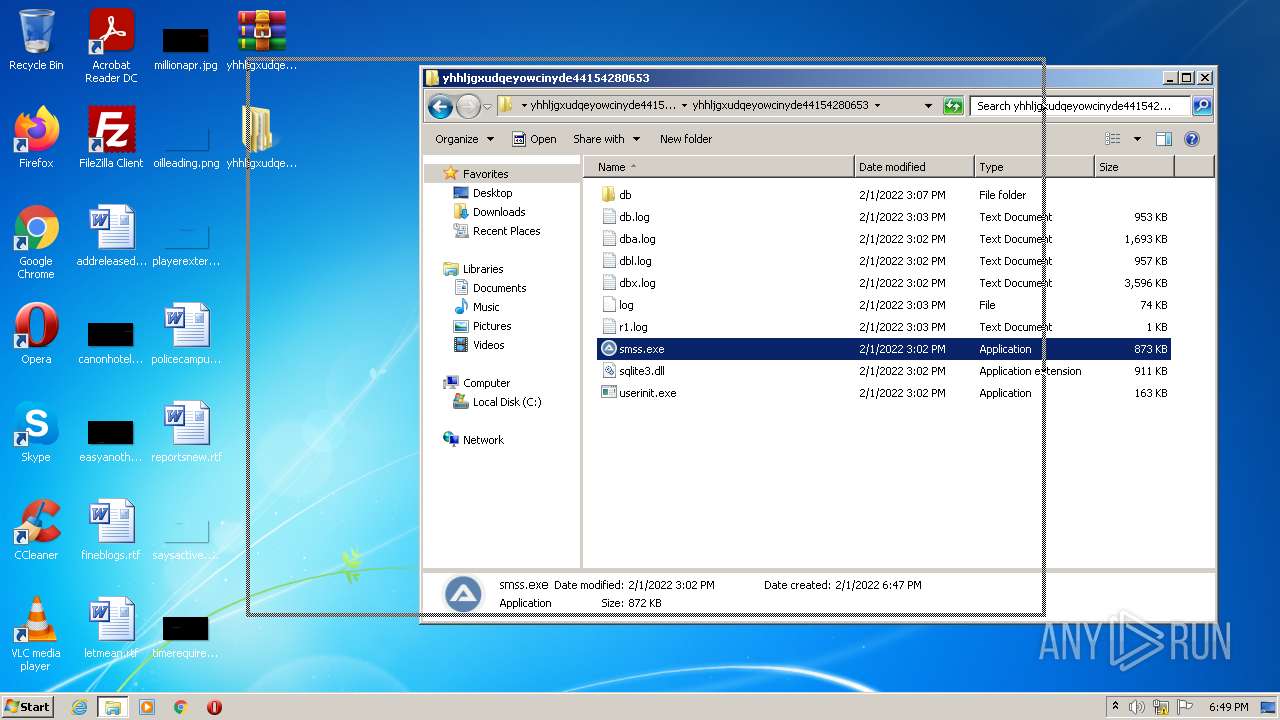
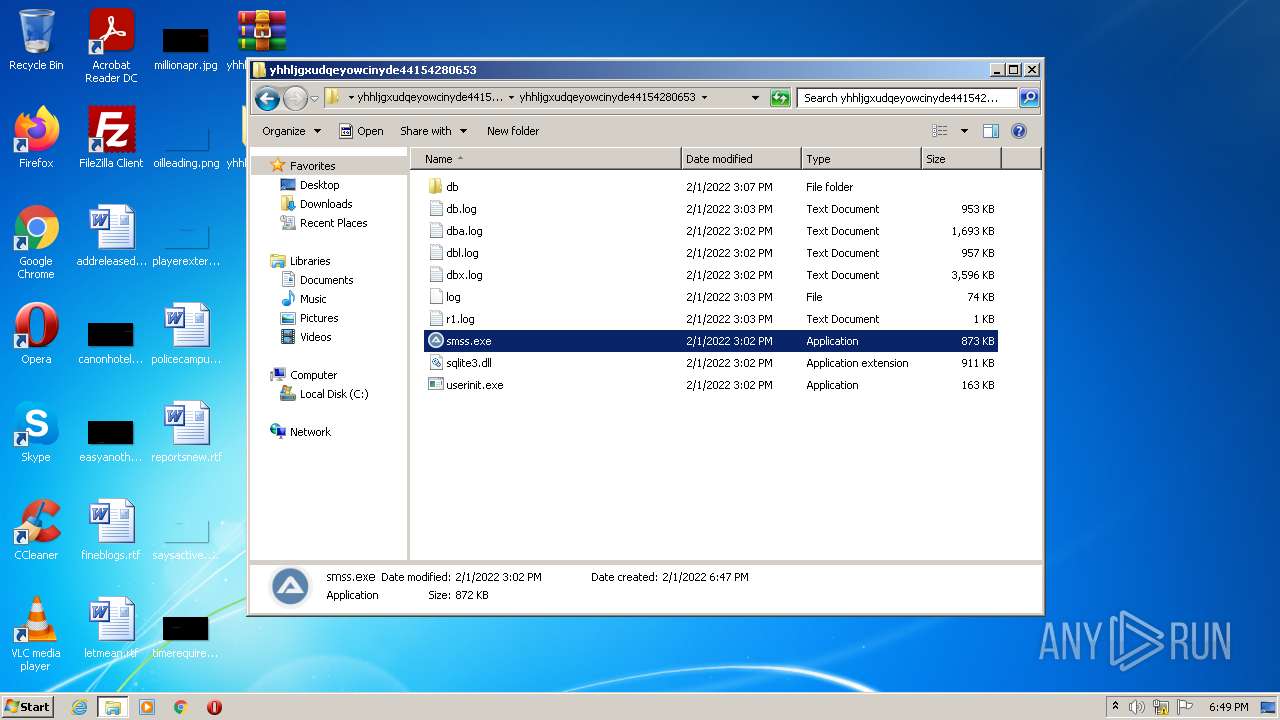
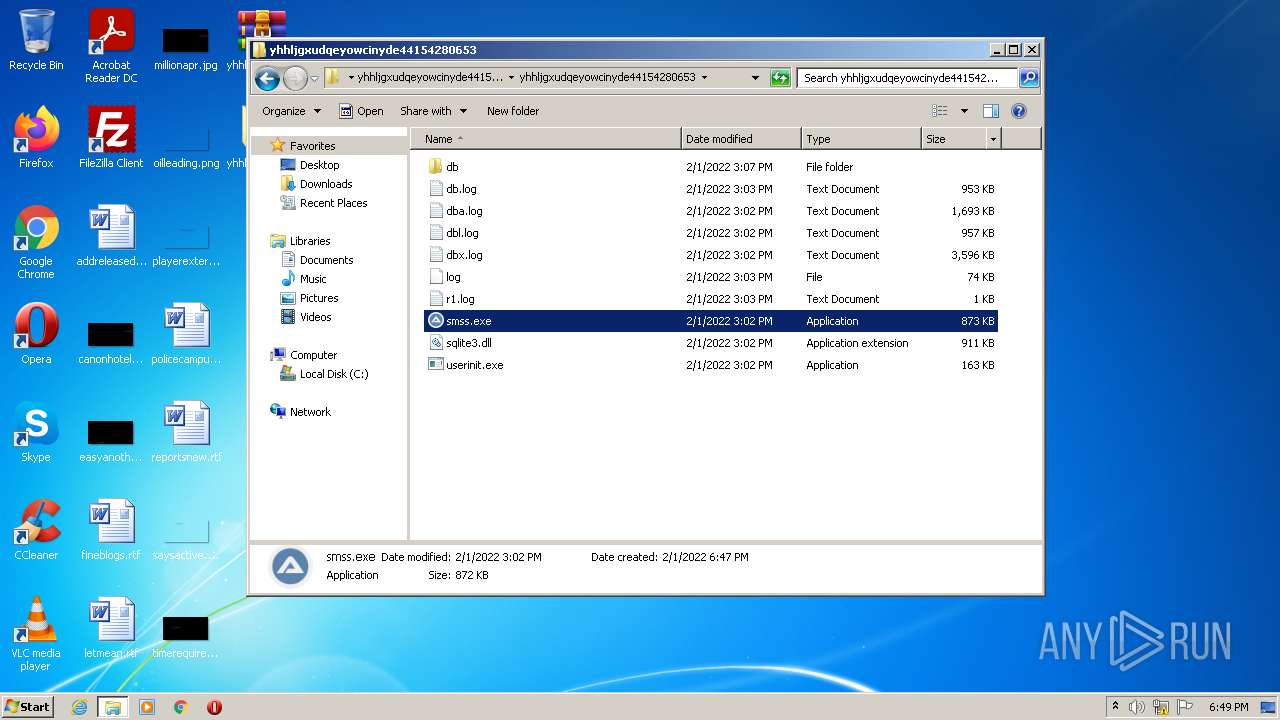
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 872 | WinRAR.exe | C:\Users\admin\Desktop\yhhljgxudqeyowcinyde44154280653\yhhljgxudqeyowcinyde44154280653\log | text | |
MD5:— | SHA256:— | |||
| 872 | WinRAR.exe | C:\Users\admin\Desktop\yhhljgxudqeyowcinyde44154280653\yhhljgxudqeyowcinyde44154280653\dbl.log | binary | |
MD5:— | SHA256:— | |||
| 872 | WinRAR.exe | C:\Users\admin\Desktop\yhhljgxudqeyowcinyde44154280653\yhhljgxudqeyowcinyde44154280653\dba.log | text | |
MD5:— | SHA256:— | |||
| 872 | WinRAR.exe | C:\Users\admin\Desktop\yhhljgxudqeyowcinyde44154280653\yhhljgxudqeyowcinyde44154280653\dbx.log | binary | |
MD5:— | SHA256:— | |||
| 872 | WinRAR.exe | C:\Users\admin\Desktop\yhhljgxudqeyowcinyde44154280653\yhhljgxudqeyowcinyde44154280653\db.log | executable | |
MD5:— | SHA256:— | |||
| 872 | WinRAR.exe | C:\Users\admin\Desktop\yhhljgxudqeyowcinyde44154280653\yhhljgxudqeyowcinyde44154280653\r1.log | text | |
MD5:— | SHA256:— | |||
| 872 | WinRAR.exe | C:\Users\admin\Desktop\yhhljgxudqeyowcinyde44154280653\yhhljgxudqeyowcinyde44154280653\smss.exe | executable | |
MD5:C56B5F0201A3B3DE53E561FE76912BFD | SHA256:237D1BCA6E056DF5BB16A1216A434634109478F882D3B1D58344C801D184F95D | |||
| 872 | WinRAR.exe | C:\Users\admin\Desktop\yhhljgxudqeyowcinyde44154280653\yhhljgxudqeyowcinyde44154280653\sqlite3.dll | executable | |
MD5:DEF2572CCAE7F518BD9D30F37B2FED04 | SHA256:B712286D4D36C74FA32127F848B79CFB857FDC2B1C84BBBEE285CF34752443A2 | |||
| 872 | WinRAR.exe | C:\Users\admin\Desktop\yhhljgxudqeyowcinyde44154280653\yhhljgxudqeyowcinyde44154280653\db\userinitUI.dll | executable | |
MD5:C6640126032A4DDCDAADF264B6B9B961 | SHA256:E049855B8561C9F68889113362CBED470649DB2575EE804E28474D1EE65827DE | |||
| 872 | WinRAR.exe | C:\Users\admin\Desktop\yhhljgxudqeyowcinyde44154280653\yhhljgxudqeyowcinyde44154280653\userinit.exe | executable | |
MD5:C7575C57DD0B3E1D93B98F22281120CE | SHA256:456BE13B7BFD64A3046E06E6732880D99214669BC2C0D648E4ECFFD83F9F75A5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2636 | svchost.exe | GET | 200 | 192.99.13.63:80 | http://sstatic1.histats.com/0.gif?4625558&101 | CA | image | 43 b | malicious |
3096 | svchost.exe | GET | 200 | 192.99.13.63:80 | http://sstatic1.histats.com/0.gif?4625558&101 | CA | image | 43 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2636 | svchost.exe | 192.99.13.63:80 | sstatic1.histats.com | OVH SAS | CA | suspicious |
3096 | svchost.exe | 192.99.13.63:80 | sstatic1.histats.com | OVH SAS | CA | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sstatic1.histats.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2636 | svchost.exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Embarcadero URI Client/1.0) |
3096 | svchost.exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Embarcadero URI Client/1.0) |