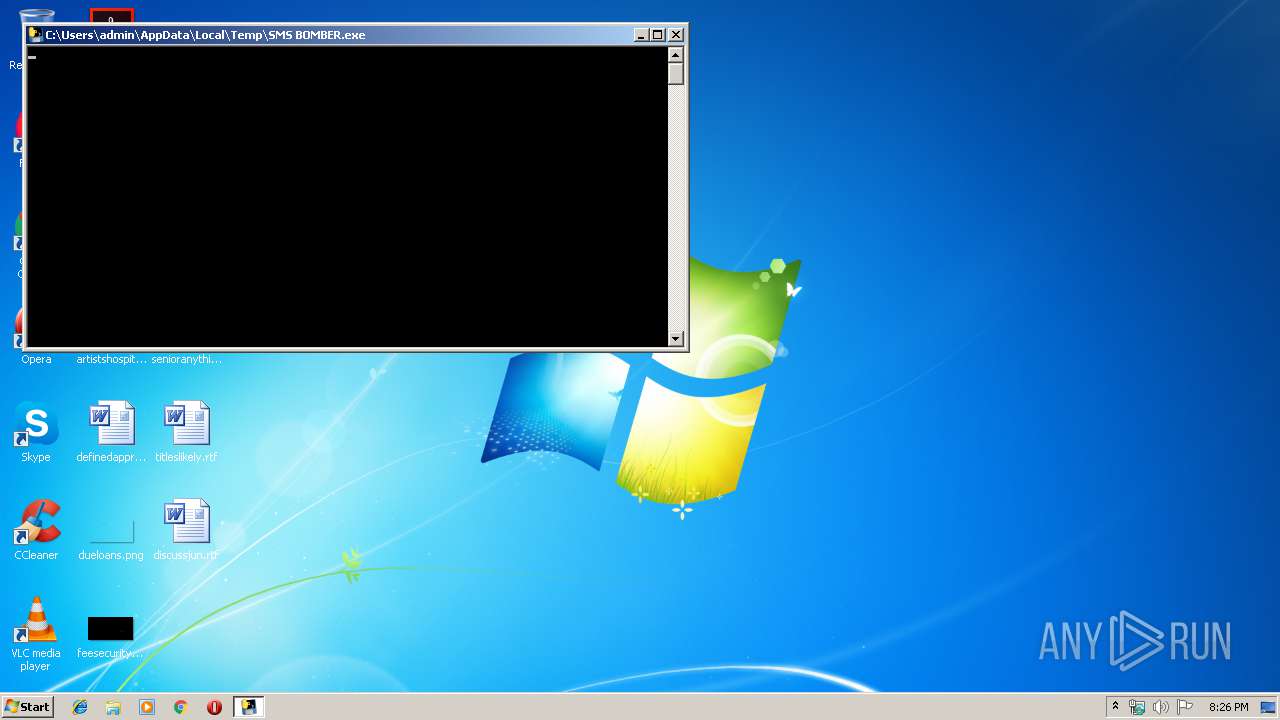
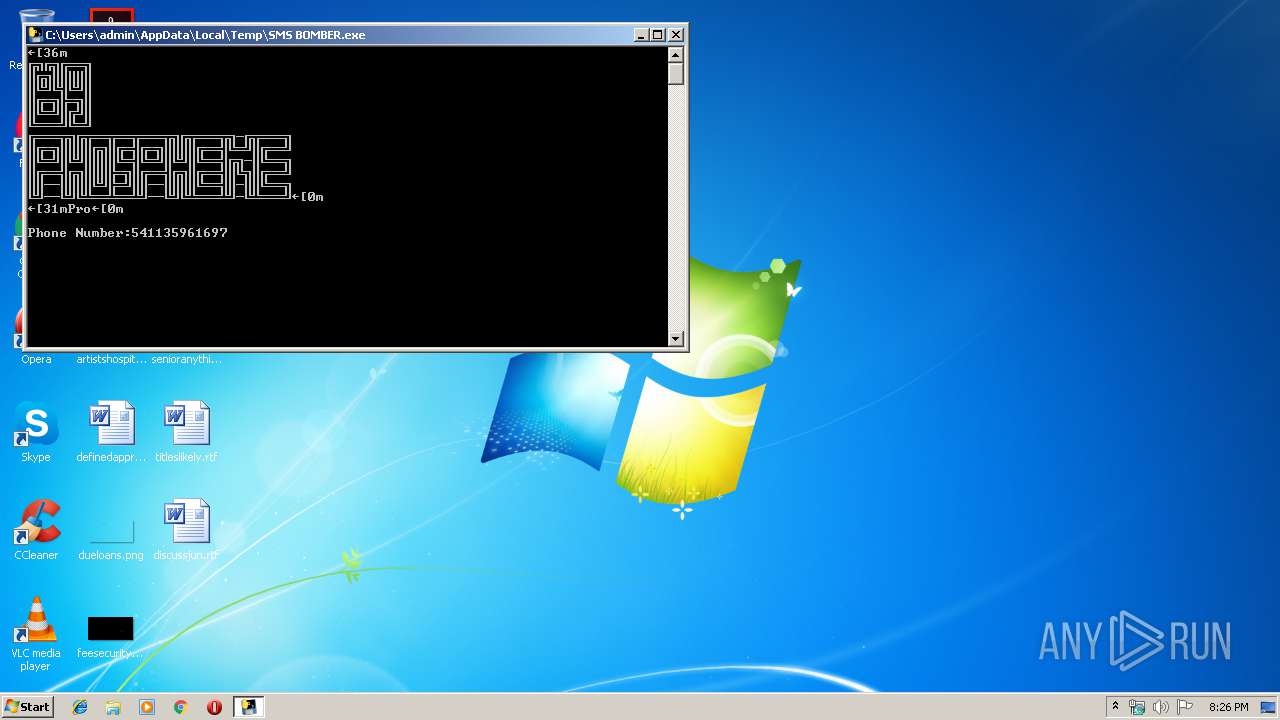
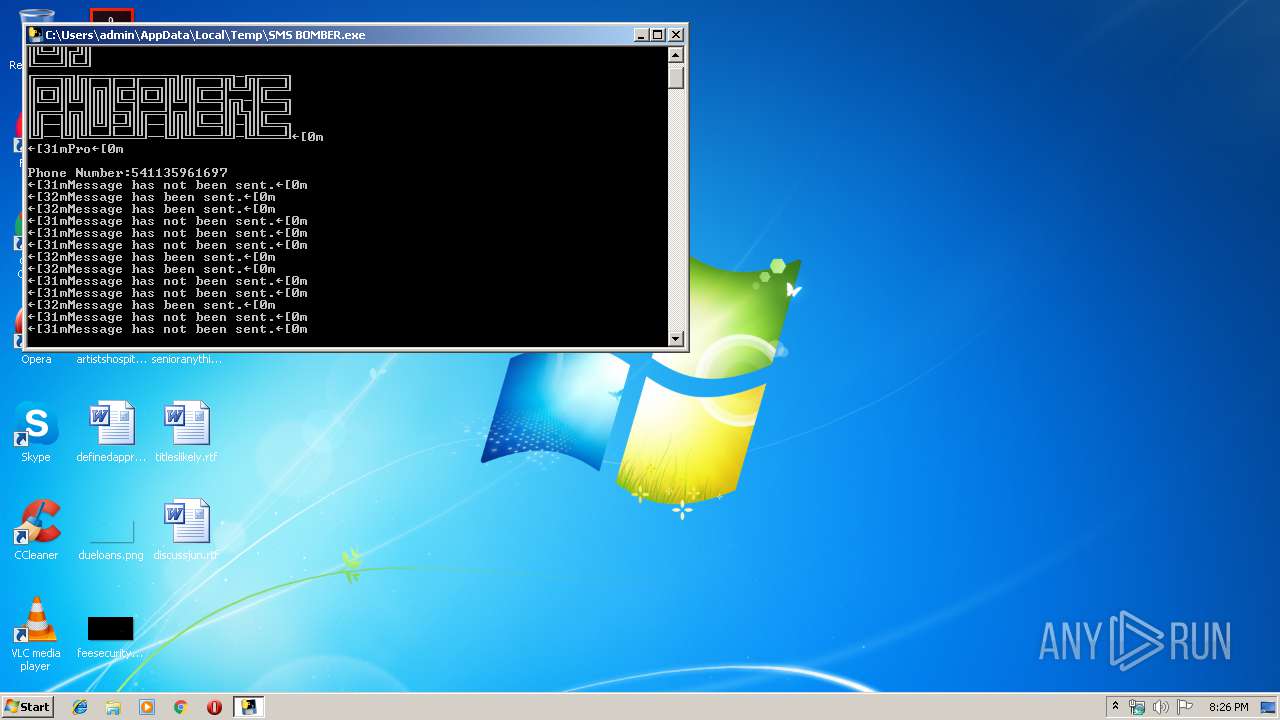
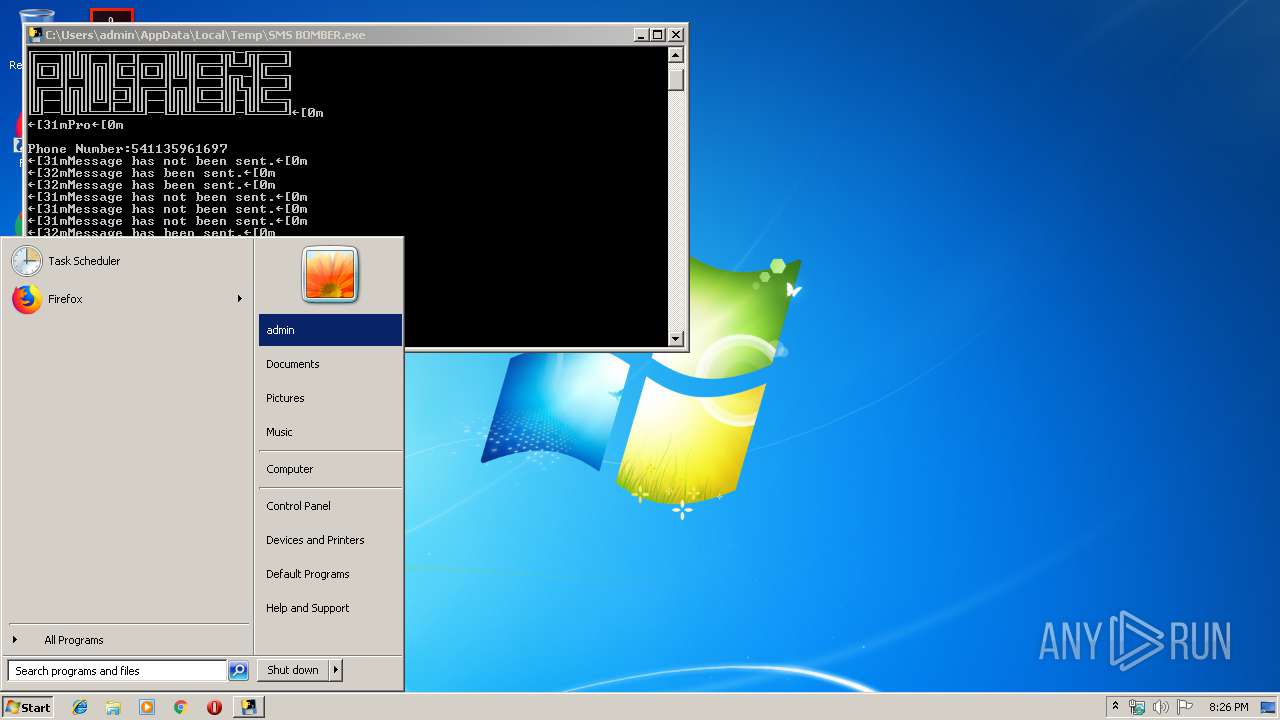
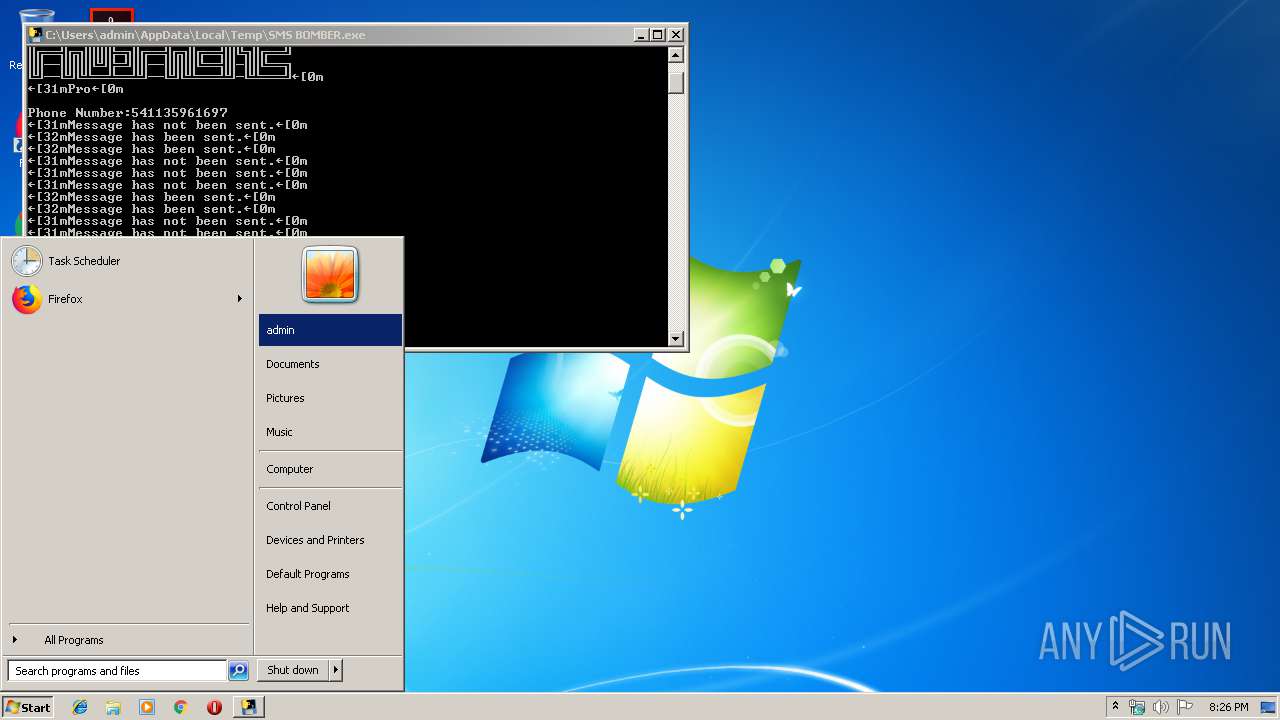
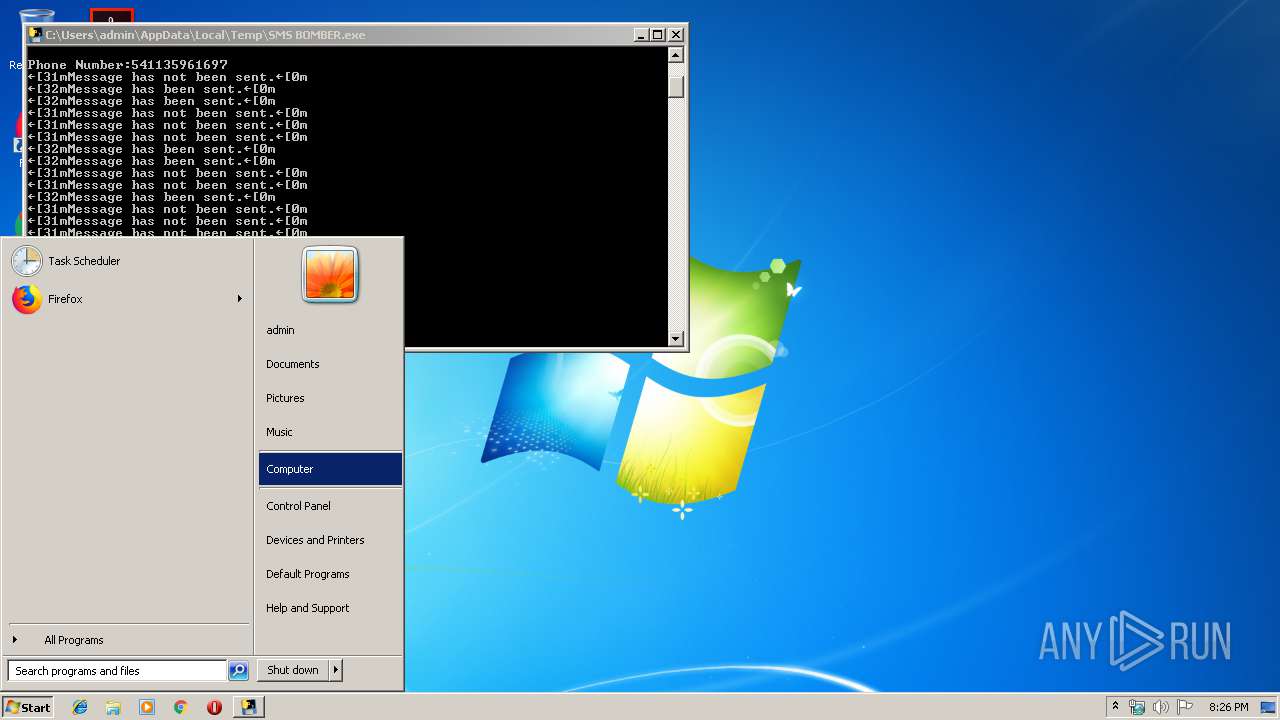
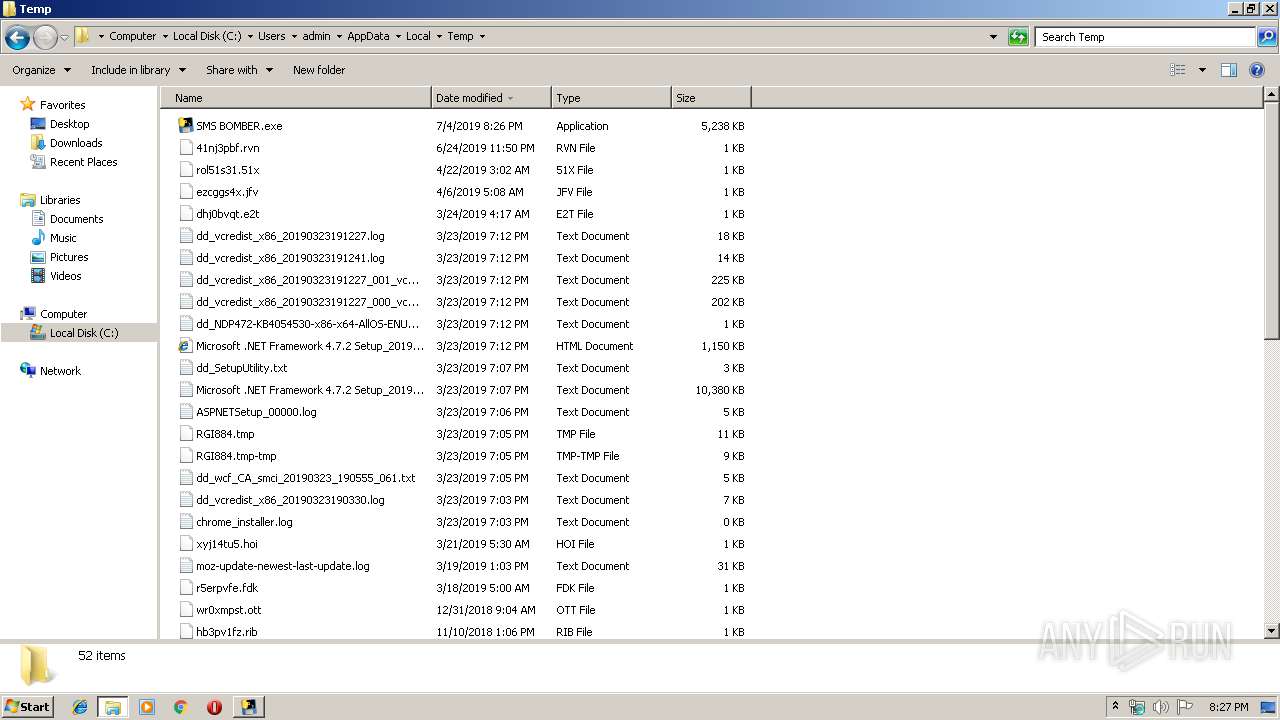
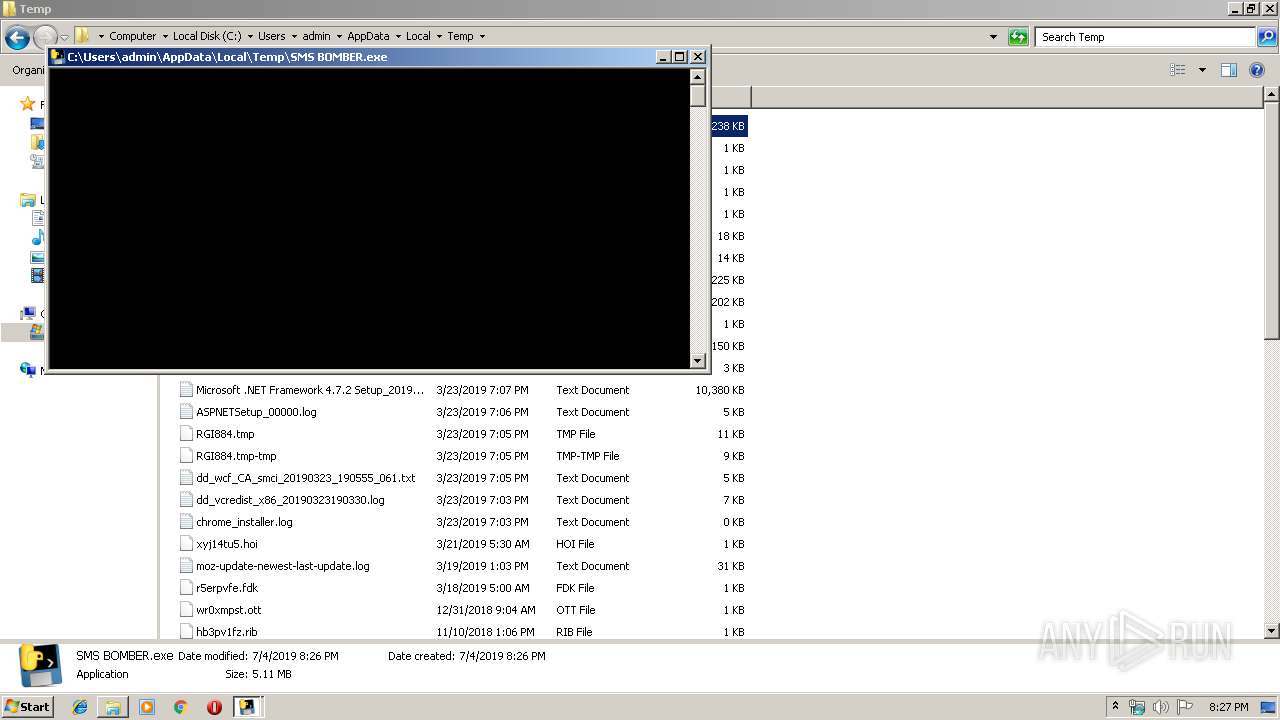
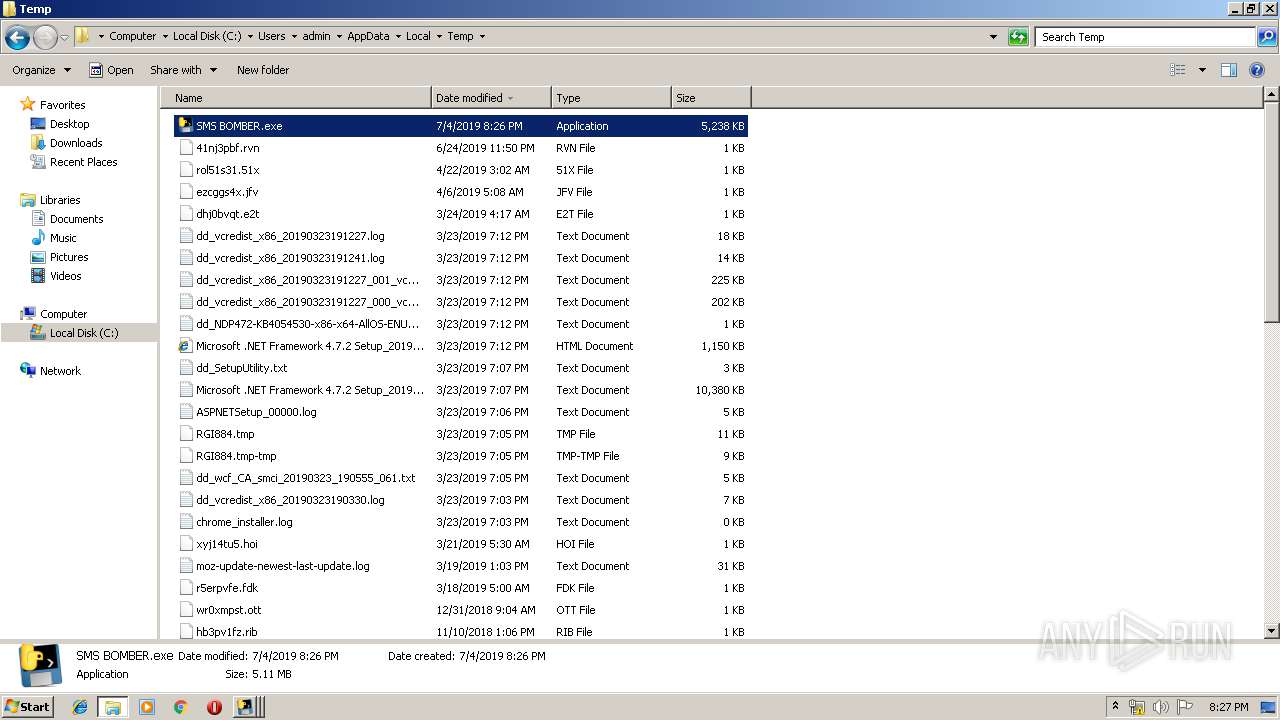
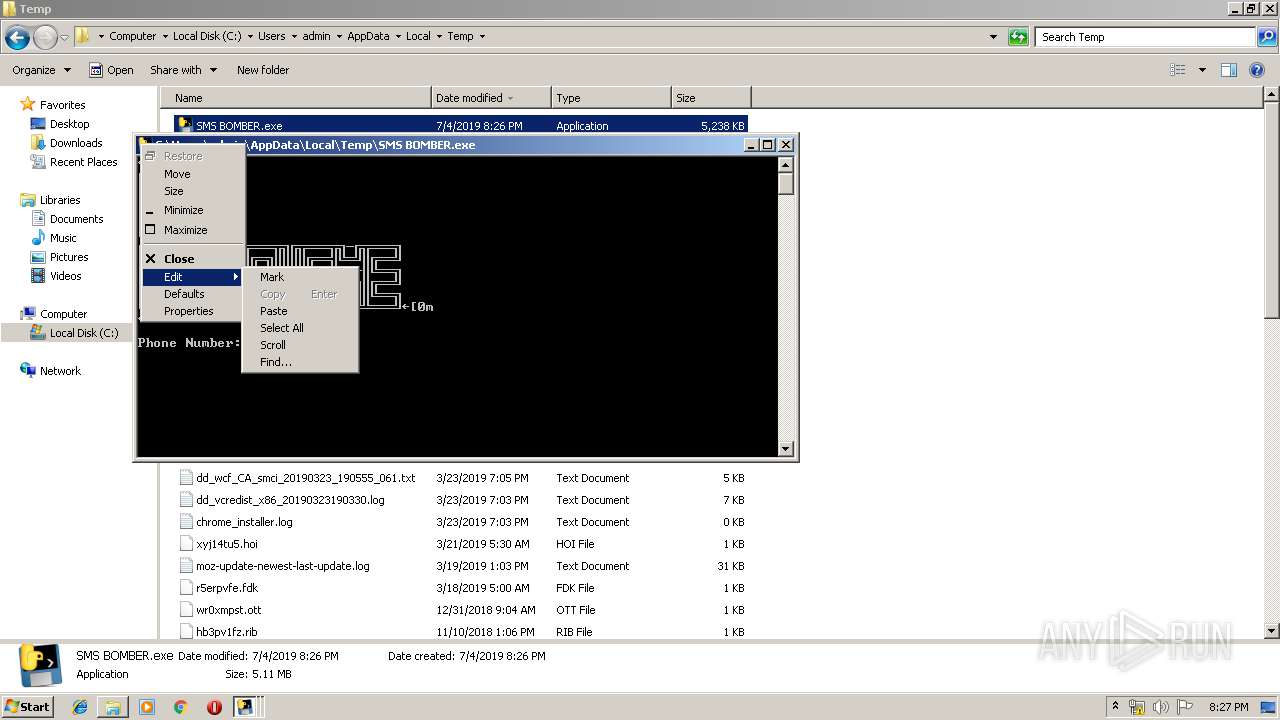
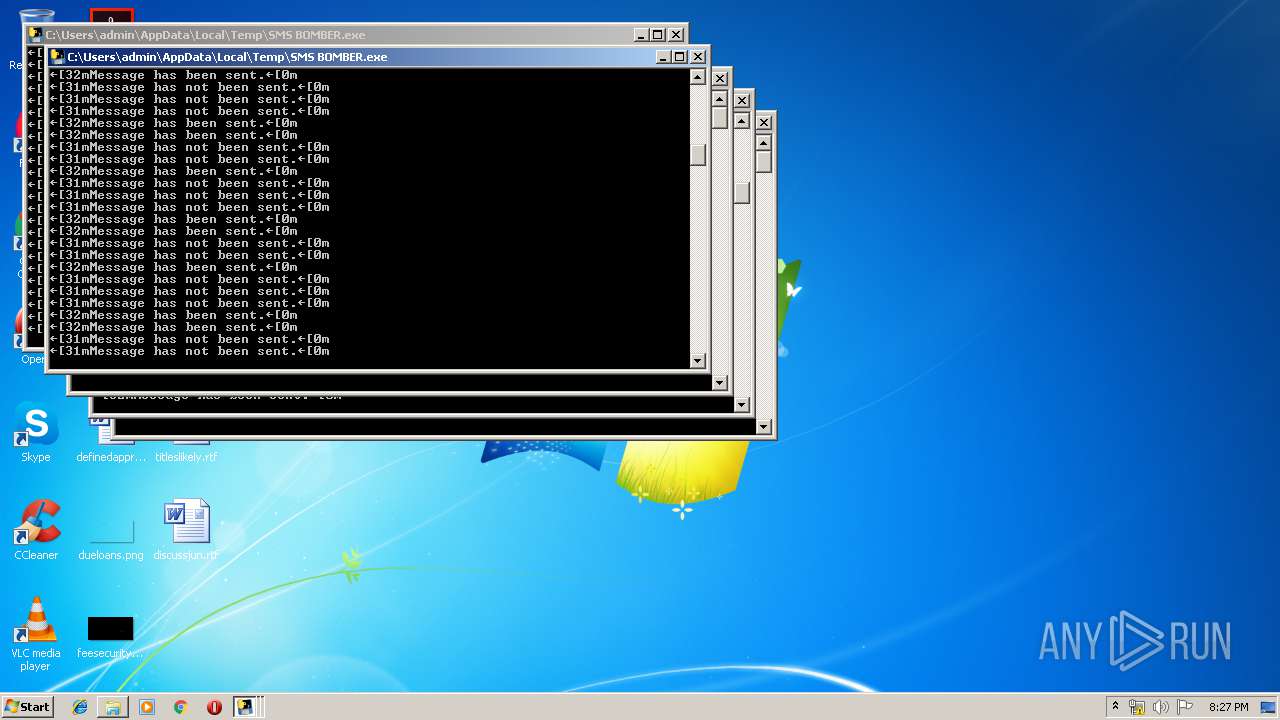
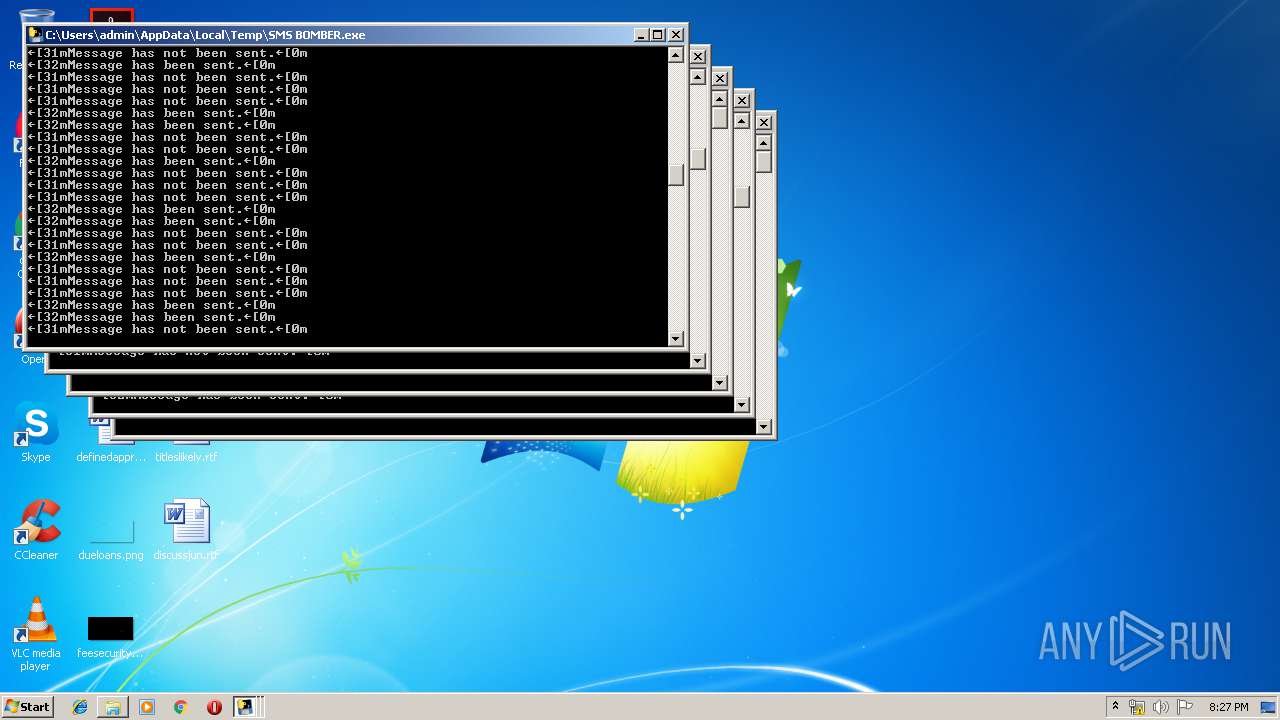
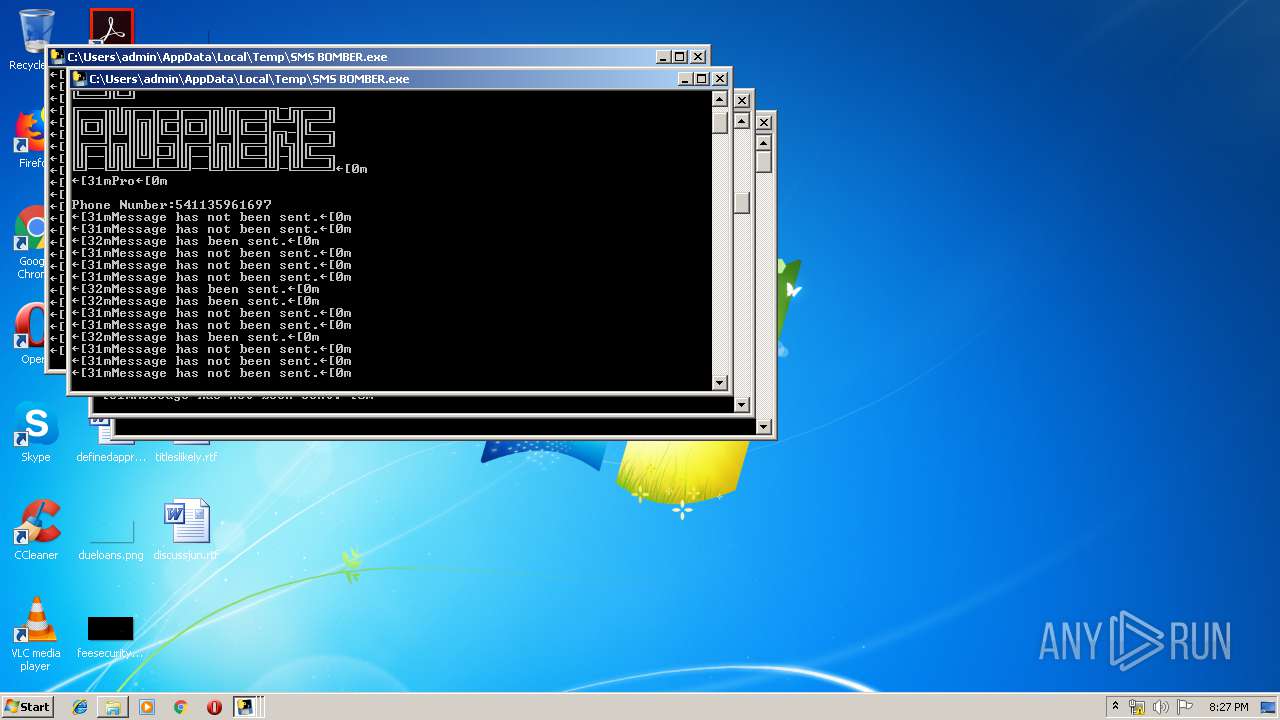
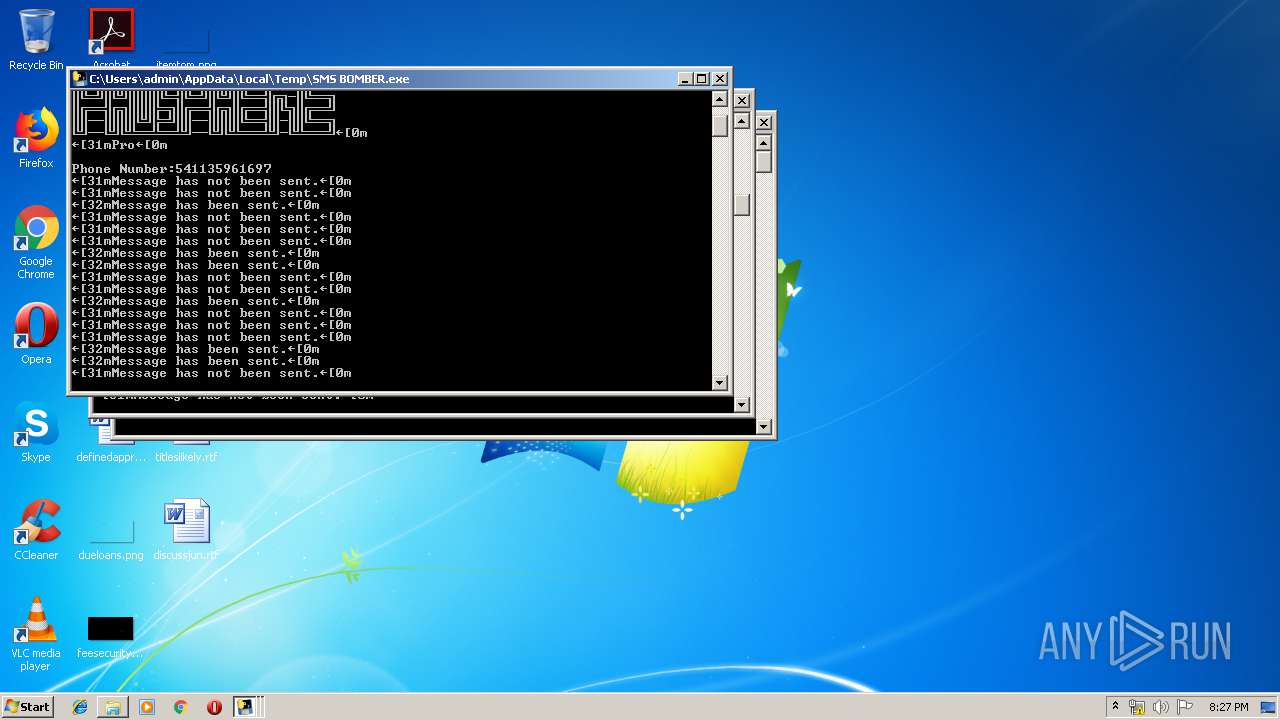
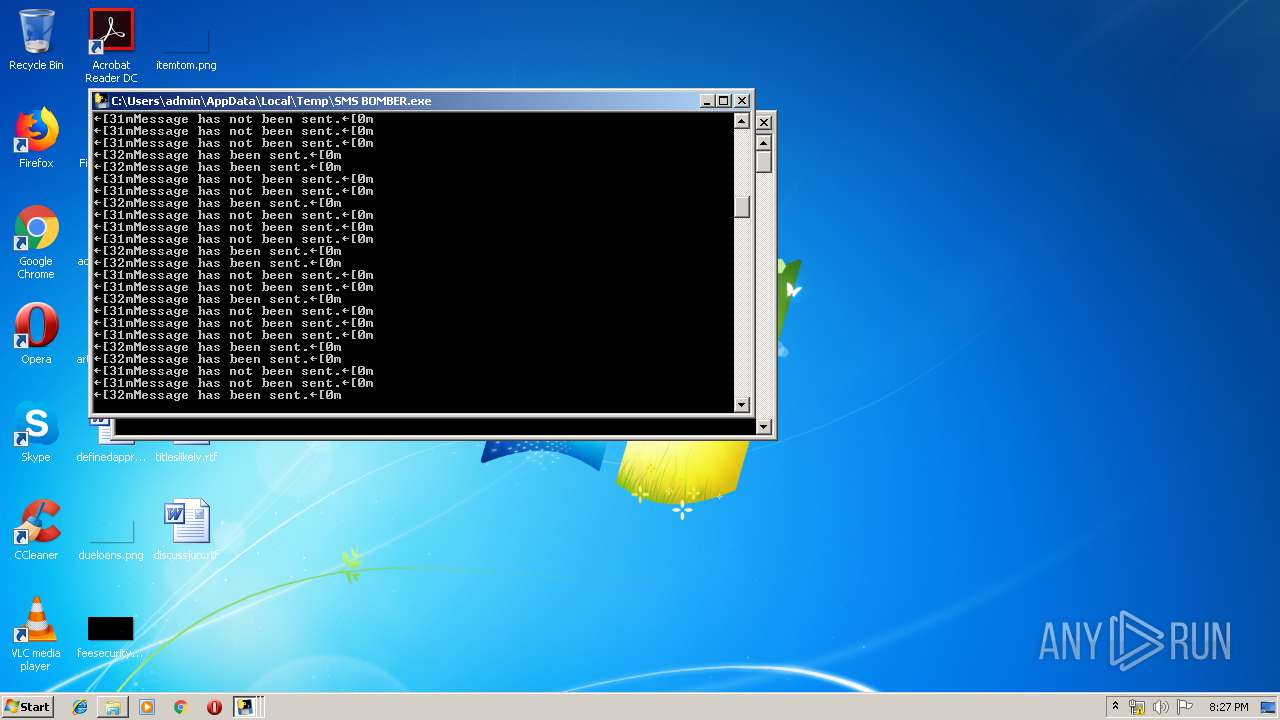
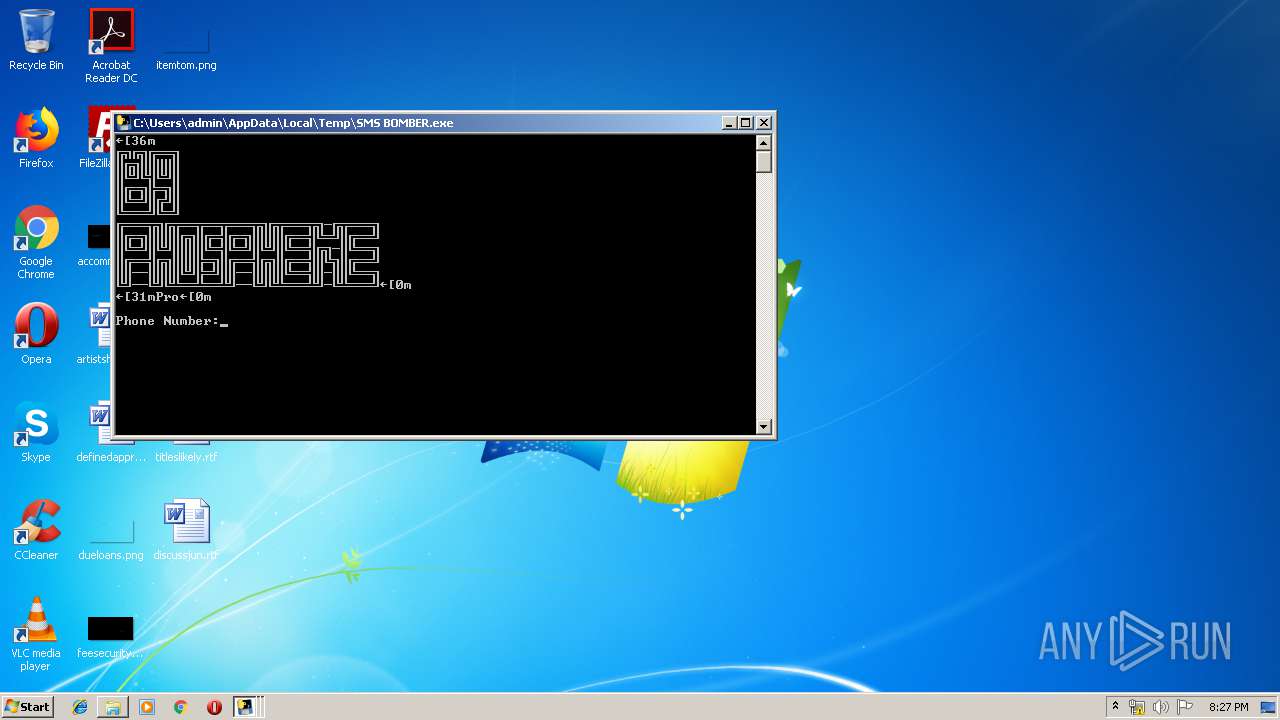
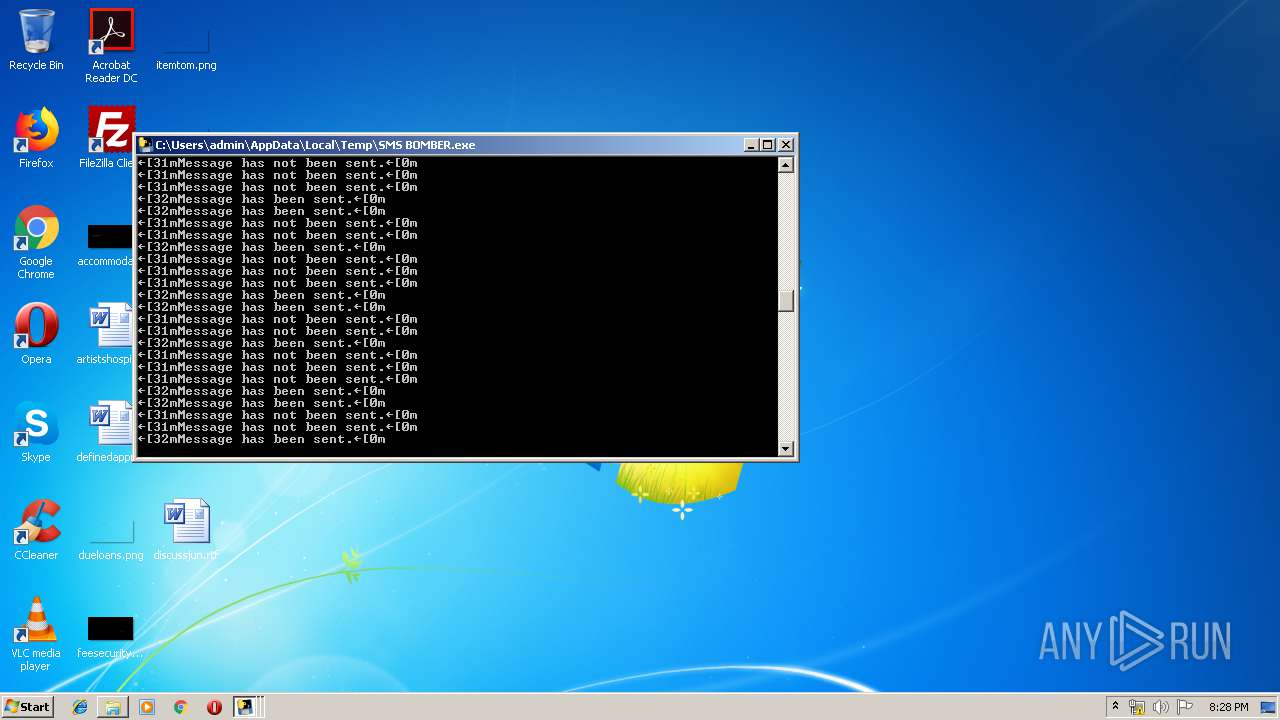
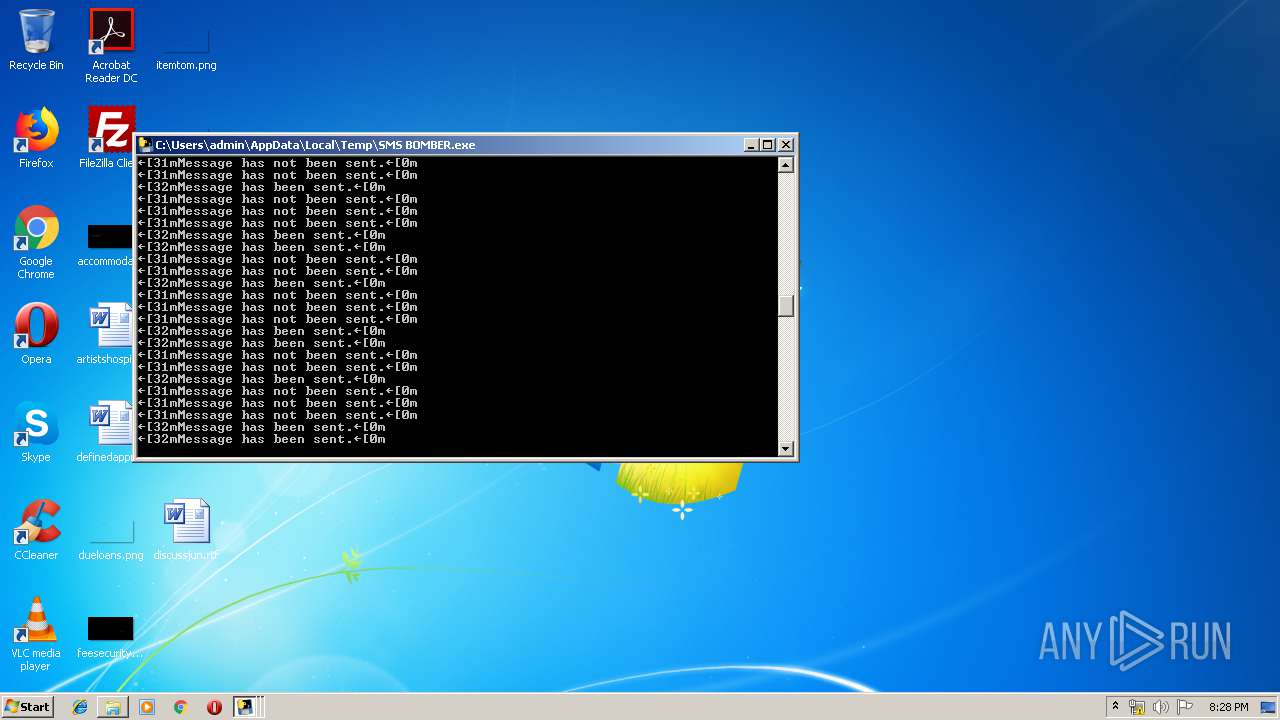
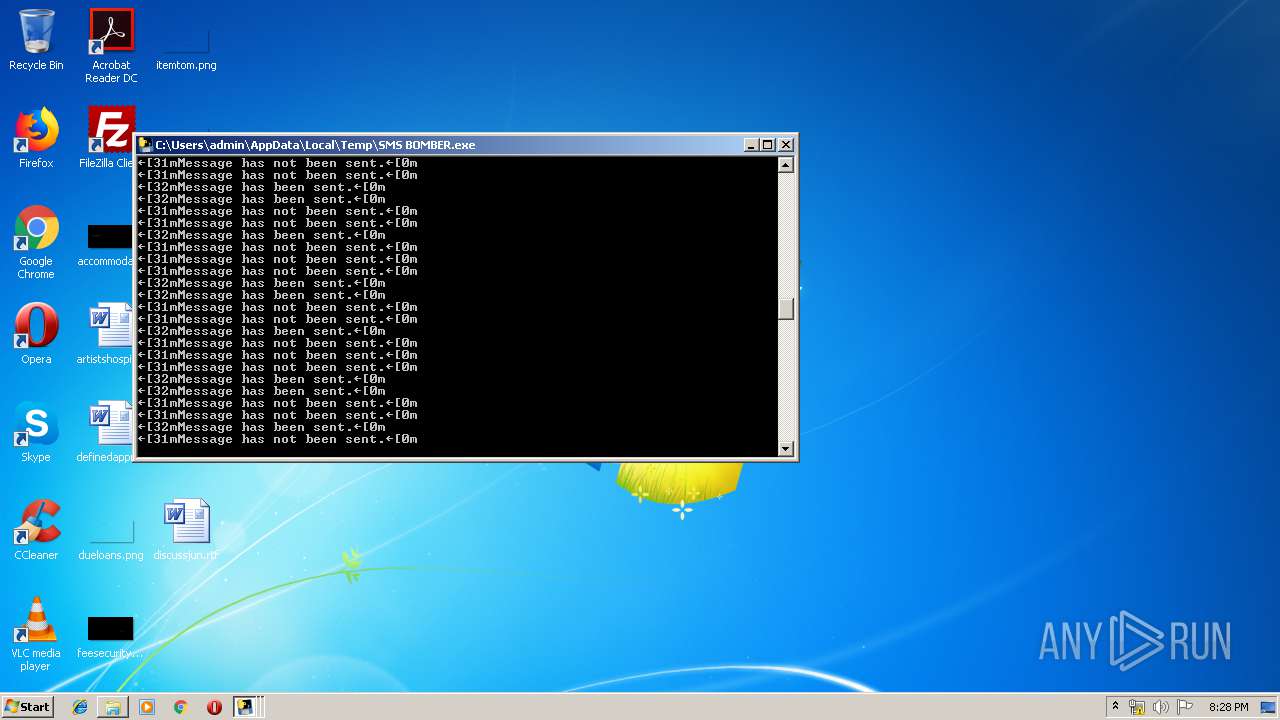
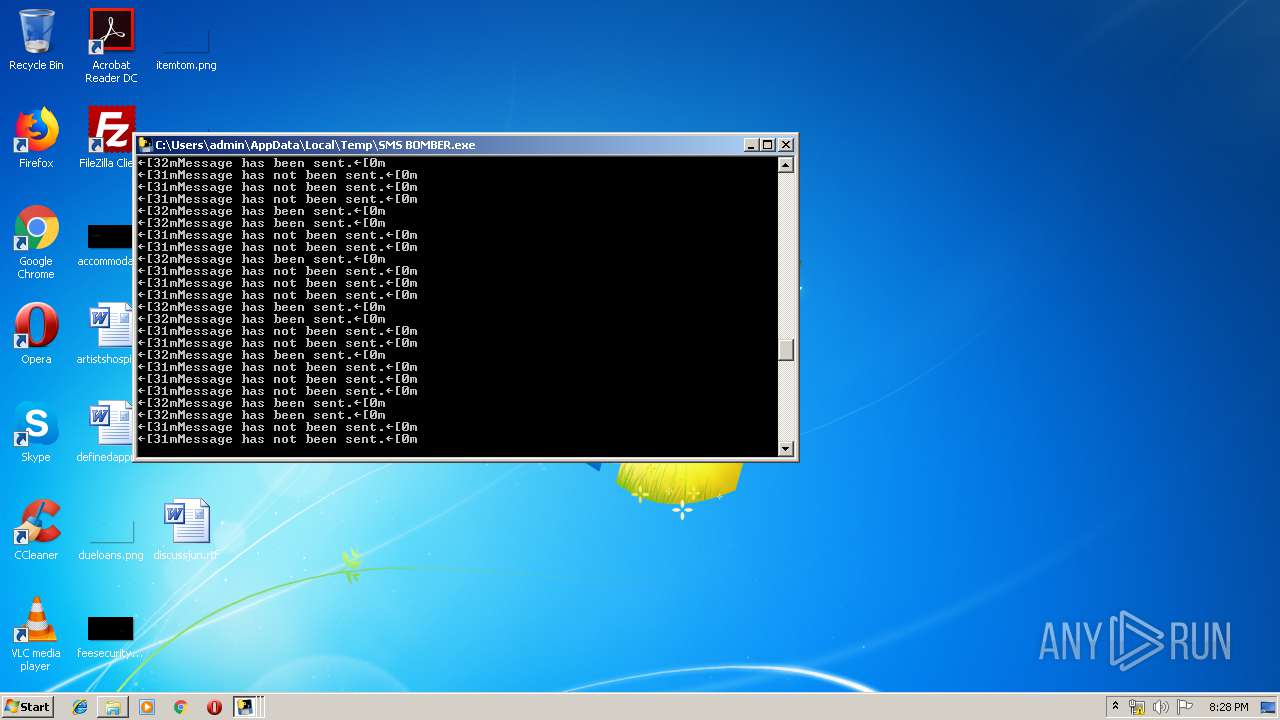
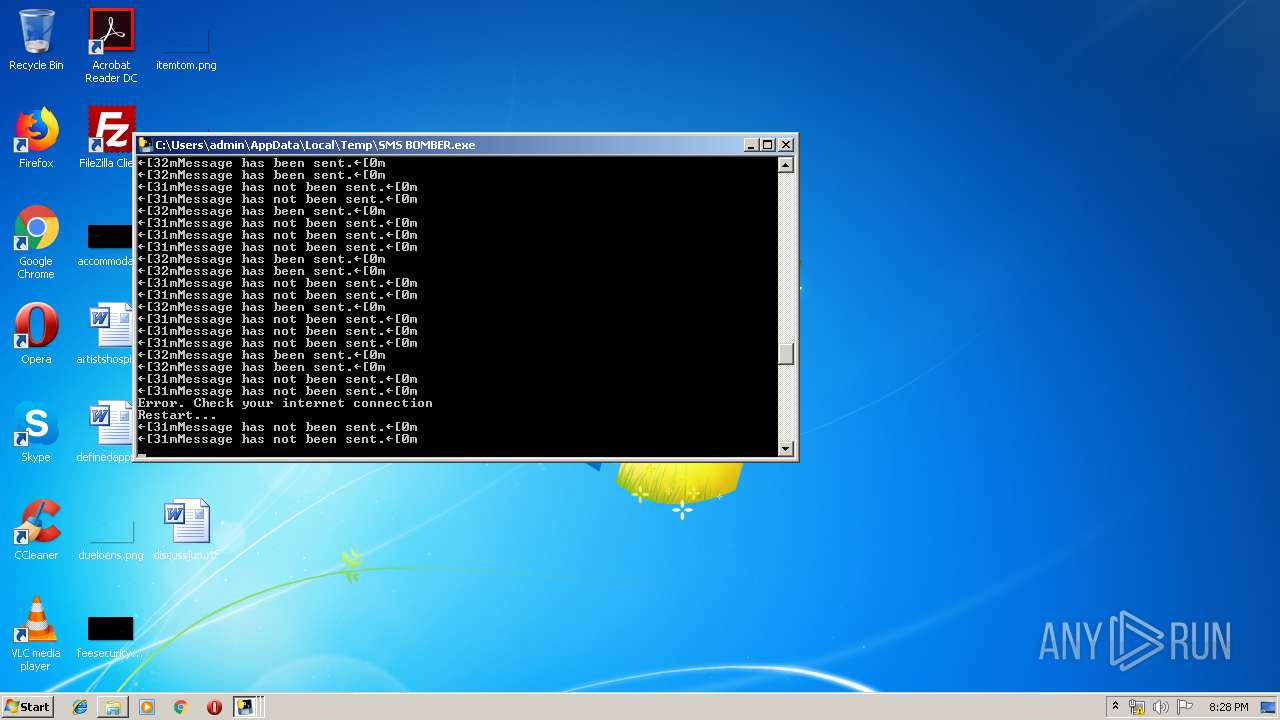
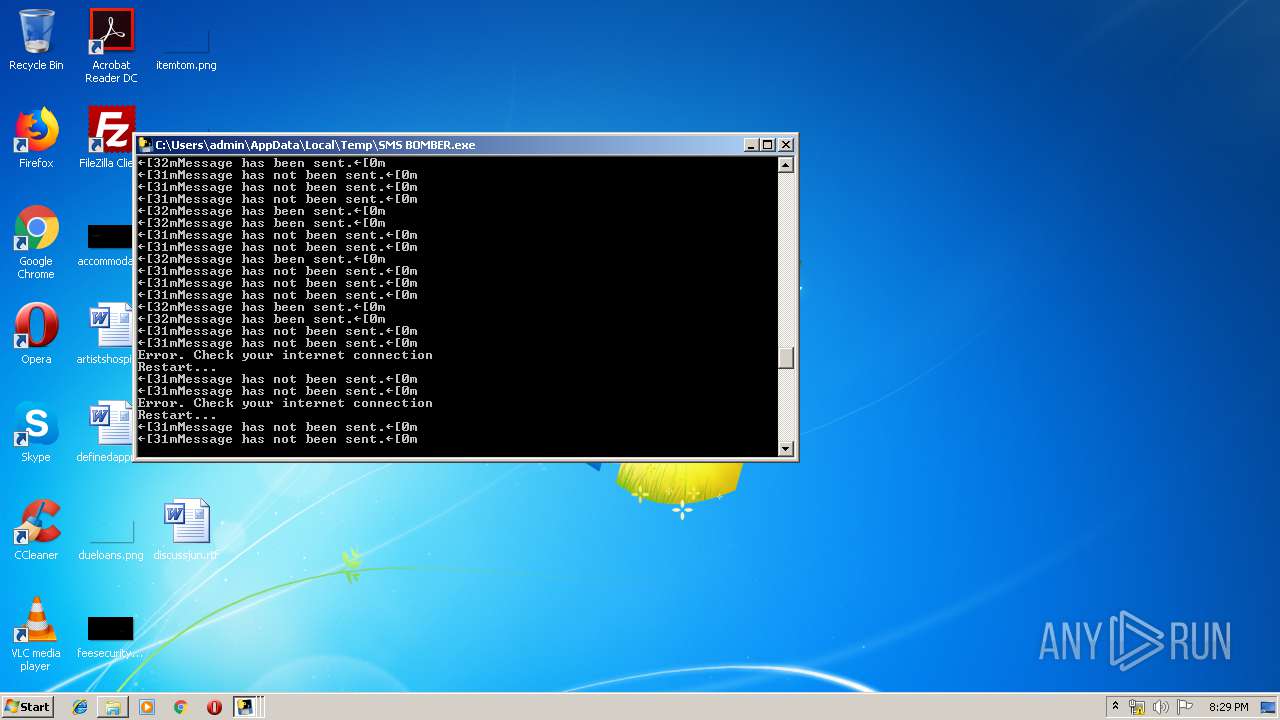
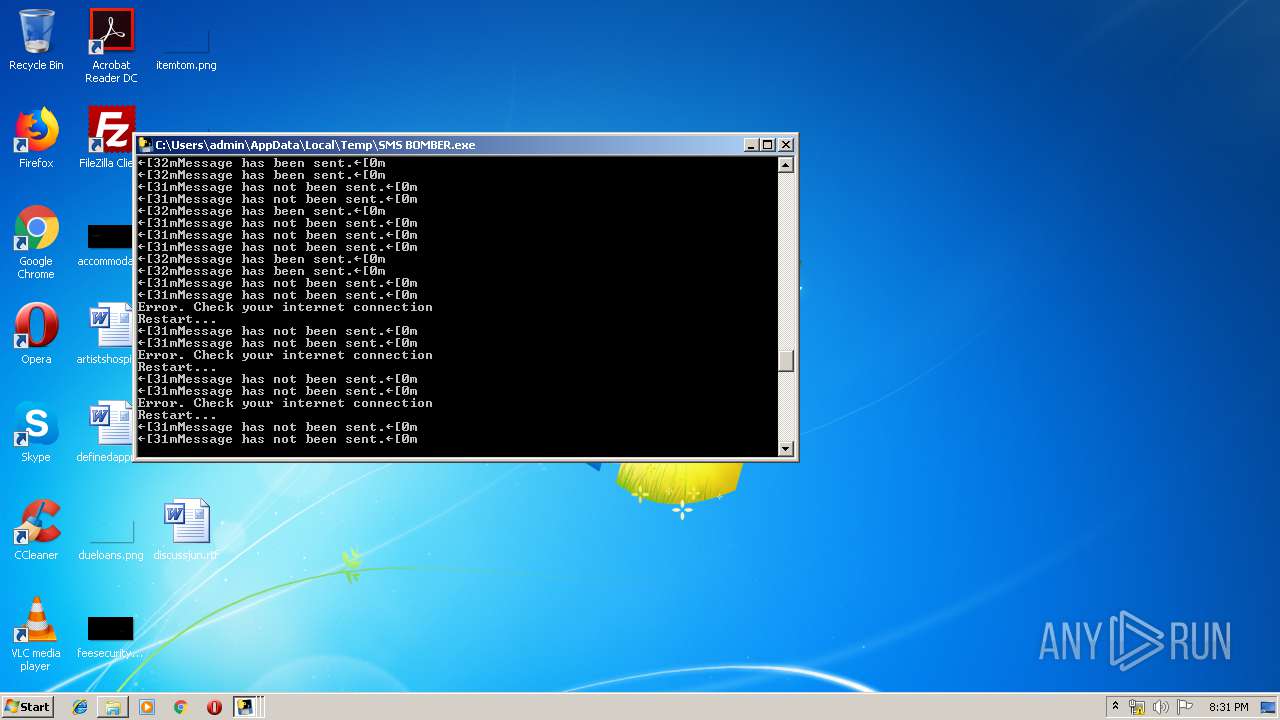
| File name: | SMS BOMBER.exe |
| Full analysis: | https://app.any.run/tasks/fd96e07f-c89f-413c-aed1-85c3f921e71b |
| Verdict: | Malicious activity |
| Analysis date: | July 04, 2019, 19:25:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | A415F7414587A40A33F8FACDDD6D5E9D |
| SHA1: | 29EAF61DA90A1962D01EB3670EDB17ABE3BD8897 |
| SHA256: | 064B421C4B1935BDF8F6D8DD164749207130BFFE1A1CD59D5D295E8AF64CDC22 |
| SSDEEP: | 98304:aiMPUXmTjJ5q9Jt4gy9ImjXE3cPtEBO7oVVgveybtML2Z+fK3yKts:92U4J5q9D4ImjXEMGBO7oAveytMiZxt+ |
MALICIOUS
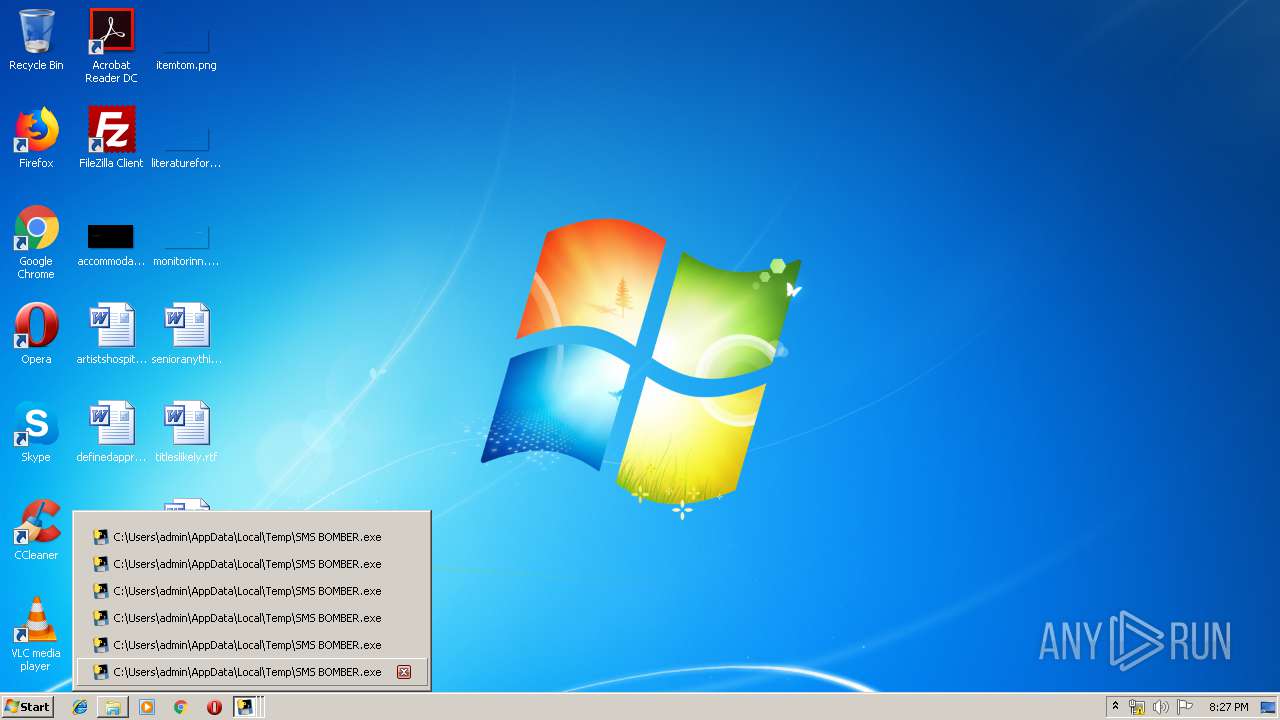
Loads dropped or rewritten executable
- SMS BOMBER.exe (PID: 2356)
- SMS BOMBER.exe (PID: 4044)
- SMS BOMBER.exe (PID: 3088)
- SMS BOMBER.exe (PID: 3860)
- SMS BOMBER.exe (PID: 3908)
- SMS BOMBER.exe (PID: 3432)
SUSPICIOUS
Executable content was dropped or overwritten
- SMS BOMBER.exe (PID: 3984)
- SMS BOMBER.exe (PID: 3336)
- SMS BOMBER.exe (PID: 2516)
- SMS BOMBER.exe (PID: 2168)
- SMS BOMBER.exe (PID: 2860)
- SMS BOMBER.exe (PID: 2340)
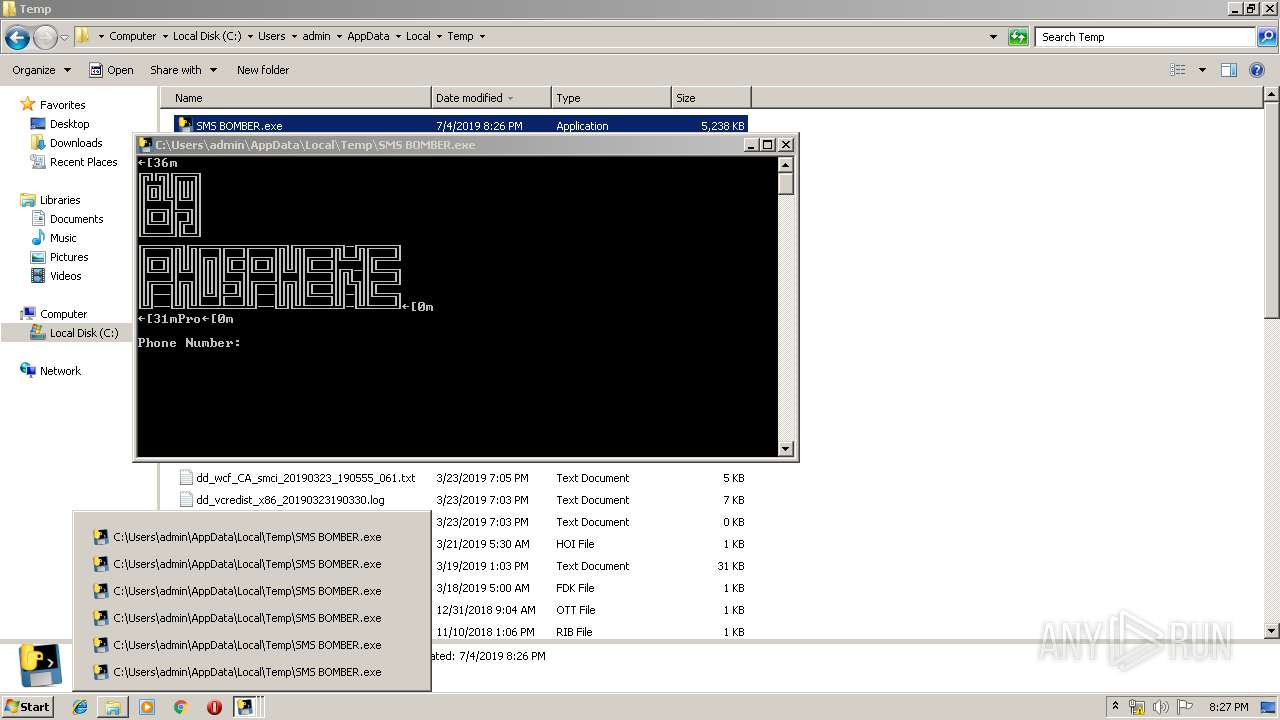
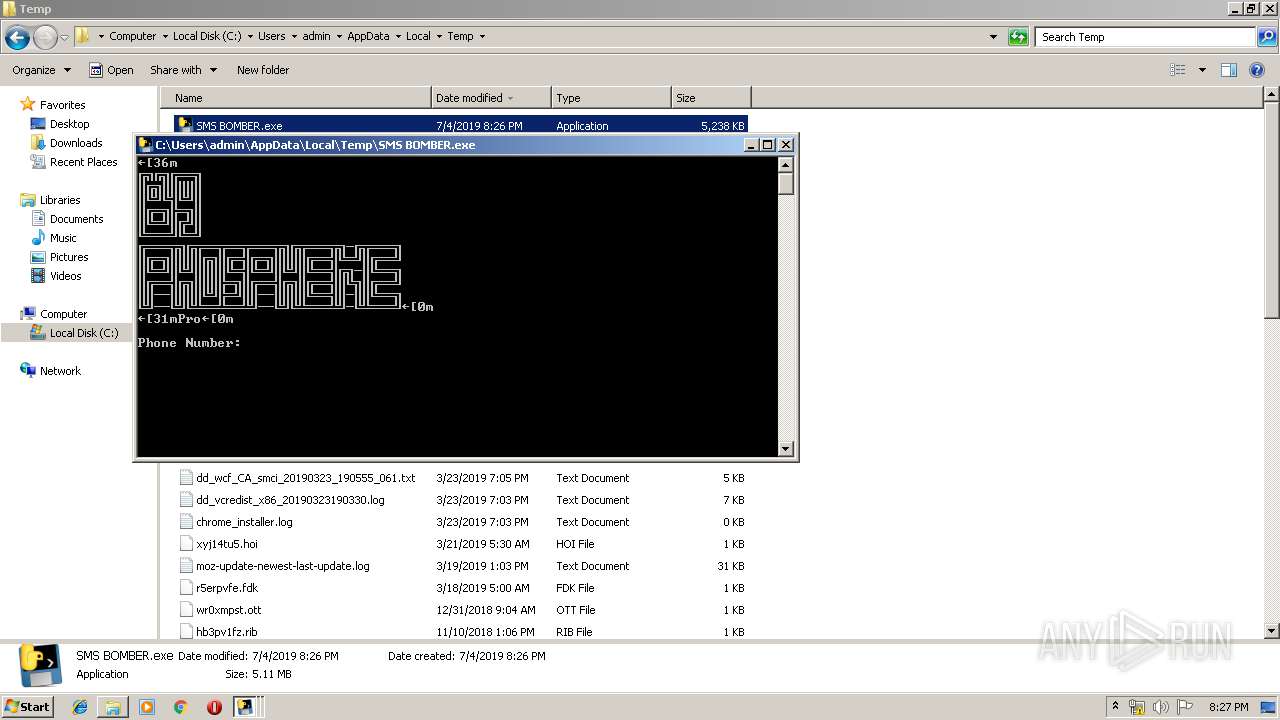
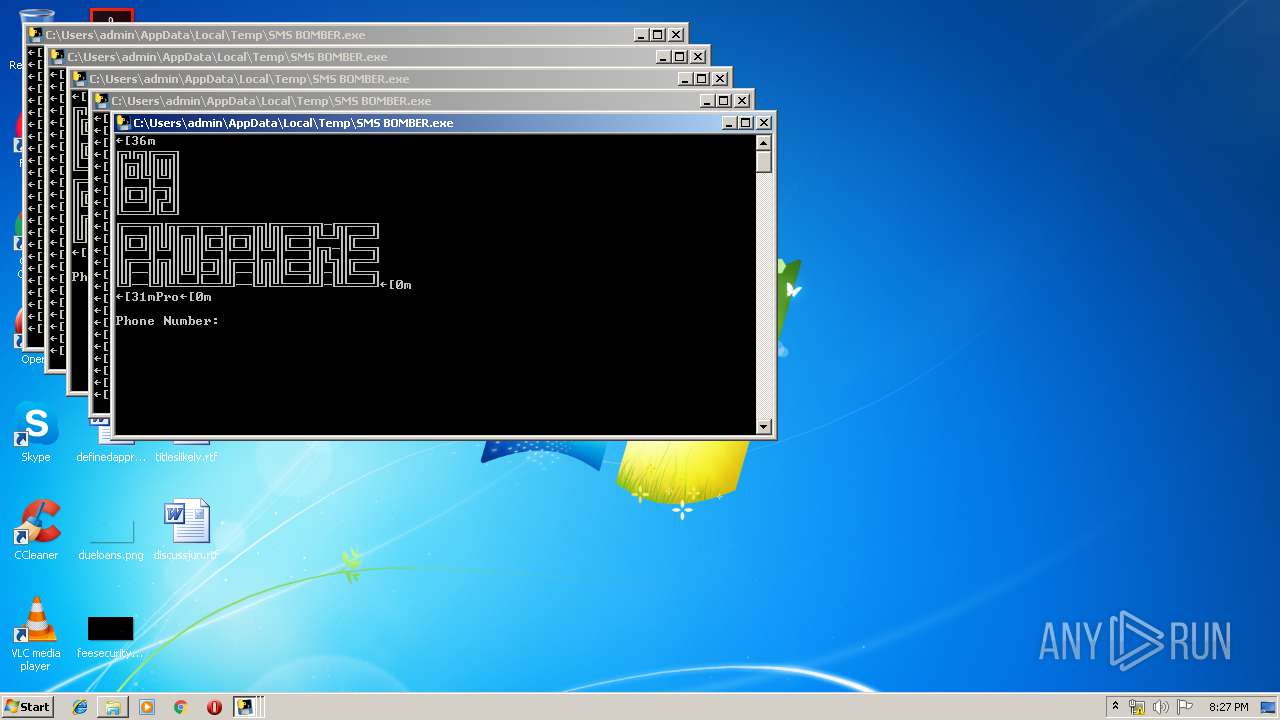
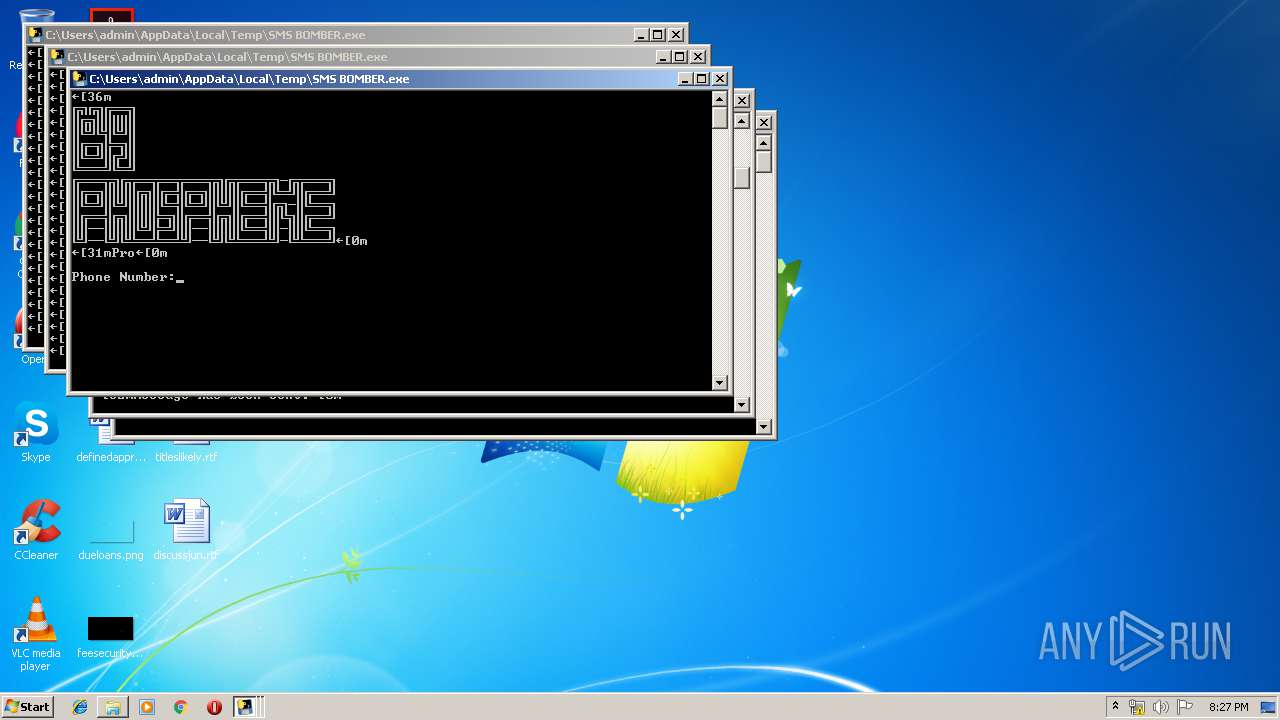
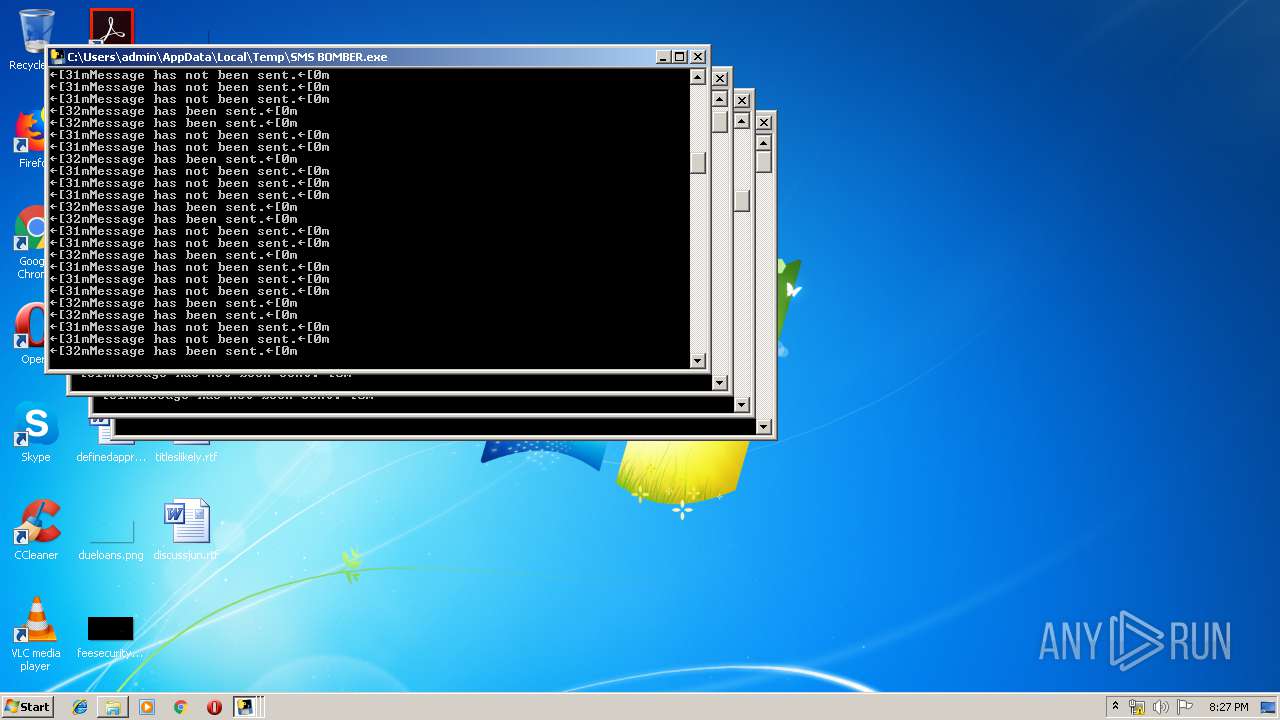
Application launched itself
- SMS BOMBER.exe (PID: 3336)
- SMS BOMBER.exe (PID: 3984)
- SMS BOMBER.exe (PID: 2516)
Loads Python modules
- SMS BOMBER.exe (PID: 4044)
- SMS BOMBER.exe (PID: 3088)
- SMS BOMBER.exe (PID: 2356)
- SMS BOMBER.exe (PID: 3860)
- SMS BOMBER.exe (PID: 3908)
- SMS BOMBER.exe (PID: 3432)
INFO
Dropped object may contain Bitcoin addresses
- SMS BOMBER.exe (PID: 3336)
- SMS BOMBER.exe (PID: 2168)
- SMS BOMBER.exe (PID: 3984)
- SMS BOMBER.exe (PID: 2516)
- SMS BOMBER.exe (PID: 2860)
- SMS BOMBER.exe (PID: 2340)
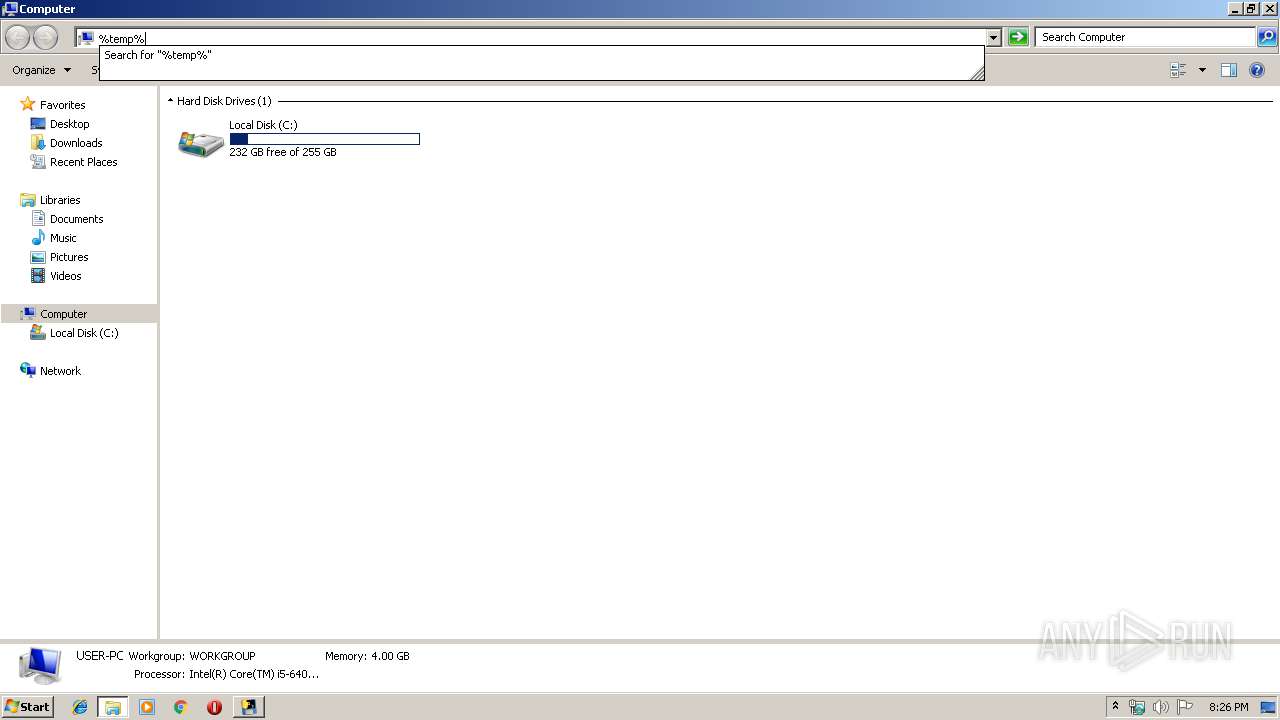
Manual execution by user
- SMS BOMBER.exe (PID: 3984)
- SMS BOMBER.exe (PID: 2516)
- SMS BOMBER.exe (PID: 2168)
- SMS BOMBER.exe (PID: 2860)
- SMS BOMBER.exe (PID: 2340)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:04 16:42:13+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 128000 |
| InitializedDataSize: | 172032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x779a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 04-Sep-2018 14:42:13 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 04-Sep-2018 14:42:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F224 | 0x0001F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.65269 |
.rdata | 0x00021000 | 0x0000B0EC | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.10091 |
.data | 0x0002D000 | 0x0000E680 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.94098 |
.gfids | 0x0003C000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.89006 |
.rsrc | 0x0003D000 | 0x0000EA38 | 0x0000EC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.29706 |
.reloc | 0x0004C000 | 0x000017B8 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65088 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.58652 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 6.05629 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.5741 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 7.95079 | 37019 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.29119 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 5.43869 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 5.89356 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
WS2_32.dll |
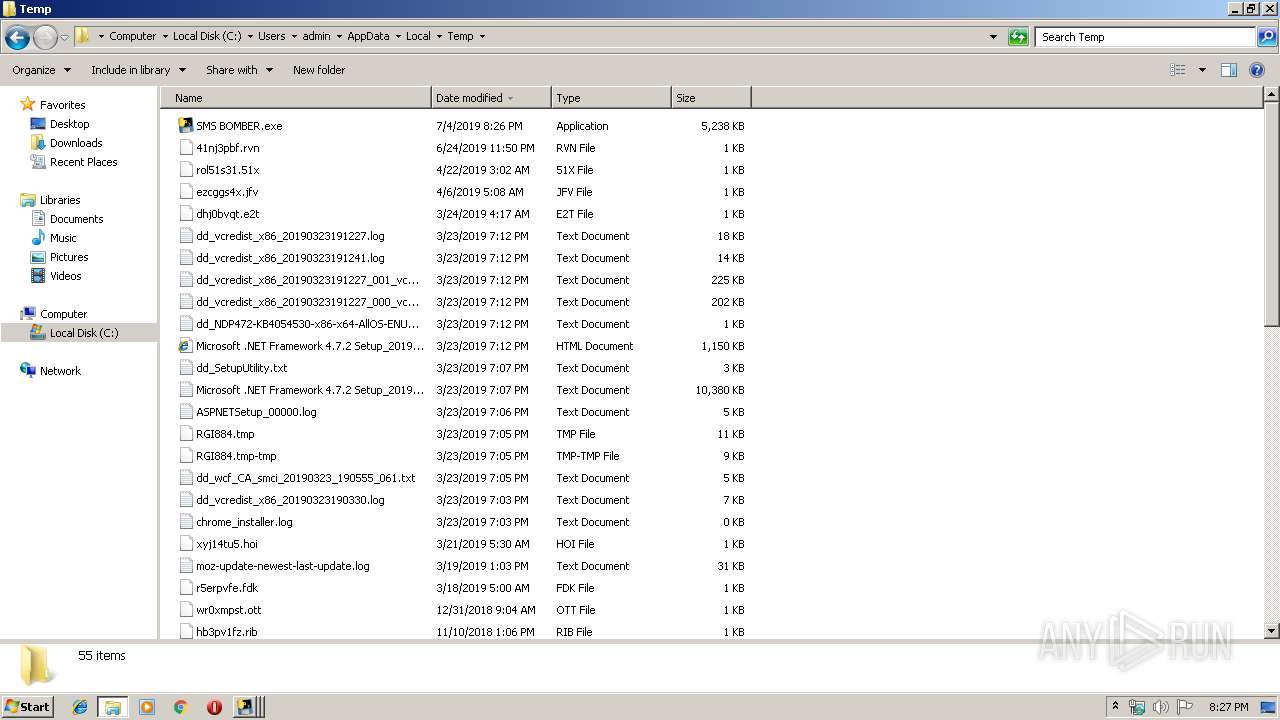
Total processes
55
Monitored processes
12
Malicious processes
7
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2168 | "C:\Users\admin\AppData\Local\Temp\SMS BOMBER.exe" | C:\Users\admin\AppData\Local\Temp\SMS BOMBER.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2340 | "C:\Users\admin\AppData\Local\Temp\SMS BOMBER.exe" | C:\Users\admin\AppData\Local\Temp\SMS BOMBER.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2356 | "C:\Users\admin\AppData\Local\Temp\SMS BOMBER.exe" | C:\Users\admin\AppData\Local\Temp\SMS BOMBER.exe | SMS BOMBER.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2516 | "C:\Users\admin\AppData\Local\Temp\SMS BOMBER.exe" | C:\Users\admin\AppData\Local\Temp\SMS BOMBER.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2860 | "C:\Users\admin\AppData\Local\Temp\SMS BOMBER.exe" | C:\Users\admin\AppData\Local\Temp\SMS BOMBER.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3088 | "C:\Users\admin\AppData\Local\Temp\SMS BOMBER.exe" | C:\Users\admin\AppData\Local\Temp\SMS BOMBER.exe | SMS BOMBER.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3336 | "C:\Users\admin\AppData\Local\Temp\SMS BOMBER.exe" | C:\Users\admin\AppData\Local\Temp\SMS BOMBER.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3432 | "C:\Users\admin\AppData\Local\Temp\SMS BOMBER.exe" | C:\Users\admin\AppData\Local\Temp\SMS BOMBER.exe | SMS BOMBER.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3860 | "C:\Users\admin\AppData\Local\Temp\SMS BOMBER.exe" | C:\Users\admin\AppData\Local\Temp\SMS BOMBER.exe | SMS BOMBER.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3908 | "C:\Users\admin\AppData\Local\Temp\SMS BOMBER.exe" | C:\Users\admin\AppData\Local\Temp\SMS BOMBER.exe | SMS BOMBER.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
3 564
Read events
3 564
Write events
0
Delete events
0
Modification events
Executable files
78
Suspicious files
6
Text files
12
Unknown types
0
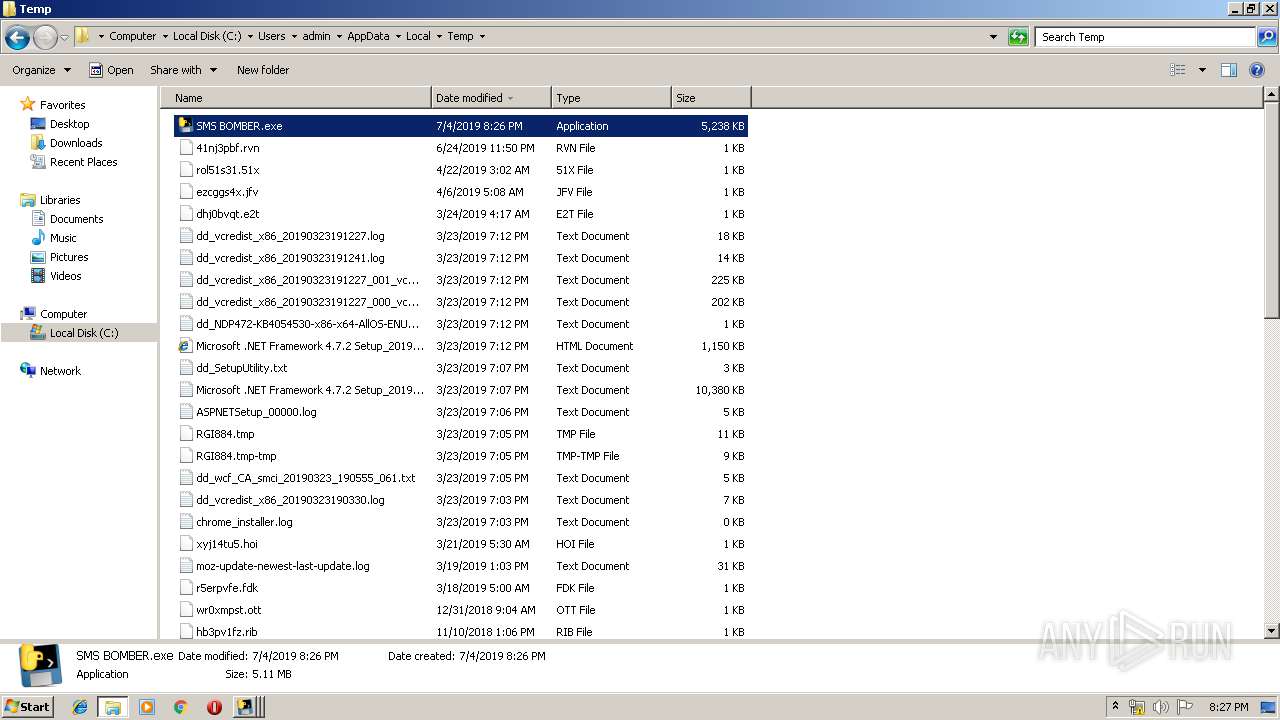
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3336 | SMS BOMBER.exe | C:\Users\admin\AppData\Local\Temp\_MEI33362\smsPRO.exe.manifest | xml | |
MD5:— | SHA256:— | |||
| 3336 | SMS BOMBER.exe | C:\Users\admin\AppData\Local\Temp\_MEI33362\base_library.zip | compressed | |
MD5:— | SHA256:— | |||
| 3336 | SMS BOMBER.exe | C:\Users\admin\AppData\Local\Temp\_MEI33362\VCRUNTIME140.dll | executable | |
MD5:AE96651CFBD18991D186A029CBECB30C | SHA256:1B372F064EACB455A0351863706E6326CA31B08E779A70DE5DE986B5BE8069A1 | |||
| 3336 | SMS BOMBER.exe | C:\Users\admin\AppData\Local\Temp\_MEI33362\_queue.pyd | executable | |
MD5:D46293D91BB845F8AB4F881C34921867 | SHA256:BA9641183C05FD2AC197508DCA02457142A18130BFF149BA3E9D68B6C1492C18 | |||
| 3336 | SMS BOMBER.exe | C:\Users\admin\AppData\Local\Temp\_MEI33362\_socket.pyd | executable | |
MD5:0281B1C65F282411916FB936DF7F7ECD | SHA256:89032E74EB1454BD3BEB212A7ED0AF0EF5D1589F06C793E8E49734DE69F2625A | |||
| 3336 | SMS BOMBER.exe | C:\Users\admin\AppData\Local\Temp\_MEI33362\select.pyd | executable | |
MD5:47EE76E87AB88AD190BD8B78029A4E8D | SHA256:8B4D0B17FDC351528ABFCCB8F0E56B7D10F9565FC1ECDC098E6A961C1EEDBEEF | |||
| 3336 | SMS BOMBER.exe | C:\Users\admin\AppData\Local\Temp\_MEI33362\libcrypto-1_1.dll | executable | |
MD5:25C4EBE7EB728EB40F9F9857849ABAD9 | SHA256:EE585C57129D29C67D1F038CA35113CE34319BFF1E8E163588E394DD096CD04A | |||
| 3336 | SMS BOMBER.exe | C:\Users\admin\AppData\Local\Temp\_MEI33362\_lzma.pyd | executable | |
MD5:2A8FFABBEC5E95F8A0BA388265FE57F3 | SHA256:1FE26E0940EADB05BAC03BBC553FD9011FDB0C067B8082B896C1D425D17F7542 | |||
| 2168 | SMS BOMBER.exe | C:\Users\admin\AppData\Local\Temp\_MEI21682\VCRUNTIME140.dll | executable | |
MD5:AE96651CFBD18991D186A029CBECB30C | SHA256:1B372F064EACB455A0351863706E6326CA31B08E779A70DE5DE986B5BE8069A1 | |||
| 3336 | SMS BOMBER.exe | C:\Users\admin\AppData\Local\Temp\_MEI33362\unicodedata.pyd | executable | |
MD5:765A3E54BEDC6D9E87BB1A031D8C3A40 | SHA256:346D37C10FD61D518FDD38E96D2942A2AF3A5BD27710C76FCE6B106525533131 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
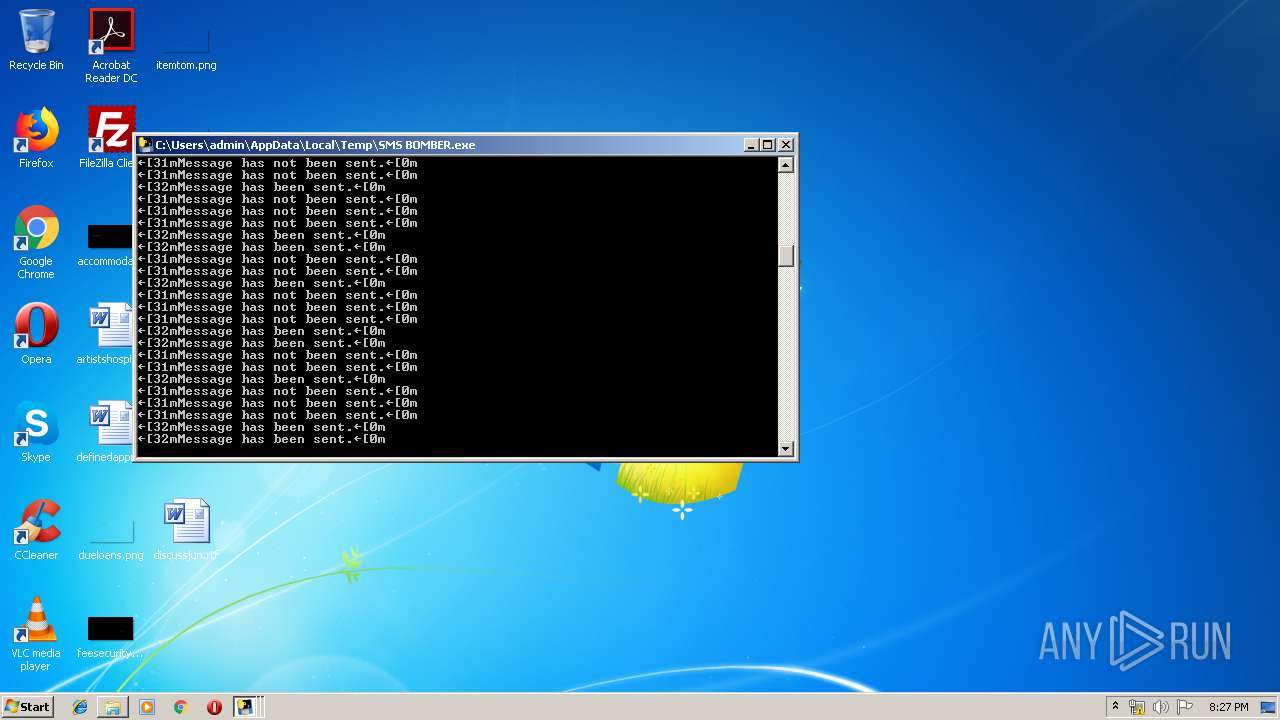
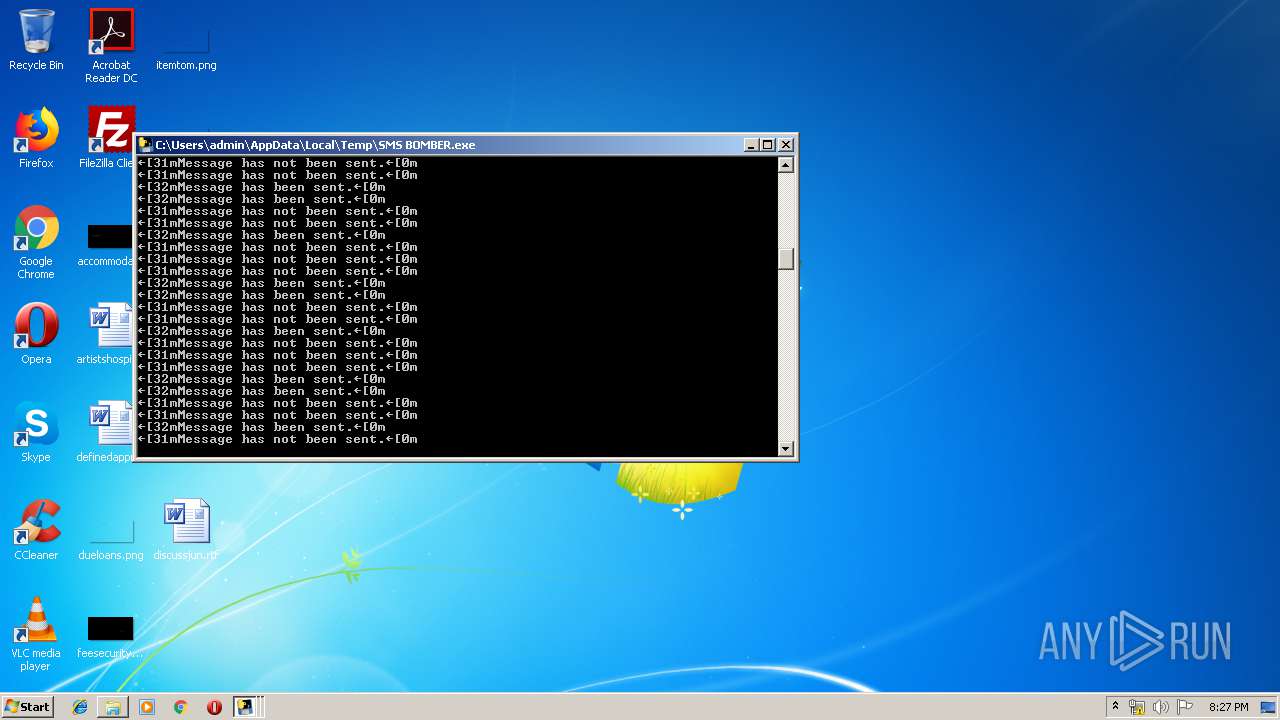
HTTP(S) requests
0
TCP/UDP connections
1 765
DNS requests
24
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2356 | SMS BOMBER.exe | 5.189.229.142:443 | drugvokrug.ru | Netversor GmbH | GB | unknown |
2356 | SMS BOMBER.exe | 194.106.216.70:443 | api.fex.net | TOV IT-Park | UA | unknown |
2356 | SMS BOMBER.exe | 93.158.193.239:443 | b.utair.ru | Stack Group, LLC | RU | unknown |
2356 | SMS BOMBER.exe | 212.53.35.240:443 | register.sipnet.ru | Tario Communications CJSC | RU | unknown |
2356 | SMS BOMBER.exe | 213.180.204.24:443 | passport.yandex.com | YANDEX LLC | RU | whitelisted |
4044 | SMS BOMBER.exe | 5.189.229.142:443 | drugvokrug.ru | Netversor GmbH | GB | unknown |
4044 | SMS BOMBER.exe | 93.158.193.239:443 | b.utair.ru | Stack Group, LLC | RU | unknown |
4044 | SMS BOMBER.exe | 5.45.217.7:443 | m.taxi.yandex.ru | YANDEX LLC | RU | whitelisted |
4044 | SMS BOMBER.exe | 52.76.178.100:443 | p.grabtaxi.com | Amazon.com, Inc. | SG | unknown |
4044 | SMS BOMBER.exe | 5.200.46.144:443 | api-production.viasat.ru | OOO IT-Grad | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.fex.net |
| unknown |
api-production.viasat.ru |
| unknown |
drugvokrug.ru |
| whitelisted |
b.utair.ru |
| unknown |
p.grabtaxi.com |
| unknown |
m.taxi.yandex.ru |
| whitelisted |
register.sipnet.ru |
| unknown |
passport.yandex.com |
| whitelisted |