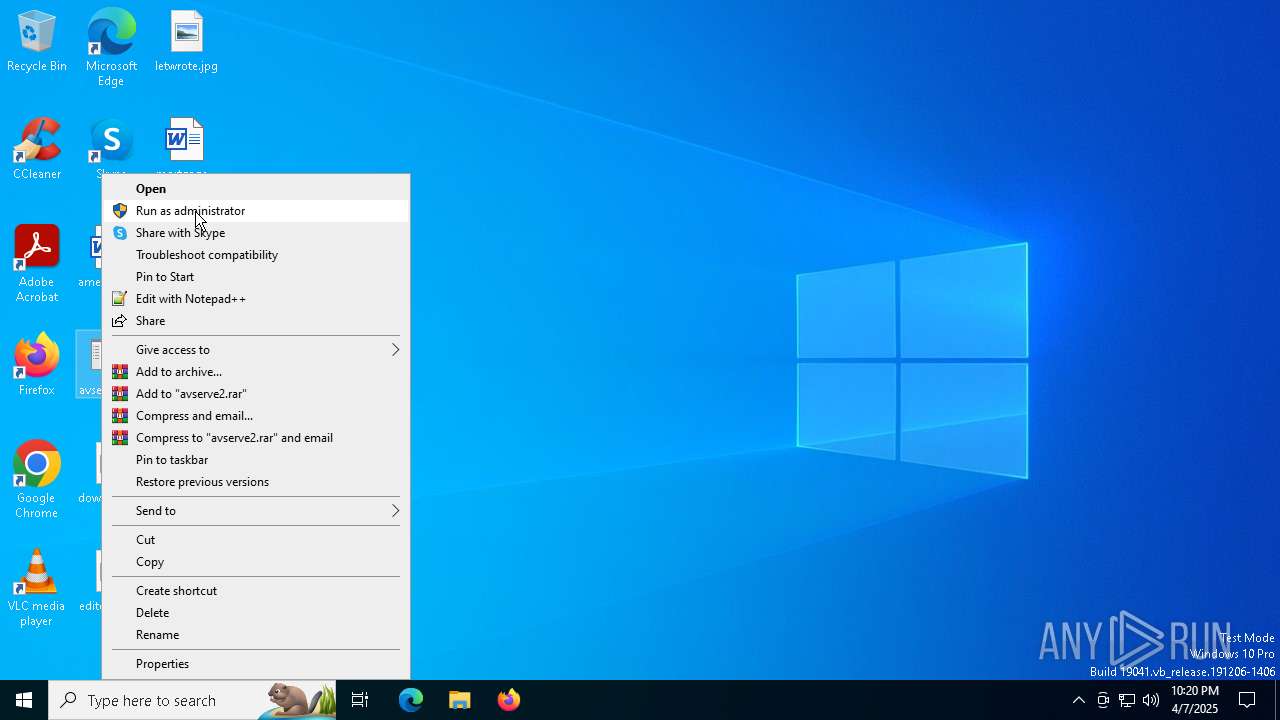
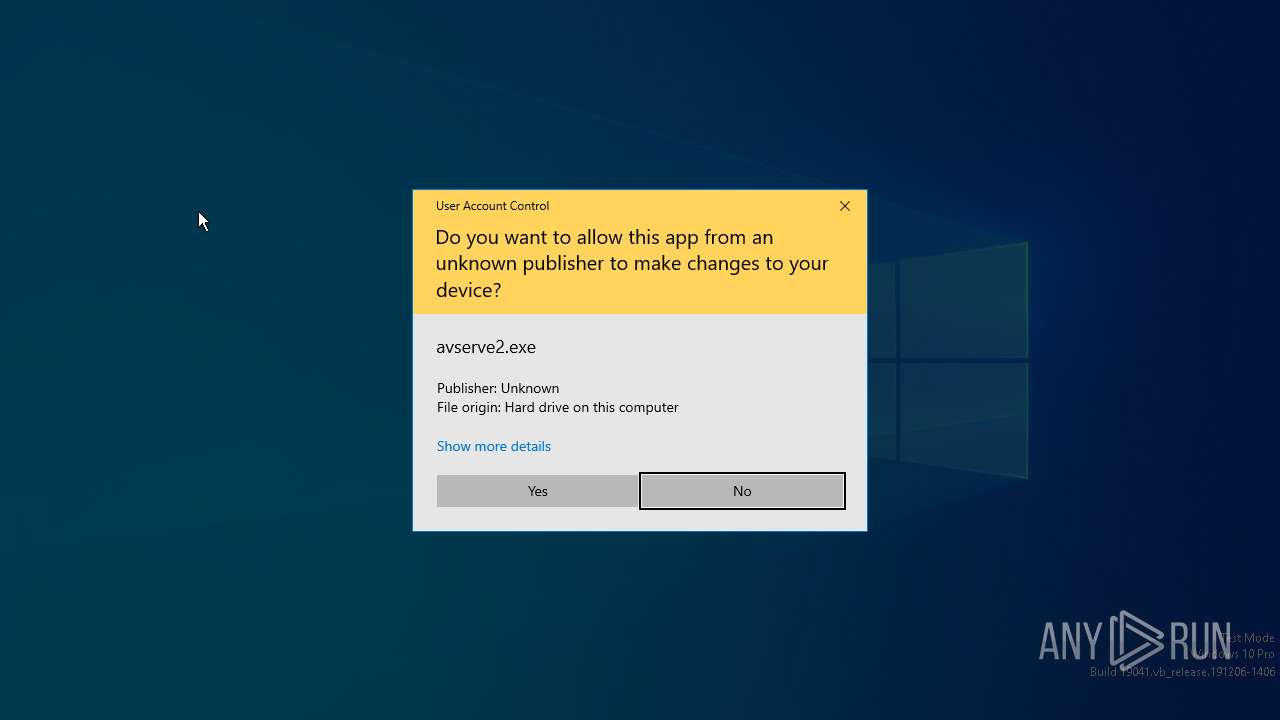
| File name: | avserve2.exe |
| Full analysis: | https://app.any.run/tasks/824a9a12-2173-43b2-829f-1521c3ac0556 |
| Verdict: | Malicious activity |
| Analysis date: | April 07, 2025, 22:19:25 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 2 sections |
| MD5: | 1F696B30880212766A804A20F6C52751 |
| SHA1: | FCF4AC36389157BBEFAFA965BA60BED5CEE22E2F |
| SHA256: | 06307940C98403DC0967007650E26C59DD79B04086B02D9531870DBCE03BF182 |
| SSDEEP: | 768:jkOoN//LRnQ+mdqJmeZvkkTlVj2GAGlpqh7ZIMOZ:jWN//LRn+dqJmgcwlUGA3h7ZIMOZ |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2004:05:01 18:07:32+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 15872 |
| InitializedDataSize: | 8704 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x19010 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
11
Monitored processes
0
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
11 732
DNS requests
25
Threats
57
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 192.168.191.54:445 | — | — | — | unknown |
— | — | 192.168.80.83:445 | — | — | — | unknown |
— | — | 96.108.154.218:445 | — | COMCAST-7922 | US | unknown |
— | — | 106.152.245.129:445 | — | KDDI CORPORATION | JP | unknown |
— | — | 192.168.151.31:445 | — | — | — | unknown |
— | — | 110.108.232.192:445 | — | China TieTong Telecommunications Corporation | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers inside a home network |
— | — | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers outside a home network |
— | — | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers inside a home network |
— | — | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers outside a home network |
— | — | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers outside a home network |
— | — | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers outside a home network |
— | — | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers outside a home network |
— | — | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers outside a home network |
— | — | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers outside a home network |
— | — | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers inside a home network |