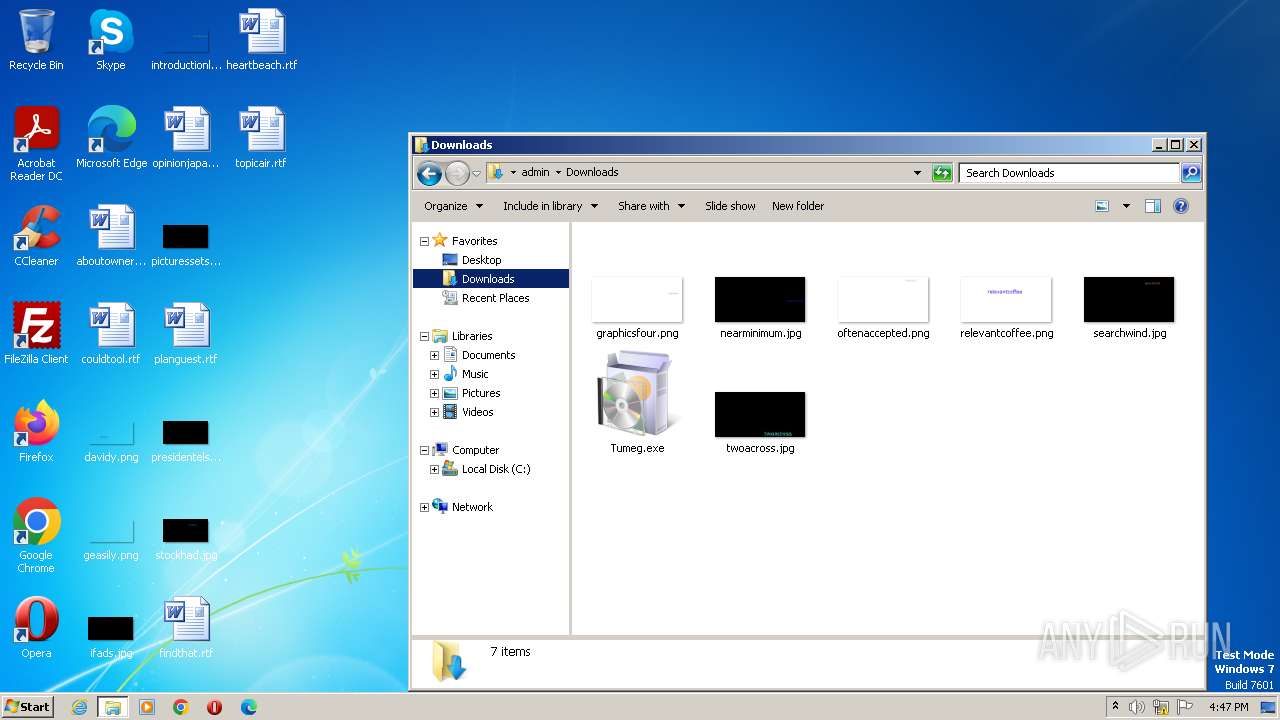
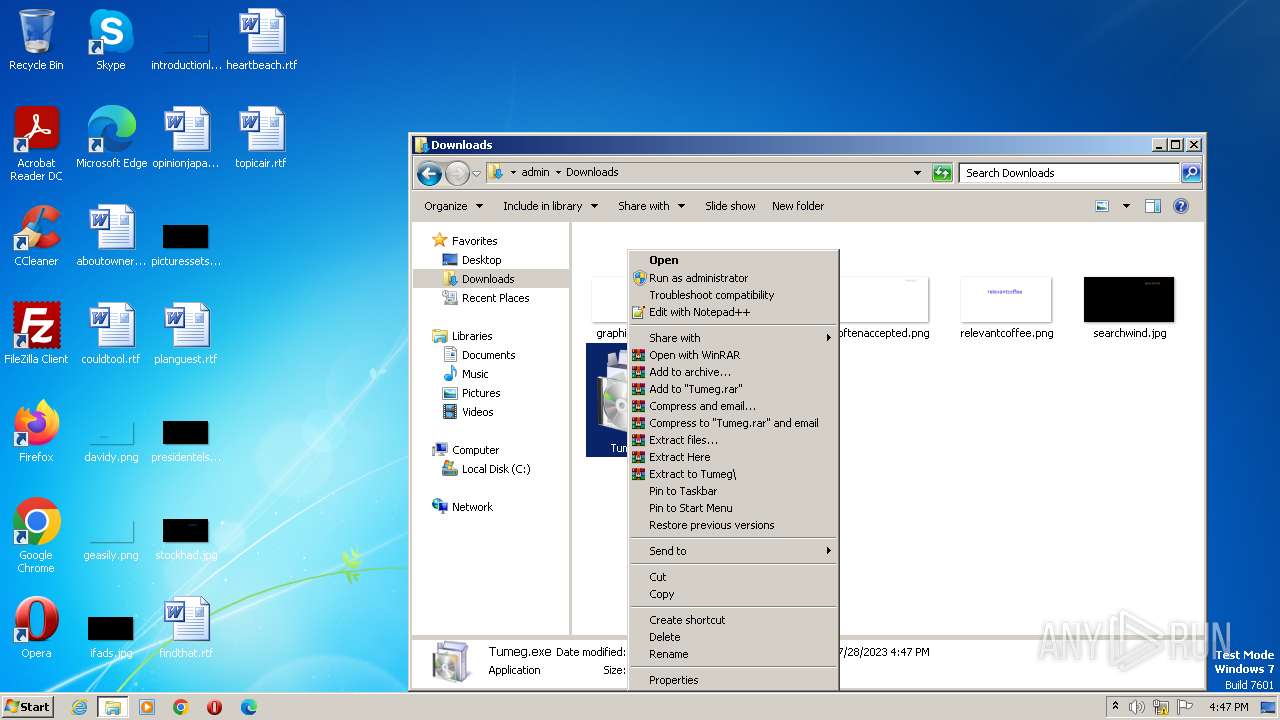
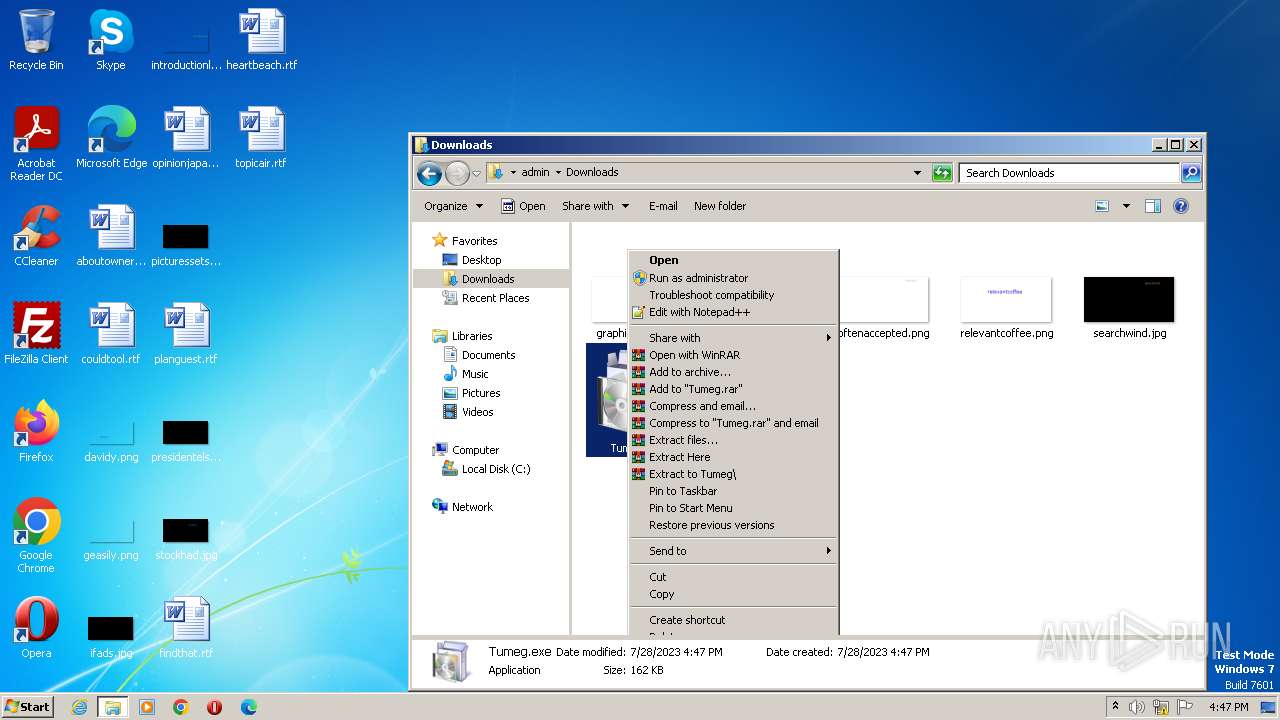
| download: | Tumeg.exe |
| Full analysis: | https://app.any.run/tasks/560e8abf-6d73-4b83-b0f7-2f2a62722cdd |
| Verdict: | Malicious activity |
| Analysis date: | July 28, 2023, 15:47:34 |
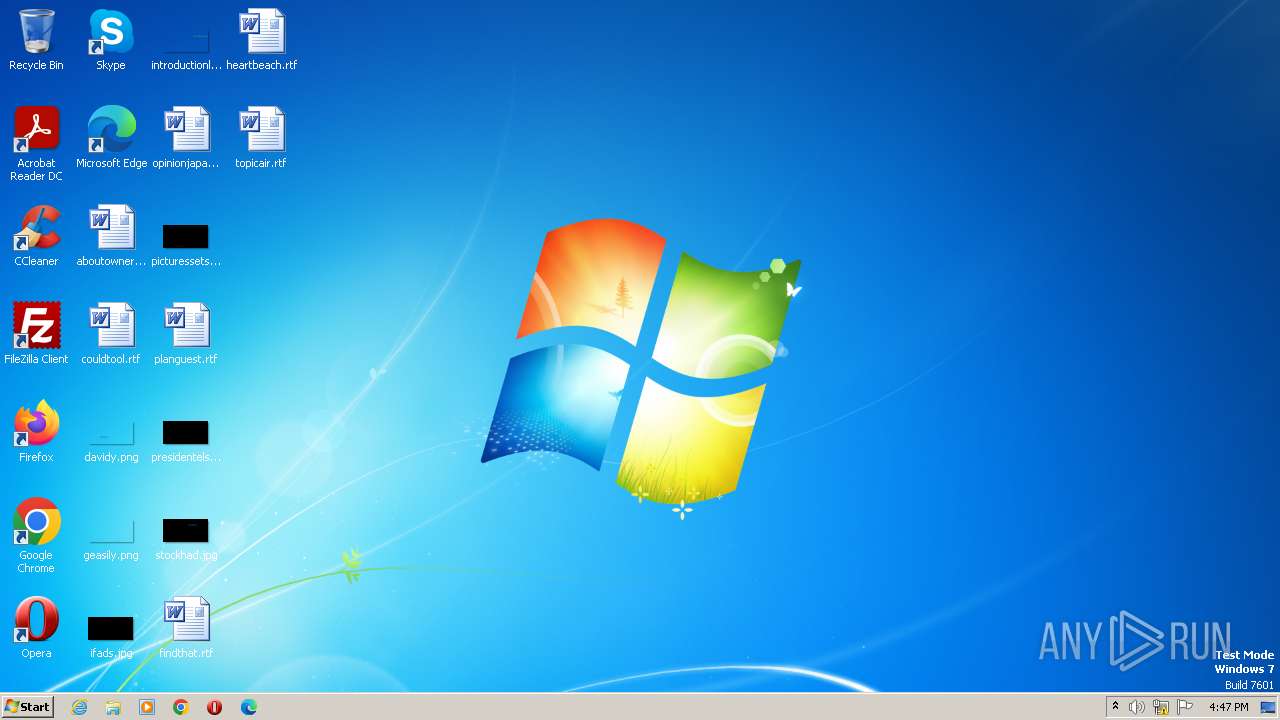
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E5655066C86F74F6B444F66F3222CE07 |
| SHA1: | C9F8053202994EE734ECD76D09B56F57F539102E |
| SHA256: | 062DE0A9FA284C56323CCAA5CF9B4A70801234B129744E1DEF53B29A7A86B8CD |
| SSDEEP: | 3072:5eFRQGCIIm1xn5GWp1icKAArDZz4N9GhbkrNEk4fH7YEqZuk8Ox:CQGCIImNp0yN90QE7fUv |
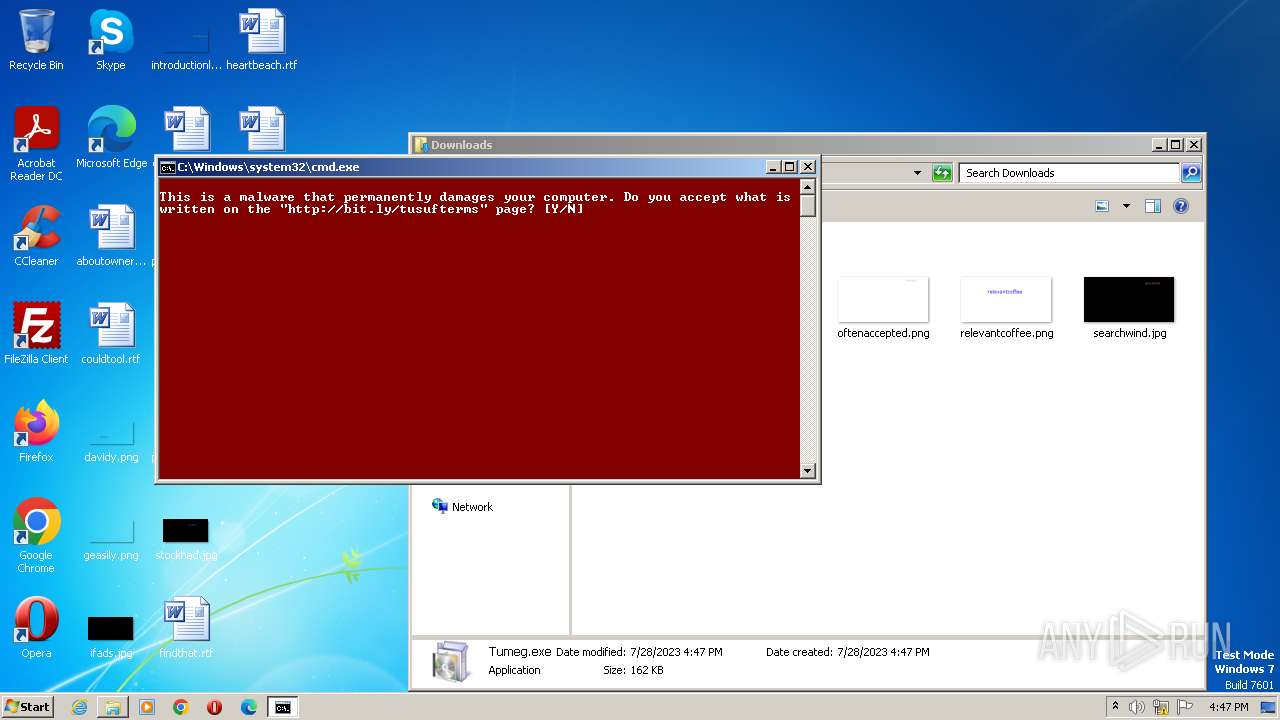
MALICIOUS
Actions looks like stealing of personal data
- icacls.exe (PID: 3044)
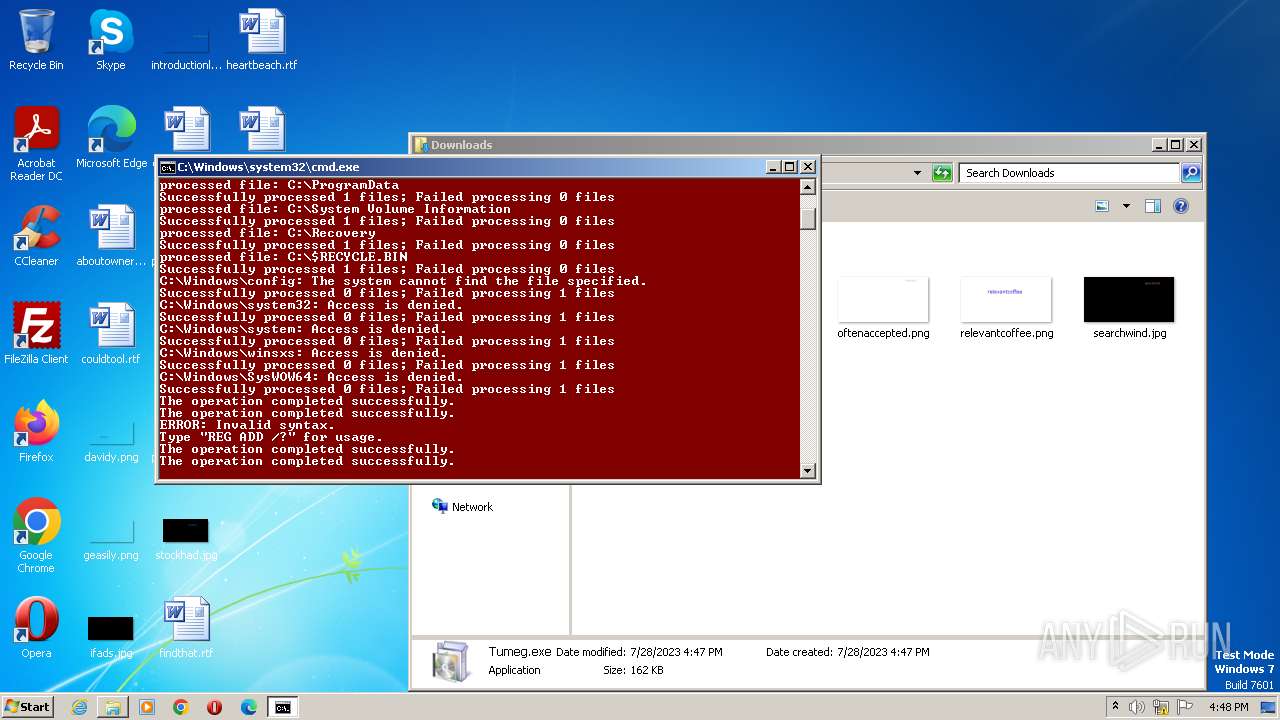
Creates a writable file the system directory
- cmd.exe (PID: 3080)
Disables Windows Defender
- reg.exe (PID: 3052)
Changes the autorun value in the registry
- reg.exe (PID: 2544)
- reg.exe (PID: 3216)
- reg.exe (PID: 880)
SUSPICIOUS
Starts CMD.EXE for commands execution
- Tumeg.exe (PID: 1004)
- Tumeg.exe (PID: 2880)
- cmd.exe (PID: 3080)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2908)
Executing commands from a ".bat" file
- Tumeg.exe (PID: 1004)
- Tumeg.exe (PID: 2880)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 3080)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 3080)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3080)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3080)
The process executes VB scripts
- cmd.exe (PID: 3080)
Reads the Internet Settings
- cmd.exe (PID: 3080)
- wscript.exe (PID: 3128)
- WMIC.exe (PID: 188)
Application launched itself
- cmd.exe (PID: 3080)
Starts SC.EXE for service management
- cmd.exe (PID: 3080)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 3080)
Process uses IPCONFIG to get network configuration information
- cmd.exe (PID: 2516)
Uses WMIC.EXE to obtain user accounts information
- cmd.exe (PID: 2404)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2516)
Uses NSLOOKUP.EXE to check DNS info
- cmd.exe (PID: 3092)
Checks for external IP
- nslookup.exe (PID: 3060)
Get information on the list of running processes
- cmd.exe (PID: 3080)
INFO
Create files in a temporary directory
- Tumeg.exe (PID: 1004)
- Tumeg.exe (PID: 2880)
Checks supported languages
- Tumeg.exe (PID: 1004)
- Tumeg.exe (PID: 2880)
- mode.com (PID: 3328)
- wmpnscfg.exe (PID: 292)
- wmpnscfg.exe (PID: 2500)
- wmpnscfg.exe (PID: 3904)
The process checks LSA protection
- explorer.exe (PID: 3292)
- icacls.exe (PID: 3044)
- taskkill.exe (PID: 2776)
- icacls.exe (PID: 3672)
- icacls.exe (PID: 3336)
- cscript.exe (PID: 2604)
- cscript.exe (PID: 2968)
- cscript.exe (PID: 2540)
- cscript.exe (PID: 3232)
- icacls.exe (PID: 3956)
- icacls.exe (PID: 2108)
- icacls.exe (PID: 3556)
- icacls.exe (PID: 2676)
- icacls.exe (PID: 1216)
- icacls.exe (PID: 4064)
- icacls.exe (PID: 1688)
- taskkill.exe (PID: 2844)
- explorer.exe (PID: 3264)
- cscript.exe (PID: 2348)
- cscript.exe (PID: 1856)
- cscript.exe (PID: 3904)
- cscript.exe (PID: 2000)
- cscript.exe (PID: 2408)
- cscript.exe (PID: 3220)
- cscript.exe (PID: 2936)
- cscript.exe (PID: 3728)
- cscript.exe (PID: 2608)
- cscript.exe (PID: 2000)
- cscript.exe (PID: 3344)
- cscript.exe (PID: 3036)
- cscript.exe (PID: 1648)
- cscript.exe (PID: 2320)
- cscript.exe (PID: 680)
- cscript.exe (PID: 2976)
- WMIC.exe (PID: 188)
- wmpnscfg.exe (PID: 292)
- wmpnscfg.exe (PID: 2500)
- wmpnscfg.exe (PID: 3904)
Manual execution by a user
- Tumeg.exe (PID: 2880)
- explorer.exe (PID: 3292)
Application launched itself
- msedge.exe (PID: 2064)
- msedge.exe (PID: 2964)
- msedge.exe (PID: 3000)
- msedge.exe (PID: 1896)
- msedge.exe (PID: 2608)
- msedge.exe (PID: 2944)
- msedge.exe (PID: 2972)
- msedge.exe (PID: 128)
- msedge.exe (PID: 2524)
- msedge.exe (PID: 2092)
- msedge.exe (PID: 3680)
- msedge.exe (PID: 3448)
- msedge.exe (PID: 3476)
- msedge.exe (PID: 2664)
- msedge.exe (PID: 1644)
Reads security settings of Internet Explorer
- cscript.exe (PID: 2604)
- cscript.exe (PID: 2540)
- cscript.exe (PID: 2968)
- cscript.exe (PID: 3232)
- cscript.exe (PID: 1856)
- cscript.exe (PID: 2348)
- cscript.exe (PID: 3904)
- cscript.exe (PID: 2000)
- cscript.exe (PID: 2408)
- cscript.exe (PID: 3728)
- cscript.exe (PID: 3220)
- cscript.exe (PID: 2936)
- cscript.exe (PID: 2608)
- cscript.exe (PID: 2000)
- cscript.exe (PID: 3344)
- cscript.exe (PID: 3036)
- cscript.exe (PID: 2976)
- cscript.exe (PID: 1648)
- cscript.exe (PID: 2320)
- cscript.exe (PID: 680)
Reads the Internet Settings
- explorer.exe (PID: 3264)
Reads the computer name
- wmpnscfg.exe (PID: 2500)
- wmpnscfg.exe (PID: 292)
- wmpnscfg.exe (PID: 3904)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 292)
- wmpnscfg.exe (PID: 2500)
- wmpnscfg.exe (PID: 3904)
Creates files in the program directory
- msedge.exe (PID: 2964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 MS Cabinet Self-Extractor (WExtract stub) (86.7) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (8.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.8) |
| .exe | | | Win32 Executable (generic) (1.2) |
| .exe | | | Generic Win/DOS Executable (0.5) |
EXIF
EXE
| ProductVersion: | 11.00.9600.16428 |
|---|---|
| ProductName: | Internet Explorer |
| OriginalFileName: | WEXTRACT.EXE .MUI |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| InternalName: | Wextract |
| FileVersion: | 11.00.9600.16428 (winblue_gdr.131013-1700) |
| FileDescription: | Win32 Cabinet Self-Extractor |
| CompanyName: | Microsoft Corporation |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 11.0.9600.16428 |
| FileVersionNumber: | 11.0.9600.16428 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | 6.3 |
| OSVersion: | 6.3 |
| EntryPoint: | 0x67cc |
| UninitializedDataSize: | - |
| InitializedDataSize: | 138752 |
| CodeSize: | 26112 |
| LinkerVersion: | 11 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2013:10:14 05:50:27+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Oct-2013 05:50:27 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Kabin Ayıklayıcısı |
| FileVersion: | 11.00.9600.16428 (winblue_gdr.131013-1700) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. Tüm hakları saklıdır. |
| OriginalFilename: | WEXTRACT.EXE .MUI |
| ProductName: | Internet Explorer |
| ProductVersion: | 11.00.9600.16428 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 14-Oct-2013 05:50:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000065CC | 0x00006600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.3849 |
.data | 0x00008000 | 0x00001A8C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.17593 |
.idata | 0x0000A000 | 0x00001078 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04858 |
.rsrc | 0x0000C000 | 0x00020000 | 0x0001F400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.87528 |
.reloc | 0x0002C000 | 0x000013AE | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.72277 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05393 | 1511 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.15864 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.07737 | 488 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.50949 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.56662 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.94251 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.99361 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 3.37828 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 7.98515 | 55762 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 5.33023 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
Cabinet.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
VERSION.dll |
msvcrt.dll |
Total processes
368
Monitored processes
326
Malicious processes
2
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | wscript.exe "C:\type.vbs" " " | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 120 | wscript.exe "C:\type.vbs" "c" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
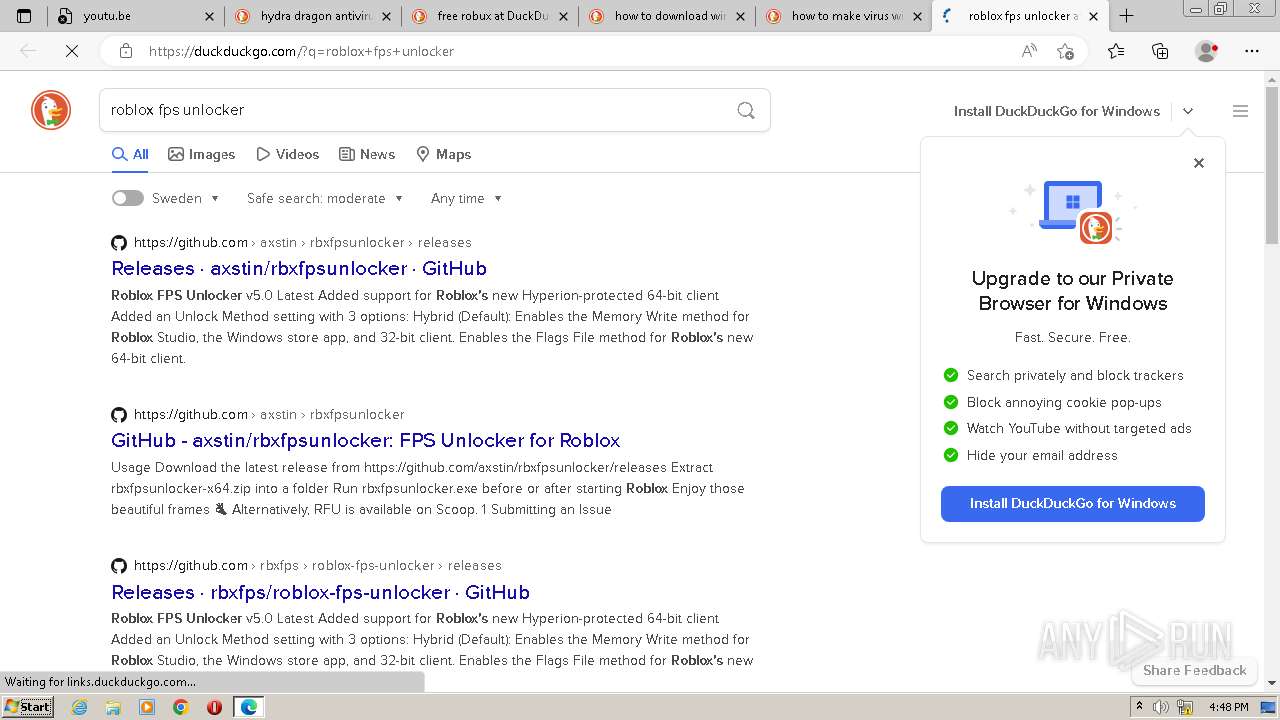
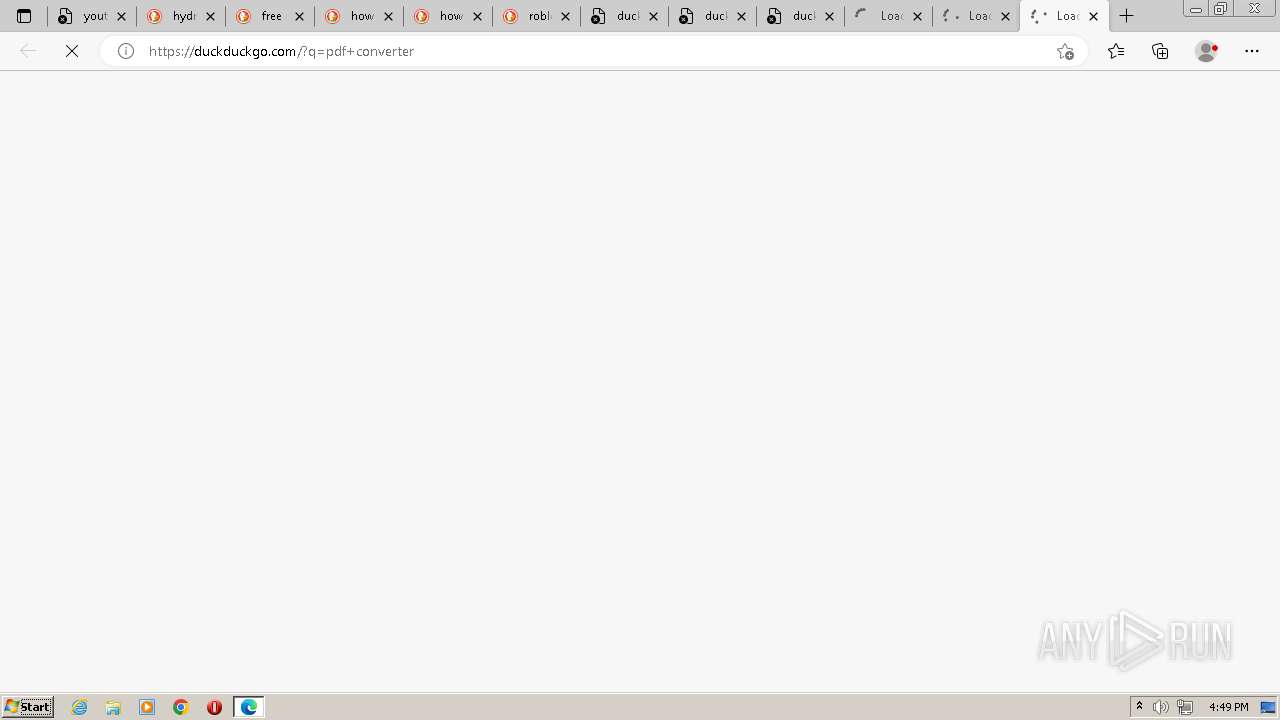
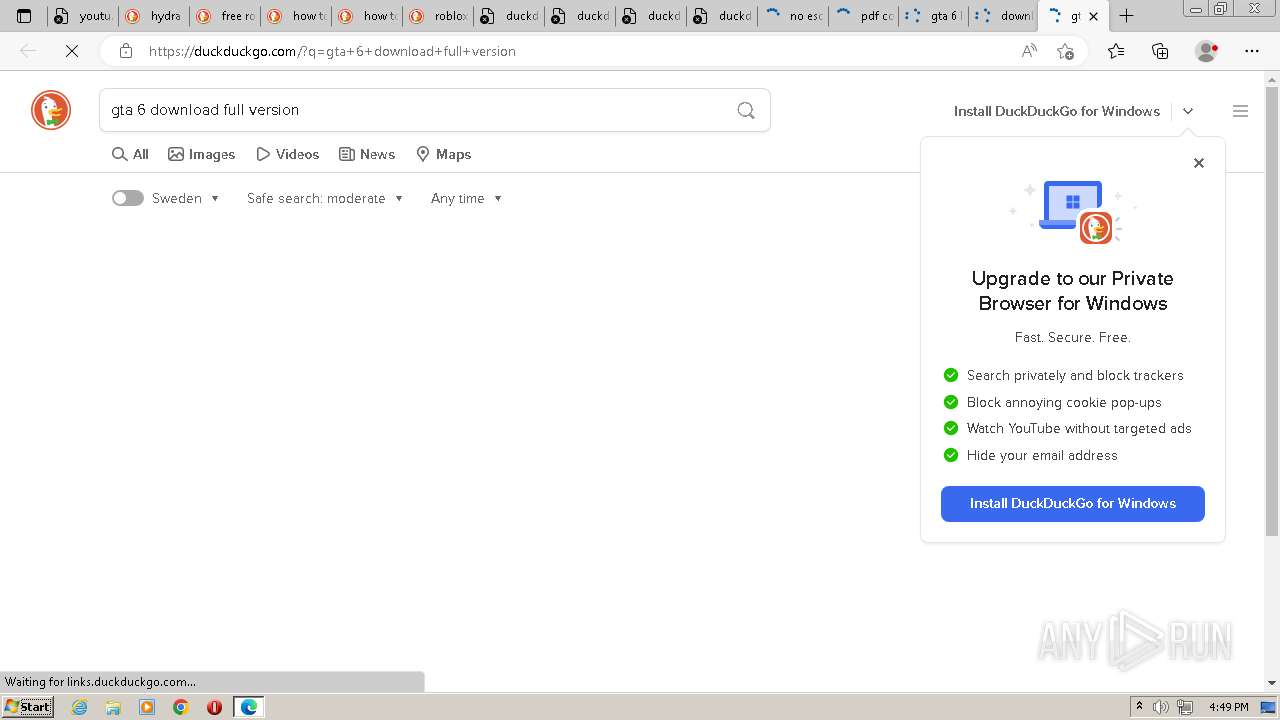
| 128 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --single-argument https://duckduckgo.com/?q=how+to+download+windows+12 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 148 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1624 --field-trial-handle=1160,i,12332076412776719067,4635840127474255466,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 188 | wmic useraccount where "Name='admin'" get Caption | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 188 | reg add "HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System" /v DisableTaskMgr /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 276 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3364 --field-trial-handle=1160,i,12332076412776719067,4635840127474255466,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 292 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 296 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0x128,0x7293f598,0x7293f5a8,0x7293f5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 | |||||||||||||||
| 300 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center" /v "AntiVirusOverride" /t REG_DWORD /d "1" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
18 067
Read events
17 787
Write events
262
Delete events
18
Modification events
| (PID) Process: | (1452) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop\WindowMetrics |
| Operation: | write | Name: | IconSpacing |
Value: -1125 | |||
| (PID) Process: | (2408) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop\WindowMetrics |
| Operation: | write | Name: | IconVerticalSpacing |
Value: -1125 | |||
| (PID) Process: | (1764) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop\WindowMetrics |
| Operation: | write | Name: | IconFont |
Value: F5FFFFFF0000000000000000000000009001000000000001000000005400610068006F006D00610000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3264) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3264) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | CleanShutdown |
Value: 0 | |||
| (PID) Process: | (3264) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{e1a82db3-a9f0-11e7-b142-806e6f6e6963} |
| Operation: | write | Name: | Data |
Value: 000000000DF0ADBA01000000080000000000008000000000000000300000000000000000FF00E703FF0000001600000084BAB9BC0400000000000000000000000000000000000000000000000000000000005C005C003F005C00530054004F005200410047004500230056006F006C0075006D00650023007B00330039006300390063006500660032002D0036003600380036002D0031003100650064002D0039006300320034002D003800300036006500360066003600650036003900360033007D002300300030003000300030003000300030003000300031003000300030003000300023007B00350033006600350036003300300064002D0062003600620066002D0031003100640030002D0039003400660032002D003000300061003000630039003100650066006200380062007D000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000005C005C003F005C0056006F006C0075006D0065007B00650031006100380032006400620033002D0061003900660030002D0031003100650037002D0062003100340032002D003800300036006500360066003600650036003900360033007D005C000000530079007300740065006D002000520065007300650072007600650064000000000000000000000000000000000000000000000000000000000000000000000000004E005400460053000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000 | |||
| (PID) Process: | (3264) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{e1a82db3-a9f0-11e7-b142-806e6f6e6963} |
| Operation: | write | Name: | Generation |
Value: 1 | |||
| (PID) Process: | (3264) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{e1a82db4-a9f0-11e7-b142-806e6f6e6963} |
| Operation: | write | Name: | Data |
Value: 000000000DF0ADBA41000000080000000000008000000000000000300000000000000000FF00E703FF000000160000004736BAC40440000001000000000000000000000000000000000000000000000000005C005C003F005C00530054004F005200410047004500230056006F006C0075006D00650023007B00330039006300390063006500660032002D0036003600380036002D0031003100650064002D0039006300320034002D003800300036006500360066003600650036003900360033007D002300300030003000300030003000300030003000360035003000300030003000300023007B00350033006600350036003300300064002D0062003600620066002D0031003100640030002D0039003400660032002D003000300061003000630039003100650066006200380062007D000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000005C005C003F005C0056006F006C0075006D0065007B00650031006100380032006400620034002D0061003900660030002D0031003100650037002D0062003100340032002D003800300036006500360066003600650036003900360033007D005C0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000004E005400460053000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000 | |||
| (PID) Process: | (3264) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{e1a82db4-a9f0-11e7-b142-806e6f6e6963} |
| Operation: | write | Name: | Generation |
Value: 1 | |||
| (PID) Process: | (2064) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
Executable files
0
Suspicious files
61
Text files
127
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Code Cache\js\4f1313d9dc46c086_0 | binary | |
MD5:691EBD126971C395F243453EEA4919B0 | SHA256:12D46FDC35FDF5AFCE6FE1D79A4EA9476274D3CA4A67A811DDE06C02CD427A3D | |||
| 1004 | Tumeg.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Tumeg.bat | text | |
MD5:6FD336E404C820CEA27C1AB6F627189C | SHA256:2E5731639E0F5EED877B8A6EFC4F765E0AFCF1065F5046F963ABCC9DF818A163 | |||
| 3080 | cmd.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\userinfo.txt | text | |
MD5:33A60F7C5CBEF8EE046E741B9C07B4D4 | SHA256:235346C43A8EC4712AFE7E96D175BE06330EDA2C0239C778B02A9AB26460ABE0 | |||
| 3080 | cmd.exe | C:\Users\admin\AppData\Local\Temp\f11.vbs | text | |
MD5:510673ACB174F67A52D761324580A0D0 | SHA256:7DBDD9E6D5D34DC8766E7A3AA09260F3A3C20E65B45189D9D9DE58BC92033E20 | |||
| 2964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\optimization_guide_hint_cache_store\LOG.old~RF17db5c.TMP | — | |
MD5:— | SHA256:— | |||
| 2964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\optimization_guide_hint_cache_store\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\optimization_guide_model_metadata_store\LOG.old~RF17db6c.TMP | — | |
MD5:— | SHA256:— | |||
| 2964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\optimization_guide_model_metadata_store\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\AutofillStrikeDatabase\LOG.old~RF17db7b.TMP | — | |
MD5:— | SHA256:— | |||
| 2964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\BudgetDatabase\LOG.old~RF17db8b.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
86
DNS requests
54
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2452 | msedge.exe | GET | 204 | 13.107.6.158:80 | http://edge-http.microsoft.com/captiveportal/generate_204 | US | — | — | whitelisted |
2452 | msedge.exe | GET | 204 | 13.107.6.158:80 | http://edge-http.microsoft.com/captiveportal/generate_204 | US | — | — | whitelisted |
860 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c05cb1de-4095-47e9-9aeb-6f81b6e7204b?P1=1691151079&P2=404&P3=2&P4=Jh4fjCvqyqSN3Gh7OR5ipU1hNZlakzbdeqdRZI5OpzNuyqNrsoXNgToLCgRJv1reDht3rhsUIGXdfSNb5wP1Hg%3d%3d | US | — | — | whitelisted |
860 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c6e779a0-da6d-4ac5-a811-faca5f1d5ab6?P1=1691151080&P2=404&P3=2&P4=dIuV0dsf%2fsZe%2fRt83j13hg1JqkxzISxa43VLlxWOH8sK%2bAiQYW3QTP6g7TDX0KILI%2b%2fNWxPDTJbpj3yEd9E6pw%3d%3d | US | binary | 13.5 Kb | whitelisted |
860 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a5d28923-29ce-4abc-9c53-b0badc436559?P1=1691151080&P2=404&P3=2&P4=J4GvqwqI%2bJErIiKqG24AxN6s08%2f38OHJW85p5ZIgNDoLjd2ie0kIw5o3%2bebVCRY2cfziEHCFgRwijk8eN4pkzw%3d%3d | US | binary | 2.15 Kb | whitelisted |
860 | svchost.exe | GET | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c6e779a0-da6d-4ac5-a811-faca5f1d5ab6?P1=1691151080&P2=404&P3=2&P4=dIuV0dsf%2fsZe%2fRt83j13hg1JqkxzISxa43VLlxWOH8sK%2bAiQYW3QTP6g7TDX0KILI%2b%2fNWxPDTJbpj3yEd9E6pw%3d%3d | US | binary | 2.15 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a5d28923-29ce-4abc-9c53-b0badc436559?P1=1691151080&P2=404&P3=2&P4=J4GvqwqI%2bJErIiKqG24AxN6s08%2f38OHJW85p5ZIgNDoLjd2ie0kIw5o3%2bebVCRY2cfziEHCFgRwijk8eN4pkzw%3d%3d | US | binary | 146 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a5d28923-29ce-4abc-9c53-b0badc436559?P1=1691151080&P2=404&P3=2&P4=J4GvqwqI%2bJErIiKqG24AxN6s08%2f38OHJW85p5ZIgNDoLjd2ie0kIw5o3%2bebVCRY2cfziEHCFgRwijk8eN4pkzw%3d%3d | US | binary | 1.18 Mb | whitelisted |
860 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a5d28923-29ce-4abc-9c53-b0badc436559?P1=1691151080&P2=404&P3=2&P4=J4GvqwqI%2bJErIiKqG24AxN6s08%2f38OHJW85p5ZIgNDoLjd2ie0kIw5o3%2bebVCRY2cfziEHCFgRwijk8eN4pkzw%3d%3d | US | binary | 1.40 Mb | whitelisted |
860 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a5d28923-29ce-4abc-9c53-b0badc436559?P1=1691151080&P2=404&P3=2&P4=J4GvqwqI%2bJErIiKqG24AxN6s08%2f38OHJW85p5ZIgNDoLjd2ie0kIw5o3%2bebVCRY2cfziEHCFgRwijk8eN4pkzw%3d%3d | US | binary | 693 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2640 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2452 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2964 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2452 | msedge.exe | 142.250.186.174:443 | youtu.be | GOOGLE | US | whitelisted |
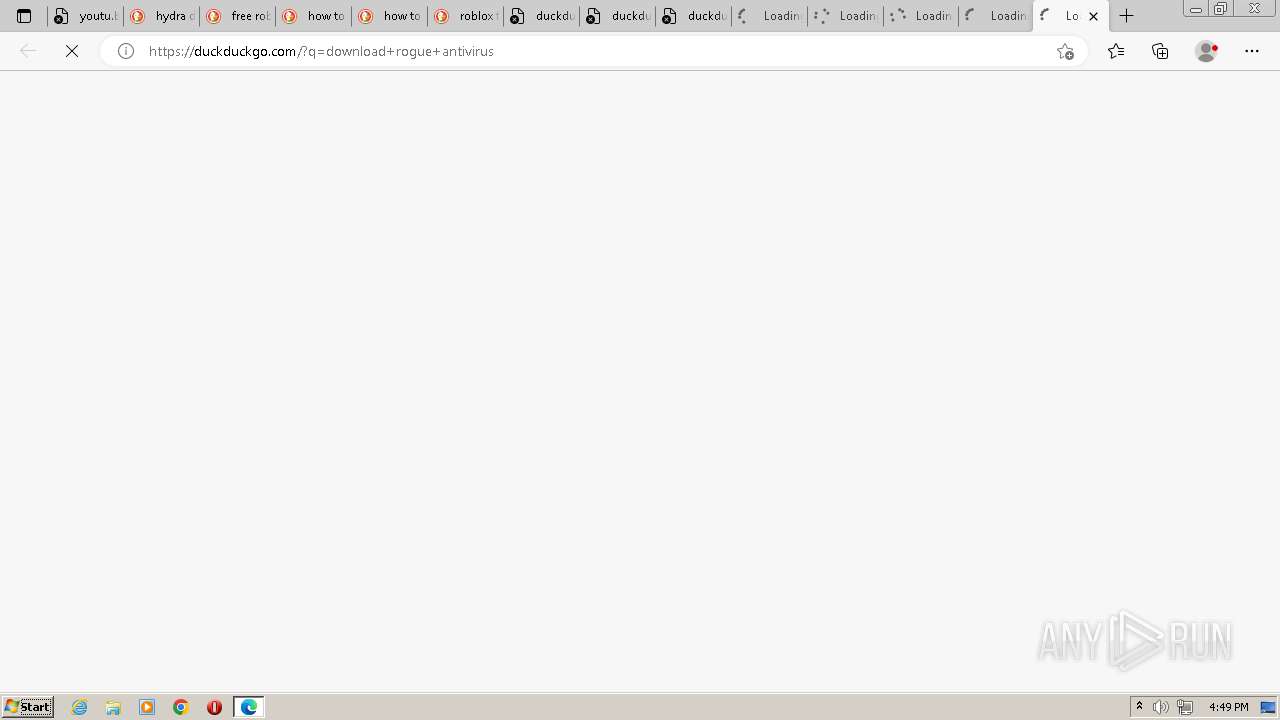
2452 | msedge.exe | 40.114.177.156:443 | duckduckgo.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | suspicious |
2452 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2452 | msedge.exe | 2.23.209.149:443 | www.bing.com | Akamai International B.V. | GB | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| malicious |
youtu.be |
| shared |
edge.microsoft.com |
| whitelisted |
duckduckgo.com |
| whitelisted |
resolver1.opendns.com |
| shared |
222.222.67.208.in-addr.arpa |
| unknown |
www.bing.com |
| whitelisted |
links.duckduckgo.com |
| whitelisted |
myip.opendns.com |
| shared |
external-content.duckduckgo.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3060 | nslookup.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup Domain (myip .opendns .com in DNS lookup) |
3060 | nslookup.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup Domain (myip .opendns .com in DNS lookup) |
Process | Message |
|---|---|
msedge.exe | [0728/164814.339:ERROR:exception_handler_server.cc(527)] ConnectNamedPipe: The pipe is being closed. (0xE8)
|
msedge.exe | [0728/164823.305:ERROR:exception_handler_server.cc(527)] ConnectNamedPipe: The pipe is being closed. (0xE8)
|
msedge.exe | [0728/164831.342:ERROR:exception_handler_server.cc(527)] ConnectNamedPipe: The pipe is being closed. (0xE8)
|
msedge.exe | [0728/164840.385:ERROR:exception_handler_server.cc(527)] ConnectNamedPipe: The pipe is being closed. (0xE8)
|
msedge.exe | [0728/164848.413:ERROR:exception_handler_server.cc(527)] ConnectNamedPipe: The pipe is being closed. (0xE8)
|
msedge.exe | [0728/164856.418:ERROR:exception_handler_server.cc(527)] ConnectNamedPipe: The pipe is being closed. (0xE8)
|
msedge.exe | [0728/164903.404:ERROR:exception_handler_server.cc(527)] ConnectNamedPipe: The pipe is being closed. (0xE8)
|
msedge.exe | [0728/164912.399:ERROR:exception_handler_server.cc(527)] ConnectNamedPipe: The pipe is being closed. (0xE8)
|
msedge.exe | [0728/164921.402:ERROR:exception_handler_server.cc(527)] ConnectNamedPipe: The pipe is being closed. (0xE8)
|
msedge.exe | [0728/164930.425:ERROR:exception_handler_server.cc(527)] ConnectNamedPipe: The pipe is being closed. (0xE8)
|