| File name: | wps_wid.cid-764651049.1762067712.exe |
| Full analysis: | https://app.any.run/tasks/e90f7786-0bb8-4c14-9102-390263a4332b |
| Verdict: | Malicious activity |
| Analysis date: | December 20, 2025, 06:56:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | DE331C6C3F329520B28E198482706950 |
| SHA1: | 8ED7DB2EF4FEBF6BEB965B98683332E1533DCDA5 |
| SHA256: | 0613B2F27D832CD91D5B4EA78B3112D95C4E41B28FC9B2399D599FB4DD63516E |
| SSDEEP: | 98304:VHs0FC8XVhfPVfBoJJd+d2efP5uksiKg1iBKtDl44KMWthu5yTK6Z1sMRzrp1Luk:zDKSoAwGs |
MALICIOUS
No malicious indicators.SUSPICIOUS
WPS mutex has been found
- wps_wid.cid-764651049.1762067712.exe (PID: 7608)
- b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe (PID: 5392)
Reads security settings of Internet Explorer
- wps_wid.cid-764651049.1762067712.exe (PID: 7608)
- b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe (PID: 5392)
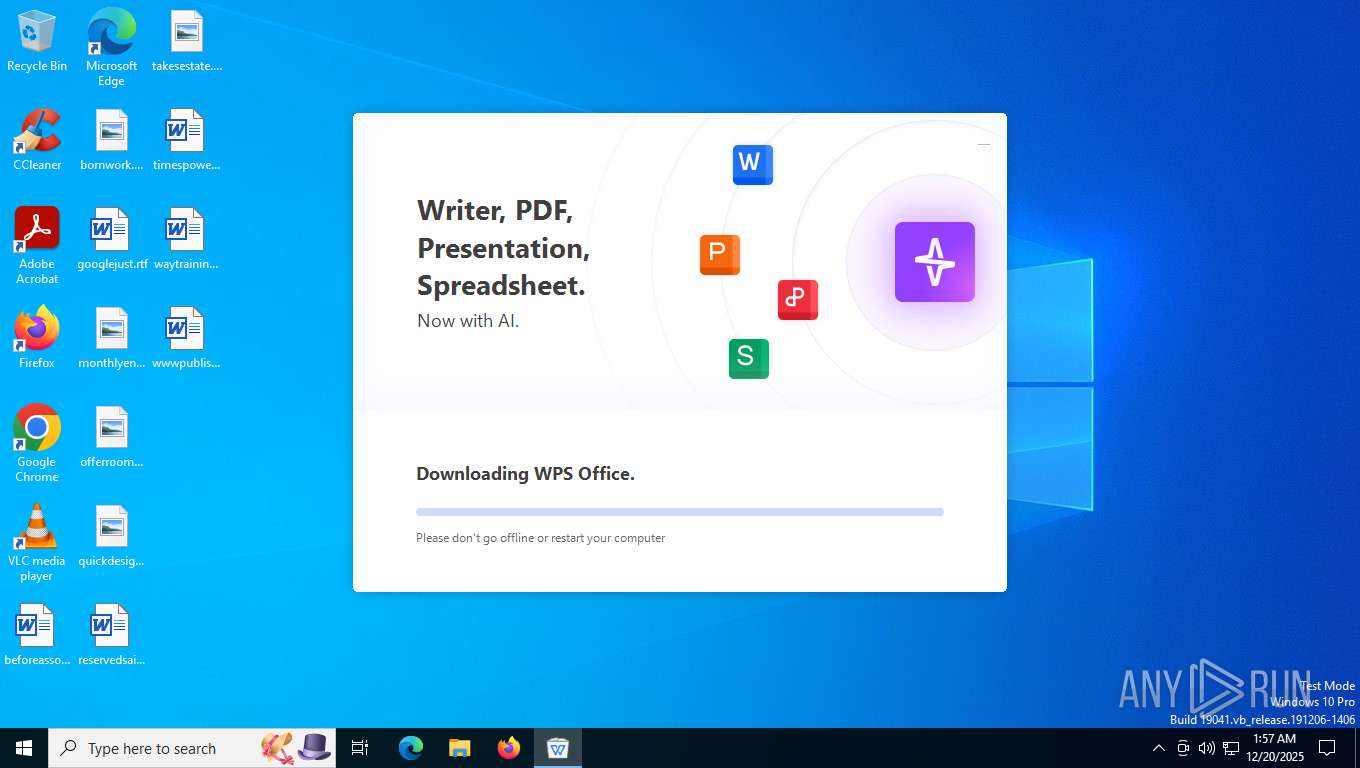
Process drops legitimate windows executable
- b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe (PID: 5392)
Executable content was dropped or overwritten
- b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe (PID: 5392)
The process drops C-runtime libraries
- b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe (PID: 5392)
The process checks if it is being run in the virtual environment
- b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe (PID: 5392)
INFO
Checks supported languages
- wps_wid.cid-764651049.1762067712.exe (PID: 7608)
- b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe (PID: 5392)
Reads the machine GUID from the registry
- wps_wid.cid-764651049.1762067712.exe (PID: 7608)
- b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe (PID: 5392)
Reads the computer name
- wps_wid.cid-764651049.1762067712.exe (PID: 7608)
- b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe (PID: 5392)
Creates files or folders in the user directory
- wps_wid.cid-764651049.1762067712.exe (PID: 7608)
- b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe (PID: 5392)
Process checks computer location settings
- wps_wid.cid-764651049.1762067712.exe (PID: 7608)
Creates files in the program directory
- wps_wid.cid-764651049.1762067712.exe (PID: 7608)
Checks proxy server information
- wps_wid.cid-764651049.1762067712.exe (PID: 7608)
Create files in a temporary directory
- b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe (PID: 5392)
The sample compiled with english language support
- b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe (PID: 5392)
The sample compiled with chinese language support
- b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe (PID: 5392)
The sample compiled with japanese language support
- b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe (PID: 5392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (3.6) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:11:28 02:56:30+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.29 |
| CodeSize: | 4228608 |
| InitializedDataSize: | 1533440 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2ba017 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 12.2.0.21570 |
| ProductVersionNumber: | 12.2.0.21570 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Zhuhai Kingsoft Office Software Co.,Ltd |
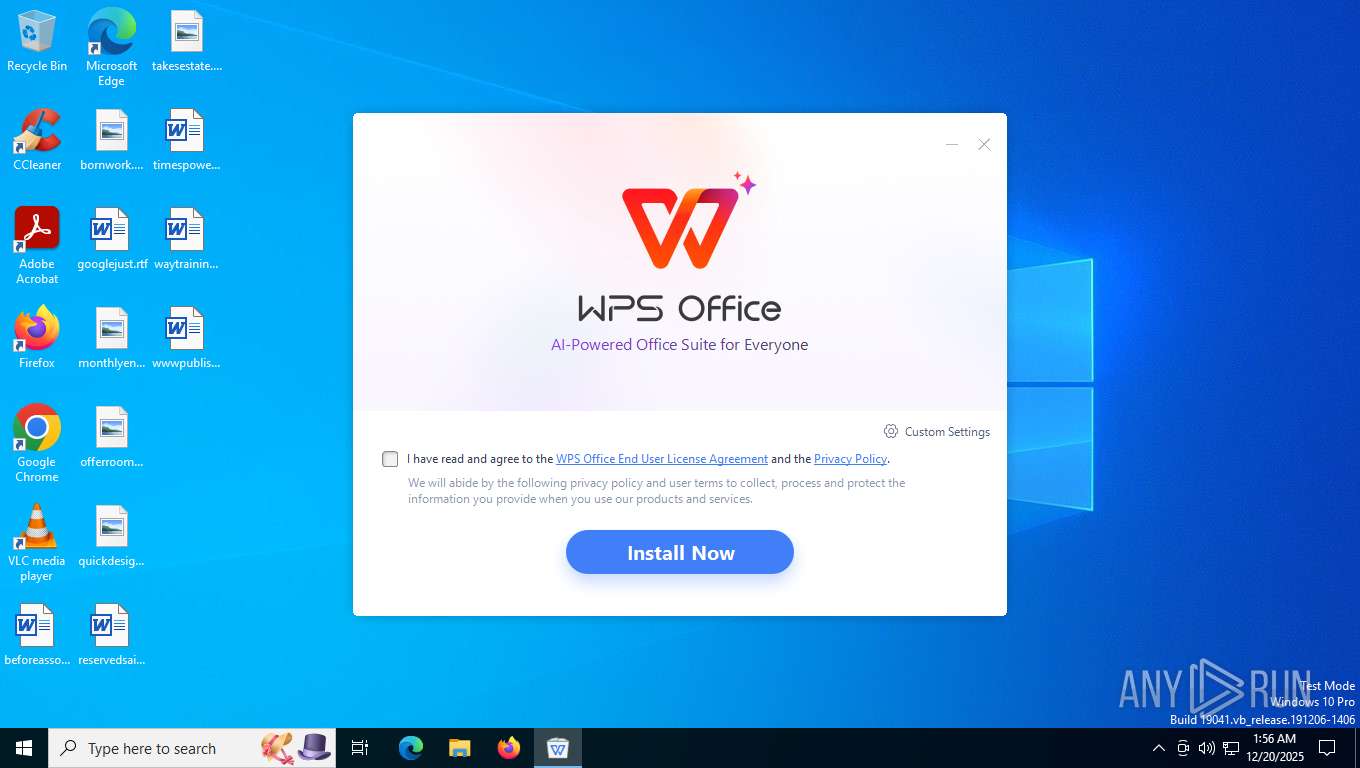
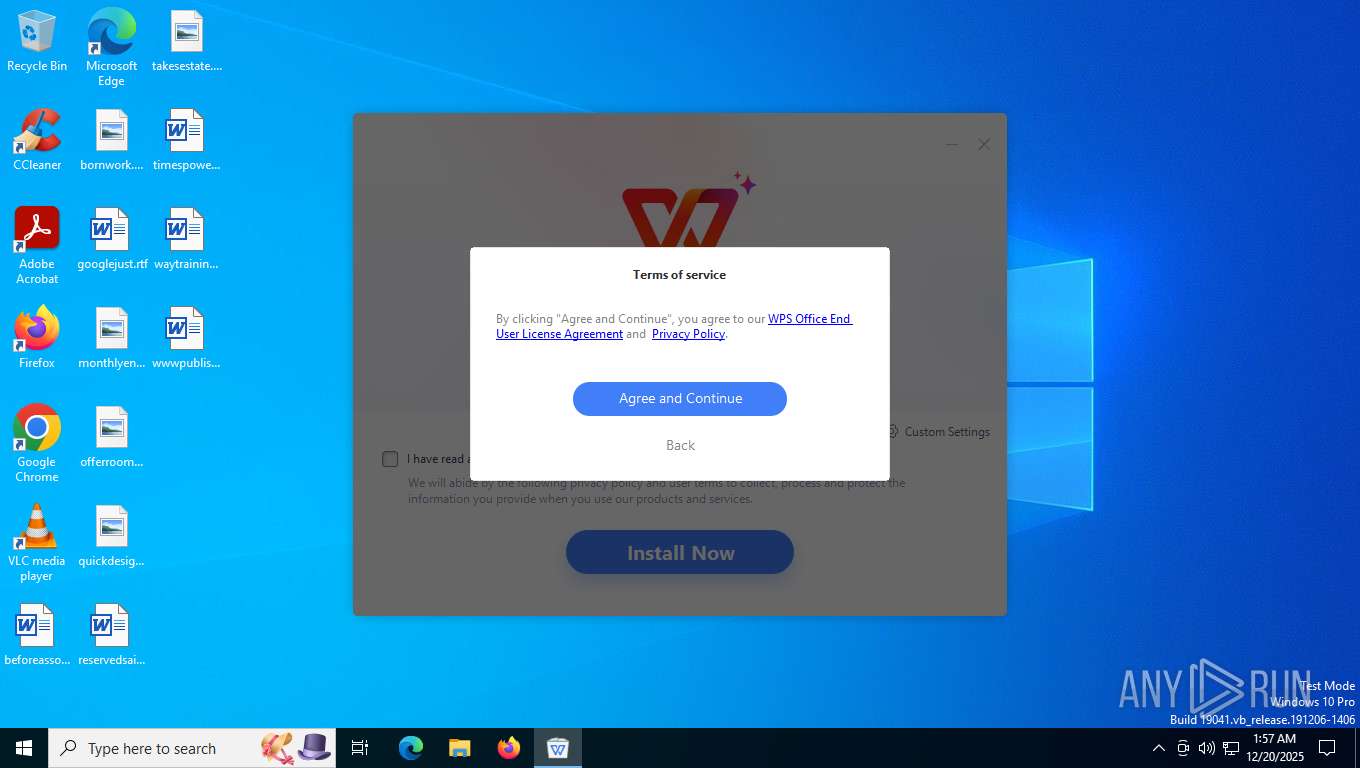
| FileDescription: | WPS Office Setup |
| FileVersion: | 12,2,0,21570 |
| InternalName: | konlinesetup_xa |
| LegalCopyright: | Copyright©2025 Kingsoft Corporation. All rights reserved. |
| OriginalFileName: | konlinesetup_xa.exe |
| ProductName: | WPS Office |
| ProductVersion: | 12,2,0,21570 |
| MIMEType: | - |
Total processes
145
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1948 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5392 | "C:\ProgramData\WPS\Installers\b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe" -installCallByOnlineSetup -defaultOpen -defaultOpenPdf -asso_pic_setup -createIcons -pinTaskbar -curlangofinstalledproduct=en_US -notElevateAndDirectlyInstall -D="C:\Users\admin\AppData\Local\Kingsoft\WPS Office" -enableSetupMuiPkg -appdata="C:\Users\admin\AppData\Roaming" | C:\ProgramData\WPS\Installers\b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe | wps_wid.cid-764651049.1762067712.exe | ||||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Install Application Version: 12,9,0,21549 Modules
| |||||||||||||||
| 7608 | "C:\Users\admin\AppData\Local\Temp\wps_wid.cid-764651049.1762067712.exe" | C:\Users\admin\AppData\Local\Temp\wps_wid.cid-764651049.1762067712.exe | explorer.exe | ||||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office Setup Version: 12,2,0,21570 Modules
| |||||||||||||||
Total events
15 172
Read events
15 145
Write events
24
Delete events
3
Modification events
| (PID) Process: | (7608) wps_wid.cid-764651049.1762067712.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\kingsoft\kwpsonlinesetup |
| Operation: | write | Name: | onlinesetup_penetrate_id_type |
Value: web | |||
| (PID) Process: | (7608) wps_wid.cid-764651049.1762067712.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\kingsoft\kwpsonlinesetup |
| Operation: | write | Name: | onlinesetup_penetrate_id |
Value: cid-764651049.1762067712 | |||
| (PID) Process: | (7608) wps_wid.cid-764651049.1762067712.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\kingsoft\kwpsonlinesetup |
| Operation: | write | Name: | startup_time |
Value: 2025-12-20 06 | |||
| (PID) Process: | (7608) wps_wid.cid-764651049.1762067712.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\kingsoft\kwpsonlinesetup |
| Operation: | write | Name: | global_progress |
Value: startup | |||
| (PID) Process: | (7608) wps_wid.cid-764651049.1762067712.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\kingsoft\kwpsonlinesetup |
| Operation: | write | Name: | infoGuid |
Value: A0B923D3A07446FEAC9752B4BFC66D99 | |||
| (PID) Process: | (7608) wps_wid.cid-764651049.1762067712.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\kingsoft\kwpsonlinesetup |
| Operation: | write | Name: | infoHdid |
Value: c06334219e9eab9dfd48f03400b059ad | |||
| (PID) Process: | (7608) wps_wid.cid-764651049.1762067712.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\kingsoft\Office\6.0\plugins\kdcsdk |
| Operation: | write | Name: | countrycode |
Value: DE | |||
| (PID) Process: | (7608) wps_wid.cid-764651049.1762067712.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\kingsoft\Office\6.0\plugins\kdcsdk |
| Operation: | write | Name: | lastupdatecountrycode |
Value: 1766213795239 | |||
| (PID) Process: | (7608) wps_wid.cid-764651049.1762067712.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\kingsoft\Office\6.0\plugins\kdcsdk |
| Operation: | write | Name: | lastUpdateDeviceInfoDate |
Value: 2025/12/20 | |||
| (PID) Process: | (7608) wps_wid.cid-764651049.1762067712.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\kingsoft\kwpsonlinesetup |
| Operation: | write | Name: | global_progress |
Value: download_start | |||
Executable files
67
Suspicious files
37
Text files
398
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7608 | wps_wid.cid-764651049.1762067712.exe | C:\ProgramData\WPS\Installers\b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe | — | |
MD5:— | SHA256:— | |||
| 5392 | b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe | C:\Users\admin\AppData\Local\Temp\wps\~10b5e4\CONTROL\prereadimages_et.txt | — | |
MD5:— | SHA256:— | |||
| 5392 | b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe | C:\Users\admin\AppData\Local\Temp\wps\~10b5e4\CONTROL\prereadimages_pdf.txt | — | |
MD5:— | SHA256:— | |||
| 5392 | b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe | C:\Users\admin\AppData\Local\Temp\wps\~10b5e4\CONTROL\prereadimages_prometheus.txt | — | |
MD5:— | SHA256:— | |||
| 5392 | b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe | C:\Users\admin\AppData\Local\Temp\wps\~10b5e4\CONTROL\prereadimages_prome_init.txt | — | |
MD5:— | SHA256:— | |||
| 5392 | b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe | C:\Users\admin\AppData\Local\Temp\wps\~10b5e4\CONTROL\prereadimages_qing.txt | — | |
MD5:— | SHA256:— | |||
| 5392 | b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe | C:\Users\admin\AppData\Local\Temp\wps\~10b5e4\CONTROL\prereadimages_wpp.txt | — | |
MD5:— | SHA256:— | |||
| 5392 | b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe | C:\Users\admin\AppData\Local\Temp\wps\~10b5e4\CONTROL\prereadimages_wps.txt | — | |
MD5:— | SHA256:— | |||
| 7608 | wps_wid.cid-764651049.1762067712.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:634B51DAA658BCACAE75C6CA29E576D6 | SHA256:EF9CDED36B9F886A05B5DBF242785FF69AFE70CCFB7CBB48DD77D24555066785 | |||
| 7608 | wps_wid.cid-764651049.1762067712.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:262D18FB9025F9415EB4432C6DBBDF84 | SHA256:C2C2D493ABA6588189B3D8085DA9F2B759B3FAFA92C92D7253229F675CF48F0C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
34
DNS requests
24
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7608 | wps_wid.cid-764651049.1762067712.exe | POST | 204 | 142.250.186.110:443 | https://www.google-analytics.com/mp/collect?firebase_app_id=1:463244832315:android:fe82dee1e0f73e232db61e&api_secret=UViz3S6KTv6YlgsE1g4FAQ | unknown | — | — | unknown |
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
7608 | wps_wid.cid-764651049.1762067712.exe | POST | 204 | 142.250.186.110:443 | https://www.google-analytics.com/mp/collect?firebase_app_id=1:463244832315:android:fe82dee1e0f73e232db61e&api_secret=UViz3S6KTv6YlgsE1g4FAQ | unknown | — | — | unknown |
7608 | wps_wid.cid-764651049.1762067712.exe | POST | 204 | 142.250.186.110:443 | https://www.google-analytics.com/mp/collect?firebase_app_id=1:463244832315:android:fe82dee1e0f73e232db61e&api_secret=UViz3S6KTv6YlgsE1g4FAQ | unknown | — | — | unknown |
7608 | wps_wid.cid-764651049.1762067712.exe | POST | 204 | 142.250.186.110:443 | https://www.google-analytics.com/mp/collect?firebase_app_id=1:463244832315:android:fe82dee1e0f73e232db61e&api_secret=UViz3S6KTv6YlgsE1g4FAQ | unknown | — | — | unknown |
7608 | wps_wid.cid-764651049.1762067712.exe | POST | 204 | 142.250.186.110:443 | https://www.google-analytics.com/mp/collect?firebase_app_id=1:463244832315:android:fe82dee1e0f73e232db61e&api_secret=UViz3S6KTv6YlgsE1g4FAQ | unknown | — | — | unknown |
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | unknown | — | — | whitelisted |
7608 | wps_wid.cid-764651049.1762067712.exe | POST | 204 | 142.250.186.110:443 | https://www.google-analytics.com/mp/collect?firebase_app_id=1:463244832315:android:fe82dee1e0f73e232db61e&api_secret=UViz3S6KTv6YlgsE1g4FAQ | unknown | — | — | unknown |
7608 | wps_wid.cid-764651049.1762067712.exe | POST | 204 | 142.250.186.110:443 | https://www.google-analytics.com/mp/collect?firebase_app_id=1:463244832315:android:fe82dee1e0f73e232db61e&api_secret=UViz3S6KTv6YlgsE1g4FAQ | unknown | — | — | unknown |
7608 | wps_wid.cid-764651049.1762067712.exe | POST | 204 | 142.250.186.110:443 | https://www.google-analytics.com/mp/collect?firebase_app_id=1:463244832315:android:fe82dee1e0f73e232db61e&api_secret=UViz3S6KTv6YlgsE1g4FAQ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
792 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1784 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7608 | wps_wid.cid-764651049.1762067712.exe | 142.250.186.110:443 | www.google-analytics.com | GOOGLE | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7608 | wps_wid.cid-764651049.1762067712.exe | 90.84.175.86:443 | params.wps.com | OCBHONEY OCB public cloud network | FR | whitelisted |
3412 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6212 | svchost.exe | 20.190.160.132:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6212 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
params.wps.com |
| whitelisted |
api.wps.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
Process | Message |
|---|---|
b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe | [kscreen] isElide:0 switchRec:0 switchRecElide:1 |
b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe | QLayout: Attempting to add QLayout "" to QWidget "m_BrandAreaWidget", which already has a layout
|
b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe | QLayout: Attempting to add QLayout "" to QWidget "", which already has a layout
|
b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe | QLayout: Attempting to add QLayout "" to KFrostedGlassWidget "m_ExtendPanelWidget", which already has a layout
|
b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
b2ba68e904911bb50212015ed56cc47a_setup_XA_mui_12.9.0.21549_Free.exe.601.1262.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|