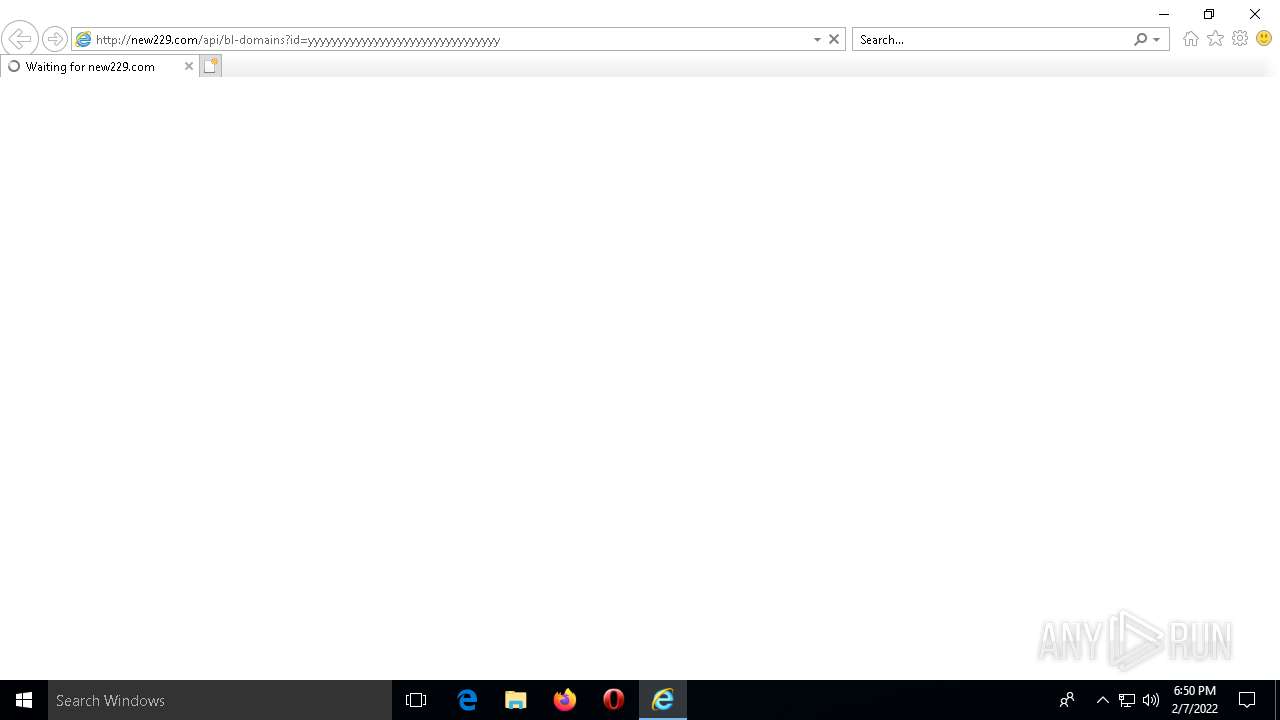
| URL: | http://new229.com/api/bl-domains?id=yyyyyyyyyyyyyyyyyyyyyyyyyyyyyyyy |
| Full analysis: | https://app.any.run/tasks/8d24e3c4-97f6-40db-971d-1fa63a87bfa2 |
| Verdict: | Malicious activity |
| Analysis date: | February 07, 2022, 18:50:23 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Indicators: | |
| MD5: | A5C26AB9B2C02A69770CCADA9E5BD409 |
| SHA1: | 237E147ED9237C5EBD981CBE686A6F0985F54062 |
| SHA256: | 060FAAB8B1A52D529FADC313CE8A213823A60E43694E85A7C86EE08801BF921D |
| SSDEEP: | 3:N1KQ38yGIULOBYctcr:CQ3RBMr |
MALICIOUS
Scans artifacts that could help determine the target
- iexplore.exe (PID: 3476)
SUSPICIOUS
Reads Microsoft Outlook installation path
- IEXPLORE.EXE (PID: 2144)
- IEXPLORE.EXE (PID: 1768)
Executed via COM
- OpenWith.exe (PID: 2132)
Checks supported languages
- notepad++.exe (PID: 4996)
Reads the computer name
- notepad++.exe (PID: 4996)
Creates files in the user directory
- notepad++.exe (PID: 4996)
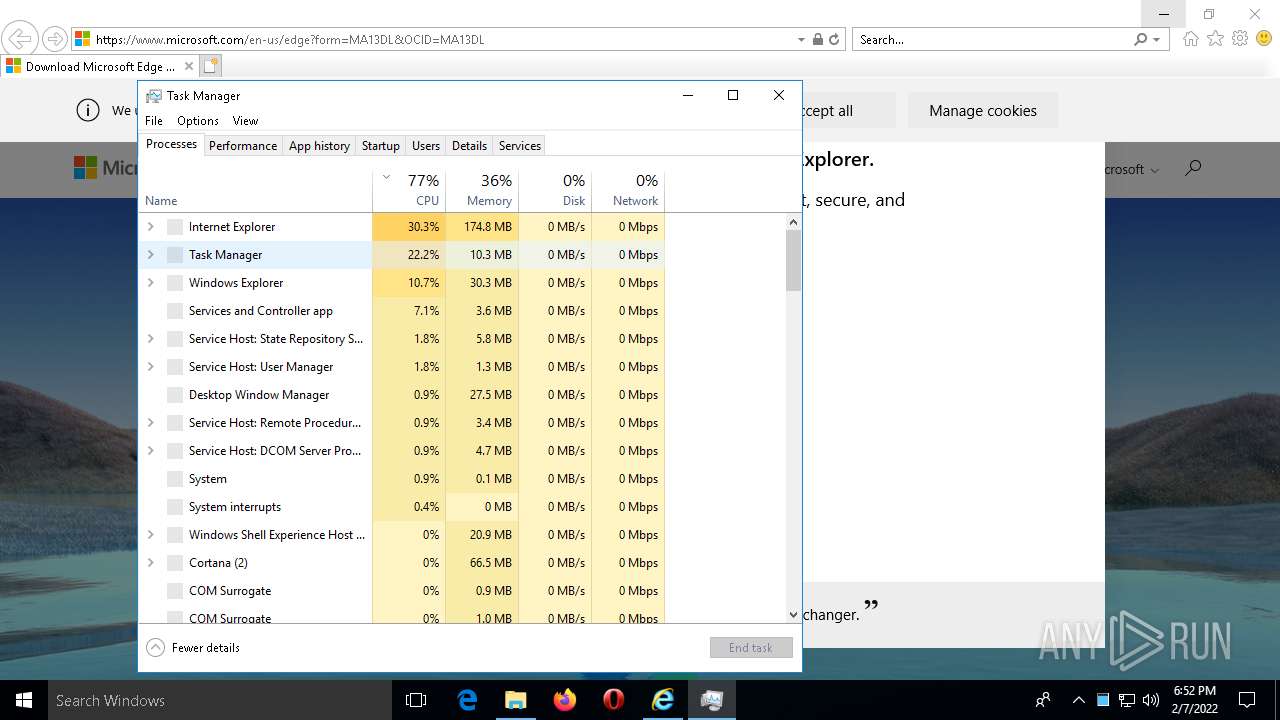
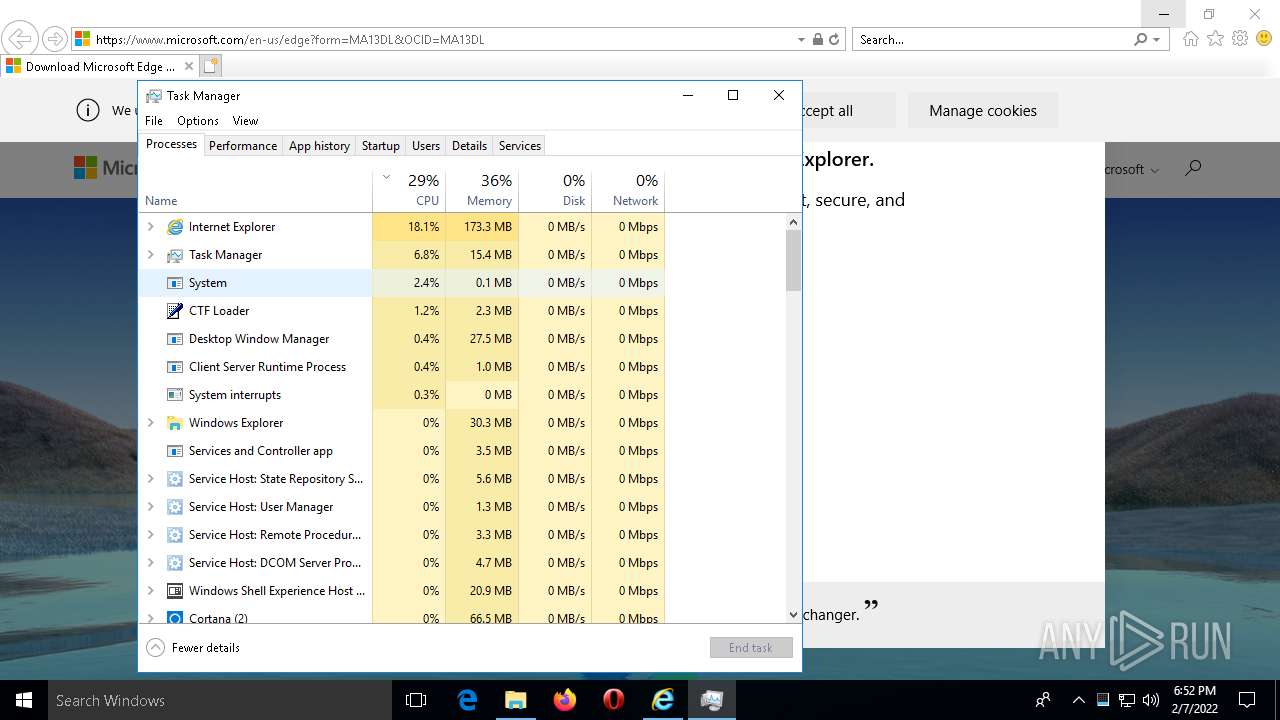
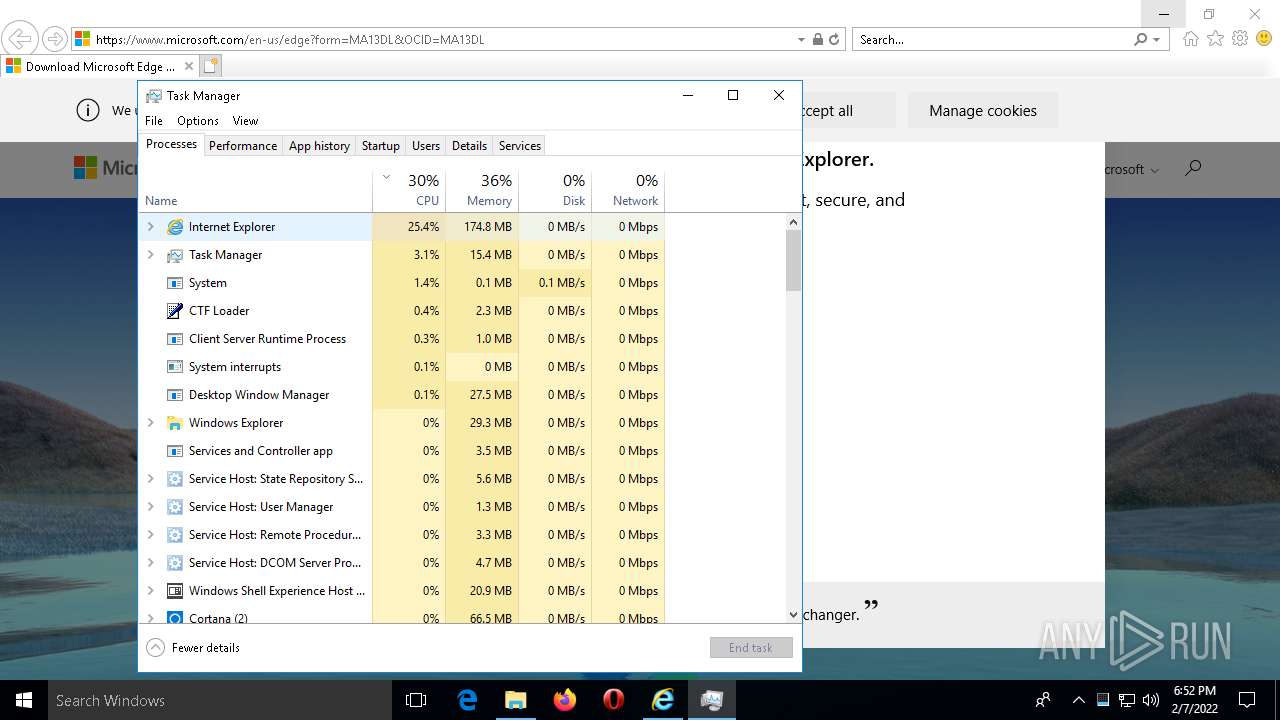
Reads the date of Windows installation
- taskmgr.exe (PID: 3384)
INFO
Reads the computer name
- iexplore.exe (PID: 3476)
- IEXPLORE.EXE (PID: 2144)
- IEXPLORE.EXE (PID: 1768)
- OpenWith.exe (PID: 2132)
- IEXPLORE.EXE (PID: 3308)
- taskmgr.exe (PID: 3384)
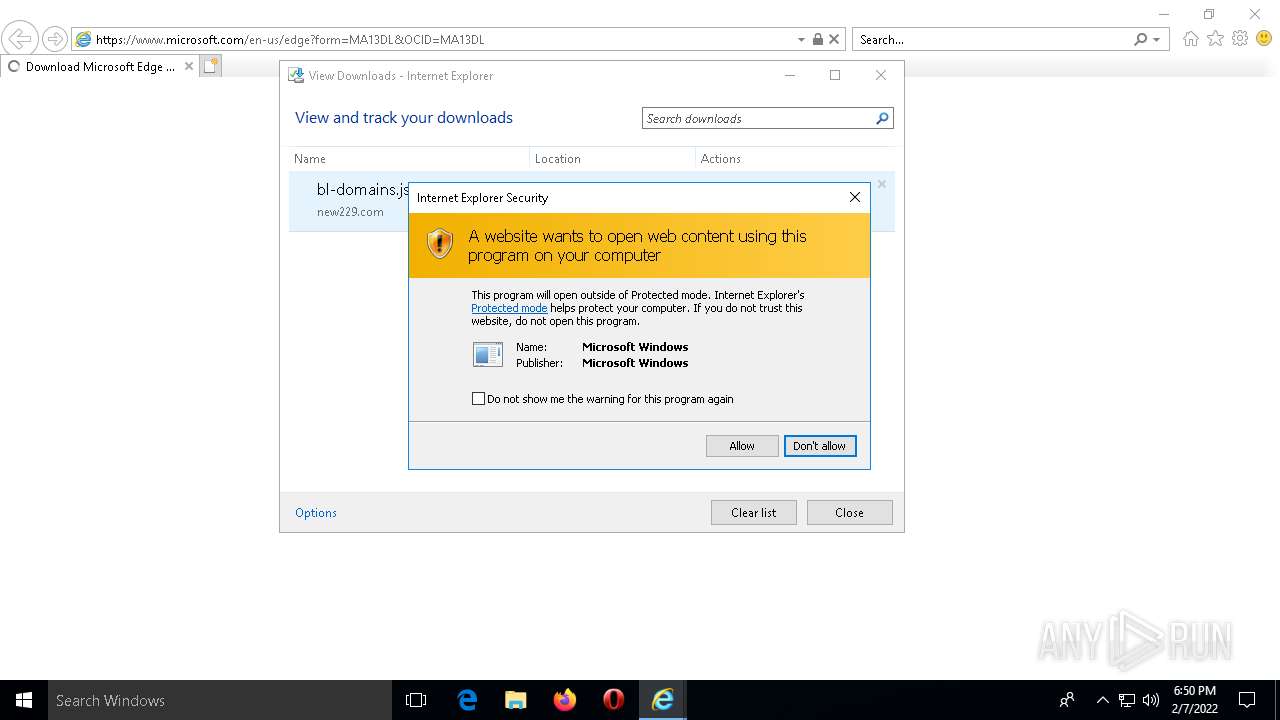
Changes internet zones settings
- iexplore.exe (PID: 3476)
Checks supported languages
- iexplore.exe (PID: 3476)
- IEXPLORE.EXE (PID: 2144)
- IEXPLORE.EXE (PID: 1768)
- OpenWith.exe (PID: 2132)
- IEXPLORE.EXE (PID: 3308)
- taskmgr.exe (PID: 3384)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3476)
Reads the software policy settings
- iexplore.exe (PID: 3476)
- IEXPLORE.EXE (PID: 1768)
Checks Windows Trust Settings
- iexplore.exe (PID: 3476)
- IEXPLORE.EXE (PID: 1768)
Reads settings of System Certificates
- iexplore.exe (PID: 3476)
- IEXPLORE.EXE (PID: 1768)
Reads internet explorer settings
- IEXPLORE.EXE (PID: 1768)
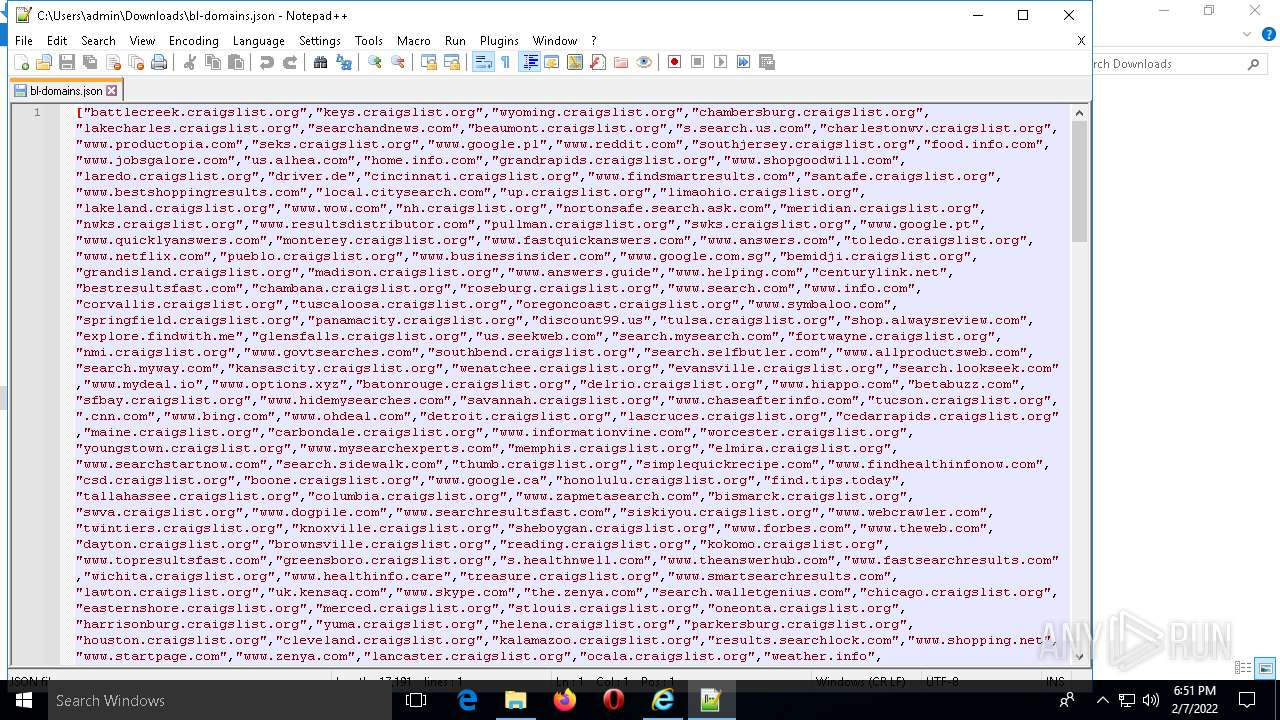
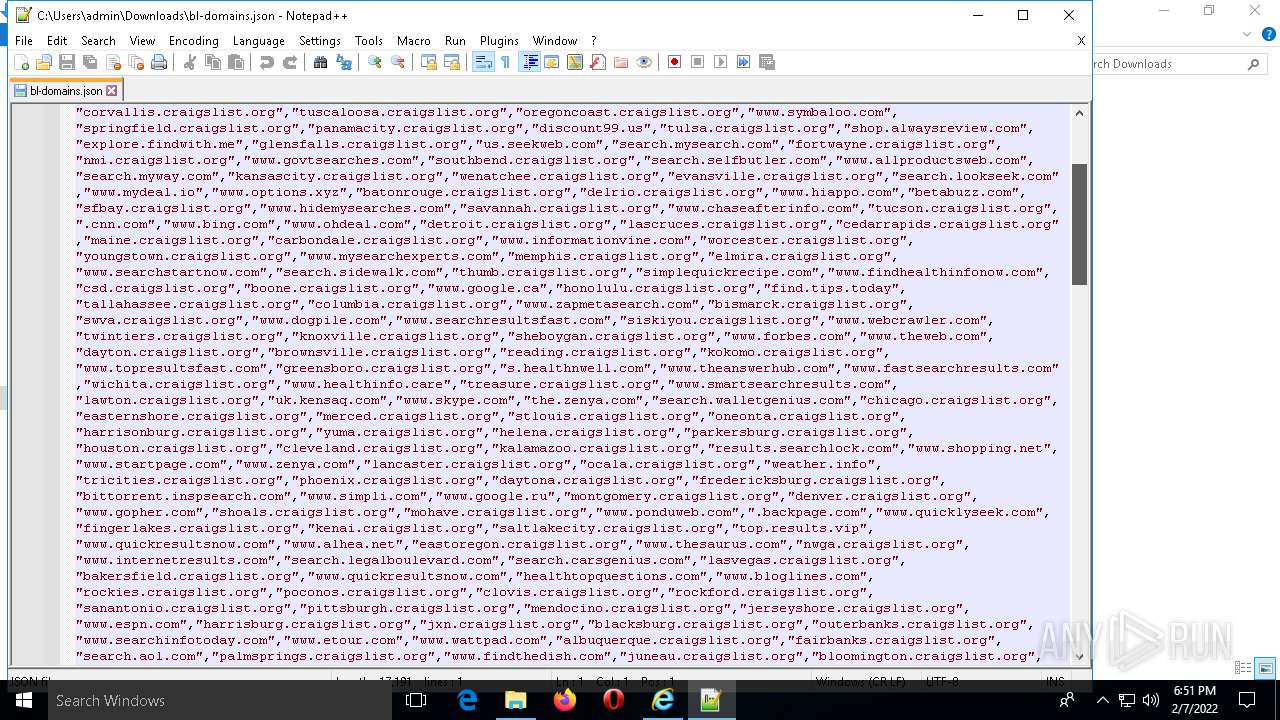
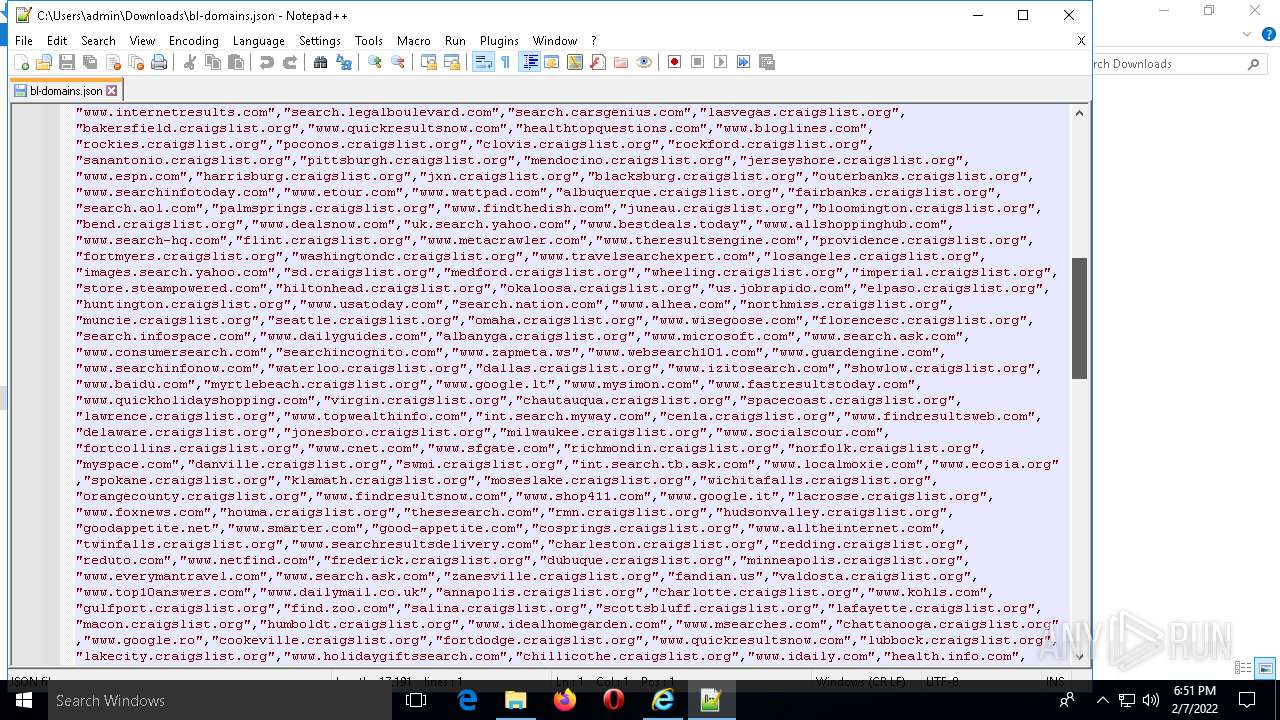
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3476)
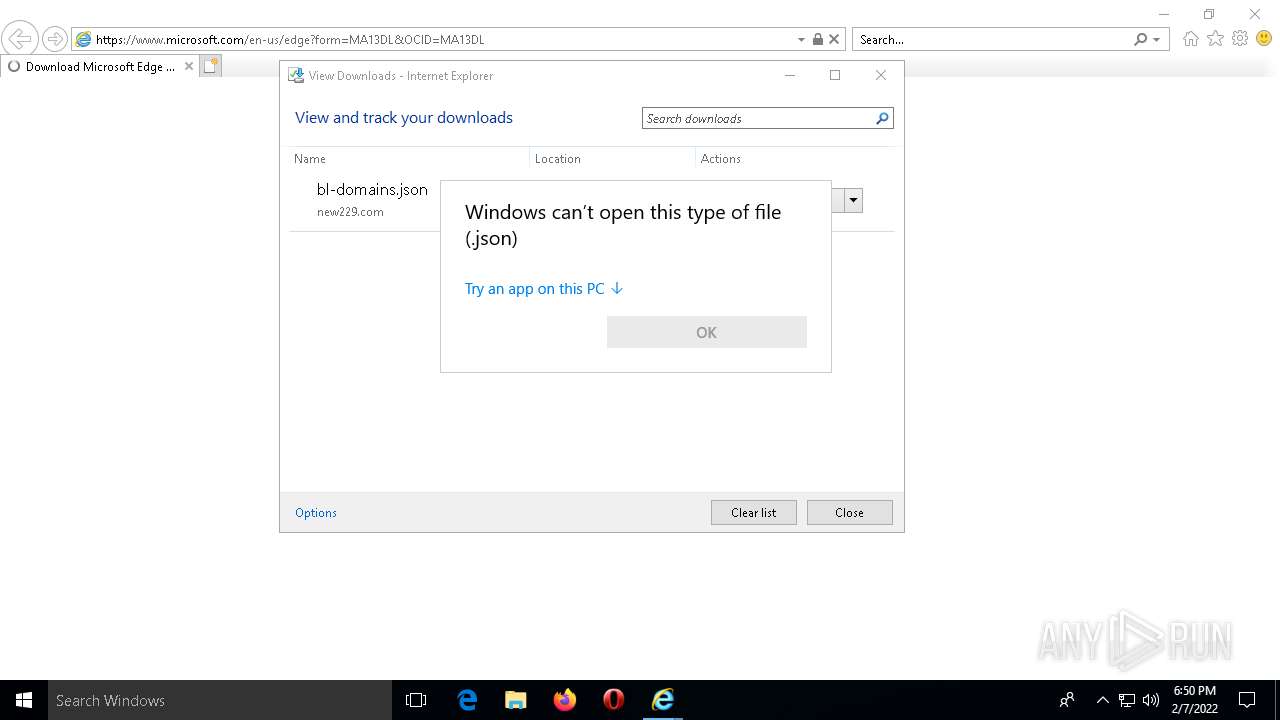
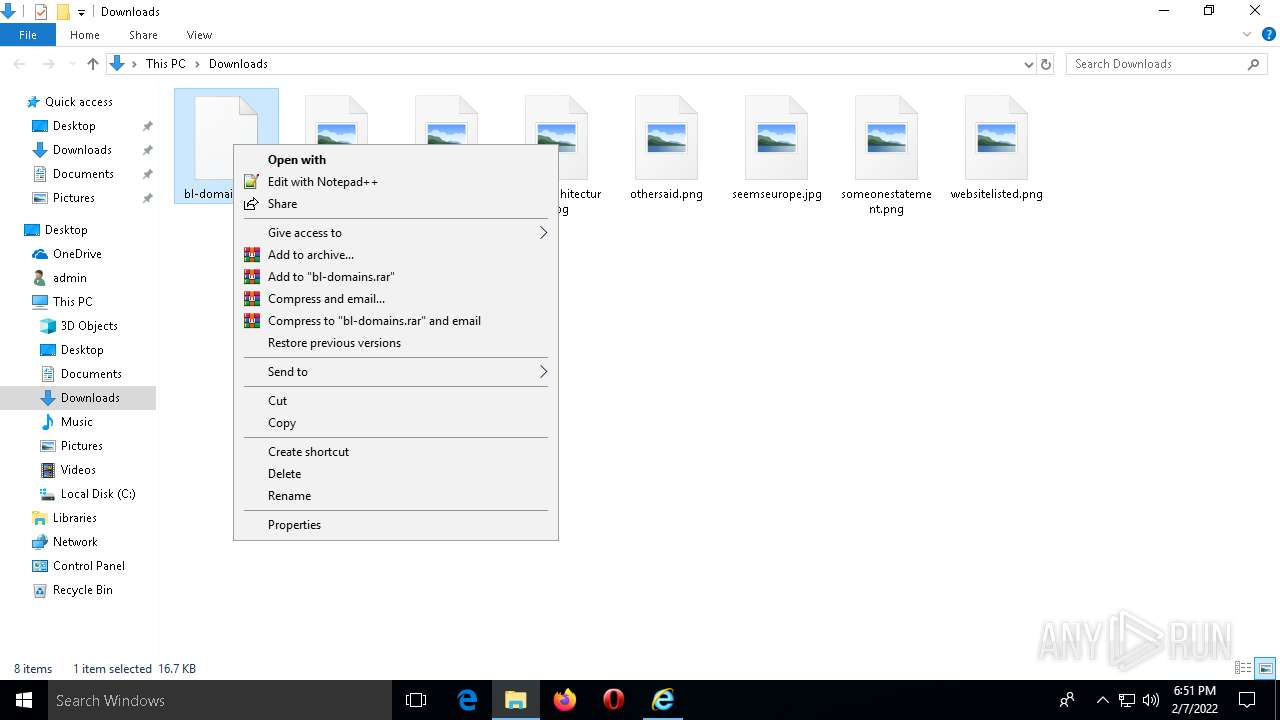
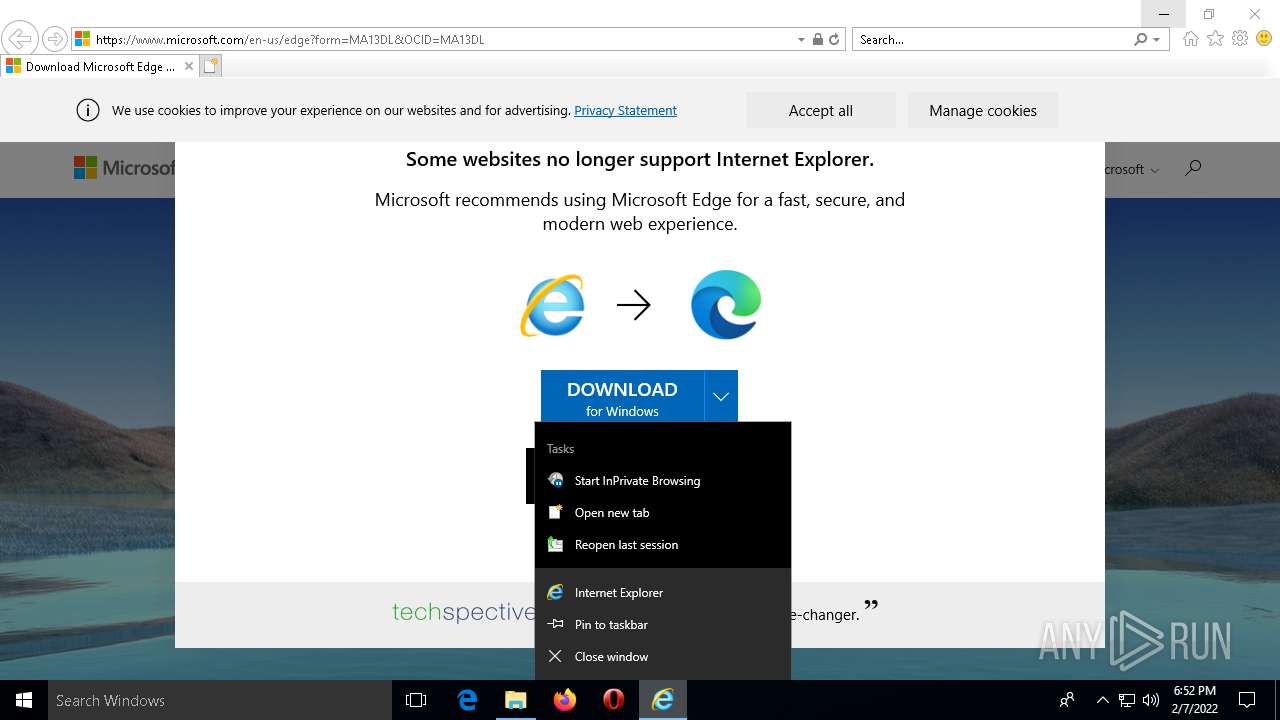
Manual execution by user
- notepad++.exe (PID: 4996)
- taskmgr.exe (PID: 488)
- taskmgr.exe (PID: 3384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
103
Monitored processes
8
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
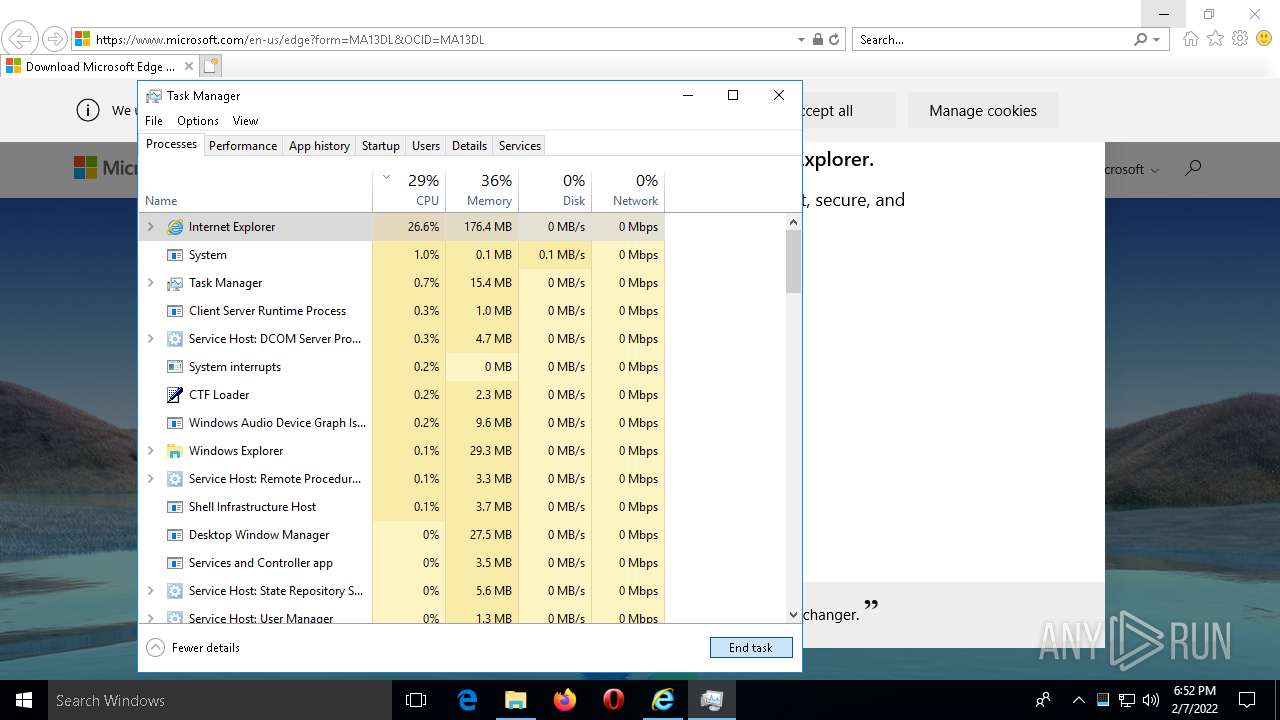
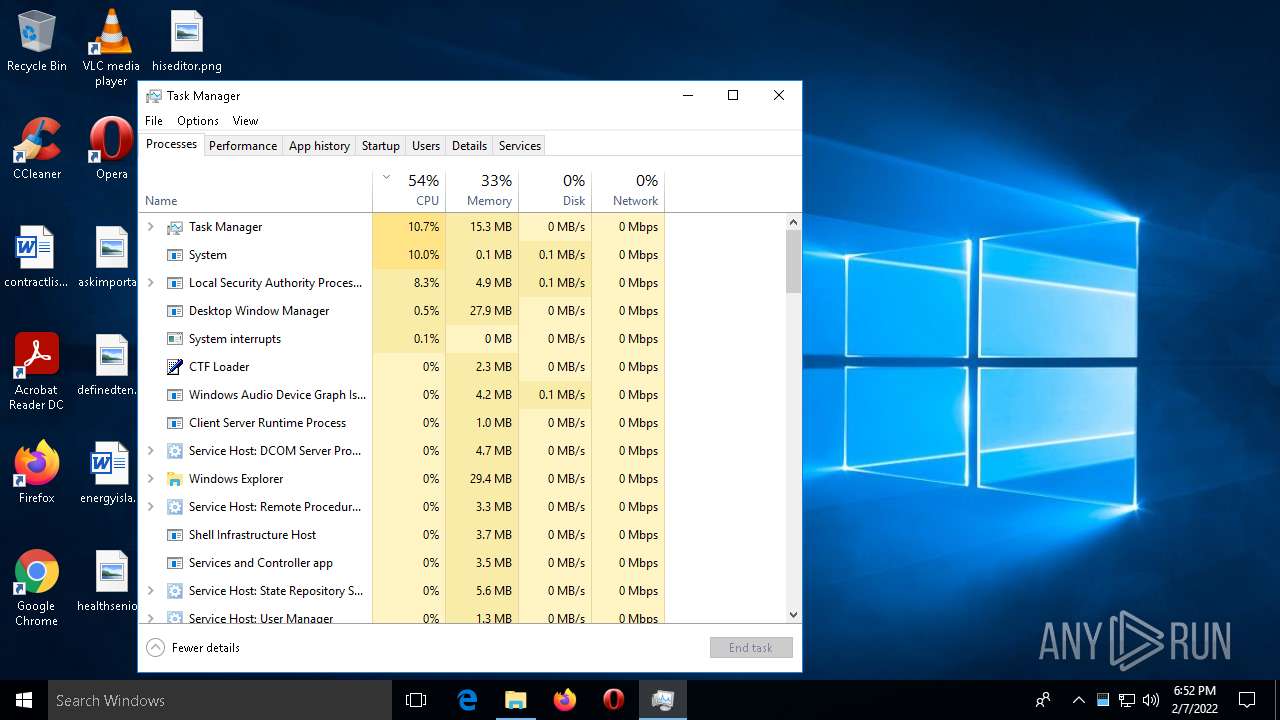
| 488 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\WINDOWS\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1768 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:3476 CREDAT:75010 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 1 Version: 11.00.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2132 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\WINDOWS\system32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2144 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:3476 CREDAT:9474 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3308 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:3476 CREDAT:1512774 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3384 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\WINDOWS\system32\taskmgr.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
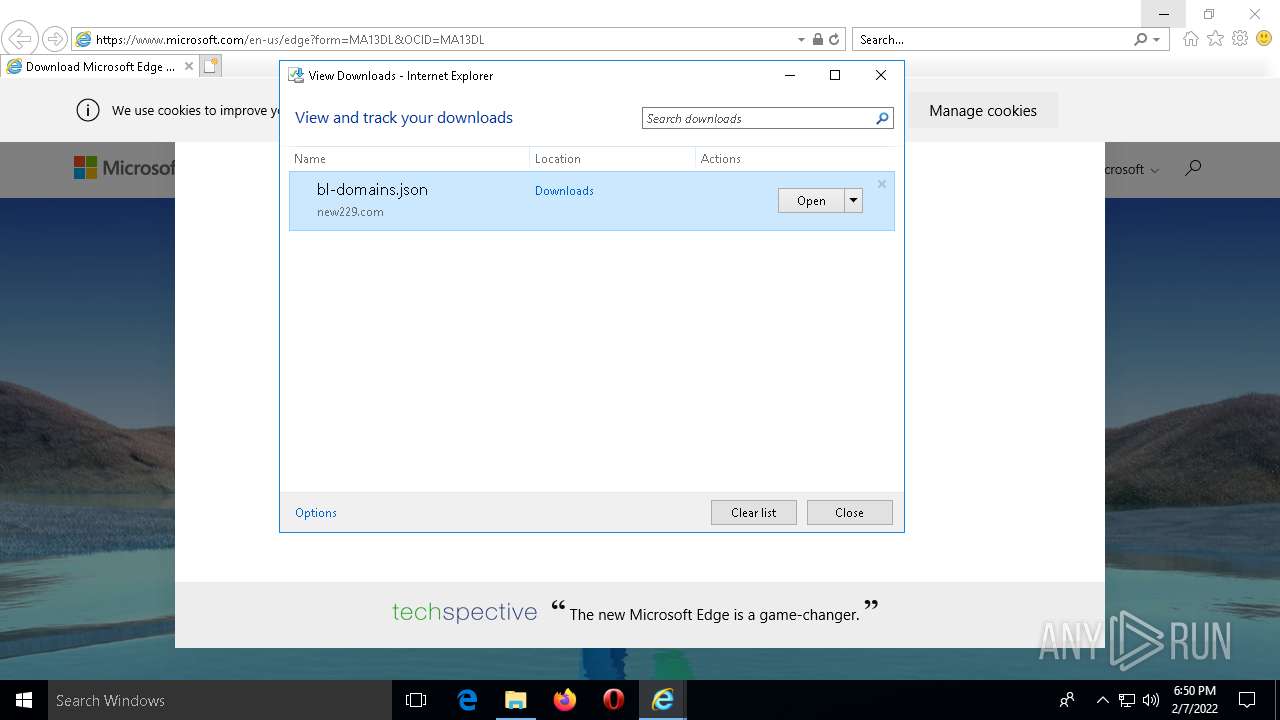
| 3476 | "C:\Program Files\internet explorer\iexplore.exe" "http://new229.com/api/bl-domains?id=yyyyyyyyyyyyyyyyyyyyyyyyyyyyyyyy" | C:\Program Files\internet explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
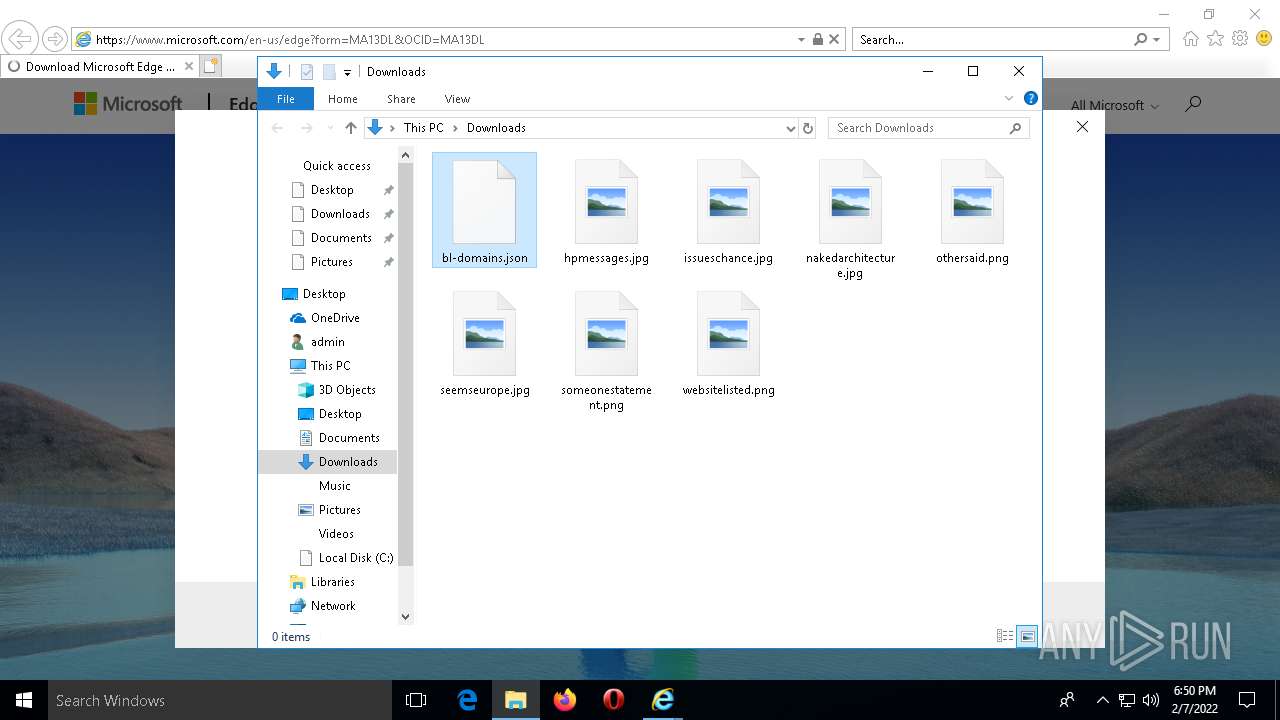
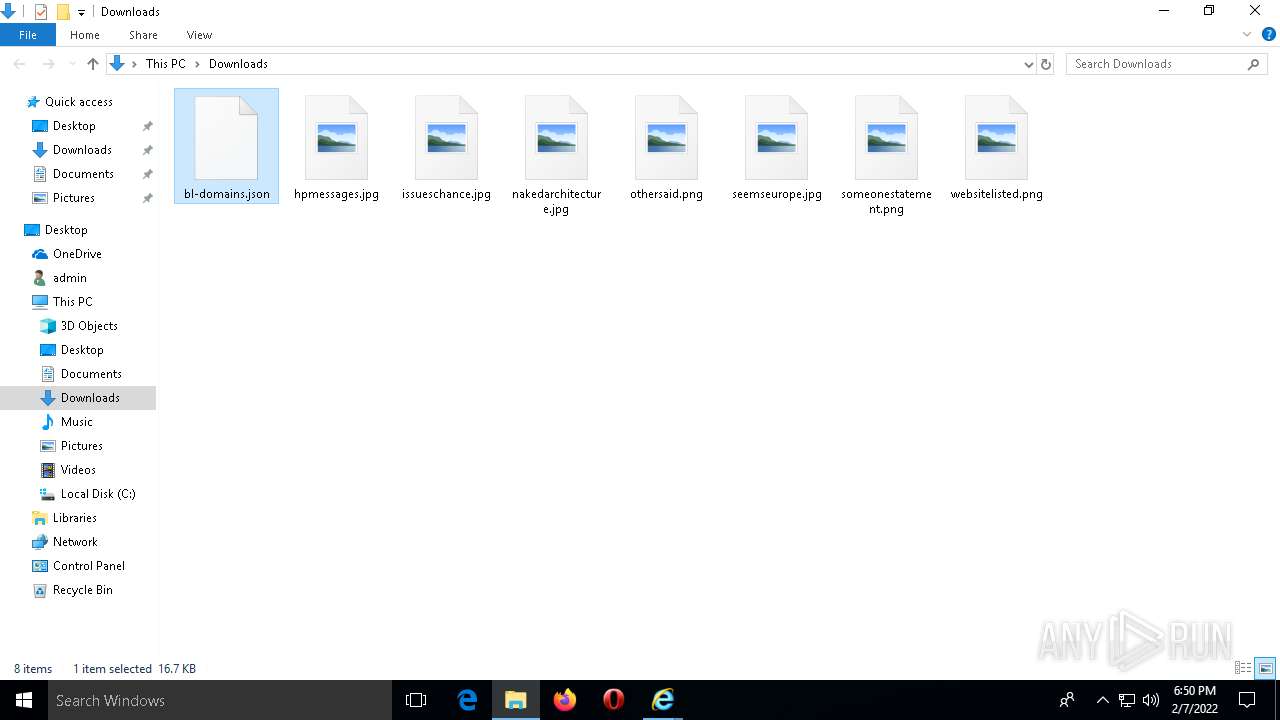
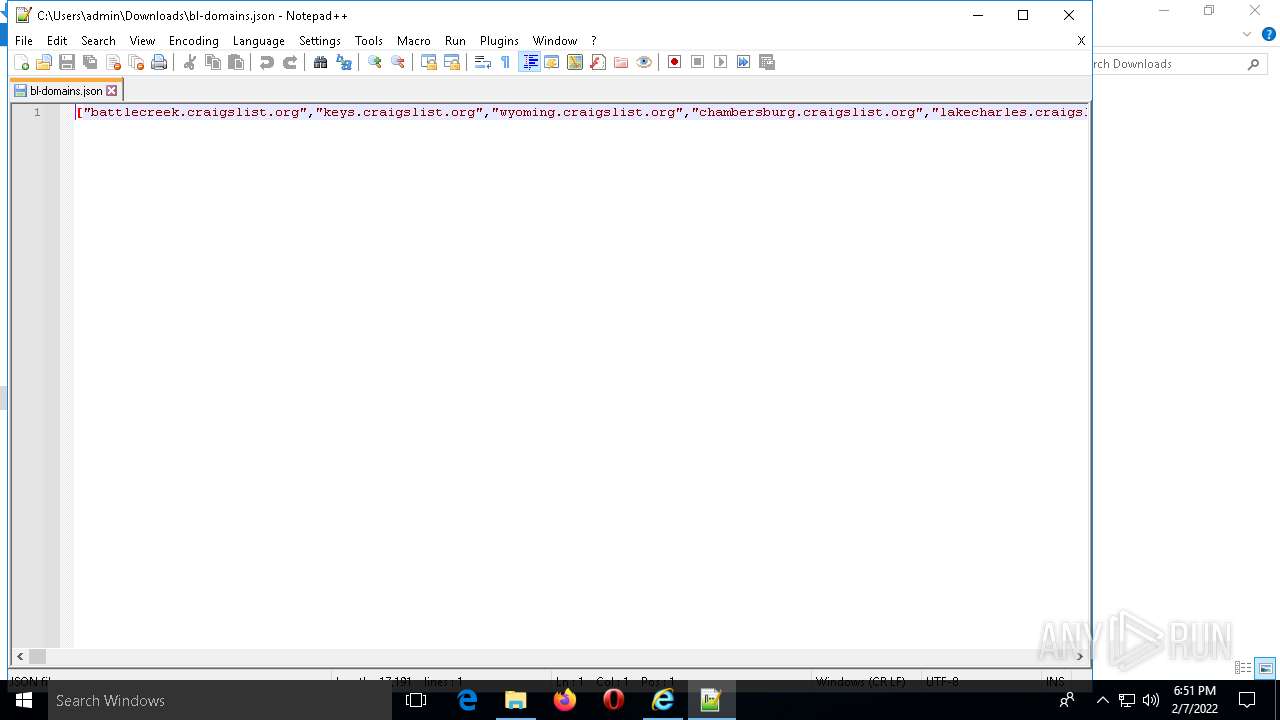
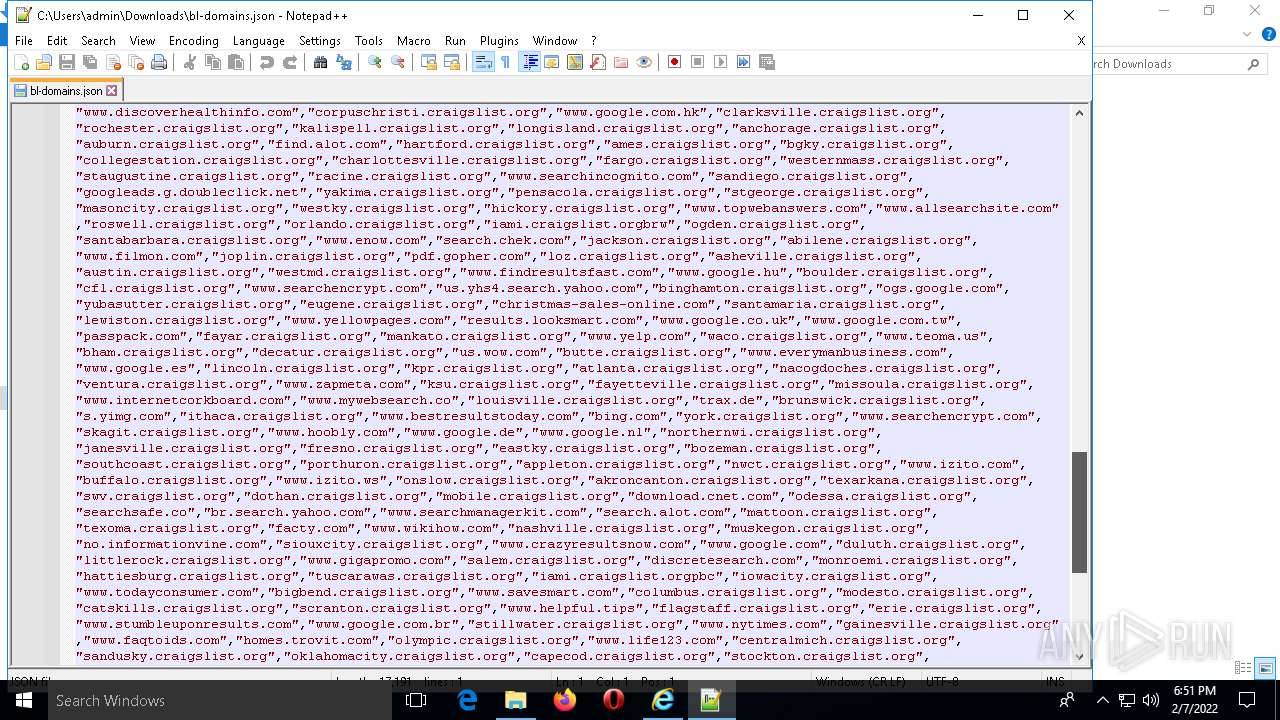
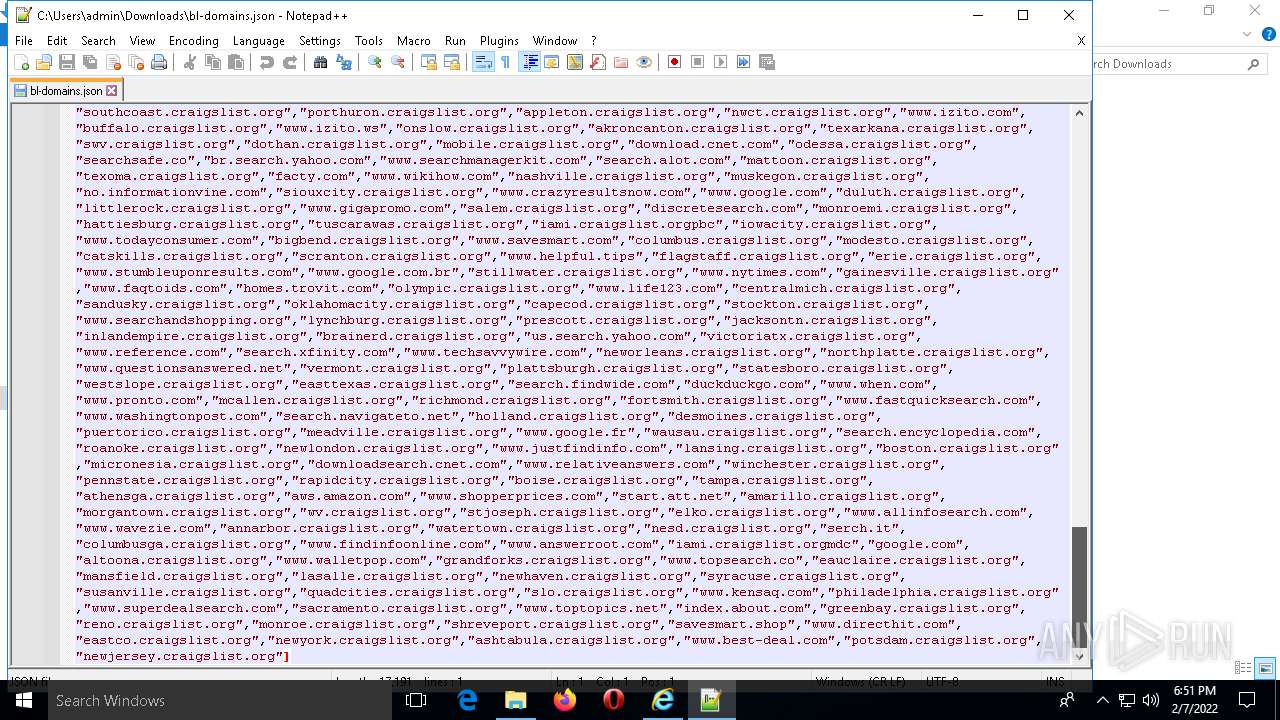
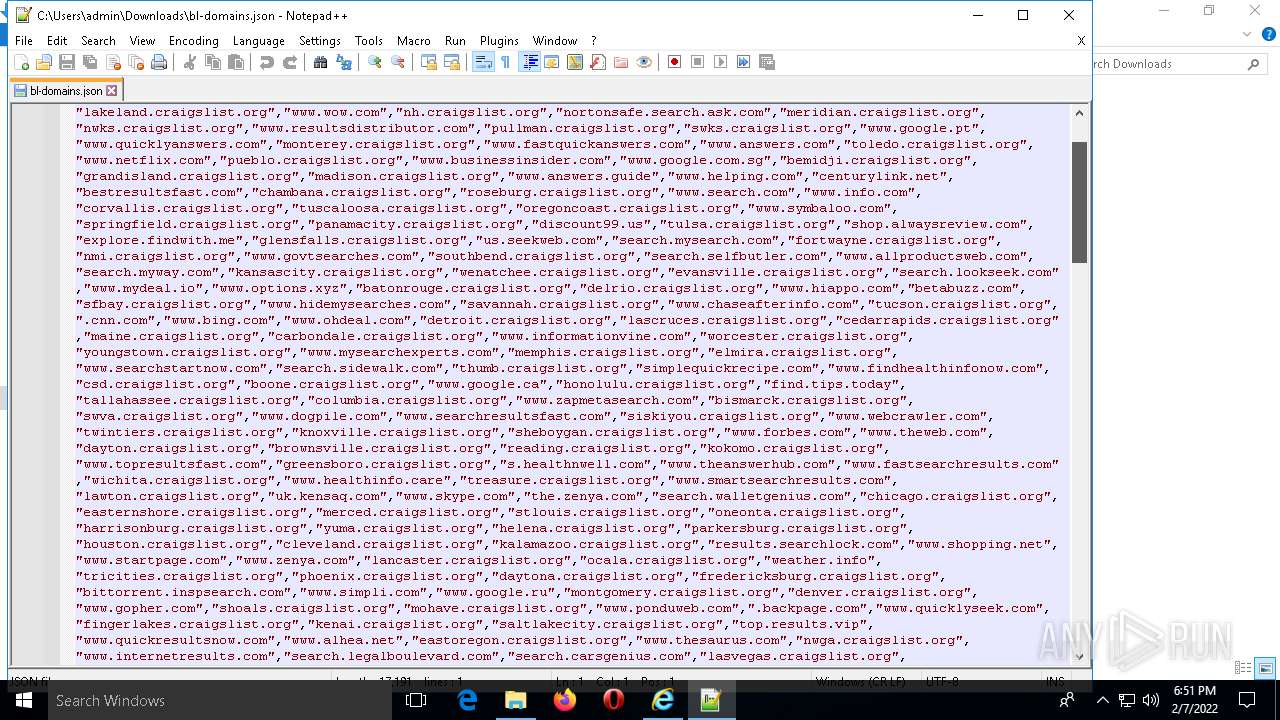
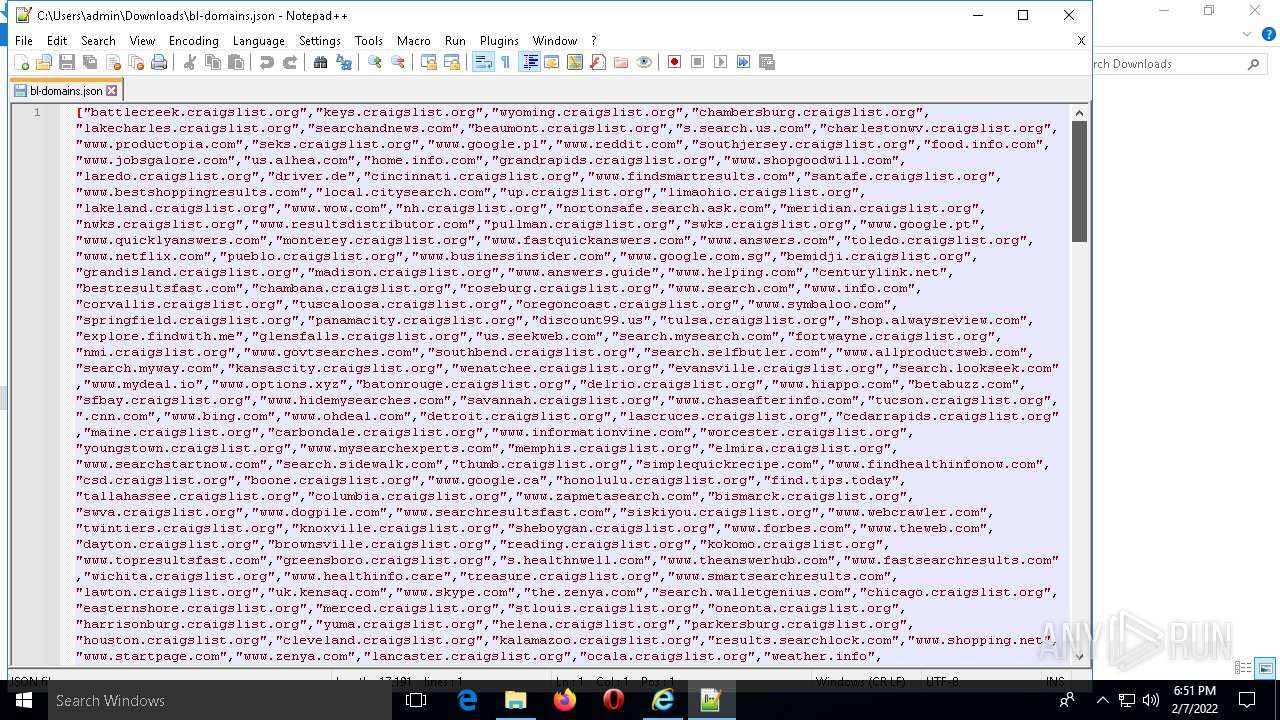
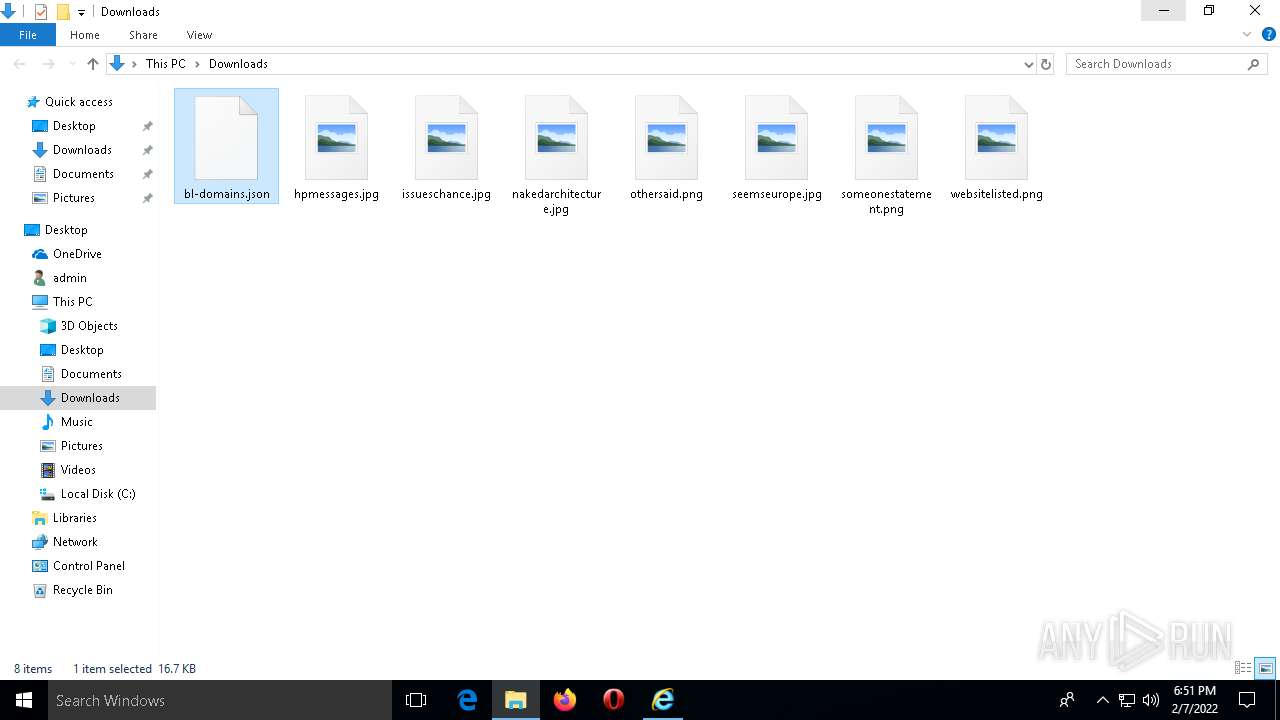
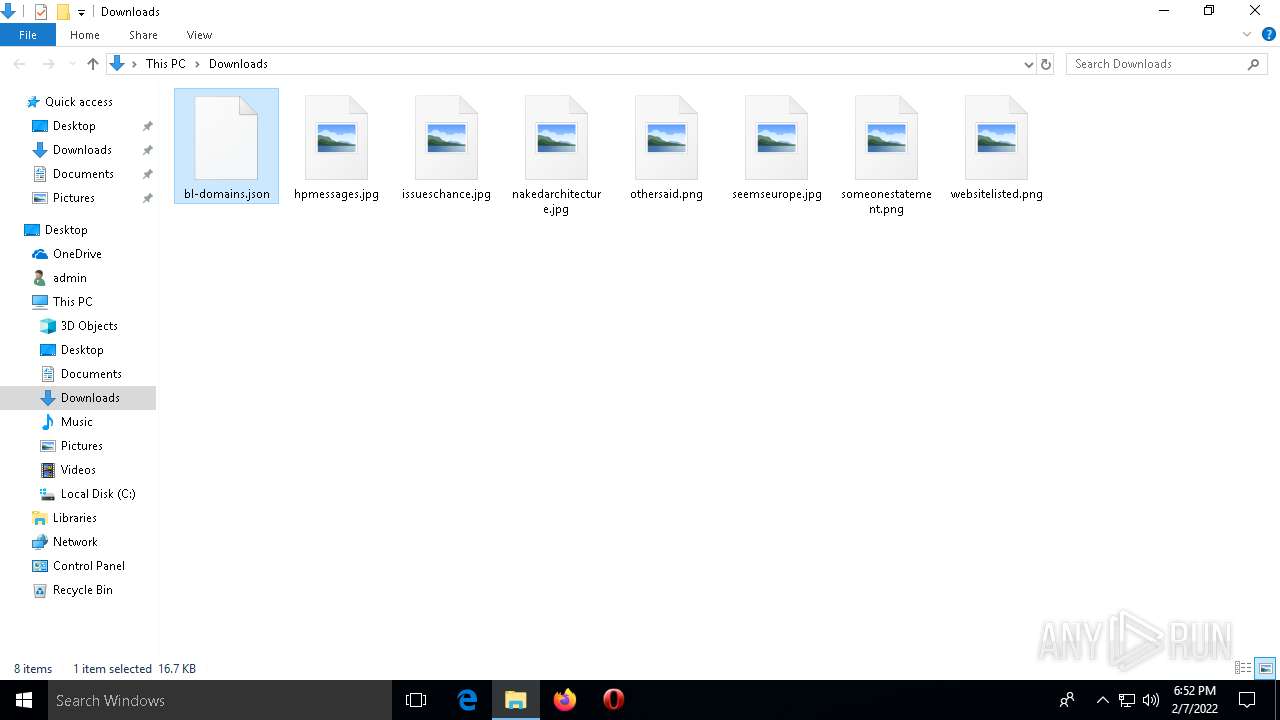
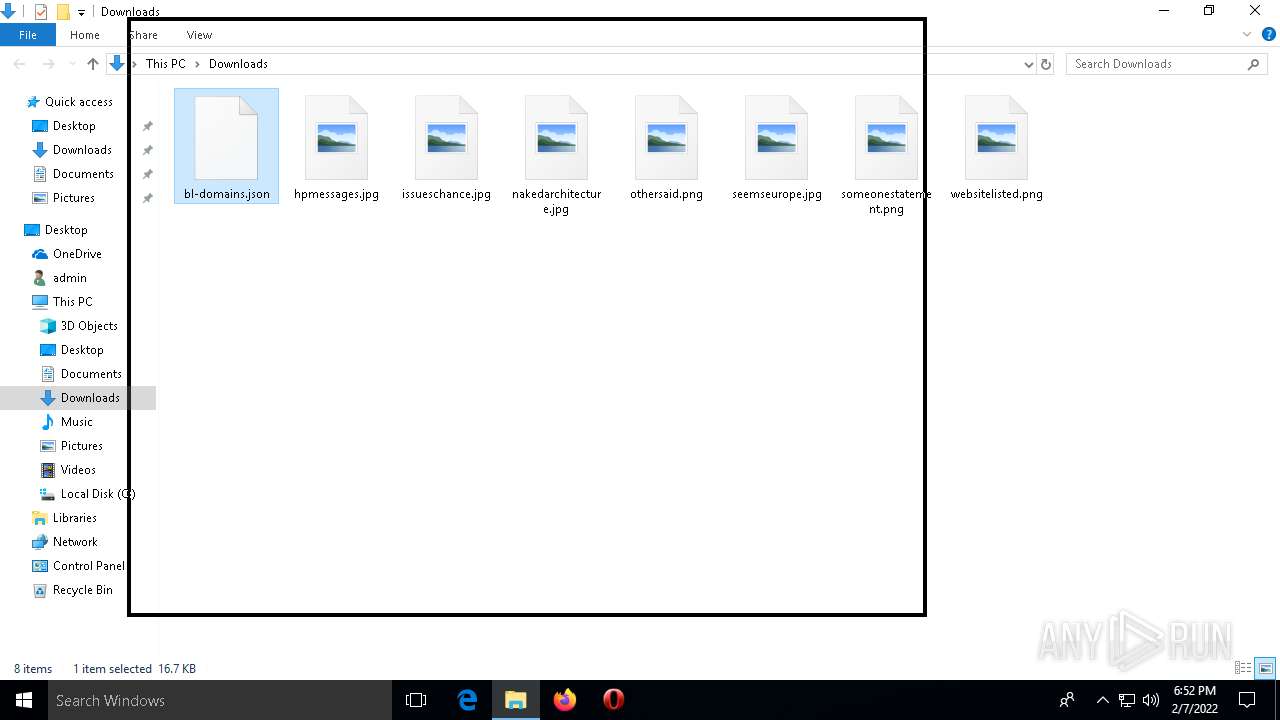
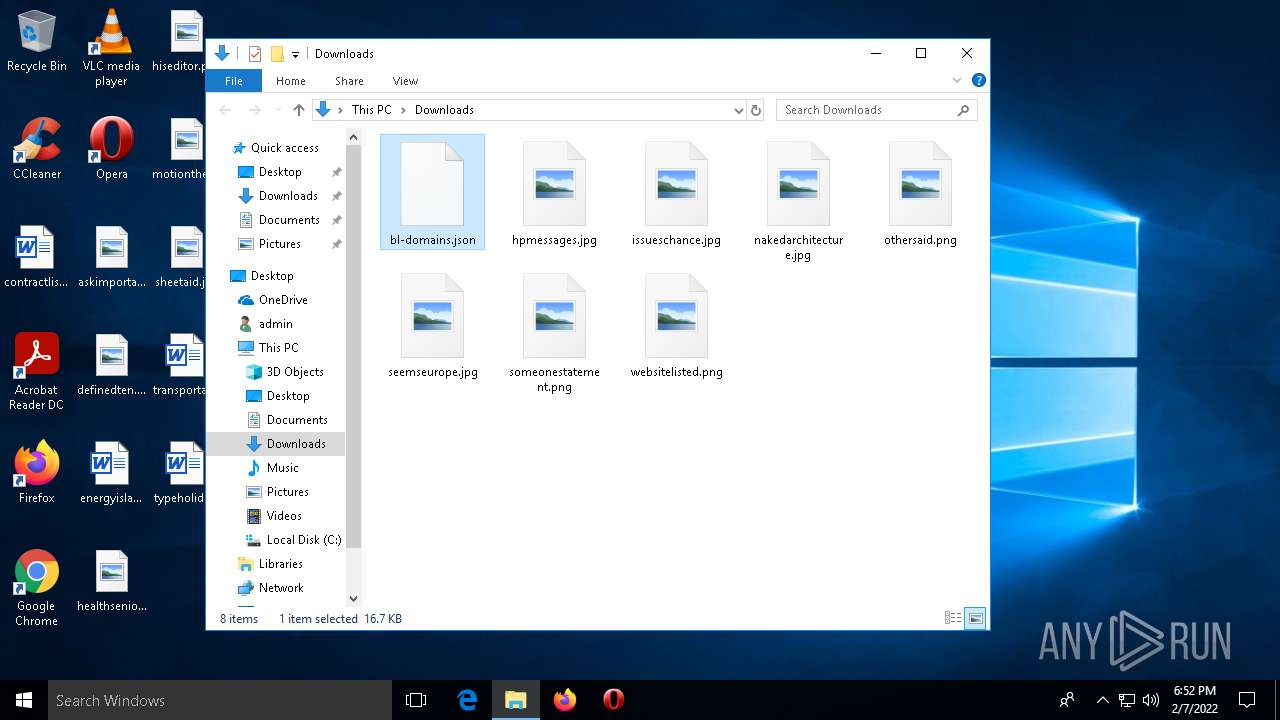
| 4996 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Downloads\bl-domains.json" | C:\Program Files\Notepad++\notepad++.exe | Explorer.EXE | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
Total events
12 244
Read events
12 088
Write events
156
Delete events
0
Modification events
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkLowPart |
Value: 956341420 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkHighPart |
Value: 148313293 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30940243 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
0
Suspicious files
8
Text files
69
Unknown types
7
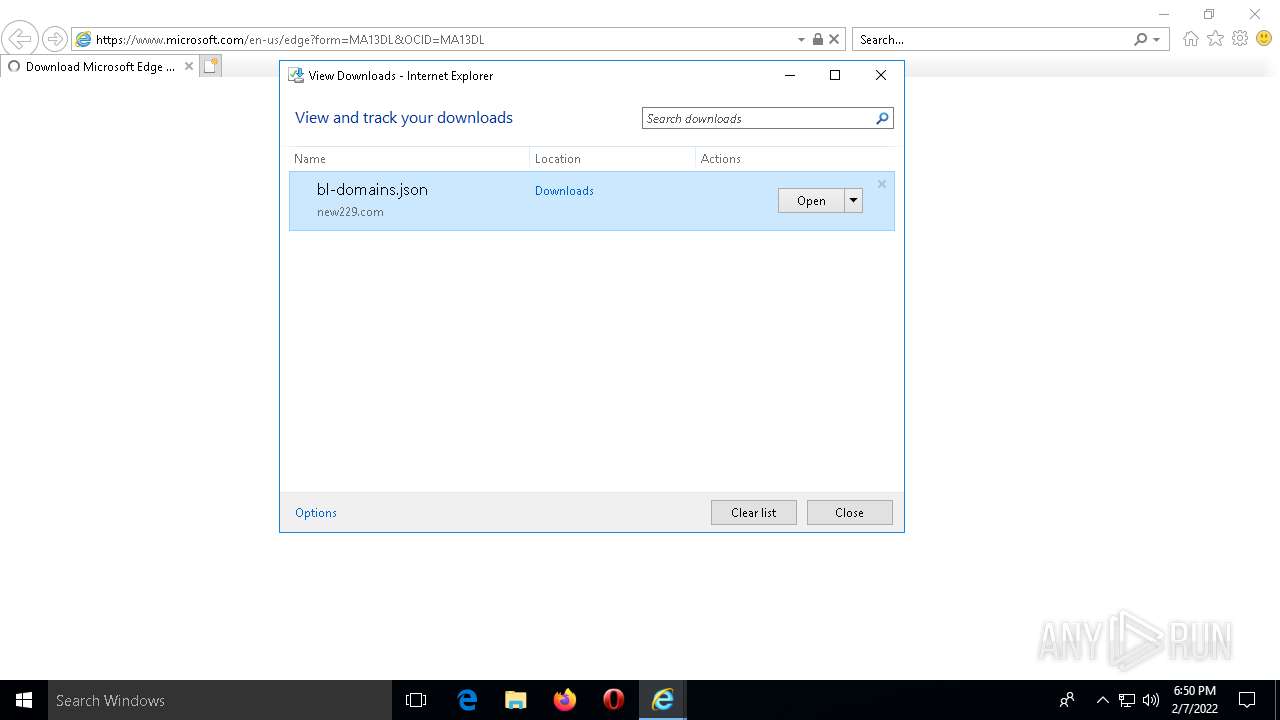
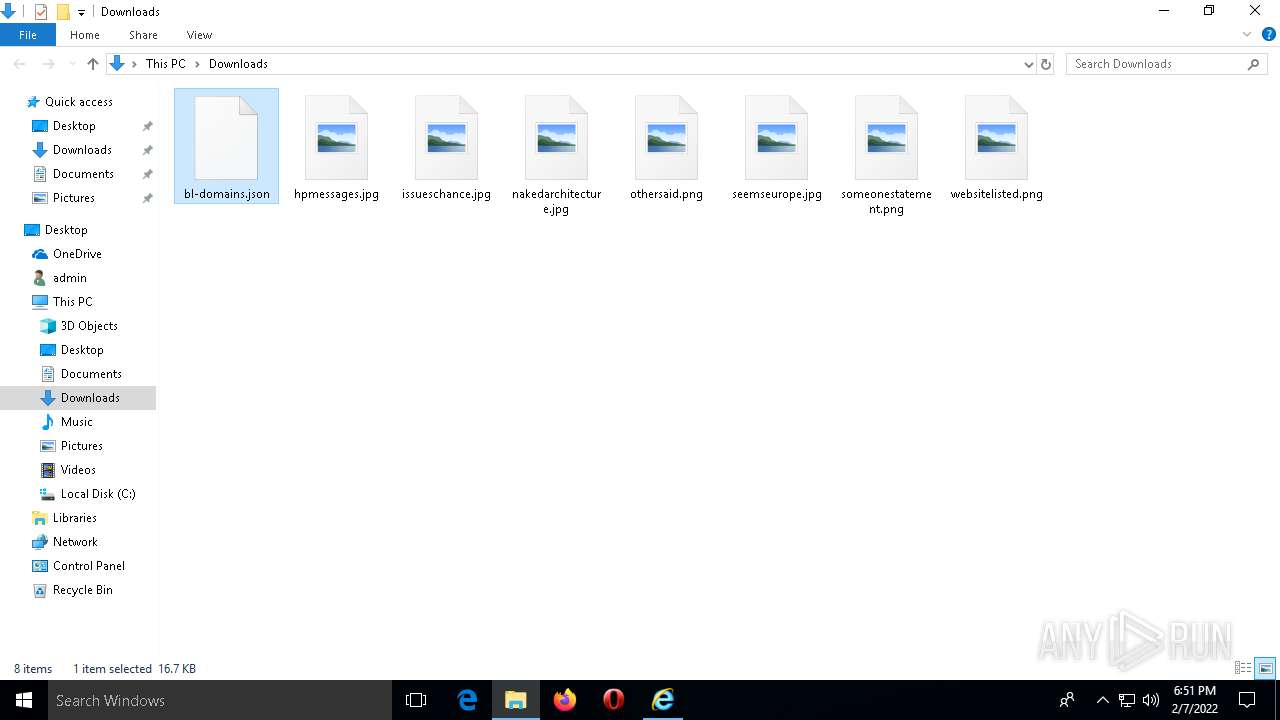
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3476 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\SmartScreenCache.dat | binary | |
MD5:4BD8825D4187D1F0EF7D2D309151F34C | SHA256:58C32AB94D6F679B92ADC410BE0A2C195A791725812C8D9264366440488D2499 | |||
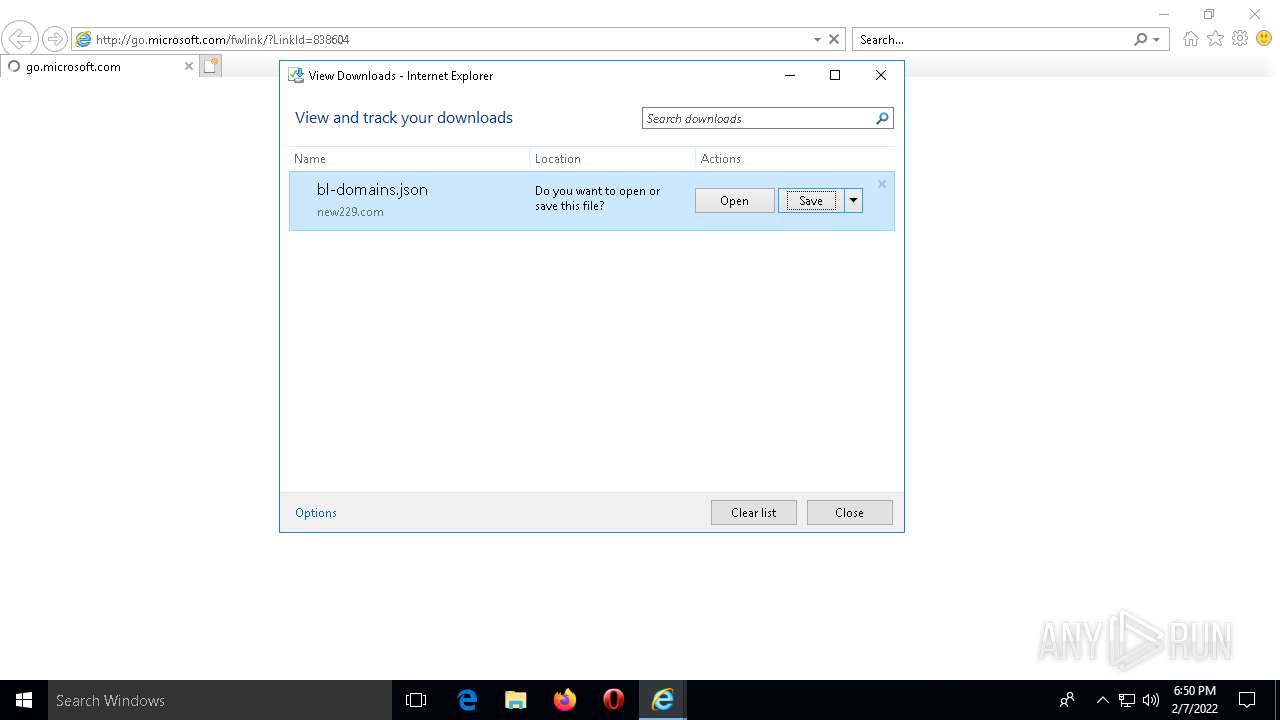
| 2144 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\84QVWPIO\bl-domains[1].json | ini | |
MD5:AB8414496A661C820A5334281B3BEED2 | SHA256:ECD776DC6FD907DDF945F51569F0F5557C15CD5ABBB35AAD51811FF634EAC0ED | |||
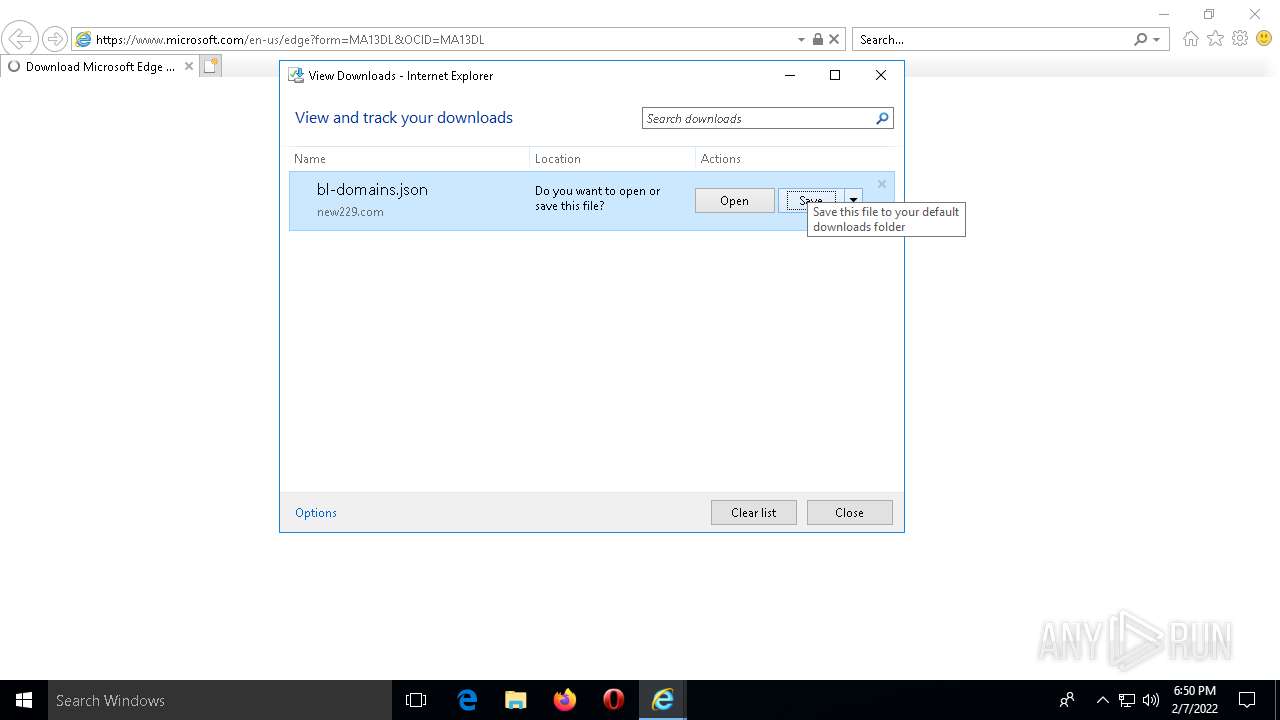
| 1768 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\QRVYFAE6\edge[1].htm | html | |
MD5:2C54F4156068FF662EAEF2C748440F70 | SHA256:0DD2FD8F11C843A28587BE77F2A3A97BDE3A8CDC2AAE47C63558FE9C8B574E6D | |||
| 1768 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\UGAFGOLY\oneplayer[1].js | text | |
MD5:4C7F040A231452B0B15C159F6A68119E | SHA256:7364CEE8567868C4E8B863B11448632741AAC2774E7223108002EF4E5779BF49 | |||
| 1768 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\QRVYFAE6\css[1].css | text | |
MD5:4FF9F1D950B39AB8FC0BC2DF3E98BD6C | SHA256:662BEF9DF2B582A86451C8436E240721D1291A623057860BA14E0F382143A756 | |||
| 1768 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\UGAFGOLY\polyfill.min[1].js | text | |
MD5:23A482F93B2EA860F5E311BCEE025D55 | SHA256:226B4C57023CF46E9B0E49C28C64DB544D255CB99979A9F478DBB70BA8610FBD | |||
| 1768 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\JVE1W4LU\launch-EN7b3d710ac67a4a1195648458258f97dd.min[1].js | text | |
MD5:908DA4C7417B52B57ED0FF4CD1040AB4 | SHA256:C5CE451CDAE7555124E7D4F34F501176E8D5F5C96C664A618E162562074C4032 | |||
| 1768 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\QRVYFAE6\mwf-auto-init-main.var.min[1].js | html | |
MD5:9EA4EE921FB70E0D7C36B186CB0D8680 | SHA256:FED336F5A5314EE9CD503033762EA4709C33764C2C214405915BF65262FED1EA | |||
| 3476 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF9551C6B47A381B4B.TMP | gmc | |
MD5:861DB6C372FDC1FB876952D6D2E4F966 | SHA256:F5BFBC952AEFDCE1D87A0A85A44D459ECA9D335C07512419979FCFBB5DB960E6 | |||
| 2144 | IEXPLORE.EXE | C:\Users\admin\Downloads\bl-domains.json.4ol424y.partial | ini | |
MD5:AB8414496A661C820A5334281B3BEED2 | SHA256:ECD776DC6FD907DDF945F51569F0F5557C15CD5ABBB35AAD51811FF634EAC0ED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
73
TCP/UDP connections
68
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
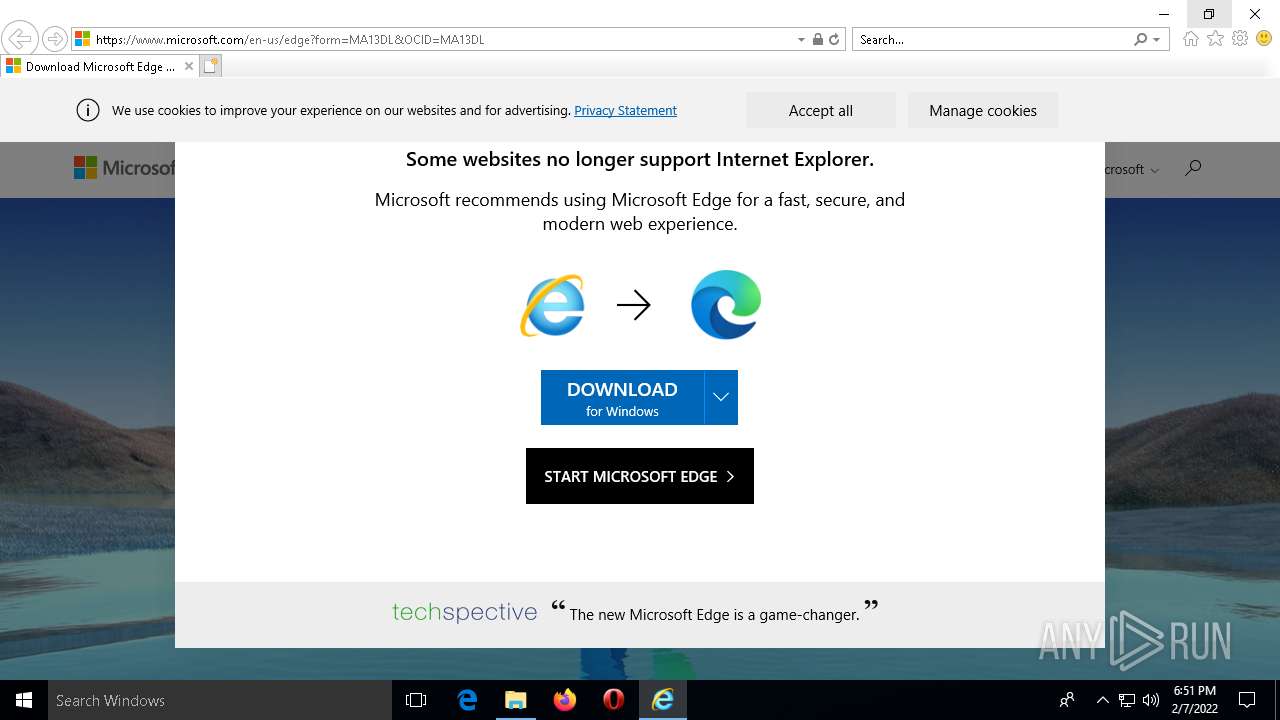
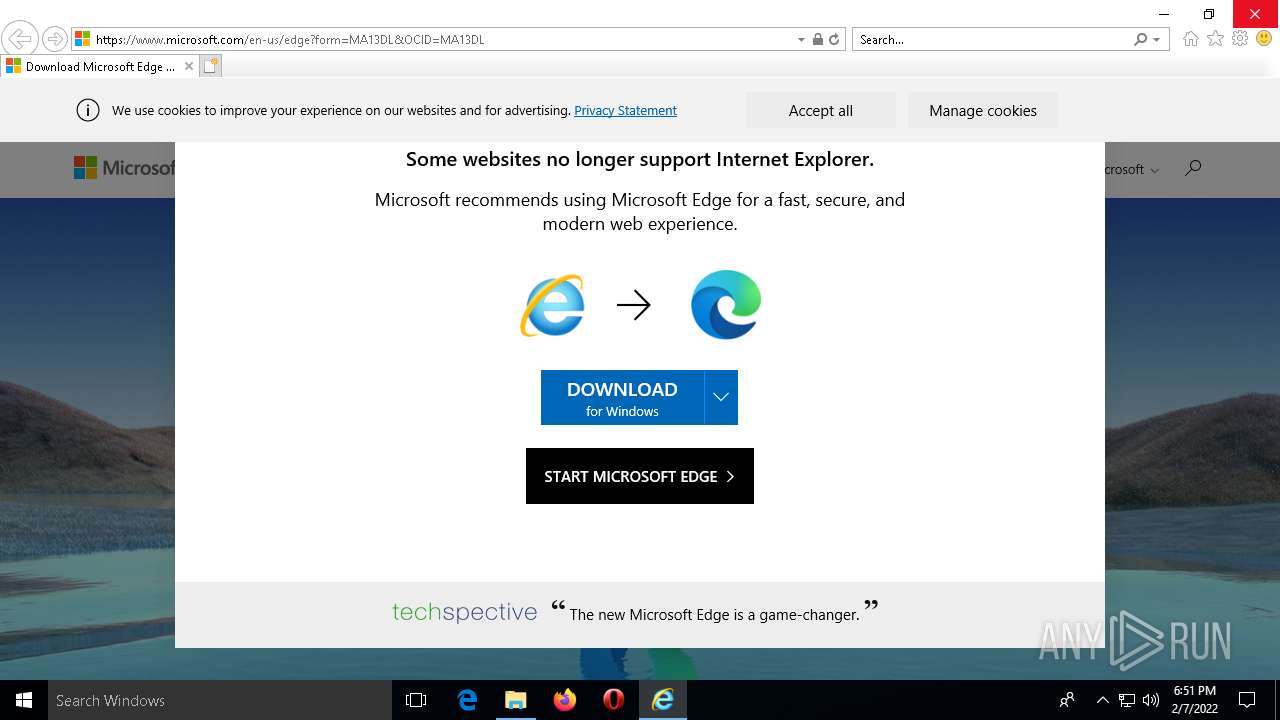
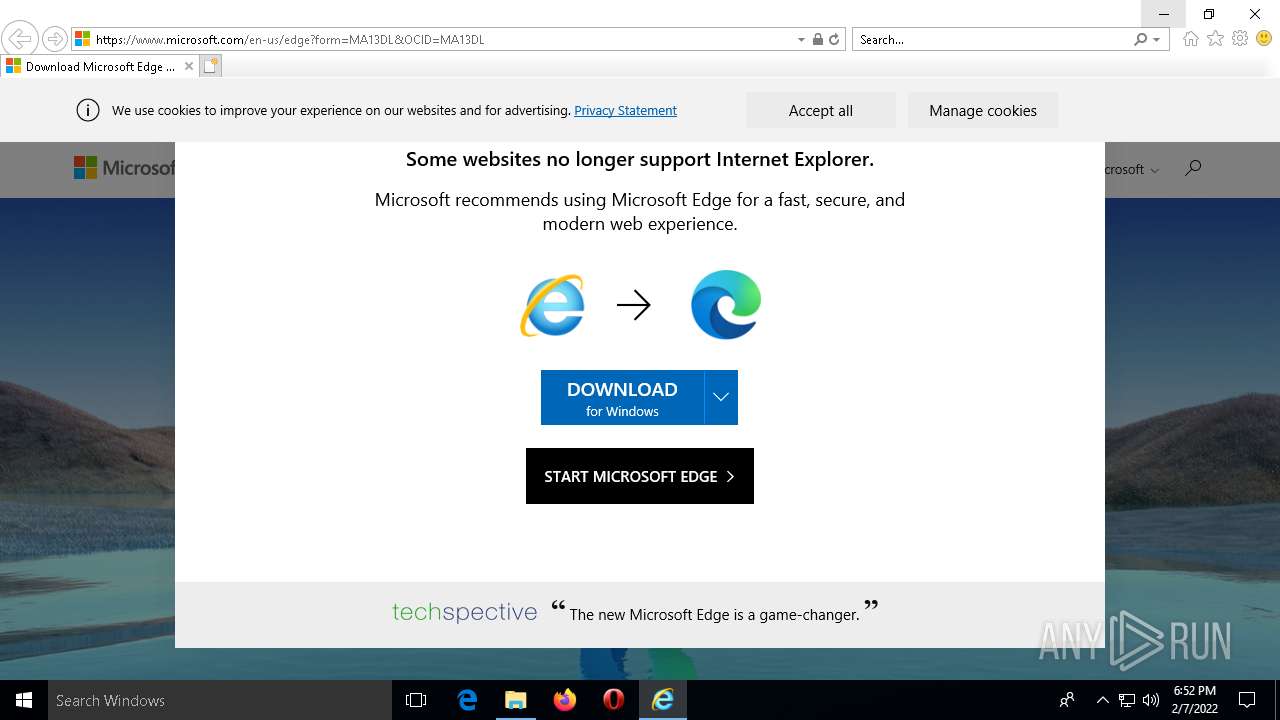
1768 | IEXPLORE.EXE | GET | 302 | 104.89.38.104:443 | https://go.microsoft.com/fwlink/?LinkId=517287 | NL | — | — | whitelisted |
3476 | iexplore.exe | POST | 200 | 20.81.51.95:443 | https://urs.microsoft.com/urs.asmx?MSURS-Client-Key=eMz3XNK6UaR/bl2FfuZuJQ%3d%3d&MSURS-MAC=l0HTG0XjNUs%3d | US | text | 1.08 Kb | whitelisted |
1768 | IEXPLORE.EXE | GET | 301 | 104.76.201.160:443 | https://www.microsoft.com/en-us/welcomeie11/ | NL | — | — | whitelisted |
1768 | IEXPLORE.EXE | GET | 301 | 104.76.201.160:443 | https://www.microsoft.com/edge/?form=MA13DL&OCID=MA13DL | NL | — | — | whitelisted |
3476 | iexplore.exe | POST | 200 | 20.98.16.82:443 | https://t.urs.microsoft.com/urstelemetry.asmx?MSTel-Client-Key=JzSeMpXfvBQq4f7T5wO1uw%3d%3d&MSTel-MAC=bN9wZ8MiM%2bk%3d | US | text | 159 b | whitelisted |
1768 | IEXPLORE.EXE | GET | 301 | 104.76.201.160:443 | https://www.microsoft.com/en-us/edge/?form=MA13DL&OCID=MA13DL | NL | — | — | whitelisted |
1768 | IEXPLORE.EXE | GET | 200 | 104.76.201.160:443 | https://www.microsoft.com/en-us/edge?form=MA13DL&OCID=MA13DL | NL | html | 215 Kb | whitelisted |
1768 | IEXPLORE.EXE | GET | 200 | 104.76.201.160:443 | https://www.microsoft.com/onerfstatics/marketingsites-neu-prod/west-european/shell/_scrf/css/themes=default.device=uplevel_web_pc/79-4cdd0a/33-ae3d41/a5-4bf7a2/13-8e1ceb/81-32f0c0/5c-b7b685/dd-4224e1/ef-a24652?ver=2.0&_cf=02242021_3231 | NL | text | 166 Kb | whitelisted |
1768 | IEXPLORE.EXE | GET | 200 | 104.76.201.160:443 | https://www.microsoft.com/videoplayer/js/oneplayer.js | NL | text | 329 Kb | whitelisted |
1768 | IEXPLORE.EXE | GET | 200 | 184.87.212.252:443 | https://assets.adobedtm.com/launch-EN7b3d710ac67a4a1195648458258f97dd.min.js | US | text | 599 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1768 | IEXPLORE.EXE | 184.87.212.252:443 | assets.adobedtm.com | Bharti Airtel Ltd., Telemedia Services | US | unknown |
3476 | iexplore.exe | 20.98.16.82:443 | t.urs.microsoft.com | — | US | unknown |
1768 | IEXPLORE.EXE | 152.199.19.160:443 | ajax.aspnetcdn.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1768 | IEXPLORE.EXE | 151.101.1.26:443 | polyfill.io | Fastly | US | suspicious |
1768 | IEXPLORE.EXE | 92.123.194.52:443 | mwf-service.akamaized.net | Akamai International B.V. | — | unknown |
1768 | IEXPLORE.EXE | 13.107.246.69:443 | wcpstatic.microsoft.com | Microsoft Corporation | US | suspicious |
2144 | IEXPLORE.EXE | 18.66.248.96:80 | new229.com | Massachusetts Institute of Technology | US | suspicious |
2144 | IEXPLORE.EXE | 18.66.248.16:80 | new229.com | Massachusetts Institute of Technology | US | malicious |
3476 | iexplore.exe | 20.81.51.95:443 | urs.microsoft.com | — | US | suspicious |
1768 | IEXPLORE.EXE | 92.123.194.25:443 | statics-marketingsites-neu-ms-com.akamaized.net | Akamai International B.V. | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
new229.com |
| malicious |
urs.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
t.urs.microsoft.com |
| whitelisted |
assets.adobedtm.com |
| whitelisted |
polyfill.io |
| whitelisted |
ajax.aspnetcdn.com |
| whitelisted |
statics-marketingsites-neu-ms-com.akamaized.net |
| whitelisted |
mwf-service.akamaized.net |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|