| File name: | HyperStealer.bat |
| Full analysis: | https://app.any.run/tasks/fa1cd9ad-b9ef-4ecc-96f8-c917d85b1dce |
| Verdict: | Malicious activity |
| Analysis date: | November 23, 2024, 23:18:36 |
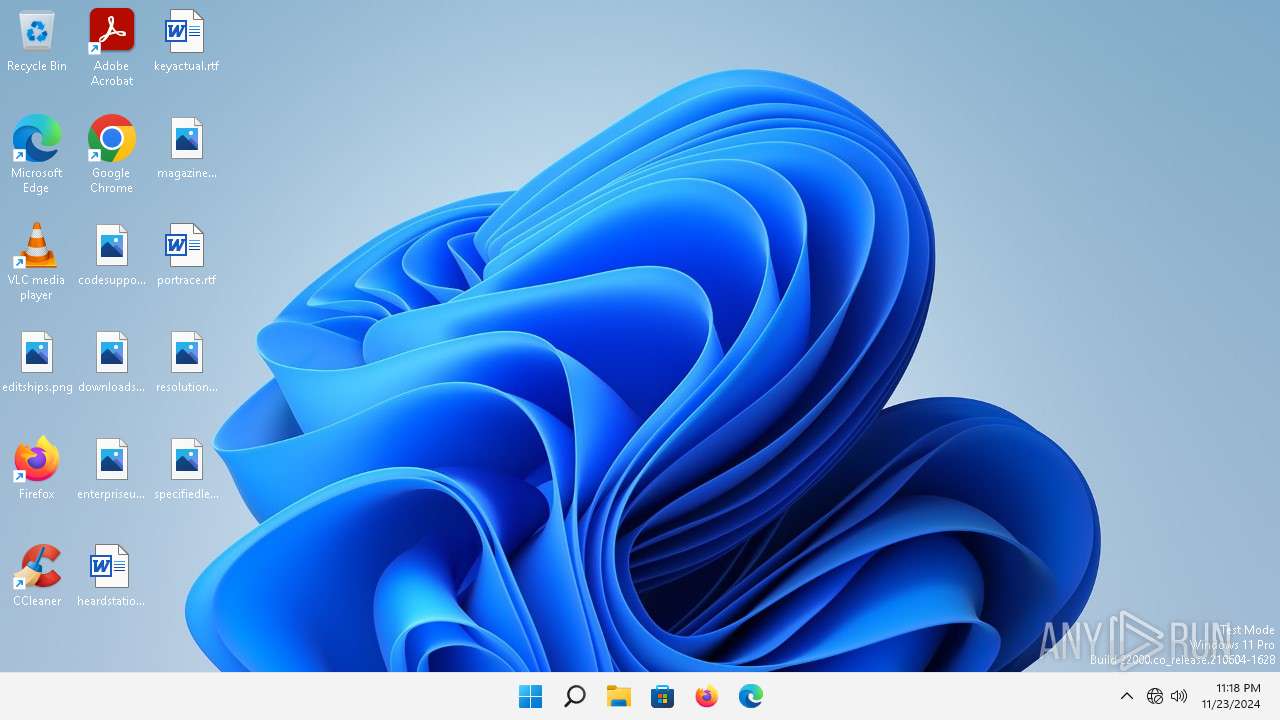
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, Unicode text, UTF-8 text, with CRLF line terminators |
| MD5: | C034D42735BE167A8835313EB939B2AC |
| SHA1: | 6C6F8D9075F13E2CF9BDEC45EF250569D428F8AA |
| SHA256: | 060F756E0373049E193FDA24B83D30610D88A5133DBA32CA1F254BAD88E3F9B8 |
| SSDEEP: | 96:J/hDypWzVH3J4lC3+2RM9gAEG2RM97Io2RM9I0Z2Fw:J/hDypWzt5lu2G9gs2G97n2G9II2Fw |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts application with an unusual extension
- cmd.exe (PID: 5564)
Possible usage of Discord/Telegram API has been detected (YARA)
- cmd.exe (PID: 5564)
There is functionality for capture public ip (YARA)
- cmd.exe (PID: 5564)
INFO
Changes the display of characters in the console
- cmd.exe (PID: 5564)
Checks supported languages
- chcp.com (PID: 7080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
119
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5564 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\HyperStealer.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6956 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7080 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
57
Read events
57
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
41
DNS requests
33
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5028 | rundll32.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2c9bde343aaf7b3e | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.160.144.191:443 | https://content-signature-2.cdn.mozilla.net/chains/remote-settings.content-signature.mozilla.org-2024-12-27-18-19-47.chain | unknown | — | — | unknown |
2524 | firefox.exe | POST | 200 | 95.101.54.107:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
2524 | firefox.exe | POST | 200 | 95.101.54.107:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
2524 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | whitelisted |
2524 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | whitelisted |
— | — | HEAD | 200 | 23.35.236.109:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | — | — | unknown |
2524 | firefox.exe | POST | 200 | 95.101.54.107:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
1296 | svchost.exe | GET | 200 | 23.55.161.191:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
5304 | MoUsoCoreWorker.exe | GET | 304 | 217.20.57.42:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8050ba87851c0947 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1296 | svchost.exe | 23.55.161.191:80 | — | Akamai International B.V. | DE | unknown |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
5028 | rundll32.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5244 | OfficeC2RClient.exe | 52.109.89.18:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2524 | firefox.exe | 34.120.208.123:443 | incoming.telemetry.mozilla.org | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
2524 | firefox.exe | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | whitelisted |
5552 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5028 | rundll32.exe | 199.232.210.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
5244 | OfficeC2RClient.exe | 52.113.194.132:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2852 | OfficeClickToRun.exe | 52.109.89.117:443 | mrodevicemgr.officeapps.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
incoming.telemetry.mozilla.org |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
telemetry-incoming.r53-2.services.mozilla.com |
| whitelisted |
prod.remote-settings.prod.webservices.mozgcp.net |
| whitelisted |
google.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ecs.office.com |
| whitelisted |
mrodevicemgr.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1296 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |