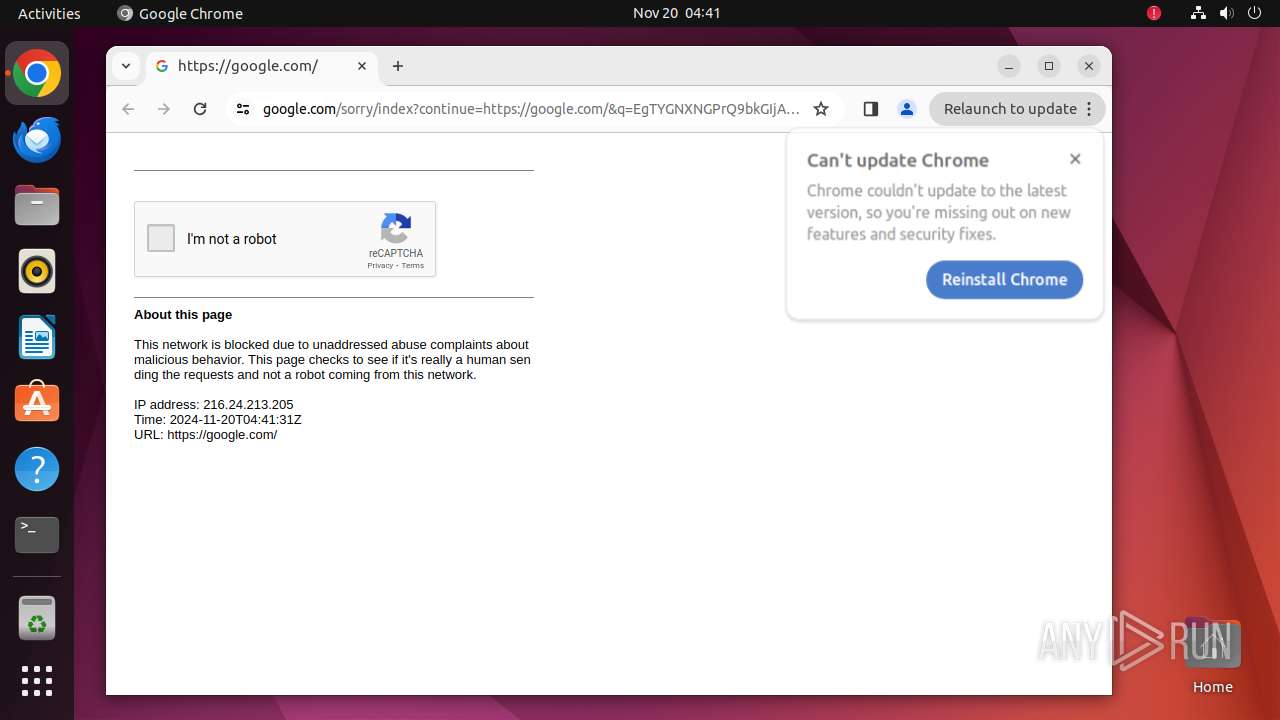
| URL: | budgepenitent.com |
| Full analysis: | https://app.any.run/tasks/c22e84cc-4448-417b-aa78-6c1dded70d69 |
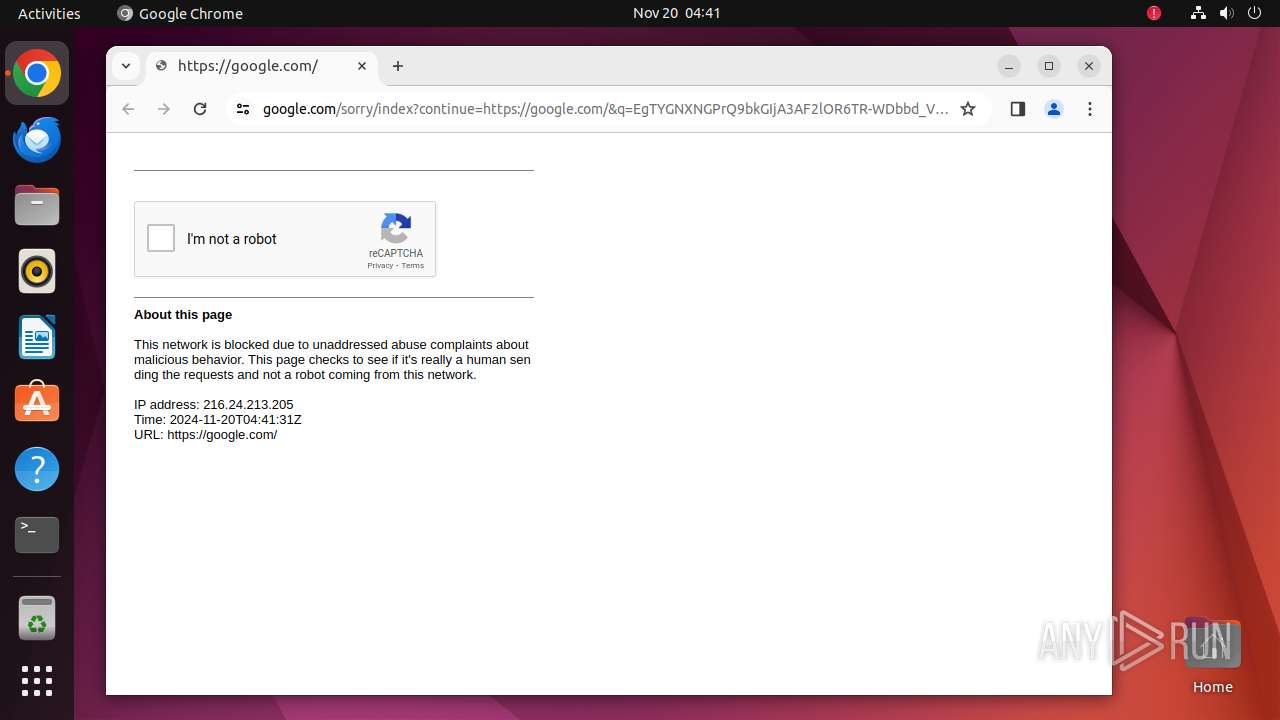
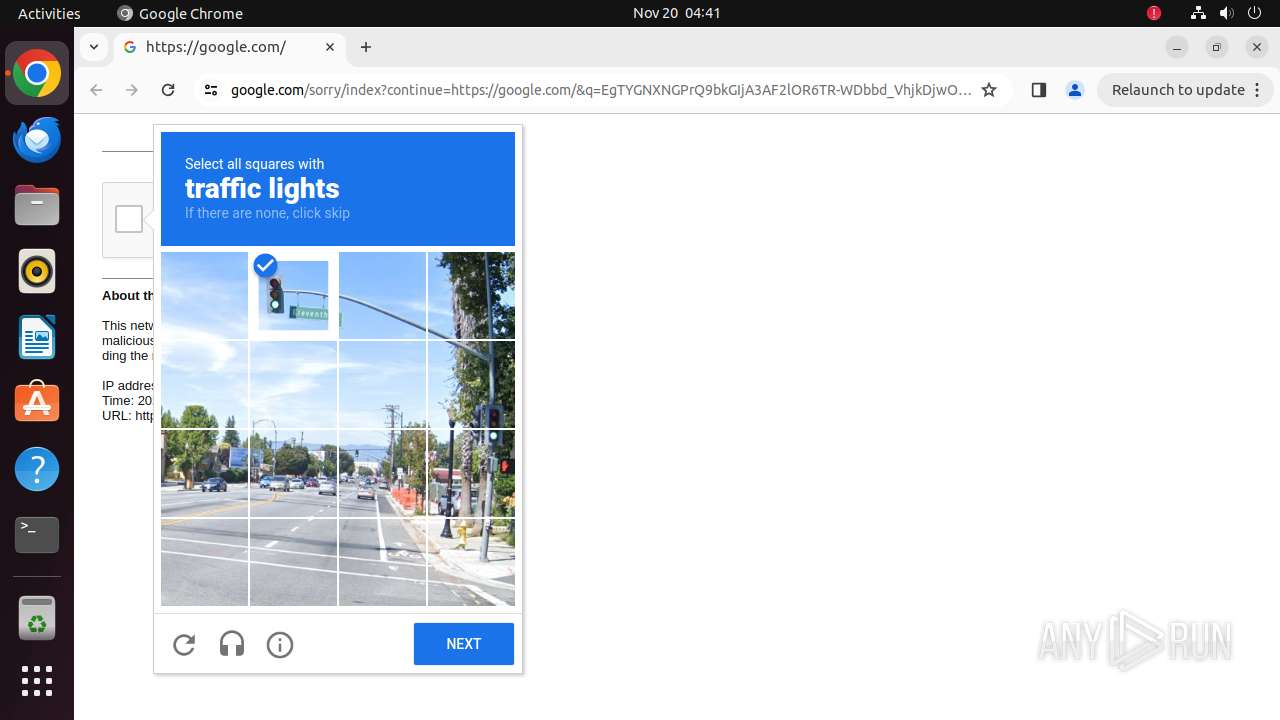
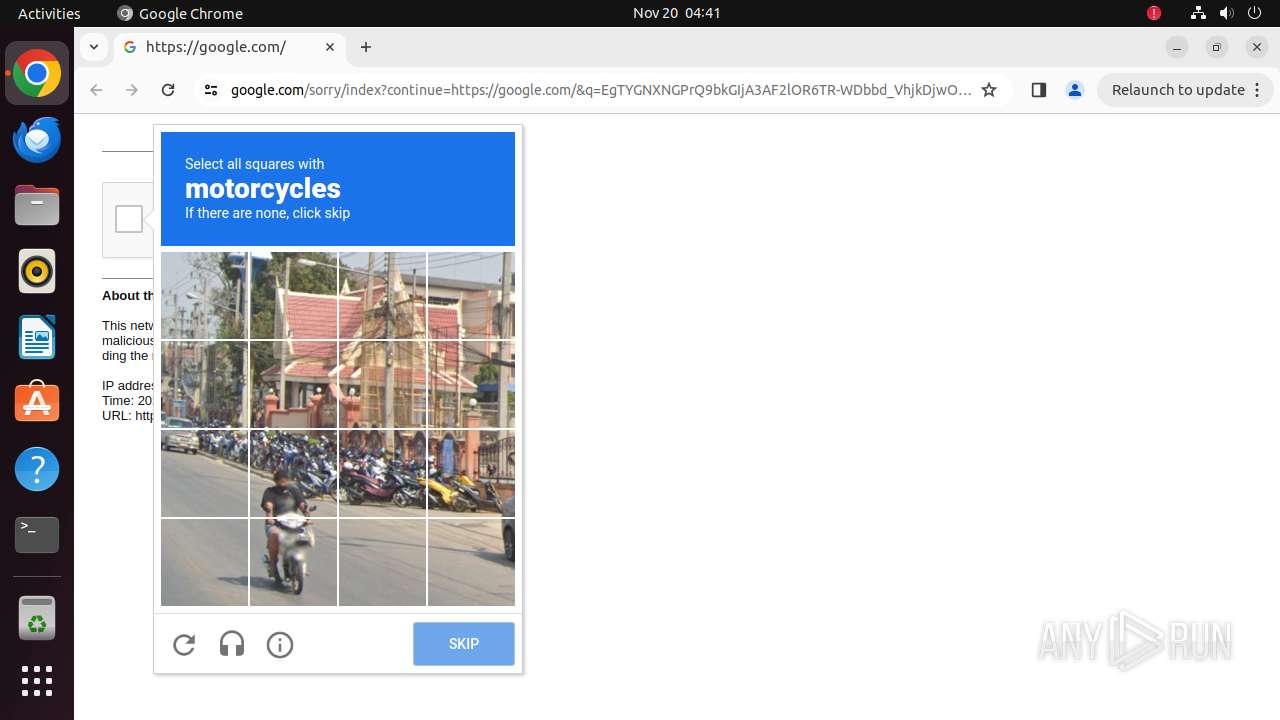
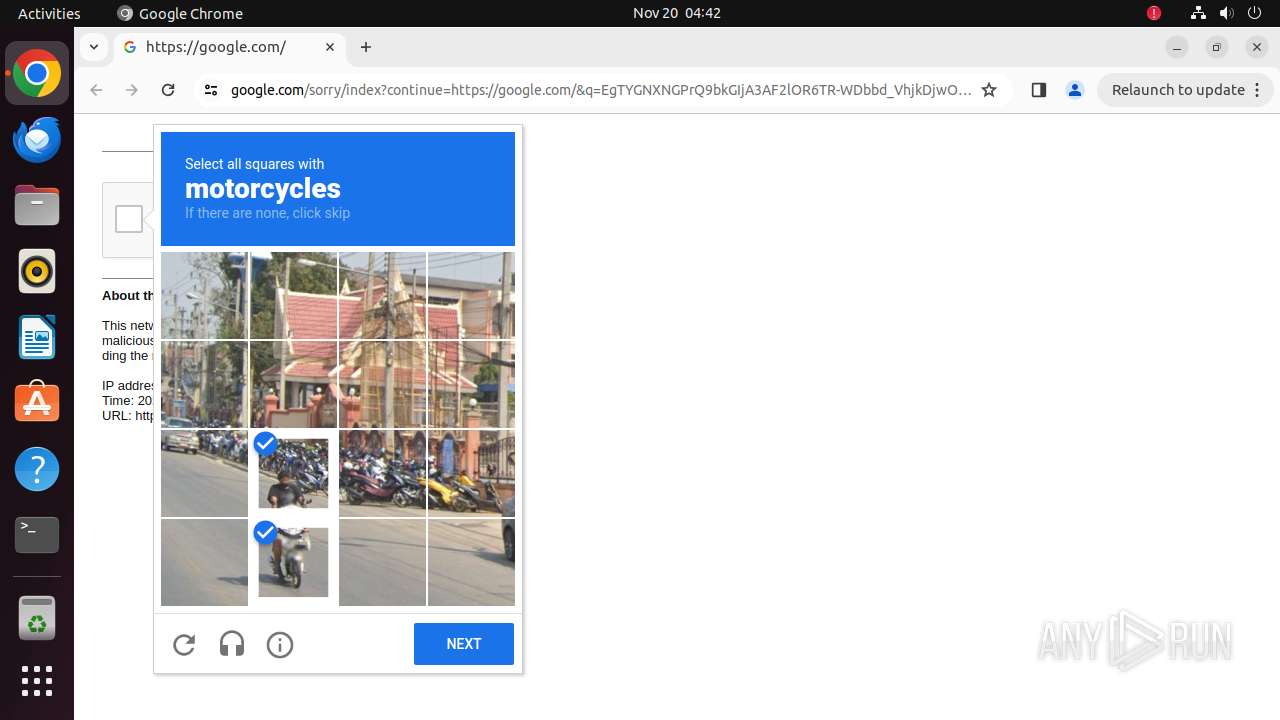
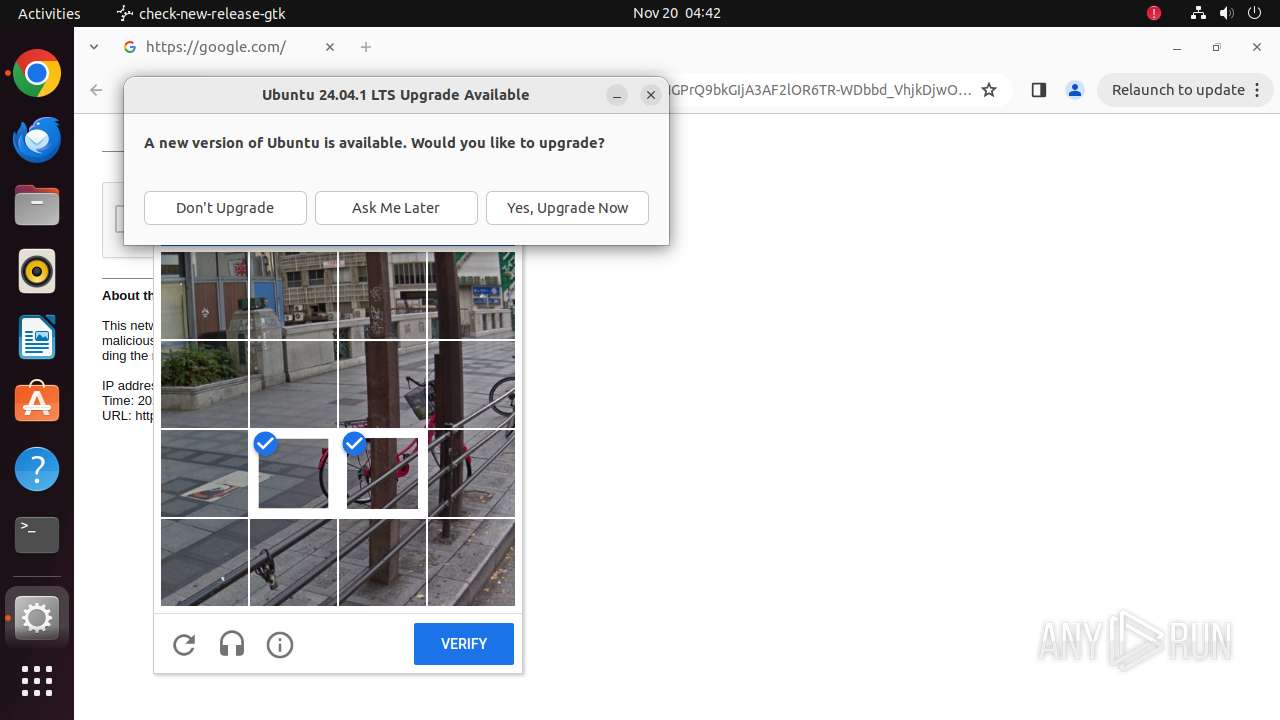
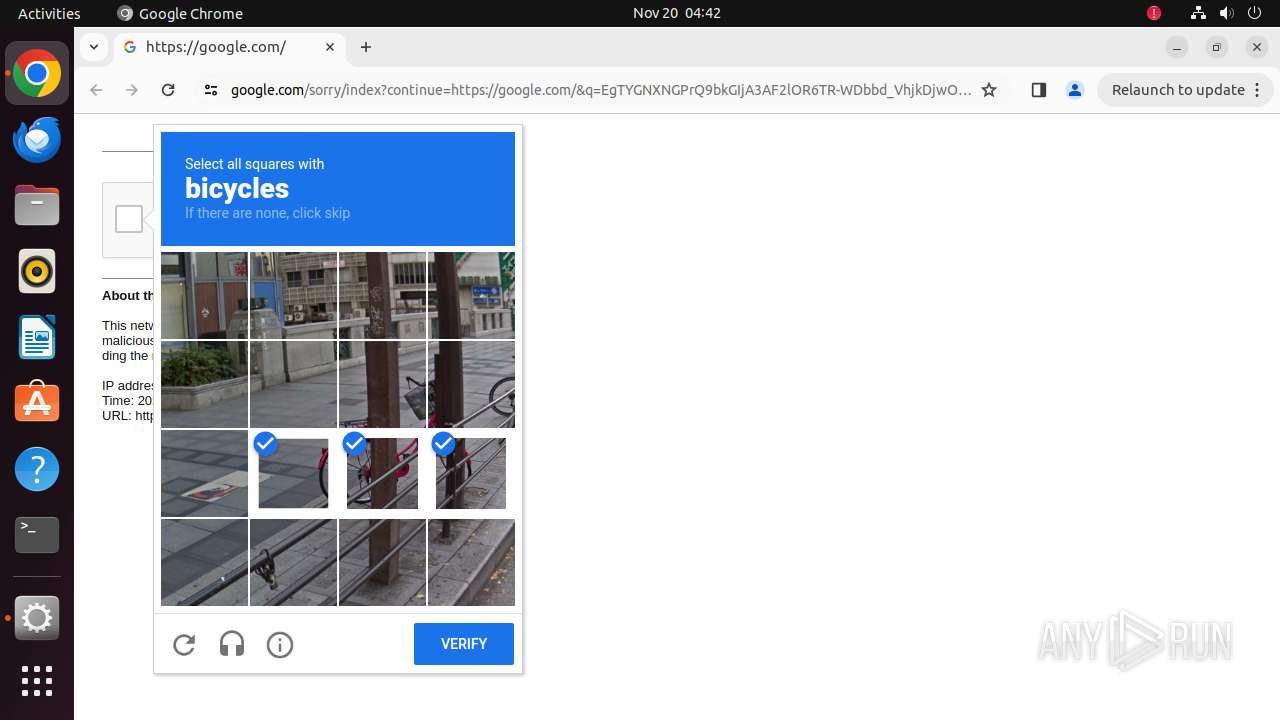
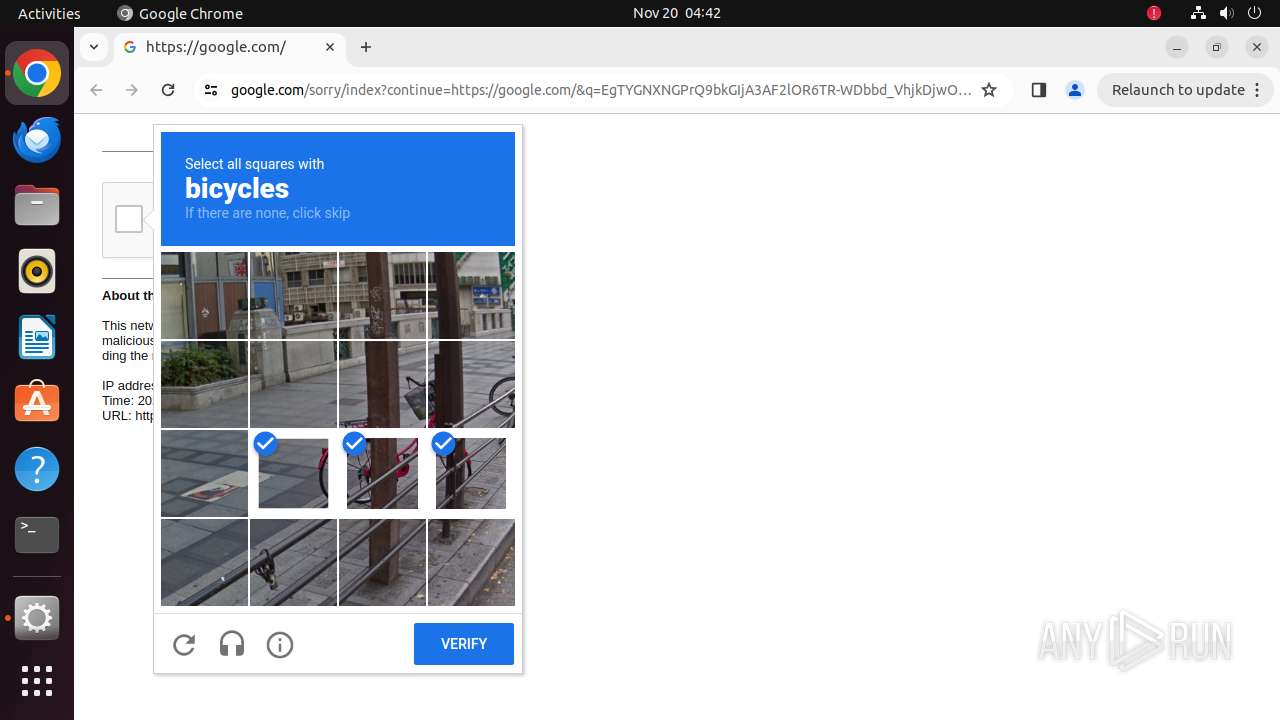
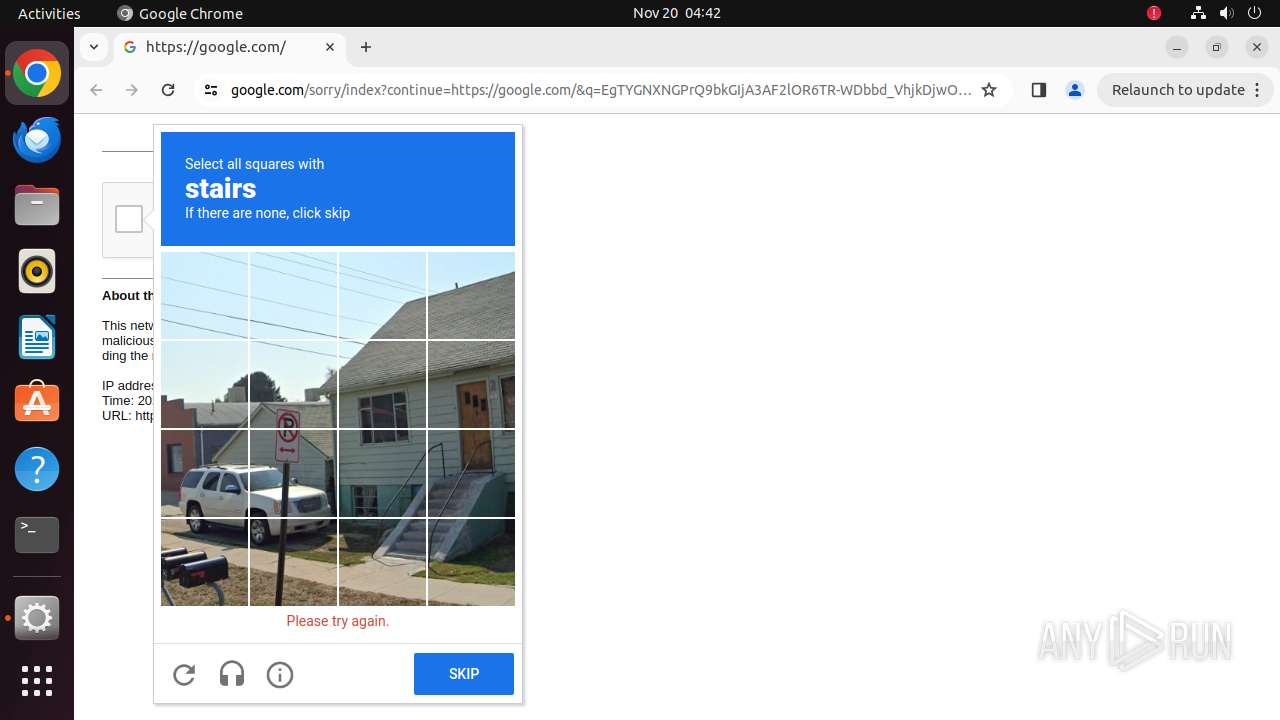
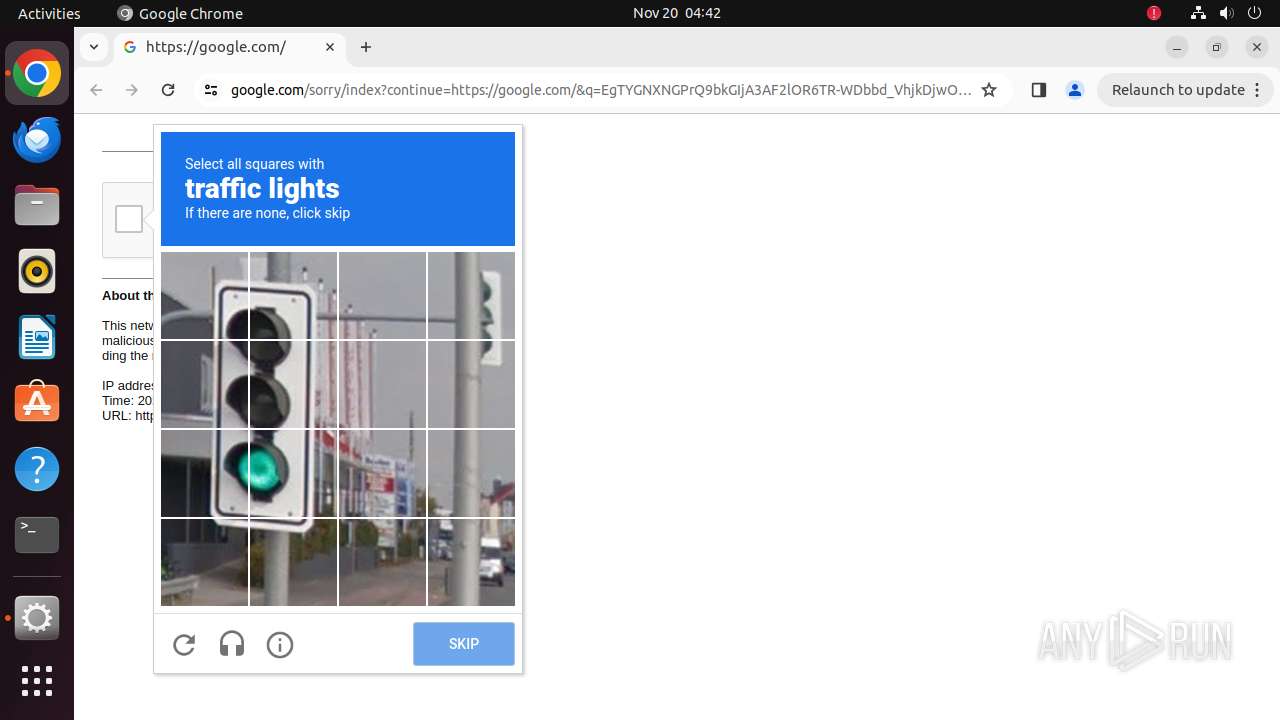
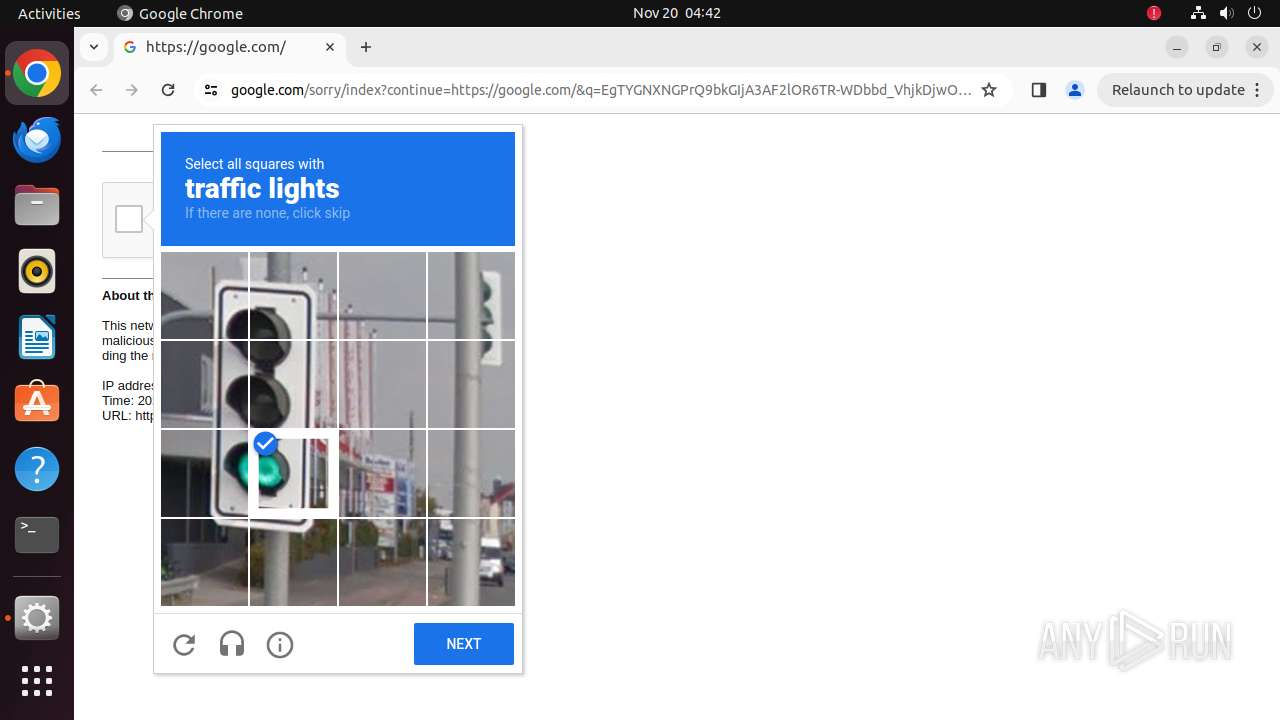
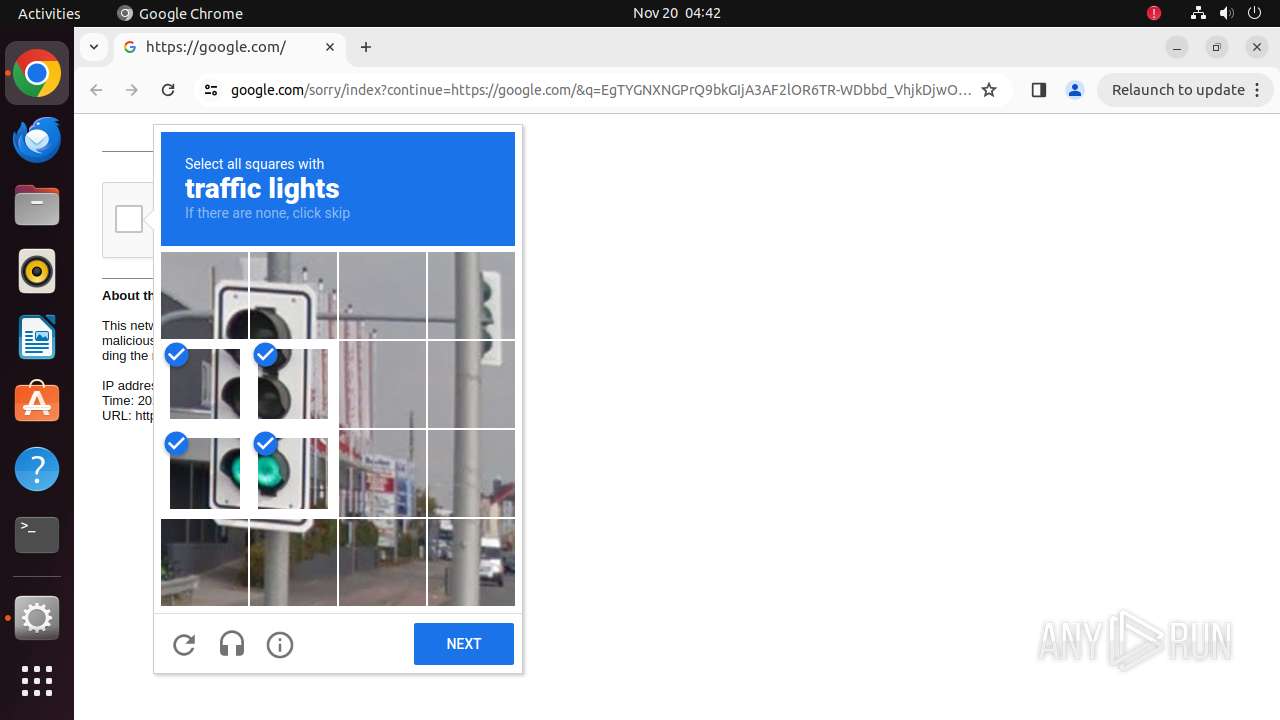
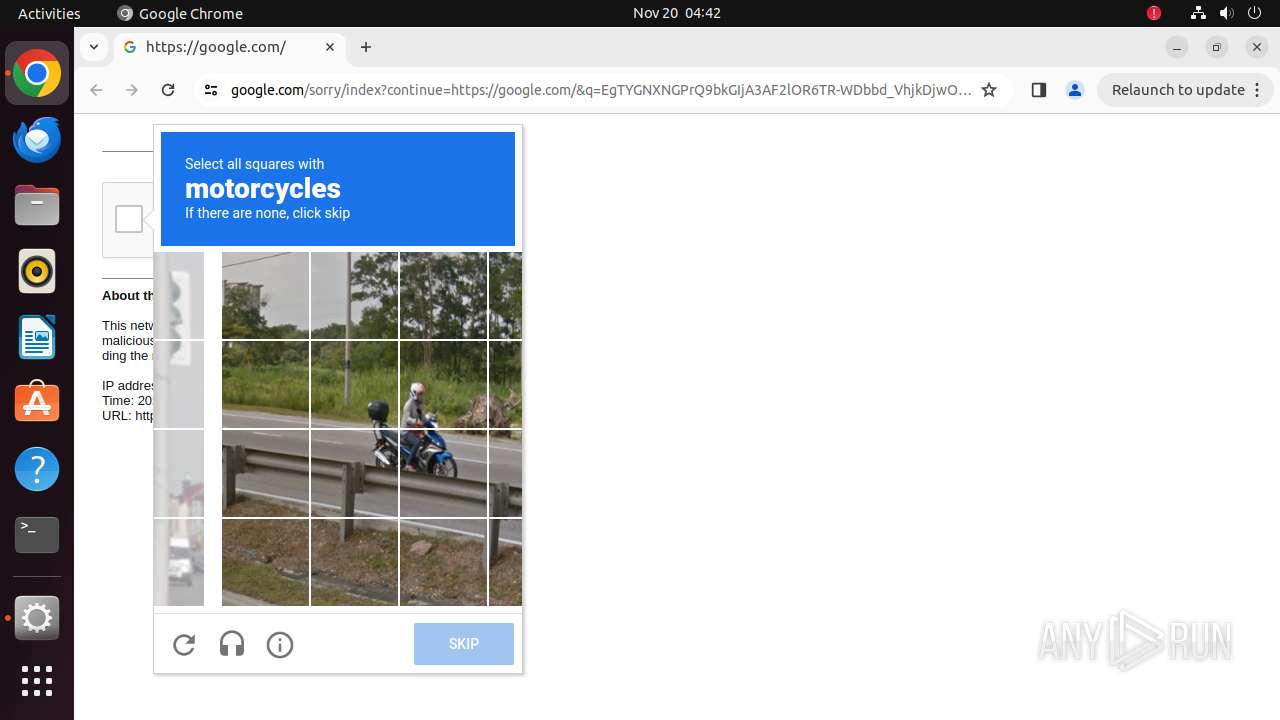
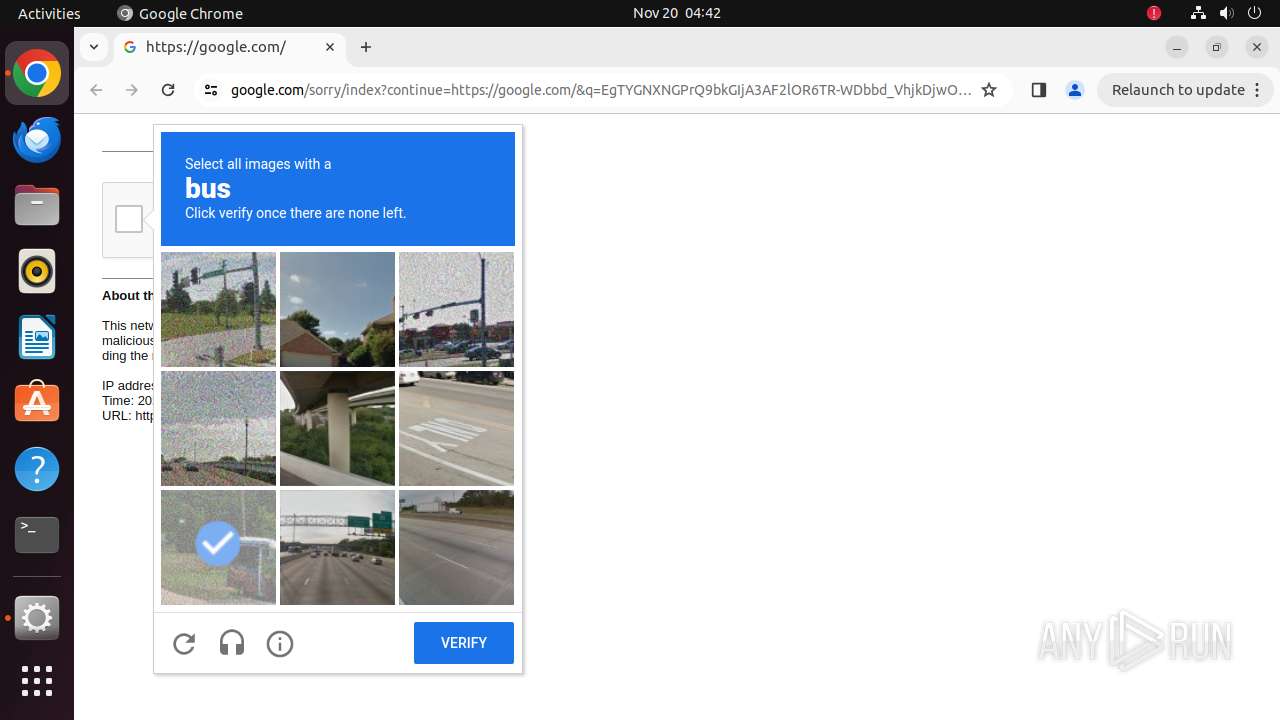
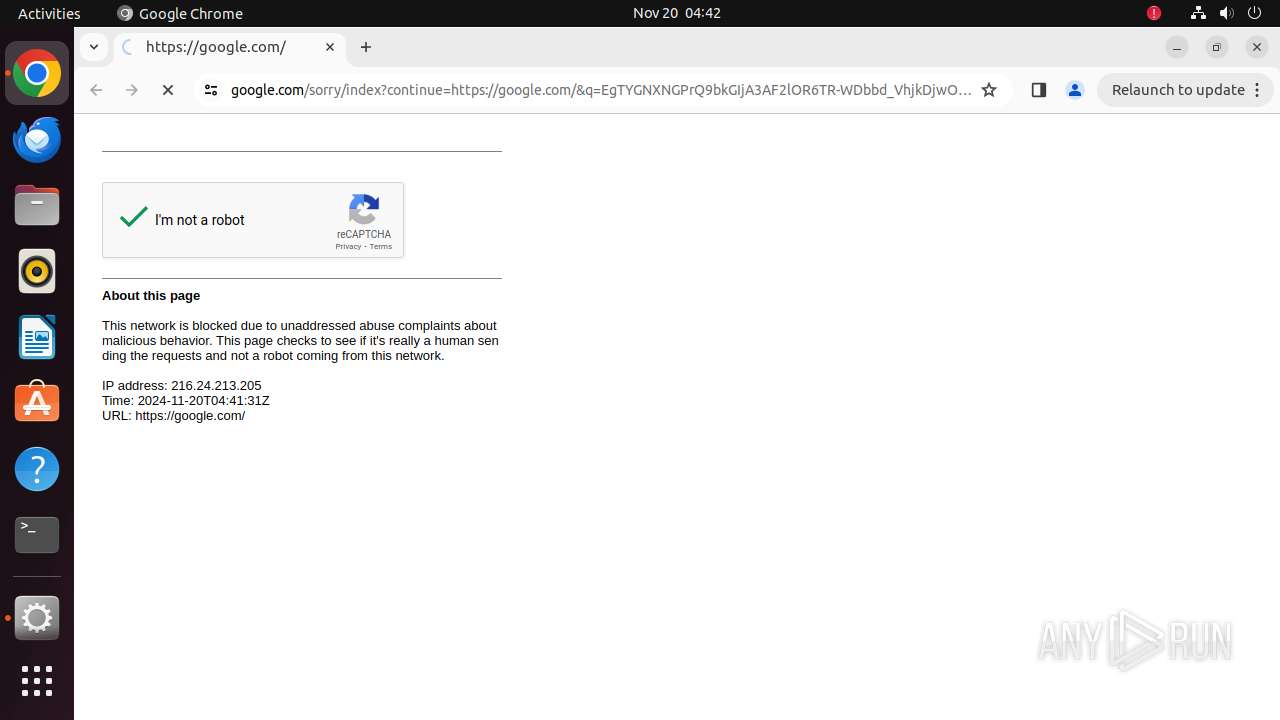
| Verdict: | Malicious activity |
| Analysis date: | November 20, 2024, 04:41:25 |
| OS: | Ubuntu 22.04.2 LTS |
| Tags: | |
| Indicators: | |
| MD5: | CFA03C7F41B36692C4A9CAEF1611A70E |
| SHA1: | A5763E947F2898C99CEE6872BBC37596D83ED3E2 |
| SHA256: | 05FF3FD7502041E09E9D4B7C620B912AB8725DD14F33980E21037EF26CF20D1D |
| SSDEEP: | 3:+RAL0Tn:uAL0T |
MALICIOUS
PHISHING has been detected (SURICATA)
- systemd-resolved (PID: 445)
SUSPICIOUS
Reads /proc/mounts (likely used to find writable filesystems)
- python3.10 (PID: 36031)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
323
Monitored processes
107
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 445 | /lib/systemd/systemd-resolved | /usr/lib/systemd/systemd-resolved | systemd | |
User: systemd-resolve Integrity Level: UNKNOWN | ||||
| 35780 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome budgepenitent\.com " | /usr/bin/dash | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 35781 | sudo -iu user google-chrome budgepenitent.com | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN | ||||
| 35782 | /usr/bin/google-chrome budgepenitent.com | /opt/google/chrome/chrome | sudo | |
User: user Integrity Level: UNKNOWN | ||||
| 35783 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 35784 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 35785 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 35786 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 35787 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 35788 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
Executable files
0
Suspicious files
156
Text files
16
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 35782 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 35782 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 35782 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 35782 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 35782 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 35782 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 35782 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 35782 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 35782 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 35782 | chrome | /home/user/.config/google-chrome/Default/History | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
48
DNS requests
50
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 91.189.91.48:80 | http://connectivity-check.ubuntu.com/ | US | — | — | whitelisted |
— | — | GET | 204 | 91.189.91.48:80 | http://connectivity-check.ubuntu.com/ | US | — | — | whitelisted |
35827 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/japrfto3glzuybauq4wkmtrqte_2024.11.18.0/niikhdgajlphfehepabhhblakbdgeefj_2024.11.18.00_all_acj3wrlm6xavgplit7omufnappaa.crx3 | US | binary | 6.55 Kb | whitelisted |
35827 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/pjnu5jyln4kujhcmwstuyyvyyu_4.10.2830.0/oimompecagnajdejgnnjijobebaeigek_4.10.2830.0_linux_ace35m3jiw32bj5wzzow5nia7yta.crx3 | US | binary | 13.5 Mb | whitelisted |
35827 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/gcmjkmgdlgnkkcocmoeiminaijmmjnii/1.b48b30af5ce18c96128bfff9d2755c7932a1f32adc66f68322f7dd505db9626f/1.cd1978742a4afdbaaa15bf712d5c90bef4144caa99024df98f6a9ad58043ae85/e37724369d5fcfa19bd2ac306e20a9a48dc3fe425aeaacd2bf30802908e3be66 | US | binary | 30.6 Kb | whitelisted |
35827 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/cxxqn654fg7hzrcrrnqcniqqye_2024.10.11.1/kiabhabjdbkjdpjbpigfodbdjmbglcoo_2024.10.11.01_all_jzb2rltf4ebriiaz3nap6gmbai.crx3 | US | binary | 8.87 Kb | whitelisted |
35827 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kkgiwsufde3jfnxs6kccldoxru_20241110.690810062.14/obedbbhbpmojnkanicioggnmelmoomoc_20241110.690810062.14_all_ENGB500000_adnu4iowd4r2vvlmvhmofzio2o4a.crx3 | US | binary | 5.14 Mb | whitelisted |
35827 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/d4kfvvvhbc52b7hvpaxpm752yu_9316/hfnkpimlhhgieaddgfemjhofmfblmnib_9316_all_o7cclcum3swyy4pblvw5ppt7by.crx3 | US | binary | 25.3 Kb | whitelisted |
35827 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/khaoiebndkojlmppeemjhbpbandiljpe/1.05399c5840405f4af2454470ceccaa3d097f07e271705cf37c1e5559ce793eeb/1.1471c6c104c7e11f08fd446f83dcdb396b1fef335f4e3c744007c2272064f538/44367e7bc13464ae48fa3a83edb9a1fc3258aa32540abba470d2ff291e5eaf0e | US | binary | 2.11 Kb | whitelisted |
35827 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acbk3qzfwhzj3ij3hxeo5shqbiyq_3051/jflookgnkcckhobaglndicnbbgbonegd_3051_all_lco5zomzyr2u6axzge5dbiezmu.crx3 | US | binary | 76.7 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 91.189.91.48:80 | changelogs.ubuntu.com | Canonical Group Limited | US | whitelisted |
35827 | chrome | 142.250.181.227:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
35782 | chrome | 239.255.255.250:1900 | — | — | — | whitelisted |
35827 | chrome | 151.101.1.91:443 | google-ohttp-relay-safebrowsing.fastly-edge.com | — | — | unknown |
35827 | chrome | 173.194.79.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
35827 | chrome | 142.250.186.42:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
35827 | chrome | 192.243.59.12:80 | budgepenitent.com | DataWeb Global Group B.V. | US | unknown |
35827 | chrome | 192.243.59.20:443 | budgepenitent.com | DataWeb Global Group B.V. | US | unknown |
35827 | chrome | 142.250.186.174:443 | google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
budgepenitent.com |
| unknown |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
google-ohttp-relay-safebrowsing.fastly-edge.com |
| unknown |
www.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
445 | systemd-resolved | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (budgepenitent .com) |
445 | systemd-resolved | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (budgepenitent .com) |
445 | systemd-resolved | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (budgepenitent .com) |