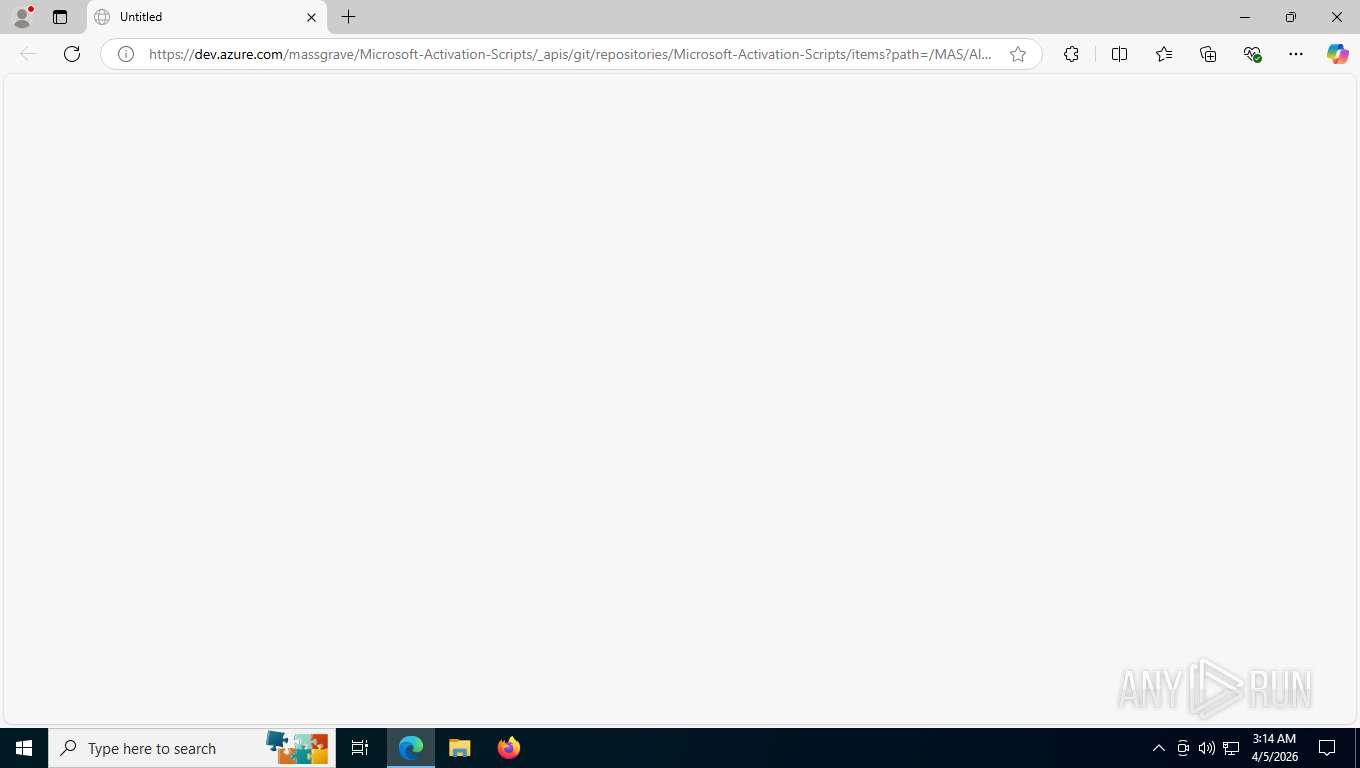
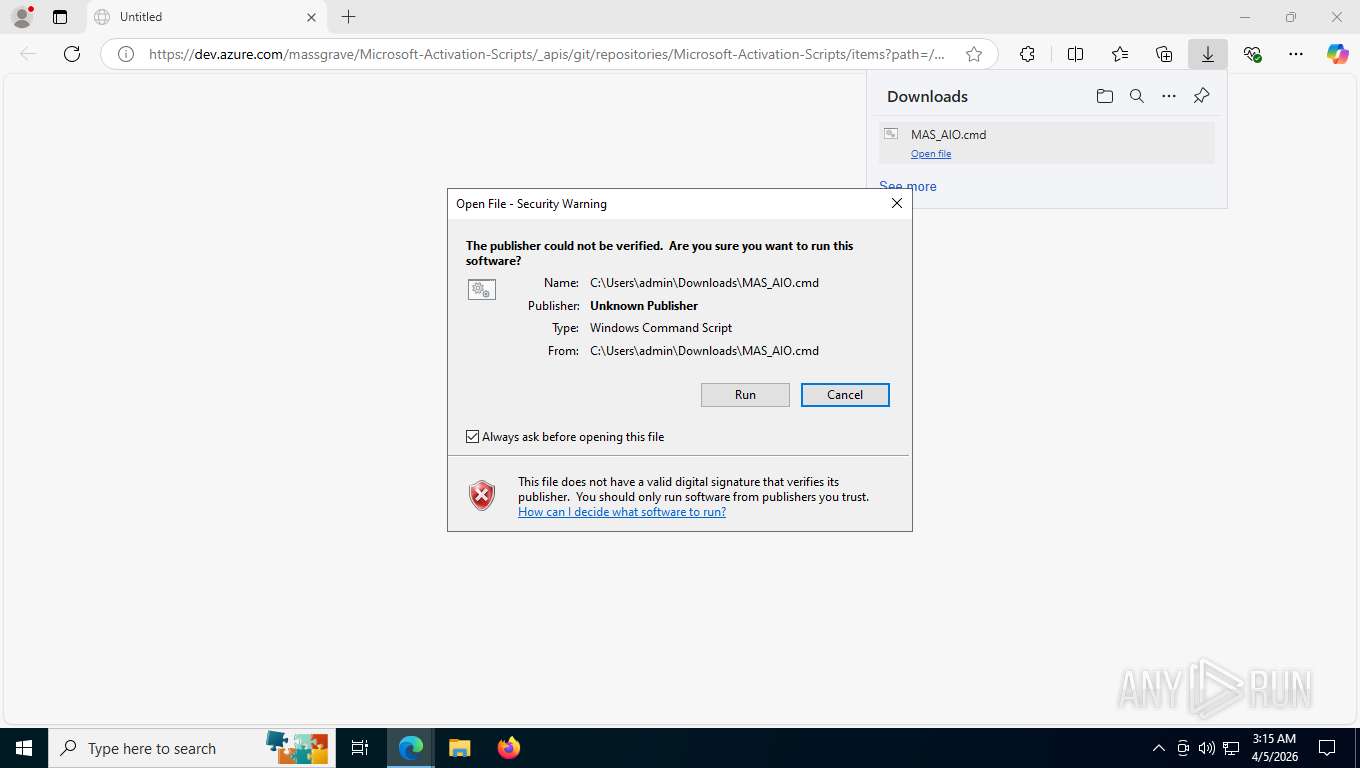
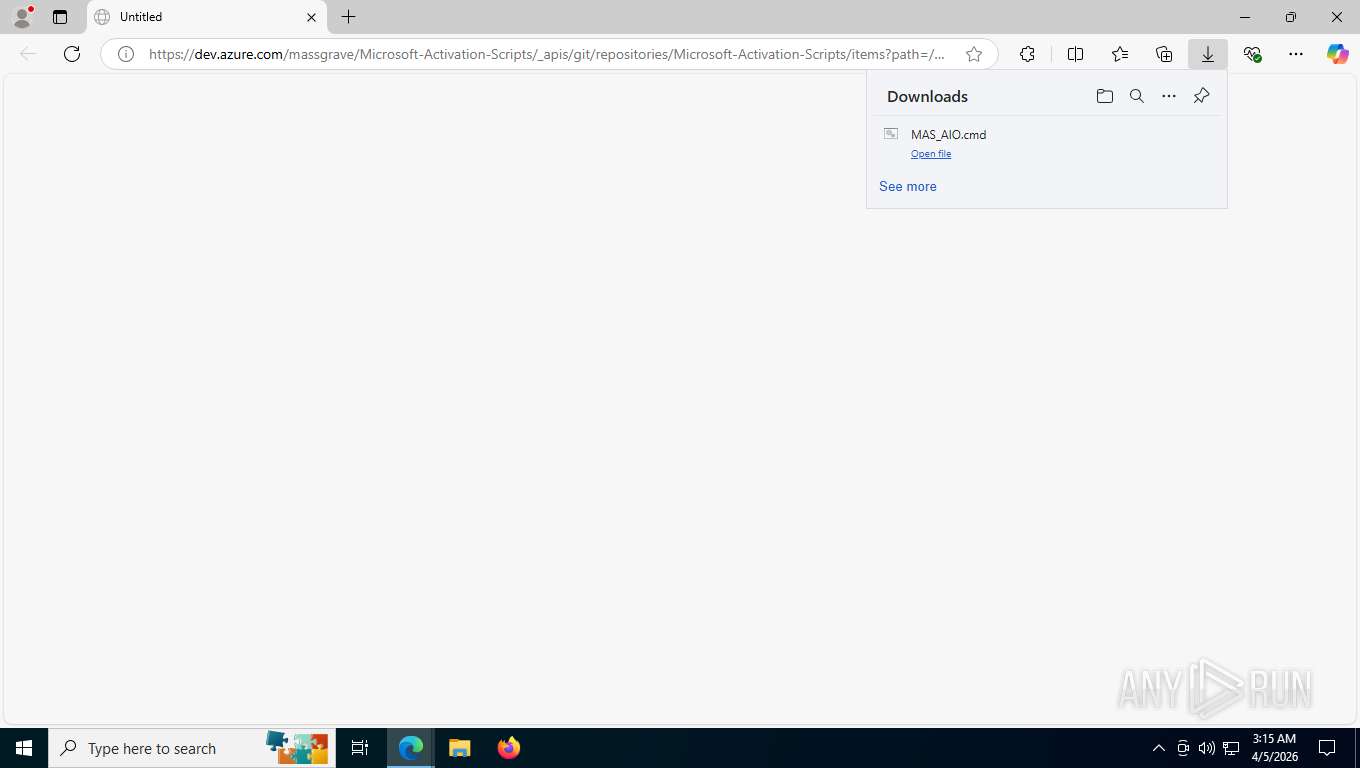
| URL: | https://dev.azure.com/massgrave/Microsoft-Activation-Scripts/_apis/git/repositories/Microsoft-Activation-Scripts/items?path=/MAS/All-In-One-Version-KL/MAS_AIO.cmd&download=true |
| Full analysis: | https://app.any.run/tasks/f30e5e33-eac4-4421-8a18-d450f4793406 |
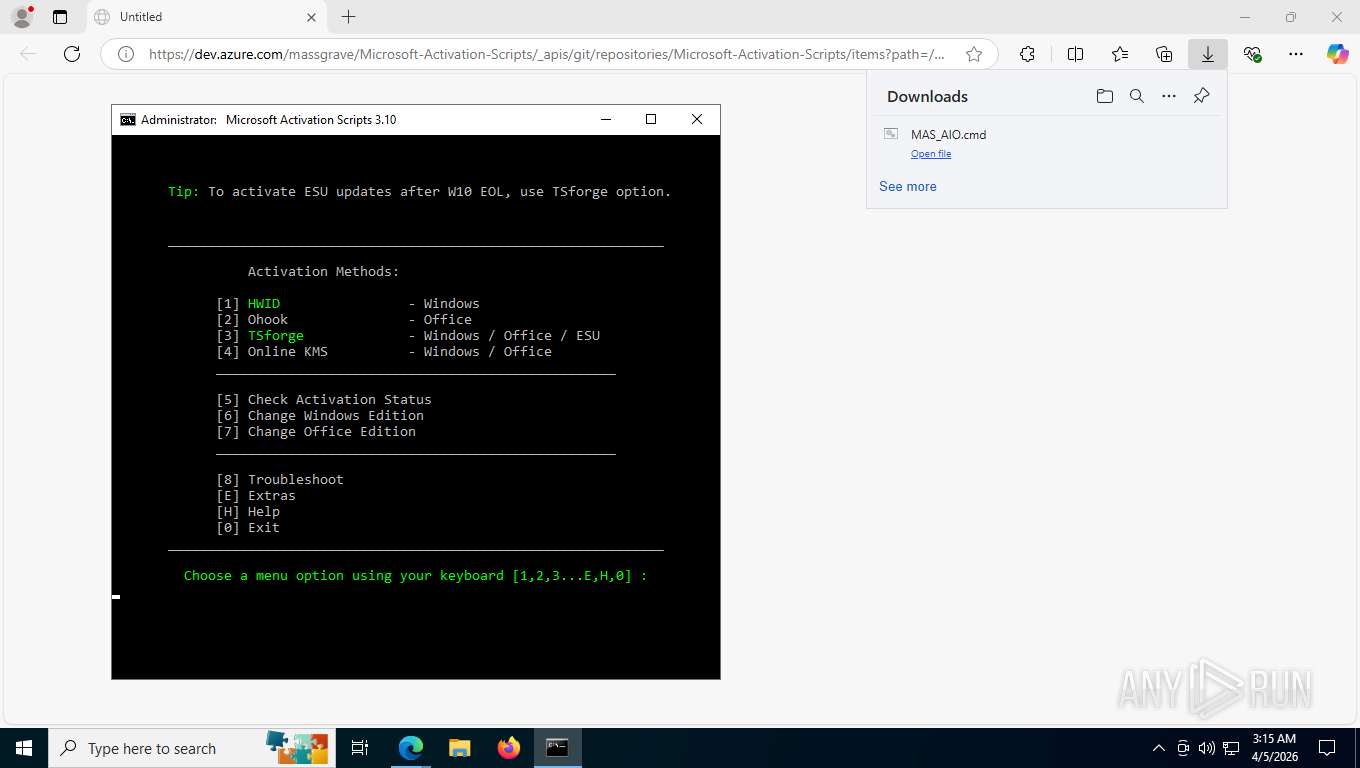
| Verdict: | Malicious activity |
| Analysis date: | April 05, 2026, 07:14:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 4B9E9D16AF12FC9B9185FFA3B491CE23 |
| SHA1: | 1B9B2050425F559A0F5C35712371D1371EE61462 |
| SHA256: | 05F593221E3AC774F6D9DB8F1DF05F794C33DF2CD50E44AE0DDA7FEBFCAD65A4 |
| SSDEEP: | 3:N8Ykf+MgXuukGR3RLLLGXUMCoKL2ZZukGR3RLLLGXUlnXstIqLAOAh9wldKZRl:2Ykf+lXuukGv/LGXUM9KC7ukGv/LGXUT |
MALICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 8504)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 8632)
- cmd.exe (PID: 8740)
- cmd.exe (PID: 9020)
- cmd.exe (PID: 9204)
- cmd.exe (PID: 8344)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 8692)
- cmd.exe (PID: 8752)
- cmd.exe (PID: 8896)
- cmd.exe (PID: 8532)
- cmd.exe (PID: 9192)
- cmd.exe (PID: 8300)
- cmd.exe (PID: 8636)
- cmd.exe (PID: 8592)
- cmd.exe (PID: 8732)
- cmd.exe (PID: 8416)
- cmd.exe (PID: 8744)
- cmd.exe (PID: 1528)
- cmd.exe (PID: 9080)
- cmd.exe (PID: 9128)
Executing commands from ".cmd" file
- msedge.exe (PID: 2956)
- cmd.exe (PID: 8504)
- powershell.exe (PID: 8864)
- cmd.exe (PID: 9020)
- cmd.exe (PID: 8752)
Application launched itself
- cmd.exe (PID: 8504)
- cmd.exe (PID: 8740)
- cmd.exe (PID: 9020)
- cmd.exe (PID: 8344)
- cmd.exe (PID: 8752)
- cmd.exe (PID: 8532)
Windows service management via SC.EXE
- sc.exe (PID: 8568)
- sc.exe (PID: 9100)
- sc.exe (PID: 6804)
- sc.exe (PID: 9048)
Starts CMD.EXE with AutoRun commands disabled
- cmd.exe (PID: 8700)
- cmd.exe (PID: 8756)
- cmd.exe (PID: 8804)
- cmd.exe (PID: 8368)
- cmd.exe (PID: 9164)
- cmd.exe (PID: 8232)
- cmd.exe (PID: 8364)
- cmd.exe (PID: 8984)
- cmd.exe (PID: 8976)
- cmd.exe (PID: 8536)
- cmd.exe (PID: 9124)
- cmd.exe (PID: 8720)
- cmd.exe (PID: 8708)
- cmd.exe (PID: 8804)
Starts CMD.EXE with special quote handling
- cmd.exe (PID: 8700)
- cmd.exe (PID: 8756)
- cmd.exe (PID: 8804)
- cmd.exe (PID: 9164)
- cmd.exe (PID: 8232)
- cmd.exe (PID: 8364)
- cmd.exe (PID: 8368)
- cmd.exe (PID: 8984)
- cmd.exe (PID: 8976)
- cmd.exe (PID: 8536)
- cmd.exe (PID: 9124)
- cmd.exe (PID: 8720)
- cmd.exe (PID: 8708)
- cmd.exe (PID: 8804)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8504)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 9192)
- cmd.exe (PID: 1528)
- cmd.exe (PID: 8752)
- cmd.exe (PID: 8416)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 8504)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 9192)
- cmd.exe (PID: 8416)
- cmd.exe (PID: 8752)
- cmd.exe (PID: 1528)
Executes script without checking the security policy
- powershell.exe (PID: 8864)
- powershell.exe (PID: 8524)
- powershell.exe (PID: 9200)
- powershell.exe (PID: 8616)
- powershell.exe (PID: 8836)
- powershell.exe (PID: 8548)
- powershell.exe (PID: 8564)
Converts TXT file into a string
- powershell.exe (PID: 8524)
- powershell.exe (PID: 9200)
- powershell.exe (PID: 8548)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 8500)
- cmd.exe (PID: 9192)
- cmd.exe (PID: 8752)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 8524)
- powershell.exe (PID: 9200)
- powershell.exe (PID: 8548)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 8524)
- powershell.exe (PID: 9200)
- powershell.exe (PID: 8548)
Queries Computer System Information (Win32_ComputerSystem) (SCRIPT)
- powershell.exe (PID: 8524)
- powershell.exe (PID: 9200)
- powershell.exe (PID: 8548)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 8524)
- powershell.exe (PID: 9200)
- powershell.exe (PID: 8548)
Hides command output
- cmd.exe (PID: 8500)
- cmd.exe (PID: 9192)
- cmd.exe (PID: 8416)
- cmd.exe (PID: 9128)
- cmd.exe (PID: 9080)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 8744)
Obfuscation pattern (POWERSHELL)
- powershell.exe (PID: 8564)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 9080)
INFO
Reads Environment values
- identity_helper.exe (PID: 7392)
Reads the computer name
- identity_helper.exe (PID: 7392)
Application launched itself
- msedge.exe (PID: 2956)
Checks supported languages
- identity_helper.exe (PID: 7392)
- mode.com (PID: 8672)
- mode.com (PID: 8492)
- mode.com (PID: 9096)
- mode.com (PID: 8488)
- mode.com (PID: 2324)
Checks operating system version
- cmd.exe (PID: 8504)
- cmd.exe (PID: 9020)
- cmd.exe (PID: 8752)
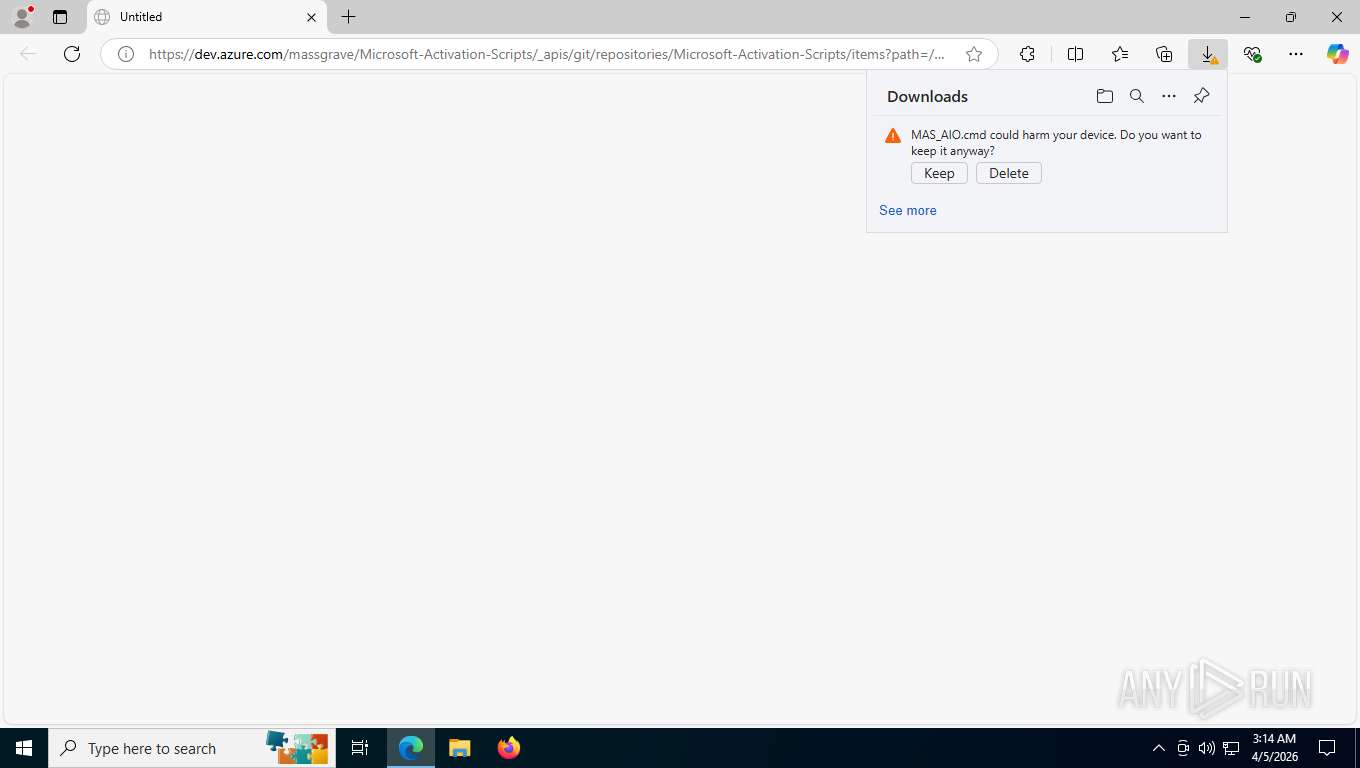
Launching a file from the Downloads directory
- msedge.exe (PID: 2956)
Search a value from a registry key
- reg.exe (PID: 8652)
- reg.exe (PID: 7768)
- reg.exe (PID: 8704)
- reg.exe (PID: 8940)
- cmd.exe (PID: 8732)
- reg.exe (PID: 9060)
- cmd.exe (PID: 9128)
- reg.exe (PID: 8532)
- reg.exe (PID: 8796)
- reg.exe (PID: 7924)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 8524)
- powershell.exe (PID: 9200)
- powershell.exe (PID: 8548)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 8524)
- powershell.exe (PID: 9200)
- powershell.exe (PID: 8548)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 8524)
- powershell.exe (PID: 9200)
- powershell.exe (PID: 8548)
Starts MODE.COM to configure console settings
- mode.com (PID: 8672)
- mode.com (PID: 8492)
- mode.com (PID: 2324)
- mode.com (PID: 9096)
- mode.com (PID: 8488)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 9012)
- WMIC.exe (PID: 9140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
268
Monitored processes
131
Malicious processes
10
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1528 | C:\WINDOWS\System32\cmd.exe /c "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe -nop -c $AssemblyBuilder = [AppDomain]::CurrentDomain.DefineDynamicAssembly(4, 1); $ModuleBuilder = $AssemblyBuilder.DefineDynamicModule(2, $False); $TypeBuilder = $ModuleBuilder.DefineType(0); [void]$TypeBuilder.DefinePInvokeMethod('SLGetWindowsInformationDWORD', 'slc.dll', 'Public, Static', 1, [int], @([String], [int].MakeByRefType()), 1, 3); $Sku = 0; [void]$TypeBuilder.CreateType()::SLGetWindowsInformationDWORD('Kernel-BrandingInfo', [ref]$Sku); $Sku" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4372,i,8907673530928681063,8553203188848752521,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=7540 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6548,i,8907673530928681063,8553203188848752521,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6560 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2324 | mode 76, 33 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2692 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x294,0x298,0x29c,0x28c,0x2a4,0x7ffe2392f208,0x7ffe2392f214,0x7ffe2392f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2956 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --disable-features=HttpsUpgrades,HttpsFirstModeV2,HttpsOnlyMode,HttpsFirstBalancedMode --no-first-run --no-default-browser-check https://dev.azure.com/massgrave/Microsoft-Activation-Scripts/_apis/git/repositories/Microsoft-Activation-Scripts/items?path=/MAS/All-In-One-Version-KL/MAS_AIO.cmd&download=true | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3612 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=12 --always-read-main-dll --field-trial-handle=6080,i,8907673530928681063,8553203188848752521,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6152 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3996 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2396,i,8907673530928681063,8553203188848752521,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2440 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4276 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3632,i,8907673530928681063,8553203188848752521,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3708 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4708 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3616,i,8907673530928681063,8553203188848752521,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3628 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
35 452
Read events
35 452
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
28
Text files
271
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFdffbd.TMP | — | |
MD5:— | SHA256:— | |||
| 2956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFdffcd.TMP | — | |
MD5:— | SHA256:— | |||
| 2956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFdffcd.TMP | — | |
MD5:— | SHA256:— | |||
| 2956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFdffcd.TMP | — | |
MD5:— | SHA256:— | |||
| 2956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFdffdc.TMP | — | |
MD5:— | SHA256:— | |||
| 2956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
48
TCP/UDP connections
50
DNS requests
48
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3996 | msedge.exe | GET | 304 | 150.171.28.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | US | — | — | whitelisted |
3996 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:CdyRFyFKXOaPhwAatocXAUAhTwv1L9oauvQtDxwok_0&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 101 b | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 958 b | whitelisted |
3996 | msedge.exe | GET | 200 | 52.123.224.69:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=67&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | US | text | 4.60 Kb | whitelisted |
3996 | msedge.exe | GET | 200 | 104.18.23.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
3996 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 314 b | whitelisted |
3996 | msedge.exe | GET | 200 | 150.171.73.16:443 | https://dev.azure.com/massgrave/Microsoft-Activation-Scripts/_apis/git/repositories/Microsoft-Activation-Scripts/items?path=/MAS/All-In-One-Version-KL/MAS_AIO.cmd&download=true | US | text | 743 Kb | malicious |
3996 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/extensionwebstorebase/v1/crx?os=win&arch=x64&os_arch=x86_64&nacl_arch=x86-64&prod=edgecrx&prodchannel=&prodversion=133.0.3065.92&lang=en-US&acceptformat=crx3,puff&x=id%3Djmjflgjpcpepeafmmgdpfkogkghcpiha%26v%3D1.2.1%26installedby%3Dother%26uc%26ping%3Dr%253D107%2526e%253D1 | US | xml | 413 b | whitelisted |
3996 | msedge.exe | POST | 200 | 142.251.13.94:443 | https://update.googleapis.com/service/update2/json?cup2key=14:ItY1sIoOg0xrLrcTbR3nhqfRQXnLEJgSTP8Xv5_0CVs&cup2hreq=21db3865fff969871911ce34e44872ac854896ad87a67b7c2116b17b80de3a5f | US | text | 889 b | whitelisted |
3996 | msedge.exe | GET | 200 | 13.107.226.44:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | US | binary | 82 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
4212 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.204.156:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.11.41.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3996 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3996 | msedge.exe | 52.123.224.69:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
dev.azure.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3996 | msedge.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Get-WmiObject Cmdlet has been detected |
3996 | msedge.exe | A Network Trojan was detected | ET ATTACK_RESPONSE PowerShell Internet Connectivity Check via Network GUID Inbound |
3996 | msedge.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Windows OS Version extraction by PS.Script has been detected |
3996 | msedge.exe | Potentially Bad Traffic | ET ATTACK_RESPONSE PowerShell NoProfile Command Received In Powershell Stagers |
3996 | msedge.exe | Potentially Bad Traffic | ET HUNTING schtasks delete Command in HTTP Body Response |
3996 | msedge.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Windows security identifiers S-1-5-18 (NT AuthoritySystem) has been detected |
3996 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] The Principal.WindowsIdentity in PS.Script has been detected |
3996 | msedge.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Check Security.Principal.WindowsBuiltInRole has been detected |
3996 | msedge.exe | Potentially Bad Traffic | ET HUNTING PowerShell Hidden Window Command Common In Powershell Stagers M2 |
3996 | msedge.exe | Misc activity | ET INFO Powershell Base64 Decode Command Inbound |