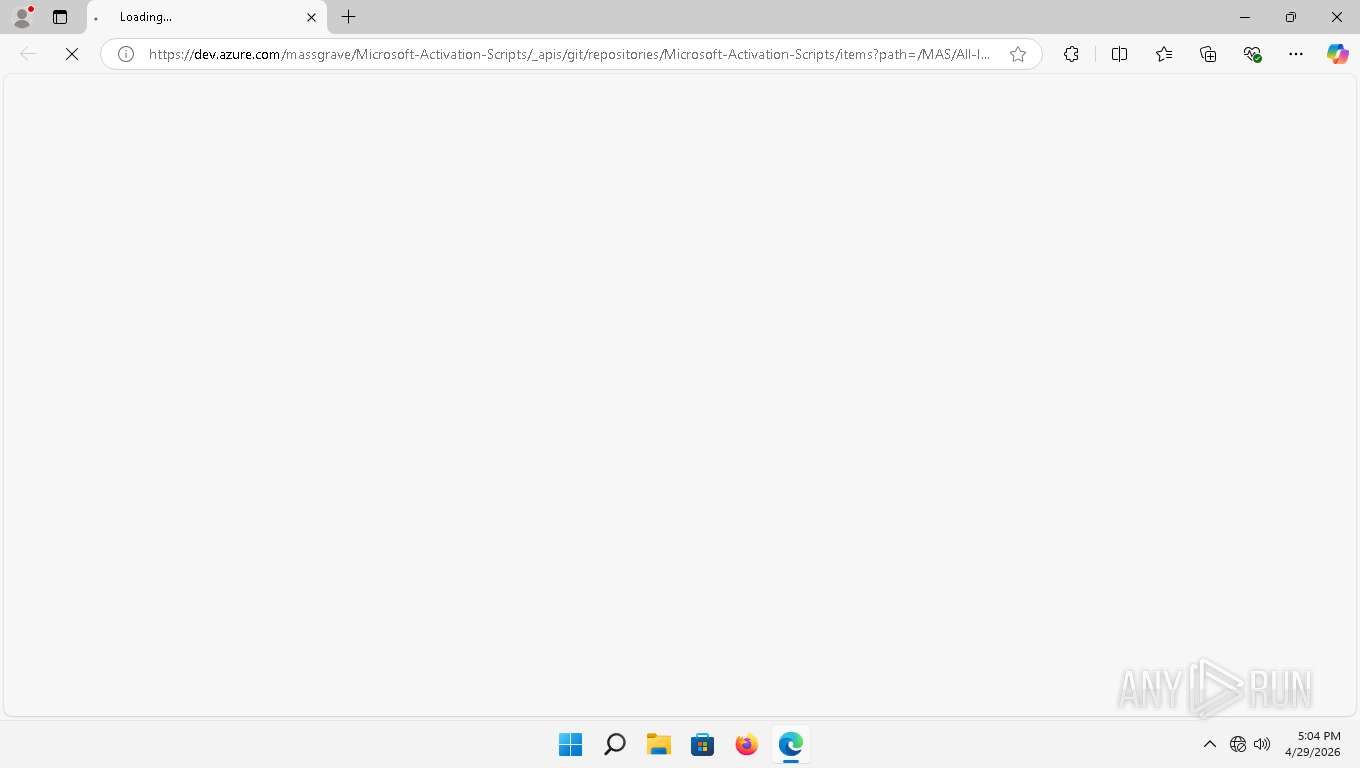
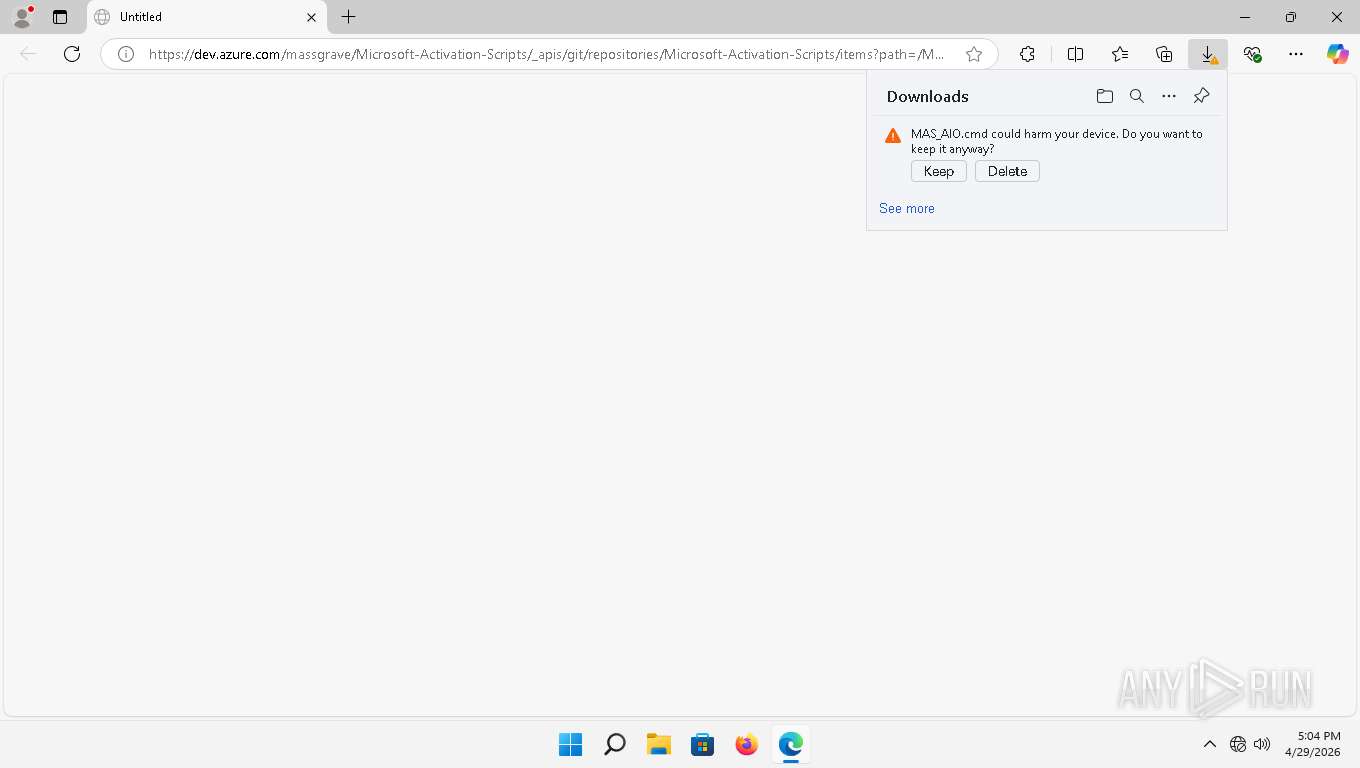
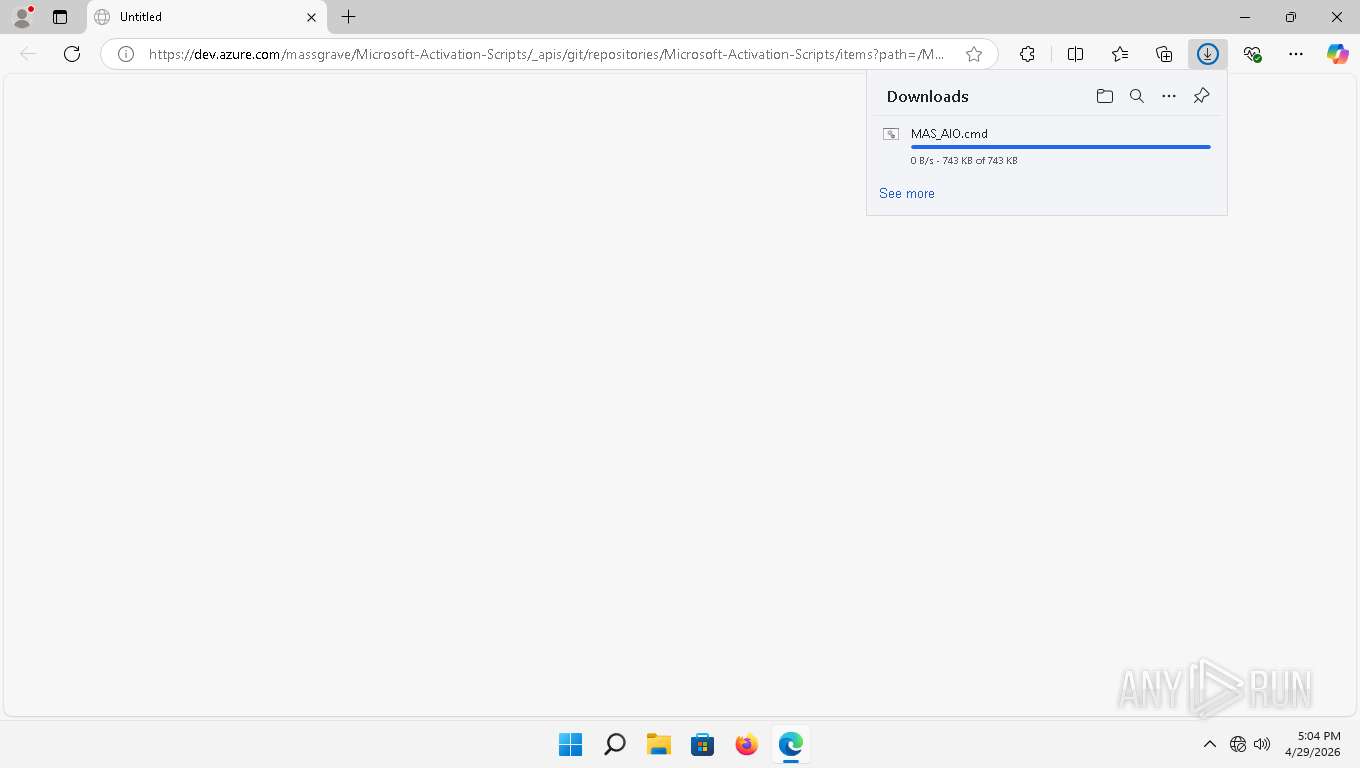
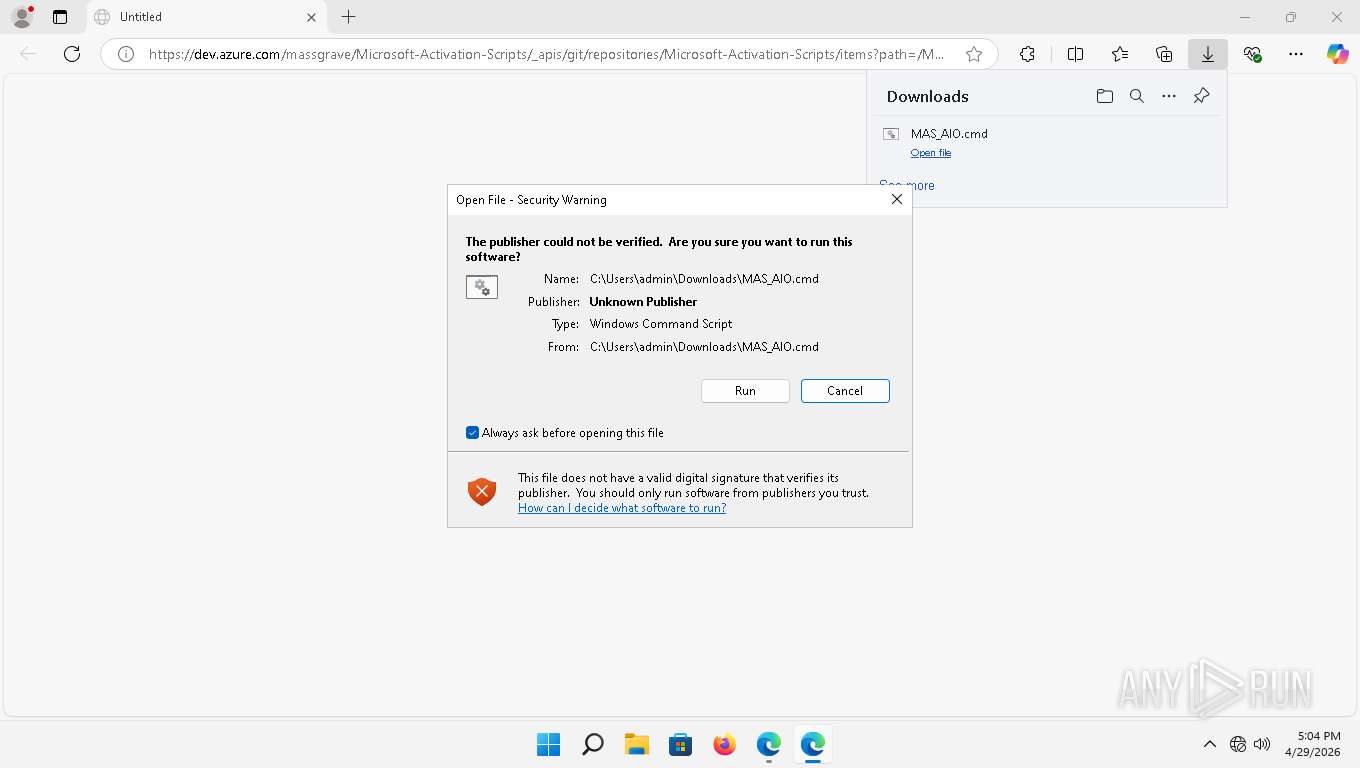
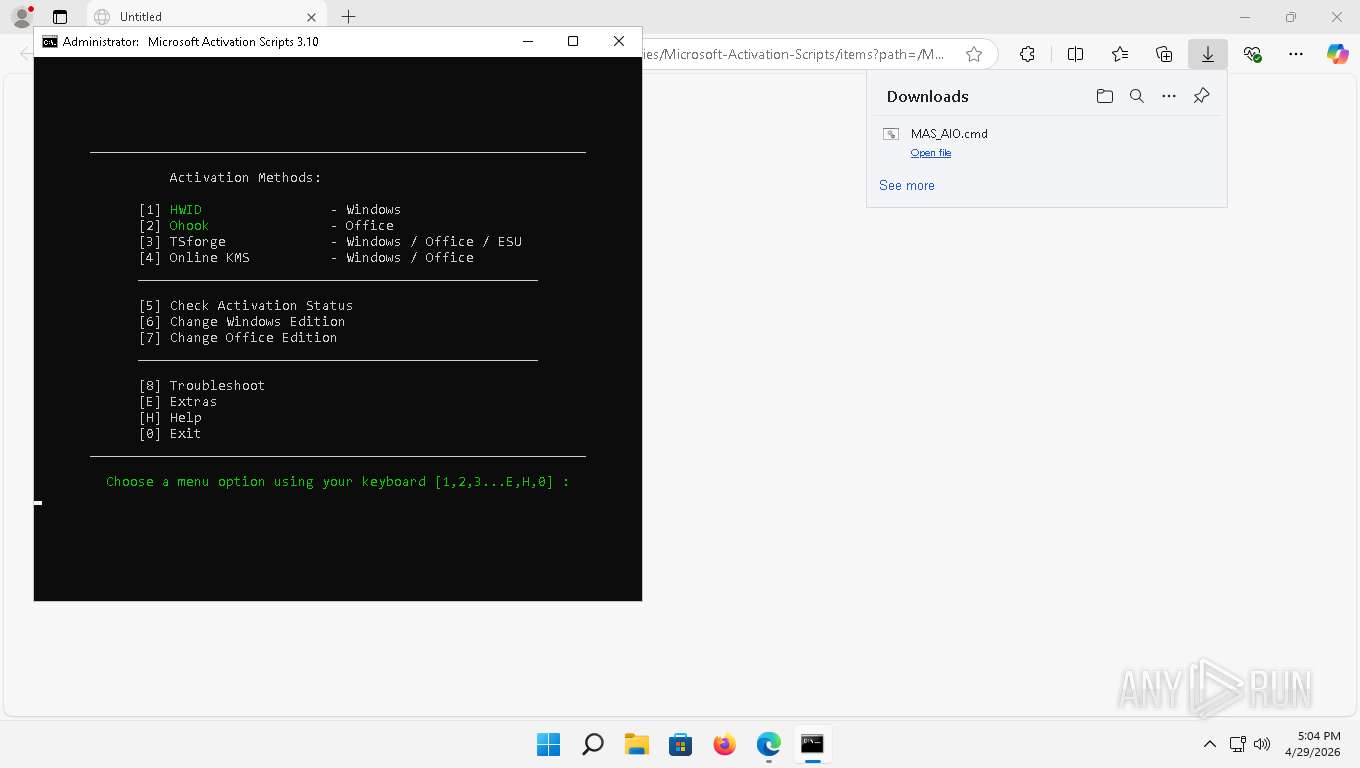
| URL: | https://dev.azure.com/massgrave/Microsoft-Activation-Scripts/_apis/git/repositories/Microsoft-Activation-Scripts/items?path=/MAS/All-In-One-Version-KL/MAS_AIO.cmd&download=true |
| Full analysis: | https://app.any.run/tasks/ed026d7b-c8c8-46c2-8b19-8407a43a10a5 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2026, 21:04:32 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 4B9E9D16AF12FC9B9185FFA3B491CE23 |
| SHA1: | 1B9B2050425F559A0F5C35712371D1371EE61462 |
| SHA256: | 05F593221E3AC774F6D9DB8F1DF05F794C33DF2CD50E44AE0DDA7FEBFCAD65A4 |
| SSDEEP: | 3:N8Ykf+MgXuukGR3RLLLGXUMCoKL2ZZukGR3RLLLGXUlnXstIqLAOAh9wldKZRl:2Ykf+lXuukGv/LGXUM9KC7ukGv/LGXUT |
MALICIOUS
Usage of PowerShell observed
- msedge.exe (PID: 7048)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 8136)
SUSPICIOUS
Usage of PowerShell observed
- msedge.exe (PID: 7048)
Starts CMD.EXE with AutoRun commands disabled
- cmd.exe (PID: 1316)
- cmd.exe (PID: 5372)
- cmd.exe (PID: 8000)
- cmd.exe (PID: 3908)
- cmd.exe (PID: 644)
- cmd.exe (PID: 1872)
- cmd.exe (PID: 4876)
- cmd.exe (PID: 6772)
- cmd.exe (PID: 8008)
- cmd.exe (PID: 7536)
- cmd.exe (PID: 2896)
- cmd.exe (PID: 6668)
- cmd.exe (PID: 2716)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7672)
- cmd.exe (PID: 4644)
- cmd.exe (PID: 6768)
- cmd.exe (PID: 7564)
- cmd.exe (PID: 7912)
- cmd.exe (PID: 2800)
- cmd.exe (PID: 7536)
- cmd.exe (PID: 8160)
- cmd.exe (PID: 7984)
- cmd.exe (PID: 7980)
- cmd.exe (PID: 7916)
- cmd.exe (PID: 8108)
- cmd.exe (PID: 4148)
- cmd.exe (PID: 3216)
- cmd.exe (PID: 6924)
Starts CMD.EXE with special quote handling
- cmd.exe (PID: 1316)
- cmd.exe (PID: 5372)
- cmd.exe (PID: 8000)
- cmd.exe (PID: 3908)
- cmd.exe (PID: 1872)
- cmd.exe (PID: 644)
- cmd.exe (PID: 4876)
- cmd.exe (PID: 6772)
- cmd.exe (PID: 8008)
- cmd.exe (PID: 7536)
- cmd.exe (PID: 2896)
- cmd.exe (PID: 2716)
- cmd.exe (PID: 6668)
Application launched itself
- cmd.exe (PID: 4644)
- cmd.exe (PID: 7980)
Executing commands from ".cmd" file
- cmd.exe (PID: 8136)
- msedge.exe (PID: 3816)
- powershell.exe (PID: 2852)
- cmd.exe (PID: 6768)
- cmd.exe (PID: 8160)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 8136)
- cmd.exe (PID: 2800)
- cmd.exe (PID: 7916)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8136)
- cmd.exe (PID: 2800)
- cmd.exe (PID: 7916)
Executes script without checking the security policy
- powershell.exe (PID: 2852)
- powershell.exe (PID: 8008)
- powershell.exe (PID: 3196)
Windows service management via SC.EXE
- sc.exe (PID: 7228)
- sc.exe (PID: 2468)
- sc.exe (PID: 7900)
Reads the Internet Settings
- powershell.exe (PID: 2852)
Hides command output
- cmd.exe (PID: 2800)
- cmd.exe (PID: 7916)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 2800)
- cmd.exe (PID: 7916)
Converts TXT file into a string
- powershell.exe (PID: 8008)
- powershell.exe (PID: 3196)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 8008)
- powershell.exe (PID: 3196)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 8008)
- powershell.exe (PID: 3196)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 8008)
- powershell.exe (PID: 3196)
Queries Computer System Information (Win32_ComputerSystem) (SCRIPT)
- powershell.exe (PID: 8008)
- powershell.exe (PID: 3196)
Uses REG/REGEDIT.EXE to modify or delete registry entries
- cmd.exe (PID: 6768)
INFO
Application launched itself
- msedge.exe (PID: 3816)
- cmd.exe (PID: 8136)
- cmd.exe (PID: 6768)
- cmd.exe (PID: 7912)
- cmd.exe (PID: 8160)
Checks supported languages
- identity_helper.exe (PID: 7848)
- mode.com (PID: 6344)
- mode.com (PID: 1932)
- mode.com (PID: 5996)
Reads the computer name
- identity_helper.exe (PID: 7848)
Reads Environment values
- identity_helper.exe (PID: 7848)
Checks operating system version
- cmd.exe (PID: 8136)
- cmd.exe (PID: 6768)
- cmd.exe (PID: 8160)
Search a value from a registry key
- reg.exe (PID: 7648)
- reg.exe (PID: 6344)
- reg.exe (PID: 7872)
- reg.exe (PID: 4148)
- reg.exe (PID: 2896)
- cmd.exe (PID: 6924)
- reg.exe (PID: 5784)
- reg.exe (PID: 7904)
Launching a file from the Downloads directory
- msedge.exe (PID: 3816)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 8008)
- powershell.exe (PID: 3196)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 8008)
- powershell.exe (PID: 3196)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 8008)
- powershell.exe (PID: 3196)
Starts MODE.COM to configure console settings
- mode.com (PID: 6344)
- mode.com (PID: 1932)
- mode.com (PID: 5996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
238
Monitored processes
103
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 172 | find /i "ARM64" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 172 | find /i "ARM64" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 172 | find /i "/S" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | C:\Windows\System32\cmd.exe /S /D /c" echo prompt $E " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1156 | find /i "ARM64" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1316 | C:\Windows\System32\cmd.exe /S /D /c" echo "AMD64 " " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1316 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1400 | cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1400 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1408 | cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 395
Read events
14 387
Write events
8
Delete events
0
Modification events
| (PID) Process: | (2852) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2852) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2852) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2852) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
27
Text files
247
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\ClientCertificates\LOG.old~RF14979b.TMP | — | |
MD5:— | SHA256:— | |||
| 3816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\parcel_tracking_db\LOG.old~RF1497ba.TMP | — | |
MD5:— | SHA256:— | |||
| 3816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\discounts_db\LOG.old~RF1497ba.TMP | — | |
MD5:— | SHA256:— | |||
| 3816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\LOG.old~RF1497ba.TMP | — | |
MD5:— | SHA256:— | |||
| 3816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\commerce_subscription_db\LOG.old~RF1497ba.TMP | — | |
MD5:— | SHA256:— | |||
| 3816 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
48
TCP/UDP connections
57
DNS requests
44
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7048 | msedge.exe | GET | 200 | 150.171.109.193:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=VN | US | — | — | whitelisted |
7048 | msedge.exe | GET | 304 | 150.171.27.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | US | — | — | whitelisted |
3248 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?e4c6dcb54f4bde95 | US | compressed | 73.5 Kb | unknown |
7048 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:h8NMJc5gS0fdTdEFkuXPG4srOzSfET7qdaVfzAOjeCU&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 94 b | whitelisted |
1936 | firefox.exe | POST | 200 | 23.11.40.157:80 | http://ocsp.digicert.com/ | NL | binary | 471 b | whitelisted |
3536 | svchost.exe | HEAD | 200 | 104.102.63.189:443 | https://fs.microsoft.com/fs/windows/config.json | US | — | — | whitelisted |
7048 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
7048 | msedge.exe | GET | 200 | 52.123.243.211:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=-307948261743016929&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.22000&wu=1&devicefamily=desktop&uma=0&sessionid=78&mngd=0&installdate=1645822881&edu=0&soobedate=1645822879&bphint=2&fg=1&lbfgdate=1759429959&lafgdate=0 | US | text | 4.15 Kb | whitelisted |
7048 | msedge.exe | GET | 200 | 150.171.73.16:443 | https://dev.azure.com/massgrave/Microsoft-Activation-Scripts/_apis/git/repositories/Microsoft-Activation-Scripts/items?path=/MAS/All-In-One-Version-KL/MAS_AIO.cmd&download=true | US | text | 743 Kb | malicious |
7048 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/entityextractiontemplates/api/v1/assets/find-assets?name=domains_config_gz&version=3.*.*&channel=stable&key=d414dd4f9db345fa8003e32adc81b362 | US | text | 267 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2160 | OfficeC2RClient.exe | 52.110.17.70:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 52.110.17.70:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3336 | SDXHelper.exe | 52.110.17.70:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4756 | SDXHelper.exe | 52.110.17.70:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 34.120.208.123:443 | incoming.telemetry.mozilla.org | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
5424 | pingsender.exe | 34.120.208.123:443 | incoming.telemetry.mozilla.org | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
1936 | firefox.exe | 34.120.208.123:443 | incoming.telemetry.mozilla.org | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
1936 | firefox.exe | 23.11.40.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
5212 | rundll32.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1380 | svchost.exe | 2.18.64.200:80 | — | AKAMAI-ASN1 | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
officeclient.microsoft.com |
| whitelisted |
incoming.telemetry.mozilla.org |
| whitelisted |
telemetry-incoming.r53-2.services.mozilla.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
eip-terr-eu.cdp1.digicert.com.akahost.net |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
dev.azure.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7048 | msedge.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Get-WmiObject Cmdlet has been detected |
7048 | msedge.exe | A Network Trojan was detected | ET ATTACK_RESPONSE PowerShell Internet Connectivity Check via Network GUID Inbound |
7048 | msedge.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Windows OS Version extraction by PS.Script has been detected |
7048 | msedge.exe | Potentially Bad Traffic | ET HUNTING schtasks delete Command in HTTP Body Response |
7048 | msedge.exe | Potentially Bad Traffic | ET ATTACK_RESPONSE PowerShell NoProfile Command Received In Powershell Stagers |
7048 | msedge.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Windows security identifiers S-1-5-18 (NT AuthoritySystem) has been detected |
7048 | msedge.exe | Potentially Bad Traffic | ET ATTACK_RESPONSE PowerShell Base64 Encoded Content Command Common In Powershell Stagers M2 |
7048 | msedge.exe | Potentially Bad Traffic | ET HUNTING PowerShell Hidden Window Command Common In Powershell Stagers M2 |
7048 | msedge.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Check Security.Principal.WindowsBuiltInRole has been detected |
7048 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] The Principal.WindowsIdentity in PS.Script has been detected |