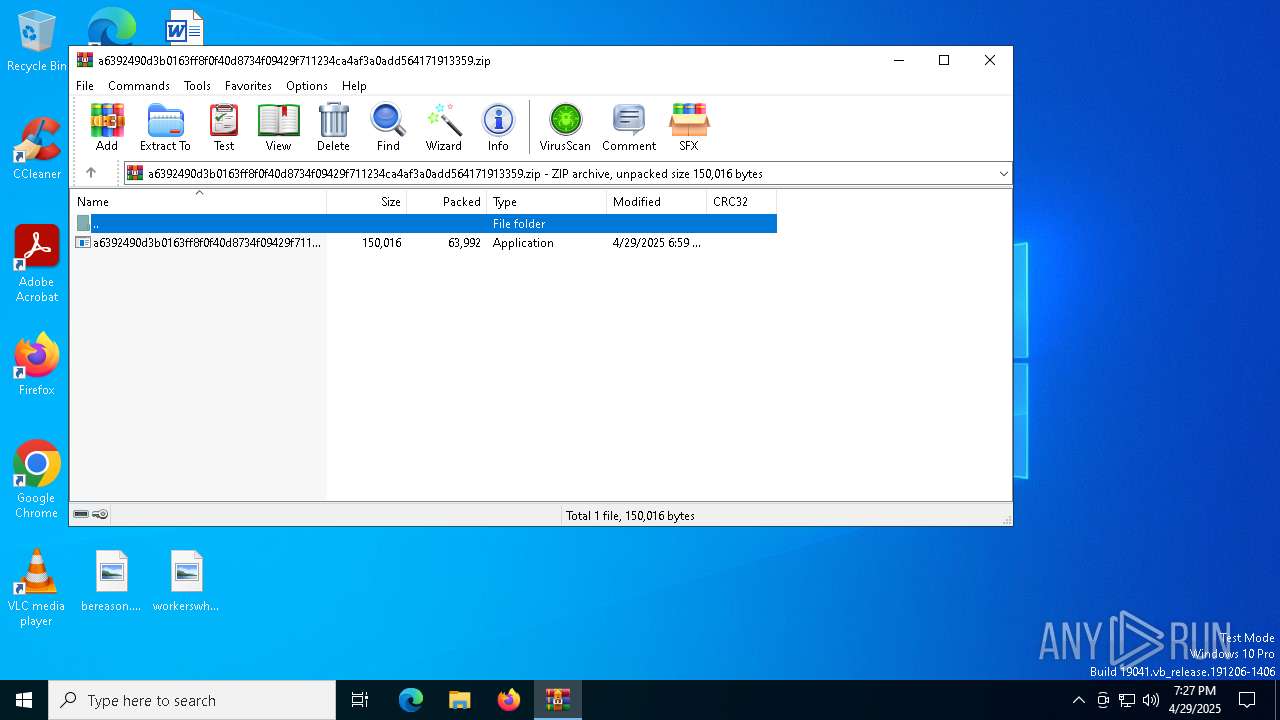
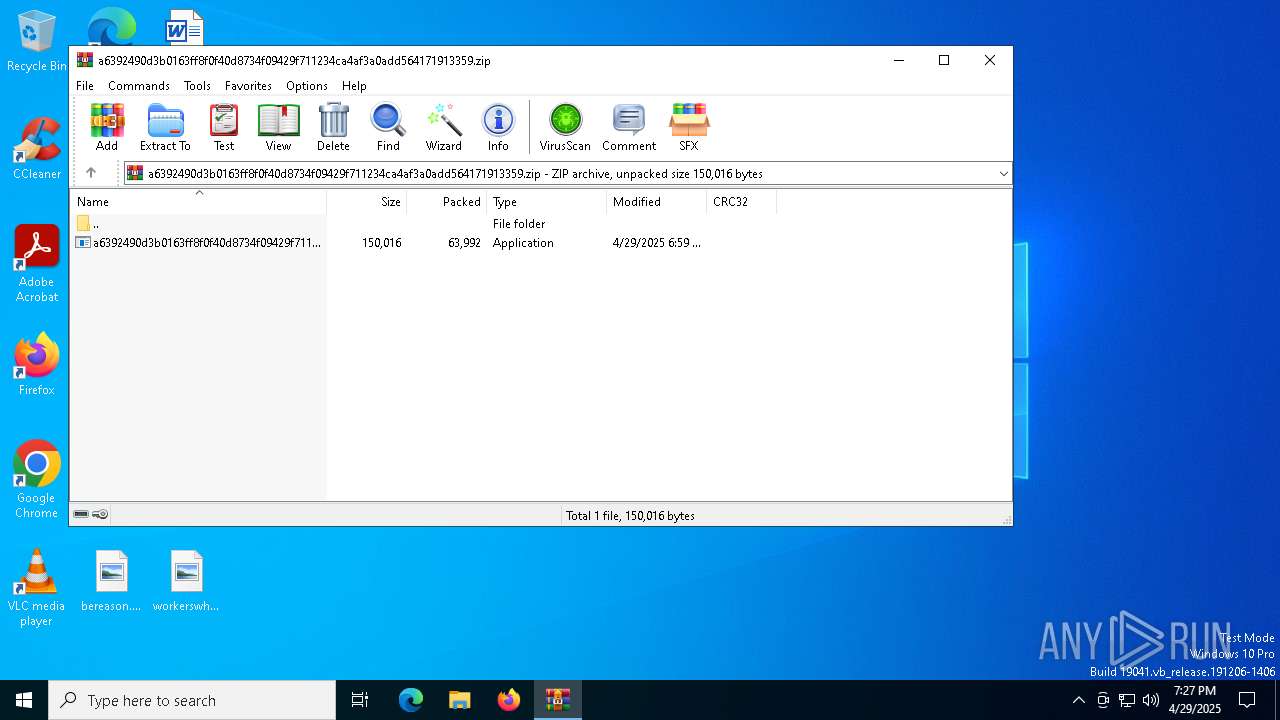
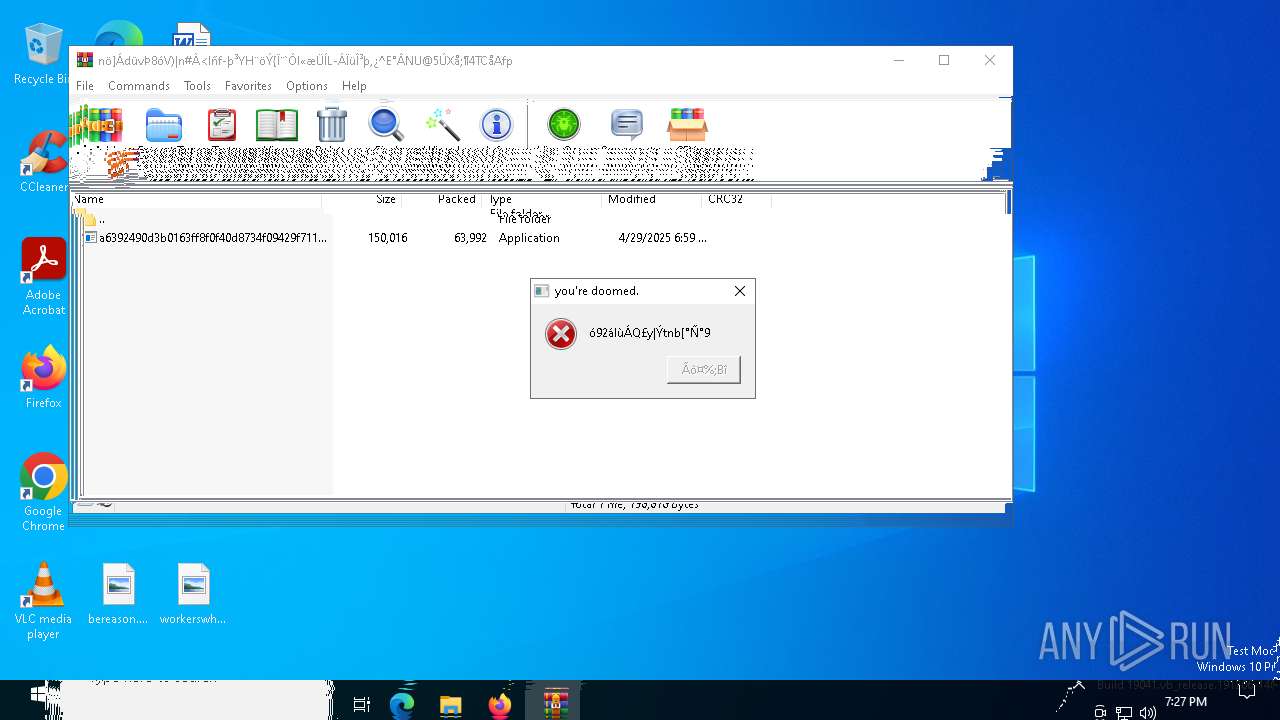
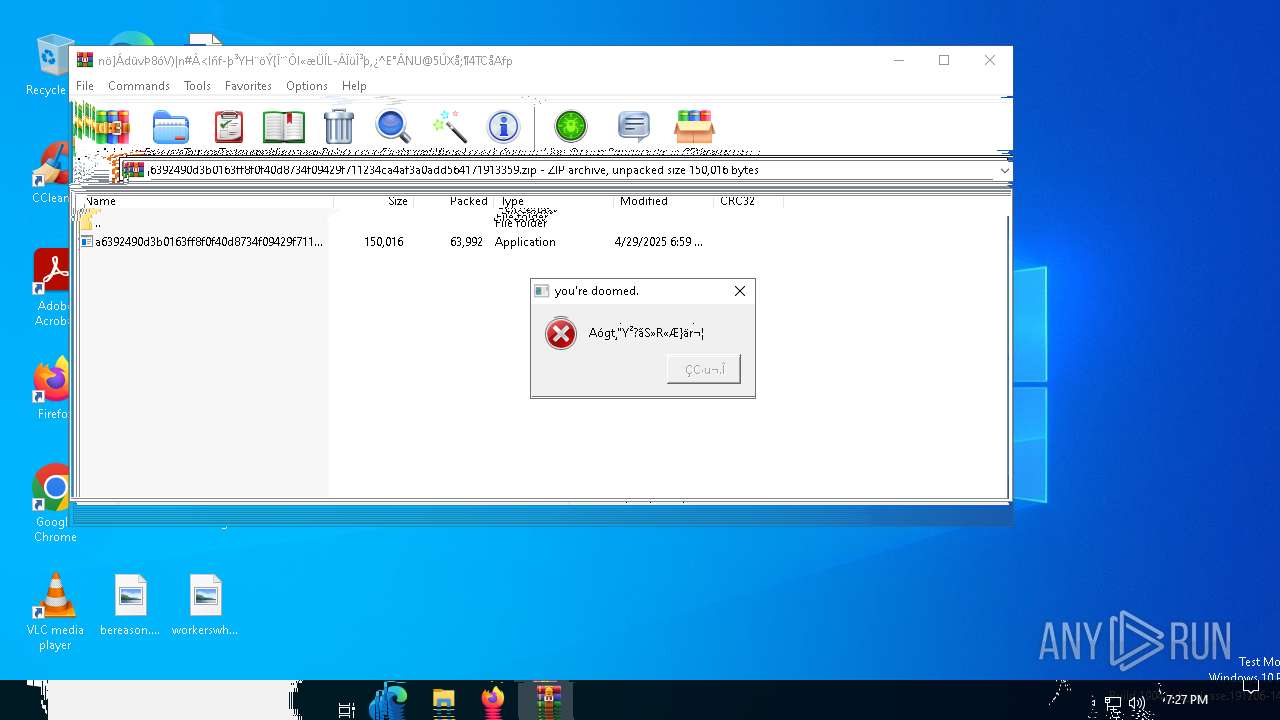
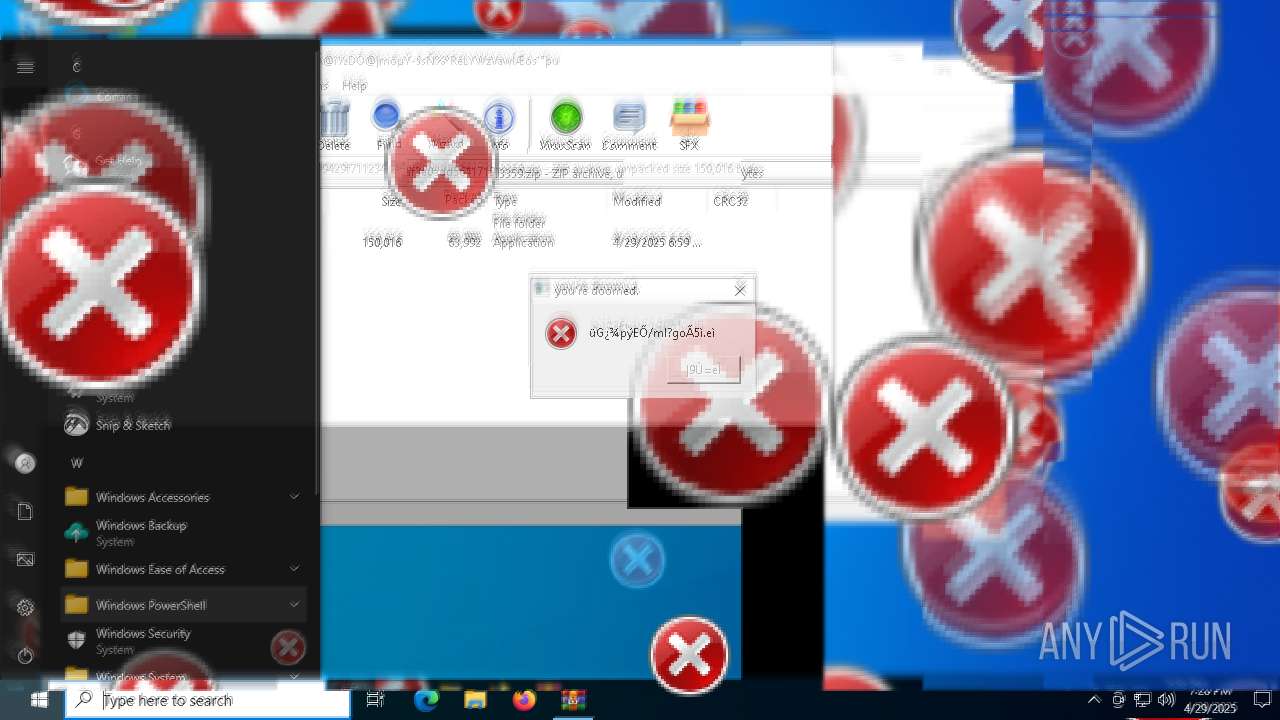
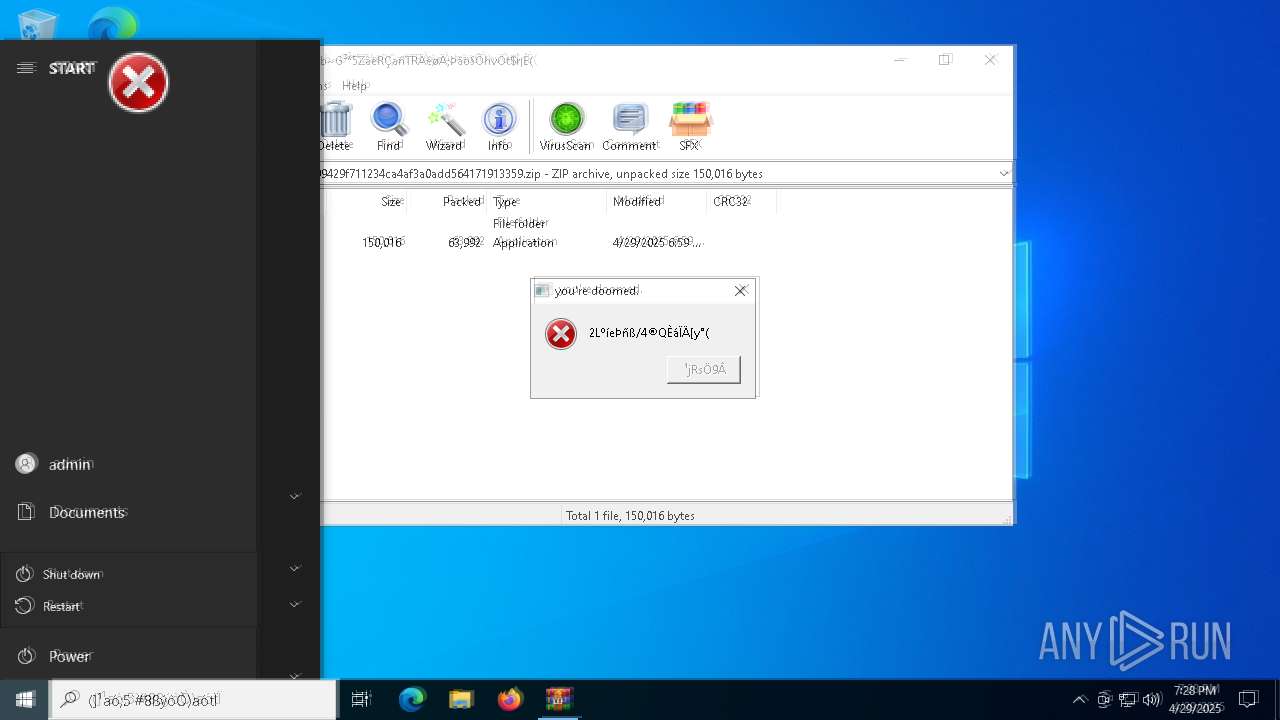
| File name: | a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.zip |
| Full analysis: | https://app.any.run/tasks/bc506c87-ea5c-4cf1-8c0c-ddf681ad2d62 |
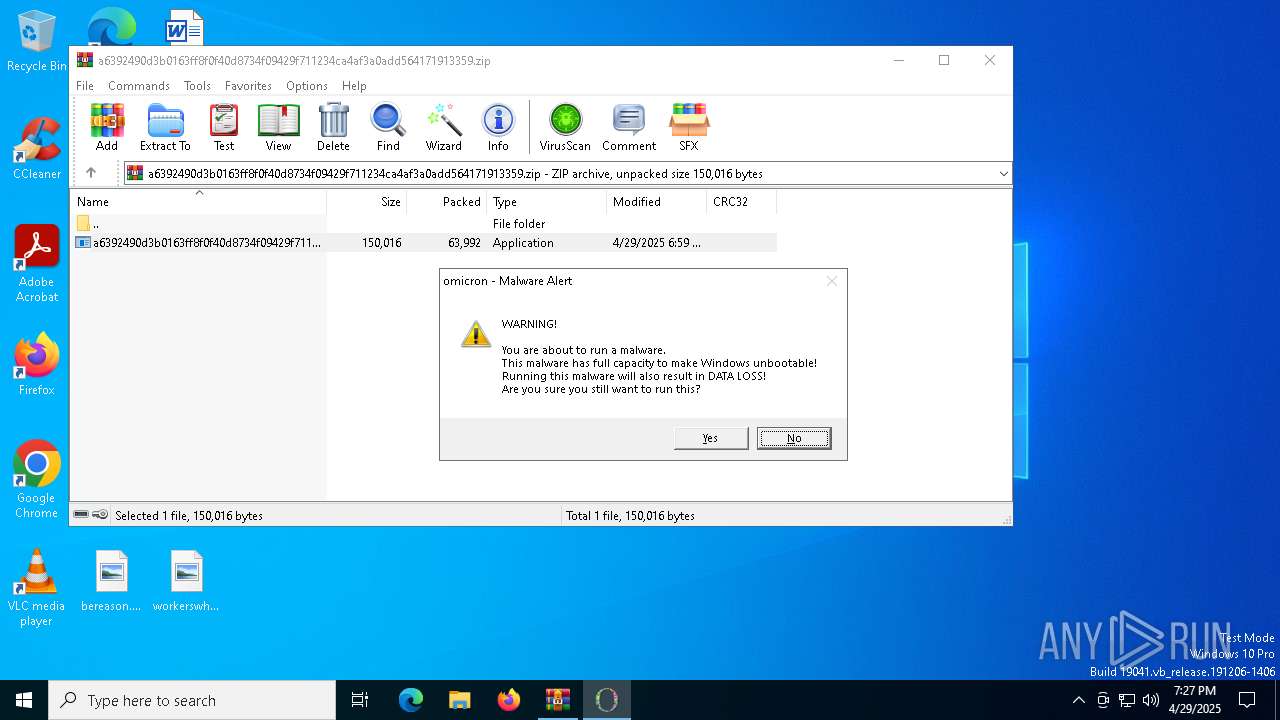
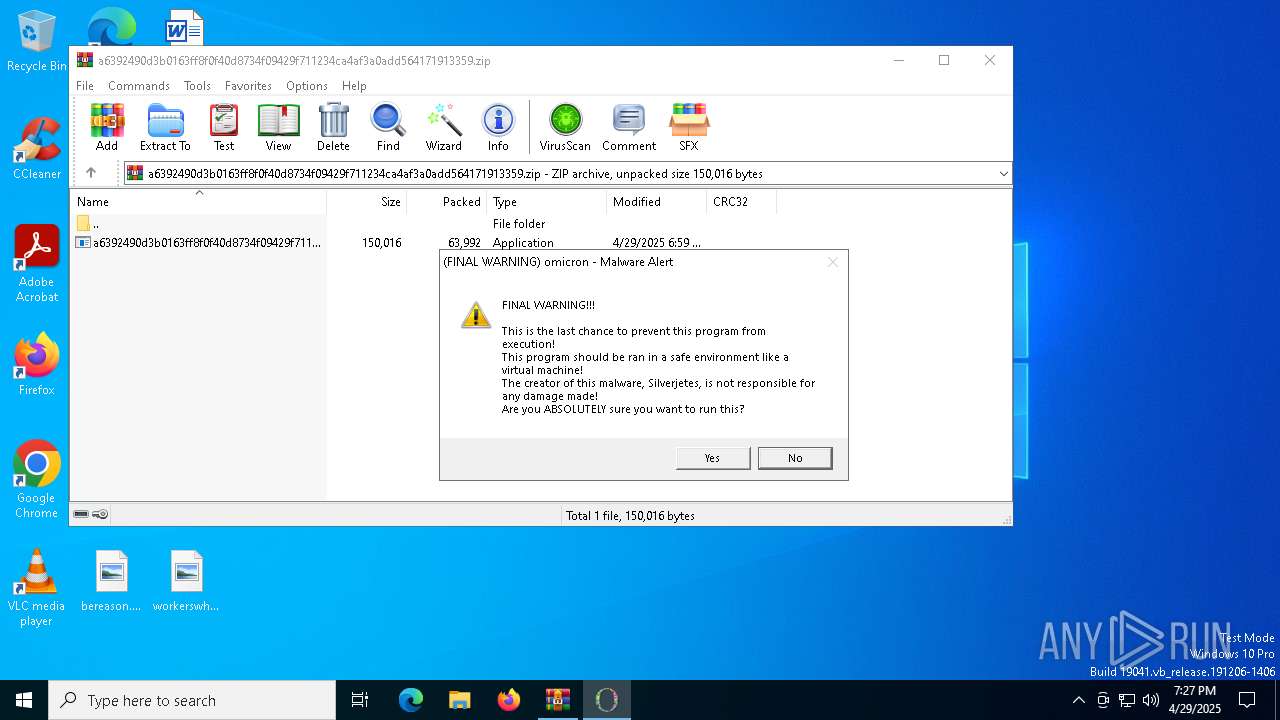
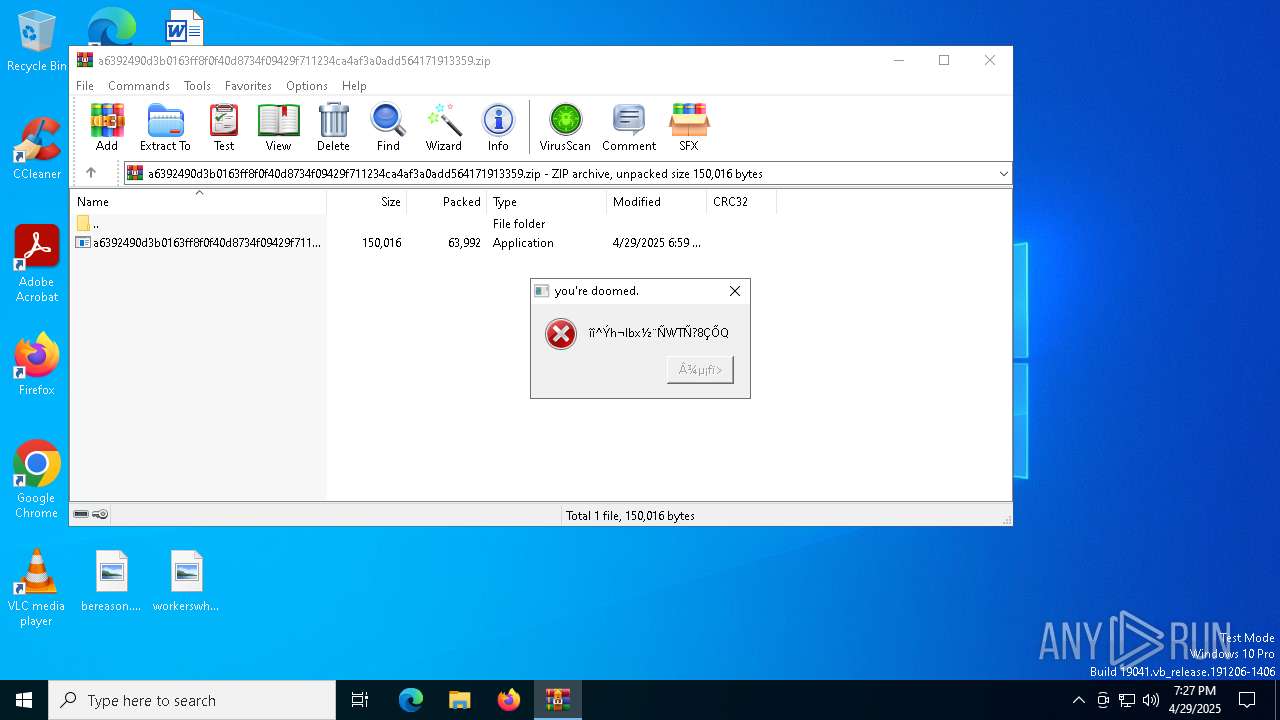
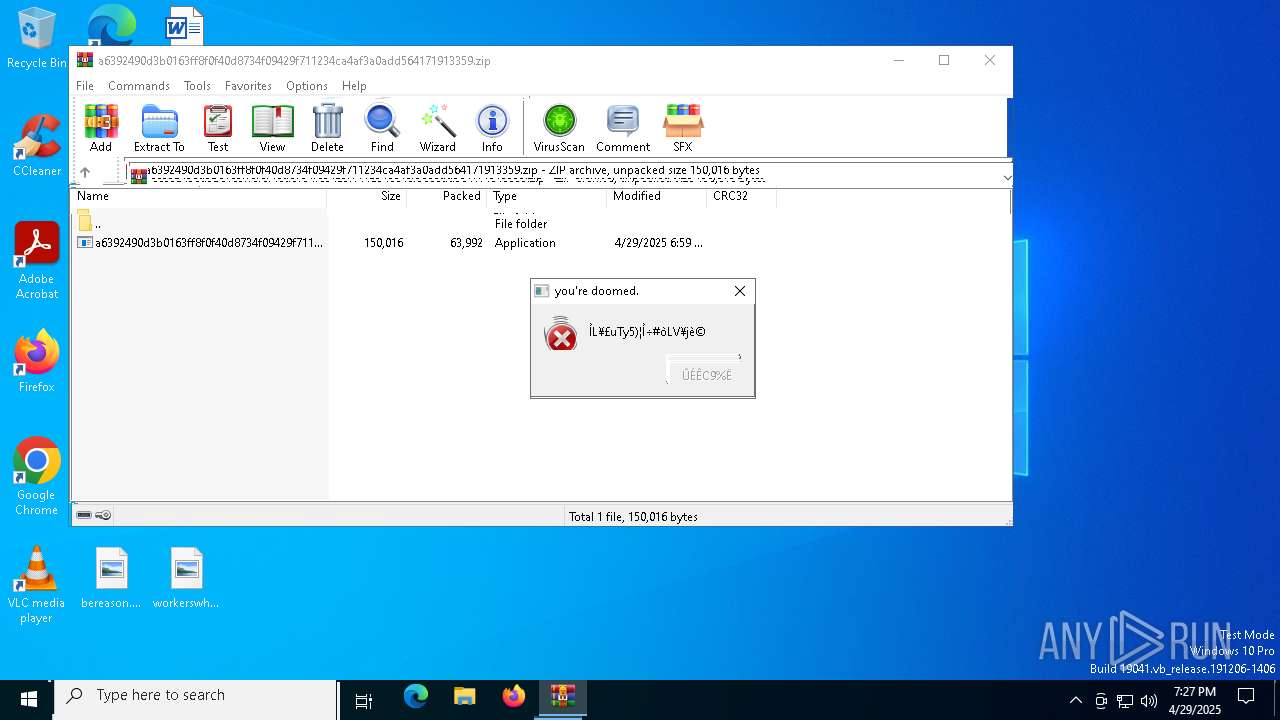
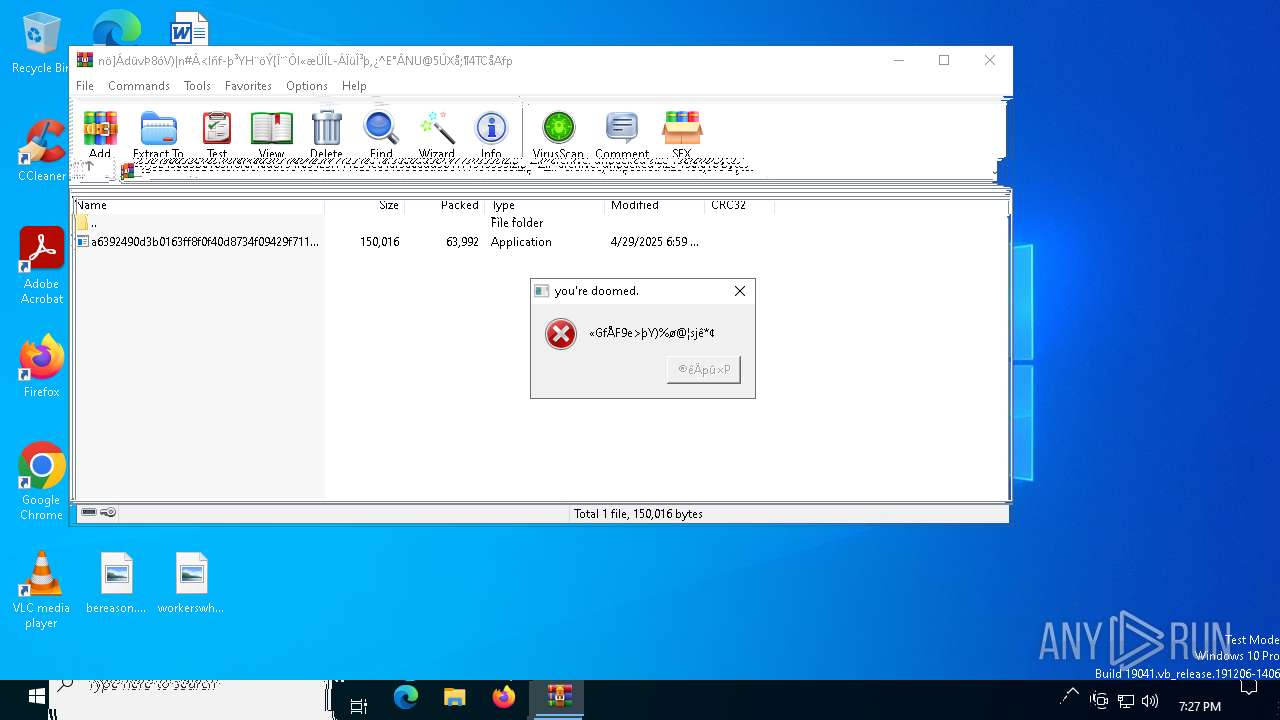
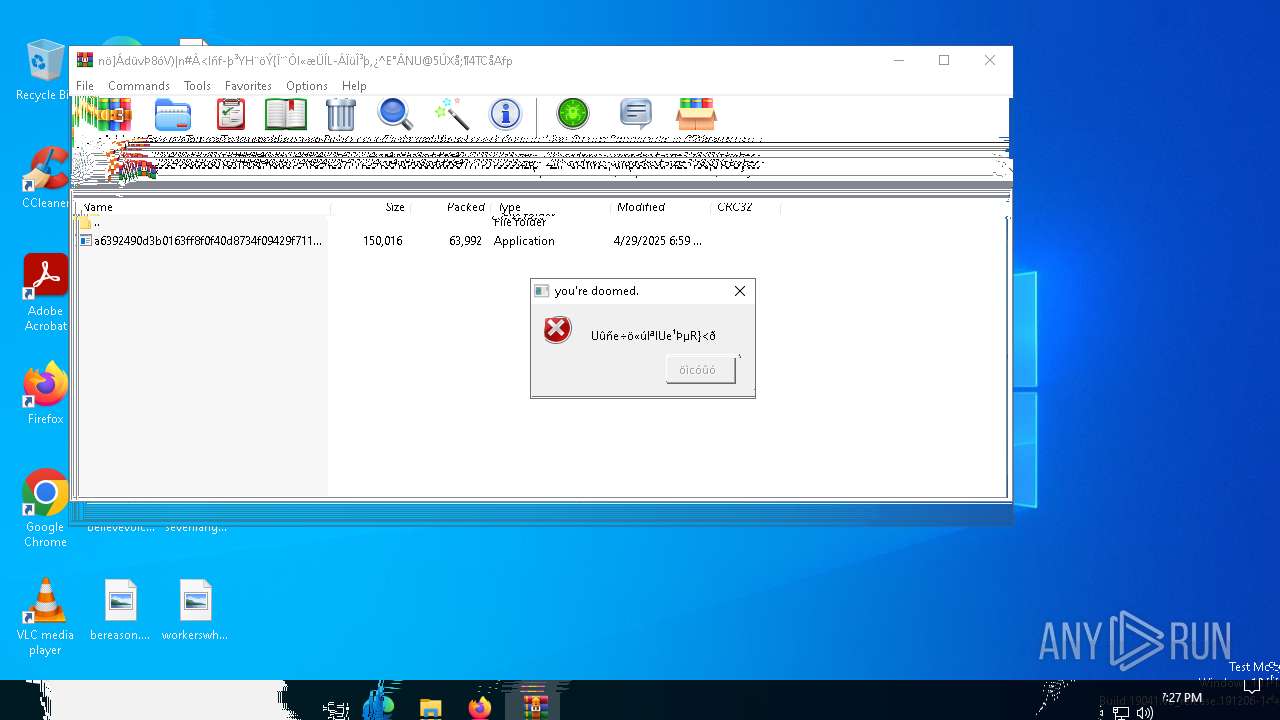
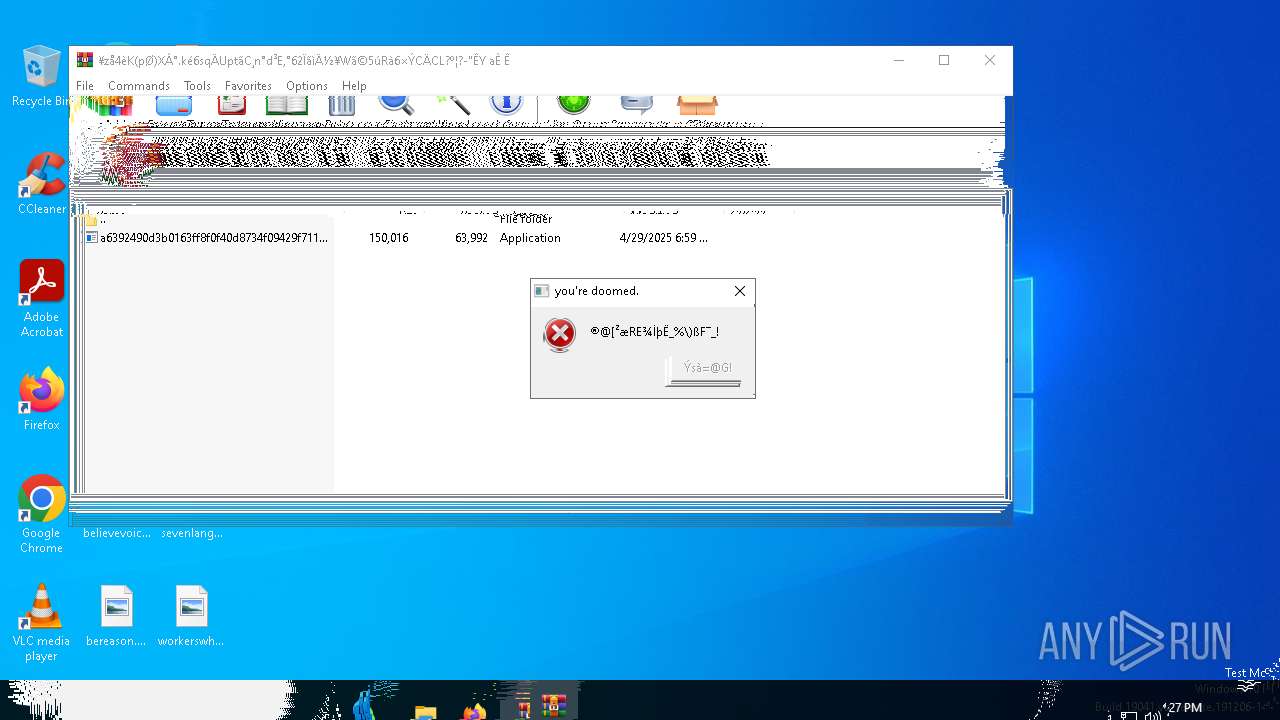
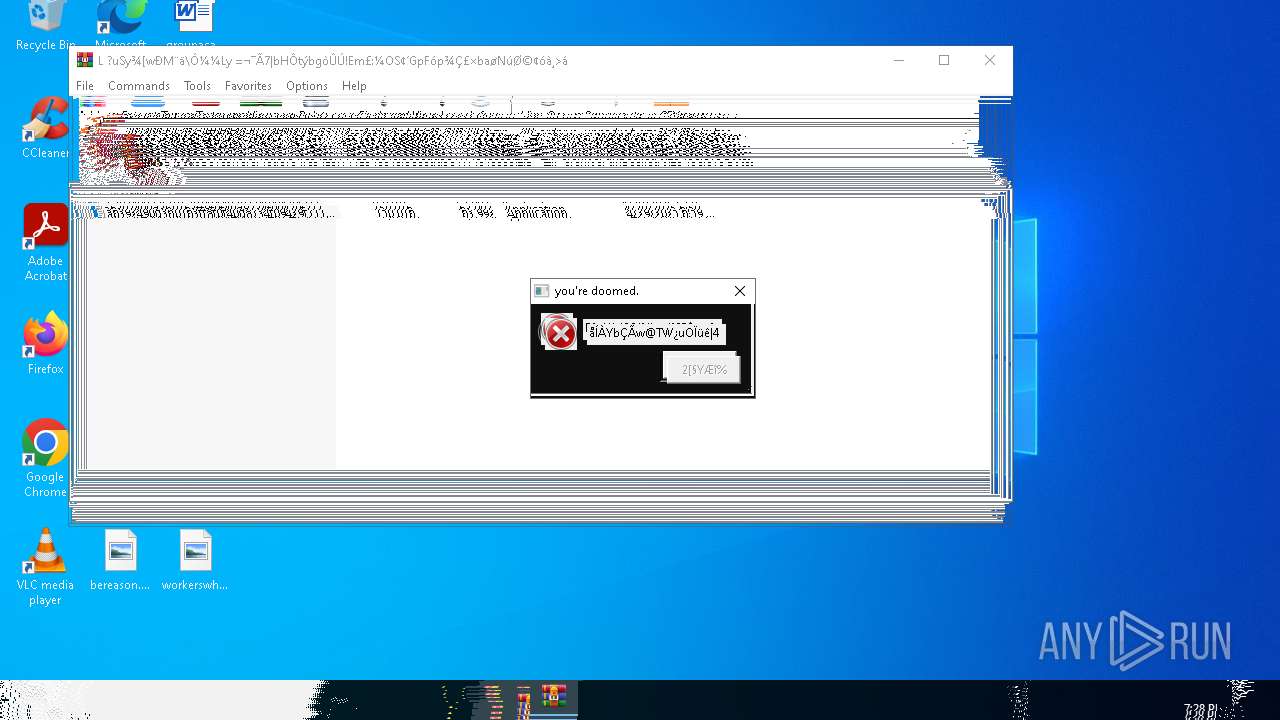
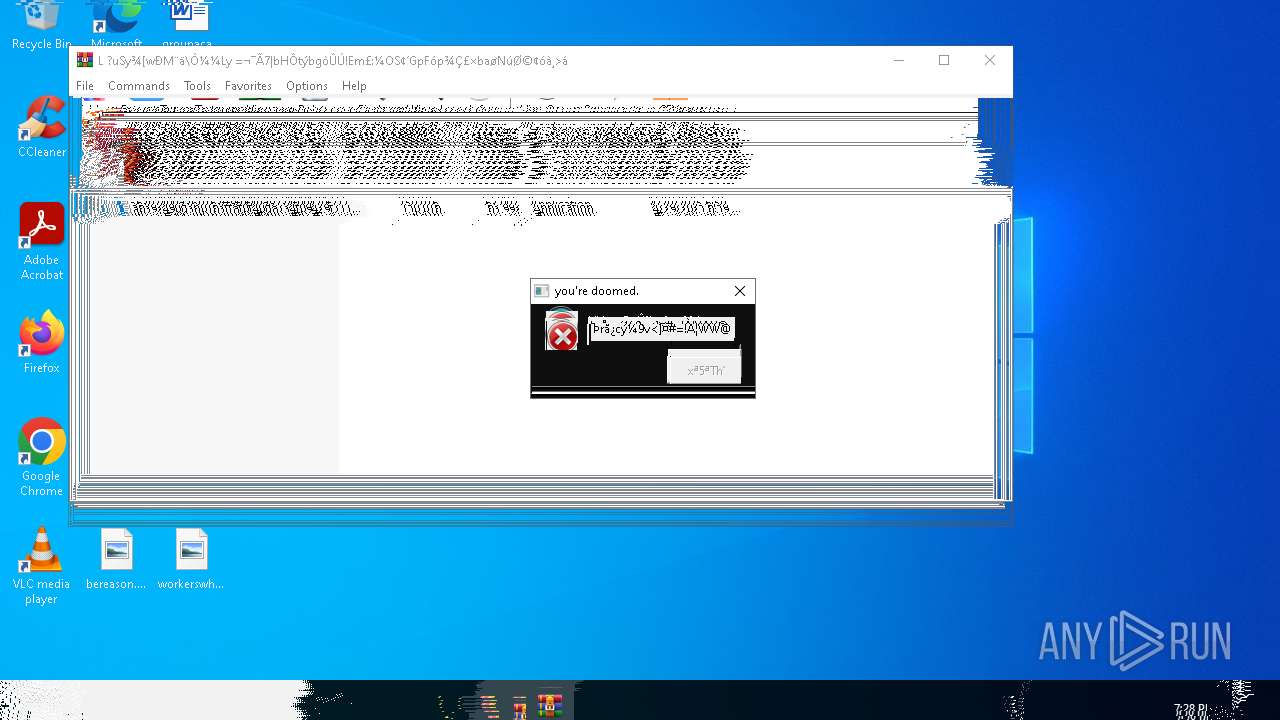
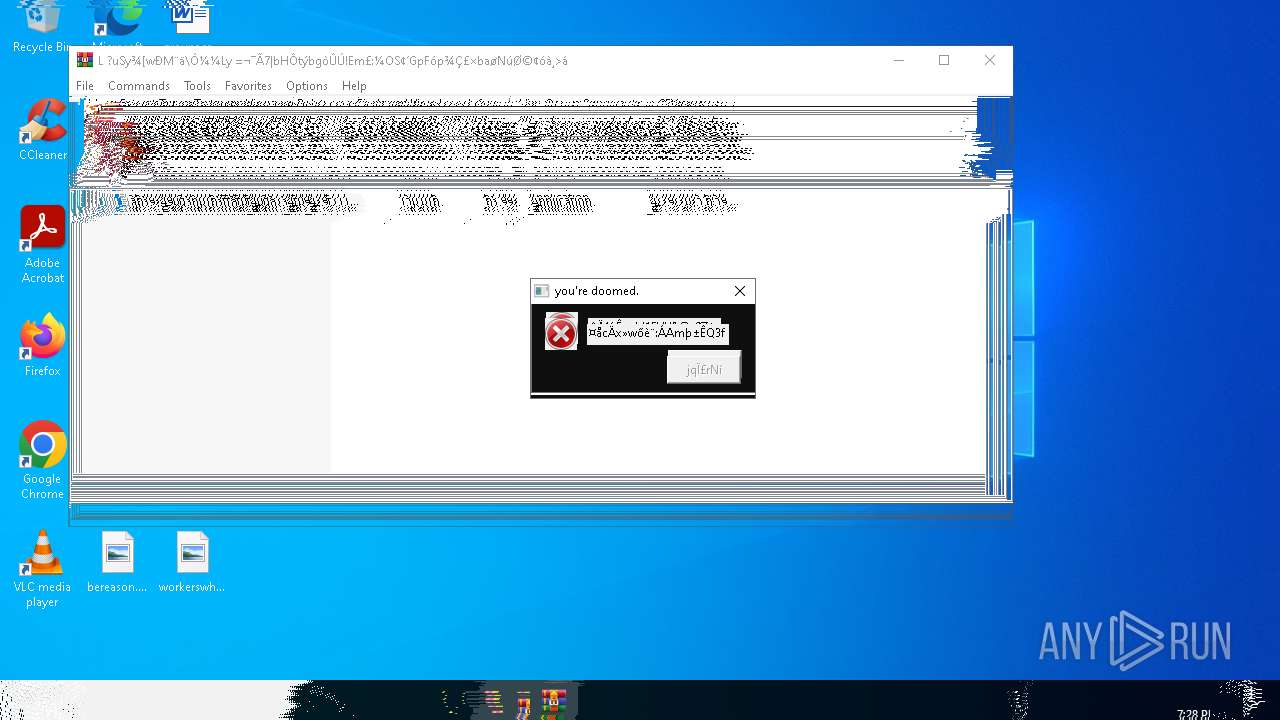
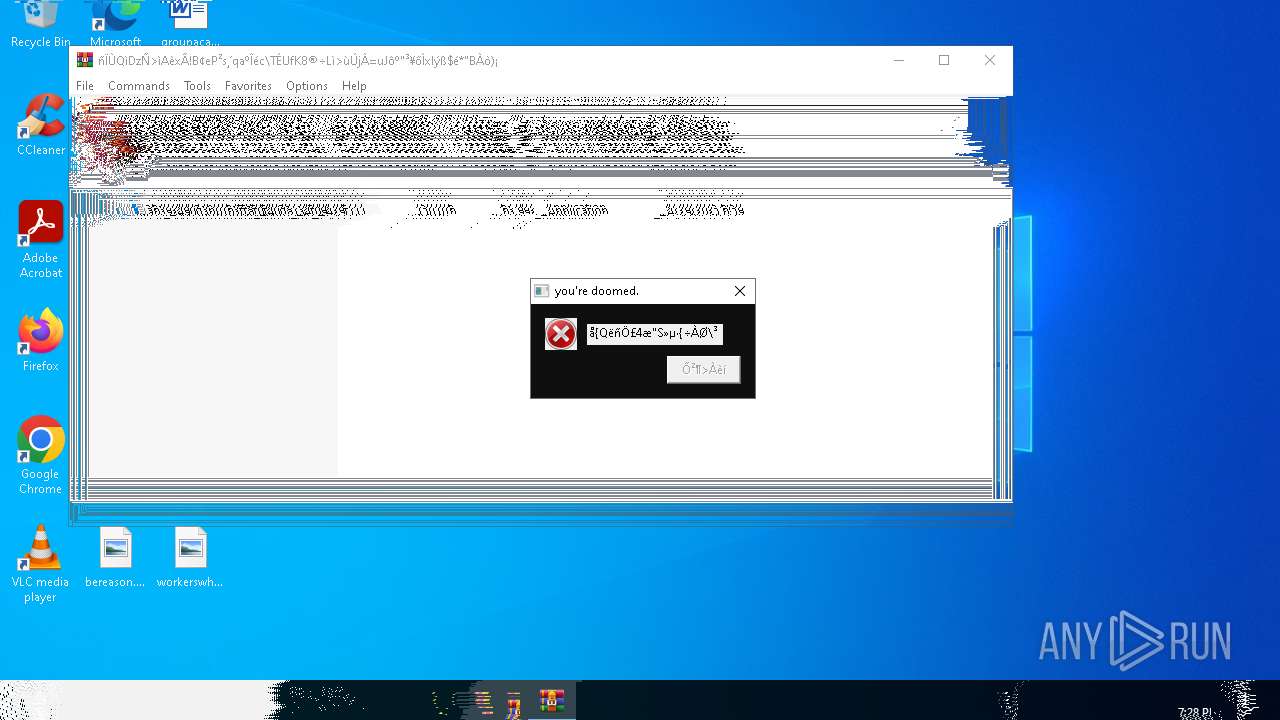
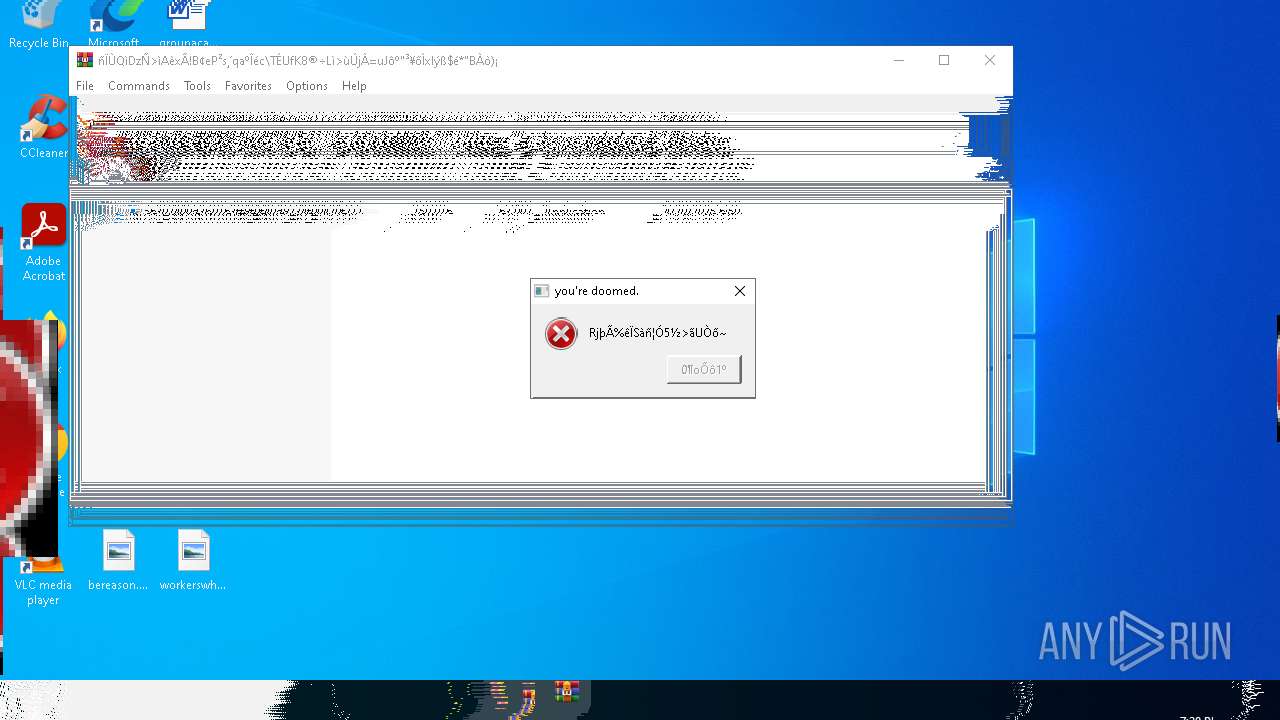
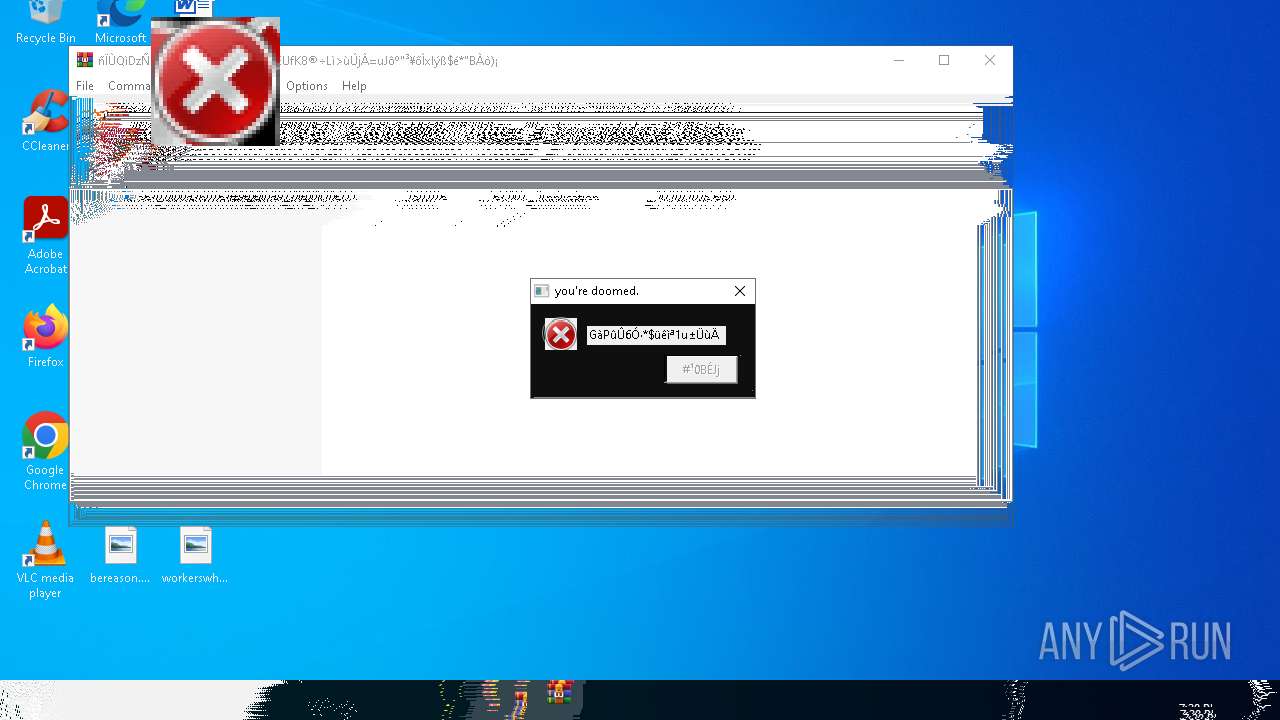
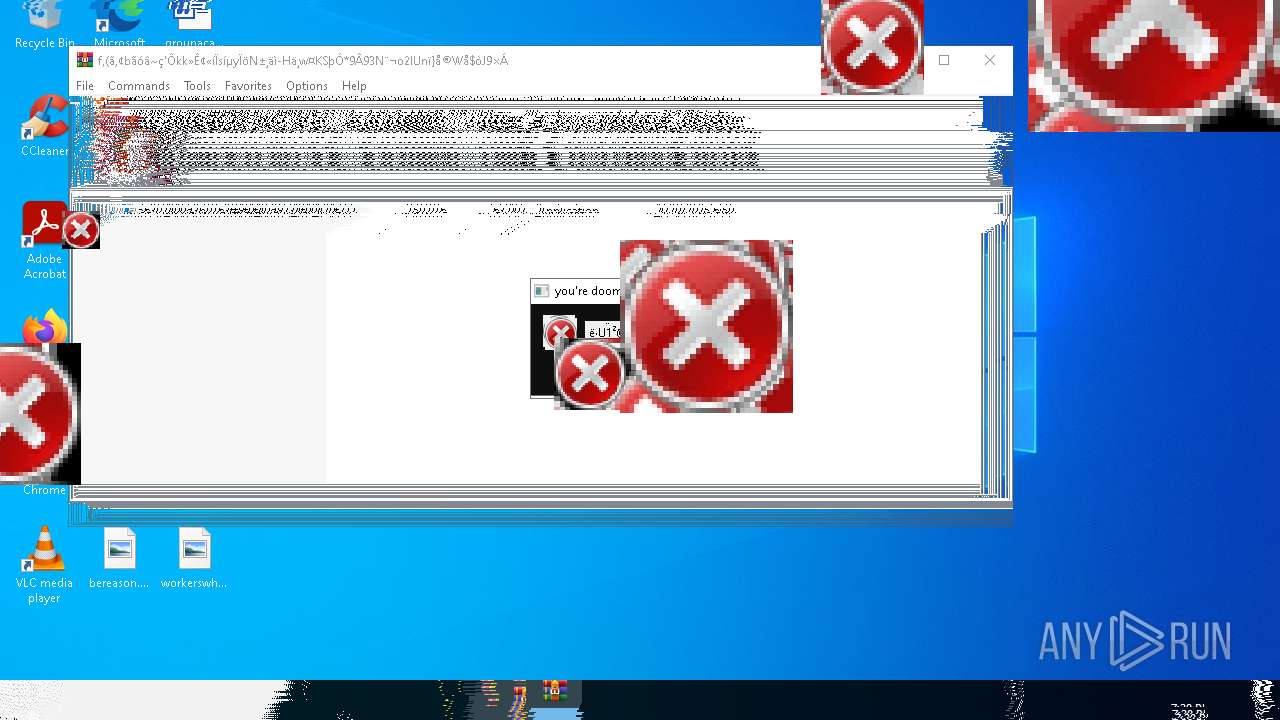
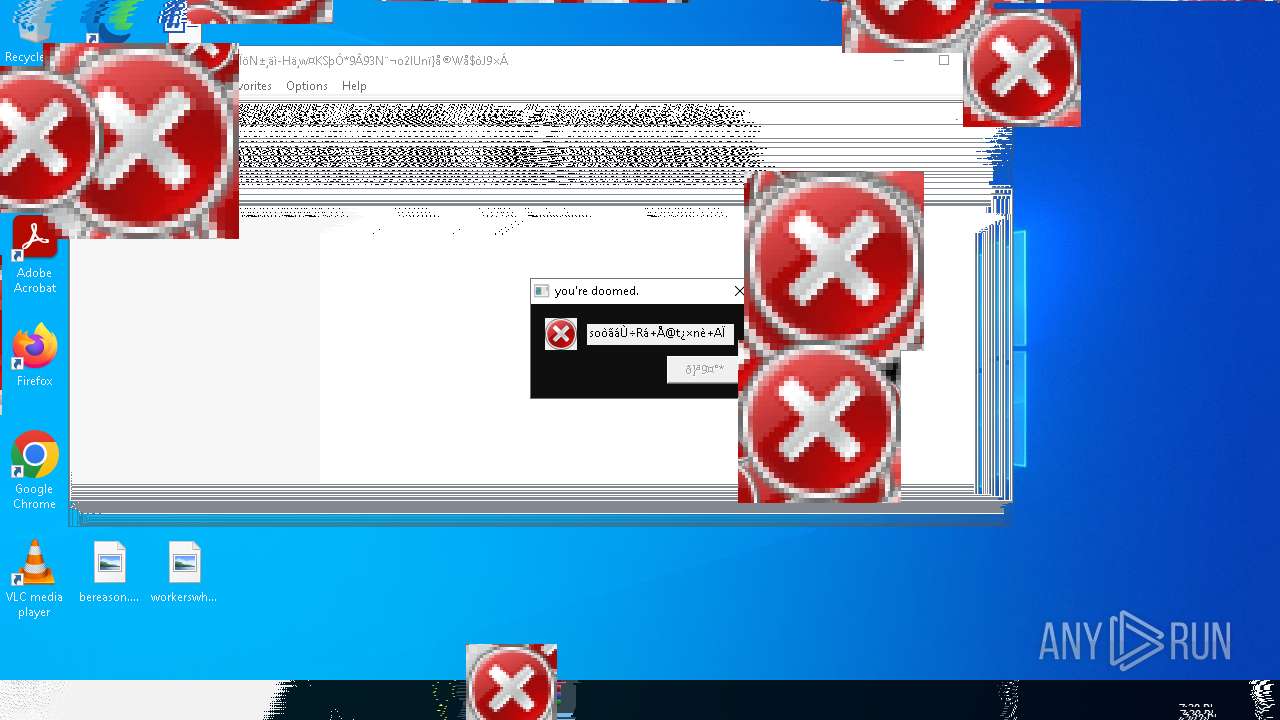
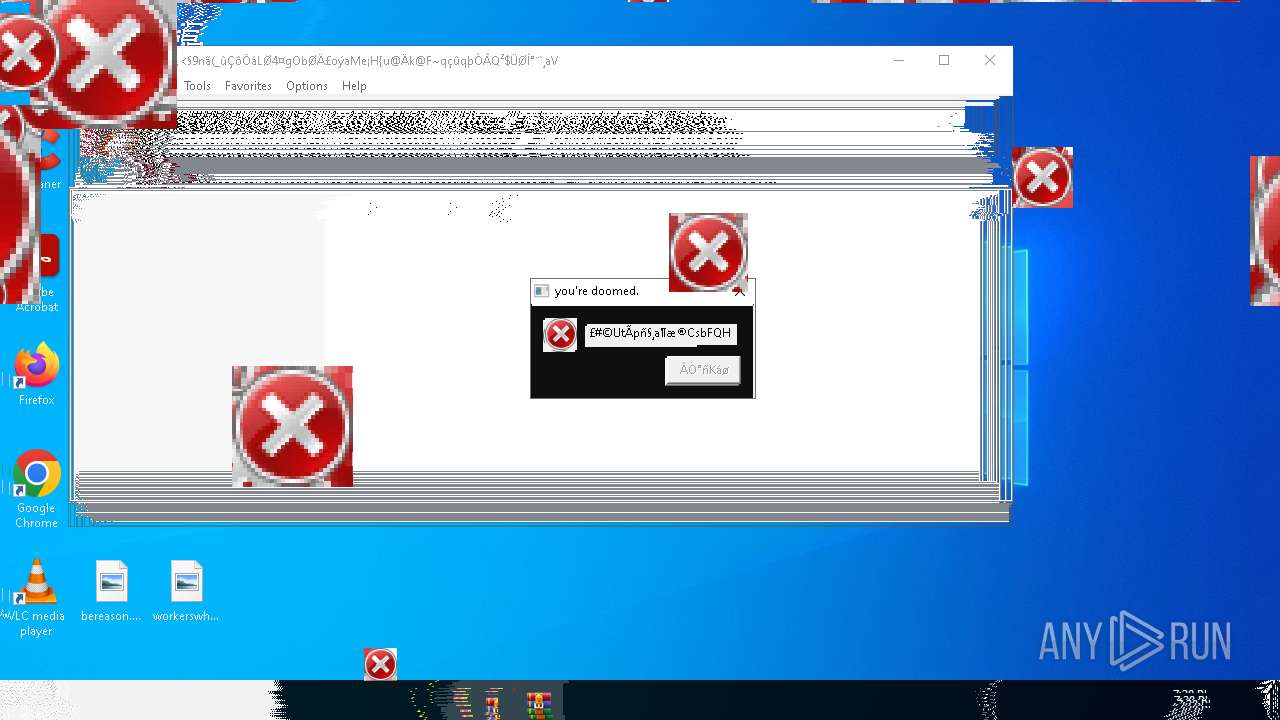
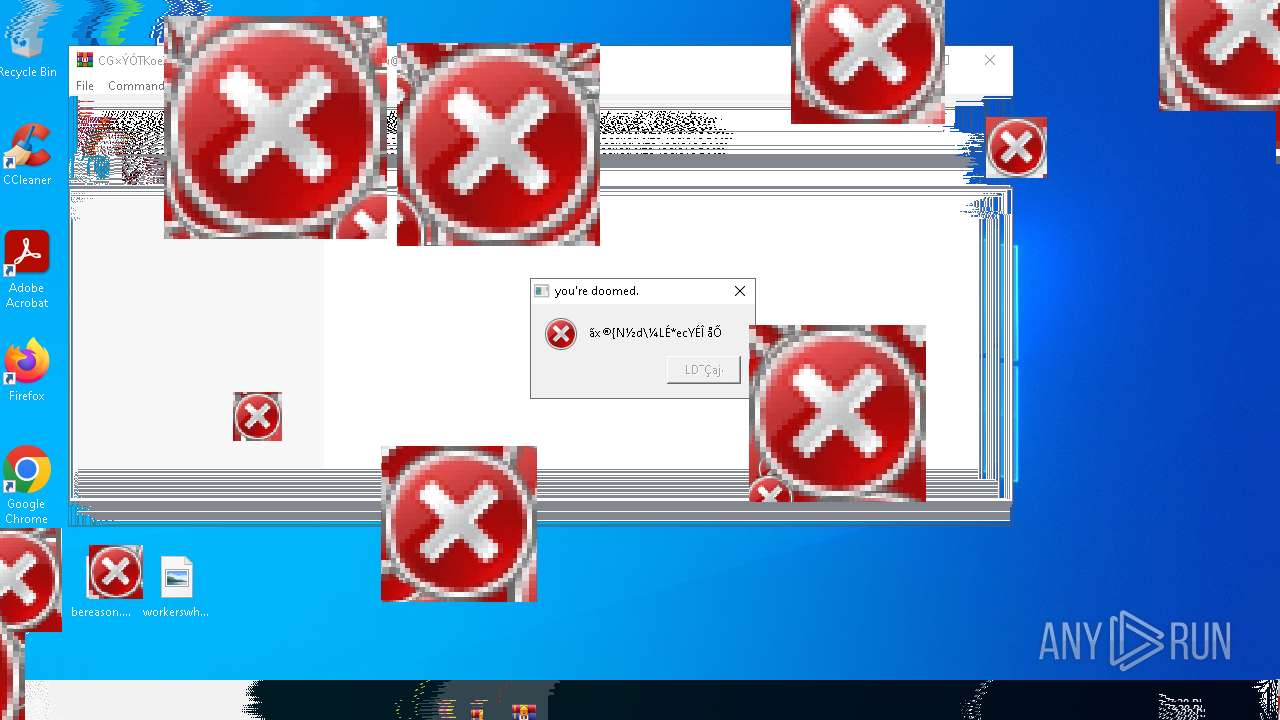
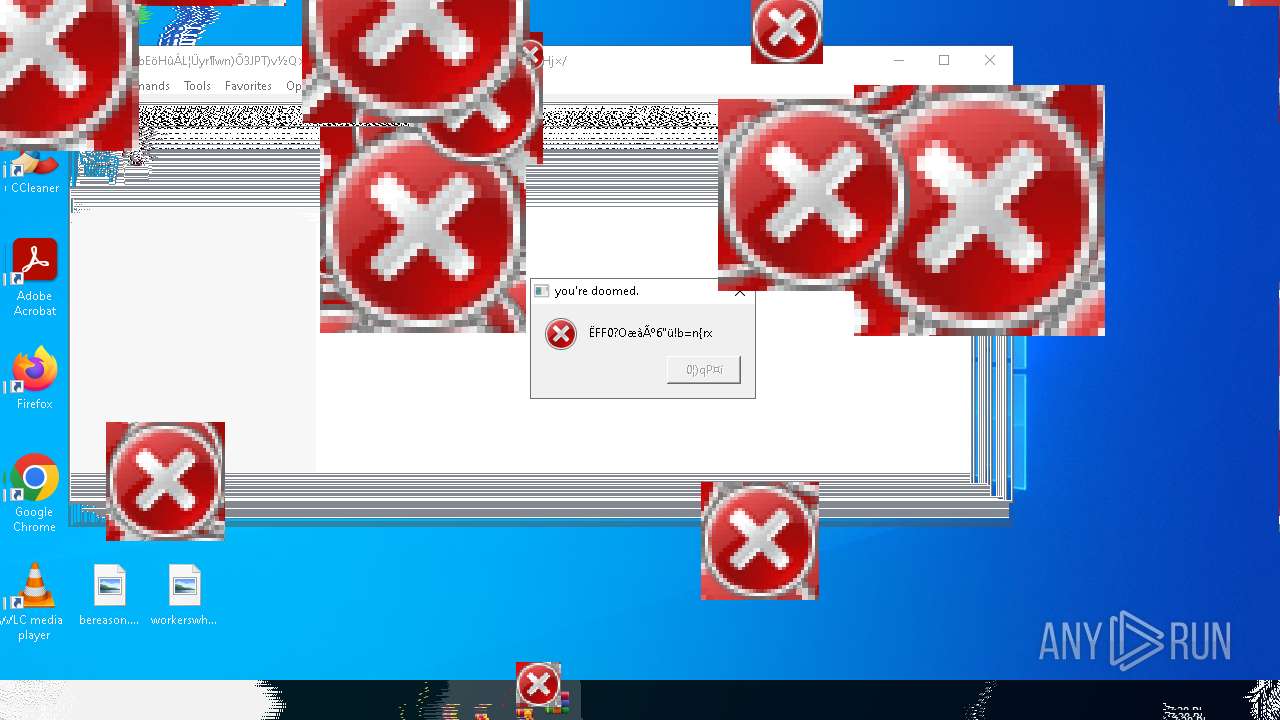
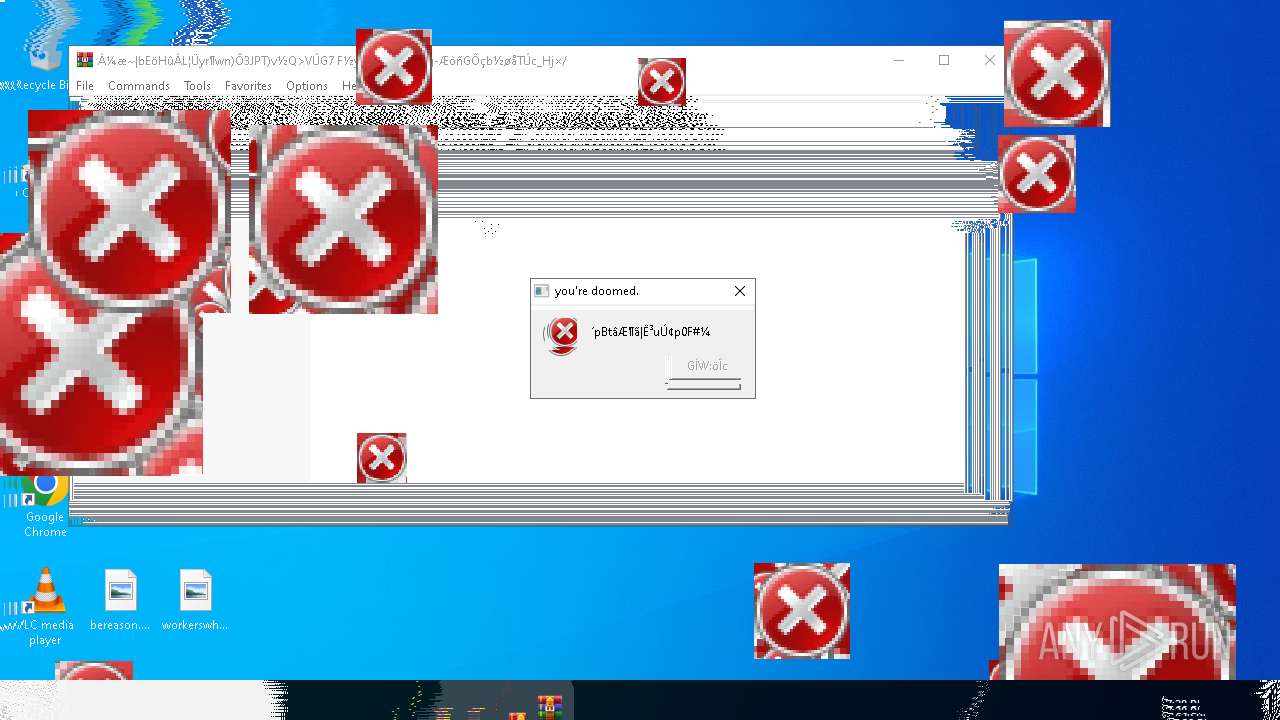
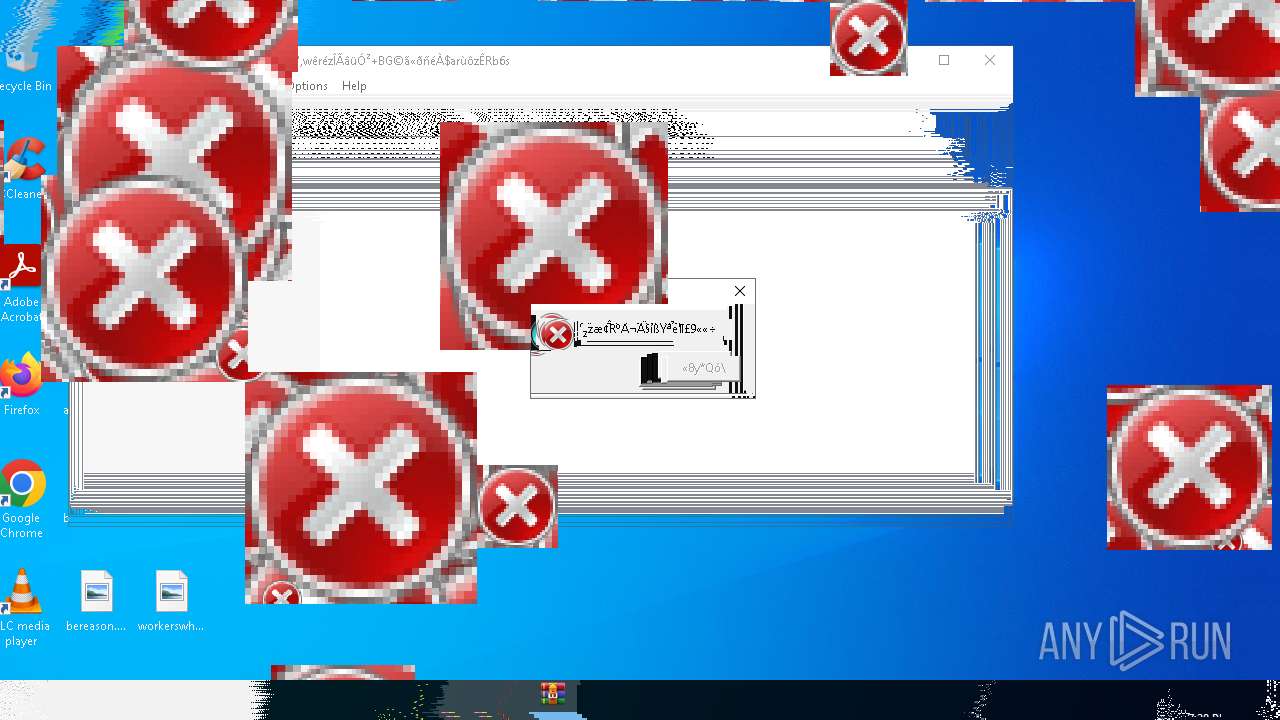
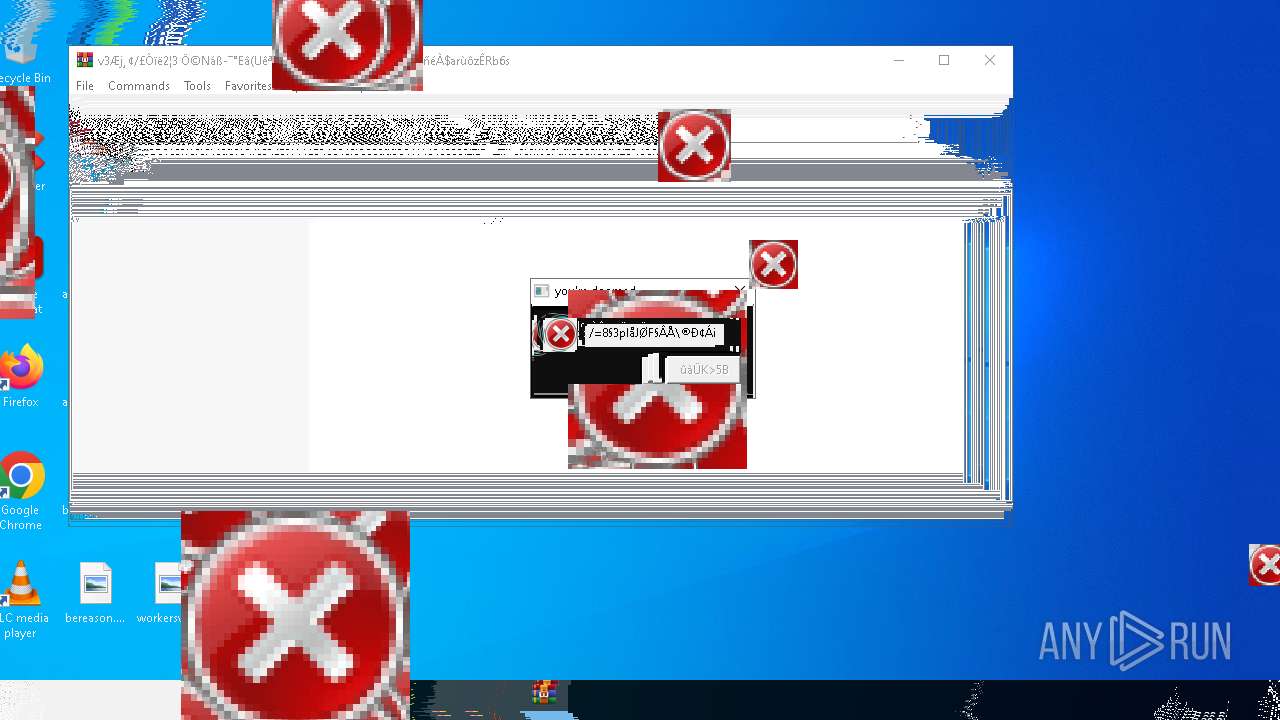
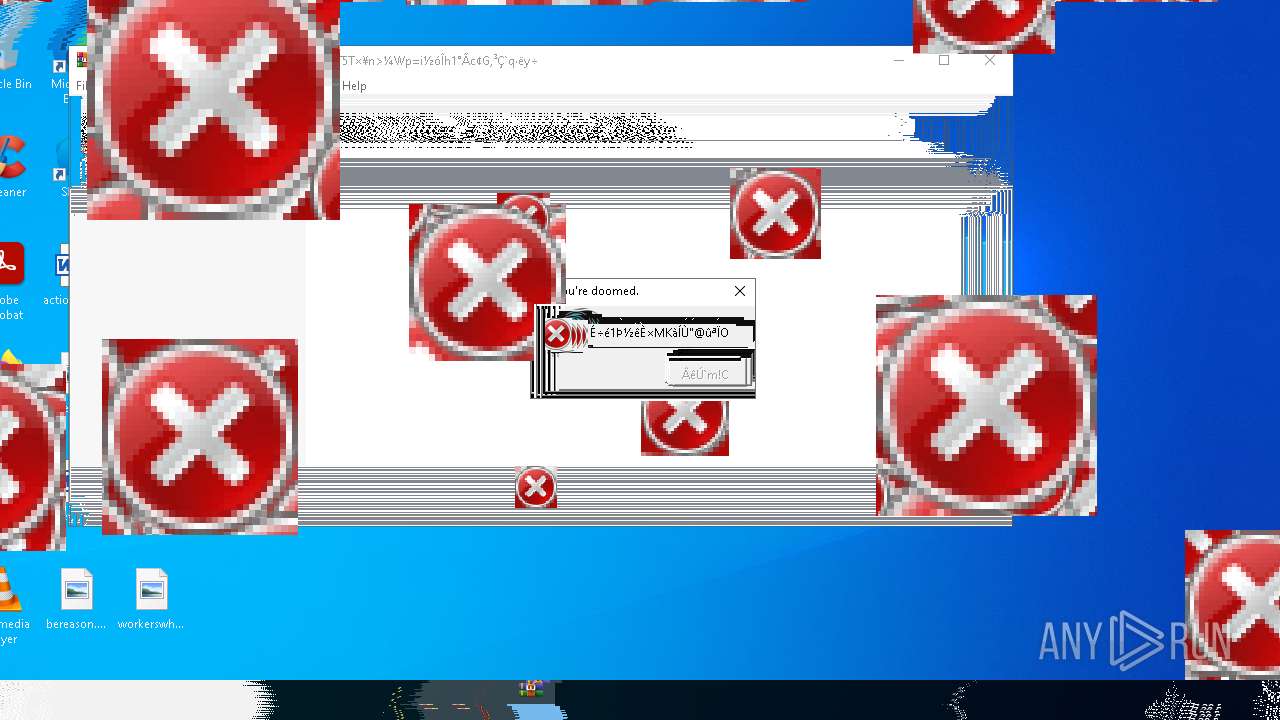
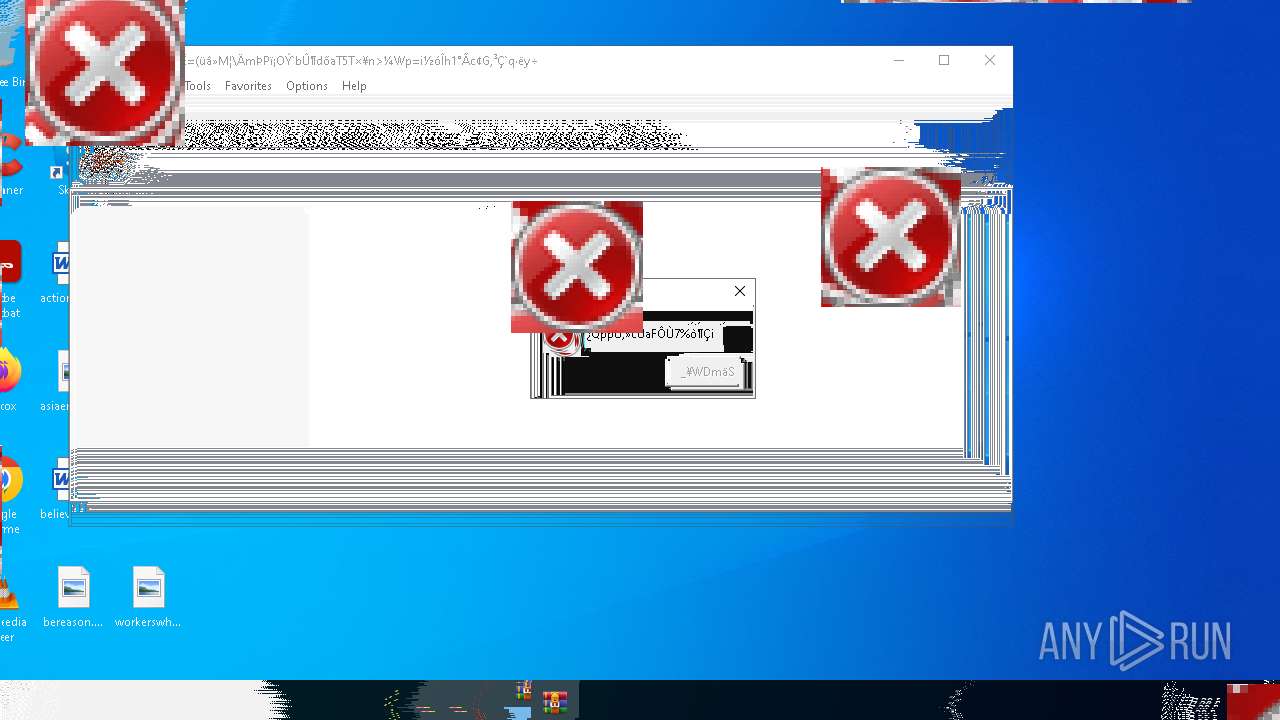
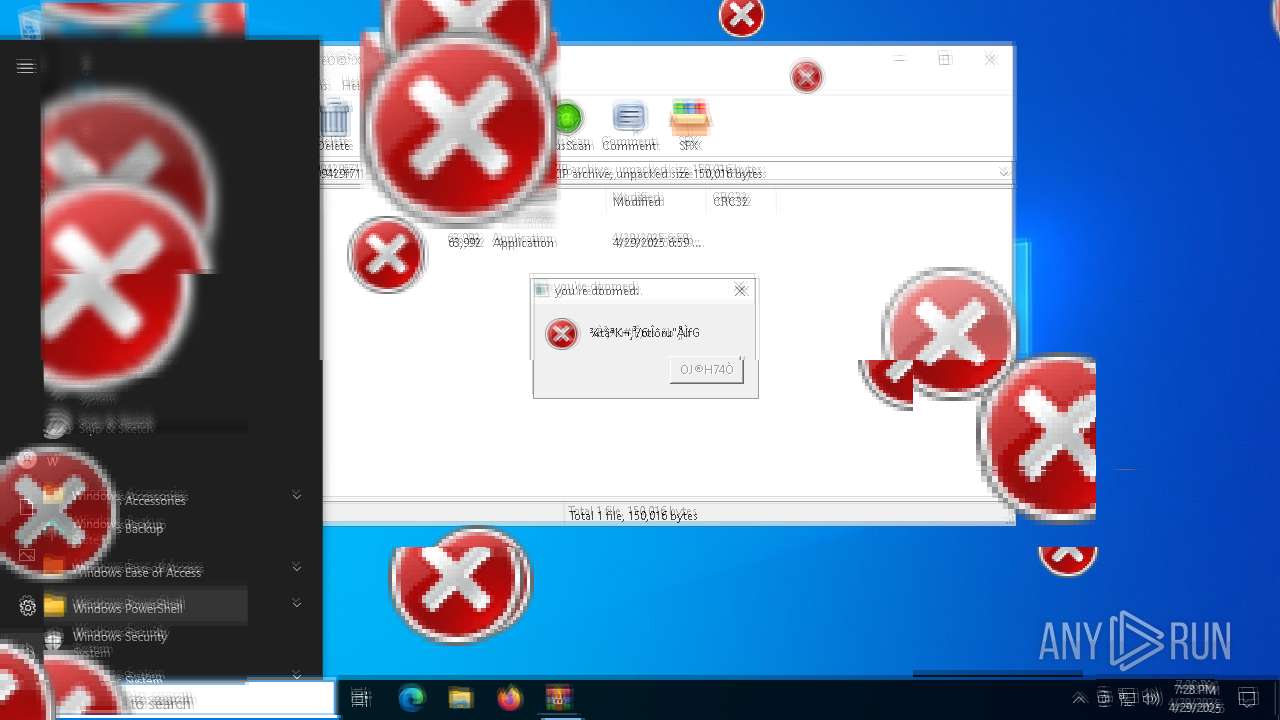
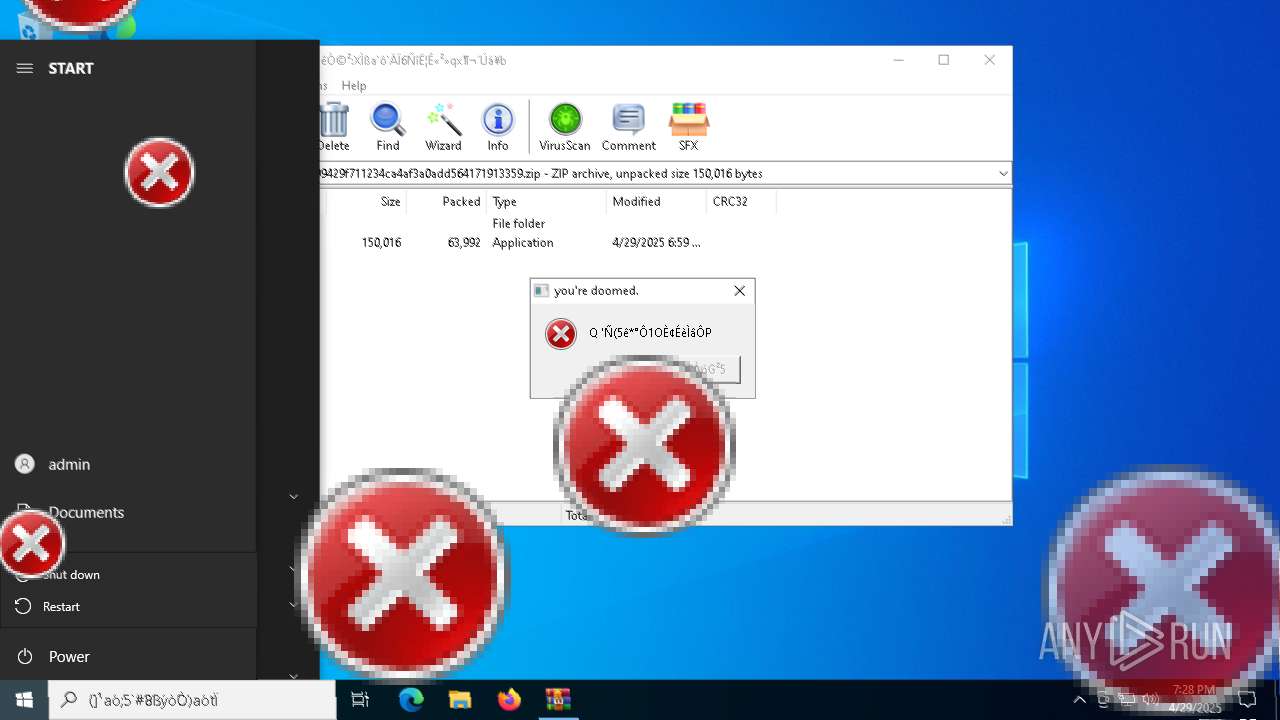
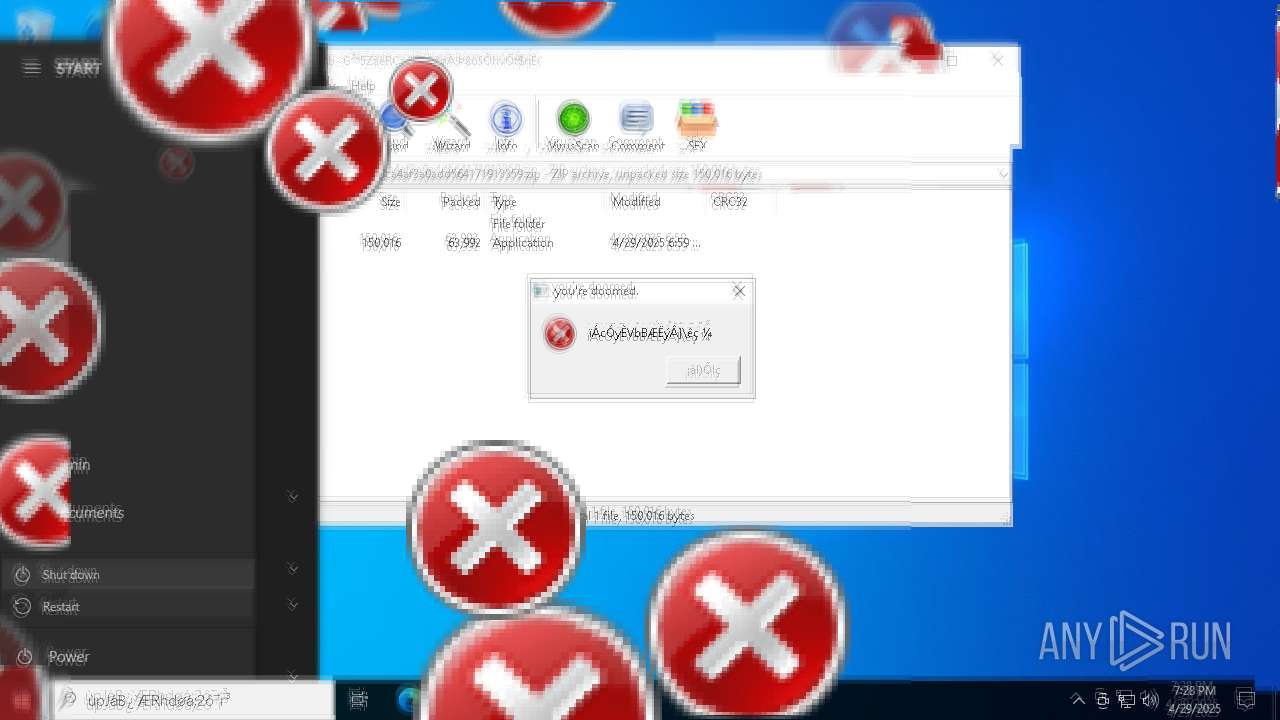
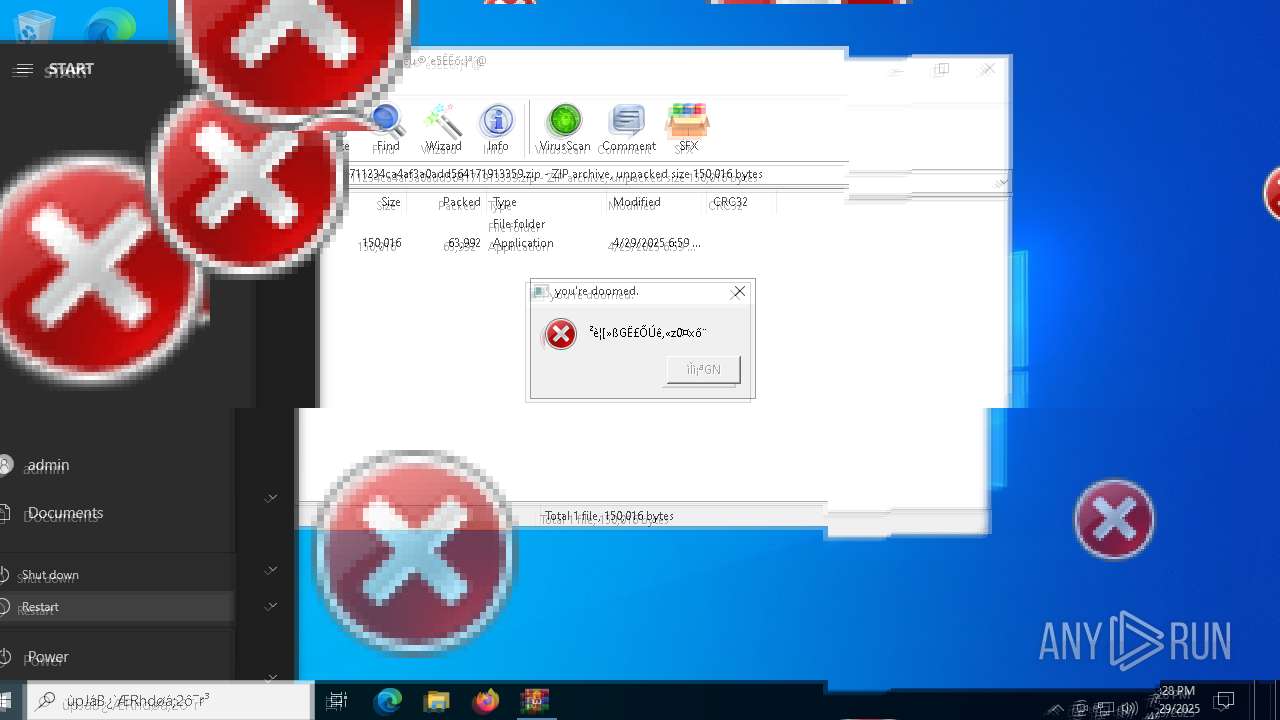
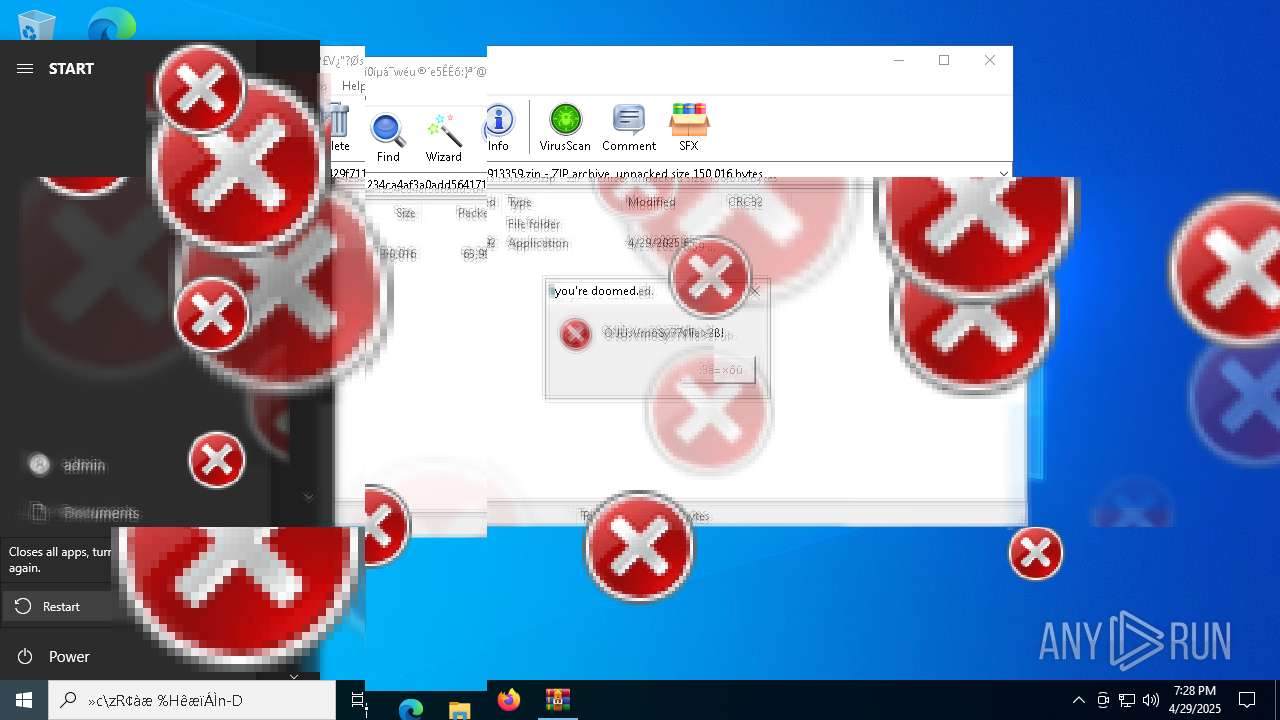
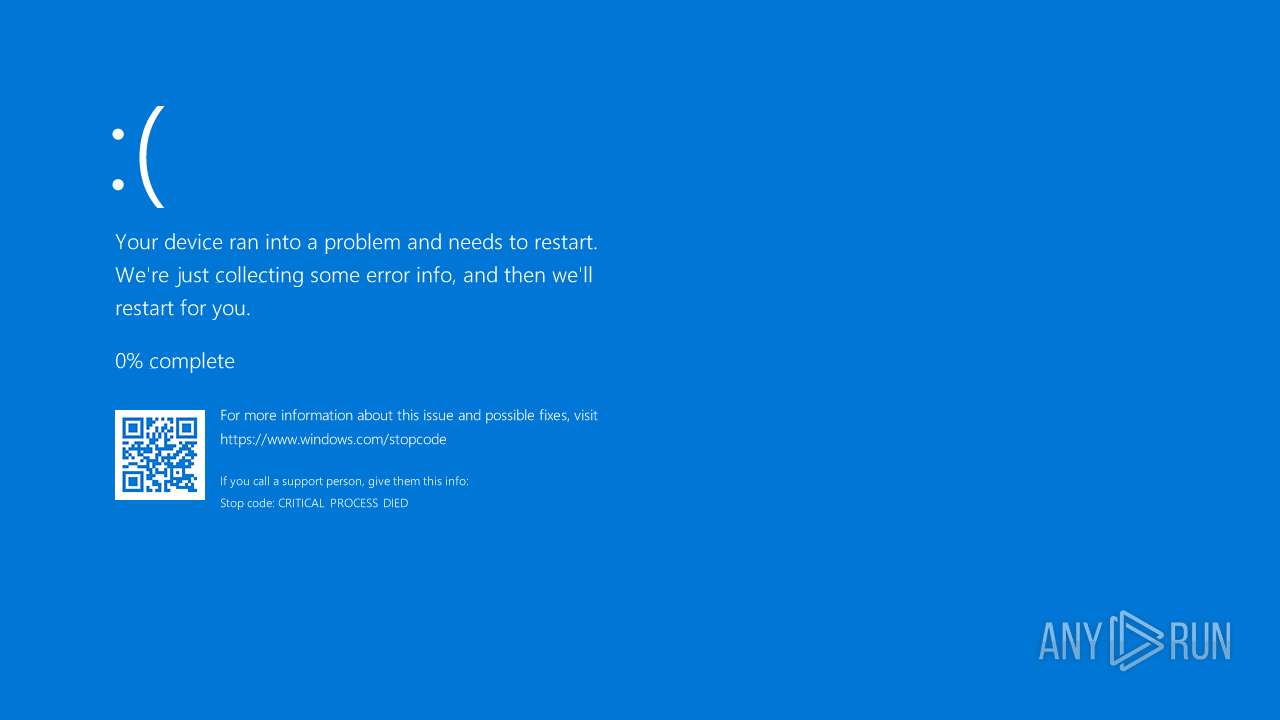
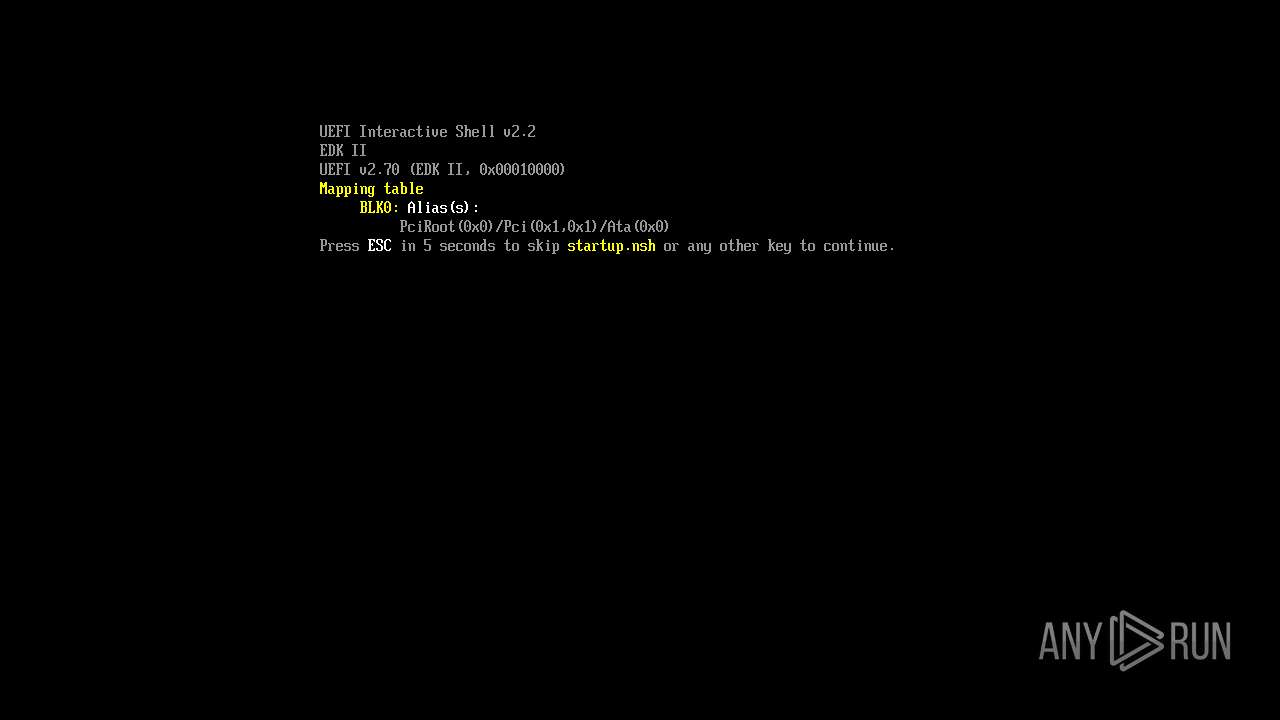
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 19:27:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
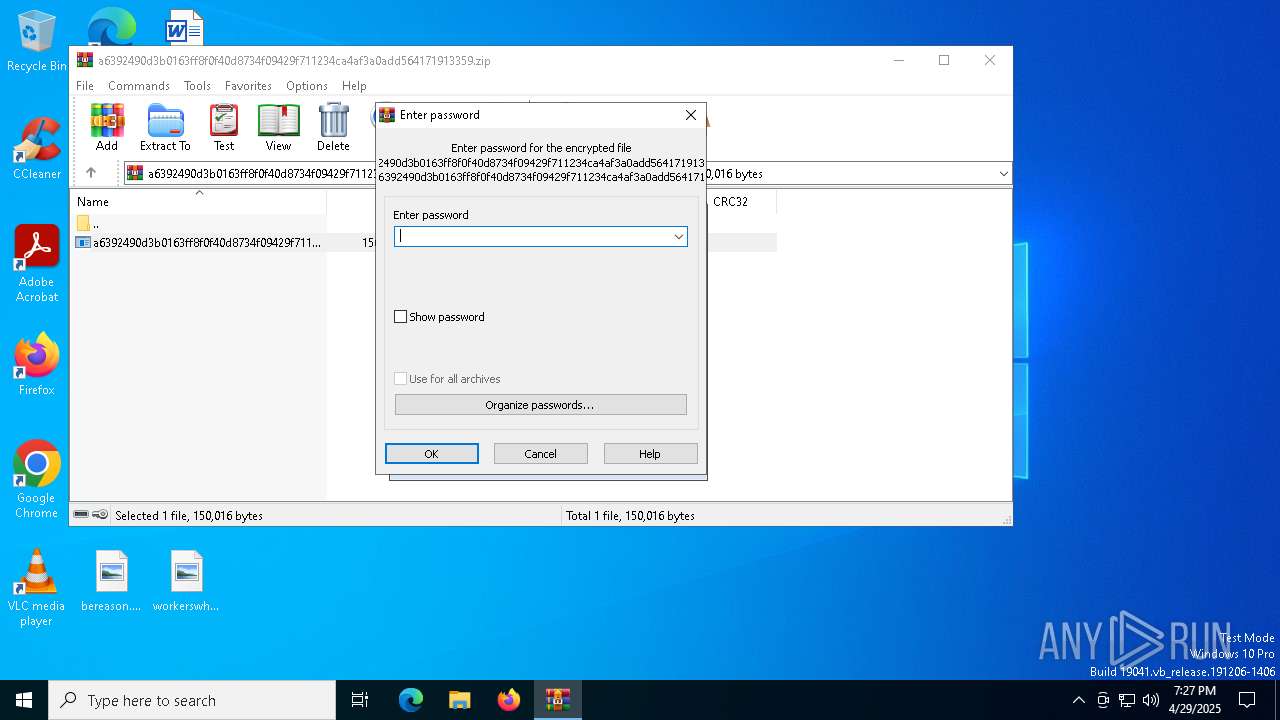
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 10FE7F8925F3FFB8CB786BB40F2B7AA9 |
| SHA1: | 37A18D89965279EBB4AD3F64A5249B424478ABC7 |
| SHA256: | 05DD264A8038F4AD3BA7E5D0DD9175797E0BA1249B6E006ECED620D03A74B1A1 |
| SSDEEP: | 1536:y0mlXu9YGeWNscza0n/ZV090Rz4wLjQrca5kv4Rq0jOrI7:y0cRWNsczZhq9Ad8rcmW4RdjO07 |
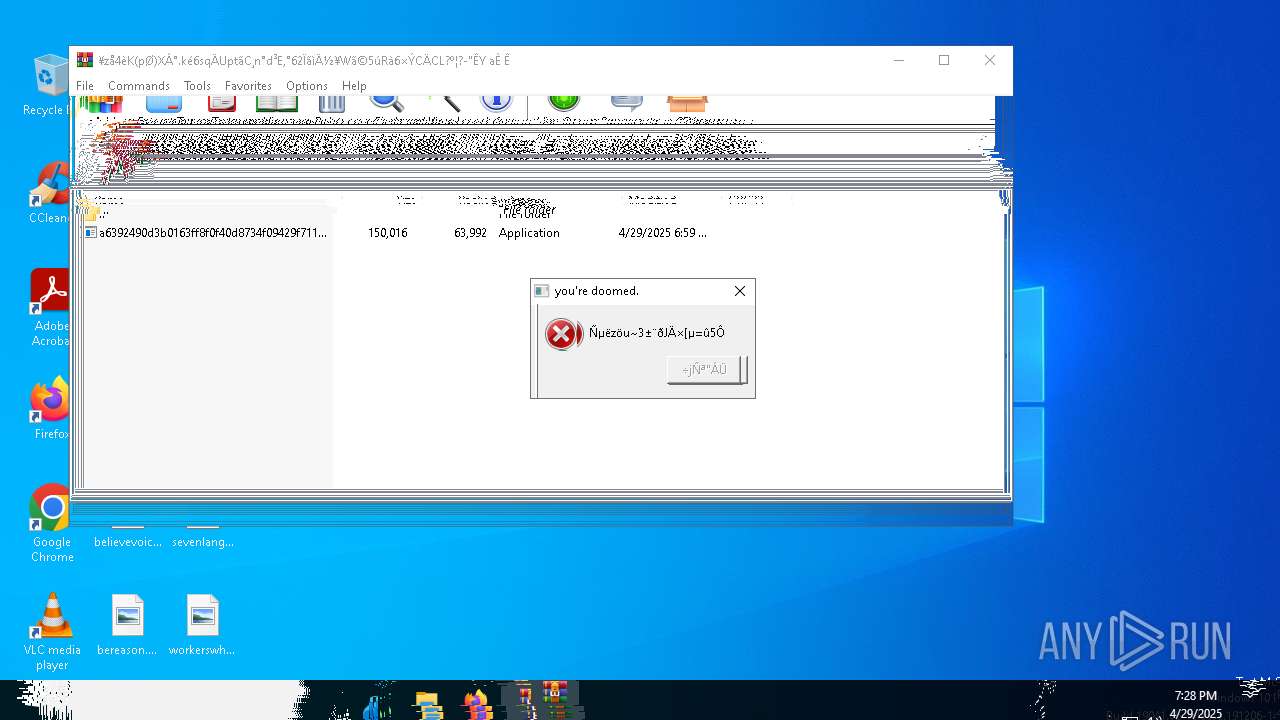
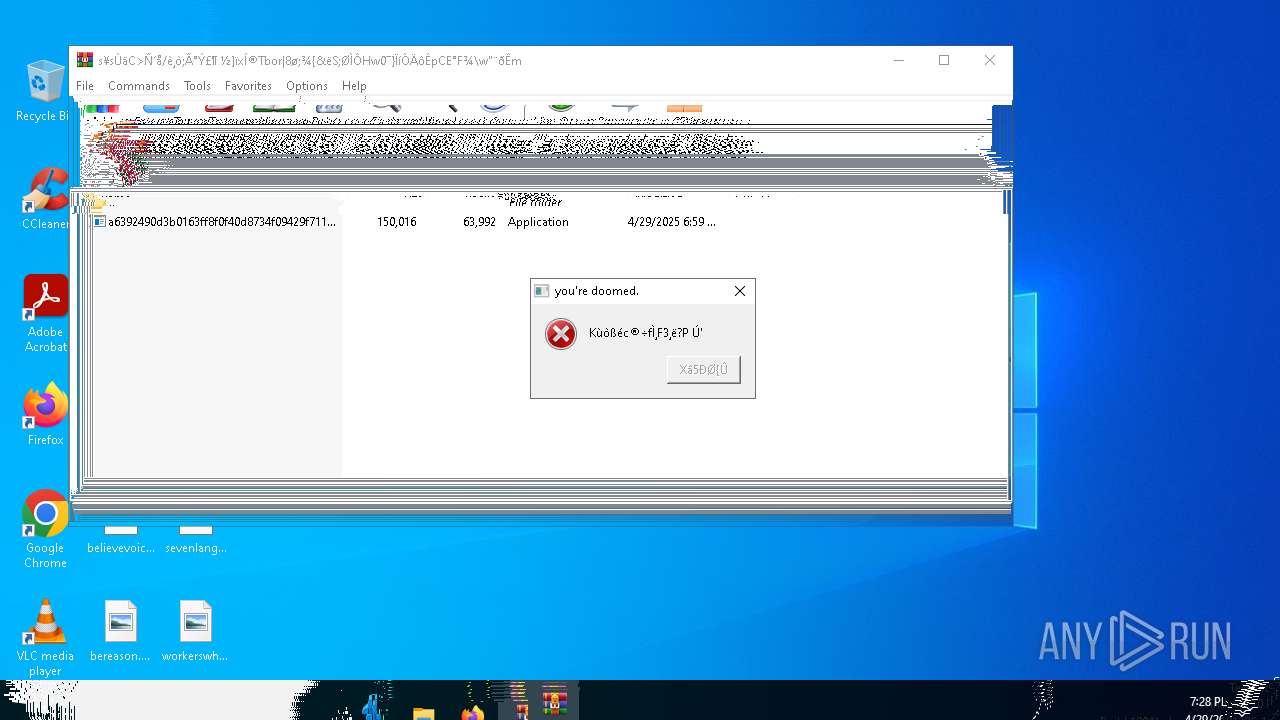
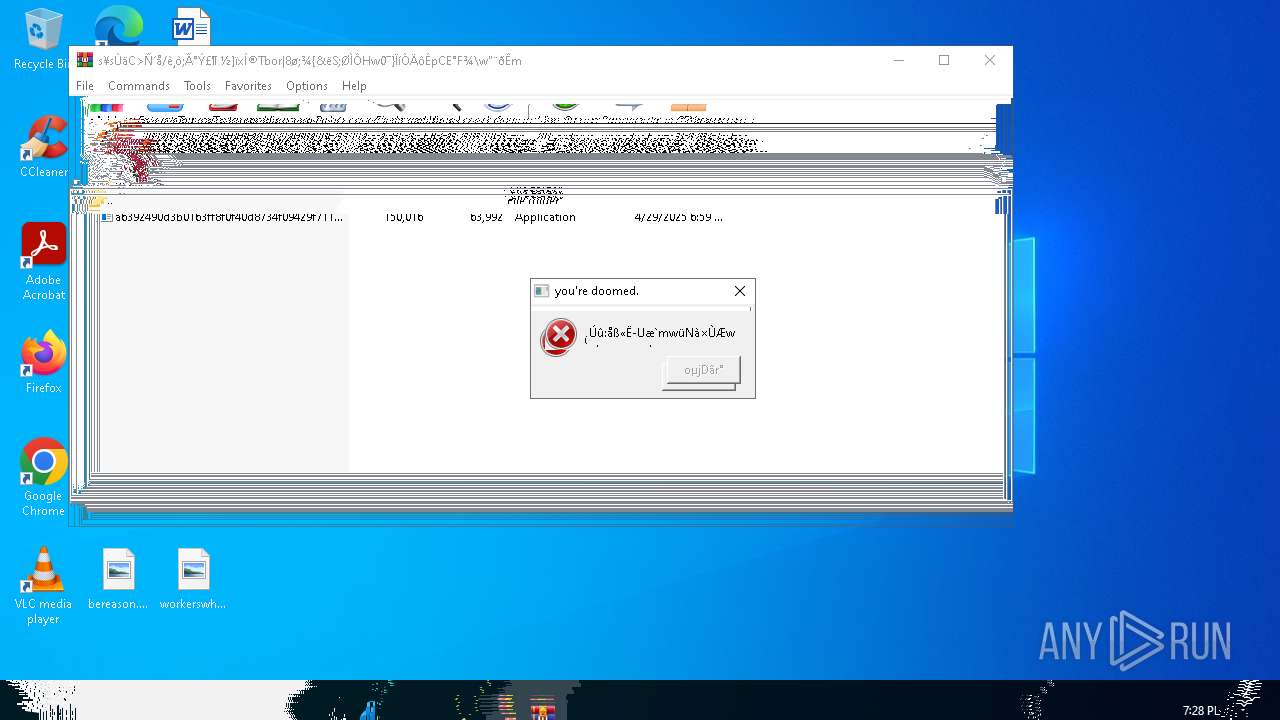
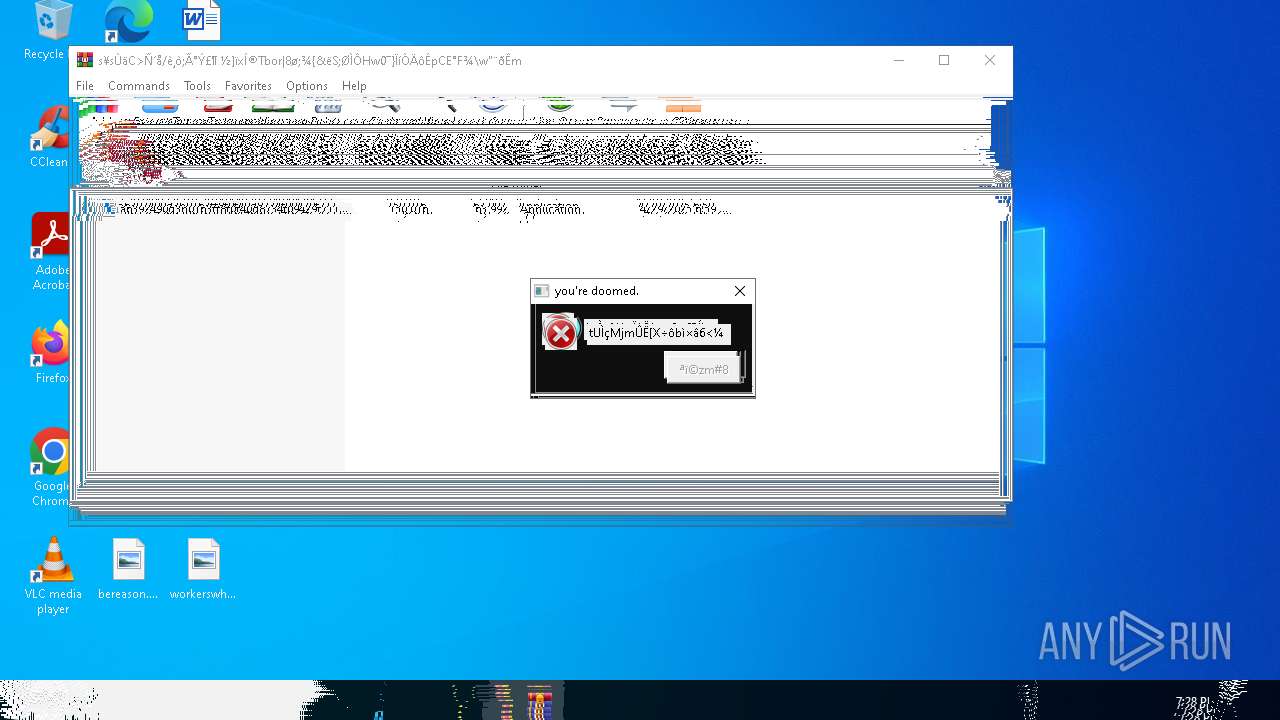
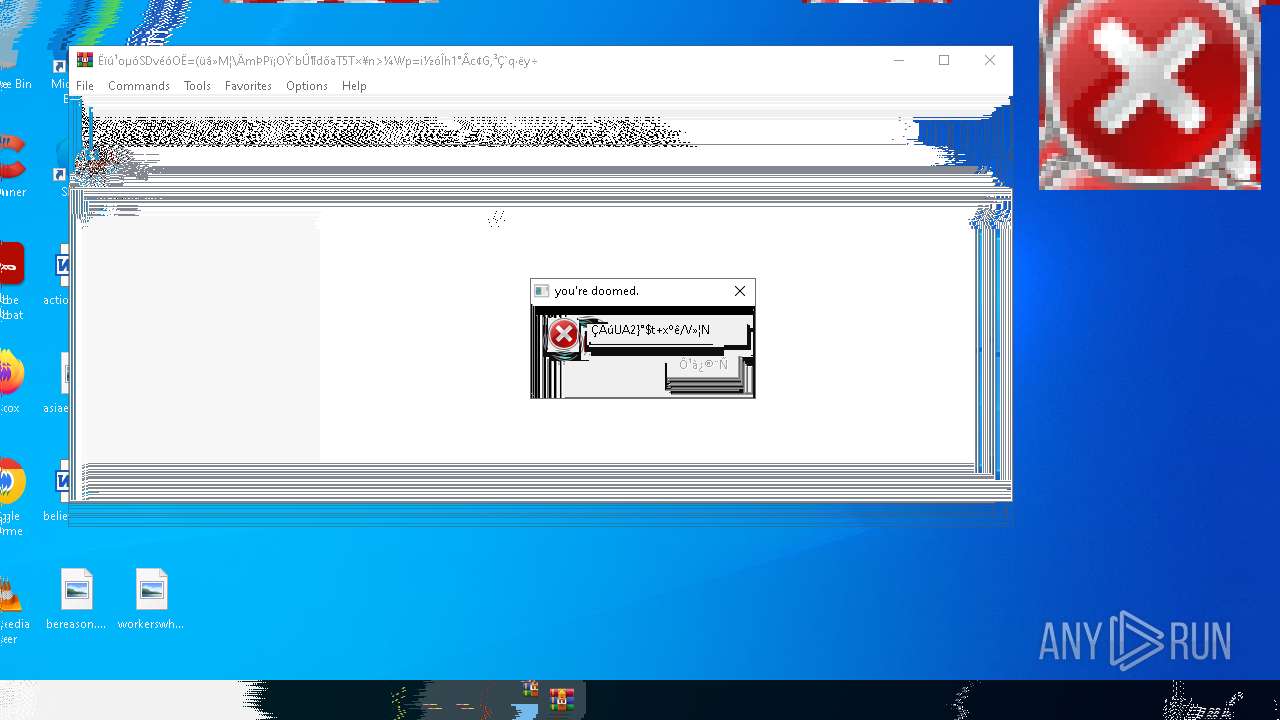
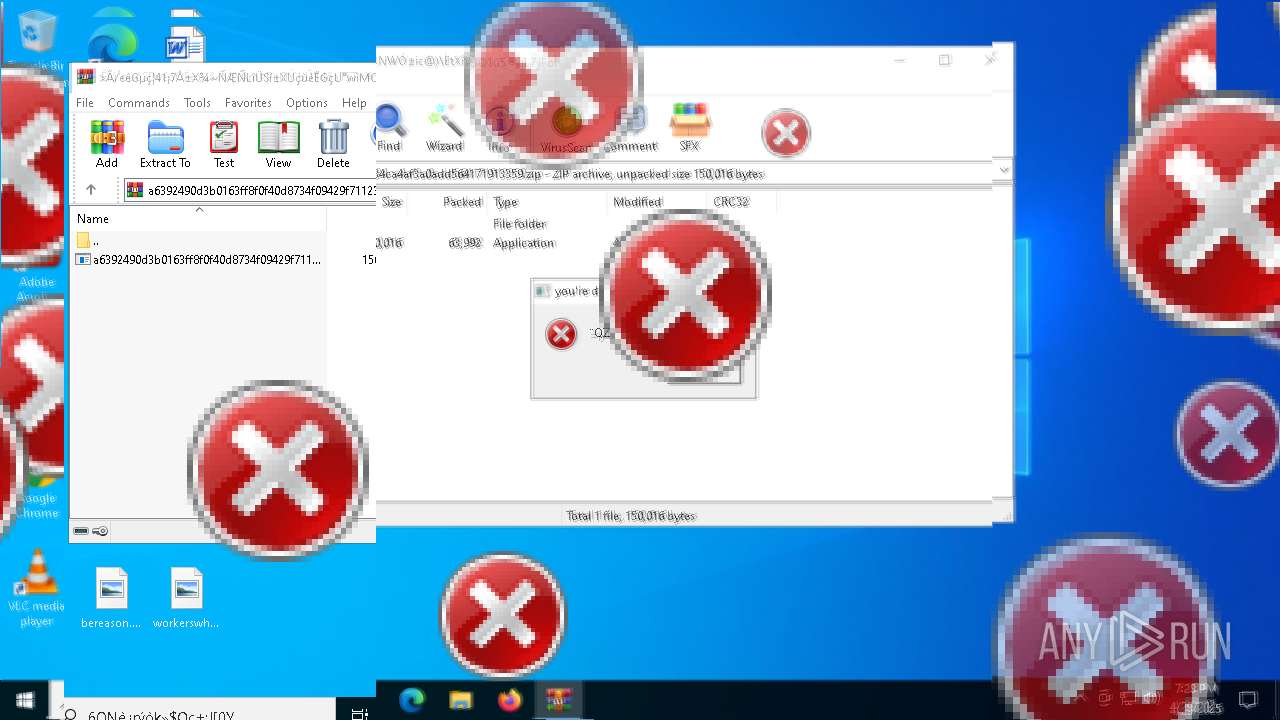
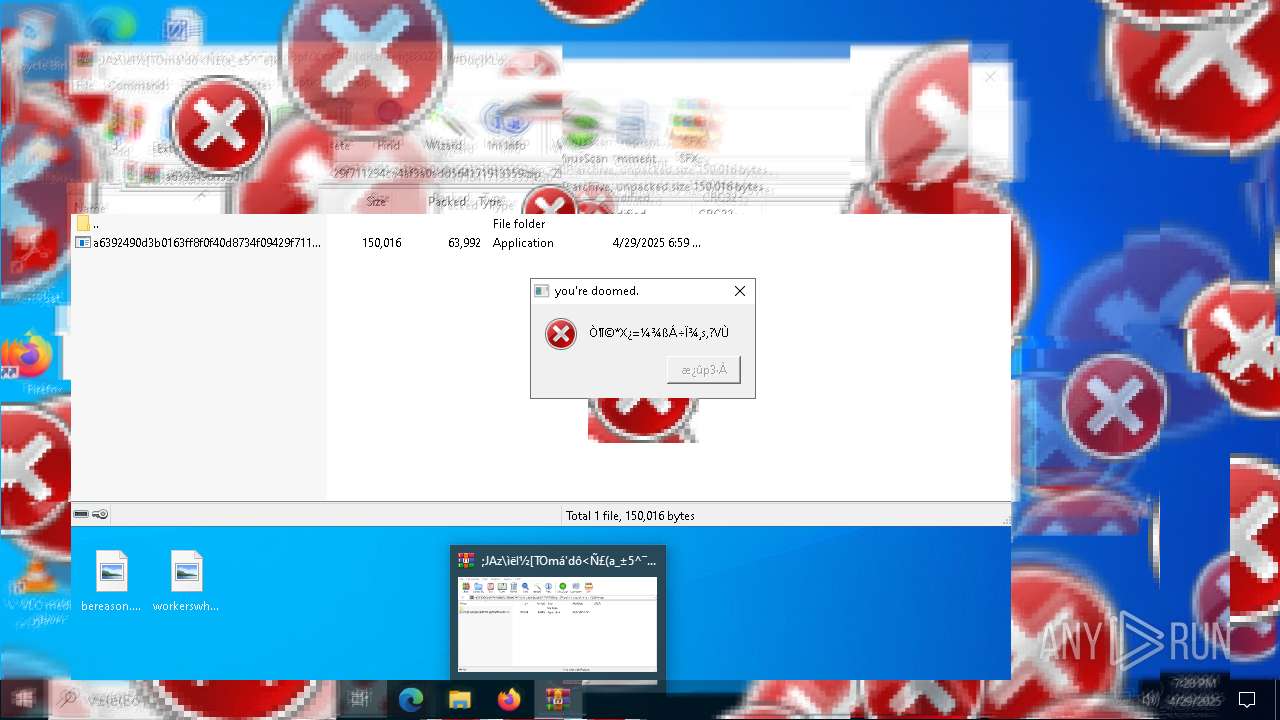
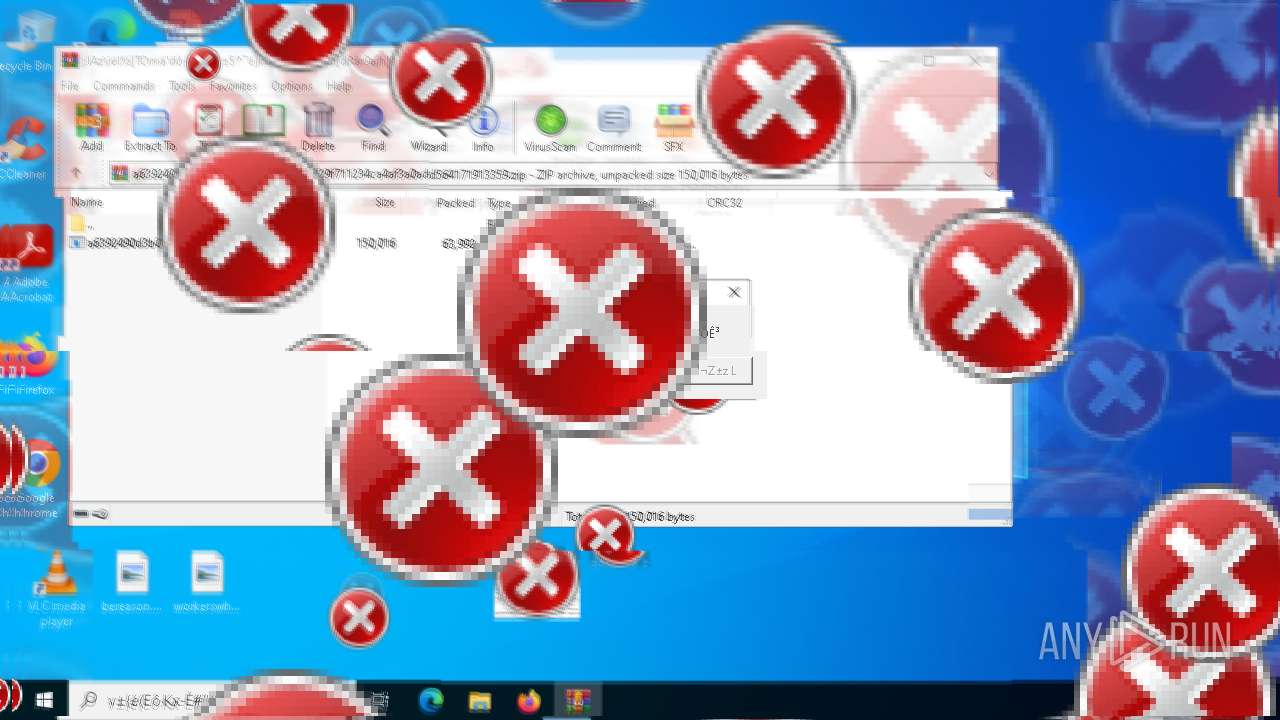
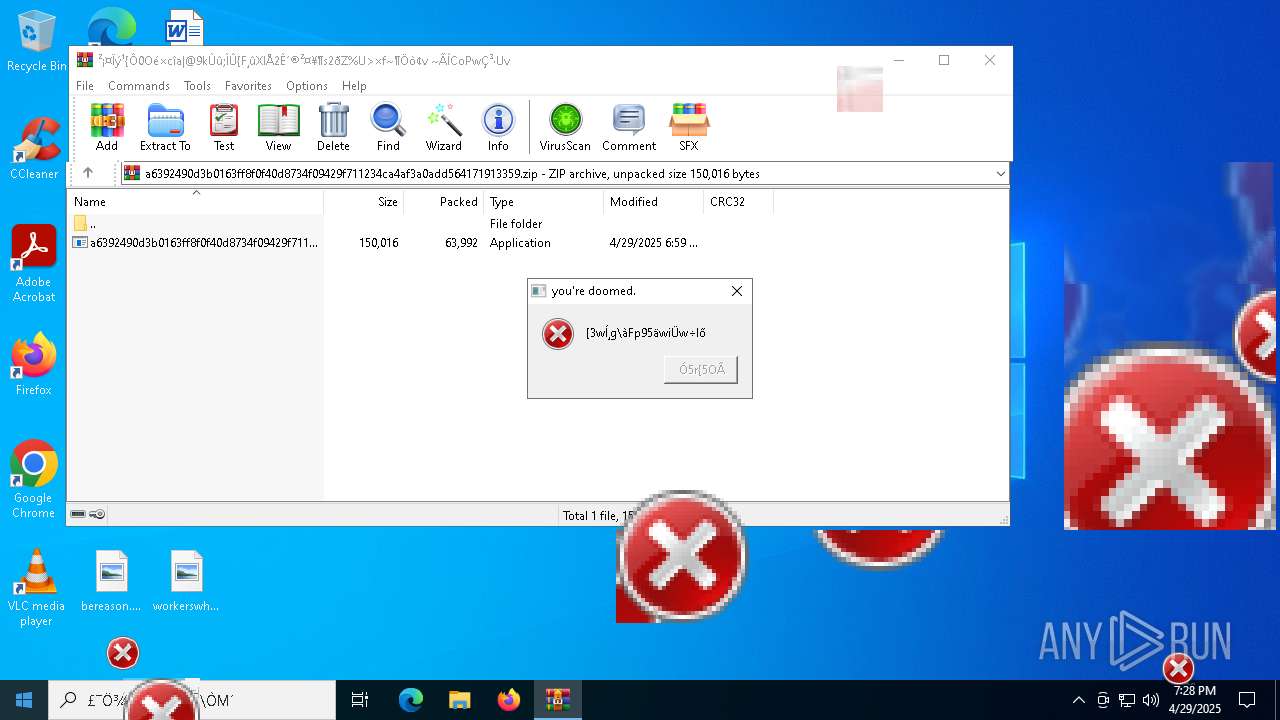
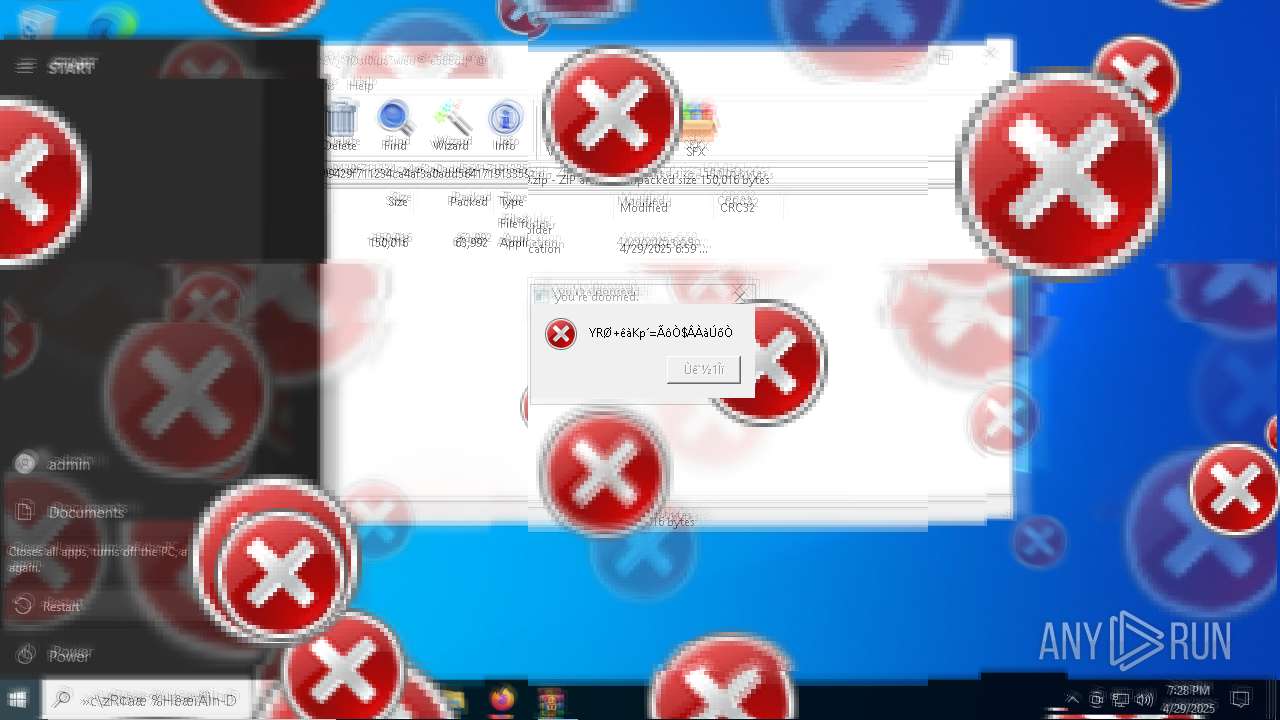
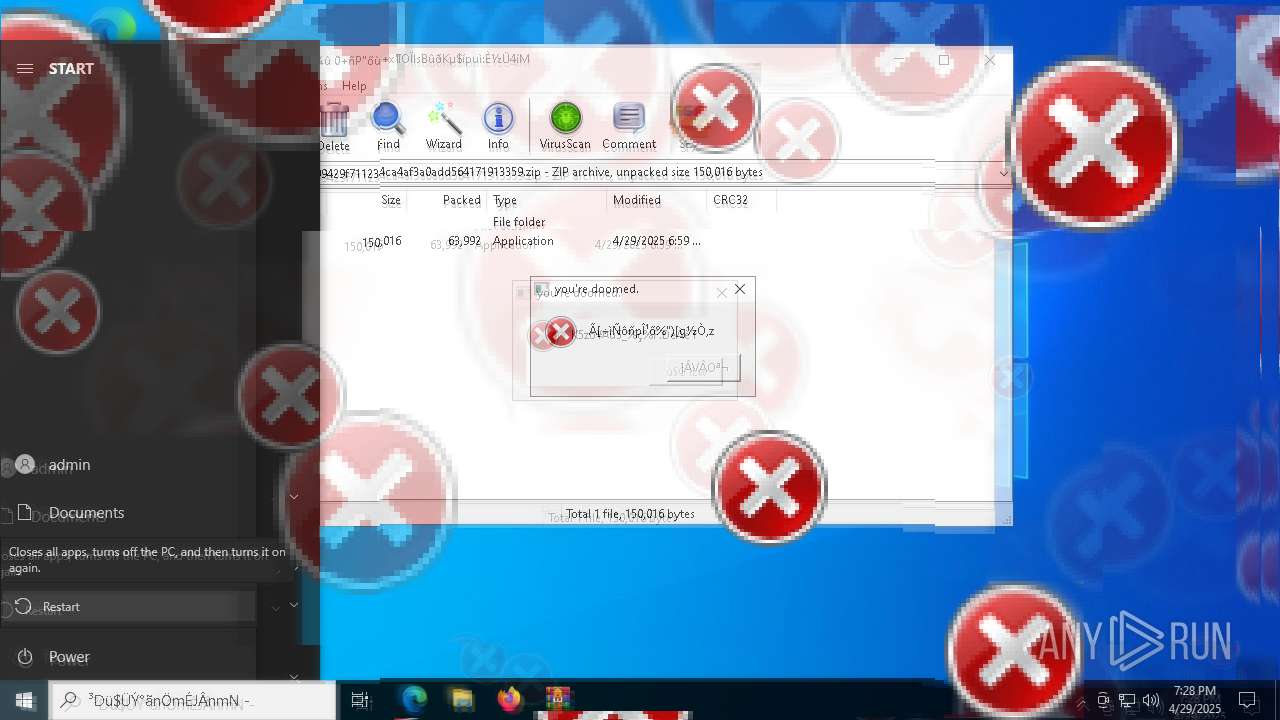
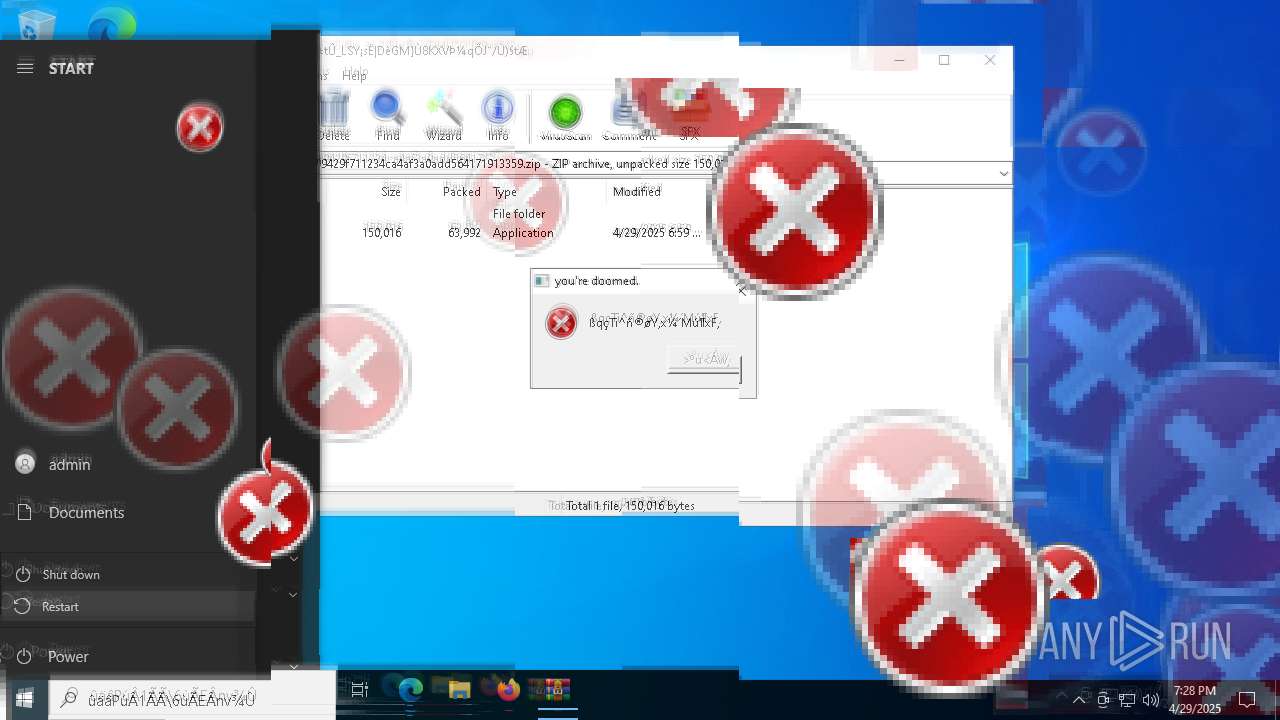
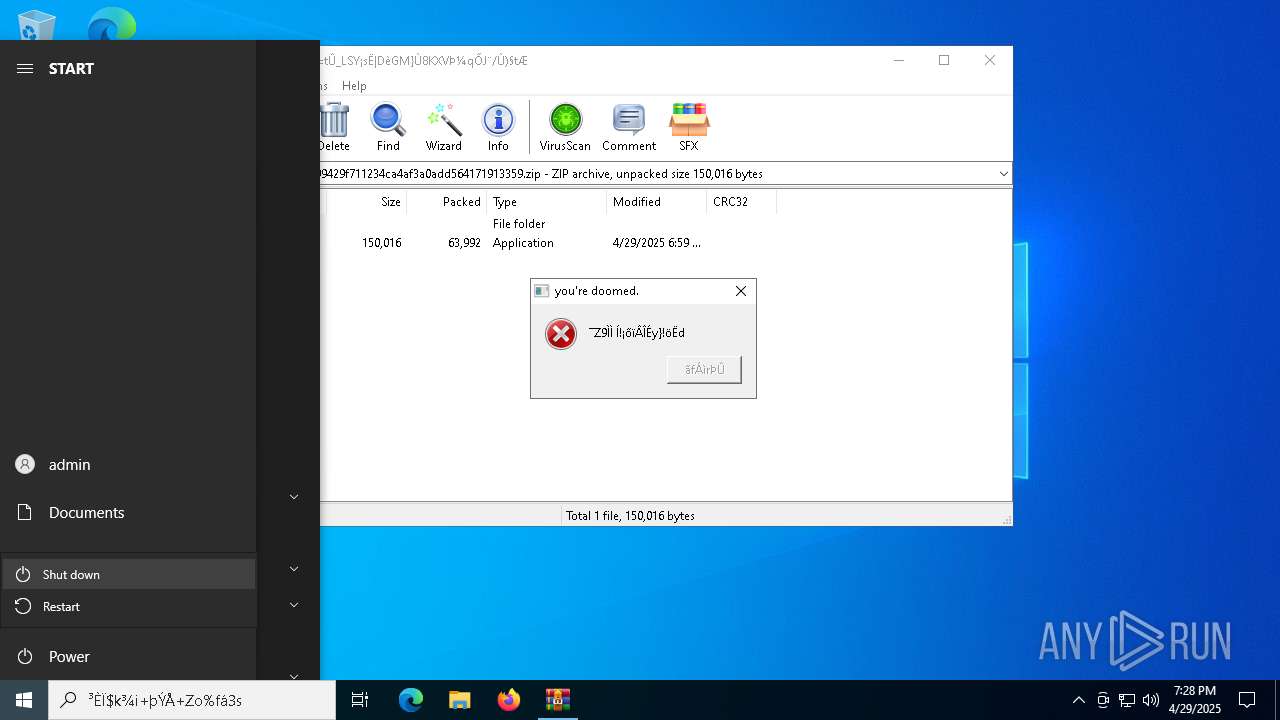
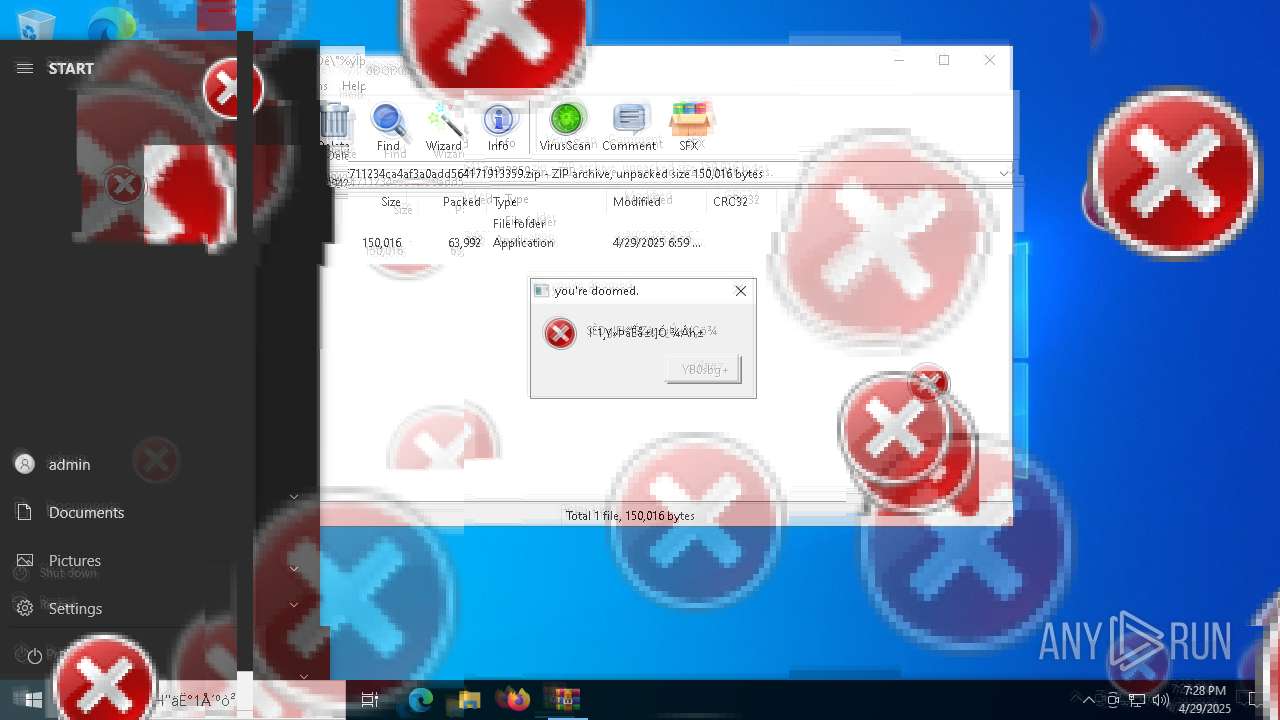
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 2852)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2852)
- a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe (PID: 1228)
Reads the date of Windows installation
- a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe (PID: 1228)
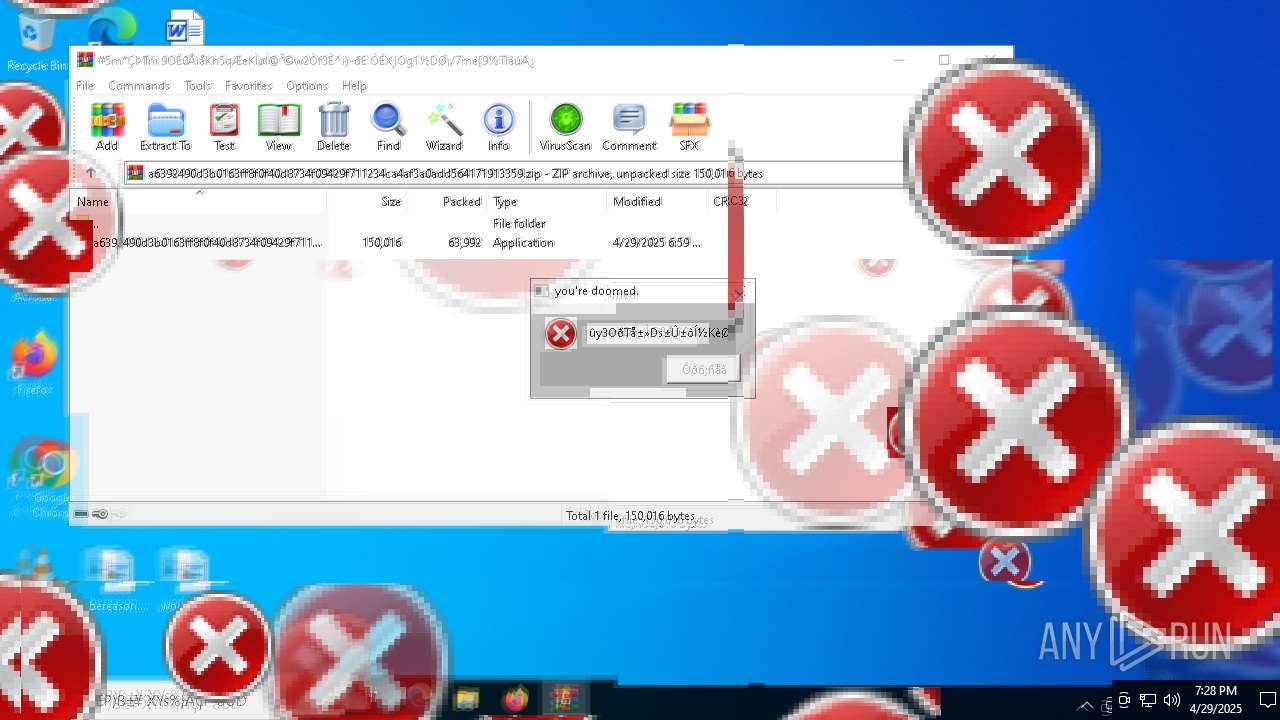
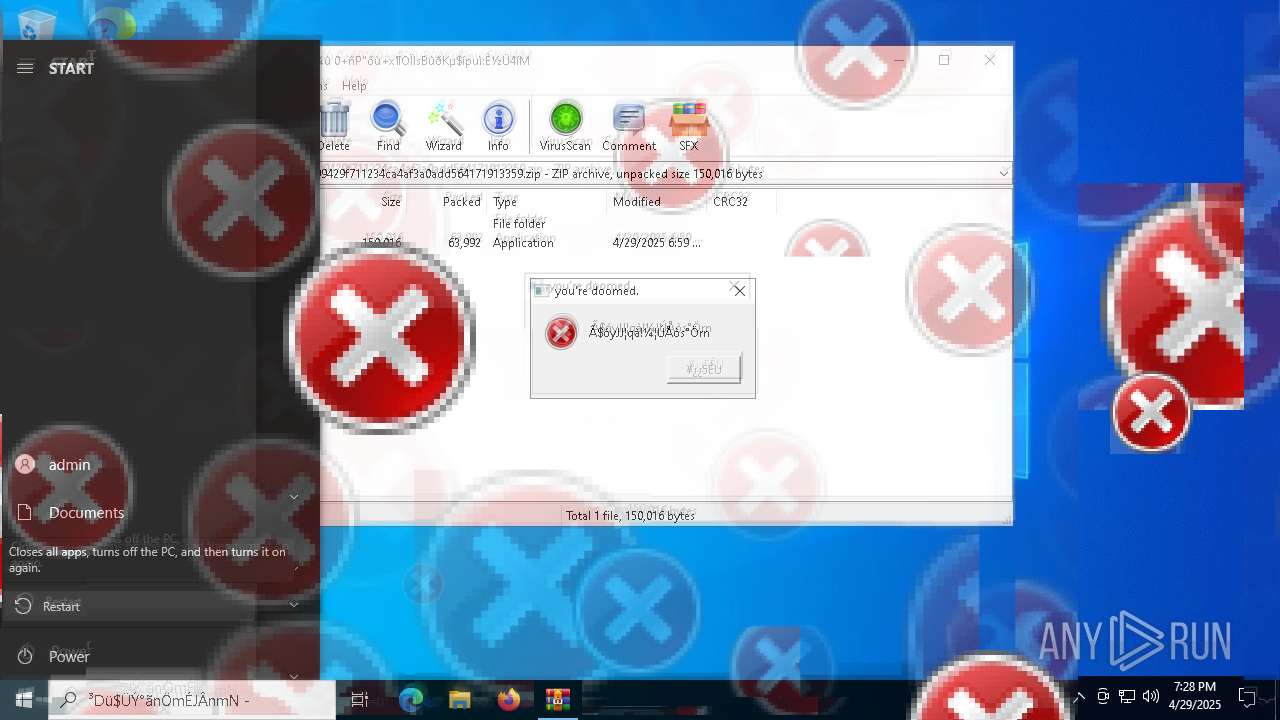
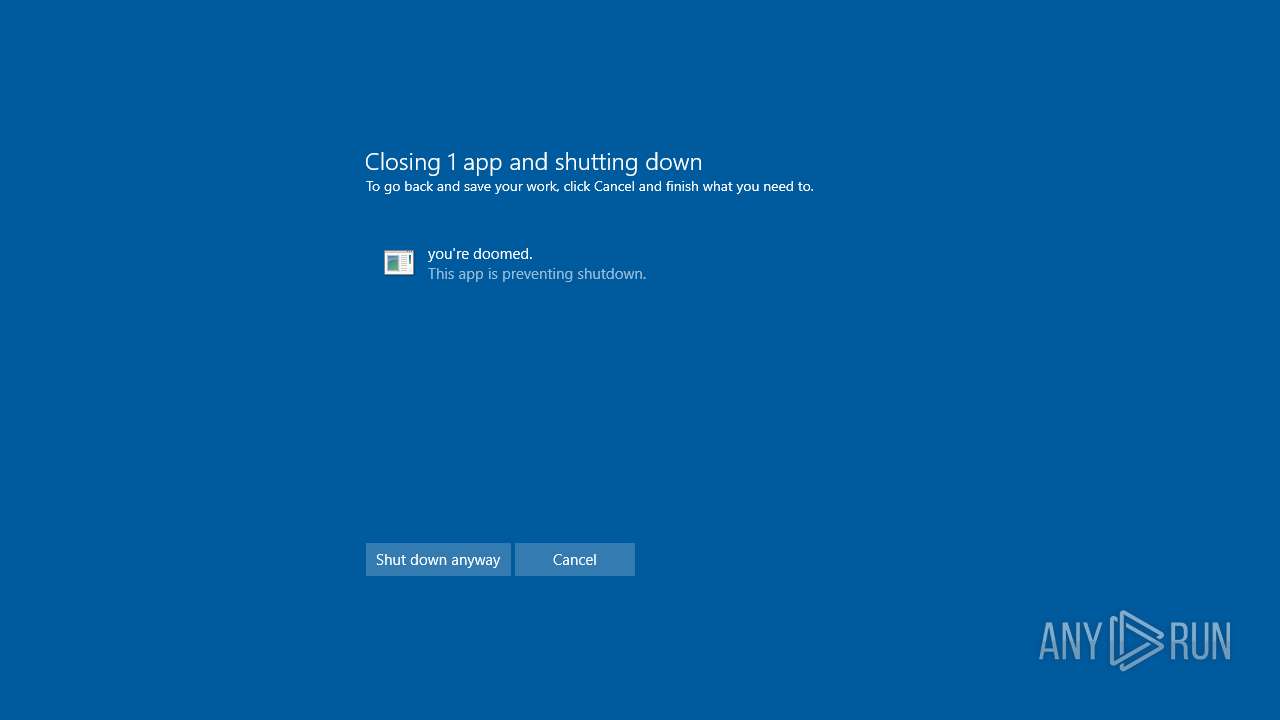
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 6392)
- cmd.exe (PID: 6068)
- cmd.exe (PID: 1184)
- cmd.exe (PID: 3272)
- cmd.exe (PID: 4608)
Starts CMD.EXE for commands execution
- a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe (PID: 1228)
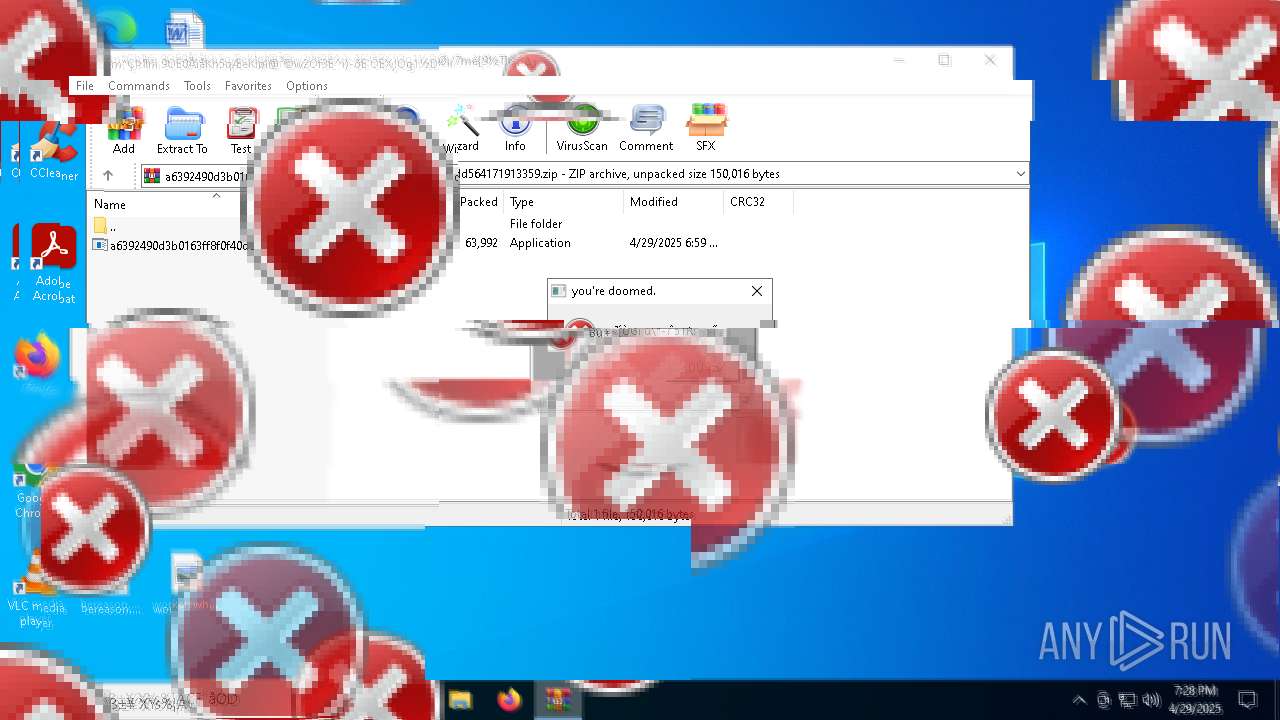
Executes application which crashes
- SearchApp.exe (PID: 1852)
- SearchApp.exe (PID: 2616)
- SearchApp.exe (PID: 1540)
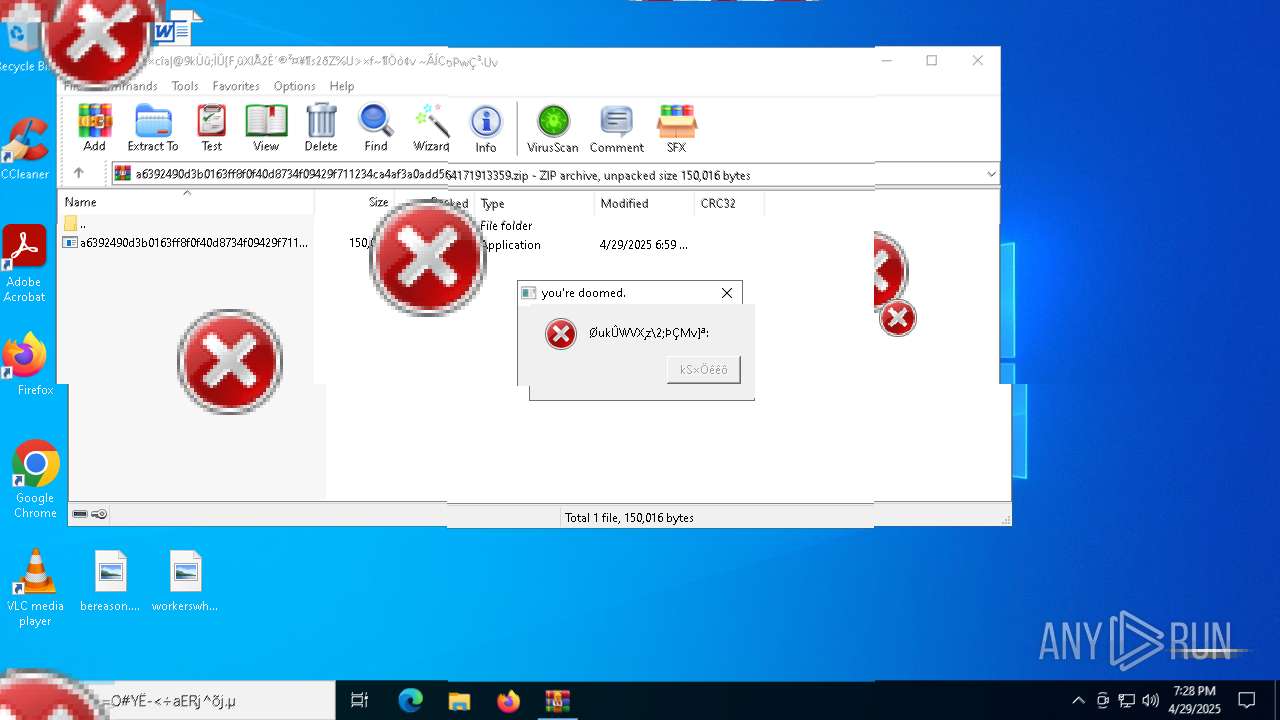
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 4428)
There is functionality for taking screenshot (YARA)
- a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe (PID: 1228)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2852)
Reads the computer name
- a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe (PID: 1228)
Checks supported languages
- a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe (PID: 1228)
Process checks computer location settings
- a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe (PID: 1228)
Reads the machine GUID from the registry
- a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe (PID: 1228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:04:29 18:59:28 |
| ZipCRC: | 0x7bdb454e |
| ZipCompressedSize: | 63992 |
| ZipUncompressedSize: | 150016 |
| ZipFileName: | a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe |
Total processes
186
Monitored processes
47
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 744 | takeown /f "C:\Program Files"*.* | C:\Windows\System32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | C:\WINDOWS\system32\WerFault.exe -u -p 1852 -s 2752 | C:\Windows\System32\WerFault.exe | — | SearchApp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | reg delete HKLM\SYSTEM\CurrentControlSet\Services /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1052 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1184 | "C:\Windows\System32\cmd.exe" /c takeown /f "%PROGRAMFILES(X86)%"*.* | C:\Windows\System32\cmd.exe | — | a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | "C:\WINDOWS\system32\wermgr.exe" "-outproc" "0" "2924" "3508" "3348" "3516" "0" "0" "0" "0" "0" "0" "0" "0" | C:\Windows\System32\wermgr.exe | — | SearchApp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2852.17155\a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2852.17155\a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe | WinRAR.exe | ||||||||||||
User: admin Company: Silverjetes Integrity Level: HIGH Description: omicron.exe Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
28 093
Read events
24 898
Write events
421
Delete events
2 774
Modification events
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.zip | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (920) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\.NET CLR Data\Performance |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
5
Suspicious files
19
Text files
49
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7140 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_Microsoft.Window_39fd55c4ee7446c589da1ab3e959162ed453fcb_ce03743e_a5979a63-3568-46c3-9d85-fba20edcd250\Report.wer | — | |
MD5:— | SHA256:— | |||
| 7140 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\SearchApp.exe.2616.dmp | — | |
MD5:— | SHA256:— | |||
| 2924 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\TempState\CortanaUnifiedTileModelCache.dat~RF1171a3.TMP | — | |
MD5:— | SHA256:— | |||
| 2924 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\DeviceSearchCache\AppCache133904285079415624.txt~RF11730a.TMP | — | |
MD5:— | SHA256:— | |||
| 2924 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\ConstraintIndex\Input_{e277b488-b659-4b32-98c0-66b8319aaf28}\settingsglobals.txt | text | |
MD5:BBEADC734AD391F67BE0C31D5B9CBF7B | SHA256:218042BC243A1426DD018D484F9122662DBA2C44A0594C37FFB3B3D1D0FB454A | |||
| 5588 | cmd.exe | C:\Windows\Logs\waasmediccapsule\WaasRemediation.001.etl | binary | |
MD5:D9768B1B36E92D098D2CEC1F625CBEC0 | SHA256:E126D8F8803260793443532BBDE3F99BD23E76957A4A9B96D2B787A4BF752C86 | |||
| 2924 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\GEH\POF-2924.dmp | — | |
MD5:— | SHA256:— | |||
| 2852 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2852.17155\a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe | executable | |
MD5:292EA56DEFD8561F16D4FD74A6D242DD | SHA256:A6392490D3B0163FF8F0F40D8734F09429F711234CA4AF3A0ADD564171913359 | |||
| 2924 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\DeviceSearchCache\AppCache133904285079415624.txt | text | |
MD5:9EF87B2D1EE756815F4BC4EFEF493626 | SHA256:938311B263F15E710E46949BB811EF7FC7C00051FAEB8DD197CCB5FCB57DDE7D | |||
| 2924 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\TempState\~ortanaUnifiedTileModelCache.tmp | binary | |
MD5:8E240A454B23534A5D4E20837AD42FFE | SHA256:98DFD3CFF9FD85E1724D0689EBD908A6B04A2A75F653182A00818A01C386A45A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
16
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |