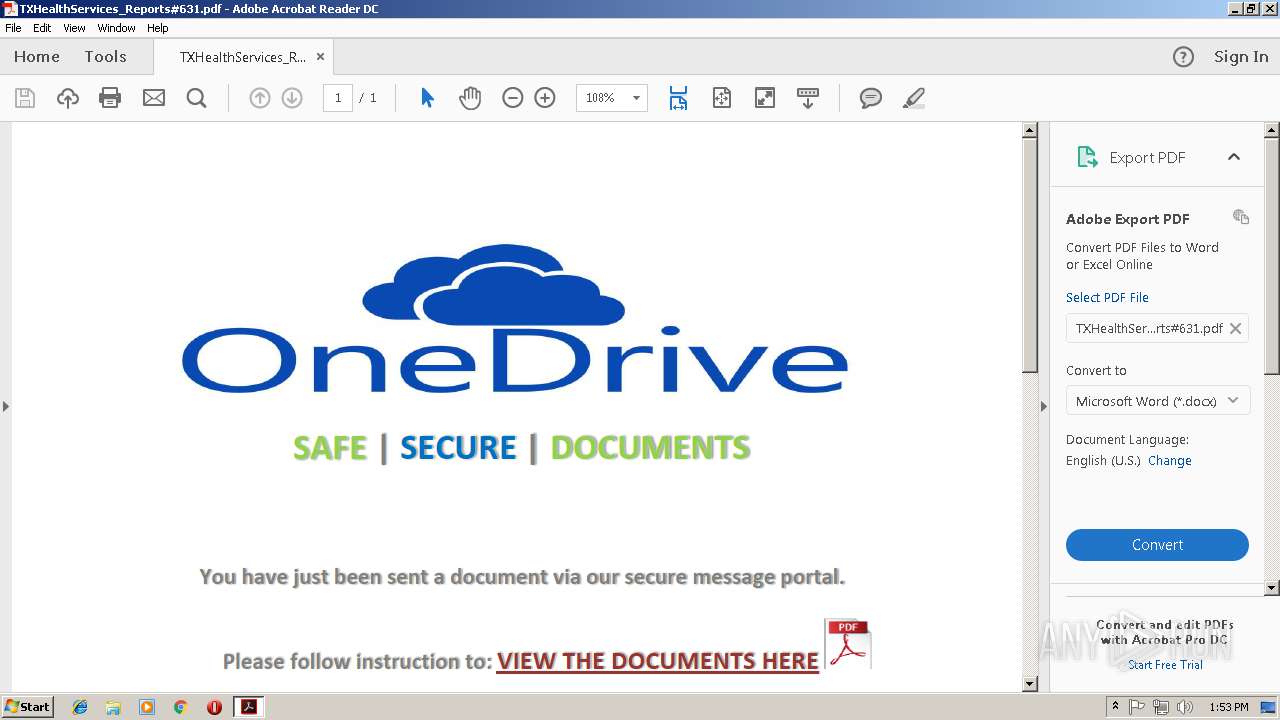
| File name: | TXHealthServices_Reports#631.pdf |
| Full analysis: | https://app.any.run/tasks/53e8e7db-9a5f-4a55-a4c8-4c7059ddebe6 |
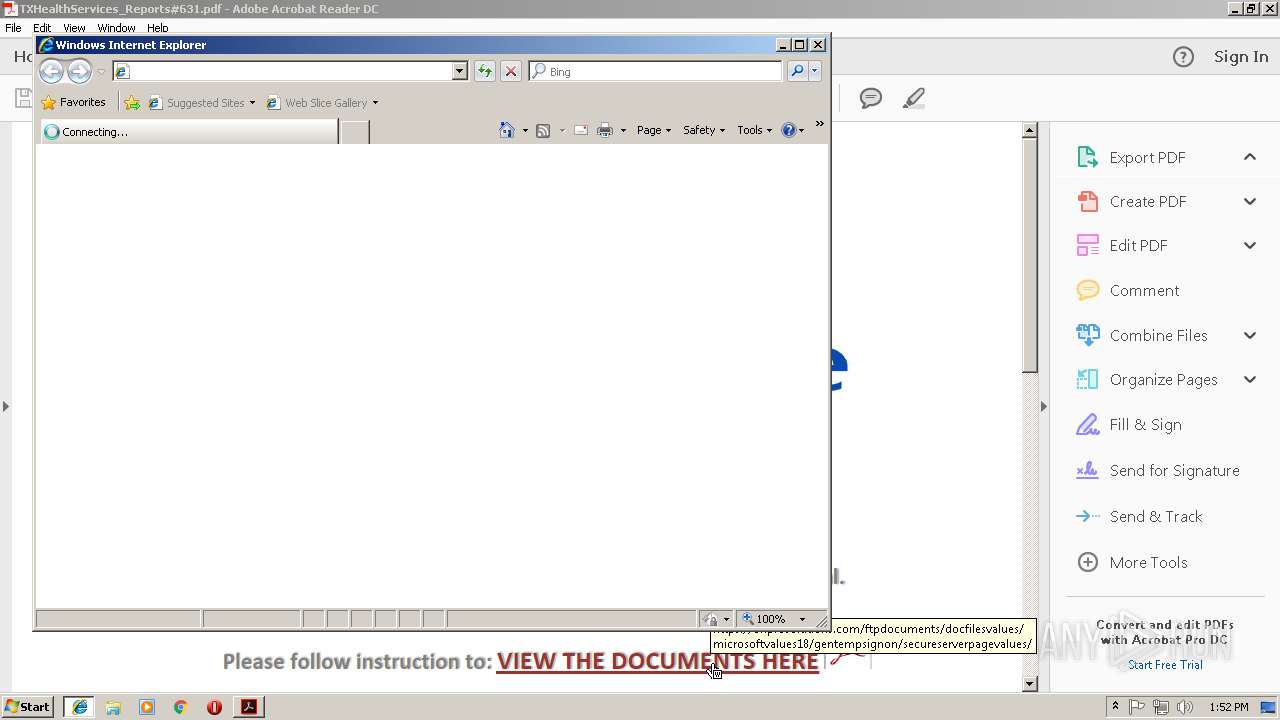
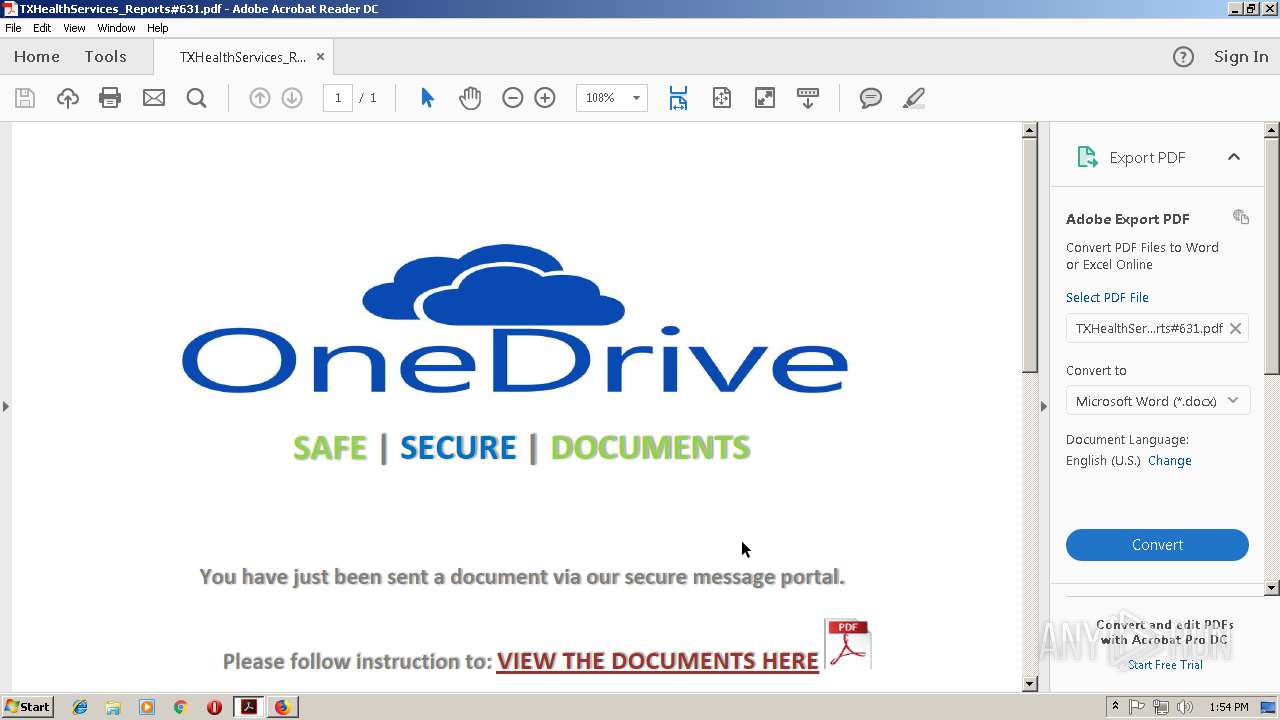
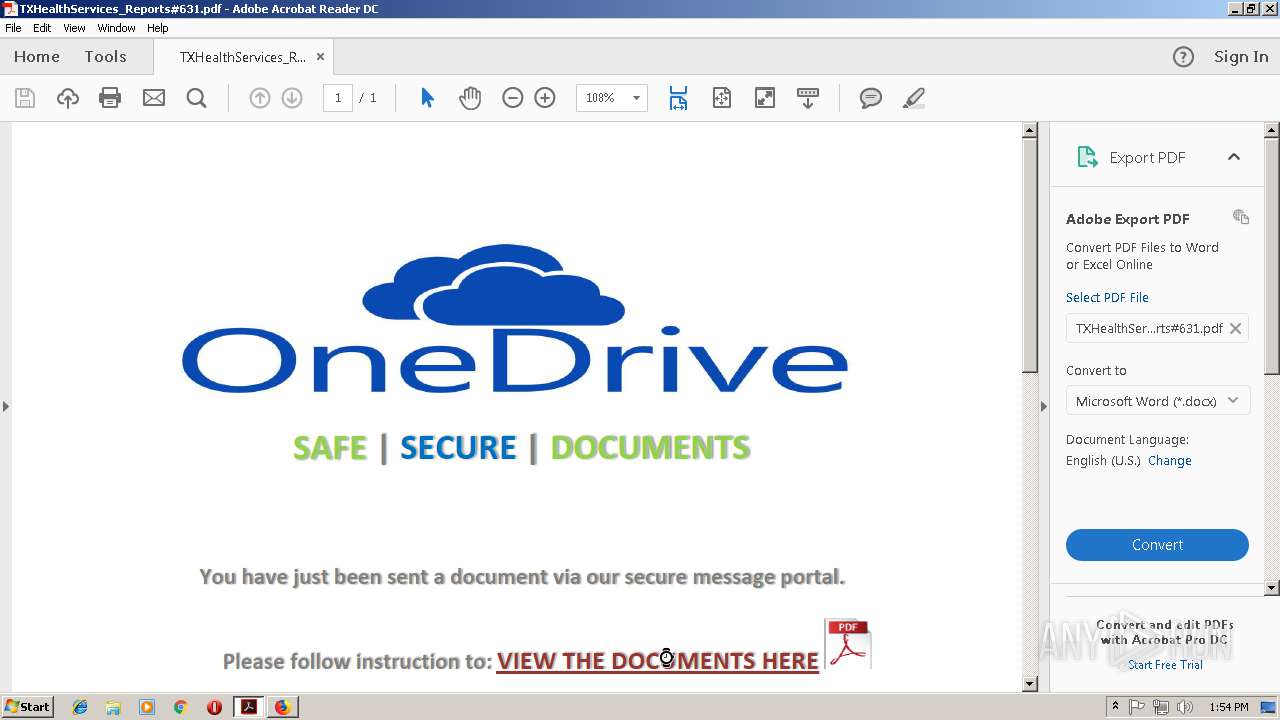
| Verdict: | Malicious activity |
| Analysis date: | November 14, 2018, 13:52:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/pdf |
| File info: | PDF document, version 1.7 |
| MD5: | 439FB16EB28BADEA7CA9DA87BE40794D |
| SHA1: | FD60F9EBE034454976B1C417F97AFC5F5EB1BA44 |
| SHA256: | 05D1CDA0BA8094D6E4FCB5D39DABEDEA4E3CDFF397ABF52554104693BBC83441 |
| SSDEEP: | 12288:0VU2CbQziVBz0YxJLs9+QntPHWnB8Mrn3vYFeP7Wot:iU2g/z0wJLJSFWB8MLX |
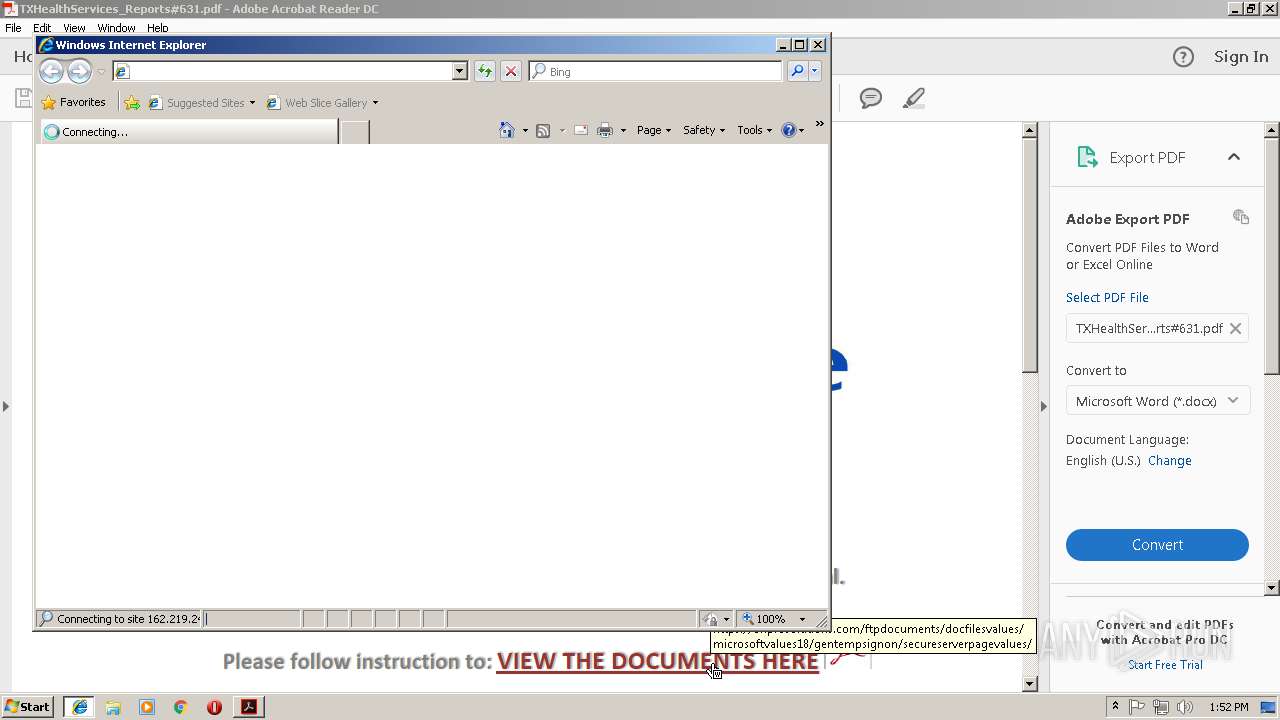
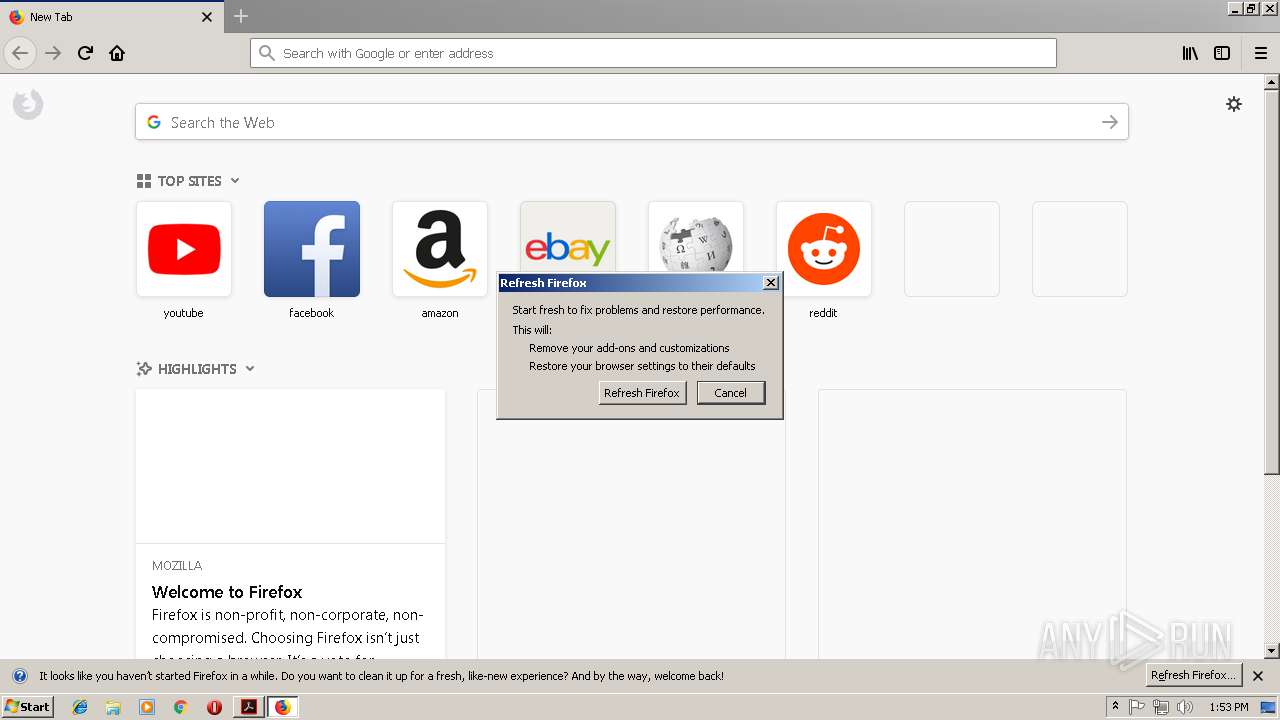
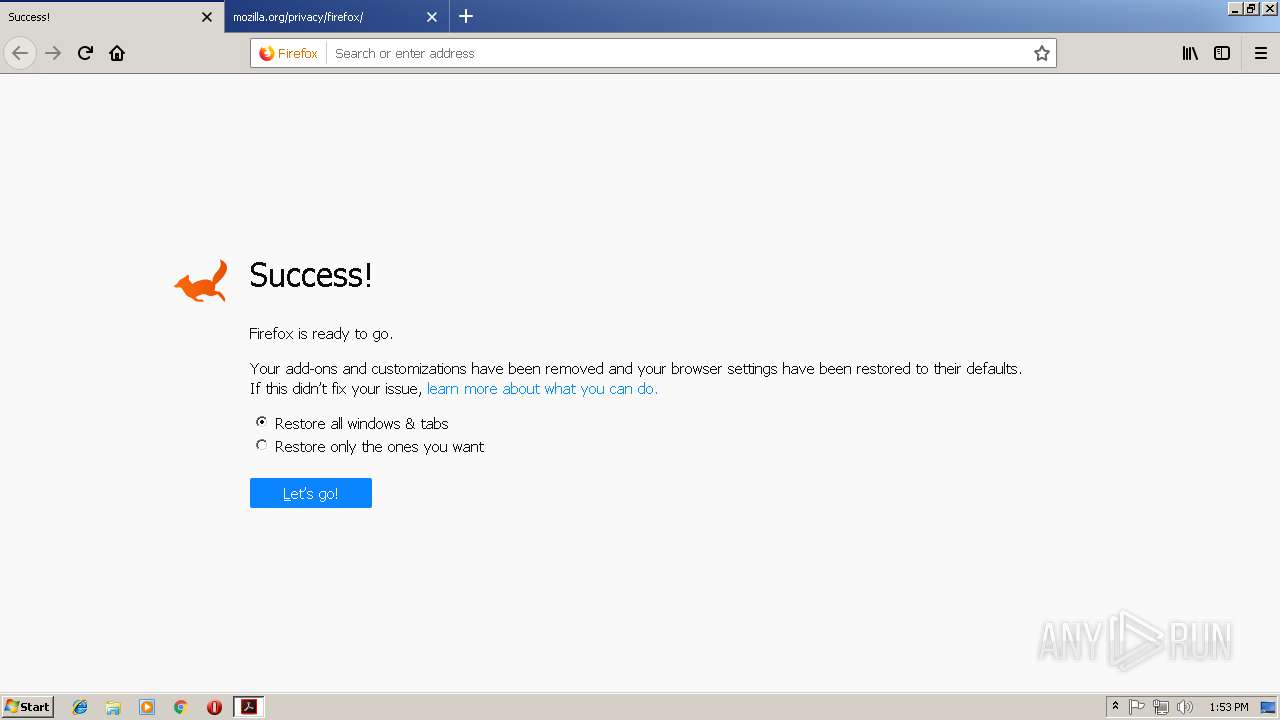
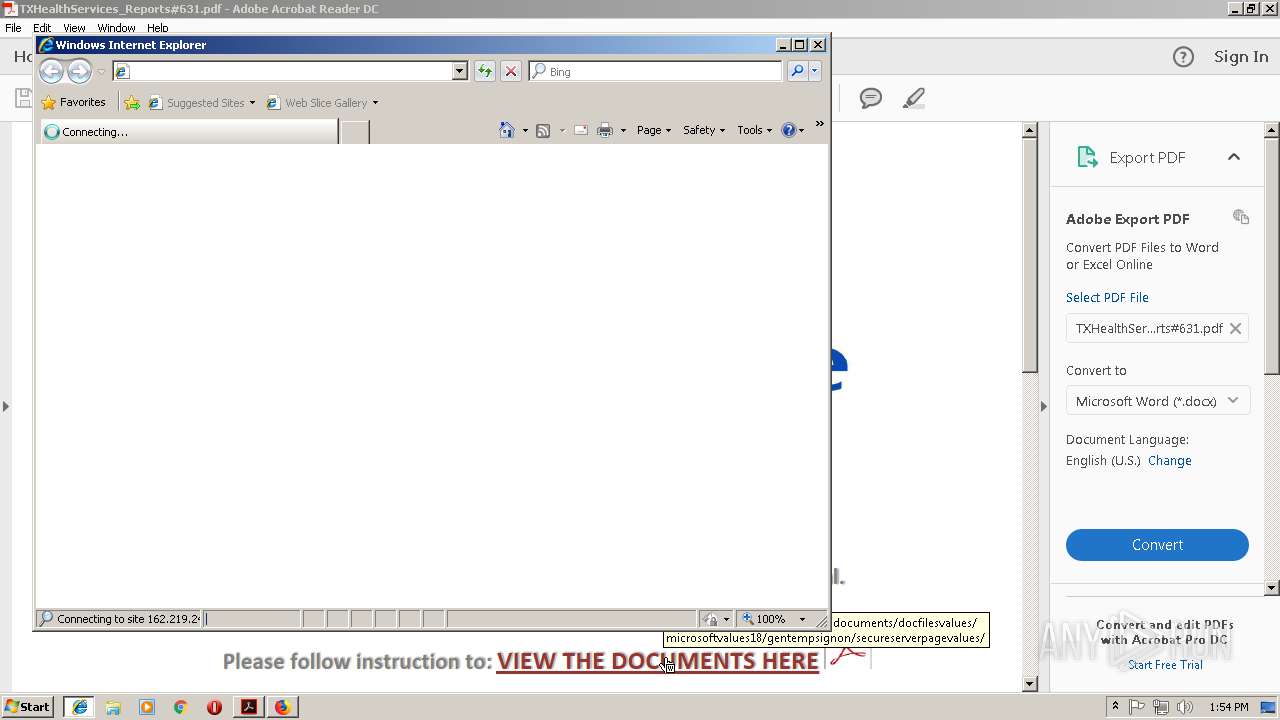
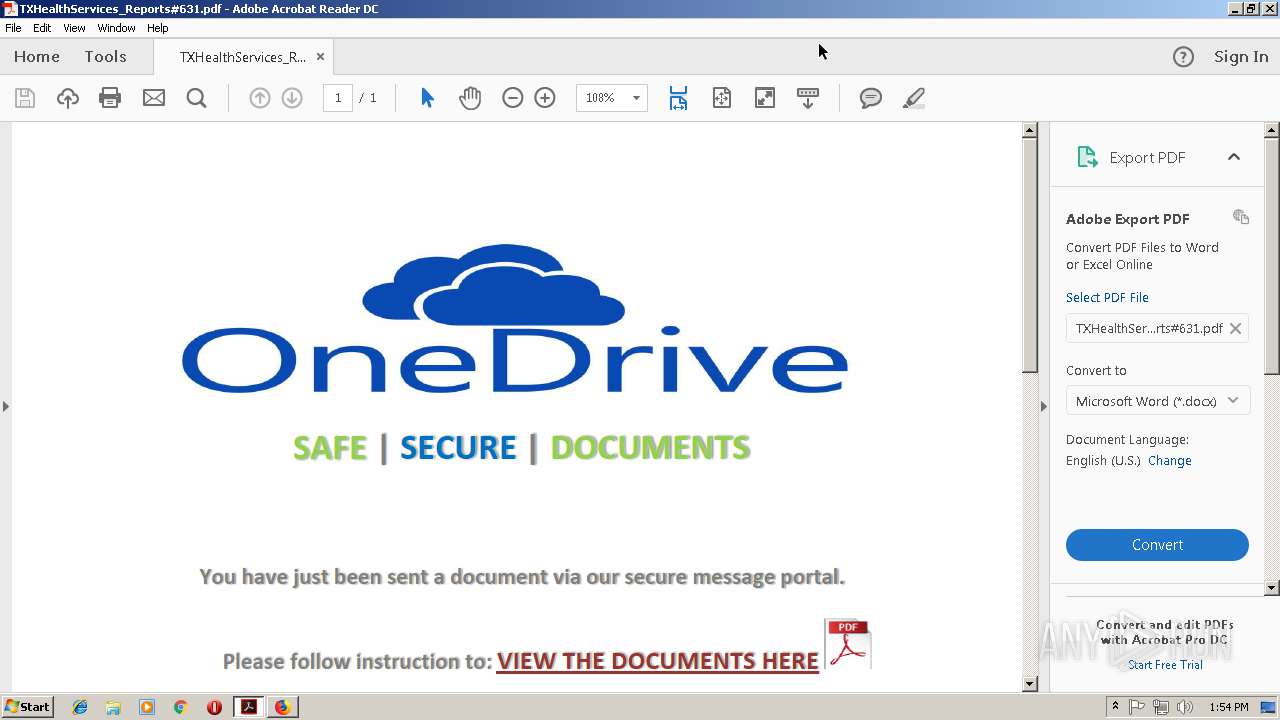
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2092)
SUSPICIOUS
Starts Internet Explorer
- AcroRd32.exe (PID: 3688)
Creates files in the program directory
- AdobeARM.exe (PID: 2816)
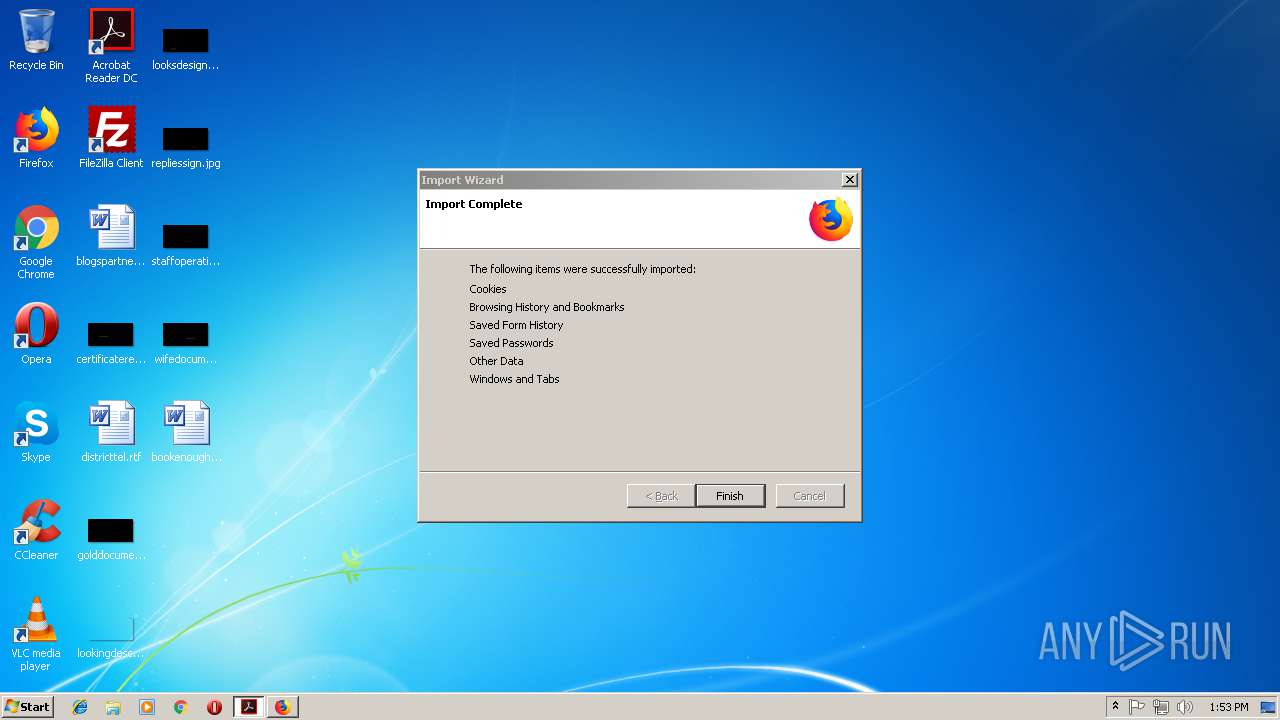
Executable content was dropped or overwritten
- firefox.exe (PID: 2932)
INFO
Application launched itself
- RdrCEF.exe (PID: 2992)
- AcroRd32.exe (PID: 3688)
- iexplore.exe (PID: 3664)
- firefox.exe (PID: 3360)
- firefox.exe (PID: 2932)
- iexplore.exe (PID: 3824)
Changes internet zones settings
- iexplore.exe (PID: 3664)
- iexplore.exe (PID: 3824)
Reads internet explorer settings
- iexplore.exe (PID: 2856)
Reads Internet Cache Settings
- iexplore.exe (PID: 2856)
- iexplore.exe (PID: 568)
Reads CPU info
- firefox.exe (PID: 3360)
- firefox.exe (PID: 3024)
- firefox.exe (PID: 4052)
- firefox.exe (PID: 2584)
- firefox.exe (PID: 1128)
- firefox.exe (PID: 2932)
- firefox.exe (PID: 2556)
- firefox.exe (PID: 3280)
- firefox.exe (PID: 2672)
- firefox.exe (PID: 3964)
- firefox.exe (PID: 3452)
Creates files in the user directory
- firefox.exe (PID: 3360)
- AcroRd32.exe (PID: 3688)
- firefox.exe (PID: 2932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| | | Adobe Portable Document Format (100) |
EXIF
| PDFVersion: | 1.7 |
|---|---|
| Linearized: | No |
| PageCount: | 1 |
| Language: | en-US |
| TaggedPDF: | Yes |
| Author: | MacBook |
| Creator: | Microsoft® Word 2016 |
| CreateDate: | 2018:11:12 08:38:14-05:00 |
| ModifyDate: | 2018:11:12 08:38:14-05:00 |
| Producer: | Microsoft® Word 2016 |
XMP
| XMPToolkit: | 3.1-701 |
|---|---|
| Producer: | Microsoft® Word 2016 |
| Creator: | MacBook |
| CreatorTool: | Microsoft® Word 2016 |
| CreateDate: | 2018:11:12 08:38:14-05:00 |
| ModifyDate: | 2018:11:12 08:38:14-05:00 |
| DocumentID: | uuid:D0588D87-CA3C-46F3-9E82-B4E012D0270C |
| InstanceID: | uuid:D0588D87-CA3C-46F3-9E82-B4E012D0270C |
Total processes
59
Monitored processes
25
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 568 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3824 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2932.12.1575651342\1601190138" -childID 3 -isForBrowser -prefsHandle 1816 -prefsLen 2403 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2932 "\\.\pipe\gecko-crash-server-pipe.2932" 2052 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2092 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2556 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2932.0.35999418\1171979307" -childID 1 -isForBrowser -prefsHandle 1684 -prefsLen 2358 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2932 "\\.\pipe\gecko-crash-server-pipe.2932" 1660 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2584 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3360.12.2067022880\1115077519" -childID 3 -isForBrowser -prefsHandle 2852 -prefsLen 11808 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3360 "\\.\pipe\gecko-crash-server-pipe.3360" 2972 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2672 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2932.18.1518400229\1259956672" -childID 4 -isForBrowser -prefsHandle 2352 -prefsLen 3685 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2932 "\\.\pipe\gecko-crash-server-pipe.2932" 2364 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2816 | "C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe" /PRODUCT:Reader /VERSION:15.0 /MODE:3 | C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Reader and Acrobat Manager Exit code: 0 Version: 1.824.27.2646 Modules
| |||||||||||||||
| 2856 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3664 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2896 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="2992.0.1273552570\170581707" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2932 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
Total events
2 899
Read events
2 714
Write events
183
Delete events
2
Modification events
| (PID) Process: | (3036) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (3036) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral |
| Operation: | write | Name: | bExpandRHPInViewer |
Value: 1 | |||
| (PID) Process: | (3036) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\NoTimeOut |
| Operation: | write | Name: | smailto |
Value: 5900 | |||
| (PID) Process: | (3664) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3664) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3664) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3664) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3664) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3664) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3664) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {960E9A30-E814-11E8-A505-5254004AAD11} |
Value: 0 | |||
Executable files
3
Suspicious files
106
Text files
126
Unknown types
110
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3036 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3036 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R12c831x_15jpsx5_2cc.tmp | — | |
MD5:— | SHA256:— | |||
| 3036 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R120abv2_15jpsx4_2cc.tmp | — | |
MD5:— | SHA256:— | |||
| 3036 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R1bmfdmq_15jpsx6_2cc.tmp | — | |
MD5:— | SHA256:— | |||
| 3036 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R14jfq9p_15jpsx7_2cc.tmp | — | |
MD5:— | SHA256:— | |||
| 3036 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R114h82j_15jpsx8_2cc.tmp | — | |
MD5:— | SHA256:— | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF7506239B7A8C4C8C.TMP | — | |
MD5:— | SHA256:— | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF25993A2720134C3C.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
63
DNS requests
123
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3688 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | unknown | — | — | whitelisted |
3688 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/message.zip | unknown | — | — | whitelisted |
3688 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/278_15_23_20070.zip | unknown | — | — | whitelisted |
2932 | firefox.exe | GET | — | 2.18.232.254:80 | http://download.cdn.mozilla.net/pub/firefox/releases/63.0.1/update/win32/en-US/firefox-63.0.1.complete.mar | unknown | — | — | whitelisted |
3688 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | unknown | — | — | whitelisted |
3688 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | unknown | — | — | whitelisted |
3360 | firefox.exe | POST | 200 | 216.58.206.14:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
3360 | firefox.exe | POST | 200 | 216.58.206.14:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
3360 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2932 | firefox.exe | GET | 302 | 34.197.40.184:80 | http://download.mozilla.org/?product=firefox-63.0.1-complete&os=win&lang=en-US | US | html | 129 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2932 | firefox.exe | 52.49.234.55:443 | location.services.mozilla.com | Amazon.com, Inc. | IE | unknown |
2932 | firefox.exe | 2.16.186.50:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
2932 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3664 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
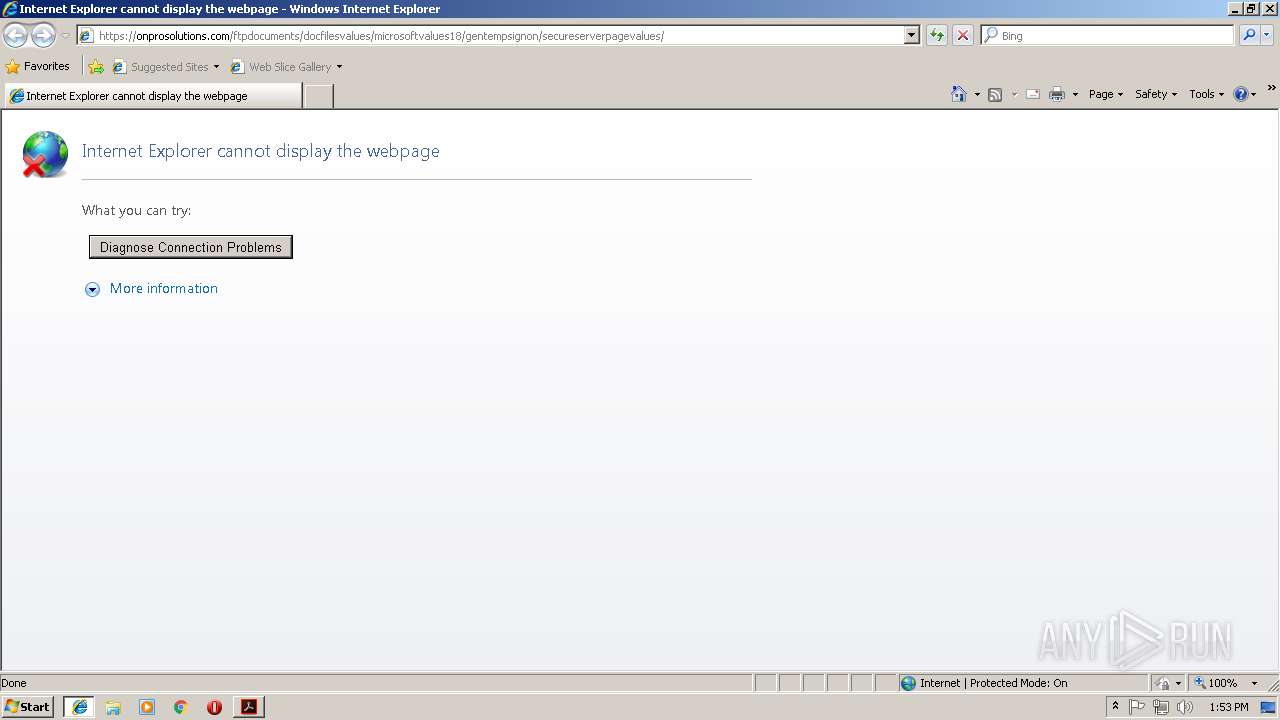
2856 | iexplore.exe | 162.219.248.247:443 | onprosolutions.com | IHNetworks, LLC | US | suspicious |
3688 | AcroRd32.exe | 2.16.186.32:80 | acroipm2.adobe.com | Akamai International B.V. | — | whitelisted |
3688 | AcroRd32.exe | 2.18.233.74:443 | armmf.adobe.com | Akamai International B.V. | — | whitelisted |
— | — | 2.18.233.74:443 | armmf.adobe.com | Akamai International B.V. | — | whitelisted |
3360 | firefox.exe | 2.16.186.112:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
3360 | firefox.exe | 52.39.244.38:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
onprosolutions.com |
| suspicious |
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
tiles.r53-2.services.mozilla.com |
| whitelisted |