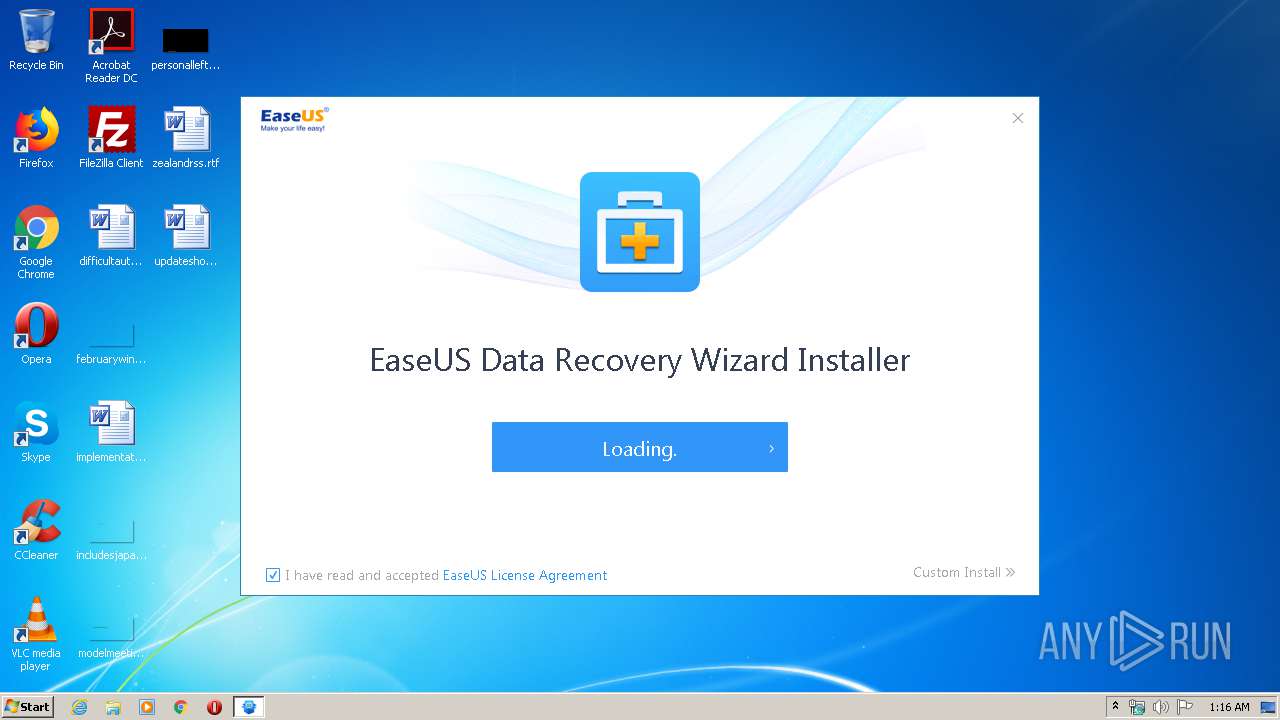
| File name: | DRW_Free_RSS_new_Installer_20200521.7339.exe |
| Full analysis: | https://app.any.run/tasks/1074f945-f85f-4364-bba2-8a43d02bea46 |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | May 22, 2020, 00:16:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | B810425D4DEAD23100B6BD5F4C75845B |
| SHA1: | 23C7FB2E70F51DF6ACC314D8AED120E2C34F78A0 |
| SHA256: | 05CA01225CF8902B8B4F3F11C84CE78FE8B52871D2EFB45ACFFECEAC52D6BBF5 |
| SSDEEP: | 24576:zyh/57wnIsLdkcAj+g+bYTAwbAxmEN/AEQEeX2KCRf4PBFgFhKuYdKU6M6OT:m/peIsxkZZlAwAfivEe+cBin8dYMX |
MALICIOUS
Loads dropped or rewritten executable
- InfoForSetup.exe (PID: 4052)
- InfoForSetup.exe (PID: 1400)
- AliyunWrapExe.Exe (PID: 2440)
- InfoForSetup.exe (PID: 3288)
- InfoForSetup.exe (PID: 1876)
- InfoForSetup.exe (PID: 1468)
- InfoForSetup.exe (PID: 2828)
- InfoForSetup.exe (PID: 2436)
- InfoForSetup.exe (PID: 1116)
- AliyunWrapExe.Exe (PID: 1348)
- InfoForSetup.exe (PID: 3680)
- InfoForSetup.exe (PID: 3816)
- AliyunWrapExe.Exe (PID: 1876)
- InfoForSetup.exe (PID: 1760)
- InfoForSetup.exe (PID: 3288)
- DRW.exe (PID: 3388)
- InfoForSetup.exe (PID: 3444)
- InfoForSetup.exe (PID: 2240)
- InfoForSetup.exe (PID: 2124)
- InfoForSetup.exe (PID: 2780)
- InfoForSetup.exe (PID: 1828)
- InfoForSetup.exe (PID: 376)
- InfoForSetup.exe (PID: 3956)
- DRWUI.exe (PID: 4032)
- InfoForSetup.exe (PID: 3172)
- InfoForSetup.exe (PID: 2956)
- InfoForSetup.exe (PID: 1156)
- InfoForSetup.exe (PID: 2768)
- InfoForSetup.exe (PID: 1468)
- InfoForSetup.exe (PID: 1460)
- InfoForSetup.exe (PID: 3340)
- InfoForSetup.exe (PID: 3956)
- InfoForSetup.exe (PID: 2904)
- InfoForSetup.exe (PID: 2308)
- InfoForSetup.exe (PID: 1456)
- InfoForSetup.exe (PID: 1784)
- InfoForSetup.exe (PID: 4064)
- InfoForSetup.exe (PID: 3312)
- InfoForSetup.exe (PID: 2812)
Application was dropped or rewritten from another process
- InfoForSetup.exe (PID: 1876)
- InfoForSetup.exe (PID: 4052)
- AliyunWrapExe.Exe (PID: 2440)
- InfoForSetup.exe (PID: 3288)
- InfoForSetup.exe (PID: 1116)
- InfoForSetup.exe (PID: 1468)
- InfoForSetup.exe (PID: 2436)
- EDownloader.exe (PID: 348)
- AliyunWrapExe.Exe (PID: 1348)
- InfoForSetup.exe (PID: 1400)
- InfoForSetup.exe (PID: 2828)
- EuSendMessage.exe (PID: 3376)
- InfoForSetup.exe (PID: 3816)
- InfoForSetup.exe (PID: 3680)
- AliyunWrapExe.Exe (PID: 1876)
- SetupUE.exe (PID: 4012)
- InfoForSetup.exe (PID: 1760)
- EUinApp.exe (PID: 3168)
- InfoForSetup.exe (PID: 3288)
- DRW.exe (PID: 3388)
- DRWUI.exe (PID: 4032)
- InfoForSetup.exe (PID: 2240)
- InfoForSetup.exe (PID: 376)
- InfoForSetup.exe (PID: 1828)
- EuDownloader.exe (PID: 3748)
- EUinApp.exe (PID: 2564)
- InfoForSetup.exe (PID: 2124)
- InfoForSetup.exe (PID: 2780)
- InfoForSetup.exe (PID: 3444)
- InfoForSetup.exe (PID: 1156)
- InfoForSetup.exe (PID: 3172)
- InfoForSetup.exe (PID: 2956)
- InfoForSetup.exe (PID: 3340)
- EuDownloader.exe (PID: 2968)
- InfoForSetup.exe (PID: 1460)
- InfoForSetup.exe (PID: 3956)
- InfoForSetup.exe (PID: 3312)
- InfoForSetup.exe (PID: 2768)
- EUUnZip.exe (PID: 2852)
- InfoForSetup.exe (PID: 2812)
- InfoForSetup.exe (PID: 2904)
- InfoForSetup.exe (PID: 3956)
- InfoForSetup.exe (PID: 1456)
- InfoForSetup.exe (PID: 2308)
- InfoForSetup.exe (PID: 4064)
- InfoForSetup.exe (PID: 1784)
- InfoForSetup.exe (PID: 2192)
- InfoForSetup.exe (PID: 1468)
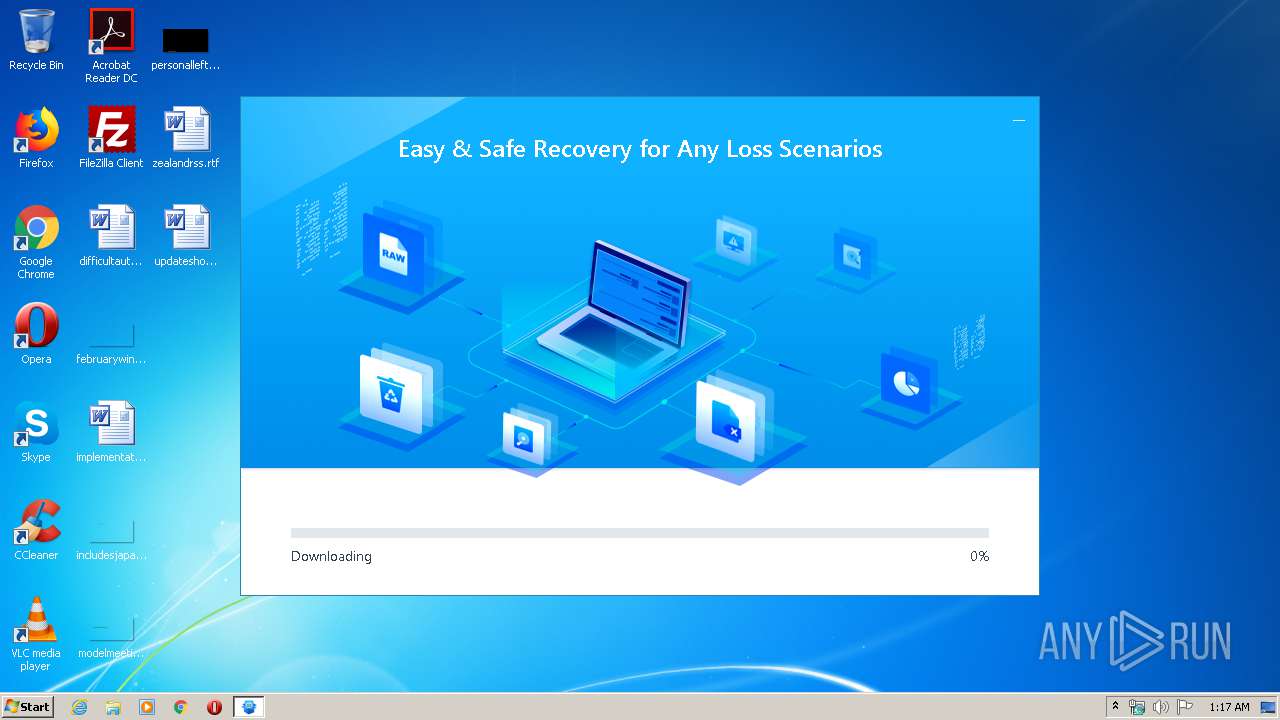
Downloads executable files from the Internet
- EDownloader.exe (PID: 348)
Changes settings of System certificates
- DRWUI.exe (PID: 4032)
SUSPICIOUS
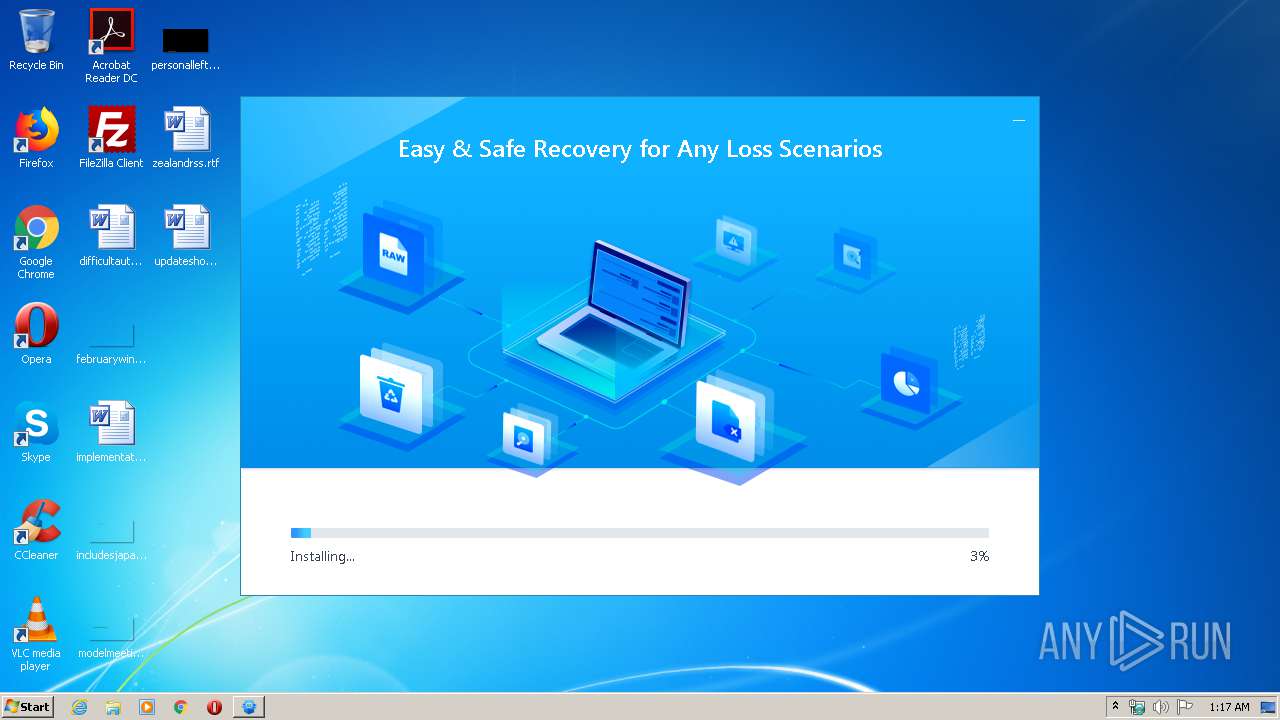
Executable content was dropped or overwritten
- DRW_Free_RSS_new_Installer_20200521.7339.exe (PID: 3204)
- DRW13.5_Free.tmp (PID: 3552)
- DRW13.5_Free.exe (PID: 2644)
Reads Internet Cache Settings
- AliyunWrapExe.Exe (PID: 2440)
- AliyunWrapExe.Exe (PID: 1348)
- AliyunWrapExe.Exe (PID: 1876)
- EDownloader.exe (PID: 348)
- DRWUI.exe (PID: 4032)
Reads Windows owner or organization settings
- DRW13.5_Free.tmp (PID: 3552)
Reads the Windows organization settings
- DRW13.5_Free.tmp (PID: 3552)
Reads internet explorer settings
- EDownloader.exe (PID: 348)
- DRWUI.exe (PID: 4032)
Changes IE settings (feature browser emulation)
- EUinApp.exe (PID: 3168)
- EUinApp.exe (PID: 2564)
Creates files in the program directory
- AliyunWrapExe.Exe (PID: 1876)
- DRW.exe (PID: 3388)
- DRWUI.exe (PID: 4032)
- EuDownloader.exe (PID: 3748)
- EuDownloader.exe (PID: 2968)
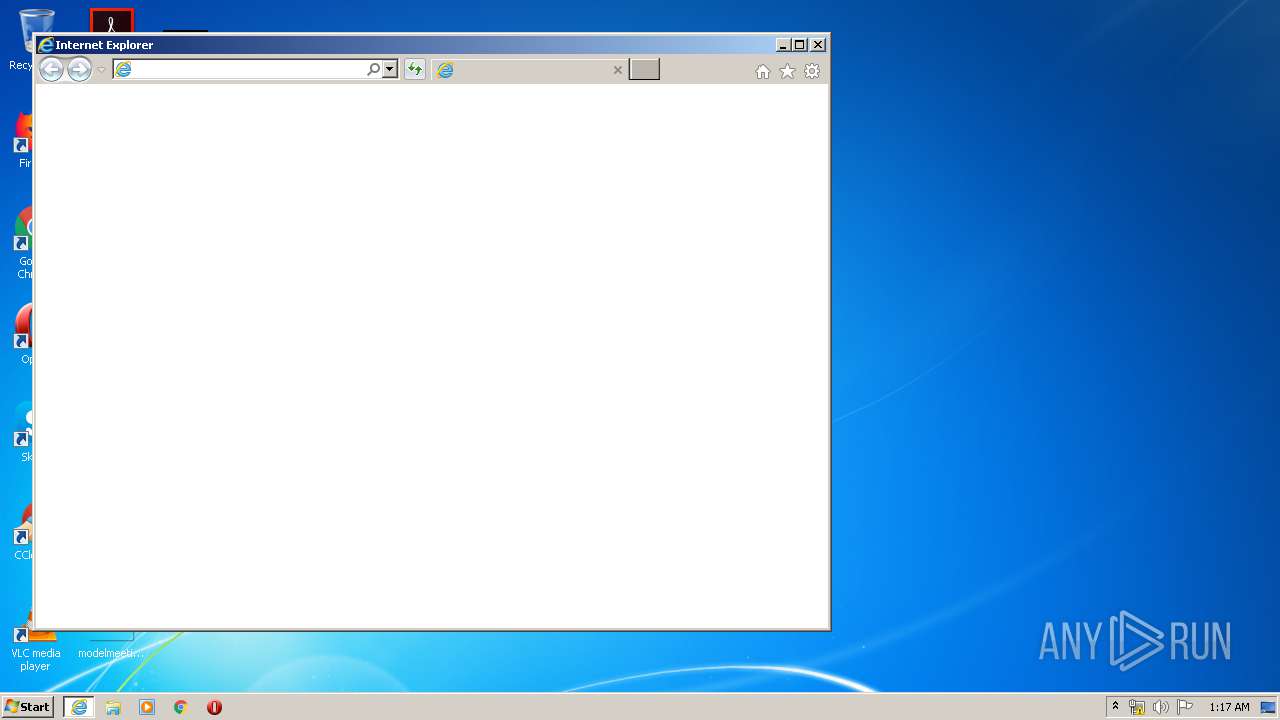
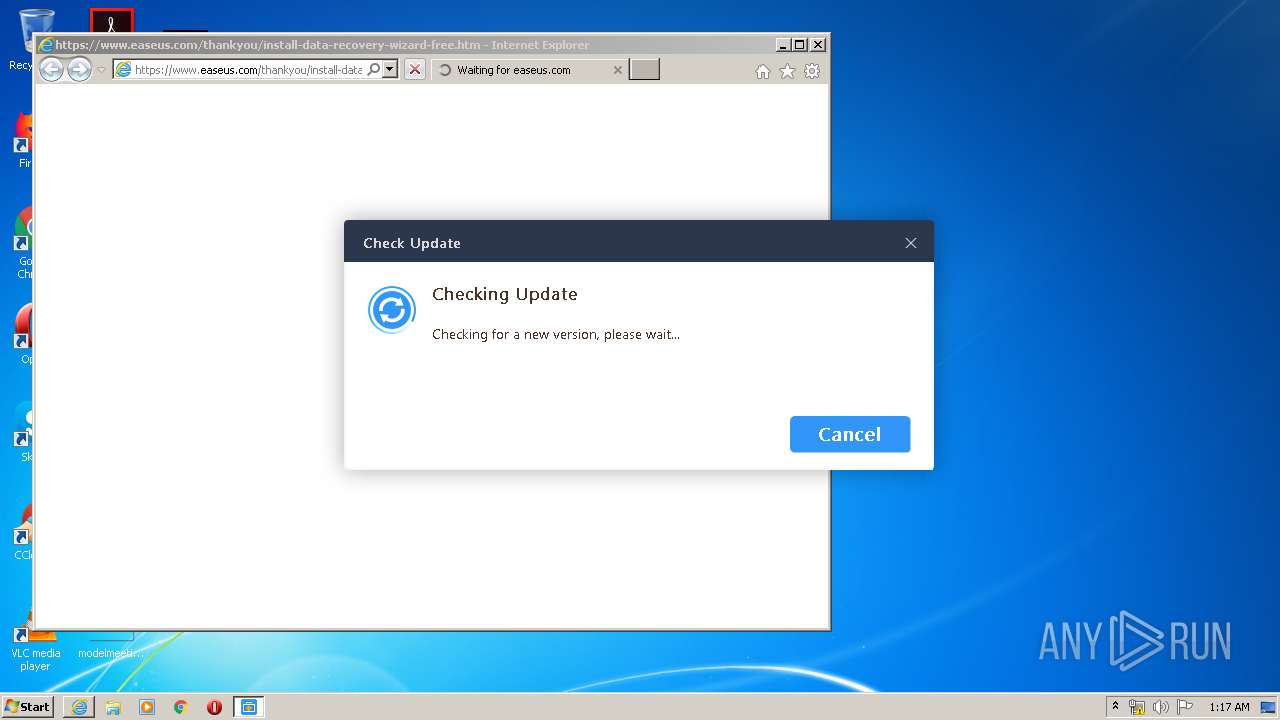
Starts Internet Explorer
- EDownloader.exe (PID: 348)
Low-level read access rights to disk partition
- DRWUI.exe (PID: 4032)
Executes PowerShell scripts
- DRWUI.exe (PID: 4032)
Creates files in the user directory
- PowerShell.exe (PID: 3148)
- DRWUI.exe (PID: 4032)
Adds / modifies Windows certificates
- DRWUI.exe (PID: 4032)
INFO
Application was dropped or rewritten from another process
- InfoForSetup.exe (PID: 2248)
- InfoForSetup.exe (PID: 880)
- InfoForSetup.exe (PID: 2720)
- InfoForSetup.exe (PID: 572)
- DRW13.5_Free.tmp (PID: 3552)
- InfoForSetup.exe (PID: 2544)
Loads dropped or rewritten executable
- InfoForSetup.exe (PID: 2248)
- InfoForSetup.exe (PID: 880)
- InfoForSetup.exe (PID: 572)
- InfoForSetup.exe (PID: 2720)
- InfoForSetup.exe (PID: 2544)
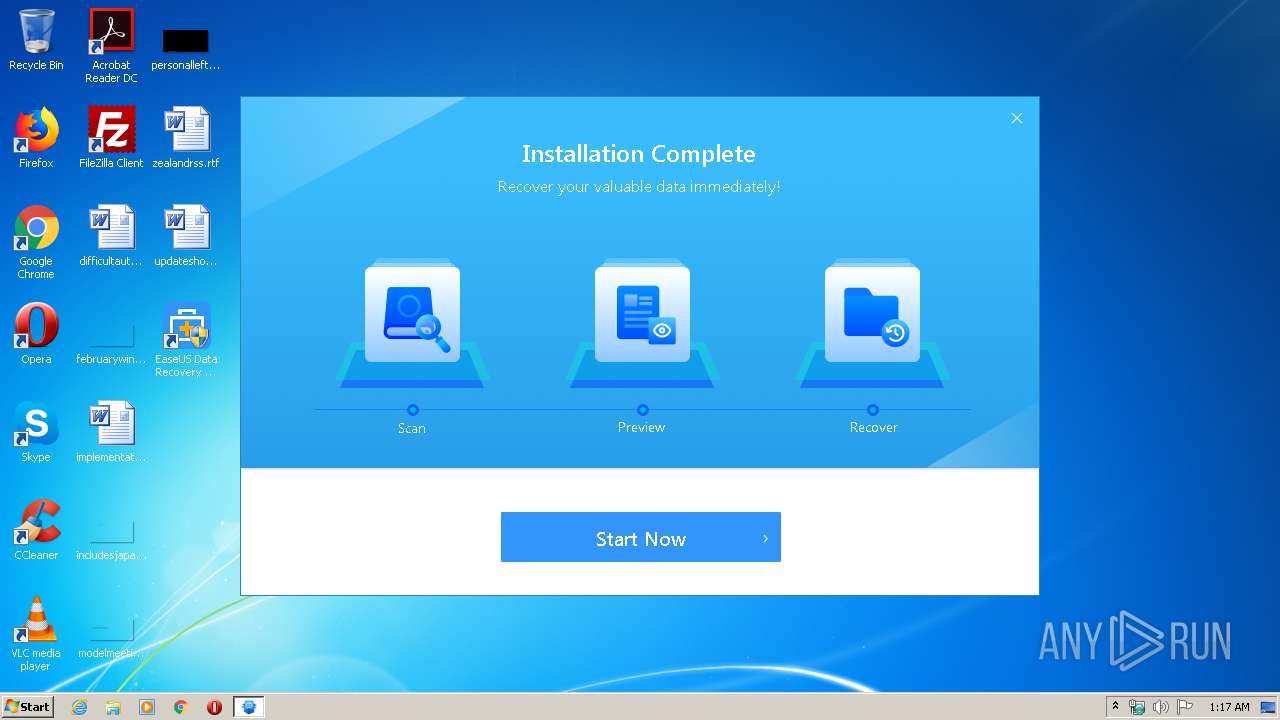
Creates a software uninstall entry
- DRW13.5_Free.tmp (PID: 3552)
Changes internet zones settings
- iexplore.exe (PID: 3868)
Reads Internet Cache Settings
- iexplore.exe (PID: 3868)
- iexplore.exe (PID: 1740)
Creates files in the program directory
- DRW13.5_Free.tmp (PID: 3552)
Application launched itself
- iexplore.exe (PID: 3868)
Reads settings of System Certificates
- iexplore.exe (PID: 1740)
- DRWUI.exe (PID: 4032)
- iexplore.exe (PID: 3868)
Reads internet explorer settings
- iexplore.exe (PID: 1740)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1740)
Creates files in the user directory
- iexplore.exe (PID: 3868)
Changes settings of System certificates
- iexplore.exe (PID: 1740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 04:57:48+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x338f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Jan-2018 03:57:48 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Jan-2018 03:57:48 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006627 | 0x00006800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45224 |
.rdata | 0x00008000 | 0x0000149A | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.00708 |
.data | 0x0000A000 | 0x0002AFF8 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.03532 |
.ndata | 0x00035000 | 0x00010000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00045000 | 0x00010D40 | 0x00010E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.14037 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28733 | 841 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.86193 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 5.0916 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 3.68334 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 3.86293 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 3.67461 | 1640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.5329 | 1384 | UNKNOWN | English - United States | RT_ICON |
8 | 5.22737 | 1128 | UNKNOWN | English - United States | RT_ICON |
9 | 3.99637 | 744 | UNKNOWN | English - United States | RT_ICON |
10 | 3.53259 | 296 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
118
Monitored processes
63
Malicious processes
6
Suspicious processes
27
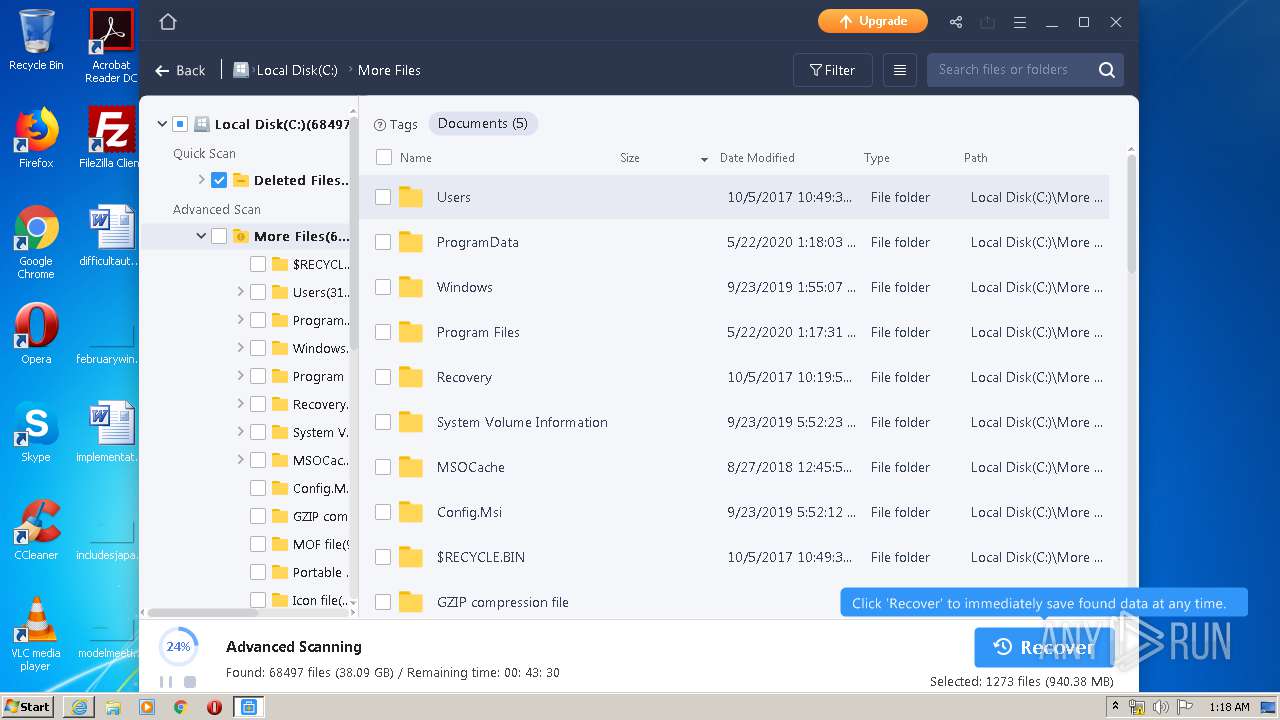
Behavior graph
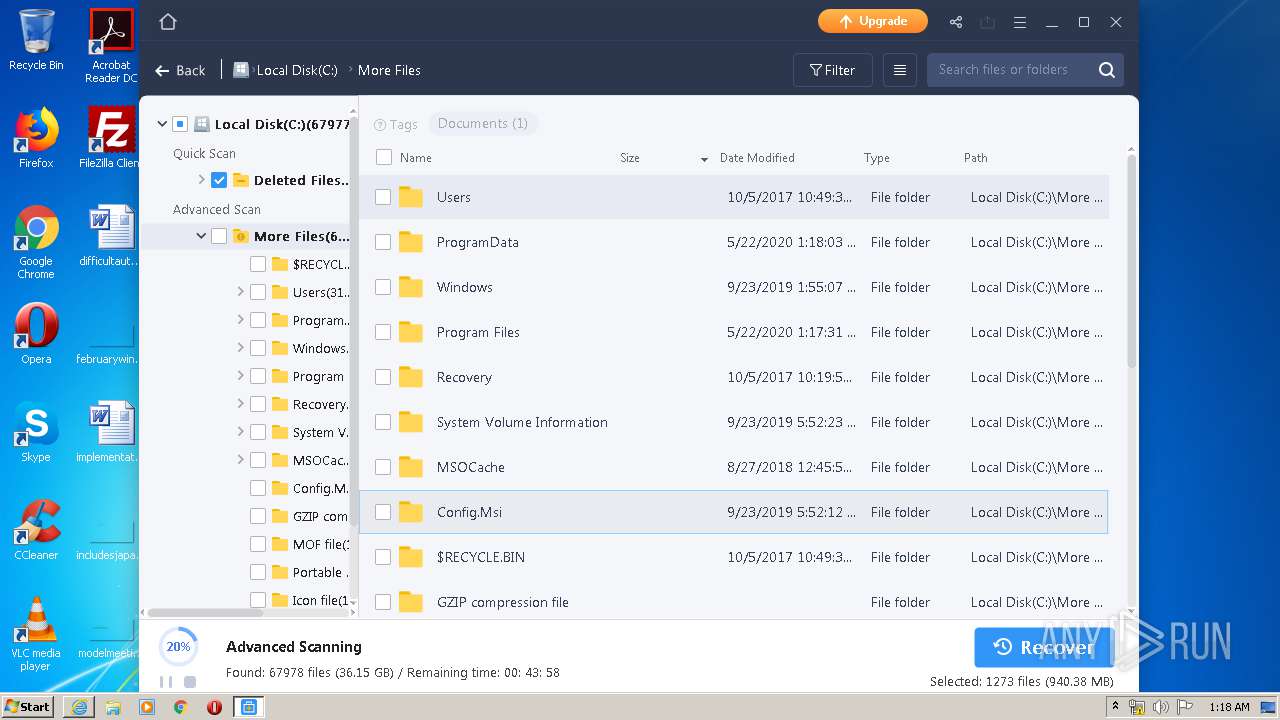
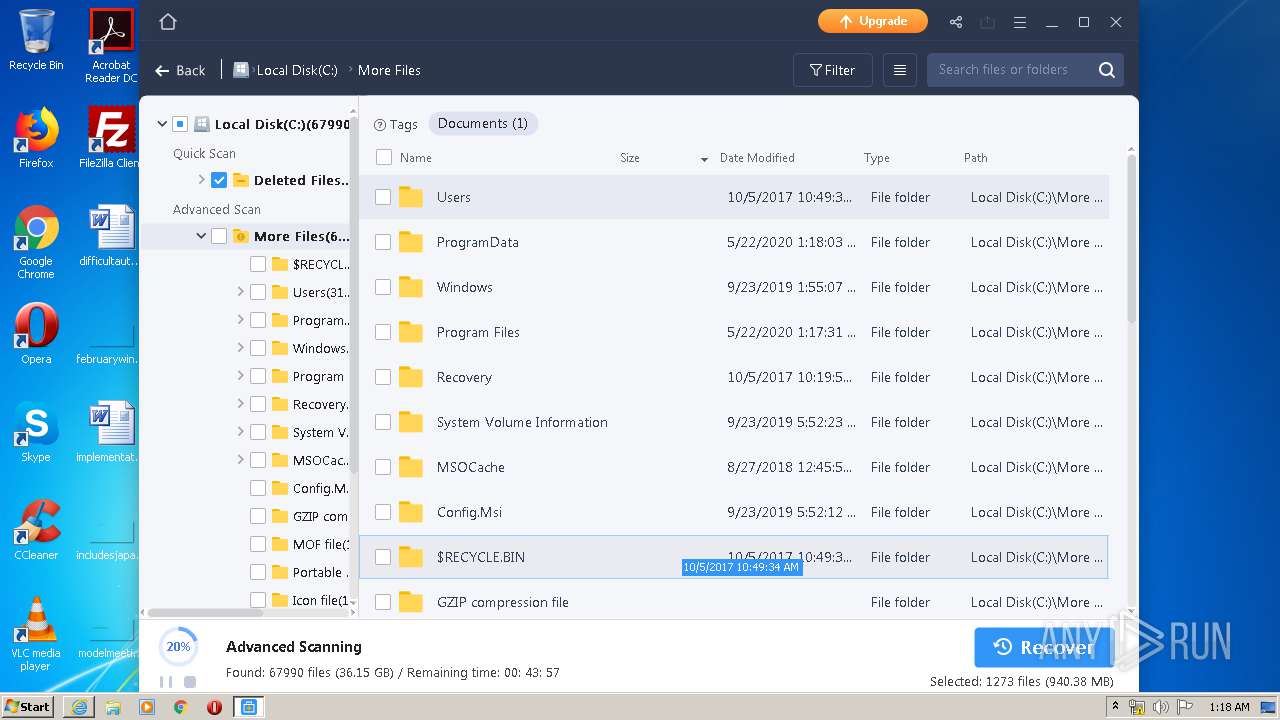
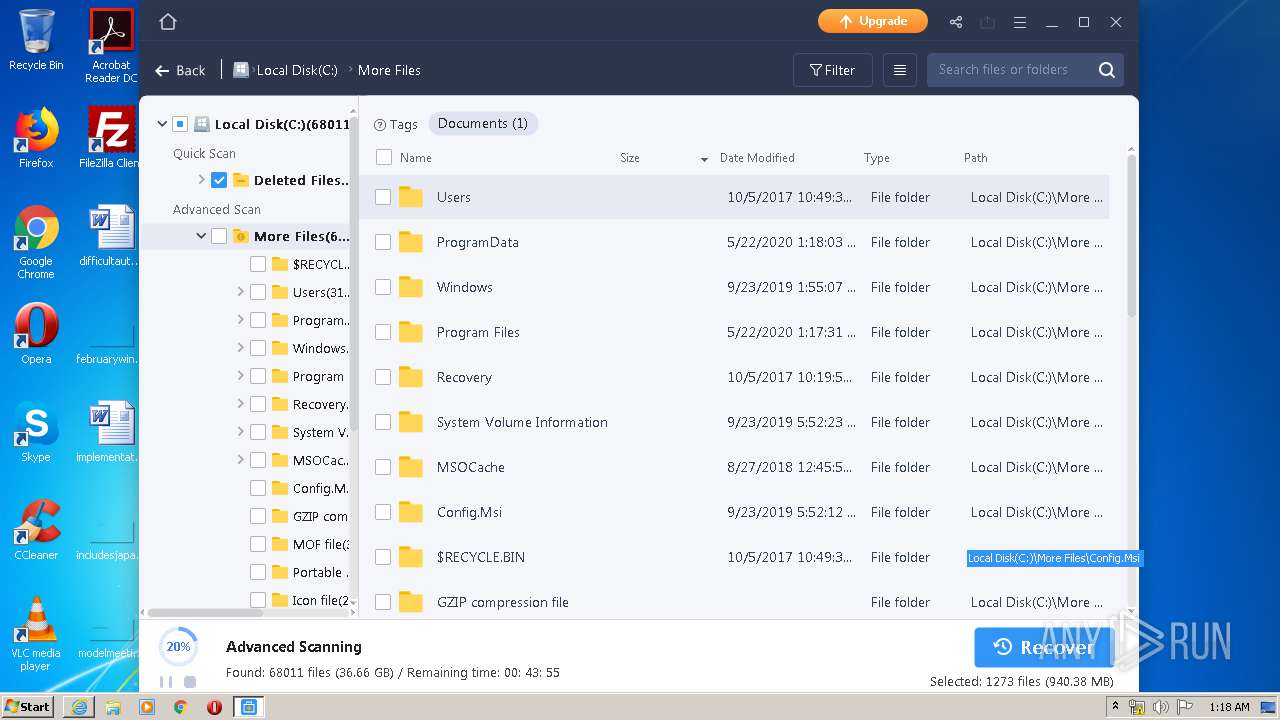
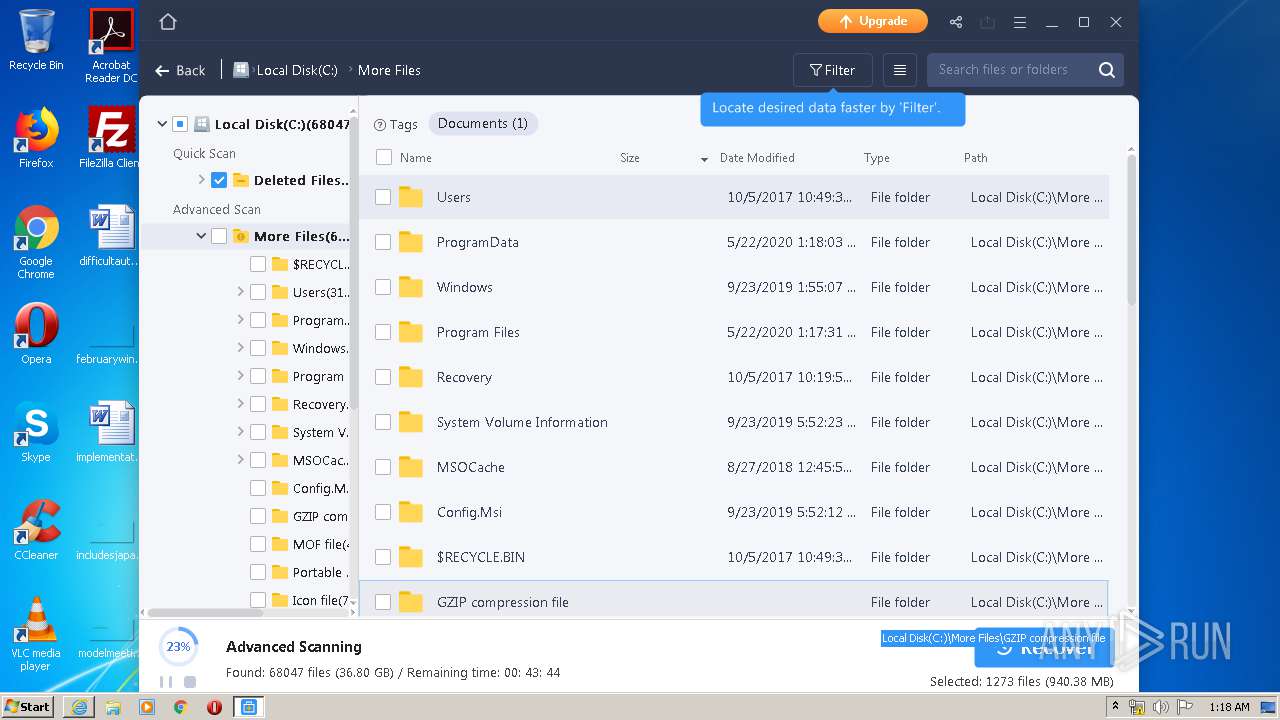
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | "C:\Users\admin\AppData\Local\Temp\DRW_Free_RSS_new_Installer_20200521.7339.exe" | C:\Users\admin\AppData\Local\Temp\DRW_Free_RSS_new_Installer_20200521.7339.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 348 | "C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2FreeB\EDownloader.exe" EXEDIR=C:\Users\admin\AppData\Local\Temp ||| EXENAME=DRW_Free_RSS_new_Installer_20200521.7339.exe ||| DOWNLOAD_VERSION=FreeB ||| PRODUCT_VERSION=1.0.0 ||| INSTALL_TYPE=0 | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2FreeB\EDownloader.exe | DRW_Free_RSS_new_Installer_20200521.7339.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 376 | /SendInfo Window "Loading" Activity "Info_Wmic_Diskdrive" Attribute "[\"Availability BytesPerSector Capabilities CapabilityDescriptions Caption CompressionMethod ConfigManagerErrorCode ConfigManagerUserConfig CreationClassName DefaultBlockSize Description DeviceID ErrorCleared ErrorDescription ErrorMethodology FirmwareRevision Index InstallDate InterfaceType LastErrorCode Manufacturer MaxBlockSize MaxMediaSize MediaLoaded MediaType MinBlockSize Model Name NeedsCleaning NumberOfMediaSupported Partitions PNPDeviceID PowerManagementCapabilities PowerManagementSupported SCSIBus SCSILogicalUnit SCSIPort SCSITargetId SectorsPerTrack SerialNumber Signature Size Status StatusInfo SystemCreationClassName SystemName TotalCylinders TotalHeads TotalSectors TotalTracks TracksPerCylinder ___ 512 _3_ 4_ 10_ __Random Access__ _Supports Writing__ _SMART Notification__ WDC WD20EARS ATA Device 0 FALSE Win32_DiskDrive Disk drive //./PHYSICALDRIVE0 1.1.0 0 IDE _Standard disk drives_ TRUE Fixed hard disk media WDC WD20EARS ATA Device //./PHYSICALDRIVE0 2 IDE/DISKWDC_WD20EARS____________________________1.1.0___/5&2770A7AF&0&0.0.0 0 0 0 0 63 4d51303030302031202020202020202020202020 1660034144 274872407040 OK Win32_ComputerSystem USER_PC 33418 255 536860170 8521590 255 ______\"]" | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\aliyun\InfoForSetup.exe | — | DRWUI.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 572 | "C:\Users\admin\AppData\Local\Temp\is-U2FVT.tmp\InfoForSetup.exe" /SendInfo "Window" "Selectdestinationlocation" "Activity" "Click_Confirm" "Attribute" "{\"Path\":\"C:/Program Files/EaseUS/EaseUS Data Recovery Wizard\"}" | C:\Users\admin\AppData\Local\Temp\is-U2FVT.tmp\InfoForSetup.exe | — | DRW13.5_Free.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 880 | "C:\Users\admin\AppData\Local\Temp\is-U2FVT.tmp\InfoForSetup.exe" /SendInfo "Window" "Licenseagreement" "Activity" "Click_Accept" | C:\Users\admin\AppData\Local\Temp\is-U2FVT.tmp\InfoForSetup.exe | — | DRW13.5_Free.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1116 | /SendInfo Window "Downloading" Activity "Info_Start_Download_Program" Attribute "{\"Downloadfrom\":\"http://download.easeus.com/free/DRW13.5_Free.exe\",\"Pageid\":\"7339\",\"Testid\":\"1352020052112\",\"Version\":\"Free\",\"Versionnumber\":\"13.5.0.0\"}" | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2FreeB\aliyun\InfoForSetup.exe | — | EDownloader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1156 | /SendInfo Window "Loading" Activity "Info_Partition" Attribute "{\"Partitioninfo\":{\"Partition1\":[\"WDC WD20EARS\",\"System Reserved\",\"\",\"lost\",\"100.00MB\",\"\",\"\",\"ntfs\",\"\",\"basic\"],\"Partition2\":[\"WDC WD20EARS\",\"\",\"C\",\"existing\",\"262042.00MB\",\"35475.38MB\",\"226566.62MB\",\"ntfs\",\"\",\"basic\"]}}" | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\aliyun\InfoForSetup.exe | — | DRWUI.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1348 | C:\Users\admin\AppData\Local\Temp\is-U2FVT.tmp\AliyunWrapExe.Exe | C:\Users\admin\AppData\Local\Temp\is-U2FVT.tmp\AliyunWrapExe.Exe | InfoForSetup.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1400 | /SendInfo Window "Home_Installer" Activity "Click_Install" Attribute "{\"Install_Path\":\"C:/Program Files/EaseUS/EaseUS Data Recovery Wizard\",\"Language\":\"English\",\"Os\":\"Microsoft Windows 7\",\"Pageid\":\"7339\",\"Timezone\":\"GMT-00:00\"}" | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2FreeB\aliyun\InfoForSetup.exe | — | EDownloader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
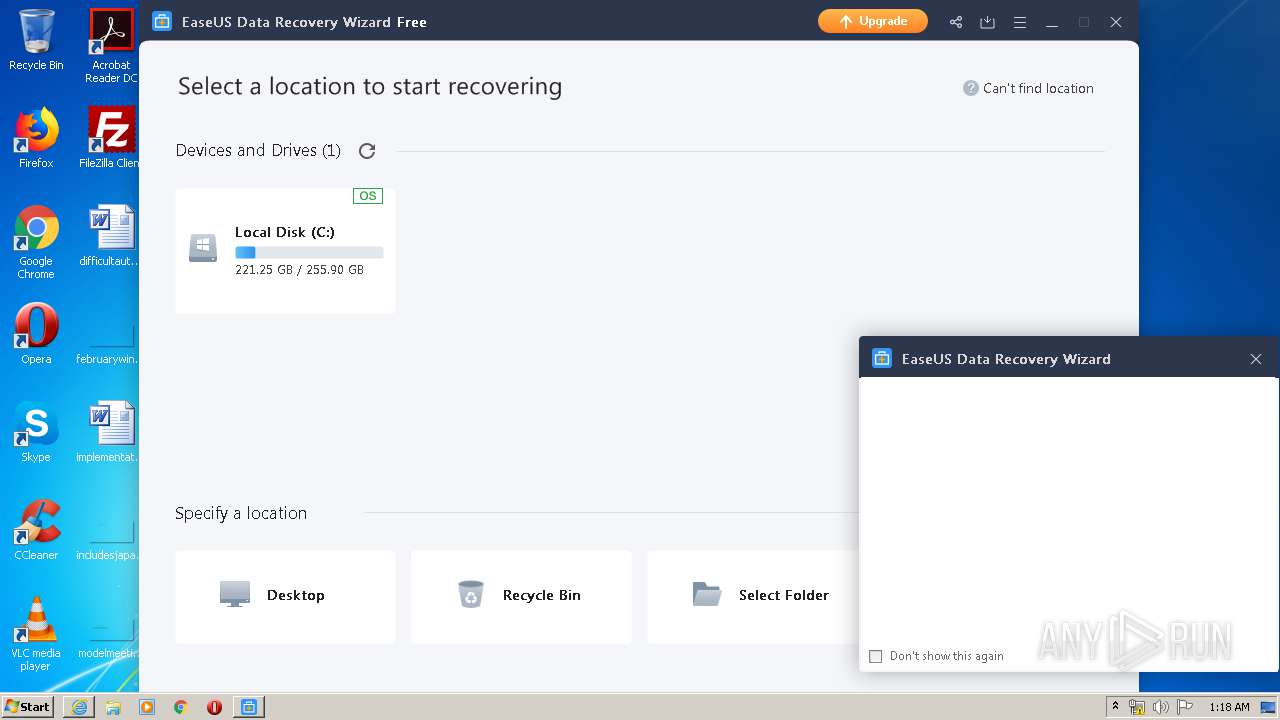
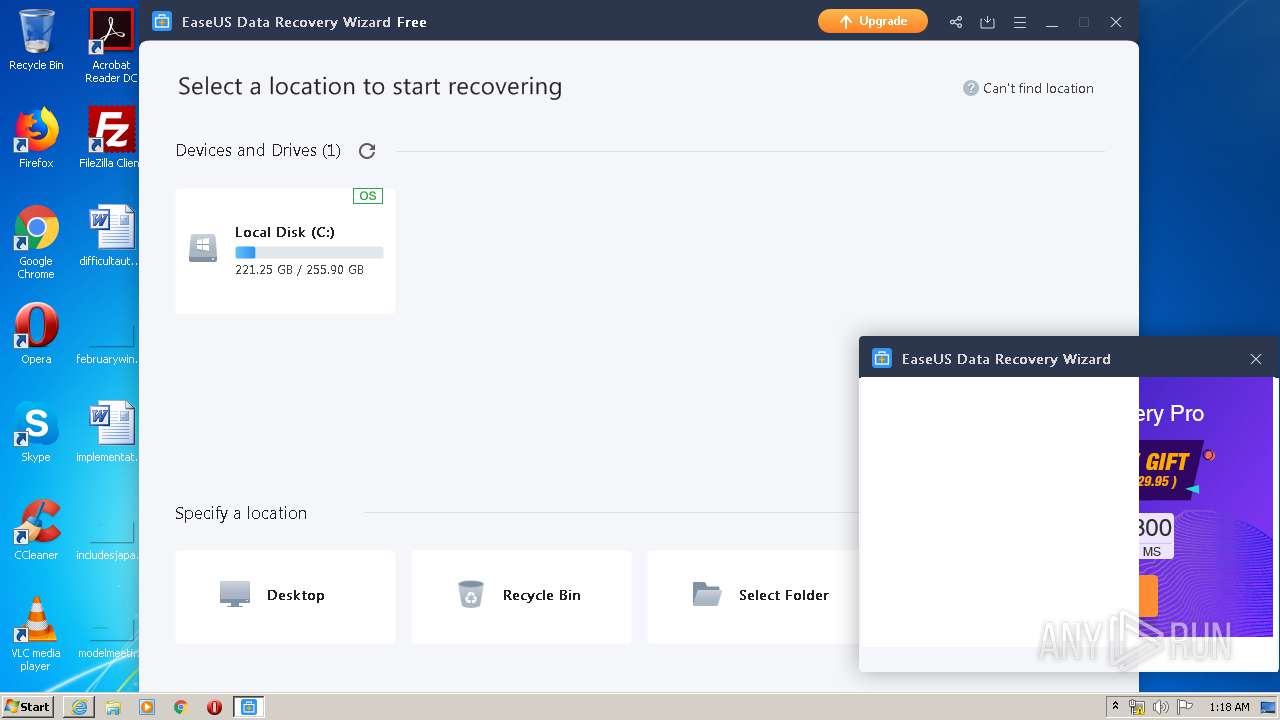
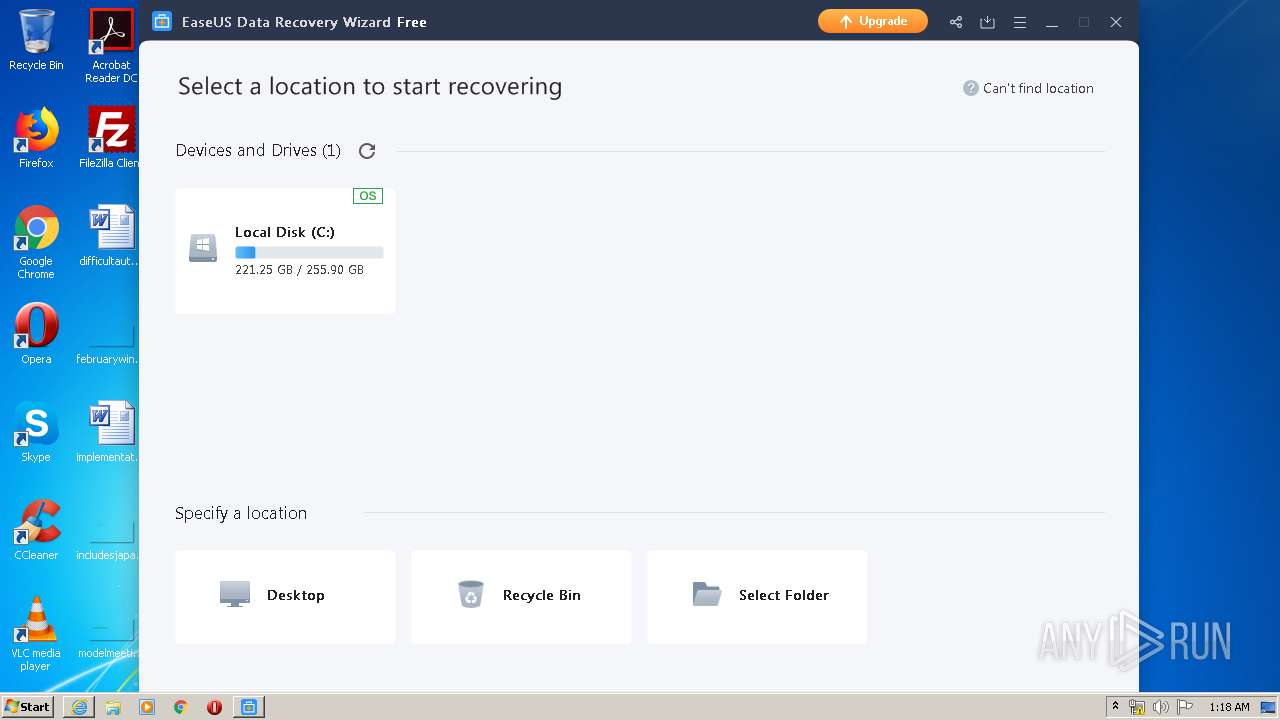
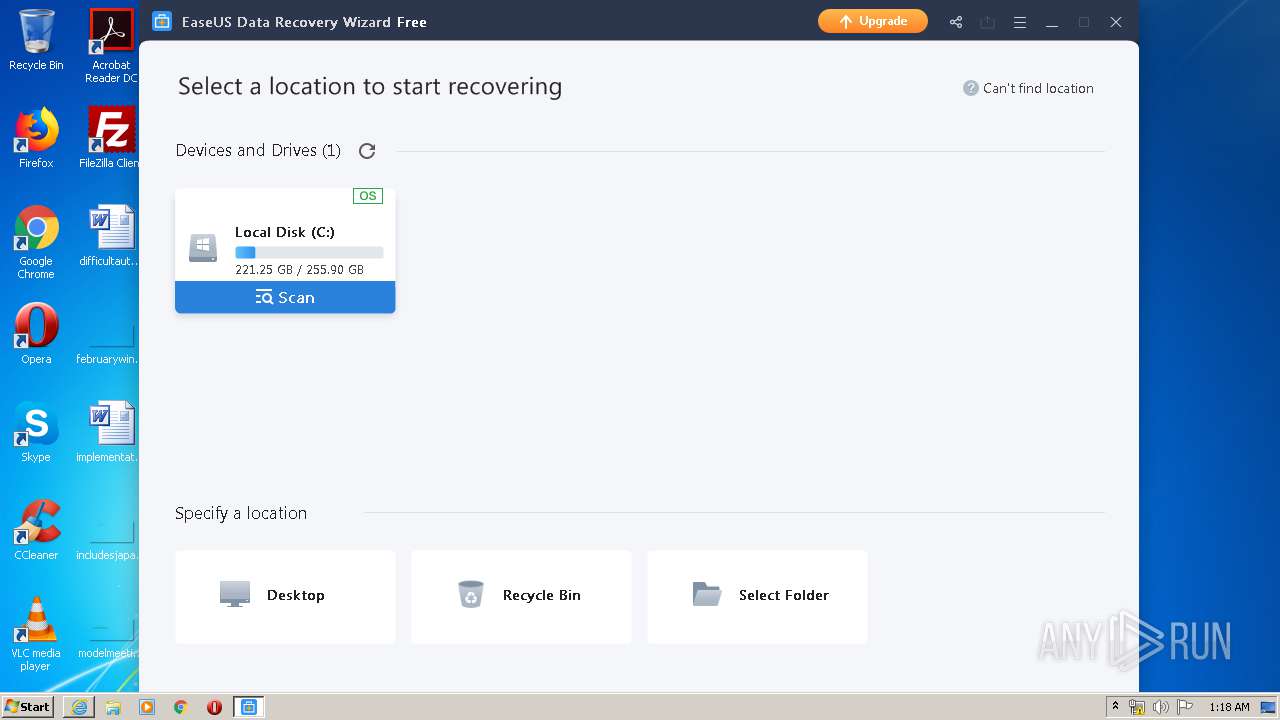
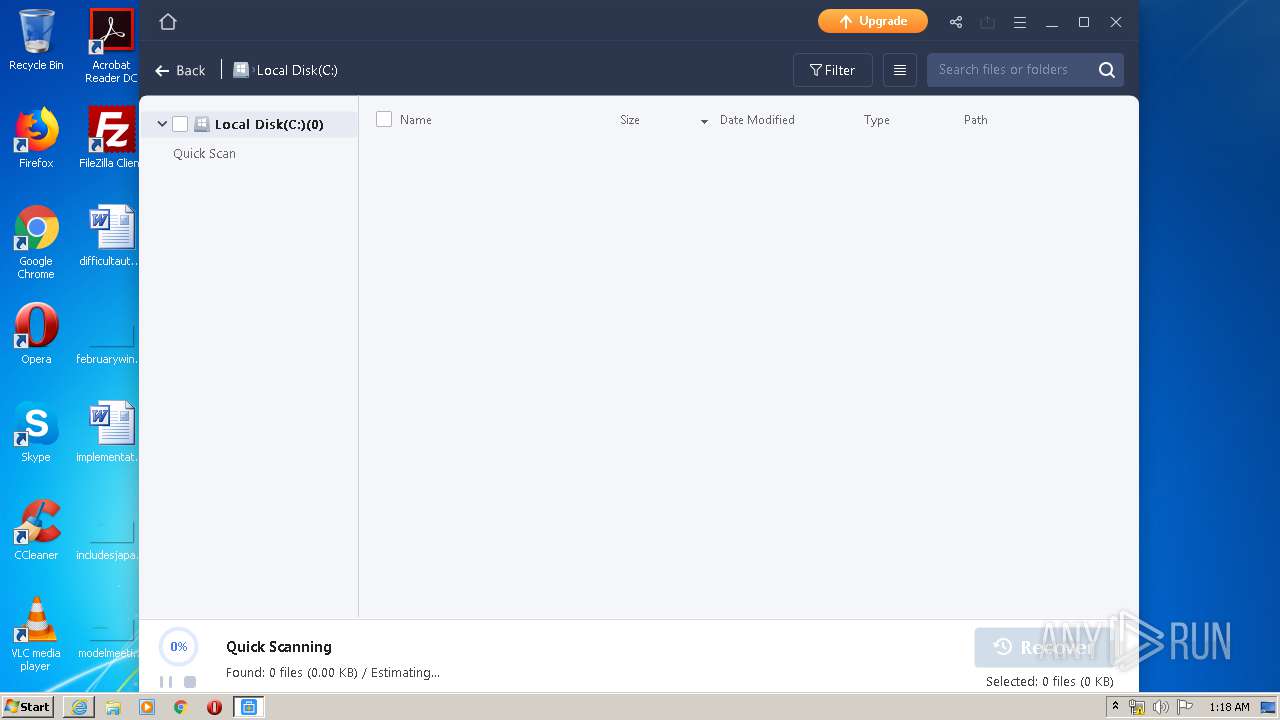
| 1456 | /SendInfo Window "Selectlocation" Activity "Click_Scanbutton" Attribute "{\"Scan\":[\"\",\"C\",\"262042.00MB\",\"35476.38MB\",\"226565.62MB\",\"ntfs\",\"internal\",\"existing\",\"\",\"basic\",\"Local Disk (C:)\"]}" | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\aliyun\InfoForSetup.exe | — | DRWUI.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
4 029
Read events
2 066
Write events
1 957
Delete events
6
Modification events
| (PID) Process: | (2440) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2440) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2440) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2440) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2440) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2440) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2440) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (348) EDownloader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (348) EDownloader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (348) EDownloader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
63
Suspicious files
45
Text files
2 142
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3204 | DRW_Free_RSS_new_Installer_20200521.7339.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2FreeB\skin.zip | compressed | |
MD5:— | SHA256:— | |||
| 3204 | DRW_Free_RSS_new_Installer_20200521.7339.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2FreeB\Danish.ini | text | |
MD5:— | SHA256:— | |||
| 3204 | DRW_Free_RSS_new_Installer_20200521.7339.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2FreeB\Mungarian.ini | text | |
MD5:— | SHA256:— | |||
| 3204 | DRW_Free_RSS_new_Installer_20200521.7339.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2FreeB\Japanese.ini | text | |
MD5:— | SHA256:— | |||
| 3204 | DRW_Free_RSS_new_Installer_20200521.7339.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2FreeB\Chinese.ini | text | |
MD5:— | SHA256:— | |||
| 3204 | DRW_Free_RSS_new_Installer_20200521.7339.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2FreeB\Korean.ini | text | |
MD5:— | SHA256:— | |||
| 3204 | DRW_Free_RSS_new_Installer_20200521.7339.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2FreeB\EDownloader.exe | executable | |
MD5:— | SHA256:— | |||
| 3204 | DRW_Free_RSS_new_Installer_20200521.7339.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2FreeB\German.ini | text | |
MD5:— | SHA256:— | |||
| 3204 | DRW_Free_RSS_new_Installer_20200521.7339.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2FreeB\Indonesian.ini | text | |
MD5:— | SHA256:— | |||
| 3204 | DRW_Free_RSS_new_Installer_20200521.7339.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2FreeB\Dutch.ini | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
62
TCP/UDP connections
87
DNS requests
29
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
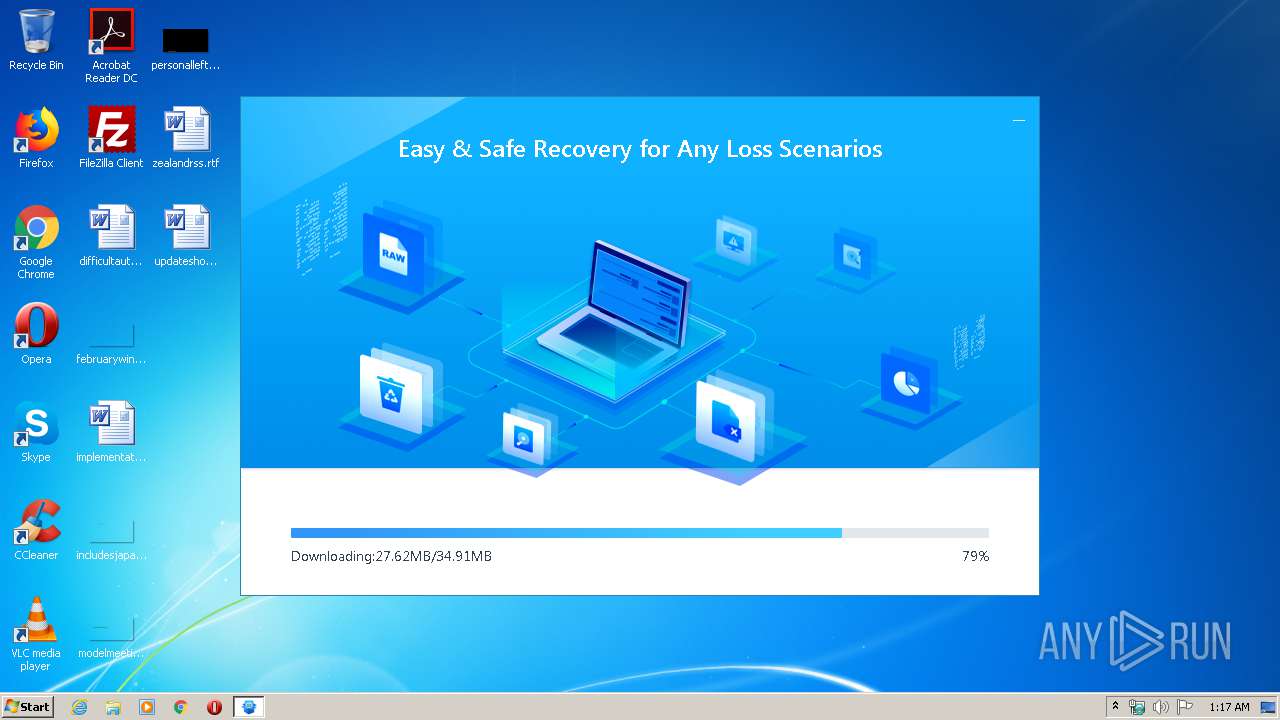
348 | EDownloader.exe | GET | — | 205.185.216.10:80 | http://download.easeus.com/free/DRW13.5_Free.exe | US | — | — | malicious |
348 | EDownloader.exe | GET | 206 | 205.185.216.10:80 | http://download.easeus.com/free/DRW13.5_Free.exe | US | binary | 11.6 Mb | malicious |
2440 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.15:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | US | — | — | malicious |
1348 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.15:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_windrw_ip/shards/lb | US | — | — | malicious |
2440 | AliyunWrapExe.Exe | POST | — | 47.252.97.15:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | US | — | — | malicious |
1348 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.15:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_windrw_ip/shards/lb | US | — | — | malicious |
2440 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.15:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | US | — | — | malicious |
2440 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.15:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | US | — | — | malicious |
1348 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.15:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_windrw_ip/shards/lb | US | — | — | malicious |
348 | EDownloader.exe | GET | 206 | 205.185.216.10:80 | http://download.easeus.com/free/DRW13.5_Free.exe | US | binary | 11.6 Mb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2440 | AliyunWrapExe.Exe | 216.92.47.198:80 | track.easeus.com | pair Networks | US | suspicious |
348 | EDownloader.exe | 205.185.216.42:443 | update.easeus.com | Highwinds Network Group, Inc. | US | whitelisted |
2440 | AliyunWrapExe.Exe | 47.252.97.15:80 | easeusinfo.us-east-1.log.aliyuncs.com | Alibaba (China) Technology Co., Ltd. | US | unknown |
348 | EDownloader.exe | 205.185.216.10:80 | update.easeus.com | Highwinds Network Group, Inc. | US | whitelisted |
1348 | AliyunWrapExe.Exe | 216.92.47.198:80 | track.easeus.com | pair Networks | US | suspicious |
1876 | AliyunWrapExe.Exe | 216.92.47.198:80 | track.easeus.com | pair Networks | US | suspicious |
1348 | AliyunWrapExe.Exe | 47.252.97.15:80 | easeusinfo.us-east-1.log.aliyuncs.com | Alibaba (China) Technology Co., Ltd. | US | unknown |
1876 | AliyunWrapExe.Exe | 47.252.97.15:80 | easeusinfo.us-east-1.log.aliyuncs.com | Alibaba (China) Technology Co., Ltd. | US | unknown |
348 | EDownloader.exe | 216.92.47.198:80 | track.easeus.com | pair Networks | US | suspicious |
1740 | iexplore.exe | 163.171.132.119:443 | www.easeus.com | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
update.easeus.com |
| whitelisted |
track.easeus.com |
| suspicious |
easeusinfo.us-east-1.log.aliyuncs.com |
| unknown |
download.easeus.com |
| malicious |
www.easeus.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
mail.easeus.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
348 | EDownloader.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
348 | EDownloader.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
EDownloader.exe | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\DRW.exe,0 |
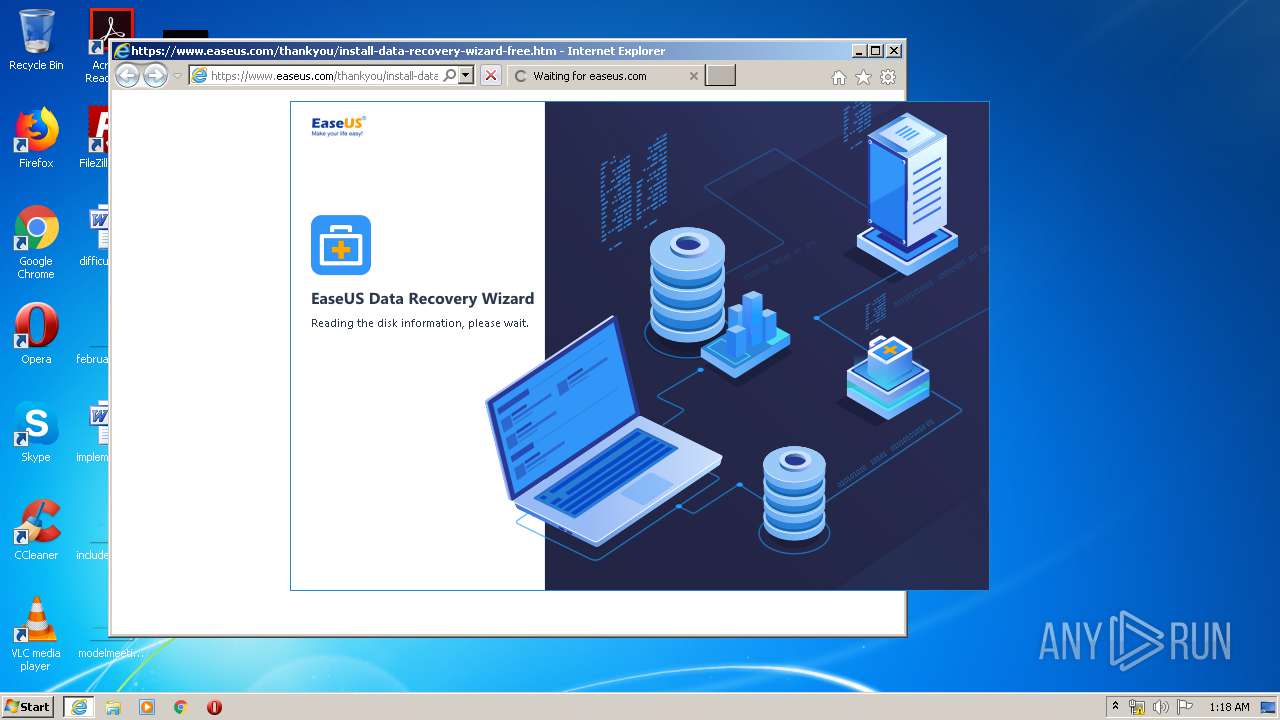
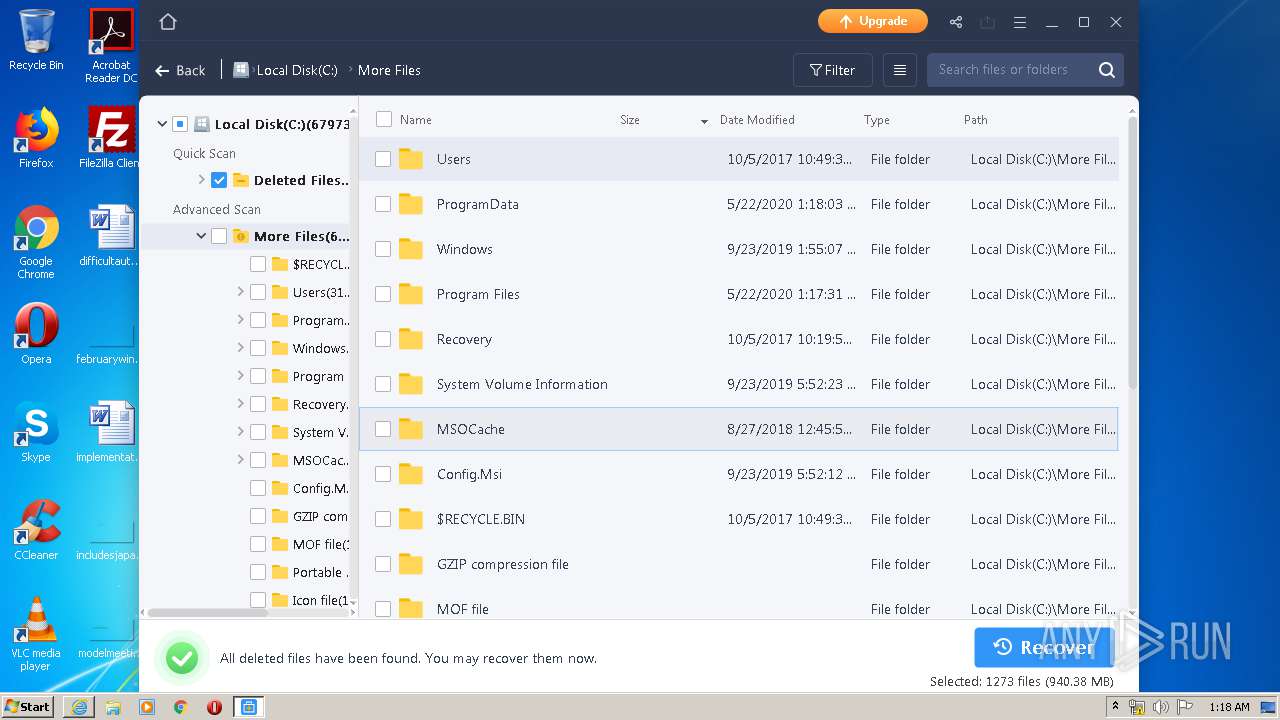
DRWUI.exe | 01:17:56:526 P[4032]:T[3948] run to EnumCollectPartition::EnumThread 430
|
DRWUI.exe | 01:17:56:511 DRWUI [13.5] build at[Apr 29 2020 10:55:08] [7a11dff4fcfbb053e2f2158f339cff908ab0468d],be x64[no]
|
DRWUI.exe | 01:17:56:542 P[4032]:T[3948] run to EnumCollectPartition::EnumThread 433
|
DRWUI.exe | 01:17:56:573 P[4032]:T[3948] run to EnumCollectPartition::EnumThread 441
|
DRWUI.exe | 01:17:56:573 P[4032]:T[3948] run to EnumCollectPartition::EnumThread 492
|
DRWUI.exe | CCollectAllBasicPartitionandDynamicVolume::sort dwElapsedTime 0
|
DRWUI.exe | CCollectAllBasicPartitionandDynamicVolume::CollectAllBasicPartitionandDynamicVolume dwElapsedTime 32
|
DRWUI.exe | 01:17:57:808 P[4032]:T[4080] run to CDRWUIApp::CheckNeedAutoUpdate 250
|
DRWUI.exe | 01:17:59:542 CheckUpdate::UseMsUrlmon2CheckThread:486 got 0
|